Abstract
There is a global danger that hides in the shadows and is changing the way continuing care operators care for residents. Today, to provide that same historical level of resident care, a group of techno-soldiers are not just a nice-to-have, but are a must, to protect our critical Information Technology (IT) infrastructure. There is little doubt that technology has enabled us to provide better care. Electronic medical records, human resources information systems, and voice over Internet communications systems have created great efficiencies in operations. However, global cybercriminals lurk in the same technologies that support us. Continuously attempting to rob our private information and hold us ransom, or play havoc with our IT systems impeding our provision of care. How can a continuing care operator, an already funding-challenged industry balance the costs of protecting their IT infrastructure against this growing massive threat? Compounding the issue, rising insurance expectations for continuing care operators to continuously enhance their IT safety controls against evolving cyberterrorism. This is the story of the Good Samaritan Society/Canada (Good Samaritan) digital transformation journey. Our digital roadmap sets Good Samaritan up to rise above the ongoing barrage of cyberattacks and loss of insurance. This is a digital divide story of David vs. Goliath.
Introduction
A global danger hides in the shadows and is challenging how continuing care operators care for residents. Not long ago, the sole concern for continuing care operators was ensuring residents received the highest quality of care from compassionate employees. Today, to provide that same level of resident support, a group of techno-soldiers are not just a nice-to-have but are a must have to protect our critical Information Technology (IT) infrastructure.
While technology has enabled us to provide better care, the offshoot is that healthcare “has seen a growing interest in information security. Cyberattacks in the industry and consumer sectors have been widely echoed in the past and recent cyberattacks in the healthcare sector are of concern.” 1 Electronic medical records, human resource information systems, and digital voice communications systems have created significant efficiencies in operations. However, criminals lurk in the technologies that support us, continuously attempting to steal our private information and hold us ransom or play havoc with our IT systems—impeding our ability to provide care. Dupont reminds us that “as in any period when new risks are emerging, wrongdoers will benefit from a window of opportunity when the public remains poorly informed of the vulnerabilities to which they are exposed and what protective measures they should implement.” 2 The warning signs are all around us, we are at a critical point in the advancements of technology, and we must be vigilant to protect our infrastructure.
How can a continuing care operator in an already funding-challenged industry balance the costs of protecting their IT infrastructure against this growing threat? This is a modern-day David vs. Goliath battle. Only this time, relying on a sole individual armed with a slingshot may not suffice in combatting an enigma that is both technological and adaptive in nature.
The Good Samaritan Society & Good Samaritan Canada (Good Samaritan) are a faith-based, not-for-profit organizations serving close to 6,000 seniors in Alberta and British Columbia. It has been facing this challenge over the past five years. Being good stewards of our publicly allocated dollars, Good Samaritan, like other operators, is limited in how quickly we can keep up with the increasing costs of technological demands. While there is a cost-benefit towards implementing technology in the form of software and hardware, a thoughtful strategic plan and roadmap is necessary to harness those efficiencies and to protect the organization against those who would do it harm.
Like all good plans, it all starts by taking the first step. In 2019, Good Samaritan identified the need to enhance its ageing technology infrastructure. Consequently, a digital roadmap was developed through an in-depth stakeholder engagement and industry review. It focused on restoring our infrastructure and enhancing our cybersecurity.
This road map helped identify the highest technology risks to the organization, assessed against industry standards. Consideration was given to technology changes that were necessary but that could also be implemented in a cost-effective manner. The timing of this approach was critical. In addition, the plan evaluated the commitments of the organization to apply the various technical changes to bring us in compliance with industry expectations as they pertain to valid and standardized cybersecurity practices. The obvious, most significant challenge was balancing the available budget from our funding envelopes between other organizational needs—for example, ageing buildings against needed technology improvements. This balancing act is becoming more prevalent as we are now at a stage within healthcare where organizations no longer have the choice to operate without technology and subsequently, this technology must be secured, managed, and maintained.
Compounding the issue on technology maintenance was increasing insurance expectations. Since 2021, insurers have faced increased claims for ransomware attacks (see examples below).
As illustrated, the risk for insurers has increased, and they have heightened their requirements for continuing care operators to obtain cybersecurity insurance. As of autumn 2021, what was acceptable in the past no longer meets these enhanced requirements. Before 2021, the Good Samaritan IT systems met the threshold on a number of the cybersecurity insurance requirements, but not all (Figures 1-4). Healthcare ransomware breaches increase over the years by region.
3
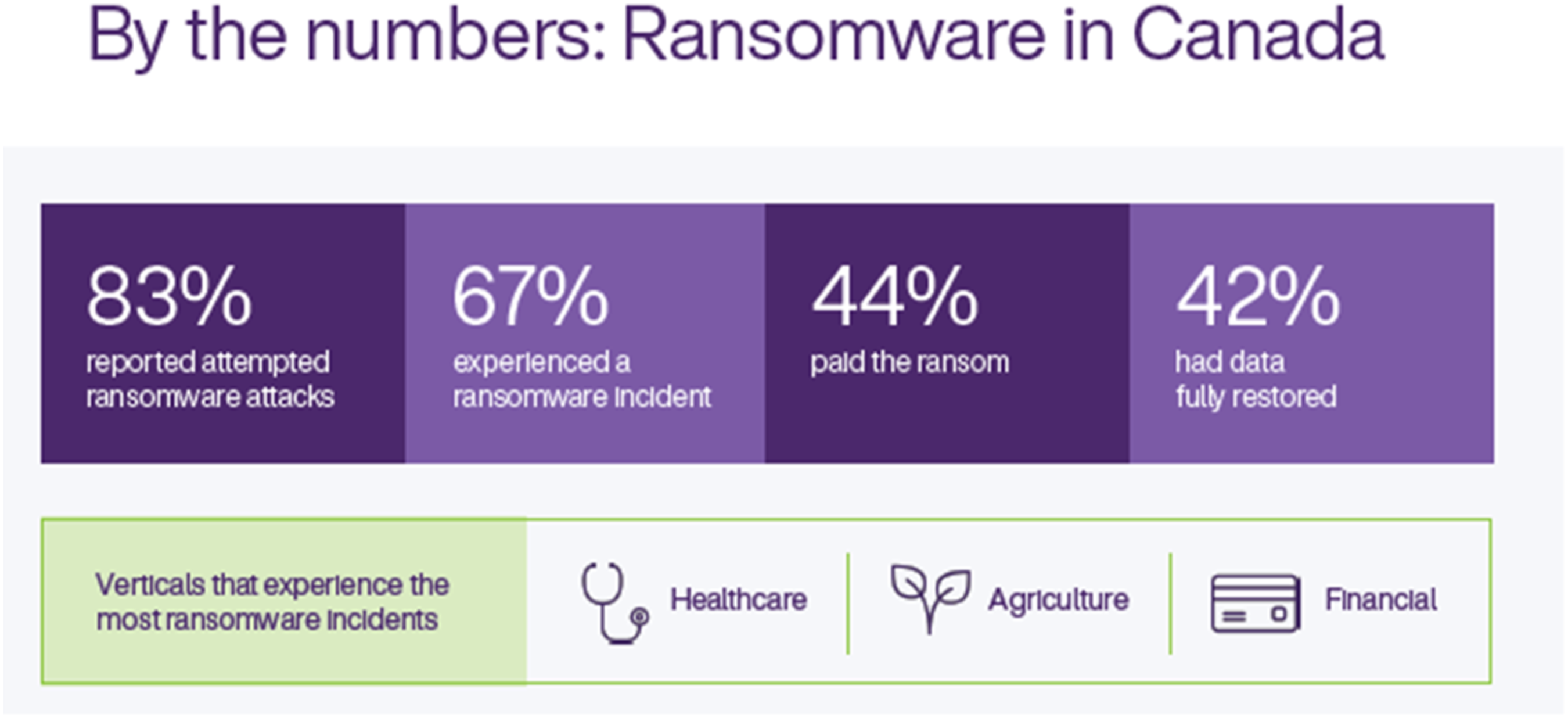
Ransomware attacks in Canada in 2021.
4
In Canada, healthcare is one of the industries that experience the most ransomware incidents. Average ransomware payments based on size of organization.
4
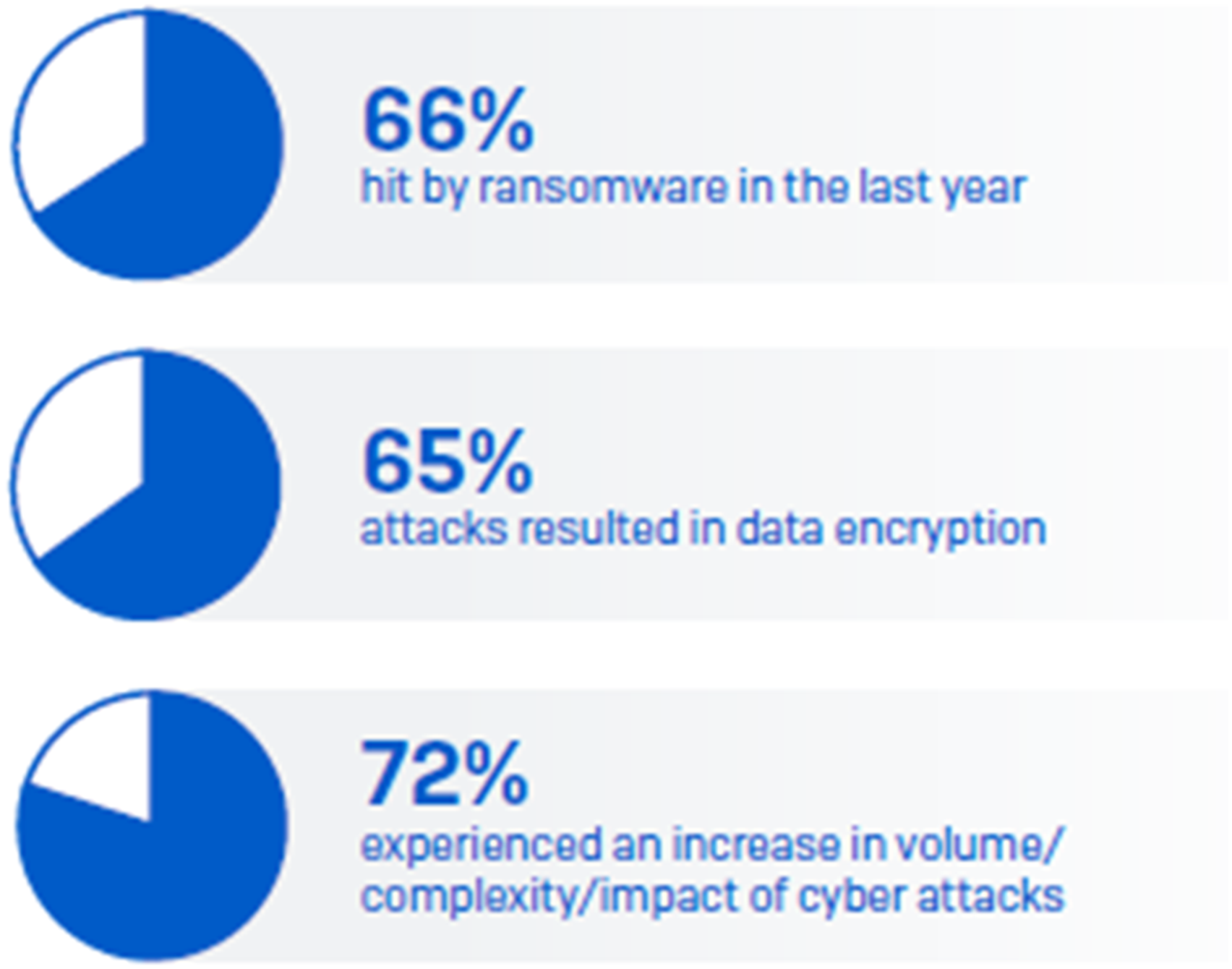
The average costs of a ransomware attack in Canada are approximately $140K, based on the size of the organization. Numbers of organizations experiencing ransomware attacks.
5
Based on surveys of 5,600 IT professionals from organizations in 31 countries. 66% of the organizations have experienced ransomware attacks in 2021. These numbers are continuing to increase.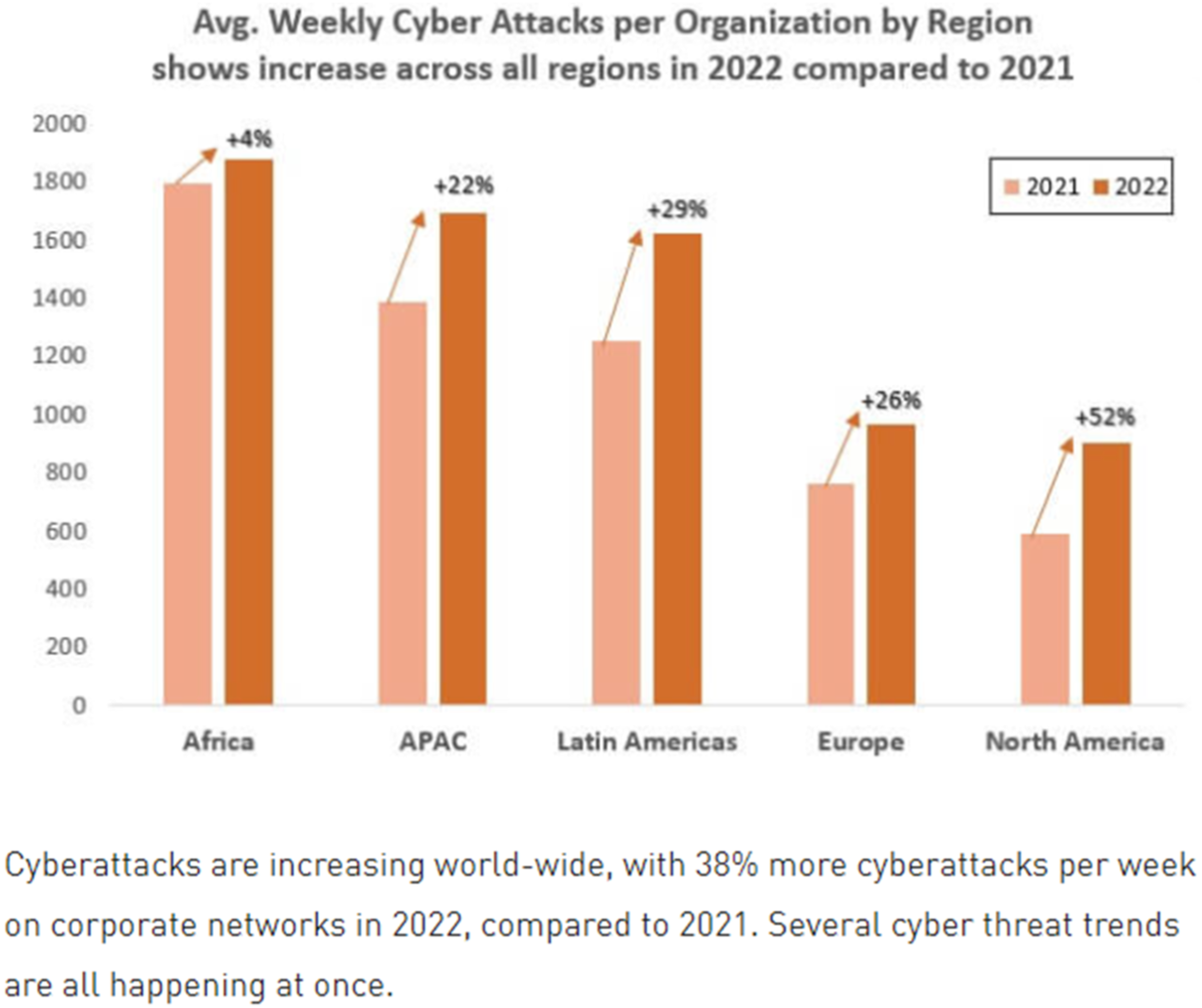

In the summer of 2022, the organization needed to retain its cybersecurity insurance.
Further aggravating the matter were the continuous cyberattacks on our organization. For example, in the spring of 2022, Good Samaritan experienced a nefarious attack on our digital phone systems at one of our care homes. Leveraging our digital lines, the attacker was making international calls. Due to the vigilance of our Good Samaritan IT support team, an emergency operations centre was quickly implemented to eliminate the threat, to analyze any other exposed risks, and finally to conduct a root cause analysis to determine the source of the attack.
Good Samaritan threats and attempts.
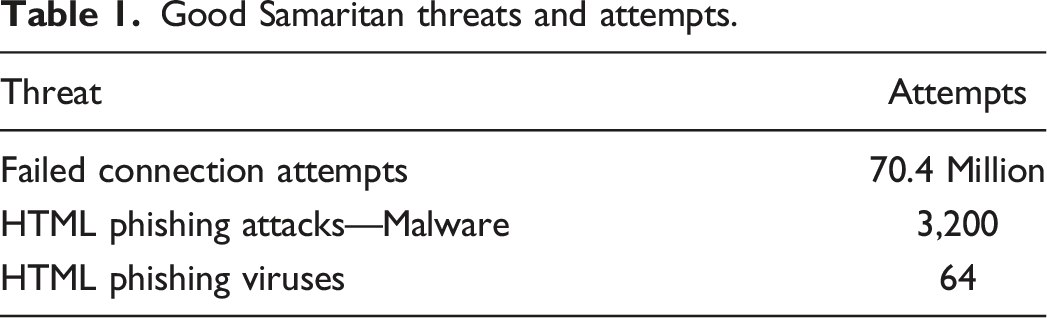
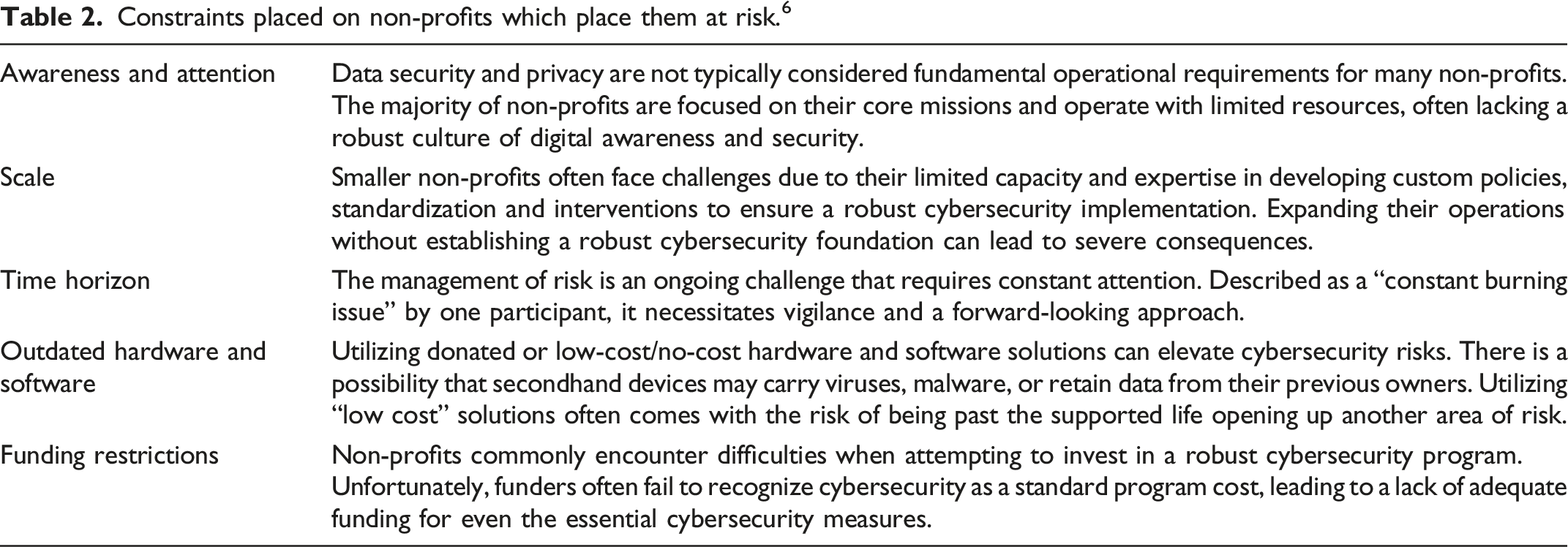
Constraints placed on non-profits which place them at risk 6 .
These continued threats coupled with the aforementioned insurance concerns have forced us to evaluate the risks of not enhancing our IT infrastructure and determining how to retain our cybersecurity.
In collaboration with our insurance broker and leveraging our existing digital roadmap, a plan was created to present to our executive leadership and board. Special consideration was taken to communicate and present a complicated IT plan to leaders who may need help understanding techno-jargon. After considering a series of analogies, the best comparison was to renovating a home. For example, a once shiny house may need upgrades after many years. These upgrades create better efficiencies—triple pane windows offer higher R-value. This analogy supported the conversation with executive leadership and our Board of Directors to help explain the past, present, and future states of our proposed plan.
This proposed plan included the costs that were necessary to fund this work. The simple fact is that cybersecurity upgrades and implementations cost money—big money. Whether in continuing care or other industries, the costs are the same, and the requirements continue to grow. As an example, external partner expectations continue to force continuing care operators into implementing technologies that are often unfunded. While there are obvious benefits to adopting technology, as highlighted in the Canadian Centre for Nonprofit Digital Resilience, funders rarely appreciate cybersecurity as a standard program cost, so non-profits lack funding for even the most basic security measures. Furthermore, non-profits routinely face constraints in their ability to adopt effective cybersecurity controls.
The issue of cybersecurity underfunding appears to be systemic in not-for-profit organizations. Bradley illustrated this through recent research, which highlights that 59% of large humanitarian organizations believed security practices we underfunded. 7 This is where the fundamental dichotomy comes in: How, without additional funding, do we keep up with these rising costs?
Good Samaritan embarked on a plan to work through capital dollars, grants, and reasonable negotiations with vendors to help support this work. This again brings us back to the “David vs. Goliath” metaphor. Continuing care operators need more dollars to fund growing IT requirements. The other factor that plays into this is the move from being able to capitalize IT “Infrastructure.” As we move into a subscription-based world for the “X as a Service” model, these requirements translate to operational expenses. For many organizations, this expense significantly impacts our budgets. We are not only dealing with enhanced requirements, but costs for these services are increasing, and there is also a considerable shift in how these costs are accounted for.
This is not just an information technology/cybersecurity issue, it is a finance issue
In autumn 2022, the Good Samaritan Board of Directors approved the execution of our plan in order to secure our insurance and enhance our technology infrastructure, allowing us to meet continuing care cybersecurity standards. The board's approval of the data centre refresh/cybersecurity plan forced us to reprioritize our strategies and subsequent budget to accommodate the emergent cybersecurity requirements.
However, there was recognition from all parties that not only will the plan protect our organization from hidden threats, but it will also improve internal efficiencies through upgraded technology. The upgrades are not gold-plating the infrastructure; they are focused on meeting requirements—not adding new fancy bells and whistles.
It cannot be understated that this pivot in strategic priorities comes at a cost. Like most continuing care operators, Good Samaritan must be funded to continuously meet the growing demands and subsequent costs of enhancing IT requirements. As a result, operators must be increasingly resourceful to seek any available provincial or federal grants to meet the increasing costs of IT.
Still, more is needed. For example, research in the United States has highlighted the increasing need for healthcare organizations to increase their IT budgets to meet the growing risks, and “it is anticipated that cybersecurity budgets will increase for most healthcare organizations.” 8 The cybersecurity threats to healthcare operators are not subsiding. Unfortunately, national examples continue to illustrate the emergency we are in, such as the recent attack on the Toronto’s Hospital for SickKids, where a ransomware gang played havoc by freely distributing a decryptor (transforms data that has been rendered unreadable back to readable form). While the gang later apologized for their actions, it highlights how vulnerable our sector has become. 9 As such, to meet these ever-increasing demands for the use of technology to enhance resident care and to improve efficiencies, provincial governments would benefit from working with facility-based care operators to arrange for proper increases in funding.
Takeaways
Through the Good Samaritan’s IT experience, continuing care operators can learn the following: • Always be on guard. While organizations may not feel threats at the moment, it does not mean we should not constantly evaluate our current infrastructure as an opportunity to prepare a plan before a threat becomes reality. When organizations get complacent with their IT infrastructure, the view becomes that they are safe, when in this evolving IT world, they are not. Complacency = vulnerability. • Leaders must familiarize themselves with their IT infrastructure and learn the risks and opportunities. With technology advancing so quickly, the average leader’s basic cybersecurity and IT understanding is often deficient and, therefore hidden; subsequently real threats can be missed. The adage “all businesses are IT businesses” extends to every modern-day business, including continuing care. • With the benefits of technology and the risk of ransomware attacks and other sophisticated cybersecurity attacks, proper oversight of IT by continuing care leaders and their organization's board has become essential. • Understanding the costs associated with some of the changes that need to be implemented opens up an opportunity for continuing care leaders and their organizations to partner with the government to gain better deals that continuing care providers can afford or implement. • It is prudent for organizations to develop a “reasonable” roadmap that aligns with industry cybersecurity standards. This should be done in conjunction with cybersecurity experts and then validated with insurers. This roadmap must also be flexible enough to adapt to the evolving nature of cybersecurity threats and industry standards. • Roadmap communication. While moving through an IT upgrade journey, organizations should be diligent to ensure timely and appropriate communication has occurred between all stakeholders involved. These open lines of communication assist the project in being more efficient, create effective collaboration, allow for enhanced problem-solving and client satisfaction, improve crisis management, and reduce the risk of misunderstandings.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Ethical approval
Institutional Review Board approval was not required.
