Abstract
This study undertakes a comprehensive analysis of the fiscal consequences of extreme cybersecurity incidents affecting publicly traded corporations in the 21st century. As cybersecurity breaches have become increasingly prevalent and financially burdensome, organisations are compelled to continuously reassess strategies and reallocate resources to safeguard their assets, maintain operational continuity, protect data and preserve client trust. Despite the pervasive nature of these threats, there remains a notable lack of academic research on the medium- to long-term economic effects of major cybersecurity incidents on the market capitalisation of affected firms. This article seeks to address this gap, offering a detailed analysis to help corporations forecast both the immediate and longer-term financial impacts of extreme yet plausible cyber events. Through an original and comprehensive analysis, this study elucidates the significant effect of extreme cybersecurity events on the market value of publicly traded corporations between 2000 and 2021. The research incorporates a series of event studies and statistical analysis to specifically scrutinise the medium- and long-term financial consequences of cyberattacks on these corporations. Our findings reveal that the immediate costs related to remediation and compensation in the wake of cyberattacks constitute merely a segment of the overall financial loss, which is better reflected in the diminution of market valuation. Furthermore, the results underscore an escalating intolerance in the market towards companies experiencing significant cybersecurity breaches, evidenced by progressively severe losses in market valuation. This trend not only amplifies the financial vulnerability of the affected companies to market forces and competitors but also signals a shifting paradigm in market perception and response to cybersecurity failures though, managed well, market positioning has been enhanced for the select few.
JEL Classification: D81
1. Introduction
In the 21st century, publicly traded companies have had to increasingly allocate their finite resources to safeguard their systems, networks and information from cyberattacks (Anderson and Moore, 2006; Parkin et al., 2023). The ever-evolving and relentlessness nature of such attacks has driven most large companies into a permanent state of uplift (Lin, 2015; Zegart, 2017). Despite significant long-term investments, the development of financial metrics to quantify cybersecurity expenditure remains limited, with precise measurement and quantification still largely an internal aspiration for most organisations (Falco et al., 2019). With no imminent technical or legislative solution on the horizon to halt cyberattacks, it is essential for academia and industry to persist in refining cyber risk assessment methods, which remain urgently needed to bolster organisations’ investment strategies.
At the core of current research, there is an intrinsic understanding that cybersecurity rarely achieves perfect solutions or completely prevents attacks. Nonetheless, these inherent limitations should not impede the pursuit of diverse strategies to enhance prevention, management and response efforts (Edgar and Manz, 2017). Building on existing research, this study seeks to expand our understanding of how extreme cybersecurity incidents influence the medium- and long-term market value of publicly traded firms. By examining these extended time horizons, we capture not only the immediate consequences of such attacks but also the evolution of public perception as reflected in the stocks’ market performance over time. This emphasis on medium- to long-term outcomes aligns with the primary interests of both corporate management and the majority of shareholders, who typically prioritise sustained stock performance rather than short-term fluctuations (Beyer et al., 2014; Porter, 1998).
Event studies have become a widely accepted means of assessing stock price responses to significant events (Binder, 1998; Campbell et al., 2003; Shevchenko et al., 2023). As an analytical approach, they measure the financial impact of a given event on a company’s market value by identifying abnormal returns (AR) in the periods preceding and following the event. By isolating AR, event studies determine whether a cyberattack imposes a statistically significant effect on a firm’s stock price. Due to the lack of a universally recognised attack severity benchmark, the present study adopts a (USD) $10 million threshold – based on mean financial costs documented in prior research (Cybersecurity and Infrastructure Security Agency, 2020; Edwards et al., 2016; NetDiligence, 2019; Ponemon Institute and IBM, 2022; Romanosky, 2016; Shevchenko et al., 2023) to identify extreme events. Under the assumption of stock market efficiency, this methodology offers a robust lens for examining both immediate and longer-term consequences of cyberattacks (MacKinlay, 1997). The resulting insights support firms and investors in strategic decision-making and may also prove relevant for governmental regulatory considerations, though advocating for regulatory policy interventions lies beyond the scope of this market-focused paper.
This study explicitly focuses on 1- and 2-year post-event windows to robustly capture and quantify the medium- to long-term economic impacts of cybersecurity incidents. Previous literature primarily examines immediate, short-term market reactions; thus, the selection of extended post-event horizons in this research fills a significant gap, allowing for the assessment of sustained market valuation effects that might not be visible immediately after the event. These longer horizons provide valuable insights into market recovery or persistent valuation impairment, critical for long-term strategic decision-making by investors and firms alike.
Pre-event return analysis was deliberately excluded from this study due to concerns about confounding factors such as unrelated firm-specific news, industry trends or broader macroeconomic conditions that could significantly distort baseline performance measurements. Including pre-event returns might introduce bias unrelated to cybersecurity incidents themselves, thus complicating clear causal attribution. Future research could beneficially explore pre-event windows to investigate potential early warning signals or market anticipation effects, further enriching understanding in this field.
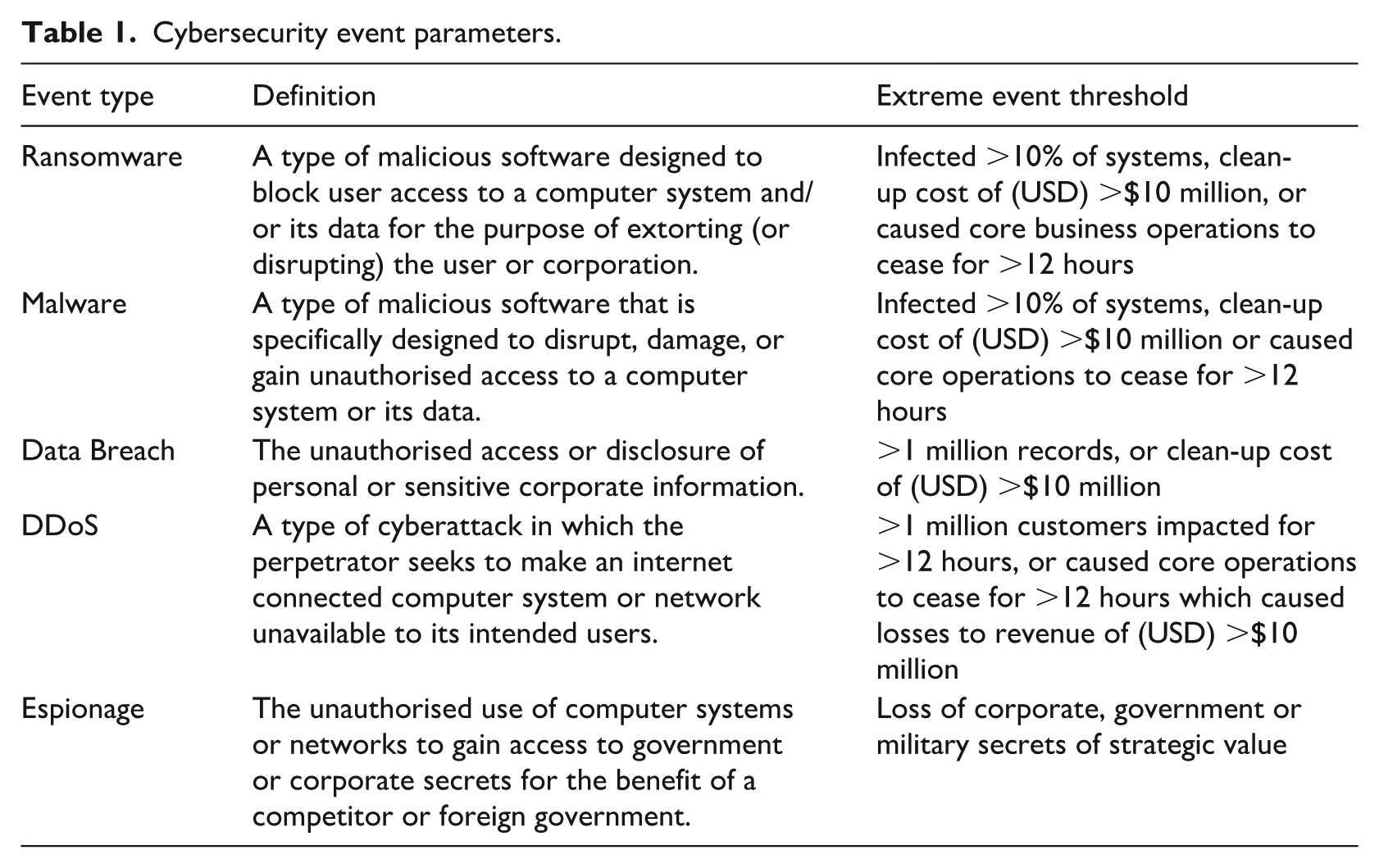
In this study, we use the terms ‘extreme cybersecurity event’ and ‘significant cybersecurity incident’ interchangeably to denote high-impact cyberattacks meeting stringent severity criteria. Specifically, an incident is classified as ‘extreme’ (and thus significant) if it exceeds threshold parameters such as incurring direct losses beyond USD $10 million or analogous scale metrics (e.g. more than one million records compromised, prolonged operational downtime). Table 1 delineates these criteria across different attack types, ensuring consistency in our terminology. This approach clearly differentiates severe incidents from low severity breaches and aligns our analysis with the study’s focus on cyber events of significant economic magnitude.
Cybersecurity event parameters.
1.1. Background and related work
In the cybersecurity domain, the enduring effects of cyberattacks on firms’ market valuations over medium- to long-term horizons remain insufficiently explored, resulting in a notably sparse body of conclusive research. Our extensive review of 21st-century security-related event studies, including those by Campbell et al. (2003), whose findings showed significant negative market reactions to information security breaches involving unauthorised access to confidential data. Acquisti et al. (2006) found the impacts of information security breaches are statistically significant and negative, albeit these effects as examined were transient in nature.
Dupont (2019) articulates a compelling argument regarding the escalating intricacy, frequency, and severity of cyberattacks, particularly those targeting financial sector institutions. He underscores their inevitability and the herculean challenge of safeguarding the integrity of critical computer systems in totality. Additional scholarly work posits that mandatory disclosure laws tend to adversely affect companies experiencing breaches, a scenario further exacerbated when such disclosures are amplified by media coverage (Gay, 2017). Recent empirical inquiries, characterised by more extensive sample sizes, further illuminated a notable concentration of losses: the most extreme 0.5% of losses cumulatively mirror the lower 99.5% (de Castro et al., 2020; Shevchenko et al., 2023). The observation of a significant concentration of losses in cyberattacks also validates the approach of distinguishing between low severity and extreme incidents in cybersecurity research. Elsewhere a burgeoning avenue for quantifying cyber risk has emerged from the cyber-insurance sector. Data from this domain indicated a significant increase in reported cyber incidents between 2008 and 2016 (Shevchenko et al., 2023). Moreover, a comprehensive thematic analysis of cyber insurance policies has revealed a striking divergence in the complexity and precision of formulas and metrics used for premium calculations (Romanosky et al., 2019). These observations support our conclusion that cyber risk quantification, though still in its infancy, is much needed.
Another emerging area of research explores translating cyberattacks into financial metrics to guide and prioritise cybersecurity investments. Notably, the Factor Analysis of Information Risk (FAIR) framework pioneered a model for understanding, analysing, and quantifying both cyber and operational risk in financial terms (Freund and Jones, 2015). Building on FAIR, the Secure Cyber Risk Aggregation and Measurement (SCRAM) methodology extends these concepts, linking problematic cyber risk control areas to those requiring additional investment, as indicated by primary order loss data (de Castro et al., 2020). Our findings aim to complement these existing approaches by enabling corporations to forecast both the immediate and medium- to long-term impacts of extreme yet plausible cyber events.
One additional dimension that demands attention in the scholarly discourse on cyberattacks is the burgeoning global phenomenon of ransomware. Most empirical studies examining the market impact of cyberattacks and security breaches predominantly rely on data gathered before 2017 (Campbell et al., 2003; Cavusoglu et al., 2004; Edwards et al., 2016; Gordon et al., 2003; Romanosky, 2016), preceding the widespread upsurge of ransomware. Our literature review reveals a marked shift in adversarial tactics with the advent of ransomware, contrasting earlier periods when many attackers avoided targeting technologically advanced entities (Ryan, 2021; Wolff, 2018). Given the ascendance of ransomware to become a prodigious cyber threat in recent years (Albrecht, 2017; Coburn et al., 2018; Greenberg, 2018; Ryan, 2021), excluding post-2017 ransomware data could introduce a significant gap in understanding the economic consequences of cyberattacks – a gap this article endeavours to address.
1.2. Hypothesis development
Existing research has primarily focused on the short-term stock market implications of severe cybersecurity breaches, often overlooking the medium- to long-term effects – particularly in the context of emerging threats such as ransomware (Campbell et al., 2003; Rosati et al., 2017; Shevchenko et al., 2023; Spanos and Angelis, 2016). To address this gap, we conducted an event study and developed a series of hypotheses to assess how these extreme cybersecurity incidents shape firm market valuations. Our principal aim is to discern the magnitude of the impact, the nature of the incident, and the influence of time on the event. By adapting Fama’s (Bradley et al., 2016; Fama, 1970; Ţiţan, 2015) economic concept of efficient markets for cyberattack scenarios, we propose the following:
These hypotheses test the assumption that publicly traded companies face substantial short-term declines in market valuation following an extreme cyberattack. Given the pronounced increase in cyberattacks since 2015, we also expect a modest reduction in impact severity over that timeframe. To examine this,
1.3. Cybersecurity event study parameters
Event studies, recognised as a standard methodology for measuring stock price reactions to significant occurrences (Binder, 1998), are crucial in both economic and cyber research. These studies assess the financial impact of specific events on stock values by comparing actual returns against expected returns, thereby determining the event’s significant effect on stock prices. This method aligns with the assumed rationality and efficiency of stock markets, and is particularly relevant when considering the immediate reflection of significant events in a company’s stock price (MacKinlay, 1997). Publicly traded companies’ analysis also benefits from implicitly assumed homogeneity, such as the need for transparency, regulatory compliance and exposure to financial markets. This allows the research to focus on financial outcomes which are largely independent of a firm’s industry, size or location.
Our research concentrates on the financial repercussions extreme cybersecurity events have on the market valuations of large publicly traded companies. Given the lack of universally accepted thresholds for distinguishing between extreme- and low-severity cyberattacks, we refer to recent studies that place the mean financial cost between (USD) $71,000 and $1.9 million (Cybersecurity and Infrastructure Security Agency, 2020; Edwards et al., 2016; NetDiligence, 2019; Ponemon Institute and IBM, 2022; Romanosky, 2016; Shevchenko et al., 2023), with $19.9 million considered to be an outlier (Biener et al., 2015). We have set a baseline of $10 million for our sample sets, using financial cost as a secondary criterion for defining extreme events (Ponemon Institute and IBM, 2022).
Extreme cybersecurity events in our study are classified with specific thresholds: ransomware, malware, data breaches, Distributed Denial of Service (DDoS) attacks and espionage, each with defined parameters for being considered extreme events: see Table 1. These parameters include system infection rates, clean-up costs, operational disruptions and data breach scales.
To satisfy these thresholds, we employed a data triangulation method drawing on primary sources such as press releases, annual reports and securities exchange filings, which were supplemented by social media and news outlets. This process allows us to filter out events unlikely to affect market outcomes materially, thereby focusing on significant cybersecurity incidents. While this approach eliminates the potential inclusion of millions of small cyberattacks (because they are unreported or not newsworthy), it is not practically possible to measure the market’s response to unreported events. Indeed, a study of correlation between undisclosed cyber breaches and market behaviour would more closely align with insider trading research, where decisions hinge on non-public information.
2. Research methodology overview
Our study focuses on extreme cybersecurity events affecting publicly listed corporations between 2000 and 2021, which is more than two decades of experience. The initial identification of these events was through social media, newspapers and academic journals, which were later validated by official sources such as press releases and annual reports. This process culminated in a comprehensive dataset to be analysed through event study methodology (Figure 1), observing market data at quarterly intervals for 1 year prior (−12 months) and up to 2 years (12, 24 months) post-event.
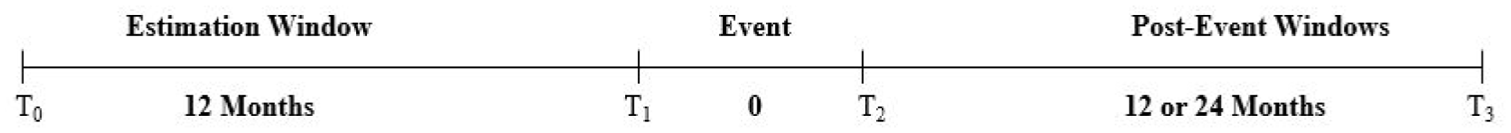
Event study methodology.
2.1. Event study denotations and methodology
The study encompasses various cybersecurity events with specified thresholds. Data triangulation methods were employed, involving press releases, company reports and securities exchange records, augmented by social media and newspaper reporting. The aim was to focus on prominent cybersecurity events and exclude non-market moving incidents. While event studies can vary in duration, a 1-year estimation and post-event window were first selected to enable the establishment of a robust baseline for each organisation’s operational and financial condition. Consideration was also given for methods which could be used to improve the accuracy of a long-run test for determining AR (Lyon et al., 1999; Tillet, 2018). The selection of a 1-year observation duration is consistent with cybersecurity and multidisciplinary economic event studies (Acquisti et al., 2006; Frank and Goyal, 2009; Goel and Shawky, 2009; MacKinlay, 1997; Ruan, 2017) and annualised cybersecurity research by both professional services and agencies (Australian Cyber Security Centre, 2012; Cybersecurity and Infrastructure Security Agency, 2022; Malwarebytes and Osterman Research, 2017; Verizon, 2022).
The preponderance of the events documented in this study was primarily observed in US-based corporations, followed by those in the European Union (EU) and Australia. This distribution aligns with findings from existing research (de Castro et al., 2020; Shevchenko et al., 2023), with the notion being that companies based in these regions remain high value targets for cyber attackers. This trend also correlates with the geographical locations of major stock exchanges, but it could also be indicative of the more stringent cyber breach disclosure policies enforced by market regulators in these jurisdictions.
2.2. Scope and exclusions
In the context of the corporations encompassed within our study, matters relating to WannaCry and to Chegg Inc required special treatment in the data used for the analysis. For WannaCry, it is noteworthy that, despite the WannaCry ransomware attack’s notoriety as one of the most extensive cyberattacks in recorded business history, the analysis incorporated only two of its victims. This selective inclusion was necessitated by the atypical resolution of the WannaCry crisis, largely attributed to the interventions of Marcus Hutchins, a reformed cybercriminal (Greenberg, 2020). Such swift remediation of the WannaCry attack left numerous aspects unexplored. This decision was further influenced by the extensive number of corporations initially compromised by WannaCry, which posed a risk of disproportionately biasing and distorting the findings of our research.
Consideration was given to including pre-event returns in the analysis of cyberattacks’ impact on stock performance. However, as the primary objective of this study is to isolate the causal effect of disclosed cyber incidents on market valuations, the use of returns prior to the event for inference was intentionally excluded. While the 12-month pre-event window (–12, –1) is incorporated into the model to estimate expected returns under normal conditions, it is not used to draw conclusions about the causes of the cyberattack or to detect trading abnormalities. Including such pre-event data in the analytical window could introduce confounding influences unrelated to the incident itself, such as macroeconomic shifts, sectoral volatility or firm-specific developments, thereby diluting the attribution of observed AR to the cybersecurity breach. Although pre-attack trading patterns may hold relevance in identifying early warning signals or information leakage, such dynamics fall outside the scope of this event study framework. This study’s design focuses instead on the post-disclosure valuation effects that follow public disclosure, consistent with established methodologies in financial economics.
In addition, the education technology company Chegg Inc., which suffered from a significant cybersecurity breach affecting more than 40 million users was also excluded from the dataset, as the initial disclosure to the event (Chegg, 2018) was considered to be inaccurate. In late 2022, these inaccuracies led to the Federal Trade Commission (FTC) launching legal action against the corporation. Due to the duration between the breach and accurate disclosure, omission of key facts in market reporting, and the volume of cybersecurity incidents incurred by Chegg between 2018 and 2020, Chegg was excluded from the research dataset.
2.3. Ordinary least squares
Our study employed market valuation to assess the economic impact of extreme cybersecurity events, capturing both direct and indirect costs to corporations. We utilised the ordinary least squares (OLS) method within the framework of the Capital Asset Pricing Model (CAPM) to estimate a firm’s market value sans the cybersecurity event. This involved thereby computing AR by comparing actual stock returns against those predicted by the model. This approach includes measuring AR against a dynamic baseline (S&P500), considering both direct and indirect costs of cyber events. We chose the S&P500 index as a proxy for market returns Rmt, and to reflect our global company dataset.
2.4. Methodological framework
The study initiated with the collation of opening price data for a multitude of corporations (samples) and the S&P500 (benchmark) across nine financial quarters, ensuring the cybersecurity event transpired in the fifth quarter for each entity. Opening price data was selected over the close data, as this is useful in capturing the immediate market reaction to overnight news, including announcements or events that occur outside regular trading hours.
The methodology operated wherein data from the initial four quarters were instrumental in calculating the expected annual return for the corporation and the benchmark, using equation (1). Here, i is the sample, that is, an identifier for the corporation, t is time in quarters, R is the actual stock return, and

Our analysis spanned a period covering 1 year prior to and up to 2 years following the cybersecurity event, allowing for a comprehensive assessment of both immediate and longer-term economic impacts. To encapsulate the overall effect, we computed the cumulative abnormal returns (CARs) across the event window, and the mean announcement impact, under the hypothesis of no market reaction to an extreme cybersecurity event announcement. These calculations aimed to quantify the deviation in market valuation attributable to cybersecurity incidents, emphasising the focus on sustained rather than transient market impacts.
2.5. Model validation
In our empirical analysis, polynomial regression and z-statistics were employed to validate the model. The choice of polynomial regression, over the more traditional linear regression, was dictated by its superior ability to capture a broader range of functional relationships between the independent variable (market shocks) and the dependent variable (S&P500 index). This method was instrumental in visualising the correlation and establishing the predictive model. Emphasis was placed on the goodness of fit for key variables, prioritising this over a more intricate explanatory relationship with additional control variables. Our focus remained on the divergence between actual outcomes and predictions in the context of cyberattacks, rather than a comprehensive elucidation of stock price movements.
Figure 2 presents the results of the polynomial regression analysis, illustrating the temporal effects of cyber events on stock prices. Here, SE stands for standard error; SD, stands for standard deviation; and R2 is the coefficient of determination. The findings indicate heightened volatility in more recent cyber events, potentially influenced by the rapid appreciation of FAANG stocks (Facebook, Apple, Amazon, Netflix, Google). At the time of the model’s construction, these firms constituted a significant portion of the S&P 500, potentially amplifying the overall market sensitivity to cyber incidents. As their market capitalisations expanded, fluctuations in their share prices likely exerted a disproportionate impact on index-wide volatility, reinforcing their role as a key driver of market responses to cybersecurity threats.
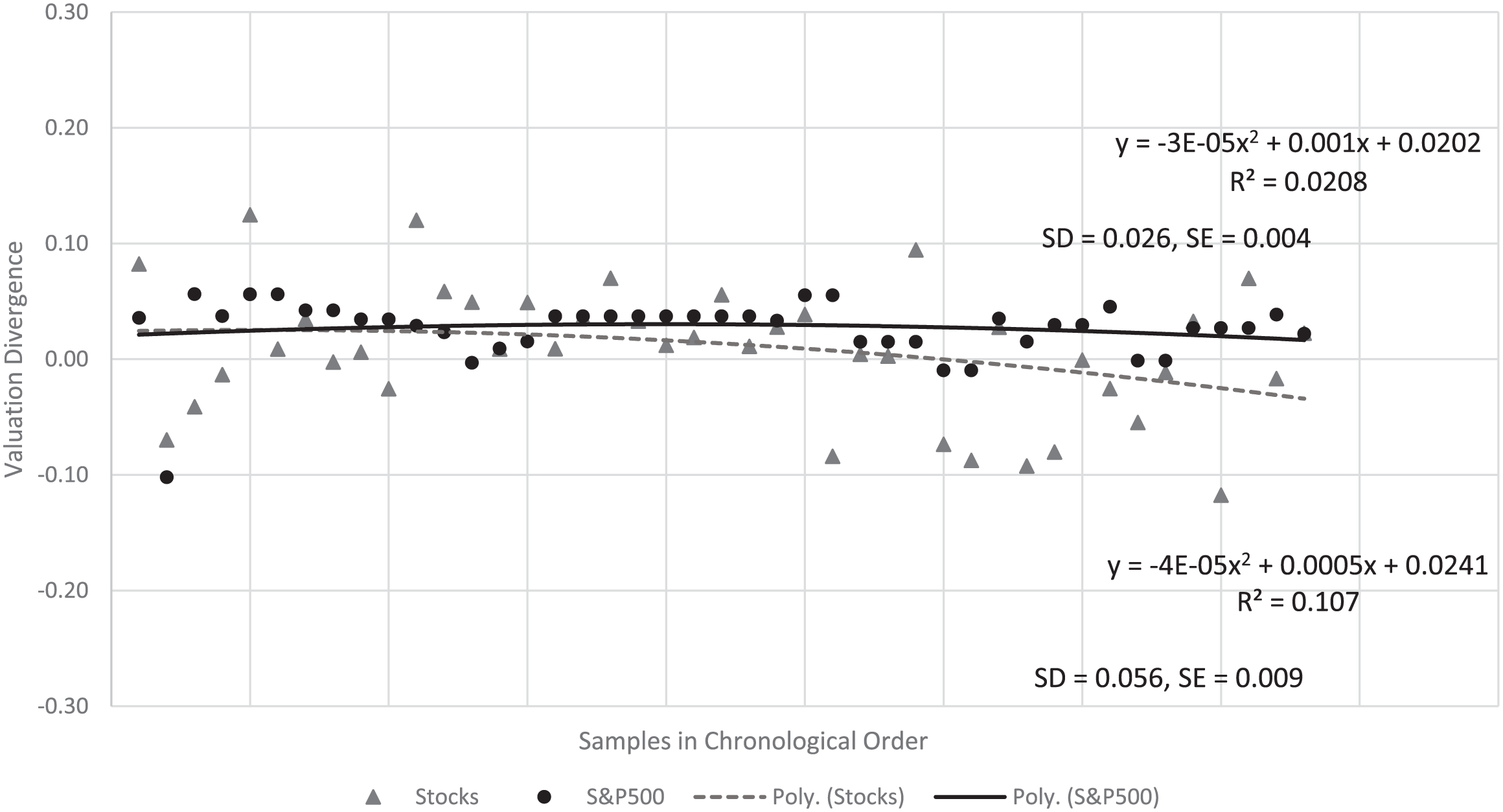
Polynomial regression.
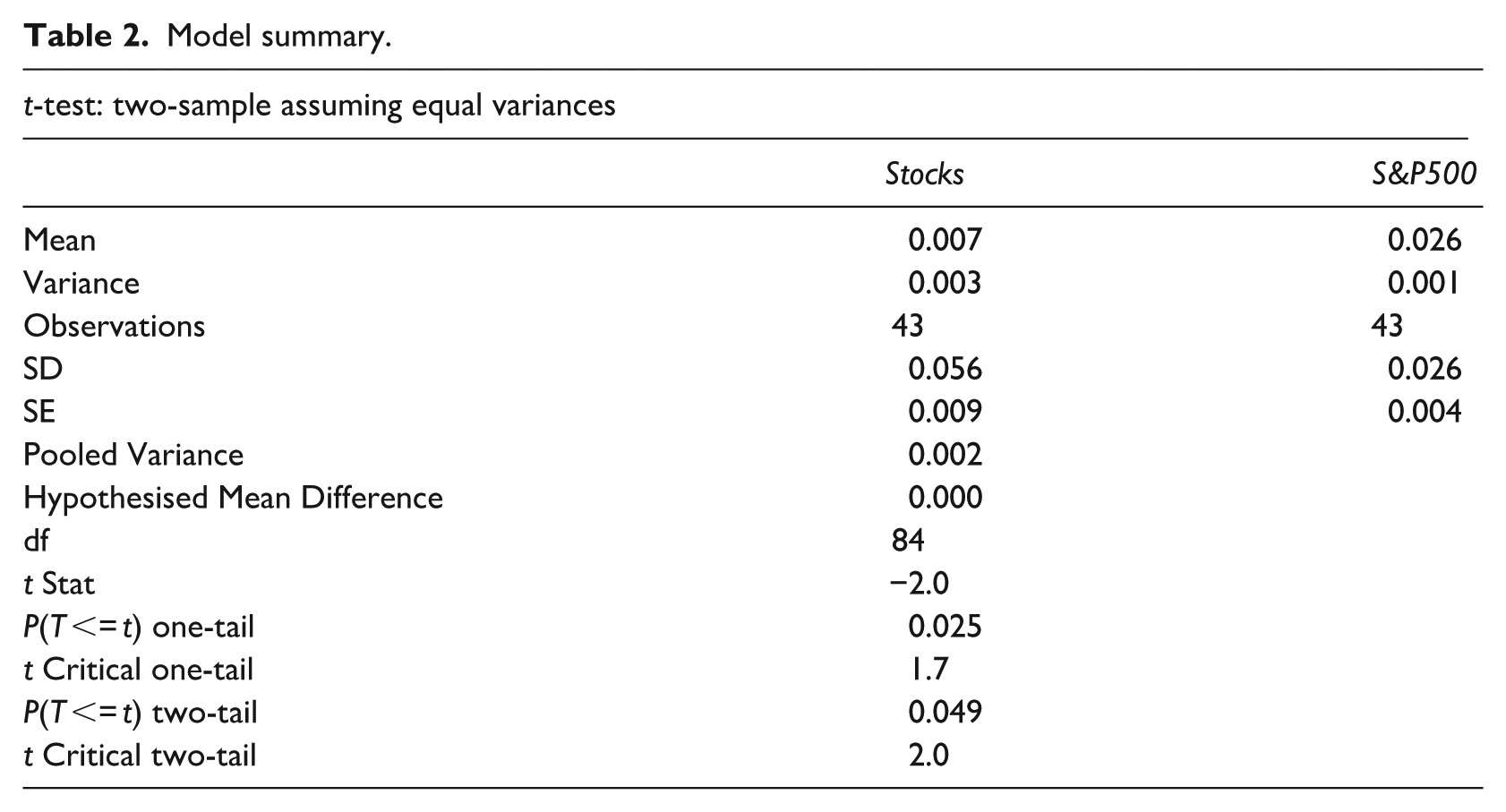
In assessing the relationship between specific stocks and the S&P500, a two-sample t-test (Table 2) was conducted, revealing a t-statistic of −2.0 and a two-tailed p-value of 0.049. This marginally indicates a significant difference at the 5% significance level. The analysis was adjusted for the 1- and 2-year AR, excluding outliers from the dataset.
Model summary.
Our evaluation of hypotheses (
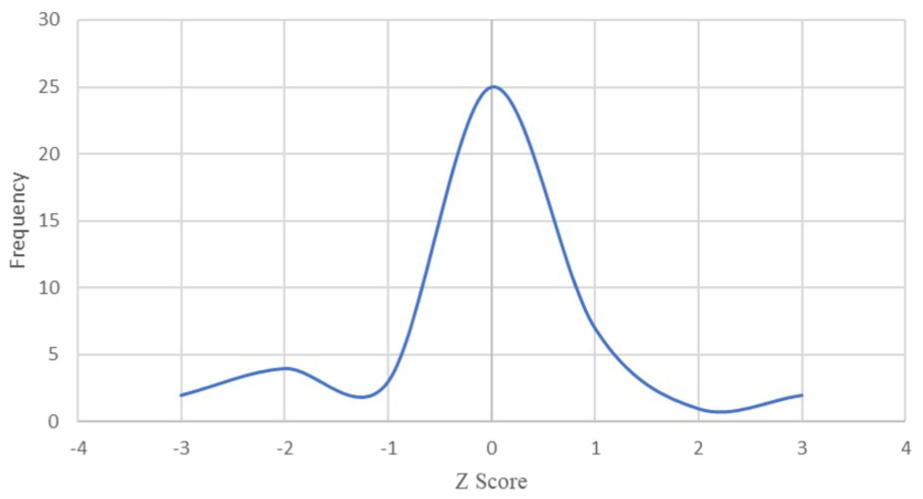
Z-score predictive model.
Finally, skewness was measured to assess the asymmetry in the data’s distribution, yielding insights into the tail’s skewness value. This comprehensive statistical approach allowed for a nuanced understanding of the market impacts of cyber events, particularly in relation to the performance of individual stocks against broader market indices.
3. Analysis and results
This comprehensive analysis offers significant insight into the financial repercussions of cybersecurity breaches on publicly traded companies. Spanning a detailed investigation over both 1- and 2-year intervals post the cybersecurity event; this research clearly reveals the lingering impacts of such incidents on market valuations.
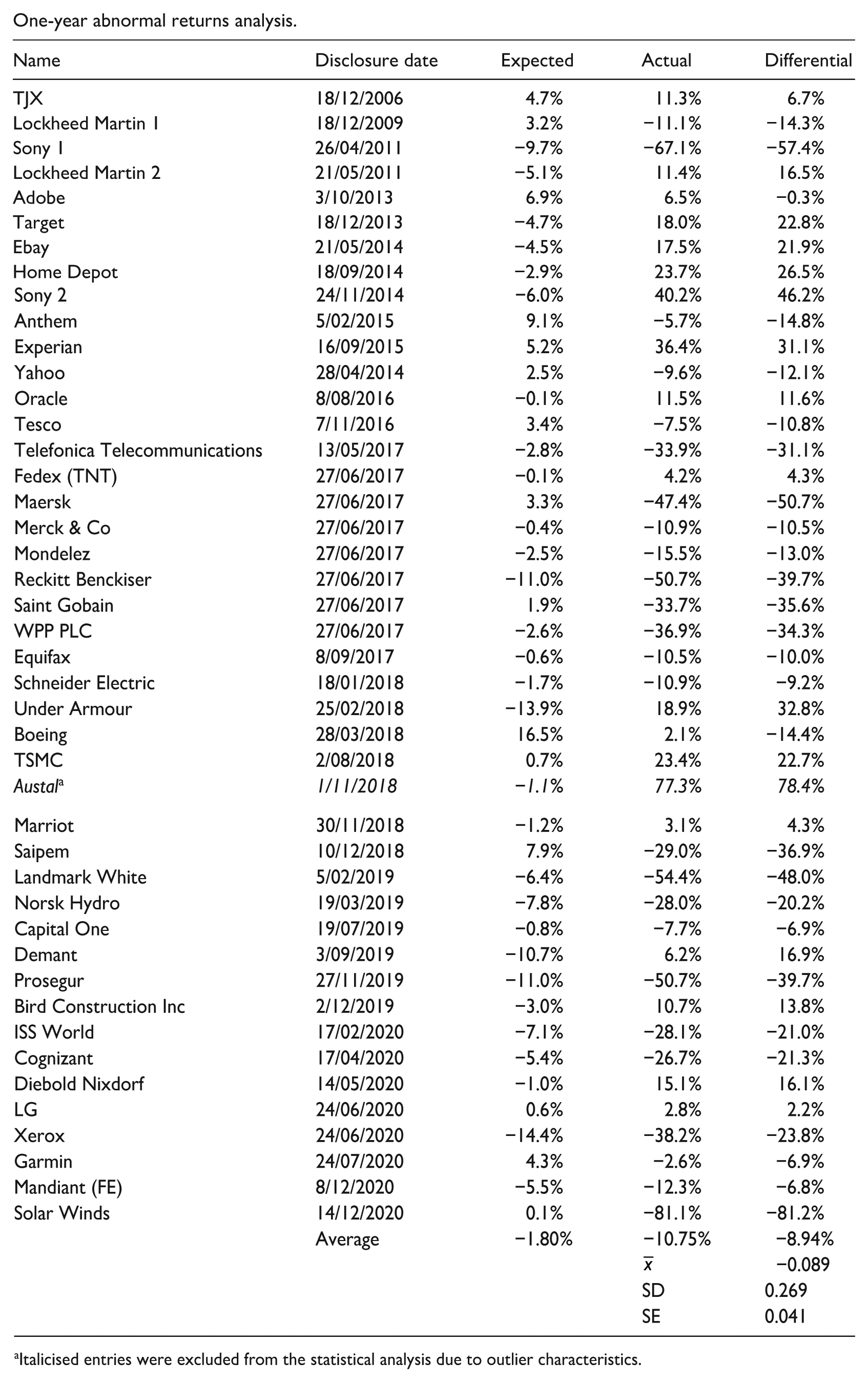
3.1. One-year cumulative AR analysis and results
Our
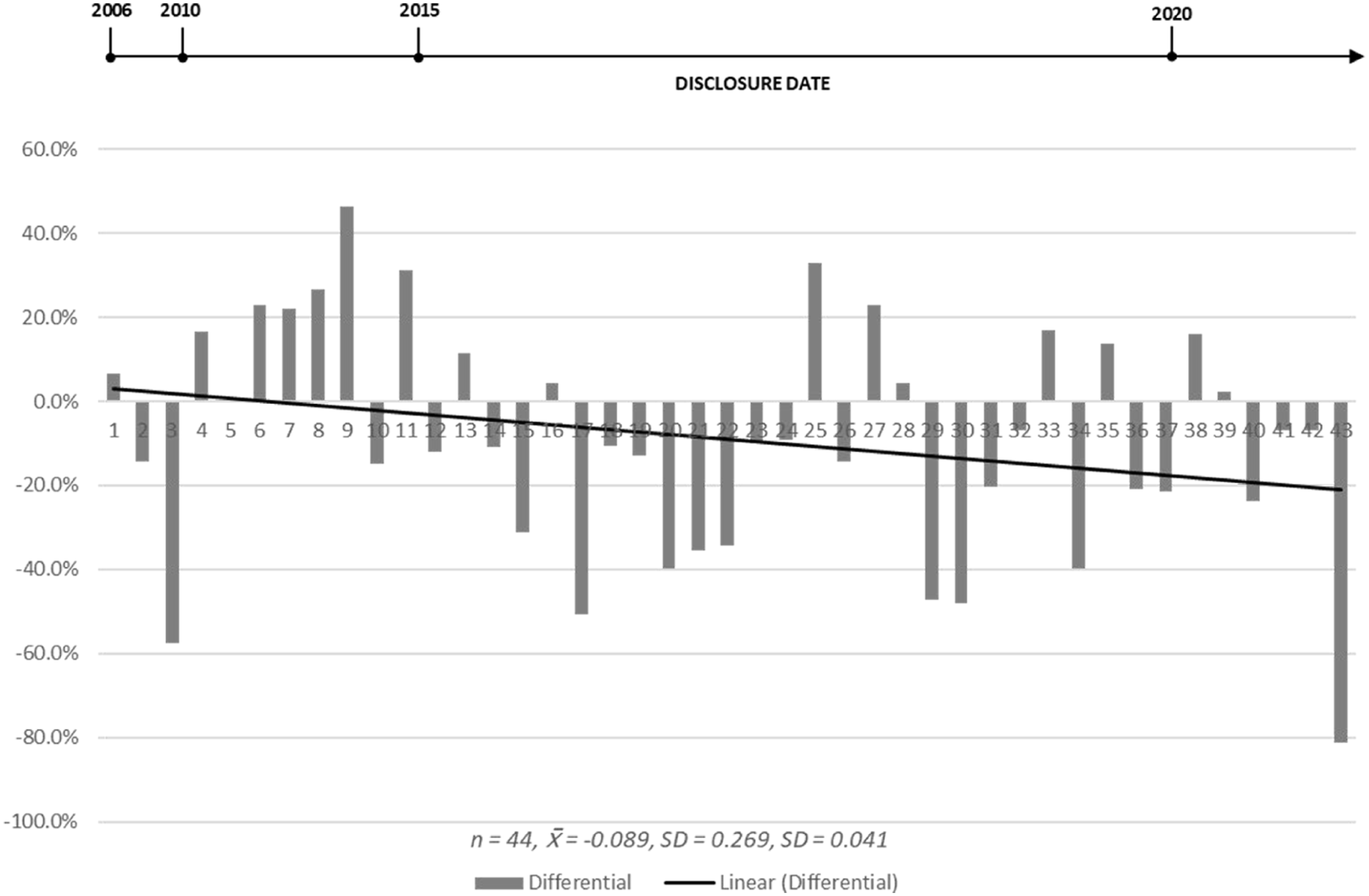
One-year analysis results.
Analysis of the results in Figure 4 also indicated two clear outliers in the dataset at sample 28 (Austal) and sample 44 (SolarWinds). Further investigations of each were undertaken to validate these results and assess inclusion/exclusion of the cases in the sample for best estimates.
The review undertaken revealed that Austal, who is a defence contractor, had incurred an extreme cyber event that resulted in the theft of sensitive defence information and an extortion attempt. While this type of event is consistent with the other samples, it does not explain the dramatic rise of its market valuation. A further examination of Austal’s financial disclosures, supplemented by an array of press releases and media publications during the relevant timeframe, unearthed a notable escalation in the firm’s market valuation. This surge was ostensibly linked to alterations in the geopolitical landscape, specifically, the US Navy amplified its initial contract with Austal, mandated to construct six Littoral combat ships in 2014, escalating the order to a total of 17 ships by the year 2019 (Tillet, 2018).
While Austal’s commercial operations as a naval ship manufacturer typically encompass securing new contracts, the magnitude and abruptness of this contract expansion were deemed extraordinary. Such a substantial alteration in contract volume, without precedent in Austal’s operational history, was classified as an outlier event. Consequently, in the pursuit of analytical rigour and accuracy, Austal was extricated from the dataset under scrutiny. This decision was grounded in the principle of maintaining the integrity of the data by excluding anomalous variables that could potentially skew the overall analysis.
The case of SolarWinds emerges as a particularly distinct and instructive instance within the broader context of cybersecurity breaches. As a prominent software vendor, SolarWinds was the target of a sophisticated intrusion orchestrated by a foreign intelligence service. This breach transcended the mere compromise of SolarWinds’ own security apparatus; it extended to facilitating subsequent attacks on the clientele of SolarWinds, epitomising what is widely recognised in cybersecurity parlance as a ‘supply-chain’ attack. Notably, this incident diverges markedly from the general pattern observed in other cybersecurity events under study. Whereas most, if not all other such incidents predominantly resulted in limited, direct disruptions to the affected entities’ own operations, the SolarWinds event had far-reaching implications which impacted a broad spectrum of their downstream clients. However, despite the unique attributes of this case, a thorough examination did not reveal any other divergent factors that could be definitively linked to the pronounced decline in SolarWinds’ market valuation after the breach. As such, in the absence of additional extraneous variables that could materially distort the analysis, it was deemed appropriate to retain SolarWinds within the dataset. This decision aligns with the overarching methodological commitment to ensuring the robustness and representativeness of the study’s empirical findings.
As detailed in Table 3, the removal of Austal from the dataset amends the average result to now indicate an almost negative 9% return over the period versus the expected result, which is of significance and supports
One-year adjusted results.
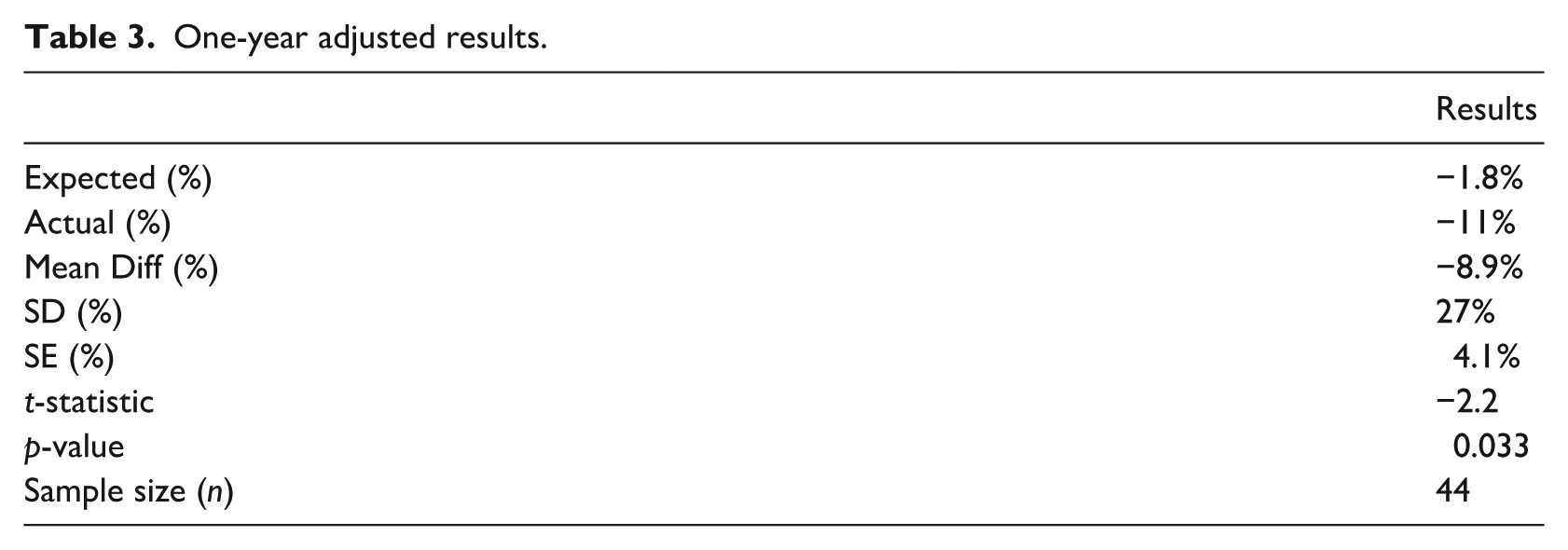
A one-sample t-test was conducted to evaluate whether the average differential between expected and actual returns was statistically significant. As detailed in Table 3, the mean differential was –8.9% (SD = 27%, SE = 4.1%), and the difference was statistically significant (t(43) = −2.2, p = 0.033). This indicates that, on average, firms experienced a substantial and significant decline in market value relative to expected performance in the year following a cyber incident.
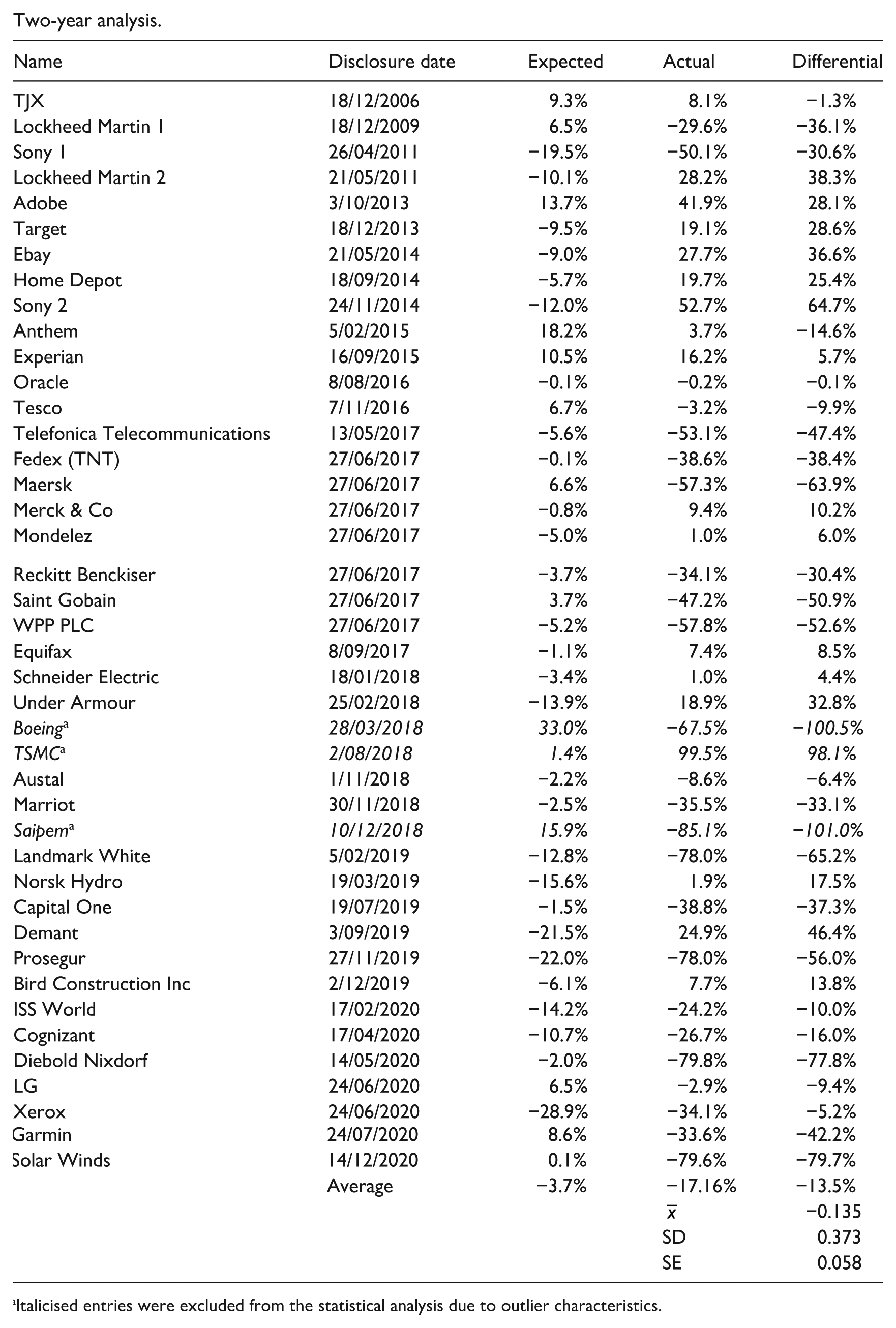
3.2. Two-year cumulative AR analysis and results
Extending the analysis over a 2-year horizon post-cybersecurity incident, as detailed in Figure 5 and at an individual firm level in Appendix 2, reveals a more pronounced underperformance of 12%. This extended analysis corroborated
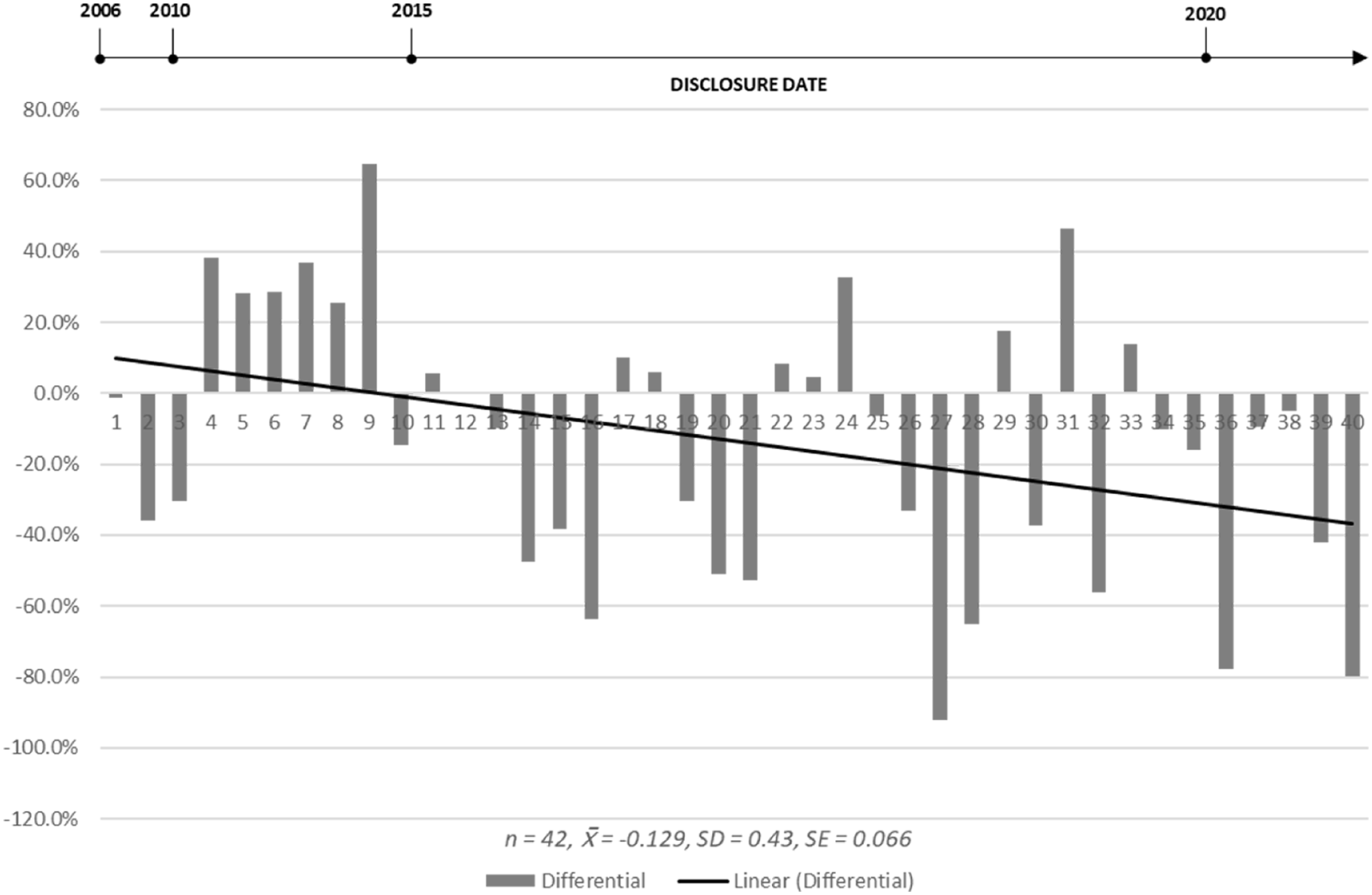
Two-year analysis results.
Upon re-evaluation of the dataset pertaining to the 2-year cumulative AR, it became evident that three entities, samples 25 (Boeing), 26 (Taiwan Semi-Conductor (TSMC)) and 29 (Saipem), markedly deviated from the established pattern, thereby meriting classification as result outliers. A further analysis then conducted during the post-cybersecurity event timeframe revealed nuanced dynamics influencing the market valuations of Boeing and TSMC, transcending the direct impact of the cybersecurity incidents themselves. Initially, these firms were included in the dataset due to their status as victims of subsequent iterations of the WannaCry ransomware attack, a phenomenon occurring over a year following the primary wave of attacks. This inclusion was premised on the rationale that these incidents, were easily preventable through effective vulnerability management, thus they constituted valid cases for inclusion in the study.
However, further examination reveals that those external factors held substantially more sway over their market valuations. Specifically, Boeing’s market valuation experienced a precipitous decline following a series of aviation disasters, which tragically resulted in significant loss of life and exposed critical shortcomings in the company’s governance and safety protocols (Whiteman, 2020). Conversely, TSMC witnessed a diametrically opposed trajectory, benefitting from a surge in semiconductor prices occasioned by the COVID-19 pandemic-induced global shortages (Vakil and Linton, 2021). As the pre-eminent manufacturer in the semiconductor arena, TSMC’s financial performance during this period was predominantly shaped by these market dynamics, rather than the cybersecurity breach per se.
In contrast, Saipem’s situation presented a different scenario. The company’s sustained decline in share price was initially exacerbated by plummeting oil prices at the onset of the COVID-19 pandemic. However, this trend was subsequently mitigated in the 12th quarter by an extensive share-buyback programme, which resulted in a 43.7% uplift in Saipem’s share price. These fluctuations, deemed within the realm of normal market operations, warranted the retention of Saipem in the dataset.
The resulting adjustments to the dataset, particularly the exclusion of Boeing and TSMC due to identifiable exogenous valuation drivers, necessitated a revision of the 2-year CAR estimate. The updated analysis yielded a statistically significant mean differential of –14% (t = −2.3, p = 0.026), indicating a robust and persistent negative market response to extreme cybersecurity events over a 24-month horizon. The fitted trendline in Figure 5 illustrates the sustained deterioration in firm value over the 2-year horizon, further strengthening support for
3.3. Conclusive insights and discussion
A comparative review of
Although extending the post-event analysis beyond 2 years was initially contemplated, it proved unsuitable for this study. Over longer periods, the specific effects of the event may become confounded by broader market dynamics or firm-specific developments. As MacKinlay (1997) notes, macroeconomic shifts, new product launches or governance alterations can significantly influence stock prices, rendering it more difficult to isolate the event’s last impact. Such dilution could also yield misleading conclusions regarding the event’s true market repercussions.
By examining a broad spectrum of cybersecurity incidents spanning two decades under diverse market conditions, this study minimises confounding variables that might otherwise skew results within a single sample or timeframe. The findings indicate that certain firms navigated these events so effectively that they experienced subsequent market gains, although these typically lagged expected or overall market performance. Furthermore, the impact of such cybersecurity incidents extends beyond immediate fiscal losses, encompassing long-term opportunity costs, reputational damage, elevated operating expenses and the diversion of critical resources.
3.4. Market-adjusted returns analysis and results
In the pursuit of a more nuanced understanding of the financial implications of cybersecurity events, this study incorporated a further market-adjusted returns analysis. This methodology, as a complement to the primary findings, affords an additional layer of insight into the relative performance of corporations vis-à-vis the S&P500 in the aftermath of such events. Brown and Warner advocate for this approach, positing that it obviates the need for performance estimation by assuming a uniform rate of return across all stocks (Brown and Warner, 1980). The analysis juxtaposes the corporation’s performance over the preceding 6 months against that of the S&P500 for the same interval, with Table 4 providing an illustrative example.
Market-adjusted return example.
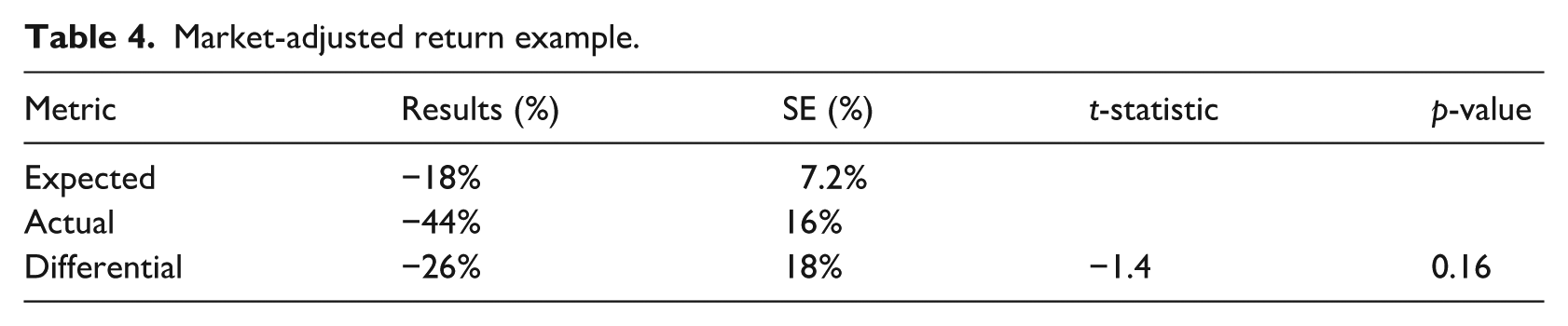
The comprehensive 2-year market-adjusted results, presented in Table 5, reveal a clear pattern in the financial trajectory of firms after an extreme cybersecurity incident. The standard error of the mean (SE = 5.8%) reflects the precision of the sample mean (−18%) as an estimate of the population mean. Although this standard error is moderate, it highlights the consistency of the observed decline across the sample. On average, companies experienced a significant depreciation in market value, most pronounced in the first 6 months post-event. Although the rate of decline appears to start moderating after the first year, many firms still had not returned to pre-incident performance levels by the 2-year mark – underscoring a more protracted recovery than initially anticipated.
Two-year market-adjusted results.
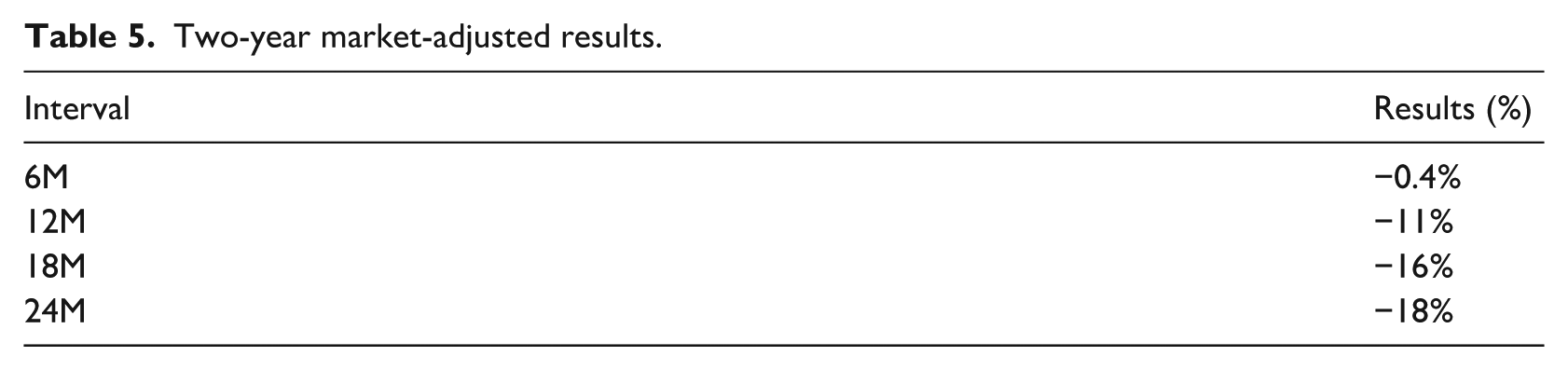
These findings underscore the persistent adverse influence of cybersecurity breaches on corporate outcomes. Even at the 2-year juncture, the data show that the average company remains significantly under market performance. By the close of the observation period, market returns among the affected firms are about 18% lower than those of comparable market counterparts – a substantial gap that illustrates a lengthy timeframe before shareholders can expect meaningful returns. This evidence suggests that both companies and investors face a protracted path to organisational recovery and market repositioning following significant cybersecurity breaches.
3.5. Timeframe analysis
To rigorously evaluate
Timeframe analysis.
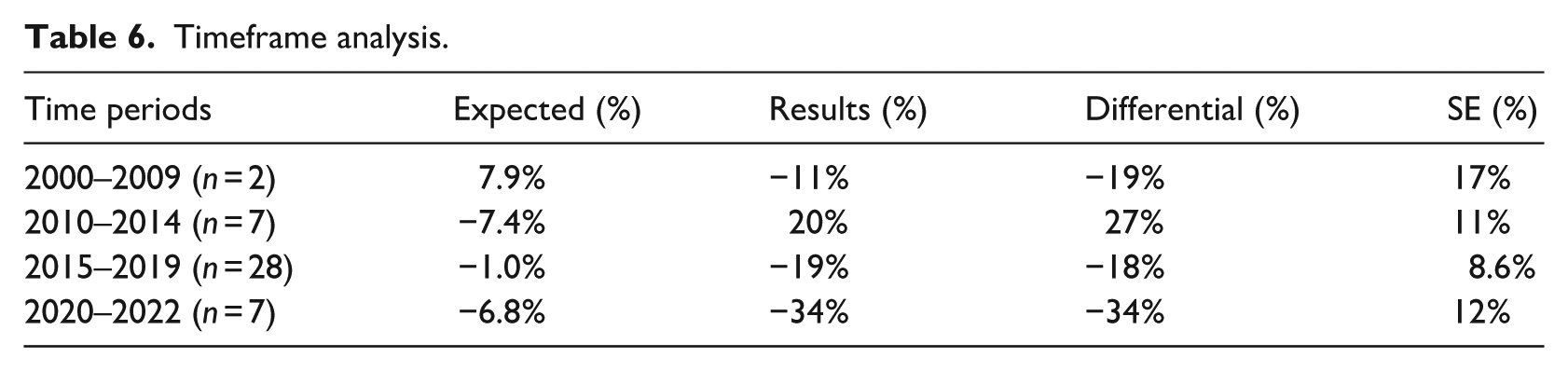
Three principal observations emerged from the
Third, and perhaps the most significant finding for management and shareholders, though not immediately evident in the published data, is the pattern of firms that suffered an extreme cyber incident and were subsequently acquired. Notable examples include Yahoo, AOL, Heartland Payment Systems, LinkedIn, and Mandiant. These acquisitions, often occurring at valuations significantly below their pre-incident levels, highlight the heightened vulnerability and potential devaluation impacts significant cybersecurity breaches can have on publicly traded firms.
3.6. Attack type analysis
Consistent with the original expectations in
A critical temporal dimension emerges in this study, underscoring the necessity of continually updating datasets to capture evolving cyber threats. Datasets focused exclusively on pre-2016 events may offer limited utility for understanding contemporary contexts, given the rapid advancement of both cybercriminal tactics and countermeasures. Should ransomware threats be effectively contained in the future, the broader study of cyber incidents may require selectively omitting data on ransomware attacks unless the specific objective is to analyse the shifting contours of the cybersecurity landscape. This flexible and adaptive research approach remains essential due to the ever-changing nature of cyber risks and their impacts on the corporate sector.
3.7. Heatmap analysis
Using the 2-year CAR data, we constructed a heatmap visualisation to deepen our analysis, with aggregated outcomes presented in Figure 6. Specifically, we compared each corporation’s quarterly market performance to the preceding quarter and then subtracted the corresponding S&P 500 growth rates. This methodology accounts for broader market forces by focusing on each firm’s valuation relative to a benchmark. We also hypothesised that a significant cybersecurity breach would trigger a negative market reaction, manifesting as a pronounced decline in relative market value during the incident quarter and immediately thereafter. We also conceived that any such effect would persist but taper over the subsequent 2 years.
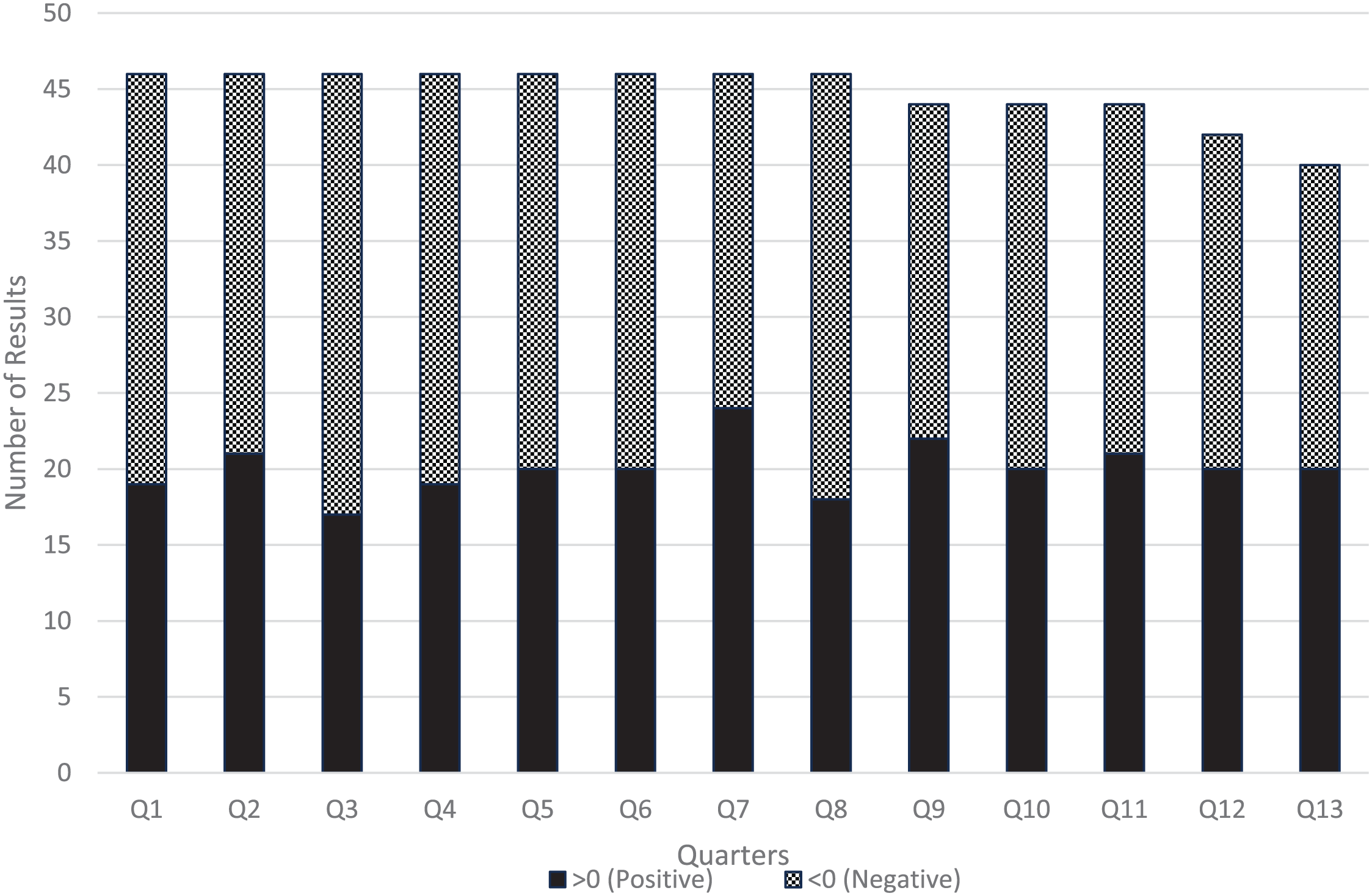
Heat analysis results.
While the data depicted in Figure 6 confirm that firms experiencing an extreme cybersecurity event generally underperform the broader market, the findings do not conclusively show a correlation between normal quarterly performance and those quarters containing a severe cyber breach. To the contrary, we observed a modest improvement in performance following the incident, likely driven by heightened internal scrutiny, enhanced managerial oversight, and the involvement of external expertise in the aftermath. These observations accord with Olson’s (2012) theory of collective action, whereby stakeholders, though vested in the firm’s success, often lack sufficient incentive for proactive engagement until a critical incident compels collective mobilisation. Furthermore, the data introduce the possibility that firms underperforming the broader market may be at greater risk of experiencing extreme cyber events. This relationship could reflect several factors, including lower investment in cybersecurity or deficiencies in risk management and governance practices.
4. Further discussion
This research challenges prevailing assumptions about the effects of cybersecurity events on publicly traded companies. On one hand, the analysis substantiates the significance of what is commonly referred to as ‘lost opportunity costs’ after extreme cyberattacks. On the other, it challenges the prevalent perception of the ubiquity and successful penetration of extreme attacks. Contrary to the often-sensationalised narrative of a relentless deluge of sophisticated cyber threats, the data underpinning this study reveal a more complex reality. Notwithstanding the billions of attempted cyberattacks annually, the empirical evidence from US-listed companies indicates that successful inductions of extreme cybersecurity incidents within these entities have been remarkably infrequent over the past two decades.
While this study primarily focuses on financial outcomes, other factors such as industry, geographic location and company size must also be considered. For instance, the prevalence of US-listed companies in the sample may be reflective of the sheer size and appeal of American stock markets rather than a greater frequency of targeting. In a broader industry context, publicly traded firms exhibit relatively dispersed exposure to extreme cyber events compared to non-public organisations, which often face a higher concentration of extreme attacks in specific sectors such as healthcare, municipal services and legal industries. This disparity may reflect deliberate targeting but could also be reflective of varying levels of cybersecurity investment and maturity across these sectors. Holistically, these findings underscore the multifaceted nature of cyberattack impacts while highlighting the limitations of the available data. They suggest that understanding the broader context of industry-specific vulnerabilities and market dynamics is essential for a comprehensive analysis of cybersecurity risks faced by publicly traded firms.
Beyond shareholders, multiple stakeholders are affected. For instance, customers and employees may suffer compromised personal or financial data, leading to privacy concerns and potential identity theft. Employees may also experience operational disruptions or face layoffs if the organisation is forced to reallocate budgets towards breach remediation and cybersecurity upgrades. Suppliers and partners can experience supply-chain inefficiencies and reputational risks from their affiliation with the affected firm, while regulators may intensify oversight and impose punitive measures, further reshaping the regulatory environment and increasing compliance costs. Collectively, these factors can undermine shareholder confidence, weaken valuations and necessitate ongoing expenditures to restore both market credibility and operational resilience.
As companies continue to undertake digital transformation and exponentially collect data, they will remain prime targets for cybercriminals. Without significant advancements in cybersecurity measures, it is plausible to anticipate a continued rise in the frequency and sophistication of cyberattacks. This evolving landscape therefore presents an opportunity for ongoing research. With an expected increase in the volume of data regarding cyber incidents, subsequent analyses will likely yield more precise insights into the impacts of specific types of cyberattacks and their effects across different industry sectors. Moreover, as the dataset expands, there emerges the potential for machine learning (ML) and generative artificial intelligence to offer innovative analytical methodologies. ML could, for instance, enable the identification of prior cyberattacks through pattern recognition in variables such as key staff departures or insider trading activities.
5. Conclusion
In this research, we have undertaken a detailed analysis of a comprehensive dataset comprising publicly listed companies over prolonged durations, to distil insights into the financial ramifications following extreme cybersecurity breaches. The study rigorously tested and validated our stated hypotheses (
Contrary to expectations, the study further revealed that despite an increased prevalence of extreme cybersecurity incidents, companies frequently struggled to revert to managing their normal financial trajectories. This observation also challenges the notion that defensive cyber capability advancements are keeping pace with the evolution and sophistication of cyberattacks. Furthermore, the examination of hypothesis (
A particularly salient finding of this research is the identification of the extensive downstream losses in market valuation, which in many instances drastically surpass the immediate clean-up expenses associated with extreme cyber events. This revelation holds substantial implications for corporate governance. Boards and executive management teams are urged to integrate these findings into their strategic considerations regarding cybersecurity risk exposure, risk appetite and corresponding investment decisions. For most corporations, this necessitates augmenting cybersecurity and risk management resources to effectively mitigate the risks associated with cyber events. This very much includes response management where some firms did perform so well here that they exceeded their previous market expectations in the long term.
Finally, the research reveals a discernible shift in market sentiment about companies that experience cybersecurity failures. The trend indicates an escalating intolerance in the market for such breaches, with the impacts of cyber events markedly intensifying since 2015. While no companies in the study were observed to have failed irrecoverably post the cybersecurity event, the data underscore their heightened vulnerability in the aftermath, leading to numerous acquisitions at significantly diminished market valuations. This highlights the criticality of robust cybersecurity measures not only for operational resilience but also for maintaining corporate value and market standing. In summary, while this study reframes the narrative around the prevalence and impact of cyberattacks on public traded companies, it also underscores the dynamic nature of this domain and the need for continued, nuanced research to keep pace with the evolving threat landscape.
Theoretical and Practical Research Contributions
This research advances both theory and practice in the domain of cyber risk and financial economics. Theoretically, it extends traditional event study frameworks by incorporating long-horizon windows to capture persistent valuation effects of extreme cybersecurity incidents, an area underexplored in current literature. Empirically, the findings demonstrate statistically significant long-run underperformance following major breaches, contributing to a more nuanced understanding of market inefficiency in the context of cyber shocks. Practically, the study provides corporate executives, insurers, and regulators with evidence-based benchmarks for assessing post-breach financial exposure and supports the development of more resilient risk management, disclosure and insurance strategies.
Footnotes
Appendix 1
One-year abnormal returns analysis.
| Name | Disclosure date | Expected | Actual | Differential |
|---|---|---|---|---|
| TJX | 18/12/2006 | 4.7% | 11.3% | 6.7% |
| Lockheed Martin 1 | 18/12/2009 | 3.2% | −11.1% | −14.3% |
| Sony 1 | 26/04/2011 | −9.7% | −67.1% | −57.4% |
| Lockheed Martin 2 | 21/05/2011 | −5.1% | 11.4% | 16.5% |
| Adobe | 3/10/2013 | 6.9% | 6.5% | −0.3% |
| Target | 18/12/2013 | −4.7% | 18.0% | 22.8% |
| Ebay | 21/05/2014 | −4.5% | 17.5% | 21.9% |
| Home Depot | 18/09/2014 | −2.9% | 23.7% | 26.5% |
| Sony 2 | 24/11/2014 | −6.0% | 40.2% | 46.2% |
| Anthem | 5/02/2015 | 9.1% | −5.7% | −14.8% |
| Experian | 16/09/2015 | 5.2% | 36.4% | 31.1% |
| Yahoo | 28/04/2014 | 2.5% | −9.6% | −12.1% |
| Oracle | 8/08/2016 | −0.1% | 11.5% | 11.6% |
| Tesco | 7/11/2016 | 3.4% | −7.5% | −10.8% |
| Telefonica Telecommunications | 13/05/2017 | −2.8% | −33.9% | −31.1% |
| Fedex (TNT) | 27/06/2017 | −0.1% | 4.2% | 4.3% |
| Maersk | 27/06/2017 | 3.3% | −47.4% | −50.7% |
| Merck & Co | 27/06/2017 | −0.4% | −10.9% | −10.5% |
| Mondelez | 27/06/2017 | −2.5% | −15.5% | −13.0% |
| Reckitt Benckiser | 27/06/2017 | −11.0% | −50.7% | −39.7% |
| Saint Gobain | 27/06/2017 | 1.9% | −33.7% | −35.6% |
| WPP PLC | 27/06/2017 | −2.6% | −36.9% | −34.3% |
| Equifax | 8/09/2017 | −0.6% | −10.5% | −10.0% |
| Schneider Electric | 18/01/2018 | −1.7% | −10.9% | −9.2% |
| Under Armour | 25/02/2018 | −13.9% | 18.9% | 32.8% |
| Boeing | 28/03/2018 | 16.5% | 2.1% | −14.4% |
| TSMC | 2/08/2018 | 0.7% | 23.4% | 22.7% |
| Austal a | 1/11/2018 | −1.1% | 77.3% | 78.4% |
| Marriot | 30/11/2018 | −1.2% | 3.1% | 4.3% |
| Saipem | 10/12/2018 | 7.9% | −29.0% | −36.9% |
| Landmark White | 5/02/2019 | −6.4% | −54.4% | −48.0% |
| Norsk Hydro | 19/03/2019 | −7.8% | −28.0% | −20.2% |
| Capital One | 19/07/2019 | −0.8% | −7.7% | −6.9% |
| Demant | 3/09/2019 | −10.7% | 6.2% | 16.9% |
| Prosegur | 27/11/2019 | −11.0% | −50.7% | −39.7% |
| Bird Construction Inc | 2/12/2019 | −3.0% | 10.7% | 13.8% |
| ISS World | 17/02/2020 | −7.1% | −28.1% | −21.0% |
| Cognizant | 17/04/2020 | −5.4% | −26.7% | −21.3% |
| Diebold Nixdorf | 14/05/2020 | −1.0% | 15.1% | 16.1% |
| LG | 24/06/2020 | 0.6% | 2.8% | 2.2% |
| Xerox | 24/06/2020 | −14.4% | −38.2% | −23.8% |
| Garmin | 24/07/2020 | 4.3% | −2.6% | −6.9% |
| Mandiant (FE) | 8/12/2020 | −5.5% | −12.3% | −6.8% |
| Solar Winds | 14/12/2020 | 0.1% | −81.1% | −81.2% |
| Average | −1.80% | −10.75% | −8.94% | |
|
|
−0.089 | |||
| SD | 0.269 | |||
| SE | 0.041 |
Italicised entries were excluded from the statistical analysis due to outlier characteristics.
Appendix 2
Two-year analysis.
| Name | Disclosure date | Expected | Actual | Differential |
|---|---|---|---|---|
| TJX | 18/12/2006 | 9.3% | 8.1% | −1.3% |
| Lockheed Martin 1 | 18/12/2009 | 6.5% | −29.6% | −36.1% |
| Sony 1 | 26/04/2011 | −19.5% | −50.1% | −30.6% |
| Lockheed Martin 2 | 21/05/2011 | −10.1% | 28.2% | 38.3% |
| Adobe | 3/10/2013 | 13.7% | 41.9% | 28.1% |
| Target | 18/12/2013 | −9.5% | 19.1% | 28.6% |
| Ebay | 21/05/2014 | −9.0% | 27.7% | 36.6% |
| Home Depot | 18/09/2014 | −5.7% | 19.7% | 25.4% |
| Sony 2 | 24/11/2014 | −12.0% | 52.7% | 64.7% |
| Anthem | 5/02/2015 | 18.2% | 3.7% | −14.6% |
| Experian | 16/09/2015 | 10.5% | 16.2% | 5.7% |
| Oracle | 8/08/2016 | −0.1% | −0.2% | −0.1% |
| Tesco | 7/11/2016 | 6.7% | −3.2% | −9.9% |
| Telefonica Telecommunications | 13/05/2017 | −5.6% | −53.1% | −47.4% |
| Fedex (TNT) | 27/06/2017 | −0.1% | −38.6% | −38.4% |
| Maersk | 27/06/2017 | 6.6% | −57.3% | −63.9% |
| Merck & Co | 27/06/2017 | −0.8% | 9.4% | 10.2% |
| Mondelez | 27/06/2017 | −5.0% | 1.0% | 6.0% |
| Reckitt Benckiser | 27/06/2017 | −3.7% | −34.1% | −30.4% |
| Saint Gobain | 27/06/2017 | 3.7% | −47.2% | −50.9% |
| WPP PLC | 27/06/2017 | −5.2% | −57.8% | −52.6% |
| Equifax | 8/09/2017 | −1.1% | 7.4% | 8.5% |
| Schneider Electric | 18/01/2018 | −3.4% | 1.0% | 4.4% |
| Under Armour | 25/02/2018 | −13.9% | 18.9% | 32.8% |
| Boeing a | 28/03/2018 | 33.0% | −67.5% | −100.5% |
| TSMC a | 2/08/2018 | 1.4% | 99.5% | 98.1% |
| Austal | 1/11/2018 | −2.2% | −8.6% | −6.4% |
| Marriot | 30/11/2018 | −2.5% | −35.5% | −33.1% |
| Saipem a | 10/12/2018 | 15.9% | −85.1% | −101.0% |
| Landmark White | 5/02/2019 | −12.8% | −78.0% | −65.2% |
| Norsk Hydro | 19/03/2019 | −15.6% | 1.9% | 17.5% |
| Capital One | 19/07/2019 | −1.5% | −38.8% | −37.3% |
| Demant | 3/09/2019 | −21.5% | 24.9% | 46.4% |
| Prosegur | 27/11/2019 | −22.0% | −78.0% | −56.0% |
| Bird Construction Inc | 2/12/2019 | −6.1% | 7.7% | 13.8% |
| ISS World | 17/02/2020 | −14.2% | −24.2% | −10.0% |
| Cognizant | 17/04/2020 | −10.7% | −26.7% | −16.0% |
| Diebold Nixdorf | 14/05/2020 | −2.0% | −79.8% | −77.8% |
| LG | 24/06/2020 | 6.5% | −2.9% | −9.4% |
| Xerox | 24/06/2020 | −28.9% | −34.1% | −5.2% |
| Garmin | 24/07/2020 | 8.6% | −33.6% | −42.2% |
| Solar Winds | 14/12/2020 | 0.1% | −79.6% | −79.7% |
| Average | −3.7% | −17.16% | −13.5% | |
|
|
−0.135 | |||
| SD | 0.373 | |||
| SE | 0.058 |
Italicised entries were excluded from the statistical analysis due to outlier characteristics.
Acknowledgements
The authors would like to thank Dr. Taylor Reynolds from the Massachusetts Institute of Technology (MIT), Prof. Peter McBurney from Kings College London (KCL), and Prof. Massimiliano Tani Bertuol from the University of New South Wales (UNSW) for their feedback and support in developing this research.
Final transcript accepted 29 August 2025 by Nik Thompson (AE – Information Systems).
Declaration of generative AI-assisted technologies
During the preparation of this work, Microsoft Copilot was used to improve the readability of the paper. After using this tool/service, Dr Ryan reviewed and edited the content as needed and takes full responsibility for the content of the publication.
Funding
The authors disclosed receipt of the following financial support for the research, authorship and/or publication of this article: This research was funded through the Australian Government Research Training Program.
