Abstract
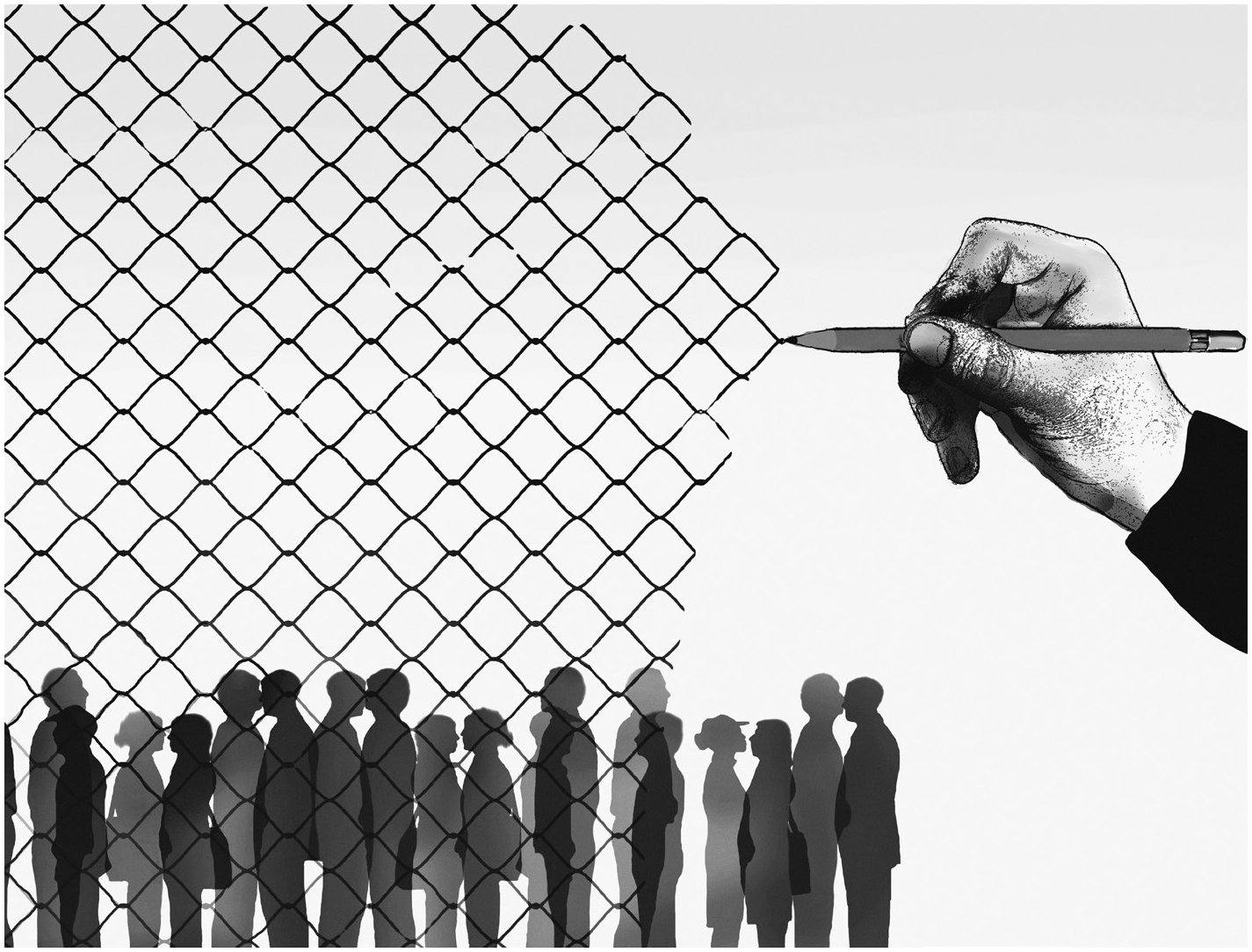
Digital security expert
Below are some key steps that you can take before you travel and while at the border, to better secure your data and your devices.
 Do your research
Do your research
Before crossing a border, you should research the law related to technology in the places you are leaving and entering. Legislation differs from country to country and it is important to stay on top of any changes to avoid breaking the law. Keep an eye on any amendments made to media and telecommunications laws or anti-terrorism acts, which have a tendency to criminalise the use of encryption and Virtual Private Networks. Do an internet search to see if anybody has been detained or put on trial for using these tools. Travellers should also look into laws around defamation and social media and be aware of any restrictions on posting and sharing content online.
 Know your adversary
Know your adversary
If you are targeted by state bodies or organisations with sophisticated tech resources, and you are entering territory controlled by them, then you should speak to a digital security expert prior to travelling about the best way to secure your devices and your information.
 Review your online profile
Review your online profile
Your online profile is what customs guards will see if they look you up online at the border, so it is important that you know how others see you. Check for your name through all search engines, and don’t look only at the general search results – review videos, images and news, too. Where possible, take steps to remove information that could put you at risk. Deleting information from the internet is difficult and a copy of that content is likely to still be available if someone should wish to find it. Changes to any information that you delete yourself will not show up on internet searches straight away.
 Make a plan in case you are detained
Make a plan in case you are detained
It is important to plan what you will do and say if you are stopped or detained. Know your rights if your devices are seized or if you are asked to unlock them or hand over any passwords. If you have concerns about crossing a particular border and have the support of an employer or an organisation, speak to them about steps that can be taken in case you are detained. Ensure you have spoken to a lawyer before travelling and carry their contact details with you.
 Know what information you want to protect
Know what information you want to protect
Review your devices for information that, if seized, could put you – or others – at risk. Look at documents and photos stored on your laptop and phone as well as information and conversations held in chat apps. Be aware that data stored in email accounts and in the cloud is at risk if your devices are seized and you have not logged out of your accounts or are asked to hand over your passwords. Review the settings of apps you use to see if they are backing up content to a cloud account linked to your devices.
 Create a secure way to back up and store information
Create a secure way to back up and store information
Once you have identified what information you need to keep, you should create a secure back-up of this content before travelling. It is a good idea to back up the information to an external hard drive, which you should then encrypt and store in a secure place. You should get into the habit of backing up information from your devices regularly.
 Think about your devices
Think about your devices
If you are travelling with data that you do not want others to access, you should either securely remove this information from the devices before travelling or buy new devices. These new devices should hold only non-sensitive information and you should not link them to any accounts that you would not want others to access. You may want to carry out factory resets of your devices, which restore them to their original settings, before each border crossing. This will permanently delete all content and apps that are on them, so ensure you back up any information first.
If there is a high probability that your devices will be seized then you may want to consider setting them to remote-wipe. This means that content from your phone and laptop will erase automatically if instructed to do so. Unless you have created a back-up you will lose all data on them. Remote-wipe must be set up in advance and you will need a person you trust to access your account and initiate the wipe. Your devices will wipe only if they are connected to mobile data or WiFi.
 Preparing your laptop
Preparing your laptop
Make sure your computer is password-protected and the operating system is up to date. Review the device to ensure all sensitive documentation is removed and backed up and that the laptop has been securely wiped. Log out of all your accounts and apps and clear your browsing history from each search engine. This will stop border guards being able to access your accounts without your password. If the law permits it, you should encrypt your laptop to protect content on the device being looked at without your knowledge.
CREDITS: Victor / iStock /Gary Waters/Ikon
 Preparing your phone
Preparing your phone
Create a long pin lock for your phone and update it to the latest version of the operating system as this patches any known bugs. Review your phone to ensure there is no sensitive data on it, back up the content and carry out a factory reset. If you install apps after the factory reset then download only the ones you need for your trip. Log out and uninstall any apps that give away personal information, such as social media apps. You will need to go into the settings section of the phone to do this rather than removing them from the home screen – you can install them again once you have crossed the border. Review your contacts and remove any that are sensitive – you will need to remove them from both the device and the cloud account. Finally, you should go into the settings section of your phone and clear your cache. This will delete your browsing history.
 What to watch for at the border
What to watch for at the border
You should turn off all devices before you cross the border as this will enable full-disk encryption, if it has been set up. This means that a border guard will have to ask you for the password in order to read the content on your device. Keep an eye on your devices at all times and watch to see if anyone tampers with them. If a device is taken away and later given back to you, be aware that the content of that device could have been copied and that malware, including spyware, could have been installed.
What Does the Future Hold?
Protecting your information while crossing borders may become more complicated in the future as governments roll out new technology at airports and customs officials are given more powers. Below are some developments to watch out for.
MORE FACIAL RECOGNITION
While facial recognition technology is already being used by security in some airports to confirm the identity of passport holders, airline companies and airports are starting to use it as a way to check in and to board planes. This raises concerns about which companies are storing your data and who else has access to it.
INCREASED LEVELS OF ONLINE SCRUTINY FOR VISA APPLICANTS
Governments could possibly follow the US model of asking for a person’s social media handle as part of the process of applying for a visa. Earlier this year, the US government started asking certain visa applicants to supply all social media user-names and made it a criminal offence not to do so.
TIGHTENED GOVERNMENT CONTROLS RESTRICTING ONLINE PRIVACY
Changes to legislation by governments around the world are making it increasingly difficult to cross borders with encrypted devices or with tools that allow you to circumnavigate online censorship. This makes it easier to detain, arrest and charge people as well as limiting access to the internet once inside the country.
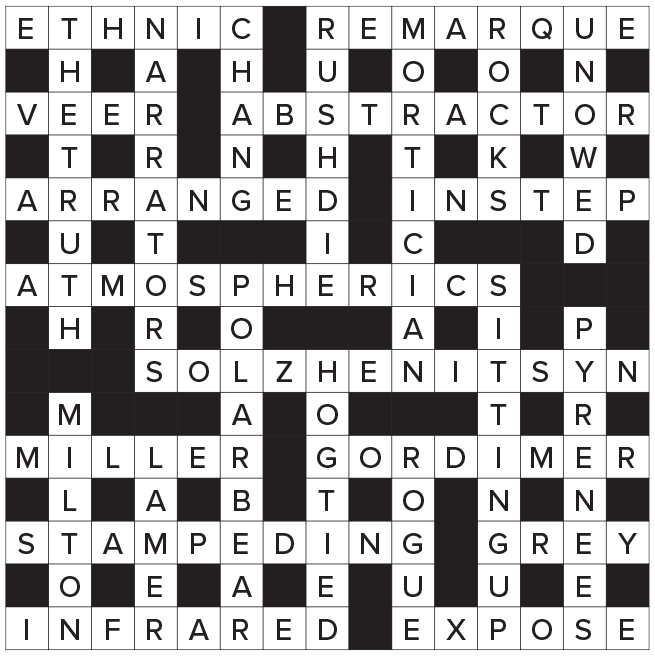
Crossword Answers
Everything you add to the truth subtracts from the truth (Solzhenitsyn)