Abstract
When is heterogeneity in the composition of an autonomous robotic team beneficial and when is it detrimental? We investigate and answer this question in the context of a minimally viable model that examines the role of heterogeneous speeds in perimeter defense problems, where defenders share a total allocated speed budget. We consider two distinct problem settings and develop strategies based on dynamic programming and on local interaction rules. We present a theoretical analysis of both approaches and our results are extensively validated using simulations. Interestingly, our results demonstrate that the viability of heterogeneous teams depends on the amount of information available to the defenders. Moreover, our results suggest a universality property: across a wide range of problem parameters the optimal ratio of the speeds of the defenders remains nearly constant.
1. Introduction
An increasingly important task where a robotic system can be employed is in defending an area against external agents, which pose varying levels of threat. Examples include defending airports against intruding and flight-grounding drones (Lykou et al., 2020), defending wildlife habitats against trespassing poachers (Casey, 2014), extinguishing and preventing the spread of devastating wildfires caused by human or natural activity (Cohen, 2007), as well as military applications (Zych, 2020).
In general, solutions to perimeter defense problems allude to finding strategies for a set of agents restricted to the perimeter of an area, entrusted with defending the area from intruders which are trying to breach the perimeter of the area (Shishika and Kumar, 2020).
Compared to a homogeneous team of robots, a team of robots with varying capabilities (heterogeneous team) comes with its unique set of advantages and challenges. Equipping different agents with different capabilities can lead to synergy effects where the heterogeneous system outperforms the alternative homogeneous system composed of identical agents. As a result, in the last decade, there has been significant interest in the robotics community to define, explore, and quantify heterogeneity in different robot applications (Mayya et al., 2022; Ramachandran et al. 2019, 2022; Ravichandar et al., 2020; Santos and Egerstedt, 2018; Twu et al., 2014).
This paper investigates the impact of heterogeneity in multi-robot teams for the perimeter defense problem. 1 We propose two optimal strategies, valid under different assumptions. The first strategy is based on dynamic programming (DP) (Cormen et al., 2001). It is optimal when the defenders are able to predict the location of the incoming attacks, but suffers from the curse of dimensionality and therefore relatively high associated computational costs. The second strategy is based on local interaction rules, and is optimal when the defenders have very limited information about the incoming attacks. This strategy can be efficiently computed in an online fashion, but does not implement any prior knowledge of the attack locations.
We prove the optimality of both strategies and analyze their time complexities, subject to a natural assumption (which will be discussed in detail in Section 5). The algorithms are extensively validated on simulations. Our numerical experiments are two-dimensional, but the majority of the theoretical results remain valid for any dimension. This includes three-dimensional perimeters in applications involving drones, and higher-dimensional perimeters arising as constraint sets in a state space of arbitrary dimension.
Our results show that heterogeneity is beneficial in the case where the defenders have access to information about the incoming attacks, and is detrimental when the defenders have very limited information about the attacks. Moreover, we show the universality property that the optimal ratio of the speeds of the defenders remains nearly constant for a two defender case setting.
For completeness, we also investigate the case of homogeneous defenders in order to establish the baseline properties of this model.
1.1. Related work
Perimeter defense problems are a variant of pursuit-evasion problems which have been studied extensively in literature. The seminal work of Issacs delineates differential-game approaches to arrive at equilibrium strategies for one pursuer one evader games (Isaacs, 1965). There has been considerable effort by researchers from various communities for solving various variants of pursuit-evasion games involving multiple pursuers and evaders (Fuchs et al., 2010; Von Moll et al., 2020; Yan et al., 2019). These papers contain works that view pursuit-evasion games either from the pursuers’ side, from the evaders’ side, or both. The curse of dimensionality poses a considerable challenge in solving problems involving multiple pursuers and evaders. The perimeter defense problem presented in this paper is a variant of the target guarding problem first introduced by Isaacs (Isaacs, 1965). In the target guarding problem setting an agent is tasked with guarding a region of interest against an adversarial agent. Investigations on perimeter defense problems are in their nascent stage. The review paper by Shishika and Kumar (Shishika and Kumar, 2020) delineates the recent works done on multi-robot perimeter defense problems (Guerrero-Bonilla et al., 2021; Lee et al., 2020; Shishika and Kumar, 2018; Shishika et al., 2019, 2020). Unlike the problems considered in these works, we consider a class of perimeter defense problems in which the number of attackers is much larger than the number of defenders. The authors of (Macharet et al., 2020; Velhal et al., 2022) consider the case of more attackers than defenders in similar (but distinct) contexts of homogeneous defenders. In particular, (Macharet et al., 2020) studies the problem of finite horizon attacks obeying an unknown probability distribution and partition the perimeter among the defenders. The authors of (Velhal et al., 2022) consider a decentralized method for allocating defenders to the incoming attacks. A one-defender analogue of the problem was previously considered in (Bajaj and Bopardikar, 2019; Chopra and Egerstedt, 2014; Smith et al., 2009) study a similar problem where attacks are assigned to defenders with differing skillsets (each attack can only be thwarted by a defender possessing a matching skill) with the goal of minimizing total defenders needed and total defender travel distance; however, their problem does not include constraints on defender speed, thus allowing any defender to reach any sequence of non-simultaneous attacks. Finally, Velhal et al. (2022) present and study a model which is very similar to our homogeneous defender perimeter defense problem; a full comparison and discussion is given in Section 4 and Appendix 5.
The remainder of the paper is organized as follows. Section 2 contains our notation together with the problem statement. Sections 4 and 5 detail our theoretical results in the infinite and unit-time horizon cases, respectively. Section 6 concludes with simulation results.
2. Problem statement
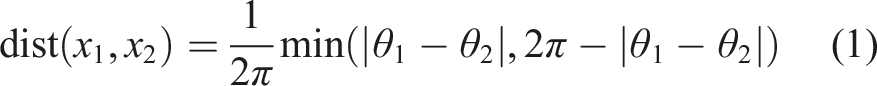
In this paper, bold letters are used to represent vectors and non-bold letters to represent scalars. Calligraphic letters are used to represent sets, and
For any positive integer
2.1. Perimeter defense against point attacks
Notations.
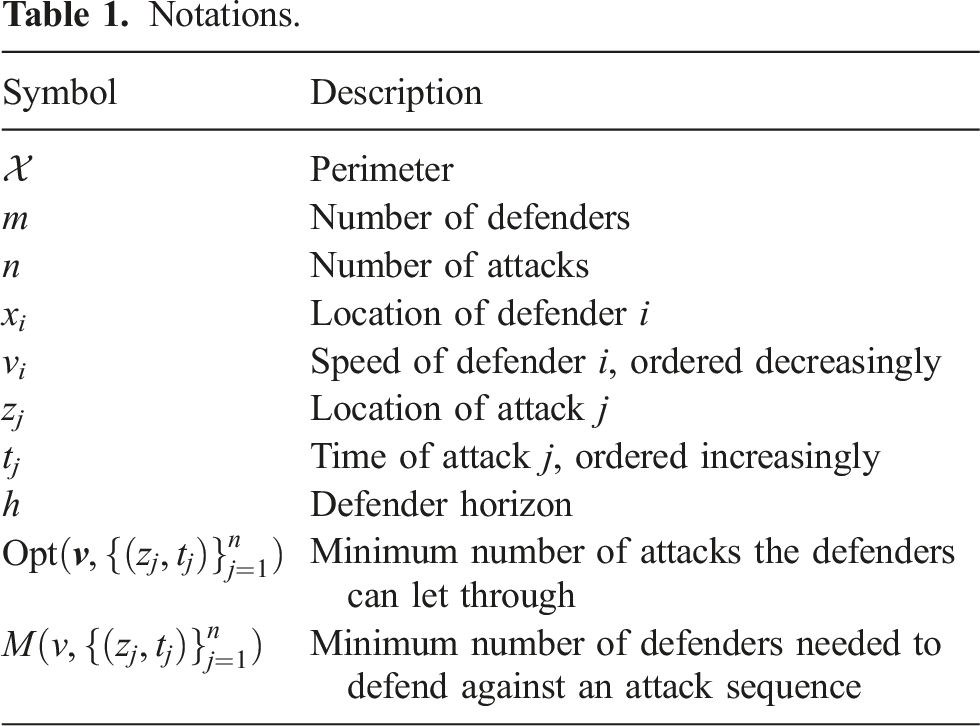
Without loss of generality we order the defenders from fastest to slowest, that is, v1 ≥⋯ ≥ v
m
, and we denote the speed vector as Three defenders facing three attacks, with the unit-time reachable sets for each defender shown. Note that the third dimension is time; if the attack represents a physical object it is approaching from somewhere outside the circle, but we are only concerned with where and when it will hit the perimeter. In this example, the defenders are not allowed to leave the perimeter, so the size of the reachable set scales linearly with speed (until it covers the whole perimeter).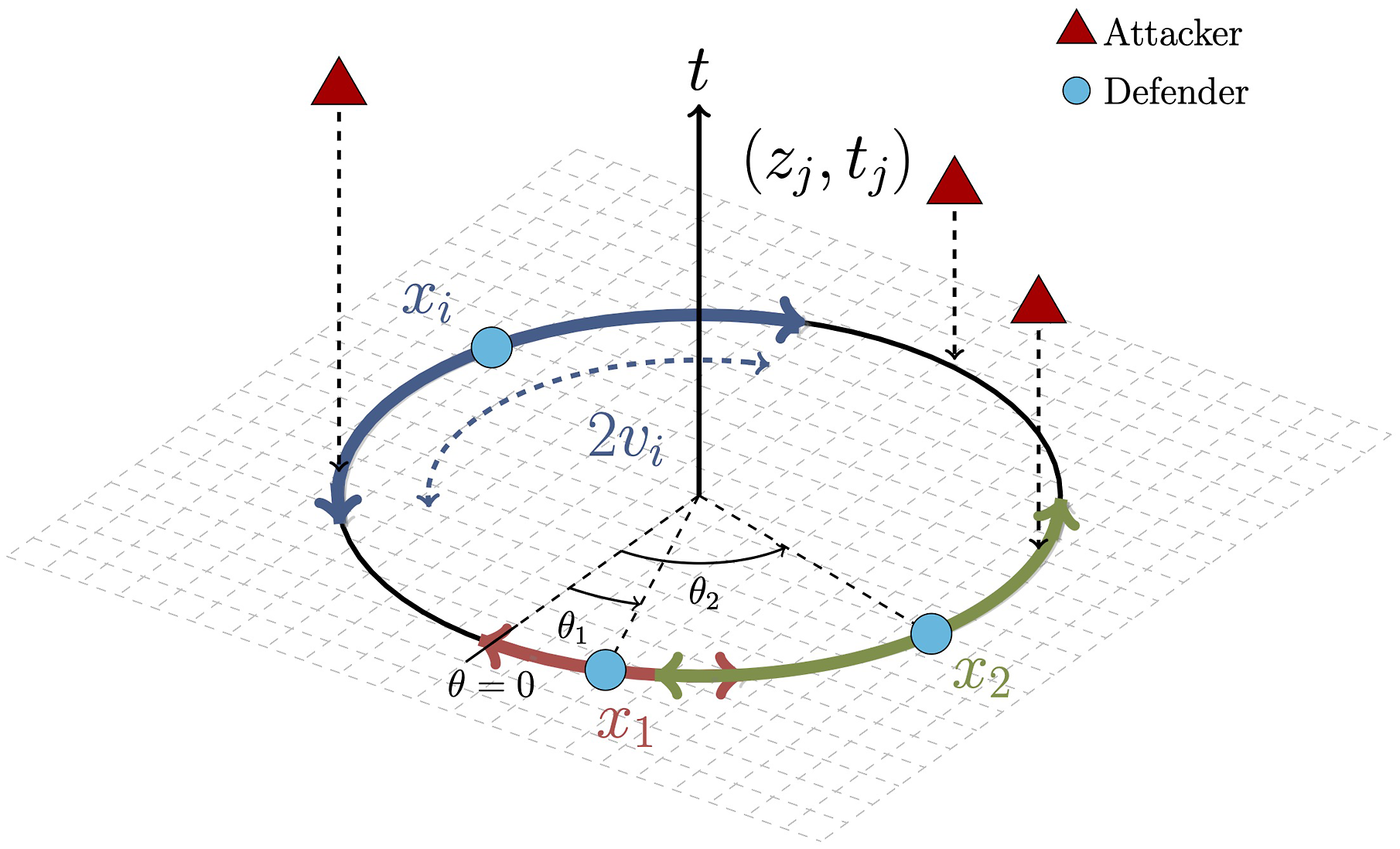
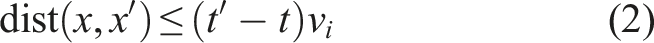
An attack (z j , t j ) is thwarted if and only if a defender is present, that is, there is some defender i at z j at time t j ; otherwise, we say that the attack breaches the perimeter. The goal is to design a policy for the defenders that minimizes the number of attacks that breach the defenses, and to study the effectiveness of different defender speed combinations against attacks.
Additionally, the team of defenders has a horizon h under which they can see attacks: specifically, at time t, any attack (z j , t j ) is known to the defenders if and only if t j ≤ t + h. We will study in particular the unit horizon h = 1 and the infinite horizon h = ∞ (all attacks are visible from the start).
Finally, the defenders are allowed to start at t = 0 at any combination of locations in
Given a speed vector
2.2. Different settings
Within the above problem description, there are several different variations, mostly to do with how the attacks are generated and the length of the horizon h. We roughly divide attack sequences into two settings: 1. Any sequence of attacks (z
j
, t
j
) is legitimate. 2. Attacks must come at unit-time intervals, that is, t
j
= j for all j ∈ [n].
Note that in setting 2 we do not lose any generality by having the attacks happen at unit-time intervals, since we can rescale the time units (and adjust the speeds of the defenders accordingly). Since the index j is superfluous in setting 2 we refer to the sequence of attacks as z1, z2, …, z n , indexed by t.
In setting 1, we study the case where all attacks are known to the defenders at the start; our primary problems are (i) find an algorithm for the defenders’ movements that minimizes the number of breaches, and (ii) study the behavior of optimal defense against uniformly random attacks (in both location and time) for different combinations of defenders. Since setting 1 is more general, the algorithms will also apply to setting 2.
In setting 2, we study the case where the attacks are (i) generated uniformly at random in location (time is fixed) and (ii) generated by an adversary which wants to guarantee a breach with as few attacks as possible. We also consider both the case where all the attacks are known to the defenders at the start (h = ∞) and the case where attack t only becomes known at time t − 1 (h = 1).
While in this work we mainly deal with the case where the number of defenders is fixed, and the question is how fast to make each defender (and in particular whether to make them all the same speed or not), we also investigate the alternative case of varying the number of (same-speed) defenders in Section 3, especially in regards to the tradeoff between fewer and faster defenders versus more and slower ones; we refer to this as the homogeneous setting. We show an efficient algorithm for determining the minimum number of (same-speed) defenders needed to thwart all attacks in a given attack sequence with infinite horizon, and empirically analyze how this minimum varies in expectation with the speed of the defenders. This shows that even the homogeneous setting has interesting and non-trivial properties that merit further study.
3. Homogeneous setting
For a team of homogeneous defenders with speed v against a sequence of attacks
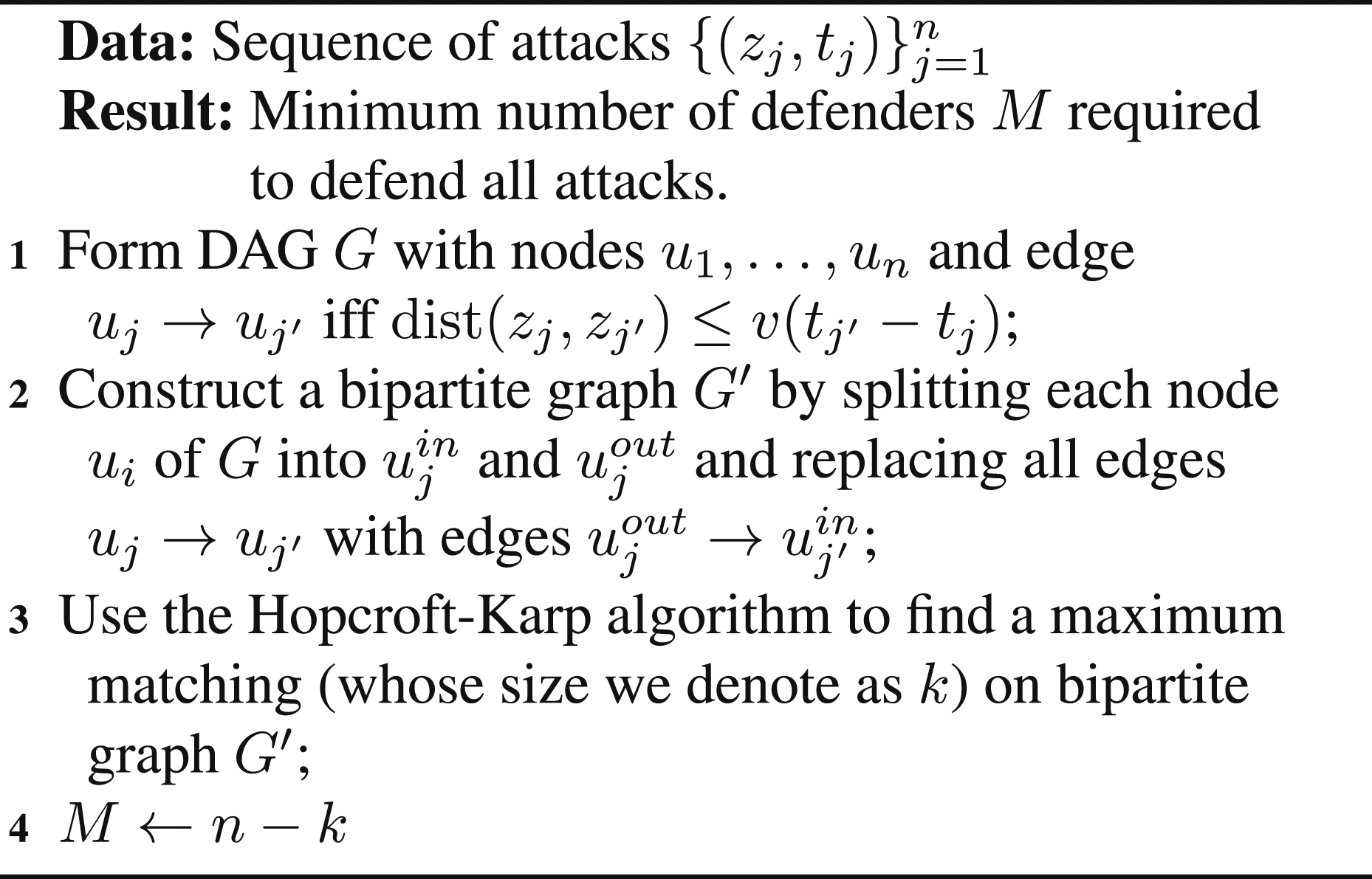
First, we build a directed acyclic graph (DAG) G on n nodes u1, …, u n , each node representing an attack; we assume that they are sorted by time t1 ≤ t2 ≤ … t j (if not, we sort them in O (n log n) time). We put a directed edge u j → uj′ (where j′ > j) if and only if dist (z j , zj′) ≤ v (tj′ − t j ), that is, if attack j′ can be reached by a defender which thwarts attack j.
Note that a (directed) path in G corresponds to a sequence of attacks that can be defended by a single defender. Thus, the goal is to decompose G into (the minimum) M directed paths which cover all vertices.
This path decomposition is done via a (well-known) reduction to maximum bipartite matching: we split each node u
j
into
Taking
Since there is one such path starting at each unmatched
Thus, we can use any well-known maximum bipartite matching algorithm (e.g., Hopcroft-Karp) to compute the number of defenders needed.
Note that a complete matching (which would imply that 0 defenders could thwart all the attacks!) is by definition impossible because G is acyclic.
The algorithm is summarized in Algorithm 1 for ease of reference.
Algorithm 1: Homogeneous case
Taking the matching produced by Algorithm 1 and adding the edge
3.1. Complexity
There are two parts to this problem: 1. Building DAG G and its bipartite counterpart G′. 2. Computing the maximum matching.
Ignoring d, which we assume to be small, (1) takes O (n2) time, and (2) with Hopcroft-Karp takes
3.2. Extension to cost minimization
As mentioned in Section 1, a very similar problem to the homogenous defender problem discussed in this section was studied in Velhal et al. (2022). 2 Under the same threat model (attacks occur at certain times and places, and a team of homogeneous defenders must intercept all of them), they extended the question to include the minimization of fuel cost (as measured in total travel distance of the defenders) while minimizing the number of defenders. They first consider a version with a fixed number of defenders; in this case the only objective is to defend all attacks while minimizing fuel cost. They formulate this as an instance of the Linear Sum Assignment Problem (LSAP), which can be solved by successive applications of Djikstra’s Algorithm in O (n3) total time (if there are insufficiently many defenders to defend the perimeter, the solution instead gives the smallest possible number of attacks which must be left undefended). They then use repeated applications of the LSAP to find the minimum number of defenders needed to protect the perimeter, and then minimize the fuel cost. Although in their work they claim that a single call to the LSAP suffices to determine the minimum number of defenders, we believe that multiple calls (naively up to even O (log n)) are necessary; see Appendix 5 for details.
In contrast, our problem seeks only to minimize the number of defenders, since our focus in this section is to characterize the tradeoff between the speed of the defenders and the number needed to protect the perimeter. Thus, in contrast to their solution, which relies on solving a complexity-O (n3) problem, we can achieve this in O (n2.5) in the worst case via reduction to maximum bipartite matching.
Nevertheless, inspired by their results, we note that our algorithm can be extended to cover the cost minimization problem as well (with an arbitrary cost function for traveling between locations, where the objective is to minimize the sum of the costs of travel): Suppose the cost of moving from attack j to j′ is given by cj,j′ ≥ 0 (if moving from j to j′ is feasible). Then, after constructing the DAG G with edges E and its bipartite counterpart G′ as in Algorithm 1, we apply a weight to edge 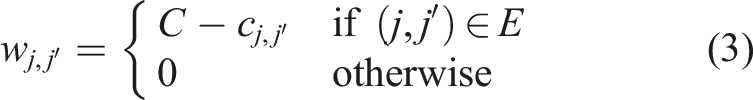
Thus, our technique reduces this problem to an instance of the Assignment Problem with weights wj,j′, which can be solved in O (n3) time by the Hungarian Algorithm. Solving this problem minimizes both number of defenders and cost simultaneously.
4. Infinite horizon theoretical results
We now turn to the question of heterogeneous teams.
4.1. Dynamic programming with infinite horizon
We now give an algorithm which, given defender speeds
Recall that by default the attacks are sorted in order of arrival time (or the user should sort them before applying the algorithm).
The pseudocode is given in Algorithm 2, in which we use the following notation: 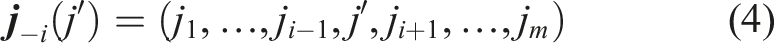
Algorithm 2 then works by recursively computing the function • V (0, …, 0) = n (the base case from which we recursively compute V), which holds since •
The for-loop in Algorithm 2 computes V(
The proof of the following result is given in Appendix 1:
Algorithm 2 outputs the correct value of
See Figure 2 for an example and Appendix 1 for the details. Computing V (6, 2, 4) (defender 1 has to thwart attack 6, etc.,) recursively; each defender is allowed to thwart attacks prior to these, but not afterward. Since 6 is the maximum value, we consider the last attack that defender 1 can handle before 6: based on its speed, it can be 0 (defend nothing before 6), 1, or 3. Thus V (6, 2, 4) = min (V (0, 2, 4), V (1, 2, 4), V (3, 2, 4)) − 1.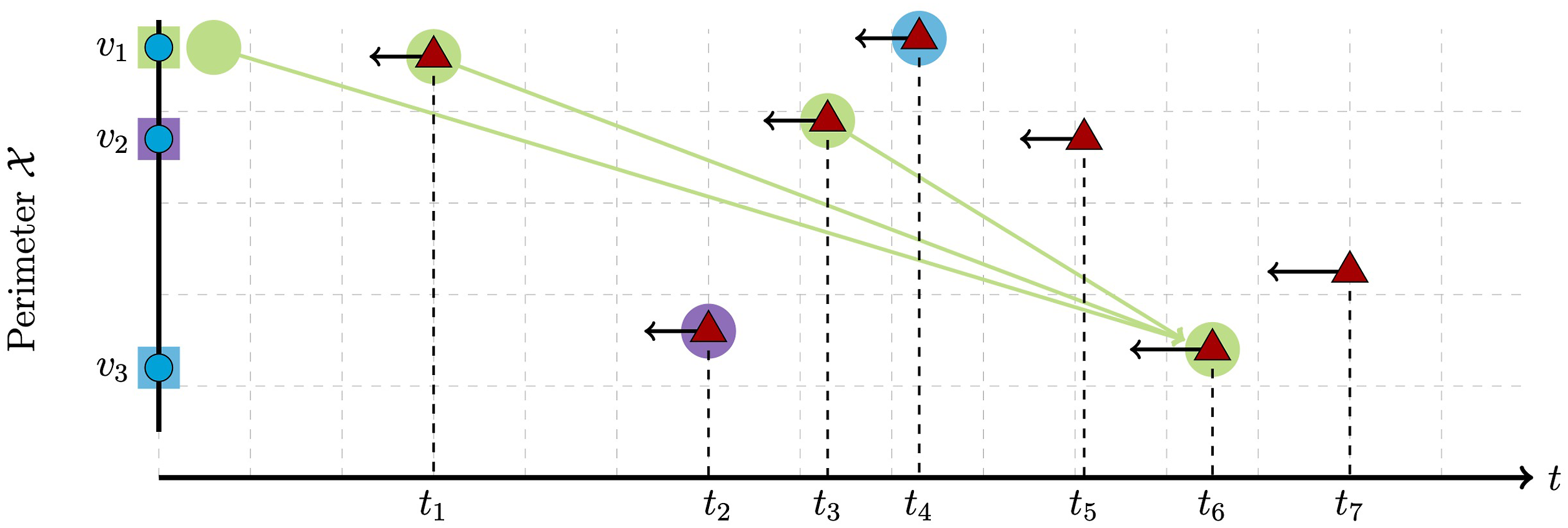
Algorithm 2: Dynamic programming for infinite horizon defenders.
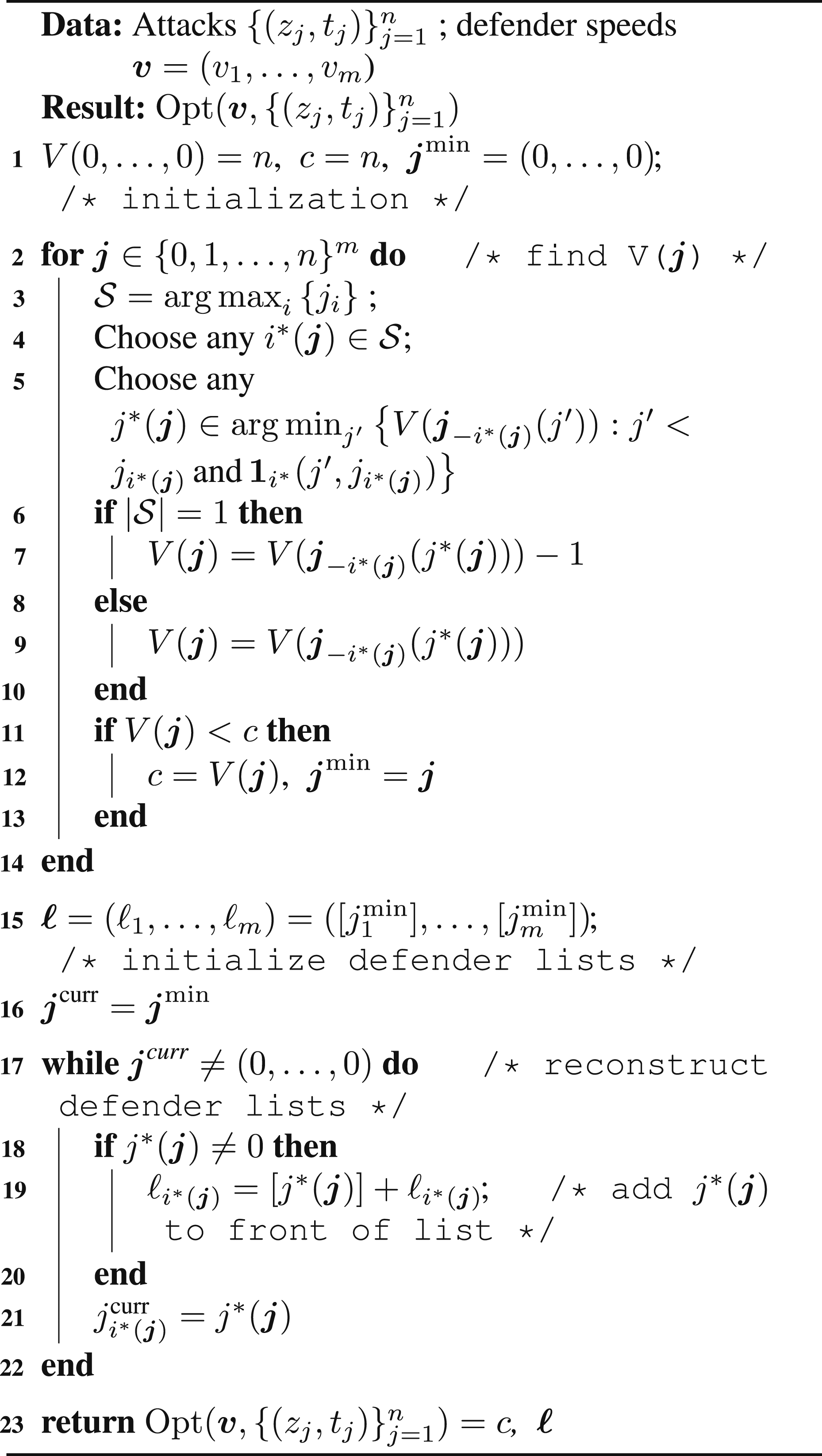
Algorithm 2 relies on the subtle point that i*(
Algorithm 2 assumes that the defenders can start at whatever locations they want, but can be modified for fixed defender starting locations (or a set of possible starting locations) by redefining
Given m defenders and n attackers, the number of computations needed to run Algorithm 2 is O ((n + 1)m+1) (we need to run through (n + 1)
m
values of
4.2. Monotonicity-based computational acceleration
In order to investigate team heterogeneity, we compute
However, as each attack sequence is evaluated on all
In particular, for any sequence 
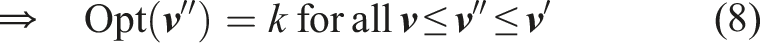
Thus we know Opt (
We now describe this order in greater detail. While we have not made any rigorous attempt to optimize the ordering, the order we use was effective enough to reduce the computation of the simulations described in the main work (see Figures 3 and 5, left-hand column for uniformly random attack times and right-hand for fixed attack times) by an average of between 93% and 99% depending on the parameters; the savings are much more pronounced for the fixed attack times case, as the Opt function is generally flatter (and hence produces more cases where the upper bound matches the lower bound and the DP computation can be skipped). The quantity w as a function of v1 and v2, with the regions defined by Theorem 2 removed.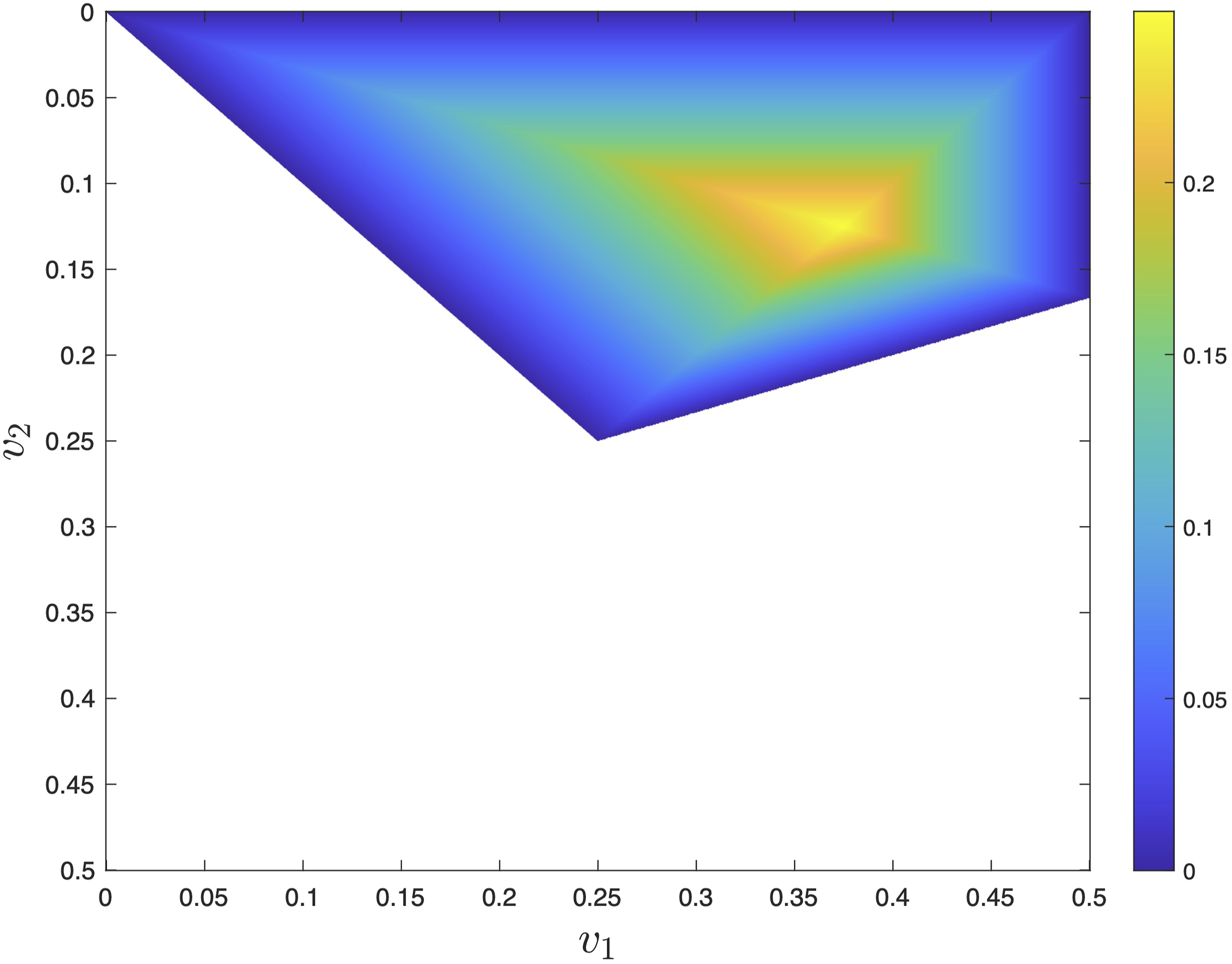
First, it is noted that permuting 
This just means that the ith defender has speed
The basic idea is to compute in order of decreasing powers of 2, which we refer to as levels: for instance, when g = 256 we compute first for multiples of 256, then multiples of 128, then 64 and so forth. In this way, at each level we can use the results from the level above to check the monotonicity condition and potentially save significant computation.
The algorithm then does the following: 1. Compute V (j1, j2) for the four corners of the grid. 2. Compute V (j1, j2) on the edges and main diagonal of the grid, in decreasing powers of 2. This establishes a border so that every subsequent step has an upper bound and a lower bound to compare. 3. Compute V (j1, j2) by decreasing levels (at each level, doing it in lexicographic increasing order as normal, skipping any entries already computed previously).
We also for simplicity only considered the upper and lower bounds generated by previous entries on the same row or column of the grid (two upper bounds, one for the row and one for the column, to two lower bounds, also one for the row and one for the column).
5. Unit-horizon theoretical results
This section considers defenders with a unit horizon of incoming attacks. The general setup is • We consider two defenders with speeds v1 ≥ v2. • We consider a perimeter • The n attackers are generated according to Setting 2 from Section 2: attacker t appears at time t, uniformly (and independently) over • The defenders have a unit horizon in time: at any given time they only see the next incoming attack, though they also know n and the current time t.
Therefore the defenders’ policy can be thought of as a sequence of decisions taken at unit-time intervals (i.e., when the next attack is revealed), which is naturally formulated as a Markov Decision Process (MDP) (Puterman, 2014) with n steps, with the reward being the number of thwarted attacks.
To simplify the MDP we can remove one state variable since, by symmetry, we can rotate
5.1. Policy and reward
A unit-horizon policy is a function 
The policy then produces a reward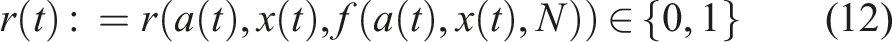
The reason for this is that by symmetry (of the perimeter and of the attacks), the ability of the defenders to stop future attacks depends only on their distance a (t + 1) = f (a(t), x(t), N). Thus, if the defenders can stop the current attack and end at distance a (t + 1) = f (a(t), x(t), N) for the next step, it is always best to do so (as opposed to ending at the same distance without stopping the attack).
So r(t) = 1 under policy f if and only if this is possible, which can be split into two cases: (i) defender 1 makes the capture; (ii) defender 2 makes the capture. If either of these are feasible, r(t) = 1; if neither are, r(t) = 0.
If dist(a(t), x(t)) > v2 and dist(0, x(t)) > v1, this means that neither defender can reach the next attack and hence r(t) = 0 no matter what.
5.2. Optimal defender policy
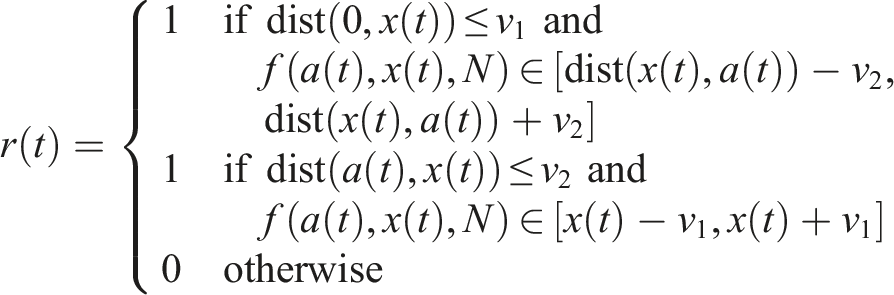
Fix a defender policy f. For a given total number N of incoming attacks and an initial distance a between the two defenders, we define the expected reward J (a; N) of the defenders as the expected total number of thwarted attacks, that is,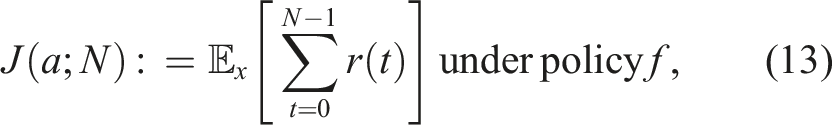
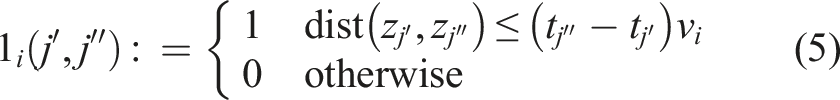
We first show necessary and sufficient conditions for perfect defense, that is, when no (fixed-time) attack sequence can force a breach.
(The perfect defense theorem). For any pair of defenders with speeds v1, v2 where v2 ≤ v1, there exists a sequence of attacks that breaches if and only if v1 < 1/2 and v1 + 3v2 < 1; whereas, if v1 ≥ 1/2 or v1 + 3v2 ≥ 1, the defenders can defend indefinitely even with a one-step horizon. Furthermore, if any sequence of attacks guarantees a breach, there also exists a sequence (not necessarily a subsequence) of at most 6 attacks that does so.
The proof is given in Appendix 1.
Next, we conjecture that it is always optimal to thwart a reachable attack; furthermore, we prove that under certain conditions (specifically, if the number of future attacks is sufficiently small relative to a parameter dependent on the defender speeds) then thwarting it is always optimal. The following result shows that, for a wide range of values for v1, v2 and N, the optimal strategy should (i) always thwart the currently known if possible.
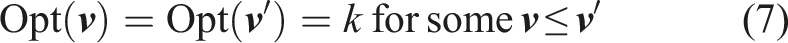
Let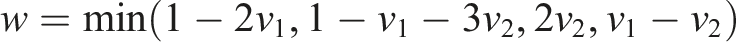
The proof is given in Appendix 2.
The value w is maximized when v1 = 3/8 and v2 = 1/8, yielding w = 1/4. We also show w as a function of v1 and v2 in Figure 3, with the regions defined by Theorem 2 removed, since these guarantee perfect defense and hence that all attackers can and should be captured.
Note also that the above holds as well if the number of future attacks is random (unknown to the defenders) with
We next prove that the optimal policy subsequently should (ii) always maximize a(t) subject to the first constraint. That is,
f* maximizes J(a; N) if (ii) a(t + 1) is maximized for all inputs, over all policies that satisfy (i) (i.e., capture when possible).
The proof is given in Appendix 3.
6. Simulation results
6.1. Simulations for homogeneous defenders
The goal of the simulations is to explore the relationship between speed and number of defenders (if we halve the speed of the defenders, how many more do we need to keep the same level of effectiveness?)
Our experiments follow the pattern: 1. Generate attacks 2. Compute the minimum number of defenders 3. Repeat the above for T trials and average the resulting values for each value of v or
We compute
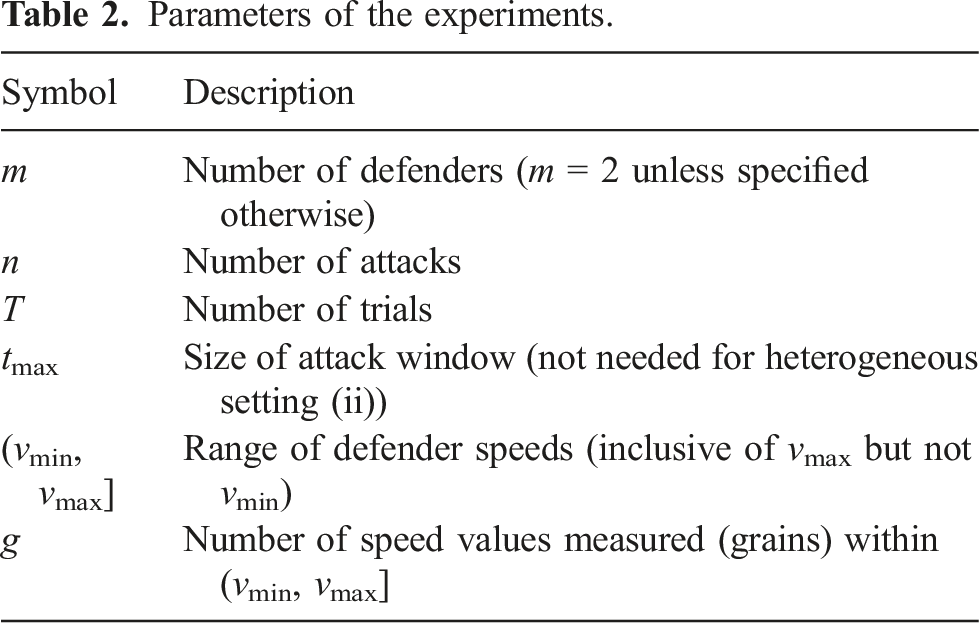
Parameters of the experiments.
For ease of notation, we denote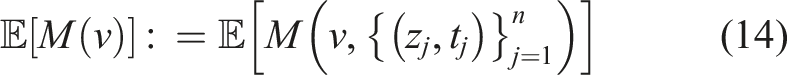
The expectation is over the attacks, that is, random (z j , t j ). All experiments are for uniformly random attack times on a circular (1-dimensional) perimeter of circumference 1.
Our simulations suggest a strong relationship between the speed v of the homogeneous defenders and the expected number Log-log plots of v versus (empirical) 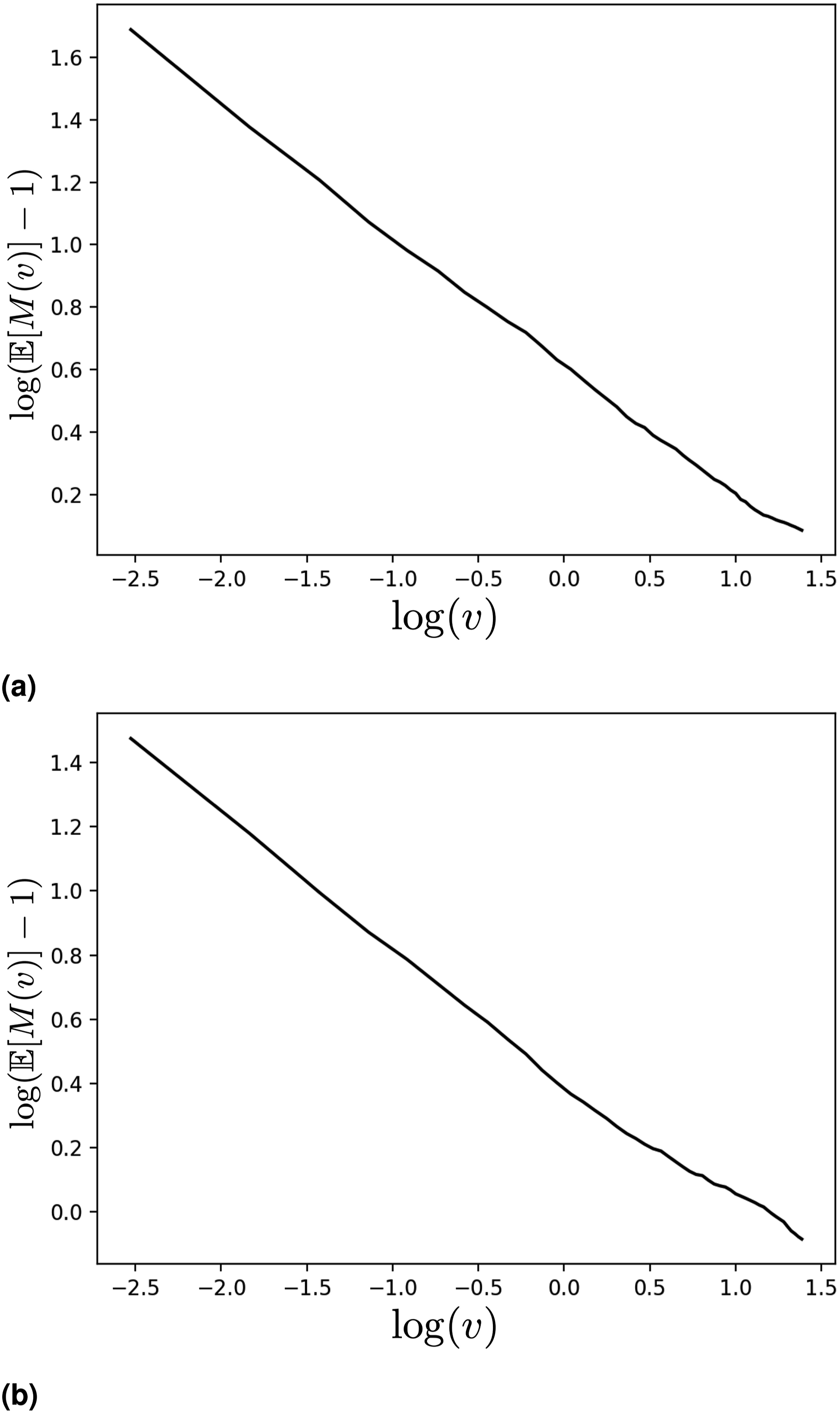
This suggests that given a particular distribution of attacks, there is some value α > 0 such that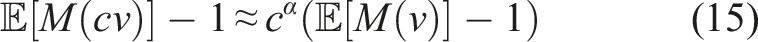
The slope of the line 6 in the log-log plots in Figure 4 is −α. What α measures, roughly, is the balance of the speed-number tradeoff for the defenders: if we double the speed of the defenders, how many fewer defenders (on average) will we need to stop all the attacks? The nearly linear nature of Figure 4 indicates that, for a given (uniform in time and location) distribution of attacks, this tradeoff is roughly constant over a wide range of speeds. When α is small, it indicates that increasing the number of defenders is comparatively more important than increasing the speed (by the same proportion); in particular, if α = 1 then doubling the speed and doubling the number are equivalent.
We then examine what this α is given different distributions of attacks: for a given value of tmax, we vary the number n of attacks and see how α changes. The results are shown in Figure 5, with the y-axis being the slope of the log-log plot of the given parameters (−α, as mentioned above). Note that α < 1 in all measured cases, meaning that increasing the number of defenders by some proportion c is always more effective than increasing the speed of the defenders by a factor of c. When there are few attacks (n = 5), α ≈ 0.8, but as n increases it drops to about 0.4 before leveling out, indicating a substantial decrease in the efficacy of increasing speed as compared to increasing the number of defenders. This general pattern holds true for both plotted cases (tmax = 15 and tmax = 25) but the drop-off is sharper when tmax = 15. Relationship of −α (y-axis) to number of attacks n (x-axis) from n = 5 to n = 40, uniform attack times, for two different values of tmax. For each value of n and each of T = 1000 random attack sequences, the value M(v) was computed for 50 linearly spaced values of v from 0 to 4 (not inclusive of 0), that is, v = 0.08, 0.16, …, 4.00, and the best-fit slope of the log-log plot extracted. (a) tmax = 15 (b) tmax = 25.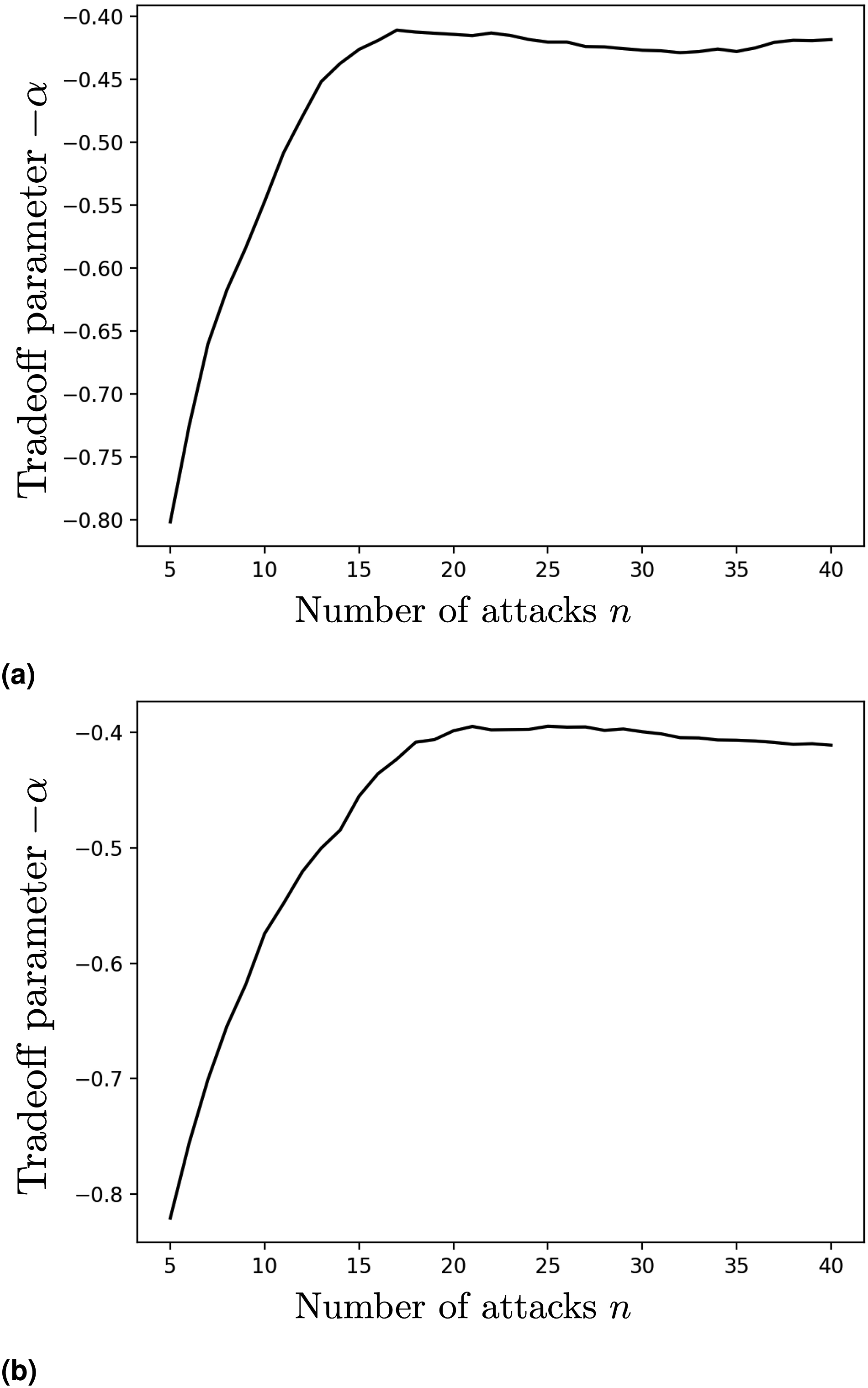
6.2. Simulations for heterogeneous defenders
We conduct simulations for each of the settings from Section 2. Our experiments are run as follows: 1. Generate attacks 2. Compute 3. Repeat the above for T trials and average the resulting values for each
We conduct all of our experiments on a circular perimeter of circumference 1, where the defenders are not permitted to leave the perimeter (so maximally distant points are at opposite ends and have distance 1/2). Comparison of the results sheds light on the conditions which favor heterogeneous defender teams and those which favor homogeneous teams and/or single super-defenders.
The structure of the simulations means each combination of defender speeds is evaluated on the same set of attack sequences, which makes the comparison fairer, and allows us to significantly speed up the computation when evaluating
Parameters of the experiments.
In Figure 6, we simulate sequences of n = 25 attacks of both settings, where the perimeter 2 defenders evaluated at g = 256 grains for speeds (vmin, vmax] = (0, 0.6] for 200 trials. Top row: 1 trial, front view. Middle row: 200 trials, front view. Bottom row: 200 trials, back view, showing the “ridge” at the center line v1 = v2 (both attack types). Left: Uniformly random attack times, n = 25, tmax = 25; Right: Fixed attack times, n = 25.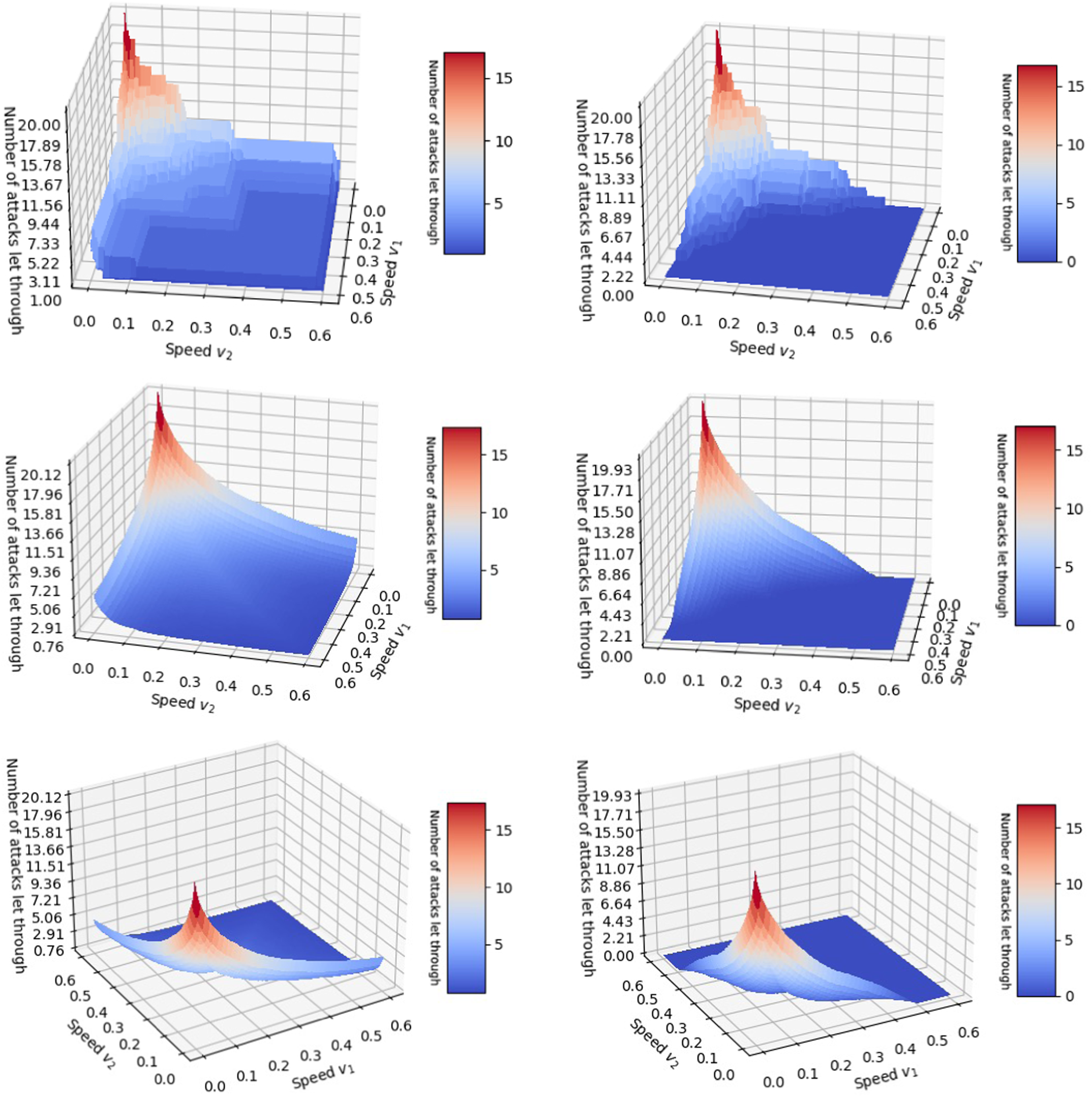
attack times; the right column shows results for fixed attack times.
The results are given as surface plots, taking defender speeds v1, v2 and returning Opt (v1, v2) (ignoring the assumption in the analysis that v1 ≥ v2, so the plots are symmetric about the line v1 = v2). We give: • •
From this we can make a number of interesting observations: • Opt (v1, v2) is generally larger for the uniformly random attack times, as attacks which are close together in time are much harder to defend. In particular, with fixed attack times Opt (v1, v2) = 0 for sufficiently large defender speeds (one defender of speed 1/2 is already sufficient to defend all attacks). • As mentioned, there is a ridge on v1 = v2 (the back view makes it clearly visible). This shows that on average, homogeneous defenders are less effective than well-designed heterogeneous ones. • Under uniformly random attack times, each “half” (cutting at the v1 = v2 line) is empirically convex, while under fixed attack times, each “half” is convex near the v1 = v2 ridge but becomes concave again near the edge of the plot (as seen in the back view) and as the defender speeds increase (as can be seen on the edge in both views).
We also consider the question: what is the optimal mix of defender speeds? To answer this, we need to consider what we want to hold constant, since obviously faster defenders are always better; an obvious starting point is to look at defenders of a fixed total speed, and consider what ratio of speeds performs the best. This also means that we are comparing defender teams whose reachable sets are of equal total size (ignoring overlaps), and (because we evaluate over a grid of possible values of
In Figure 7, we show the best (empirical) mixture: for each value of v
tot
= v1 + v2, the returned value is Empirical optimal ratio v2/v
tot
versus total speed v
tot
under uniformly random (left) and fixed (right) attack times, averaged for n = 25 attacks with tmax = 25 over 200 trials.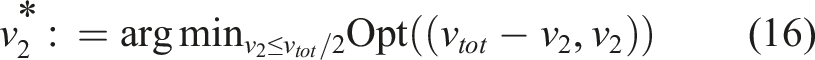
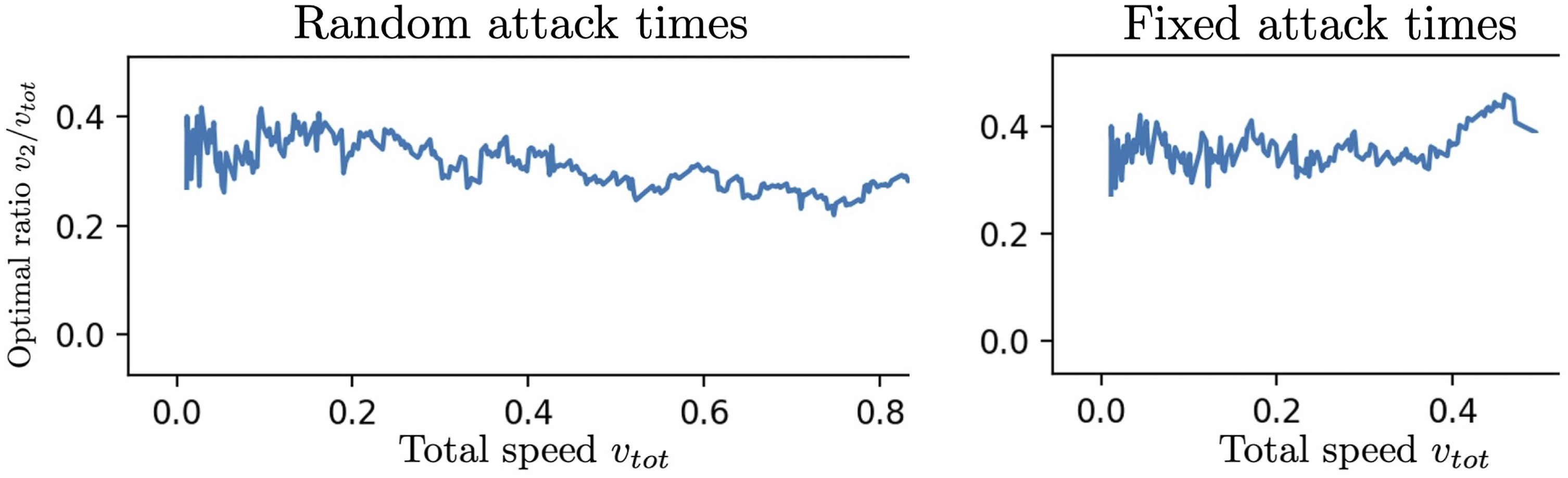
That is, given a total speed of v tot , what is the optimal fraction of the speed “budget” to assign to the slower defender? A value of 0.5 signifies homogeneous defenders are best; a value of 0.0 signifies that a single super-defender is best; and a value in between signify some heterogeneous mix of defenders is best.
These are based on the same experiments as shown in Figure 6. Note that the fixed attack times graph ends at v tot = 0.5; past that, both one single super defender and homogeneous defenders will defend perfectly, so measuring the minimum no longer makes sense. However, it is striking that the benefits of a heterogeneous team persist so close to that threshold, and the optimal ratio remains relatively stable over a wide range of speed “budgets” in both settings.
6.2.1. Computational complexity of simulations
The results of the monotonicity-based computational acceleration discussed in Section 4 can be seen in Figure 8, corresponding to the simulations shown in Figure 6. As before, the left-hand column is the results for uniformly random time attacks, and the right-hand column is the results for fixed-time attacks, while the top row represents a single trial (corresponding to the top row of Figure 8) and the bottom row correspond to the average of T = 200 trials. Monotonicity savings for the trials depicted in Figure 6. Uniformly random attack times on the left, and fixed attack times on the right. Axes labeled by position in the vector of possible speeds (0 to g − 1). Top row is for one trial (corresponding to the single trials shown in Figure 6) and bottom is average over 200 trials. Axes are labeled by grain number from 1 to 256 (linearly corresponding to speeds v1, v2 in Figure 6). Output in [0, 1] (depicted yellow to purple) denoting fraction of time Opt (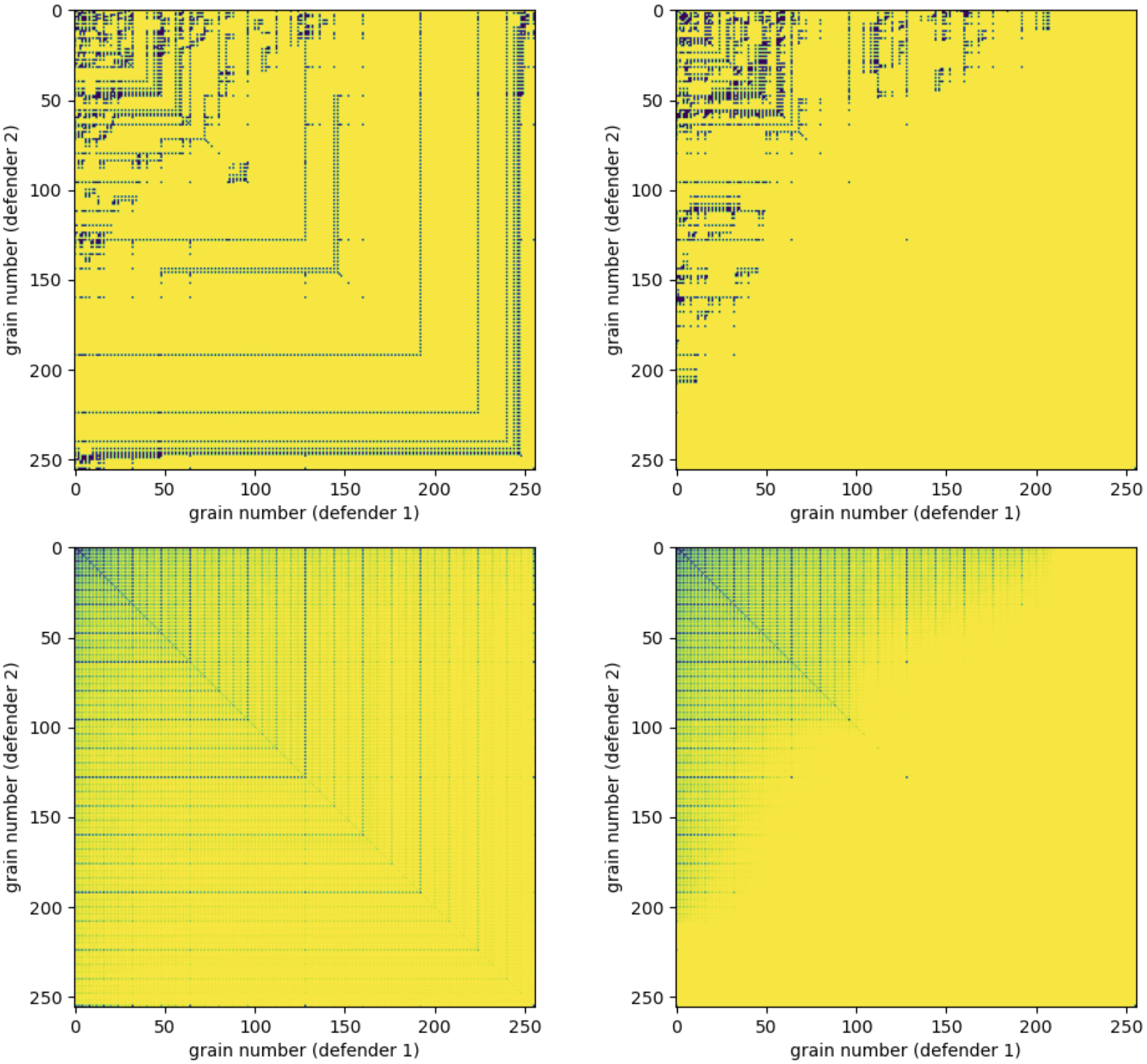
Each square is a 256 × 256 grid, representing the 2562 combinations of speeds
We note a few things: (i) the savings increase strongly where
Even with m = 2 and the strategic use of monotonicity, which can save up to about 95% of the running time, this can get big fairly quickly.
6.2.2. Simulations for unit horizon
Simulation results for the case of two defenders on a circular perimeter with unit horizon are shown in Figure 9. Note that in this case, heterogeneity is not beneficial, it is even detrimental. The optimal speed allocation is to assign the entire speed budget to one defender or split it equally. Unit-horizon case, 2 defenders evaluated at g = 128 grains for speeds (vmin, vmax] = (0, 0.5] for 10,000 trials and n = 25 attacks. Color bar corresponds to average of Opt(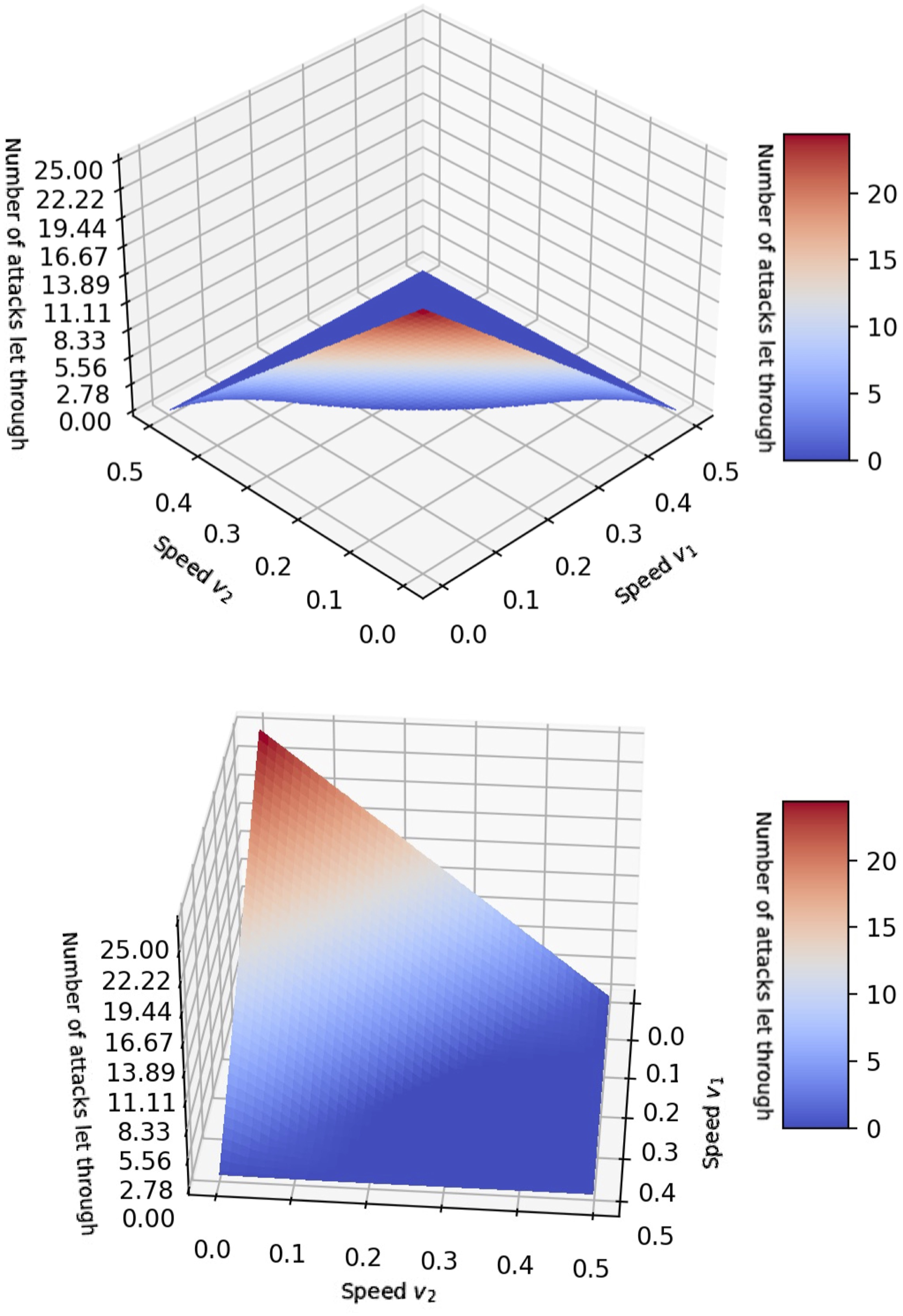
7. Conclusion
We introduced and studied a minimal model to map out how and why heterogeneity in robotic teams affects performance in perimeter defense applications.
In the case of homogeneous defenders, our results show a preference for a larger number of slower robots instead of a smaller number of quicker robots. The resulting multi-robot setting then raises the question if heterogeneity in the team composition is beneficial or detrimental. Thus, we also investigated the heterogeneous setting.
On the one hand, we showed that a heterogeneous team achieves better performance when full information of the oncoming attacks is available to the defenders. Moreover, we uncovered a seemingly universal behavior, where the ratio of optimal defender speeds is nearly constant for a range of problem parameters.
On the other hand, we proved that heterogeneity is detrimental to the system’s performance in the converse case where minimal attack information is available. These results suggest that heterogeneity is potentially a non-robust property, since less system information dramatically decreases its usefulness.
Future directions involve quantifying and studying the use of heterogeneity when intermediate levels of information are available to the defenders. This would explore the existence of a phase transition where heterogeneity changes from decreasing to improving system performance. Possible scenarios include varying the horizon length of incoming attacks between the cases of 1 and ∞ considered in the paper. Another scenario augments the unit-time horizon with the knowledge of the number of remaining attacks. In particular, we conjecture that even in this case defenders should always capture attacks if possible and that heterogeneity remains detrimental. Lastly, we wish to perform numerical simulations for a larger number of defenders.
Footnotes
Author’s note
Sukhatme holds concurrent appointments as a Professor at USC and as an Amazon Scholar. This paper describes work performed at USC and is not associated with Amazon.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by Army Research Laboratory.
Notes
Proof of Theorem 1
In this proof, for readability we denote i*≔i*(
Algorithm 1 depends on the function • V (0, …, 0) = n (the base case from which we recursively compute V); •
We then want to recursively compute V(
We can then ask: suppose j′ is the last attack that defender i* thwarts before thwarting
Proof of Proposition 1
Our setup is: the defenders are currently at a distance a and an attack comes in at x which can be reached by at least one of the defenders, after which N further (uniformly and randomly distributed) attacks will follow. We have two policies: f′, which declines to capture in this case, and f*, which follows the conjectured optimal strategy of always capturing, and always maximizing the distance between the defenders conditional on whether or not a capture is made.
We let Jf′(a; x; N) be the expected reward of following policy f′ from the given conditions (current separation a, attack at x, N attacks after that), and
We also assume that the current separation between the defenders (before deciding whether to thwart the current reachable attack) is a ≥ 2v2; this assumption is justified because by Proposition 2 in the main work, we know that all things equal we want to maximize separation (J is monotonic in a), and 2v2 separation can always be maintained even when capturing since the non-capturing defender can always maximize its distance to the current attack; even if the initial position of the defenders does not satisfy this, after 2 attacks it can always be achieved (even with captures).
We assume that 2v1 ≤ 1 and v1 + 3v2 ≤ 1 (otherwise by Theorem 2 from the main work it is possible to thwart all attacks no matter what, which by definition means the optimal policy thwarts the current attack).
Let sf′(i) and
Thus, the probability that the attack at step i is reachable (with the current attack considered step 0) is bounded by the above, and hence
Subtracting using these bounds, we get that
The extra “+1” comes from the fact that f* makes a capture at the current step, while f′ does not. Thus, we are done.
Note that the bound in the Proposition is not the best possible. We can sharpen it by noting that under f*, when a capture is not made, the union of the reachable sets on the next step is min (1, 2 (v1 + v2)) (maximizing separation without needing to capture allows the defenders to have non-intersecting reachable sets). We leave the improvements to future work.
Proof of Proposition 2
We next proceed with the proof of Proposition 2 in the main text.
The proof is by induction on the number of attacks N. We show (ii) together with the following additional properties:
(iii) For any N, J (a; N) is an increasing function of a;
We start with the base case N = 0. Note that given an initial defender distance a, the probability that the first attack can be defended is just the size of the union of the interval [−v1, v1] (where the faster defender can reach) with the interval [a − v2, a + v2] (where the slower defender can reach). We denote the size of this union as
Clearly, J (a; 0) ≤ s(a), with equality if (i) holds. Since s(a) is a monotonically increasing function for a ∈ [0, 1/2], (ii) holds. Clearly, J (a; 0) = s(a), so (iii) holds as well.
Next, we proceed with the induction step and show (ii). We make use of the following recursive formula:
Proof of Theorem 2
Analysis of cost minimization extension for homogeneous defenders
In Section 4, inspired by the work of Velhal et al. (2022),
7
we showed an extension of Algorithm 1 which both finds the minimum number M of defenders needed to intercept all the attacks and also finds the assignment of those M defenders to the n attacks
They also split their method into two parts: (a) Fixing the number (and origin) of the defenders, find the assignment of defenders to attacks which minimizes the fuel cost. This is done by formulating a Linear Sum Assignment Problem (LSAP, as given in [equation (10)-(10e), Velhal et al. (2022)]), which is then solved by known techniques. If no such solution exists, then it will find the cost-minimizing assignment that thwarts the maximum possible number of attacks. (b) Determine the minimum number of defenders needed to defend all attacks, which is done by analyzing the output of the LSAP and either adding defenders if there were undefended attacks or removing them if there were idle defenders in the optimal solution of the LSAP. This is given in [Algorithm 1, Velhal et al. (2022)].
In [Section 3.2, Velhal et al. (2022)], it is claimed that [Algorithm 1, Velhal et al. (2022)] computes the minimum number of defenders required to neutralize all the intruders. However, we believe that there are examples where [Algorithm 1, Velhal et al. (2022)] does not successfully find the minimum number of defenders.
First, it is asserted in [Algorithm 1, Velhal et al. (2022)] (lines 11-12) that “ • The perimeter is the square {(x, y): |x|, |y| ≤ 1}, with a defender reserve station at (0, 0). All defenders have speed 1. • 10 attacks occur at the following times and locations on the perimeter: 5 attacks at (0, 1) at times 2, 6, 10, 14, 18; and 5 attacks at (1, 0) at times 4, 8, 12, 16, 20.
To minimize the fuel cost for 2 defenders, one should be sent to (0, 1) (arriving at time 1) and wait there, neutralizing all attacks at that location; and the other to (1, 0) (also arriving at time 1 and neutralizing all attacks at that location). This yields a total cost of 2, and assigns each defender at least one task. However, the problem can be solved by one defender by alternating between (0, 1) and (1, 0) (requiring a total cost of
Additionally, it is claimed that if the optimal solution to the LSAP with m defenders leaves q attacks undefended, then the minimum number of defenders needed to defend all the attacks will be M = m + q; this is used in line 8 of [Algorithm 1, Velhal et al. (2022)]. This claim is substantiated by [Theorem 1, Velhal et al. (2022)], which asserts that adding another defender can only neutralize one additional attack, while all other undefended attacks remain infeasible.
However, a similar counterexample as above seems to show that this is not the case. Consider the above counterexample, but where the defenders have only speed 1/2 (sufficient to arrive at (0, 1) by time 2 from the reserve, but insufficient to traverse the
Therefore, it appears that [Algorithm 1, Velhal et al. (2022)] will not always find the minimum number of defenders.
Finally, however, we note that since the solution to the LSAP does indicate whether the problem is feasible for the given number of defenders, it is possible to use O (log n) calls of the LSAP to find the minimum number of defenders needed by using a binary search (thus taking a total of O (n3 log n) time).