Abstract
The escalating menace of online romance scams (ORS), exploiting human vulnerabilities and trust through social engineering, necessitates robust preventive strategies. This study pioneers the development of victim script, utilizing Crime Script Analysis to map the decision-making process of victims and highlight potential intervention points for preventing scams. Drawing from a prior comprehensive data set of verified victim testimonials, the research articulates a detailed victim script encompassing the entire trajectory of ORS—from initial encounters on digital platforms to the culmination of financial exploitation. By examining the correspondence between offender tactics and victim responses, this study identifies critical stages where interventions could effectively thwart scammers’ strategies. The findings advocate for enhanced awareness programs, rigorous platform security measures, and the empowerment of potential victims through educational outreach, aiming to curtail the financial and emotional damage inflicted by ORS.
Keywords
Introduction
Cybercrimes are increasingly concerning for individuals, businesses, law enforcement agencies, and governments (Wall, 2007), with large-scale cyberattacks exposing massive amounts of personal data becoming more frequent and severe (Dhaliwal, 2024). Among these offenses, Online Romance Scams (ORS) have emerged as a particularly damaging form of online fraud, inflicting substantial financial and psychological harm on victims worldwide (Cross, 2023; Wang and Topalli, 2023; Whitty, 2013, 2015; Whitty and Buchanan, 2012). Unlike other cybercrimes that rely primarily on advanced technology, ORS exploit human psychology through social engineering, with offenders creating fake personas to build trust and manipulate emotions to deceive and defraud victims (Kopp et al., 2016; Sorell and Whitty, 2019).
Given the seriousness of this crime, solutions must be developed to prevent the victimization of those at risk. One potential avenue for developing solutions for ORS is through the analysis of crime scripts (Leclerc, 2013). Crime scripts explicitly lay out the decisions an offender makes to prepare for and commit a crime and any choices made after the crime has been committed (Cornish, 1994). The utility of crime scripts lies in their ability to delineate intervention points to disrupt or prevent specific forms of crime from occurring (Cornish, 1994). Crime scripts have demonstrated their utility in understanding the decision-making of offenders for burglary (King-Parker et al., 2024), sexual abuse (Chopin and Beauregard, 2020), organized crime (Chainey and Alonso Berbotto, 2022), and intimate partner violence (Carney et al., 2024).
One common characteristic of these crime script analyses is that they are frequently developed from the offender’s perspective (Leclerc, 2017). This seems logical, considering that most prevention efforts target the offender (Berg and Schreck, 2022). Drawing on the routine activity perspective (Cohen and Felson, 1979), others have argued that scripts should also be constructed from the perspective of the victim and guardian (Leclerc, 2013, 2017). This is because understanding the decision-making of victims and guardians may shed light on additional intervention points to disrupt or prevent the offense from occurring.
The aim of this study is to develop a victim script that maps the decision-making process of individuals targeted by ORS. This script does not suggest that victims could have easily avoided deception or that they are responsible for their victimization. Instead, it seeks to identify points at which external interventions, awareness efforts, and support mechanisms could potentially disrupt scammers’ tactics.
The next section of this paper reviews the literature associated with ORS with an emphasis on the offender decision-making process. A discussion of crime scripts follows this review. The subsequent section then combines these two bodies of knowledge and presents the victim script for ORS. Potential intervention points and solutions for each step of the crime event process are discussed, and policy recommendations are offered.
Literature review
Online romance scams
The proliferation of Internet usage and technological advancements has introduced unprecedented convenience worldwide but also facilitated the rise of cybercrimes. Among these, ORS stand out due to their reliance on psychological manipulation rather than sophisticated technology. In a typical ORS, offenders create fictitious personas to win the trust of victims and exploit the fabricated relationship to commit fraud (Federal Bureau of Investigation (FBI), n.d.; Whitty, 2015). This form of cybercrime began to gain prominence around 2014 and saw a surge in the United States and globally by 2016 (Wang and Topalli, 2023; Whitty, 2015). Throughout the fraudulent process, romance scammers typically persuade victims to either transfer money directly to them or make upfront payments in exchange for promised emotional or financial gains. A study by Whitty (2015) delineates five primary stages in the operation of romance fraudsters: establishing the fake profile, grooming the victim, executing the scam, potentially engaging in sexual exploitation, and finally revealing the scam. Importantly, in some instances, victims have been unwittingly involved in money laundering activities, convinced by scammers to transfer funds or goods under false pretenses (e.g. Esoimeme, 2021; Huhn and Aten, 2023; Raza et al., 2020).
Research shows that victims of ORS often share sociodemographic and psychological characteristics that make them particularly vulnerable. Women are disproportionately targeted compared to men (Aborisade et al., 2024; Cross and Holt, 2023; Saad et al., 2018; Whitty, 2018), and victims typically range from 20 to 49 years old (Garrett, 2014; Lu et al., 2020; Saad et al., 2018; Whitty, 2018). While well-educated individuals from higher-income families and economically developed regions are frequently exposed to scams, findings are mixed regarding whether education and financial literacy enhance detection of fraudulent activities (Jiang, 2022; Saad et al., 2018; Whitty, 2018; Zhuang et al., 2022). Older individuals with lower educational attainment are particularly susceptible due to reduced digital literacy, limited awareness of cybercrime threats, and weaker scam detection capabilities (Cross and Holt, 2023; Garrett, 2014). Victims also commonly include individuals involved in financial markets or small businesses, whose active economic engagement may elevate their exposure to fraudulent schemes (Jiang, 2022; Lu et al., 2020). Psychological factors further heighten vulnerability, including a strong desire for romantic relationships, highly idealized beliefs about romance (Garrett, 2014; Whitty, 2019), impulsivity, urgency, sensation-seeking, trustfulness, and addictive dispositions (Buchanan and Whitty, 2014; Jiang, 2022; Whitty, 2018, 2019). High neuroticism, loneliness, and emotional dependence increase susceptibility to manipulation (Buchanan and Whitty, 2014), while prior scam experiences and low cyber-awareness further contribute to victimization (Cross and Holt, 2023; Garrett, 2014; Offei, 2021; Whitty, 2019). These findings suggest that although online romance scam victims are diverse, women, older adults with lower education levels, and individuals with limited technological literacy remain at higher risk, underscoring the need for targeted educational initiatives and multilingual cybersecurity awareness campaigns to effectively reach and protect vulnerable populations.
In some regions, particularly where English is not the primary language, ORS have developed culturally specific labels that reflect local nuances and operational practices. One example is the scheme commonly referred to as ‘pig butchering’, which originated primarily in Asian countries like China before spreading internationally (Faux, 2024; Newman and Burgess, 2024; Wang and Zhou, 2023). This form of fraud typically involves offenders befriending and dating individuals online to gain their trust before coercing them into fraudulent financial activities, such as counterfeit investment opportunities or gambling schemes. The distinguishing feature of this scam lies in its long-term grooming process aimed at extracting significant financial returns, metaphorically described as ‘fattening a pig before slaughter’ (Han and Button, 2025; Whittaker et al., 2024; Xie and Duan, 2025). While the term ‘pig butchering’ is widely used in law enforcement and media discourse, scholars have critiqued its dehumanizing connotations, noting that it emerged from offender subcultures and portrays victims as foolish and complicit (Whittaker et al., 2024). In 2024, INTERPOL similarly urged discontinuing this terminology, emphasizing that it stigmatizes victims and discourages reporting and access to support services. Furthermore, the term inadequately reflects the hybrid nature of these schemes, which combine elements of romance and investment fraud.
This example highlights that ORS can take different forms and names depending on cultural and regional contexts, yet their impact is consistently severe across jurisdictions. As of 2023, the Federal Trade Commission (FTC, 2024) reported 64,003 ORS incidents in the United States, with losses totaling US$1.4 billion and a median loss of $2,000 per victim. Similarly, UK data from the National Fraud Intelligence Bureau revealed 8,036 reports of romance scams amounting to £92 million in losses, while Canadian victims reported losses exceeding $41 million (CBC News, 2024; City of London Police, 2024). Beyond financial harm, victims endure significant psychological distress. Discovering the deception often results in trauma, self-blame, and long-term emotional damage (Aborisade et al., 2024; Buchanan and Whitty, 2014; Coluccia et al., 2020; Cross, 2020; Cross et al., 2018; Whitty, 2018; Whitty and Buchanan, 2016). Many victims report that the emotional impact surpasses financial losses, with some experiencing public or institutional blame (Cross, 2015; Meikle and Cross, 2024). Regardless of the magnitude and seriousness of this type of scam, there are limited practical and consistent initiatives from the government and private sectors to combat ORS (e.g. Cross et al., 2018; Whitty and Buchanan, 2016). Furthermore, existing scholarly attention has predominantly centered on utilizing victim data to produce victim vulnerability profiles or understand fraudsters’ operations and decision-making processes (e.g. Buchanan and Whitty, 2014; Wang and Topalli, 2023; Wang and Zhou, 2023; Whitty, 2013, 2015; Whitty and Buchanan, 2016). However, there is a gap in research related to understanding the victimization process for this offense. In an effort to fill this gap, building upon a previously developed offending model for ORS, this study seeks to utilize crime script analysis to create a victim script for this offense. This model aims to provide a comprehensive understanding of behavioral patterns, vulnerabilities, and essential decision-making processes implicated in both detecting and preventing ORS for victims.
Crime scripts
Scholars have long recognized that understanding offender decision-making is essential for preventing crime (Clarke and Cornish, 1985). Accordingly, researchers have sought to understand the decision-making process for a variety of types of offenders including burglars (Bennett and Wright, 1984), robbers (Wright and Decker, 1997), and car thieves (Cherbonneau and Copes, 2006). Several findings have emerged from this literature, such as an understanding of offender motivation, offender strategies for arrest avoidance, and situational and environmental cues used by offenders. These findings support many of the tenets of situational crime prevention (Cornish and Clarke, 2003) and led to the development of crime scripts (Cornish, 1994).
Borrowing from cognitive psychology, Cornish (1994) based the notion of crime scripts on schemas used to make decisions based on our previous behaviors and experiences (Augoustinos et al., 2006). Schemas contain knowledge about how to interact with others, the behaviors that are appropriate in specific settings, and steps required to complete tasks or solve problems. Event schemas, sometimes referred to as event scripts, contain the necessary steps required to complete tasks within a specific context (Baldassano et al., 2018). For example, if an individual wishes to withdraw cash from a bank, they must select a bank, choose the amount, drive to their bank, choose to use either the drive thru or enter the lobby, fill out a withdrawal slip, communicate with the teller, receive their cash, store it in their purse or wallet, and then leave the bank. Most of the steps in this process are likely to be automatic for us because we have performed them many times in the past with success.
Cornish (1994), recognizing the importance of event scripts for understanding criminal decision-making and crime events, appropriated them to map the sequence of steps required to complete a crime. Leclerc (2017) discusses the two main purposes of crime script analyses. First, crime scripts allow for the dissection of crime events into individual parts with a focus on the decision-making that occurs at each step. In this way, crime scripts not only help us understand how crime events are carried out, but they also offer insight into offender behavior during this process. Second, crime scripts help identify intervention points where efforts to prevent or disrupt crime events can be applied after being broken down into individual steps.
To demonstrate their utility, Cornish and Clarke (2003) presented a model script for committing residential burglary. The 10 steps in this model include preparation, entering the setting, precondition, target selection, initiation, continuation, completion, finishing up, post condition, and exiting the setting. Using this model, one can choose a particular step in the process, such as target selection, to focus preventive efforts. Installing CCTV and/or motion sensor lighting are examples of prevention efforts that could reduce the likelihood of burglary. In addition, crime scripts have been developed for many different types of crime including sex offenses (Chopin et al., 2023), human trafficking (Savona et al., 2013), terrorism (Williams et al., 2022), and online fraud (Lee, 2022). 1
The utility of crime scripts extends further than the offenders’ perspective. Routine activities theory asserts that crime events require the presence of a motivated offender, a suitable target, and the absence of capable guardianship at the same place and time (Cohen and Felson, 1979). Leclerc (2013) argues that script analysis can be conducted from the victim and guardian perspectives to maximize our ability to prevent or disrupt crime events. The general purpose of a victim script is to illustrate the actions individuals can take at each step of the crime commission process to avoid victimization. Guardian scripts outline the actions that can be taken to intervene at intervention points associated with specific crime events. The objective of these two types of scripts is to facilitate the avoidance of victimization and successful intervention.
A number of studies have examined crime events from the victim or guardian perspectives (Leclerc and Reynald, 2017; Smith, 2010, 2016; Tun and Birks, 2023). For instance, Tun and Birks (2023) demonstrated how natural language processing can be used to support the development of victim scripts for phone and online scams. Alternatively, Leclerc and Reynald (2017) offered a script for the guardianship intervention process with a specific focus on preventing or disrupting crime in public settings. The process in this script illustrates the steps required for guardians to effectively respond to crime events, ranging from being available to intervene to reporting the incident to law enforcement and/or other authorities. Within each stage of this model, the authors included specific techniques drawn from situational crime prevention that can be used by potential guardians to facilitate the disruption of crime. For example, at the ‘availability to intervene’ stage, the authors argue that the effort required by a guardian to intervene during a crime event can be reduced by designing public spaces in an aesthetically pleasing and accessible way to promote traffic and, by extension, guardianship.
With potential avenues for intervention or disruption of crime events perceptible from three perspectives, it is readily apparent how script research has become a useful prevention tool. One crime type yet to be fully examined through the lens of script analysis is ORS. As previously relayed, this offense has particularly serious consequences for victims’ financial and emotional well-being but has not received significant attention in terms of prevention efforts. Thus, the aim of this study is to develop a victim script to support the prevention of ORS.
Wang and Topalli’s online romance scam offender script
ORS have recently been examined from the offender’s perspective. 2 Specifically, Wang and Topalli (2023) used 52 detailed victim testimonials from five websites documenting ORS. These qualitative accounts offered insights into scammers’ tactics, victim interactions, and the progression of fraud, leading to the development of a crime script model that explains how offenders operate in ORS, based on victim testimonials. They identified five distinct stages in which scammers typically engage when attempting to deceive their victims: (1) initial encounter, (2) peak of relationship, (3) turning point, (4) relapse, and (5) moment of truth.
As Figure 1 presents, during the initial encounter stage, scammers use strategies such as matching with victims on dating platforms or initiating conversations, followed by asking them to move to private messaging apps, to entice victims to engage in conversations with them. This phase marks the very first interaction victims have with scammers, which can establish the groundwork for later deceptive scenarios. In the peak of the relationship phase, victims become further ensnared in the virtual relationship as scammers employ romantic or sexual language. These verbal interactions are intertwined with deceptive strategies where scammers impersonate themselves as wealthy, mature individuals working for prestigious companies. In some instances, scammers may send gifts to victims as ways to demonstrate ‘affection’ and the legitimacy of their identities. As trust and affection deepen, scammers initiate the turning point stage by fabricating crisis stories to ask victims for money, often under the pretense of arranging an in-person meeting. In rare cases, victims of ORS may also experience sexual exploitation during this stage, where scammers use explicit footage previously shared by victims or coerce them into performing live acts, both of which can be used to blackmail the victim. In most scenarios, after reaching this stage, victims come to realize they have been scammed and actively seek ways to extricate themselves. However, in certain cases, particularly for victims who are deeply entrenched in the relationship and refuse to escape even after recognizing the fraudulent nature of it, they may enter a cycle where they voluntarily return to the scam and experience it again until they finally grasp the true nature of the deception. In the final stage of an online romance scam, the moment of truth, victims strive to recover and move on using various approaches, while offenders exit the scam and vanish from the victims’ lives.
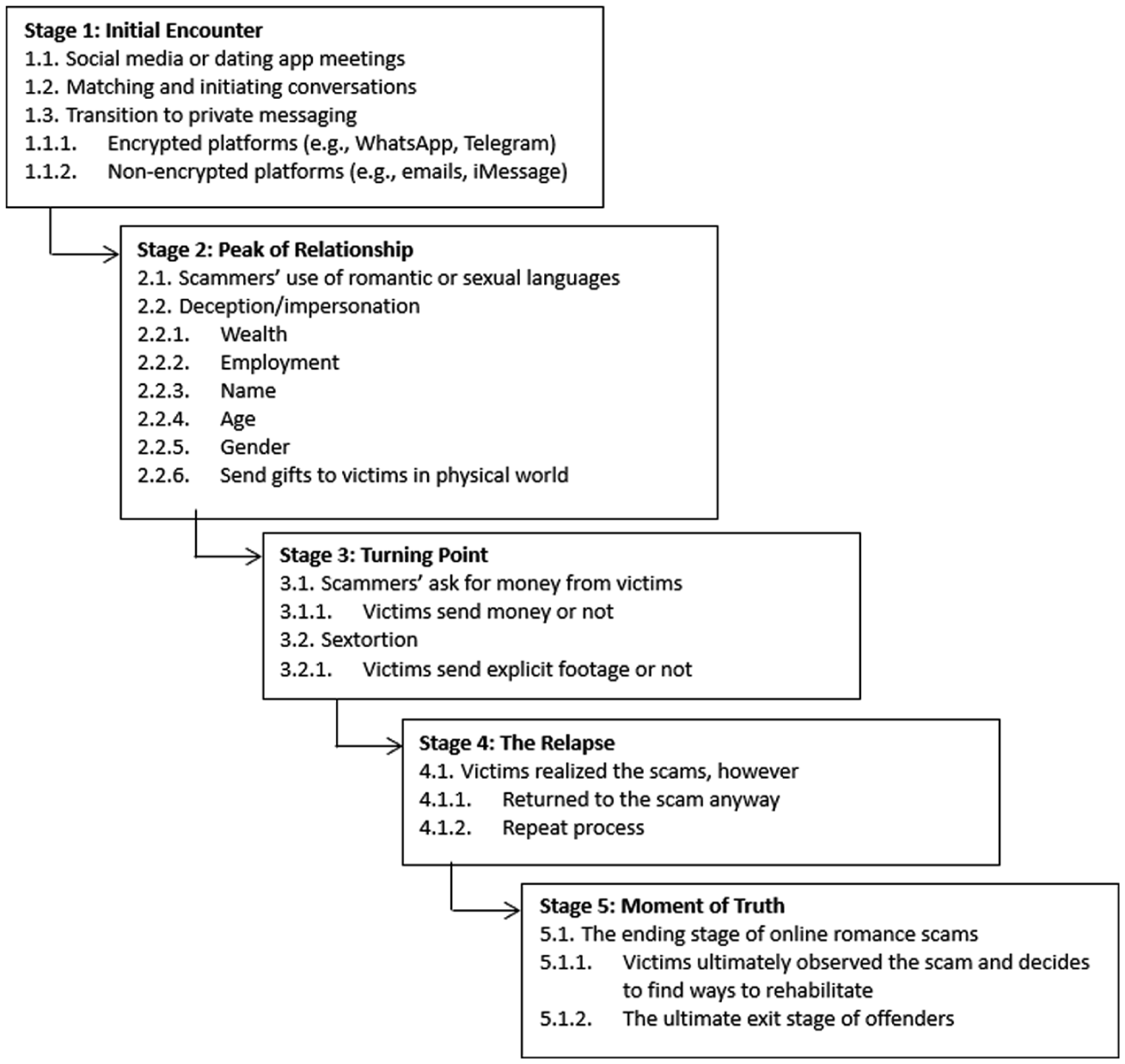
Online romance scam offender script.
The current study
Wang and Topalli (2023) and others (Whitty, 2013, 2015); have provided a substantial amount of information about offender decision-making as it relates to this specific form of cybercrime at a crucial stage in its evolution. However, no study of which we are aware, has developed scripts from the victims’ perspective for ORS. This study seeks to develop a victim script for ORS with a specific focus on how victims’ decisions can either protect themselves or facilitate the crime as they respond to offenders’ deceptive strategies across all five stages of the offense. Thus, this study marks the first attempt to address this limitation in existing literature, signaling a crucial step toward understanding and preventing ORS.
Method
This study utilizes a data set originally compiled for a prior analysis of offender decision-making in ORS (Wang and Topalli, 2023). While the same data set is employed, the focus of the current research differs substantially, as it aims to construct a victim-centered crime script that captures stages of victimization and interactional dynamics with offenders. To ensure this manuscript stands alone, we provide a detailed description of the data set, selection procedures, and analytical process specific to this study.
Data collection
In Wang and Topalli (2023)’s prior work, 52 victim testimonials were systematically gathered from multiple online platforms designed for sharing experiences of romance scams, including stop-scammers.com, male-scammers.com, romancescamsurvivor.org, scamwatch.gov.au, and manystories.com. These platforms were deliberately chosen because they contain extensive, detailed first-person accounts of romance scam victimization, often accompanied by supporting evidence such as screenshots, police reports, or financial records. The administrators of these sites actively moderate and verify submissions to ensure authenticity, which enhances the reliability of the data set.
For this study, we did not recollect these cases but re-examined the previously compiled data set specifically to analyze victim-centered interaction patterns. This reanalysis allowed us to shift the focus from offender-oriented modeling in the original study to constructing a detailed crime script that captures the victim experience and decision-making processes throughout the scam lifecycle.
Case selection and inclusion criteria
On stop-scammers.com and male-scammers.com, approximately 10,000 victim-submitted reports (about 5,000 per site) were identified. Due to resource constraints, a randomized sampling procedure was applied by selecting 100 pages (20% of total pages) from each site, resulting in 2,132 reviewed reports. Additional searches on scamwatch.gov.au and manystories.com yielded one comprehensive victim story from each platform, bringing the total number of reviewed reports to 2,134. From these, 52 testimonials met strict inclusion criteria: narratives had to contain sufficient detail covering multiple stages of victimization (initial scammer approach, offender characteristics, timing and methods of money requests, victim realization of the scam, and post-scam experiences). Reports with fewer than ten sentences, lacking narrative context, consisting only of scammer messages, or incomplete were excluded. The final data set included 32 female and 20 male victim accounts, with 16 cases (14 female, 4 male) from romancescamsurvivor.org, 34 cases (17 female, 15 male) from stop-scammers.com and male-scammers.com, and one case each from scamwatch.gov.au and manystories.com. Importantly, the data set does not have demographic or jurisdictional restrictions, as it draws from a large, diverse pool of publicly available reports. Many accounts are anonymous, making it impossible to ascertain victims’ demographics or locations unless voluntarily disclosed, which was not the case, nor was direct interviewing of victims conducted.
While this same data set was used in Wang and Topalli (2023), its role in the current analysis is conceptually distinct. The earlier study focused on offender tactics and decision-making, whereas this manuscript re-examines these 52 cases from a victim-centered perspective. Each case was revisited and recoded with specific attention to victim actions, emotional responses, and situational contexts that shaped their interactions with scammers. This analytical shift enabled the development of a novel victim-oriented crime script, highlighting decision points and the progression of victimization that were not addressed in the offender-focused framework of the prior study.
Coding and analytical procedure
To analyze the data, Wang and Topalli (2023) originally conducted thematic content analysis using NVivo qualitative software, independently coding each case to identify stages of victimization, emotional and cognitive responses, and behavioral decision points. In this study, we further validated and refined this coding process by re-examining all 52 cases. Both authors independently recoded the data, applying the same thematic framework while paying particular attention to victim-centered dynamics. Codes were iteratively refined through constant comparison across cases, and discrepancies were resolved through discussion until full consensus was achieved. This additional layer of recoding ensured consistency and enhanced reliability, allowing us to develop a novel victim-centered framework distinct from the offender-focused analysis in the earlier study and suitable for constructing the present crime script.
The victim script
Drawing on Wang and Topalli’s (2023) study, we propose a victim script for ORS (see Figure 2). Each stage mirrors those taken by the offender to facilitate a comparison between the two. Moreover, each decision point includes potential preventive actions that a would-be victim could take to prevent the scam from being successfully completed. Each stage of this offense is discussed below, with a particular emphasis on the victim decision-making process.
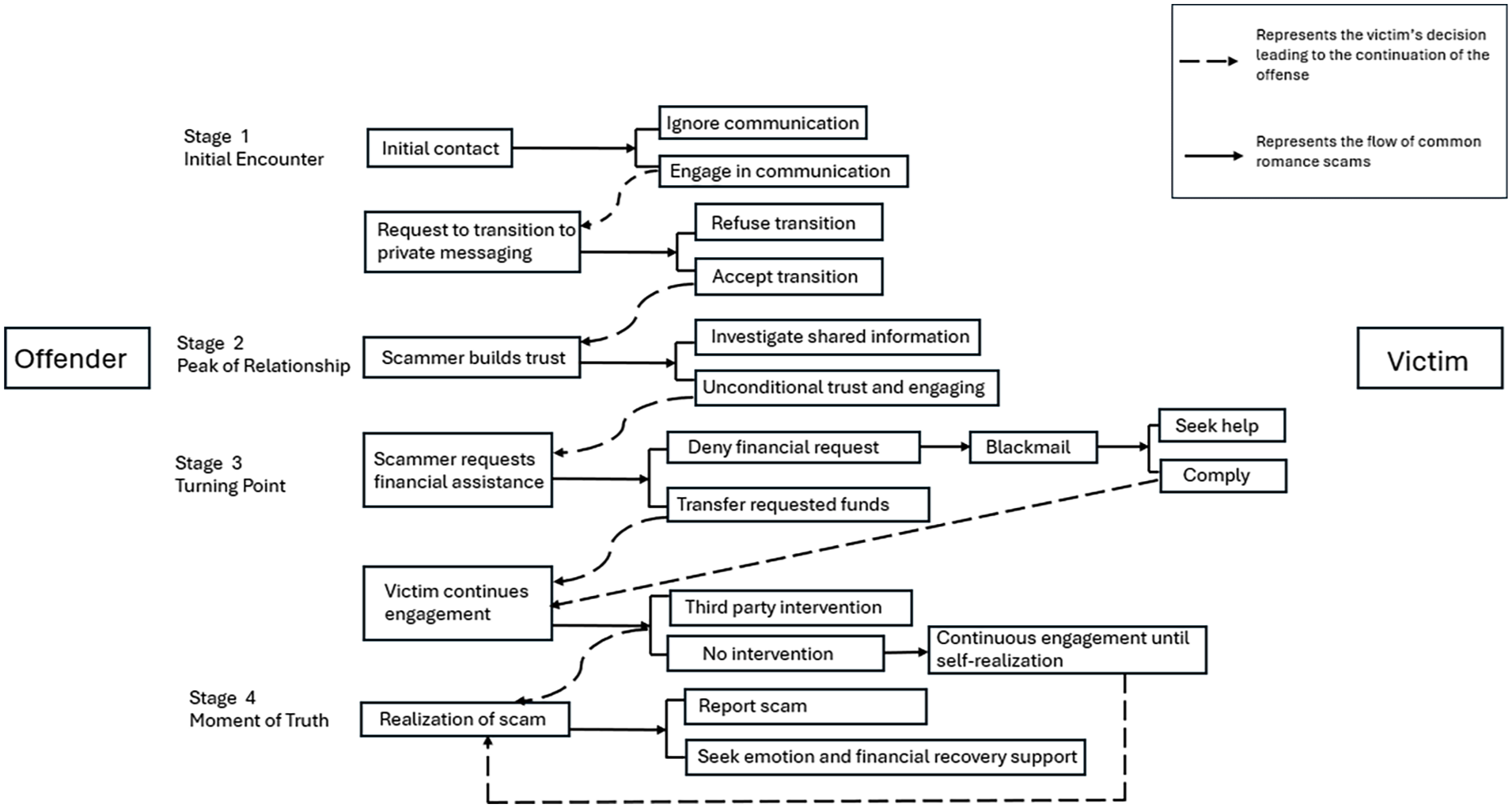
Online romance scams victim script.
Stage 1. Initial encounter
For an online romance scam to be carried out, potential victims must first use some form of online dating application or maintain a social media account. The more commonly used dating applications include Tinder, Bumble, Hinge, and OkCupid, while Facebook and Instagram remain the most widely used social media programs. As one victim recounted, On 10 May 2017, a man sent friend request to me on Facebook social networking . . . We chatted on Viber social networking because he wanted to close relationships with me. (Female victim-3) I found a beautiful woman on Filipina Cupid . . . We talked for a couple of weeks all the while I asked her to take selfies. (Male victim-10).
Once contact is established, scammers rapidly attempt to build familiarity by exploiting the victim’s interests and emotional vulnerabilities. They often do this by engaging with posts, commenting on personal updates, and mirroring hobbies or values: We shared details about our lives with each other and found we had a lot in common. I began to look forward to his messages more than I should have. (Female victim-7) Later in 2014 after a lot of correspondence and increasing intimacy and realizing we have a lot interests overlapped, I asked and believed Lisa was agreeable to her coming here and us meeting and seeing if we were compatible and it was worth moving forward with a relationship. (Male victim-3)
Once a scammer initiates contact, the potential victim can either engage with them or decline communication (see Figure 2). Engaging often facilitates the scam, while ignoring may prevent it. Victims frequently reported being asked early on to switch to private messaging services, a tactic used to isolate them and avoid platform monitoring. As one victim later reflected, And when he asked me to move from the app to WhatsApp, that should have raised red flags, as it is too quick. (Female victim-7)
This transition is a critical tactic, as it enables scammers to deepen trust and exert more influence, ultimately facilitating financial exploitation.
In many cases, as part of the initial encounter, a crucial part of this early manipulation involves stolen or fabricated images used to create appealing profiles. One female victim described her experience, After months of research with many reverse image tools, I have found the REAL MAN whose pictures were stolen or used. His name is Musa Hoti, a businessman from Kosovo living in Belgium. He first contacted me by private messages on Twitter . . . then via emails, and then on WhatsApp. (Female victim-25). This man sent me a friend request on Facebook in October 2019 under the name Sydney McCarthy. Two weeks after I accepted, he closed that account but still has 11 other Facebook pages under the same name Sydney McCarthy. (Female victim-27)
Stage 2. Peak of the relationship
Once initial communication is established, scammers escalate emotional intimacy to solidify the victim’s trust. This stage is characterized by frequent messaging, sharing personal stories, and sending numerous images or documents to make the fictitious identity appear authentic. For instance, We communicated almost for a month using the messenger service of Instagram. I was so happy, I was enjoying his attention, his words, all the things he was telling me that I haven’t heard in a very long time . . . We talked about many things, his family, the love for his granddaughter, etc. (Female victim-25) It was relentless morning, lunch, afternoon and late at night. I wondered how he could find this time as he was supposed to be building a railway bridge. We had frequent phone calls, Skype messages, and emails. It felt like we were truly building a real relationship despite the distance. (Female victim-2)
Scammers often describe elaborate careers, family circumstances, and shared values that resonate with their targets. Victims have reported feeling special, believing they had found someone who genuinely understood them. At this point, many described strong emotional attachment and anticipation of a future relationship: She (Jane Curtis) contacted me via my ad on match.com and left her phone number asking me to text her . . . she said she is a nurse in the military . . . she had a phone number from an .org area code but when she referred to military personnel she would call them ‘commander’, and the US Army does not have commanders. She also told me she might be getting deployed to Afghanistan and needed money to get a marriage certificate. (Male victim-17) Kelly is a sociopath that lies without skipping a beat. She said she was an only child and comes from a wealthy family of doctors and lawyers. She was quick to ask to be my girlfriend and I fell in love with her because she loved to cook and clean and she was very attentive to me and we seemed to have mutual understanding and feelings for each other. (Male victim-25).
At this stage of the offense, potential victims can (1) continue to communicate with the scammer or (2) pause and attempt to investigate them. Suspicion occasionally emerged when stories seemed inconsistent, but this realization was often delayed. This mind-set is reflected in the experience of Victim 5 from Story 5, who later recognized the warning signs: I felt bit weird about the fact he overly talks about the business he runs as soon as we started chatting (Now I know most scammers claim they’re self-employed), felt weird about the fact he types words very quickly (Now I know he was copying and pasting the template replies). (Female victim-5)
The illusion of intimacy was further reinforced through acts of apparent vulnerability, including stories of personal struggles or tragic past events designed to elicit sympathy. Victims described sharing their own secrets and receiving comforting responses, deepening the emotional bond.
Stage 3. Turning point
Having built trust, scammers gradually introduced requests for financial assistance. This turning point often involved carefully staged crises that portrayed the scammer as being in urgent need. Typical fabricated emergencies included medical bills, travel complications, or stalled business deals: She told me she was in Malaysia buying gold jewelry and the total value of the goods was AU$2.5 million. A while after she told me about her goods she said she needed some money to get the goods to Australia. It was $4,000 . . . She told me she needed some more money. I think it was another $2,000 for legal costs . . . Then she needed more, this time another $4,000. (Male victim-1) Five days later, I received an email from Windhoek Central Hospital, but it came from a Gmail account under the name of Dr. Johanna Kruger. The message said Dieter had been in a car accident, was unconscious in the hospital, and needed urgent surgery. They even phoned me, urging that I pay 13,000 rand to start the surgeries. On the same morning, Dr. Kruger called again, saying he was still unconscious, yet Dieter himself also messaged me on WhatsApp claiming he was in the hospital. (Female victim-28)
These scenarios are designed to evoke sympathy and urgency, compelling the victim to act quickly without questioning the legitimacy of the request (Wang and Topalli, 2023; Whitty, 2013, 2015). This presents another decision point for would-be victims of ORS. Specifically, they can (1) send money or (2) deny the request. The first path leads to the successful completion of the online romance scam by providing the offender with the money. The second route is denying the offender’s request for money.
In many cases, victims viewed these situations as temporary setbacks in an otherwise genuine relationship. Scammers reassured them with promises of repayment or future plans together. However, when victims hesitated or refused to send money, threats and coercion often followed, I said that if he did not pay me back my monies, I would go viral with the story and all of his pictures on YouTube. He hang up on me. Yesterday (17 March 2020) I received a WhatsApp message from him threatening me and reminding me that he knows where I live (he sent me flowers on two occasions). (Female victim-24) Every time I broke it off or threatened to terminate the relationship, she threatened to harm herself or suicide or to go ‘astray’ . . . When I broke it off recently, her ‘uncle’ emailed me . . . saying she cried all day and that I was her life. (Male victim-5)
This phase frequently involved deliberate isolation from friends and family. Offenders manipulated victims into believing outsiders could not understand their relationship: She started making me feel guilty for spending time with my friends and family. She would constantly tell me how lonely she felt and how I was the only person who truly cared about her. I believed her because she shared stories of her difficult past and how much she trusted me. Looking back, it was all lies to keep me close and away from others. (Male victim-13)
At this stage, some scammers also engaged in explicit image-based extortion. They either persuaded victims to share private images or used publicly available photos to fabricate compromising material for blackmail.
Finally constantly wanting pictures which I did a few times but stopped when she didn’t send me any or had excuses on why she couldn’t. (Male victim-4) He managed to trick me into letting him add me on Facebook . . . But then he dropped a Bomb and I will never forget the feeling and the violation I felt when I heard the words ‘if you don’t pay the money I want I’m going to post the semi nude pics of you. (Female victim-8)
Stage 4. The relapse
A subset of victims, even after suspecting deception, continued to engage with scammers due to strong emotional bonds or psychological dependence. This relapse often mirrored patterns of repeat victimization, where individuals struggled to fully disengage despite financial loss and evidence of fraud. Here, victims may immerse themselves further in the fabricated affection created by the fraudsters, continuing to send money to maintain the illusion of the relationship. Just as one male victim recounted, I was deeply in love with her, and even after realizing that she was lying to me, I kept going back to her messages. She apologized profusely, sent me more photos, and told me she really cared. I couldn’t let go. I sent more money just to keep the relationship alive, even though my family begged me to stop. (Male victim-10) I was scammed 2 years ago . . . My family told me it was a scam, but I believed everything he told me. I sent all my savings . . . It finished in January . . . One night the phone rang about 4am and they caught me out . . . Something strange happened a few months ago . . . a man through Facebook . . . I was really surprised as he looked like the same person . . . I never reply to these but I answered this . . . He said it was a terrible thing for anyone to do. (Female victim-6)
This behavior is analogous to drug addiction, wherein the victim’s dependency on the emotional high provided by the scam mirrors the compulsive nature of substance abuse. The victim’s need for emotional validation and connection drives them to ignore the reality of the deception, perpetuating a cycle of financial and emotional exploitation.
Stage 5. Moment of truth
The final stage of an online romance scam is characterized by the victim’s realization that they have been deceived. This stage of the offense marks the transition from deception to awareness (Wang and Topalli, 2023). As one victim reflected after the scam: I had never heard of romance scams, never knew they existed. Though plenty abounds in the local language and beyond, of finding a partner, of capturing a heart-throb. Had never entertained the thought of seeking a partner online, was never curious about such services, who would be interested in the profile of mine! Awoken to the world so severe, I was willing to be intrepid. And journey through this canyon? But I did. For the dangers, they were beyond my perception, well past my imagination. (Female victim-4. Given these warning signs, you are probably asking why I was so stupid to continue to keep in contact? And the answer is blind arrogance and the belief that I was something special to her. Pretty foolish in hindsight but that is something I have to live with . . . I now realise that I have been scammed. (Male victim-13)
At this stage, the offender often exits the scheme after having received the victim’s money. Once completed, victims are unable to prevent or disrupt the offense. However, they do have several options for reporting and support seeking.
I’m ashamed, betrayed, the sadness I felt is very hard to describe but no matter how bad I feel I’m starting to call the FTC, FBI, Western Union, SS, Equifax and other companies to file a complaint for what happened to me. (Female victim-11). Already been treated for depression taking meds and going to group therapy weekly . . . I go to my group therapy weekly, take my meds, attend church weekly . . . This cycle repeats and I’m told it’s part of my healing. (Male victim-2)
Despite initiating help-seeking efforts, particularly with law enforcement agencies, many victims explicitly reported encountering significant obstacles when trying to obtain assistance after realizing they had been defrauded. As victims described, After I figured out what had happened, I filed reports with the FBI, FTC, and local law enforcement. I even joined a legal support membership and consulted with attorneys. Despite all this, I am still $150,000 in debt and feel like there’s no real help out there. The whole process has been emotionally exhausting and I don’t know how I’ll ever recover financially. (Male victim-16). I personally went to my local FBI field office and talked to an agent, but he said the FBI doesn’t consider this type of swindle a crime, which floored me. How can I explain what happened as anything other than a crime? (Female victim-10)
These accounts highlight that even in the final stage, when victims have recognized the scam and actively seek help, they often do not receive immediate or effective assistance. Barriers such as law enforcement’s failure to recognize the offense as a crime, automated or dismissive responses, and delayed investigative actions further hinder victims’ ability to obtain timely support and justice.
Discussion
This study represents the first known attempt to construct a victim’s script for ORS. Using data from Wang and Topalli (2023), which examined offender decision-making, we developed a complementary script outlining victim decision points at each stage of the offense. These decision points mirror offender actions and either facilitate or disrupt the scam, offering multiple intervention opportunities. Importantly, they are not intended to place responsibility on victims but rather to highlight opportunities for support and protection in the face of deliberate, manipulative deception. The following section summarizes key stages of the offense and highlights actionable prevention and intervention strategies, followed by a discussion of study limitations and future research directions.
The initial encounter
All ORS require that victims have access to dating applications or social media. Those without such profiles are unlikely to experience these scams. Evidence suggests that reducing risky online activity can lower cybercrime victimization (Álvarez-García et al., 2016; Pratt et al., 2010). From an opportunity perspective, less time spent online reduces exposure to offenders (Kowalski et al., 2014).
More feasible prevention efforts could entail smaller behavioral changes on the part of application users. Two approaches are particularly relevant: limiting time spent online and exercising greater vigilance. Routine activities theory (Cohen and Felson, 1979) suggests that spending less time using social media and dating applications limits individuals’ exposure to offenders and reduces target suitability. There is ample evidence to suggest that limiting online activity can reduce the likelihood that one becomes a victim of a cybercrime (Álvarez-García et al., 2016; Pratt et al., 2010). However, limited use alone may not prevent scams if users still interact with potential offenders (Holt and Bossler, 2008; Marcum et al., 2010; Ybarra et al., 2007). Given that online platforms inherently encourage personal information sharing, feasible prevention must remain practical (Clarke, 1997).
The second approach to exercising greater vigilance online, is likely to be the more realistic (and probably more effective) of the two. Exercising vigilance might include limiting the amount of personal information shared with strangers online, which can generally reduce the risk of experiencing cybercrime (Reyns, 2010; Ybarra et al., 2007). Refraining from sharing phone numbers, physical and email addresses, employer information, location, and posting fewer photos would limit the publicly available information that scammers seek when engaging in target selection. This aligns with situational crime prevention (Clarke, 1997), particularly online access control and target concealment. Offenders often select profiles with more disclosed information, making fewer revealing profiles less attractive.
Another preventive measure is refusing requests to switch communication to less secure platforms, a tactic offenders use to evade detection (Wang and Topalli, 2023). Although framed as convenient or intimate, such switches increase vulnerability. Awareness campaigns should highlight these requests as red flags. Given the pattern exhibited by offenders to exploit targets online after this request is granted, it is essential that users of social media and online dating applications are informed about this practice as well as the consequences and vulnerability their decision can lead to. Public information campaigns designed to help online users recognize the suspicious and unusual nature of these requests would be well suited to support prevention efforts for this offense (Drew and Webster, 2024). For example, initiatives such as ‘Take 9’, which encourages users to pause before sharing information online (Take 9, n.d.), and Massachusetts’ ‘Pause, Verify, Report’ campaign (Massachusetts Office of the Comptroller, 2025) demonstrate effective approaches for educating users to verify interactions with strangers. Building on these models, platforms could implement in-app safety prompts that issue warnings when users receive suspicious messages, are asked to switch to less secure communication channels, or attempt to send money overseas (Cross and Lee, 2022; Drew and Webster, 2024). Delivering these timely alerts would help users recognize potential risks, disrupt offenders’ manipulation tactics, and discourage moving conversations outside the safety of the platform. Platforms could further mitigate risks by improving in-app messaging to reduce incentives to switch. Finally, reverse image search tools, such as Google Images (images.google.com), offer users a means to verify the authenticity of shared photos. 3
Peak of the relationship
In the next stage of the offense, often described as the peak of the relationship, victims typically engage in online communication with scammers, sometimes through less secure platforms. Offenders share personal information and photos to elicit emotional closeness and prepare for future exploitation (Wang and Topalli, 2023). Much of this information is fabricated, and many images are stolen or AI-generated. At this point, victims can either continue engaging or pause to investigate the authenticity of their online partner. Successful prevention depends on recognizing suspicious behaviors and red flags early, such as contradictory information, reluctance to meet in person, monetary requests, and emotionally dramatic narratives. Trusting intuition and acting on these warning signs can help prevent harm (Drew and Webster, 2024).
Verification is key to disrupting scams at this stage. Victims can check employment details through company websites, LinkedIn, or by contacting HR directly. In cases where gifts are received—a tactic documented in prior studies (Wang and Topalli, 2023; Whitty, 2013, 2015)—addresses can be verified via Google Maps or Zillow to confirm residential legitimacy and connections to the romantic partner. Open-Source reverse image search tools (e.g. Google Images) can also help identify stolen or fraudulent photos. While some users may spot AI-generated images due to unnatural features (the ‘uncanny valley’ effect) (Wang et al., 2015), studies show many cannot reliably distinguish them (Cooke et al., 2024). Researchers are developing detection methods (Baraheem et al., 2023), and platforms should deploy these tools to protect users (Ara et al., 2024). Awareness campaigns teaching visual cues of AI images (e.g. extra fingers, inconsistent textures) could further support prevention (Aljalabneh, 2024).
Certain groups, particularly older adults, face heightened risks. The FBI’s Internet Crime Complaint Center reported 6,740 elder fraud cases involving ORS in 2023, with $356,888,968 in losses, ranking third in frequency and fourth in financial impact (FBI, 2024). Older adults (55 +) are disproportionately victimized due to factors like loneliness, limited technological literacy, and financial stability (Andonellis, 2022; Judges et al., 2017; Sorell and Whitty, 2019). To mitigate risks, older individuals and their families should learn common scam tactics, monitor suspicious behavior, maintain open communication, adjust privacy settings, and regularly review financial accounts (Gradon, 2013; Leukfeldt and Jansen, 2019; Saridakis et al., 2016).
Finally, platforms can reduce scams through stronger user verification measures. Applying situational crime prevention’s principle of access control (Clarke, 1997), requiring photo ID verification would make creating fake profiles significantly more difficult, thereby limiting offenders’ ability to operate (Drew and Webster, 2024). These implications suggest that both individual and systemic prevention strategies are essential. At the individual level, improving victims’ access to investigative tools such as reverse image searches and their effective use can help potential victims detect inconsistencies in profiles earlier (Cross and Layt, 2022). At the systemic level, platforms can reduce scams through stronger verification measures (Cross and Lee, 2022). Applying situational crime prevention’s principle of access control (Clarke, 1997), requiring photo ID verification would make creating fake profiles more difficult, thereby limiting offenders’ ability to operate.
The turning point
Recall that the third stage of the online romance scam, the turning point, is one in which the offender has gained their target’s trust and is now fabricating crisis scenarios to elicit sympathy. Ultimately, the scammer will use this crisis to justify requests for money. Requests are framed within urgent, fabricated crises designed to pressure victims into immediate action. Potential victims can (1) comply with the offender and send money or (2) deny their request.
This is the most important decision point in the process of ORS. If the potential victim sends money to the scammer, the offense has been successfully completed and their ability to disrupt it diminishes almost completely. Thus, individuals should avoid sending money to others without first verifying the identity of the requester. This verification could begin by researching the requester’s name, photos, or details they have shared. Potential victims might look for additional red flag behavior such as inconsistencies in the request, heightened urgency, or a refusal to meet via video call. Those targeted by online romance scammers might seek input from trusted individuals and consult local authorities or consumer protection agencies. Similarly, payment applications could incorporate enhanced friction before international or large-value transfers by displaying verification prompts asking users to confirm whether they know and trust the recipient. Such in-app interventions at critical decision points could disrupt offenders’ manipulation tactics and provide immediate protection for potential victims.
In addition, to mitigate the risk of sextortion incidents within ORS, individuals should exercise caution when it comes to sharing intimate images or engaging in explicit activities during video calls with anyone online. It is important to recognize that the person on the other end may not always be who they think they are and consider that such content can easily be misused or manipulated. One potential method of reducing the likelihood of sextortion is to keep social media accounts private to prevent sextortionists from accessing your follower lists or personal pictures (Reyns, 2010). If social media profiles remain publicly accessible, scammers may use this information to threaten you by claiming they will send explicit images or videos to your followers and friends or use your face for illegal activities (Al Habsi et al., 2021).
In situations where victims have sent money to scammers and realized they were scammed after the fact, or if they are being blackmailed, it is imperative that they immediately report the incident to law enforcement (Cross, 2020). Reporting to law enforcement can initiate investigations that may stop the scammer from victimizing others. Law enforcement agencies are also equipped to handle such cases and can provide guidance on the next steps. They may also be able to track the scammer’s activities, potentially leading to recovery of lost funds. Furthermore, reporting scams helps authorities gather data to educate the public and prevent future scams.
Finally, victims of ORS should seek help and support from others, such as family and friends, rather than isolating themselves. By reaching out to others, victims can break free from the isolation imposed by the scammer (Jansen and Leukfeldt, 2018). This support can provide emotional relief as well as practical assistance in dealing with the scam. Family and friends can offer a supportive network to help the victim regain their sense of reality and self-worth, which are often eroded by the scammer’s manipulative tactics (Kaakinen et al., 2018).
The relapse
Relapse occurs when victims continue engagement even after recognizing signs of fraud, often due to emotional bonds or sustained psychological control. Psychological vulnerabilities, particularly loneliness and unmet emotional needs, play a significant role in this stage (e.g. Buchanan and Whitty, 2014). Offenders exploit these vulnerabilities to maintain influence over victims, making disengagement psychologically challenging even when deception is suspected. This phenomenon reflects trauma bonding and coercive manipulation similar to patterns observed in abusive relationships (Cross et al., 2018). Breaking free typically requires intervention from supportive networks and professional assistance, emphasizing that victim disengagement is not a simple matter of personal choice. External recognition and intervention are often essential in helping individuals disengage from the manipulative cycle created by online romance scammers (Meikle and Cross, 2024). Family members and friends can play a supportive role by offering understanding, encouragement, and resources that counteract the scammer’s psychological control. To provide effective assistance, it is important that these support networks are informed about the tactics used by scammers and the emotional trauma victims may experience (Cross et al., 2016). With this awareness, they can respond with empathy and constructive guidance, such as maintaining open, non-judgmental communication, offering emotional reassurance, and helping connect victims with professional counseling or specialized support services. These forms of assistance can strengthen resilience and aid recovery.
The moment of truth
During the final stage of realization, victims may feel shame or self-blame (Buchanan and Whitty, 2014). It is vital to stress that this self-blame is misplaced, as offenders exploit human trust and emotional needs. Post-victimization strategies should focus on recovery, support, and institutional resources to rebuild confidence and protect against future scams (Cross et al., 2016). An important first step is seeking assistance from law enforcement and financial institutions. In the United States, victims can file reports with the Internet Crime Complaint Center (IC3), 4 the Federal Trade Commission, 5 local police, or state consumer protection agencies. 6 Prompt reporting provides victims with official support and may increase the likelihood of recovering stolen funds (FBI, 2024).
Importantly, as highlighted by victims’ accounts, even after they recognize the scam and actively seek help, they often face significant obstacles in receiving timely assistance (Cross, 2020). Law enforcement agencies can play a crucial role in addressing this gap by improving victim support mechanisms (Maher et al., 2024). Strategies include providing specialized training for officers to better understand ORS, establishing dedicated cybercrime reporting units with faster response times, and ensuring that reports are not dismissed or treated as non-criminal matters (Cross, 2020; Dodge and Burruss, 2019). Agencies can also collaborate with financial institutions to streamline evidence collection and recovery processes, create victim liaison programs to guide individuals through reporting and investigations, and partner with community organizations to provide multilingual outreach and educational campaigns (Halpin and Todd, 2024). These systemic improvements would not only enhance victims’ experiences in the aftermath of scams but also strengthen prevention and early intervention efforts for future cases.
Further, victims should contact their bank or credit union as soon as possible to secure their accounts, request investigations into unauthorized transactions, and if possible, initiate chargebacks or wire transfer reversals (Reynolds, 2024). Providing documentation such as messages and transaction records can help with these efforts. Fraud alerts and credit monitoring may protect against unauthorized account openings or identity misuse (Cross et al., 2016).
Because these scams often cause significant emotional distress, psychological recovery is equally important. Professional counseling, therapy, and participation in support groups offer safe spaces for processing the experience and receiving validation from others with similar experiences (Cole, 2024). Engaging in self-care and building a supportive network of trusted friends and family can help rebuild confidence and emotional well-being (Cross et al., 2016).
Finally, resources on online safety can empower victims to feel more secure in online interactions (Drew and Webster, 2024). Educational programs, webinars, and information on scam tactics can help individuals recognize potential threats without implying fault for prior victimization. Practical safeguards, such as strong passwords, two-factor authentication, and regular account monitoring, can enhance security and peace of mind (Cross and Lee, 2022).
Limitations
There are a number of important limitations to consider for this study. First, this study only includes a victim script for ORS. Recall that Leclerc (2017) argued that crime scripts can be created from the perspective of the offender, victim, and guardian. This study does not include an offender or guardian script for this offense. A more holistic perspective for preventing ORS could be gleaned from scripts developed from all three perspectives. We chose to focus on the victim’s perspective in this study for several reasons. First, the bulk of the literature around crime scripts have been focused on the perspective of the offender with far less attention paid to victims (Dehghanniri and Borrion, 2021). This study is an attempt to fill that dearth in the literature and bring focus to the strategies and approaches that victims can take to protect themselves online. We hope that this study will be used to empower those at risk for experiencing an online romance scam. Second, constructing offender scripts for offenses often requires data collected from offenders who have engaged in the type of crime under consideration (Leclerc, 2017). We only have access to data collected from victims of this offense. Thus, it was not possible for us to create a crime script for ORS from the offender’s perspective. Third, for the purposes of prevention, it seemed more appropriate to develop a victim script for this offense because any recommendations that this study has yielded are more likely to be used by potential victims compared to potential guardians. Specifically, capable guardians for this offense would include social media and dating application creators, web developers, IT professionals, and online security engineers (Leclerc and Reynald, 2015; Reyns et al., 2016). We felt these individuals may not be as receptive to making changes to their platforms and applications as online users would be to changing their behavior and approaches to communicating with others online (Leclerc and Reynald, 2015). As a result, we believe the victim script has more utility for preventing ORS. Nonetheless, it is essential that researchers make efforts to develop crime scripts from the perspective of the offender and guardian for this offense so that more comprehensive prevention strategies can be created (Leclerc and Reynald, 2017). Future research that involves data collected from the offender and guardian perspectives would be well suited for this endeavor.
Second, it is well understood that offenders are constantly adapting to prevention efforts in terms of the methods they use to engage in different forms of crime (Ekblom, 1999). Cybercrimes, such as ORS, are no different. This means that any prevention efforts used, and strategies employed by offenders, should be continuously examined to determine their effectiveness. Offenders may change techniques for selecting and exploiting their targets, and prevention efforts should be updated to combat them. Relatedly, this study is an initial starting point for understanding ORS from the victim’s perspective. We have not evaluated whether the intervention points and strategies to disrupt the offense are effective. Future research should assess whether the approaches included in this study to prevent victimization are truly effective.
Finally, throughout this study, references have been made to the decisions and choices presented to those targeted by online romance scammers at each stage of the offense. These decisions only represent the potential actions that individuals may or may not take when targeted by offenders and should not be interpreted as victim blaming. It is important to recognize the serious emotional and financial consequences that victims of ORS face. The primary aim of this study was to gain a better understanding of the process by which individuals fall victim to ORS so that preventive efforts and potential intervention points could be developed. To achieve this aim, it was essential to outline the various ways in which a victim’s actions could facilitate or prevent the offense from being completed. Any blame for the offense transpiring should be placed where it belongs—squarely on the offender.
Despite these limitations, this study has contributed an additional crime script written from the victims’ perspective. This study demonstrates the utility of crime script analysis to identify methods for the prevention and disruption of a novel crime type, but also the importance of considering criminal offenses from the perspective of the victim. We hope this study encourages scholars to continue this line of inquiry for other crime types to support the successful prevention of other offenses.
Footnotes
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
