Abstract
Sextortion is the threat to distribute intimate, sexual materials unless a victim complies with particular demands. Cyber sextortion, specifically, takes advantage of the Internet’s anonymous nature and uses explicit personal images to inflict harm on victims. Despite this crime’s serious nature, there is a dearth of empirical knowledge of sextortion, particularly the process of fear management for the victims. This article employed a qualitative content analysis of the victim testimonials posted on the Reddit sextortion forum to explore the coping mechanisms of 175 cyber sextortion victims. Borrowed from the transactional model of stress and coping developed by Lazarus and Folkman, the characteristics of person–environment stimuli, ransom, appraisal and coping, revisit, and reappraisal were identified and revealed an extended model of fear and stress management applied particularly among sextortion victims. In addition, characteristics that are unique to female and male victims are also revealed in this analysis. In sum, the dynamic nature of fear and stress management among victims of sextortion implies specific crime control and prevention policies.
Keywords
Introduction
Cyber sextortion, a derivative from the words ‘sexual’ and ‘extortion’, represents a burgeoning online act of coercing victims by threatening to distribute their intimate or sexual images or recordings unless they satisfy the ransom requests. It represents a more sophisticated forms of extortion as offenders increase their sexual explorations on different social media platforms and the use of smart tablets (O’Malley and Holt, 2022). Whitty (2013) has highlighted that sextortion is occasionally used by a few online romance fraudsters as one of the approaches to financially blackmail victims. In cases where victims are unable to meet the fraudsters’ demands, they are coerced into performing sexual acts in front of a webcam, with the recorded footage subsequently utilized to extract further monetary gain from the victims. Despite the interconnected nature of these phenomena, cyber sextortion is slightly different from online romance scams; the purpose of sextortion can range from maintaining an intimate relationship to financial requests (e.g. Cross et al., 2023a, 2023b; O’Malley and Holt, 2022). Most importantly, what distinguishes sextortion from other types of image-based sexual abuse is the influence of the level of uncertainty that seriously torments victims, creating feeling of desperation, shame, and fear. Victims are perpetually uncertain about when and where their personal files will be distributed online. Consequently, offenders exploit this psychological vulnerability to exert control over and isolate their victims.
According to the 2023 report from the Federal Trade Commission Center in the United States, sextortion cases have undergone an exponential surge, escalating by over eightfold since 2019 (e.g. Fletcher, 2023). The Internet Crime Complaint Center has estimated that they have received over 18,000 sextortion-related complaints nationally (FBI Newark, 2022), resulting in more than US$13 million in 2021 (Campbell and Kravarik, 2022). Of particular concern is the significant representation of minors among the victims, with statistics indicating that 1 out of 4 victims were 13 years old or younger at the time of the threats (Thorn, 2017). Over the past year, law enforcement agencies have received over 7,000 reports related to online sextortion of minors (Department of Justice, 2023). In the United Kingdom, reports related to sextortion have experienced a 90% surge from 2020 to 2021, with male victims comprising 88% of the cases (Coker, 2022). Similarly, law enforcement in Canada has observed a sharp increase of nearly 300% in sextortion cases over the past decade, with a substantial rise occurring during the pandemic (Malone, 2022). This phenomenon is particularly prevalent among minors, and tragically, some of these cases have resulted in suicide (Nilsson et al., 2019).
Notably, sextortion is a transnational crime, involving victims not only in Western countries but also around Asian regions. China, for instance, experiences sextortion in two different forms. The first one is known as ‘nude chat scams’, wherein scammers impersonate attractive women or men and explicitly chat with male or female victims. The nude video calls are conducted on an app, where scammers can record the screen, retrieve the victim’s personal information using click baits, and use it to blackmail the victims (Wang et al., 2021). The second form is called Luo Dai, which translate into ‘nude loans’. In this scenario, financially desperate female college students would provide their nude pictures, holding their identification cards, to potential but illegal lenders. If they cannot pay the loan in time with usurious interests (approximately 30%), their nude pictures would be published online or sent to family members or used for other sexual purposes (Li et al., 2021; Liu and Keane, 2021). Despite increased attention from Chinese law enforcement, numerous individuals continue to fall victim to sextortion schemes, resulting in substantial financial losses. In one province alone, the police station recorded losses exceeding 24.7 million Chinese yuan (3.9 million US dollars) between December 2020 and January 2021(China Daily, 2023).
Despite the seriousness, there is a dearth of knowledge regarding the interplay between sextortion processes and the coping mechanisms employed by victims to mitigate the stress resulting from sextortion. Previous research on sextortion has primarily focused on understanding the complexity of this crime, such as the nature of the relationship and the location involved, as well as its prevalence and the impact on victims’ mental health (e.g. Cross et al., 2023a, 2023b; O’Malley and Holt, 2022; Patchin and Hinduja, 2020; Walsh and Tener, 2022). The detailed iteration of victims’ stress management experiences is often inadequately explored in relevant studies, typically situated within the broader framework of sextortion research.
As a result, given the aforementioned background, this study is of significant importance as it addresses a previous research gap by aiming to investigate the complex cognitive processes of sextortion victims, examining their appraisal and coping strategies in the face of cyber sextortion incidents. Utilizing Lazarus and Folkman’s (1984) framework, the research adds its depth through the inclusion of a substantial number of victim testimonials from a diverse online discussion forum, incorporating both female and male perspectives. The exploration of potential gender-based differences in responses throughout the sextortion experience contributes to an in-depth understanding of this phenomenon. Ultimately, the study’s findings, encompassing the initiation of sextortion, the dynamics of the ransom, victims’ appraisals, coping mechanisms, and subsequent reappraisals, provide a comprehensive model. Such observations are essential for crafting impactful awareness programs, implementing preventive measures, establishing robust support systems, and formulating legal responses to combat cyber sextortion and mitigate its impact on individuals within the digital landscape.
Sextortion
The literature on the topic of technology-facilitated sextortion has grown tremendously in recent years. The prevalence of sextortion has been the focus of a few research studies (Eaton et al., 2023; Patchin and Hinduja, 2018; Wittes et al., 2016; Wolak and Finkelhor, 2016). In the United States, Wolak and Finkelhor (2016) conducted a study involving 1,631 cyber sextortion victims, revealing that 46% of them were minors and 6% were adults aged 23–25 years. This finding aligns with that of Wittes et al. (2016), who reported that the majority of cases (71%) involved only minors. Among minor victims, Patchin and Hinduja (2018) found that 5% of students aged 12–17 years had experienced sextortion, and 3% admitted to having threatened to share explicit images of others. Notably, females were more frequently observed as victims, while males were more often the perpetrators (Wittes et al., 2016). However, Eaton et al. (2023) pointed out that men and young adults have increasingly became victims of sextortion, particularly during the pandemic.
In various notable investigations into sextortion, multiple studies have examined the characteristics of both the offense and the offenders (Cross et al., 2023b; Draucker and Martsolf, 2010; Kopecký, 2017; O’Malley et al., 2023; O’Malley and Holt, 2022; Wolak et al., 2018; Wolak and Finkelhor, 2016). Wolak and Finkelhor (2016) categorized sextortion into two primary groups: the first involves one partner threatening to disseminate explicit images after intimate relationships involving shared sexual images, often as a means of manipulation or embarrassment. The second group pertains to online perpetrators using sexual images, whether obtained from the victim or elsewhere, to coerce additional images or sexual acts. In the first category, a number of victims including minors reported that images were frequently used by their current or previous romantic partners as ways to force them to stay in an unwanted relationship (Draucker and Martsolf, 2010; O’Malley and Holt, 2022; Wolak et al., 2018; Wolak and Finkelhor, 2016). Offenders in the second category have been observed in several studies as primarily targeting minors and engaging in systematic patterns of sextortion (Kopecký, 2017; O’Malley et al., 2023; O’Malley and Holt, 2022). In these cases, offenders primarily seek sexual gratification rather than any financial gains. In sextortion cases involving non-minors, the majority of offenders did not personally know their victims but exhibited gender preferences, primarily with the aim of financial gain (Cross et al., 2023b; O’Malley and Holt, 2022). Regardless of the offender category, the transmission of explicit images plays a significant role in the extortion process (Wolak et al., 2018).
The study of sextortion victims has also garnered attention in several other scholarly works (Cross et al., 2023a; Nilsson et al., 2019; O’Malley, 2023; Walsh and Tener, 2022). The aftermath of sextortion is frequently linked to a range of adverse emotional experiences, such as shame, fear, and hopelessness, as well as suicidal behaviors (Nilsson et al., 2019). These emotional responses, classified as short-term impacts, are also corroborated by O’Malley (2023). In the study conducted by Walsh and Tener (2022), participants revealed that sextortion could be a profoundly transformative event in their lives, leading to persistent anxiety, the constant fear of potential retaliation, and subsequent effects on their mental well-being and interpersonal relationships. This sustained state of anxiety is referred to as the long-term impact of sextortion events (O’Malley, 2023). Notwithstanding these negative consequences, victims often convey that positive coping strategies and support from third parties can aid in their recovery over time (O’Malley, 2023; Walsh and Tener, 2022). Finally, Cross et al. (2023a) identified various behavioral factors, such as the loss of personal information and contact through social networking sites, as well as demographic factors, including being male and facing financial hardship, which are associated with the reporting of sextortion victimization and the resultant financial losses.
Collectively, most empirical research on sextortion has primarily centered around its prevalence and offending characteristics, with less emphasis on the experiences of victims, particularly their reactions to the extortion and threats, both during and after the sextortion incidents. Consequently, this study aims to address this gap by applying a well-established stress and coping model developed by Lazarus and Folkman (1984) to comprehend the evolving responses exhibited by victims throughout the entire sextortion process.
Model of stress and coping
To gain a deeper understanding of how people manage stress, Lazarus and Folkman’s (1984) transactional model of stress and coping suggests that stress is best understood as an ongoing process characterized by constant interactions and adaptations between the individual and their environment (see also Quine and Pahl, 1991). In essence, when individuals encounter specific stimuli in their environment, they tend to exhibit particular stress responses, such as coping mechanisms, which can be influenced by the mediating factor of appraisal. In this transactional model, Lazarus and Folkman (1984) propose a continuous cognitive appraisal involving three distinct processes that occur along the processes toward either a harmful or beneficial stress outcome, with each of these processes functioning as a distinct pathway. The first part of this process involves the primary appraisal of the stressor, which centers on prompting individuals to reflect on their needs that may influence their emotional responses. The second part comprises secondary appraisal, which involves recognizing that a particular situation is indeed stressful and leads individuals to assess the available resources for future coping strategies. These initial two-stage appraisals can guide individuals in developing coping strategies to regain control over initially perceived stressful situations. These coping strategies can be broadly categorized into emotion- and problem-focused approaches. Emotion-focused coping is typically employed by individuals who see the stressor as unmanageable due to limited resources, while those using problem-focused coping perceive the situation as more manageable and employ rational approaches (e.g. the use of different coping resources, materials, social or psychological) to address the issues at hand.
In general, researchers across various disciplines have applied the transactional model of stress and coping to explain the complex interplay between stress or stressors, appraisal processes, and coping strategies (e.g. Balneaves and Long, 1999; Gieselmann et al., 2020; Gowan et al., 1999; Green et al., 2005, 2010; Herman et al., 2020; Kelso et al., 2005; Quine and Pahl, 1991). Broadly, these studies have revealed that individuals’ interactions with their environments can shape their unique appraisals, subsequently influencing their choices of coping methods. Notably, these studies have also found that the presence of stressors, the availability of sufficient resources, and the appraisal of stressors can collectively impact the degree of stress experienced by individuals and their coping abilities, as seen in various contexts, including police officers (Ermasova et al., 2020), individuals facing involuntary job loss (Gowan et al., 1999), those afflicted by nightmares (Gieselmann et al., 2020), and siblings of individuals with schizophrenia (Avcıoğlu et al., 2019). Furthermore, the selection of coping mechanisms by individuals also plays a crucial role in influencing their overall well-being in managing stress (e.g. Green et al., 2005, 2010). Researchers have also examined how demographic and personality traits relate to individuals’ assessments of stressors and their choices of coping strategies (e.g. Adasi et al., 2020; Johnstone and Feeney, 2015; Leandro and Castillo, 2010; Quine and Pahl, 1991; Watson et al., 2011).
To date, only one empirical study has explored the coping strategies used by victims to address both short- and long-term consequences (O’Malley, 2023). Currently, there is no additional research seeking to dive deeper into the process of appraisal and coping selection among those sextortion victims. Consequently, this research seeks to bridge this gap by borrowing and further extending the model developed by Lazarus and Folkman (1984). The transactional model is considered a fitting framework for understanding sextortion. It offers an integral conceptual structure that views sextortion as an external event capable of inducing stress among victims. This, in turn, triggers their coping responses, helping them safeguard their reputations and personal images within their social circles, including their families and friends. Crucially, the model acknowledges that not everyone can effectively manage the stress, particularly those who tend to rely on emotions over rational thinking. This aligns with the typical reactions observed in a majority of sextortion victims. As such, this transactional model provides a valuable conceptual framework for advancing our comprehension of sextortion, with a specific emphasis on victimization appraisal and coping strategies in response to various stressors. Such insights can significantly contribute to the formulation of more effective policies and interventions in this context.
Data and method
This study uses a qualitative research approach to analyze the stress coping process for victims of sextortion. The current data sample is sourced from victims’ posts from Reddit, which serves as a prominent social news aggregation and discourse platform where individuals have the opportunity to express their views on a wide array of topics and phenomena while maintaining anonymity. It presently holds the distinction of being the largest and most influential online forum in the United States. In addition, it has been the subject of extensive interdisciplinary research, including notable studies within the realm of criminology (e.g. Chen and Tomblin, 2021; Curiskis et al., 2020; Letico et al., 2022; Mkono and Hughes, 2023). Admittedly, the use of online forum data can pose limitations with regard to potential representativeness and verification challenges arising from the anonymity of the contributors. Regardless, it provides the researcher with firsthand accounts and narratives from individuals who have experienced sextortion, offering valuable insights into their experiences, coping mechanisms, and perspectives. Most importantly, as Reddit is accessible to the general public without any encryption and particularly has the feature of being anonymous, thus when collecting this type of data (no images involved or recruitment of participants) from Reddit, there are minimal or barely any ethical concerns (e.g. Facca et al., 2020; Roberts, 2015; Wang and Topalli, 2022).
Significantly, the selection of qualitative analysis using online forum data is grounded in challenges associated with obtaining firsthand datasets directly from victims and offenders, as well as the limited availability of publicly accessible quantitative data. Victims who have experienced sextortion incidents may be hesitant to come forward or share their experiences due to fear, shame, or concerns about privacy. Moreover, the digital dimension of sextortion, typically occurring online, can add complexity to identify victims scattered across various online platforms. This reasoning is also extended to offenders, given the anonymity provided by the Internet and their apprehension about potential exposure to law enforcement. Research on sextortion encounters additional challenges when obtaining publicly available quantitative data. This difficulty may stem from privacy and ethical considerations associated with collecting and releasing quantitative data on such a sensitive topic. Furthermore, the dynamic nature of sextortion incidents poses a significant obstacle to providing real-time and comprehensive quantitative insights. Therefore, utilizing a qualitative approach to analyze victims’ experiences is the optimal choice for this study. It allows for the exploration of the distinctive aspects of each case and the in-depth information provided in victims’ testimonials, contributing to a comprehensive understanding of how individuals cope with stress in sextortion incidents.
Search strategy
To identify the most pertinent posts from victims on Reddit related to the issue of sextortion, the researcher initiated a search using the specific keyword ‘sextortion’ to locate the particular forum or community that exhibited the most comprehensive accounts of such incidents. Subsequent analysis revealed that over 50% of the search results were concentrated within a Reddit community known as ‘r/sextortion’. This community appeared to serve as a specialized platform where victims of sextortion shared their personal experiences and sought advice in the context of their unique sextortion situations. Therefore, this research selected ‘r/sextortion’ as the principal source for the extraction of analyzable narratives from victims. It is noteworthy that, among the various sextortion support groups on Reddit, this particular community stands out as the largest, boasting a total participation of 19,000 individuals.
Specifically, one of the special features of this community is that it provides a filter option which allows the user to search based on the genders of victims revealed by themselves. It is essential to emphasize that gender information is voluntarily provided by the victims themselves, and a relatively small proportion, approximately 15% of community users, opt to make such disclosures. Thus, based on this information, the researcher decided to incorporate all reports where users identified themselves as male or female victims in the preceding year, concluding in July 2023. One of the advantages for selecting reports using this filtering approach is to ensure that all included reports included a comprehensive account of the victimization cycle, as opposed to merely including posts where the victim’s gender remained unidentified, focusing on inquiries about sextortion, or posts aimed at raising awareness about preventing sextortion. Initially, the researcher was able to collect 250 reports from male victims and 68 reports from female victims. To incorporate reports that contain sufficient information to generate analysis, posts that contained fewer than 10 sentences or offered incomplete testimonials—such as those lacking essential details spanning from the initiation to the culmination of sextortion—were omitted from the dataset.
As a result, 146 male posts and 29 female posts were selected from the original sample (N = 318). As all posts on Reddit are anonymous, no demographic information can be accessed except the self-disclosed gender information. However, based on the incidental characteristics, this study is able to produce preliminary descriptive statistics relying on the aims of those sextortionists. Among female posts, 41% of them were asked to send pictures for sexual purposes, 1 while 24% were asked about sending money in exchange for explicit pictures or videos. Interestingly, 31% of females expressed that they did not know the actual purposes of those offenders as they simply were threatened to send out pictures, however did not know what to do to make this incident stop. For one particular case of 29 of them, a female experienced sextortion through her previous intimate partner. In contrast with the dynamic representations in female cases, the sextortion among males seemed to be more stagnated around asking for money to exchange for that footage (98%), with only two male cases having no specific aims.
The researcher named male posts as ‘MV-1’ to ‘MV-146’, while female posts were ‘FV-1’ to ‘FV-29’, respectively, to protect the online privacy of these victims to the greatest extent.
Analytical strategy
While a limited number of previous studies have employed quantitative methods to analyze sextortion, the absence of an accessible quantitative database leads the researcher to adopt an alternative approach. This study makes use of an openly available dataset found online and employs a qualitative research methodology to delve into the coping strategies of sextortion victims and the reasons behind their choices. As demonstrated in various studies, the qualitative approach holds significant merit, offering an opportunity to construct comprehensive narratives regarding individuals’ inner experiences within specific contexts, as well as uncovering nuanced aspects that may not be so obvious initially (see Bachman et al., 2015; Higgins, 2009; Wright et al., 2017). It is worth noting that the qualitative approach is a versatile and effective method utilized across multiple disciplines, including health, business, criminology, psychology, and more, consistently proving its efficacy in producing valuable research outcomes.
As a result, to effectively implement this approach in a rigorous fashion in this study, the researcher first organized those reports into an NVivo database. Following this, based on the model established by Lazarus and Folkman (1984), the author identified appropriate quotes that align with each theme. Subsequently, the author revisited the data to identify any additional themes unique to sextortion, focusing on the first 87 reports as they were sequentially arranged in NVivo. The remaining 87 reports were placed in a separate NVivo project. After identifying any new themes emerging from the first 87 reports that could complement the existing model, the researcher turned their attention to the other project containing the remaining 87 reports to determine if similar observations could be made. This process was followed by a comprehensive review to address any discrepancies or variations in relation to the themes and nodes stored in the distinct NVivo projects. Finally, once these additional thematic patterns were established, the researcher selected the most relevant quotes that resonated with the central idea of each identified theme.
Results
The results of this study involve a systematic analysis of victims’ narratives, accompanied by illustrative quotes for each identified theme. This approach allows a recognition of a five-stage process model, starting from the initial person–environment encounter (stage 1) and concluding with the subsequent stage of reappraisal (stage 5). The interconnectedness of these five stages contributes to a comprehensive understanding of how sextortion victims cope with stress, offering valuable insights for future research and prevention efforts.
Stage 1: person–environment encounter
Whitty (2013) highlighted that fraudsters in online romance scam use different strategies to contact victims. In sextortion scenarios, similar to romance fraud, offenders use techniques such as the establishment of a legitimate figure, inquiring about identifiable personal information, the exchange of intimate footage, the use of bribery and hacking to obtain intimate images of victims, or using relevant information to make threats in a later stage. Male and female individuals subjected to initial targeting exhibit distinct patterns of victimization strategies.
Male victims
Attempting to establish a trusted and legitimate figure reflects fraudsters’ aims in controlling or affecting the amount of reliability that victims can place on the fraudsters to not leak victims’ explicit footage in later stages. Such a process in sextortion involves deployment of a series of deceptive cues, such as the creation of legitimate accounts, non-suspicious conversations, and pictures and snaps/videos. Despite the type of platforms, fraudsters are described as using similar strategies to convince victims to trust them. All those activities assist in establishing trust which further facilitates the sextortion schemes. Some, like V-112 and V-59, recounted the legitimacy of fraudsters’ profiles from the number of followers and following and the snap scores, in their own words, ‘I saw this one girl requested me . . . She had like 1,000 followers and followed like 800, and the bio and pfp actually looked genuine’ (MV-112) and ‘It had a snap score of over 100k which led to believe it’s real’ (MV-59). Those offenders also are described as holding normal interactions with victims, for example, ‘wanting to call and having conversation’ (MV-118), ‘acting very cool and having a perfect grammar’ (MV-41), and ‘sending normal snaps’ (V-49). Most importantly, fraudsters also actively created commonalities between them and the potential victims by having a few similar followers from the victim’s side (i.e. their friends) (e.g. MV-132 and V-17) and fabricating going to the same college with the victim (e.g. MV-43 and MV-55).
Second, nearly all victims (female and male) narrated that fraudsters would ask for varied personal identified information, such as Instagram or Snapchat accounts, phone number, age, the school victims attended, and even their home address. For instance, MV-12 said, ‘I spoke to a women on a certain website of which she asked for my 9nstagram [sic], not snap, and once there she sent me her number telling me to call her’. Likewise, MV-106 also details how fraudsters ask for personal identifiable information from him, Within a few messages she asked for my phone number and me still being a little cautious only gave her a VOIP phone number . . . She ask for my name and I only gave her my first name, she also got the city I lived in.
From analyzing those victims’ self-reports, it is not hard to reason why fraudsters would ask for that information upfront—that is to use as potential leverage to further the sextortion scheme in its later stages. One victim in this sample of reports demonstrated that, ‘I now know why they want to move to Instagram, they can screenshot all my followers and use that to threaten me if I do not pay’ (MV-45).
After obtaining personal information, fraudsters would quickly turn into being intimate and persuade victims to send explicit sexual footage. Unlike the grooming stage in online romance scam, this process happened relatively quickly after sending a few non-sexual pictures back and forth. Nearly all victims narrated themselves as being controlled by ‘the peak of hormone’ and ‘irrationality’, even some of them did not want to send those pictures initially. This can be highlighted in the comments below.
MV-52: Moved sexually pretty quick, and my dumbass went along with it, showed me her boobs, and wanted to see my privates, which I did.
MV-106: She started sending me hot pictures of herself starting with clothes on and then with nothing on. I got really horny and lost all reasoning and within 20 minutes ‘she’ convinced me to send her a nude with my face showing.
MV-51: We started talking normal, she told me she was from Australia and she asked me for normal photos of myself . . . we kept talking and the conversation turned hot, ‘She’ asked me to send my nudes and I told her that after her and she agreed and sent me her nudes.
Interestingly, although all victims in this sample sent explicit images or video footages to fraudsters, a very few victims expressed that they were cautious when sending personal images to strangers as they only sent sexual images without their faces or sent in separate images. Despite this precautionary behavior, fraudsters still carry out sextortion, however in a different way, which will be further explained in the next section.
Female victims
In a similar fashion to the male sample, 11 out of the 30 female victims exhibited an exactly similar pre-ransom stage, starting from establishing trusted figures to persuading the sending of explicit pictures or videos. In these cases, sextortion came in when there was enough trust constructed through conversations between offenders and victims.
One of the major differences that distinguished the female and male samples was that female reports revealed a dynamic persuasive or deception technique deployed actively by offenders. It was absent from the male sample, but female victims reported that threatening was frequently carried out not just for the sake of the relationship, but rather when offenders used (1) money as bribery for nudes, (2) hacking, (3) impersonating, and/or (4) acquaintances as excuses.
When looking at the first female report, she revealed that she ‘was bribed with money on Discord’ (FV-1). The guy she was talking to has been ‘messaging me (her) for three weeks offering me thousands of dollars if I (she) showed myself (herself) on a video call with him’. Oddly enough, the extortionist in this case seemed to know or search about her family financial distress and pretended that she will get more money if she is willing to show more explicit pictures of herself. For the sake of money, the victim from the first report surrenders, leading to a cycle of sextortion. A similar experience was also revealed by a female victim in report 30.
Furthermore, five female victims in the sample wrote that their pictures and personal information were somehow stolen or leaked to malicious extortionists who may use ‘some kinds of hacking techniques’. In these circumstances, rather than voluntarily sending personal information and pictures under the influence of false pretenses, victims in this scenario were unaware of the leaking incidents until they got ransom messages. This is evident in the excerpt below.
FV-13: I work kinda publicly and the blackmailer claims he knows my work address or email, I can’t figure out which, but he actually said the place I lived and my family background.
FV-11: My cloud storage was hacked that’s how he got the data. My social media is dark as night, and I’m not searchable.
In addition, four additional female victims revealed that scammers impersonated them by using their faces to create random erotic Instagram pages or post on a porn site. For example, a victim said that ‘what happened is they edited my face onto some porn and got my IP address and was gonna leak it unless I sent them real nudes’ (FV-3). In this following case, offenders even used the impersonated Instagram page to make profits, ‘They had videos of me and they were posted to ph without consent (also I was 16 in said videos) and they made Instagram accounts pretending to be me and selling the videos via ig’ (FV-10). Impersonation occurred not only when fraudsters pretended to be the victims themselves, but also when they posed as individuals that the victims were searching for or as the victims’ close friends. The following quotes provide examples of this scenario.
FV-29: My family ran into some financial crisis and I went onto a sugar daddy website to find a sugar daddy, hoping to maybe find someone who could help me. Someone (A) texted me on there on early March, and we moved on to Telegram where we ‘discussed terms and conditions’, and from there, I send him pictures and videos where my face is very clearly visible.
FV-21: Some dude pretended to be my friend even though he was a mean piece of shit. He somehow gathered all my information from getting to know me and I guess he found my Facebook account . . . He doesn’t have my nudes though but he has my secrets.
Finally, a few female victims exposed that sextortion also happens between acquaintances. In particular, a ‘wicked’ ex-boyfriend is often said to initiate the ransom scenario by threatening to post girlfriends’ explicit pictures online. This is evident in three victims’ testimonials. Moreover, sextortion can also be carried out by a close family member (i.e. uncle), a familiar stranger met at a party, or someone living in the same town. For example, a female victim from report 16 said that I started getting flirty with my boyfriend, and then started sending him nude photos of me . . . Well I woke up and didn’t realize that I was sending the photos to my mom’s cousin/my uncle . . . Now my uncle is telling me I have to do what he says (sexual acts) or he’s going to expose me to our family.
Overall, this section highlights the methods employed by offenders to coerce victims into sharing explicit images. While the techniques applied to both female and male victims share similarities, there is a notable observation that the methods employed with female victims tend to be more dynamic. Moreover, although these techniques may not be as meticulously planned as those in online romance scams, which involve a longer grooming process, offenders nevertheless invest substantial resources in obtaining intimate images for the purpose of deception.
Stage 2: the ransom
During the second stage, as reported by victims in various accounts, offenders appear to leverage previously acquired intimate images or videos, employing various threatening tactics facilitated by a sense of urgency. Among data gathered from both male and female victims, ransom scenarios can be differentiated based on the presence of financial demands. Notably, financial requests were more prominent in cases involving male victims, while female victims were more likely to encounter non-financial requests, such as solicitation for additional personal or intimate imagery.
Male victims
Nearly all male victims demonstrated that there are always threats involving monetary requests. Fraudsters would send screenshots threatening victims that they have a list of victims’ followers or have located their close relatives. For example, MV-105 described that ‘scammer immediately created and IG group with all my friends and relatives and just blasted the photos but then asked for money’. Similarly, the fraudster in MV-126 was said to ‘text to my (the victim) phone number with threats and screenshots of messages typed out. They threatened to send to my friends and families on Fb if I did not pay in time’.
More specifically, some financial requests were consistently accompanied by the employment of various threats to intensify their intimidating impact. For example, eight victims wrote that fraudsters would compose a very similar picture collage containing the victim’s identifiable information (i.e. normal photos with their faces, social media usernames, phone numbers, and more) and the explicit pictures or recorded sexual videos they extorted. Among those victims who did not send sexual pictures without faces, fraudsters would find victims’ personal pictures on different social media platforms or request them from victims directly using excuses. Following this, they would continue to sextort victims by collaging victims’ faces and the pictures showing victims’ private parts. This technique is evident in the cases below.
MV-51: The scammer sent me a collage of my nudes and my normal photos of me that he had obtained from hoop and that I sent to ‘her’, the collage had my phone number my Instagram (Instagram) and my snapchat in the collage (the scammer knows my Instagram (Instagram) because I put my Instagram (Instagram) in a photo of my hoop).
MV-104: I got bombarded with a collage of my friends’ profiles on Instagram (Instagram) and got threatened; So, this person made a collage of my face and the pic of my peter (tbh one can argue that it isn’t mine).
In addition, two fraudsters in the sample also used a higher authority to escalate the urgency and increase fear among victims. MV-17 said that ‘she [the fraudster] sent a flyer with all my pics in a grid with a caption stating that she filed for sexual harassment and that the FBI already have it’. Similarly, the fraudster in MV-146 also used the same excuse by saying ‘they will leak my (the victim) images to the FBI and I am (the victim) going to prison’. By embedding the urgency of sending money into a higher authority context, fraudsters in sextortion schemes were intending to increase the perceived damage that leaking explicit images can have on victims, consequently multiplying fear.
Finally, instead of threatening to send it later if victims did not pay, some fraudsters attempted to probe the amount of compliance among victims by sending explicit images or videos to only a small number of their victims. This strategy can additionally be used to blackmail victims to send money if they want those pictures or videos to be unsent or deleted by fraudsters. For example, MV-64 wrote that ‘the scammer sent the images to people I followed on Instagram and telling me it was me. The scammer then told me it would unsend the messages for $400’. In the same way, victims in reports 65, 97, and 31 all demonstrated that fraudsters threatened to show screenshots to people close to the victims. While it is possible that fraudsters would actually do this, however, the victim from report 57 expressed that ‘she (the fraudster) send a photo of really shitty screenshot showing a hacking programe saying the emails were progressing (I knew that was fake bcuz of the shitty photo)’. As a result, it is likely that fraudsters may only use the photoshopped screenshot to intimidate victims into sending money.
Female victims
Evidence from female testimonials indicated a contrasting ransom scenario to that for male victims. There were only seven reports indicating that they had experienced a financial ransom scenario, so common in the male sample (e.g. FV-12 and FV-4). For example, one said, ‘They said they have the explicit pictures and threaten me to send my nudes and videos to my Instagram friends and family if I do not keep giving them money’ (FV-4).
In some cases, there was no explicit demand or more blackmail requests, but rather as victims said, more ‘indirect money requests’ and ‘intentional defamation’. In these scenarios, some fraudsters would threaten to send/post victims’ explicit pictures on social media platforms and escort/porn sites or family members. For example, a female victim said, He sends a message of a screen recording of my followers and following on ig, telling me if I don’t perform sexual favours for him on video, he will proceed to send the pictures and videos to those on my Instagram. (FV-8)
Other fraudsters impersonated the victims themselves and made social media accounts posting personal intimate images. For example, a female victim from testimonial 10 said, They had videos of me and they were posted to ph without consent (also I was 16 in said videos) and they made Instagram accounts pretending to be me and selling the videos via ig.
Moreover, another female victim experienced similar situation where the offenders Did not ask any money or pictures from me, but rather they impersonate as me on Instagram and send terrifying messages and nudes to my friends and family and telling them I am a sex worker. (FV-17)
The main purpose, as indicated in victims’ testimonials, was not yet to ask for monetary benefits but rather to ask for more intimate images and videos or demand victims perform more sexual acts in front of the webcam.
Female ransom scenarios also involved offenders claiming they only wanted to be with the victim or use their intimate images to perform sexual acts:
FV-18: He just said I want you to be with me and start a life together. So I did stay with him and I talked to him and I was trying to be nice even though I literally wanted to kill him.
FV-11: He sent me the pics back and said ‘they are for a friend of his, and they were jacking off together’(idk if it is true or sent them to me just to show me he actually has them) This grossed me out a lot. He then proceeded to call me by my real name.
Regardless, although some female victims reported that the threats did not entail explicit financial demands, however it is challenging to assert that this aspect was not part of the offender’s broader strategy. It remains plausible that financial demands might emerge in later stages of sextortion, as such details were not elucidated in victims’ accounts. In summary, the existing data emphasize the diversification of ransom scenarios employed by offenders when targeting both female and male victims.
Stage 3: the appraisal and coping
Lazarus and Folkman’s (1984) transactional theory of stress and coping underscores that individuals encounter specific environmental stimuli, triggering stress reactions influenced by the mediating role of appraisal. The qualitative observations in this section align with this model, demonstrating that both male and female victims exhibited dynamic responses to stressors based on environmental cues. This transactional process shapes their choice between problem- and emotion-focused coping strategies.
Male victims
First pathway: primary appraisal to emotion-focused coping strategy
In the male sample, 108 out of the 147 victims directly expressed that they immediately felt anxiety, stress, or had a panic attack after the presentation of ransom cues from fraudsters. MV-106 described his emotion as ‘I freaked out and just about had a hear [heart] attack realizing that all those pictures may go to my friends and family’. Similarly, MV-115 said in a similar way, ‘The first hours of being blackmailed was the worst of my life, I am stressed and embarrassed to kill myself, hands down, the only thing I can let it go away is to comply’. This is not to say that the other 38 individuals did not exhibit fear, but it was felt rather in an indirect way (‘I have no idea what to do’, ‘I cannot believe this happens to me’).
Among those who came up with a solution to deal with stressors immediately after the primary appraisal, some sent money to the offenders immediately because they feared losing their successful or peaceful lives if those explicit pictures or videos were to be revealed to their family, friends, and employees. Examples of this are presented below:
MV-106: I freaked out and just about had a heart attack realizing that if the pics ever got out to my family and workers I would lose my good paying job, family would never look me in the eyes the same again, I could get kicked out of the house and so on. I would face damages and missed opportuines (opportunities) equaling up the $200,000 between lost jobs etc (environmental cues).
MV-40: I’d like to think I’m a smart guy but I was in a state of panic I didn’t any any of my family or people from work to see and I didn’t want to lose my job or anything so I sent the money (environmental cues).
On the contrary, to deal with emotional stress, another group of victims chose to confess to their family members or friends to get emotional support. MV-122 recounted that I just feel so violated, but my mum’s been so supportive and told me that in the grand scheme of things, if it’s leaked it’s leaked and it’s a crime for them to do so, but also that people aren’t going to care in the long run.
Likewise, the victim in testimonial 89 also described his friend being ‘extremely supportive and patient with him’ even after ‘the fraudster has sent the picture to her inbox’.
In two particular cases, two victims from testimonials 45 and 106 expressed their fears toward these ransom events as even more tremendous because they came from a very conservative religious family and community. The following excerpts demonstrate their desperate mindsets when facing sexuality and the only thing that came to their minds was to do whatever they could to prevent the leak and preserve their reputations.
MV-45: I’m kicking myself for it, I have a pretty good reputation and am well liked in my church community, but I hide a dark secret of sex addiction, it would suck if these got leaked to people who I know from church . . . And to make matters worse literally mins after I got the first text from the scammer revealing they were a scammer I got a text from a parent saying a grandparent was in the hospital.
MV-106: I come from a religious family so something like this would be unacceptable and would detroy (destroy) me.
Consequently, victims who were driven by their primary appraisal ultimately chose an emotion-focused coping strategy, that was to send money to the fraudsters to distance themselves from this scam and ultimately hid this shameful incident from their friends and family. Victims’ presentation of such a vulnerable mentality further strengthens the fraudsters’ nerve in repeatedly asking for money by exerting accumulated fear on victims. They were also the most likely to experience the revisit stage, described below.
Second pathway: primary to secondary appraisal to problem-focused coping
In contrast, some individuals who initially felt panic still managed to calm down and make an assessment based on situational cues and were inclined not to send money to the offenders. This was when victims began to experience the secondary appraisal stage. Specifically, this group of victims began to further evaluate the situation and form problem-focused strategies based on their available objective and subjective resources. For example, the victim from report 35 narrated that ‘They then demand $100 or they’d post it. I said delete it, but then they posted their demands etc. and I immediately felt something was off and stopped responding’. Very few victims in the sample described in detail their transitional process from primary fear appraisal to the secondary evaluation stage, except those in testimonials 120 and 132. The victim in testimonial 132 described himself as initially panicking; however, he quickly calmed down and did the search and determined his plan to resolve the stress.
MV-120: I have bad anxiety and I panicked and sent about 800 to him (I know Im dimb but please dont harrass me for making this bad choice). After calming down, I realized that I should just ignore him as he was asking for more. He tried to text and call me in the few days after but I just ignored and finally decided to block him (situational cues).
MV-132: I panic, obviously. I genuinely did think about cooperating. I calm down, look up some stuff online, figure out my next moves, all while buying time. They claimed to be in the USA, I am in Europe. This helps with pretending not to know how to move money internationally. I figure out my plan, such as saying ‘I’ve already contacted the police, I told all my followers, and I don’t care if they see me’ (partially true, I don’t care if my friends see me I just don’t want my family to lol). Execute plan. I think (hope) the complete turnaround from blubbering and scared to confident and resistant made them think twice.
Importantly, three minors in this sample also revealed their helplessness with empty pockets and were not able to pay for fraudsters initially. It seems that they had intentions to send money to fraudsters; however, they still made an assessment of their financial status and the risks of ‘loaning money from others’ (MV-63) without consulting their parents.
In one particular scenario, 10 victims similarly expressed that they did not feel anxiety or stress at all because they neither showed their faces nor exposed their social media information to fraudsters. The following excepts demonstrated victims’ unwavering mentality when facing the threats from fraudsters as they did not have any hold over the victims:
MV-102: I did not panic as I did not even send one response because I gave no identifiable social media or no mention of my name.
MV-127: However, none of the content includes my face or voice, that’s good. Even they may be leaked to my family or friends, I do not need to admit or care.
In sum, this group of victims who went through a secondary appraisal undoubtedly chose a problem-focused coping strategy, in which they decided not to comply with the fraudsters’ requests but to figure out any possible solutions. In this case, the majority of victims chose proactive approaches to alleviate stress, for example, blocking fraudsters, deactivating accounts, changing usernames and profile pictures, or reporting to the authorities.
Female victims
Analysis of evidence collected from female victims reveals that, in a similar way to their male counterparts, they initially engaged in primary appraisal when processing incidental information. During this initial phase, female victims commonly experienced a series of negative emotions, including panic, negativity, and shame. In addition, the responses exhibited by female victims closely paralleled those observed in male victims, with these responses falling into two distinct categories. One group tended to adopt an emotion-focused approach to cope with their circumstances, while the other group progressed to the secondary appraisal stage, choosing problem-focused resolutions as a means of addressing the situation.
In the first group, the majority of female victims followed the pathway exhibiting a tendency to alleviate their stress either by ‘ignoring’ (FV-14, for example) the offenders because they found the stress and pain unbearable or by feeling ‘completely lost and unsure of what to do next’ (FV-29, for example). This group of individuals was inclined to keep engaging in conversations with the scammers out of fear that blocking or deleting them would anger the scammers and worsen the situation. Consequently, instead of reaching out to third parties for assistance, these female victims internalized their negative emotions, potentially increasing the level of stress they experienced and even leading to thoughts of suicide. Intriguingly, some of them who initially chose the emotional pathway ultimately calmed down and decided to either ‘report to police’ (FV-22) or ‘delete’ (FV-17) or ‘block’ (FV-4) those offenders after the threats intensified. In addition, a few others distanced themselves from these scamming incidents by sending whatever money was asked for by the scammers. One female victim said she had sent money on three different occasions to fraudsters just to avoid the ‘pain’ (FV-9) and ‘stress’ (FV-14) and ‘just want to get things settled’ (FV-13). Undoubtedly, these behaviors ultimately stopped once they realized the truth.
In the second group, a few more victims who initially walked through the primary appraisal stage eventually chose a problem-focused strategy. Those strategies covered not only self-help but also seeking support from outside assistance (i.e. family members, friends, law enforcement, or social organizations). Although victims expressed in their reports that they still constantly experienced fear, stress, and anxiety, they believed that ‘it will hopefully go away as time passes by and with situations get controlled’. The following excerpts demonstrate such an aspect:
FV-1: Anyway, so far although panic, I have ghosted (not blocked) him and screenshotted all evidence, reported all his accounts and got him banned from the servers.
FV-24: I am going to my local police tonight to file a report. I also spoke to the Cyber Civil Rights group and got some resources too . . . I then proceed blocking him and end our conversation.
Overall, this section underscores the pivotal role of victims’ perception of personal control in shaping their compliance during sextortion. Those who initially experienced panic but subsequently engaged in rational thinking or sought external support, such as from family and friends, had less tendency to send ransoms to the fraudsters. In addition, the extent of personal control was reflected in whether victims disclosed identifiable or traceable personal information, such as faces, voices, or social media details. Individuals who reported a stronger sense of personal control, whether physical or psychological, were less inclined to yield to the fraudsters’ demands.
Stage 4: revisit
In this current dataset, there are reports from victims who explicitly indicated that they underwent the revisit stage. More specifically, those who complied with the initial monetary request were likely to experience the revisit stage forcibly due to the extortionists being prone to instigating a second or further round of requests by asking for more money. Those victims said that offenders would directly call or text, threatening them about leaking explicit pictures to friends, followers, or family members. There were in total eight victims who sent money on two or more scam scenarios created by the offenders. Intriguing enough, and different from the prior stage, more offenders at this stage tended to carry out their actions (e.g. typically sent to one or two persons as a test) if the victim expressed incredulity toward the threat. For example, a female victim said that, ‘One time I didn’t listen to his orders and he dmed my cousin with my real nudes . . . I had to comply to prevent more of this happening to my other family members’. (FV-12). Similarly, a male victim wrote that, ‘They threatened me to send the photos to the followers by showing me a collage and asked for 100$ . . . finally I sent $50 gift card hoping to end it’ (MV-84).
In some cases, offenders would deceive victims by using crisis scenarios to impose threats other than the sextortion ones. For example, they might use law enforcement agencies to threaten victims to pay more because of the unpaid ransom or those sexual pictures they sent. In MV-146, for example, the victim wrote that Then this morning they come back in my google chat with a new email that says something like fbi assist collective but while I’ve never been in a conversation with an officer they kept trying to blackmail with the account that says fbi like at least try to trick me into thinking your fbi but then again this wasn’t the first time.
Alternatively, the victim in MV-94 said, ‘They said they were connected with the police and INTERPOL (obviously fake claims) and told me nothing would happen if I followed their demands’. By using pressure from the authority, offenders attempted to exert additional fear onto the victim and force them to pay consecutively. Moreover, an offender from female report 29 pretended to be four different persons asking money from the victim with different excuses. Using a quote from this report, (A) texted me on there on early March, and we moved on to Telegram . . . I send him pictures and videos where my face is very clearly visible. After, he turned on me, and (B) texted me saying that he was about to leak all of them. B then gave me one more contact (C), claiming C is a victim of A and would tell me how to stop A . . . A first asked me to transfer him >$1k, I did . . . then (D) messaged me, saying B is now the one threatening to leak my pictures/video, and B started asking for $500 again . . . I transferred the $500. I do not believe they actually deleted those pictures. Especially since B was ‘so kind’ to try and help me stop ‘A’, but then became the one blackmailing me. Also, ‘A’ and ‘B’ used the same online bank account.
When facing continuous threats, the majority of victims in this group who were initially driven by the primary appraisal (e.g. anxiety, stress, and depression) and chose to initially send out money would gradually transit their mentalities into believing that ‘no matter what I do they are always going to hang it over my head and ask more money’ (MV-111). As a result, they began to reevaluate their situations by thinking more clearly and decided not to send ‘a single dime’ to offenders no matter what kinds of threats they posed. They developed more proactive problem-focused coping strategies to deal with the stress (i.e. block, ignore; seek help from close relatives, friends, or law enforcement). Such a change of attitude also occurred among those victims who sent money to scammers on two or more occasions.
Regardless, there was still a group of victims who were manipulated by their emotions and were scared to instigate the offenders. Very few male and female victims expressed their reluctance to either send the money or block those extortionists. Therefore, they decided to seek help and suggestions from the online forum (i.e. Reddit). Although they had not sent the money in the second-round yet, their mentalities seemed extremely fragile. In their posts, they demonstrated that ‘but they asked for more money and i don’t know what to do’ (MV-80); ‘They keep asking for more money. I want to block them but I’m afraid if I do they’ll leak the photos. What should I do next in this situation?’ (MV-59).
A small number of them attempted to negotiate the time and amount to pay; however, they were not sure if they needed to fulfill offenders’ monetary requests or block them and deactivate the accounts. In this group, three victims appeared to exhibit heightened stress and anxiety and planned to send money to those offenders again, but had not done so yet as they suspected that offenders would ‘actually send those bad and embarrassing videos to my friends and family’ (MV-143). Three of them expressed that ‘I cannot afford to let people around me see those pictures and videos. I am thinking about sending them money however was not sure if that is the right thing to do’ (MV-60). However, there was still one female victim who surrendered and continued to send the fraudsters money on four separate occasions even after the scammer ghosted her for 2 months and then came back asking for more.
Finally, two other victims asked if they should present somewhat sympathetic behaviors (i.e. suicide) to force offenders to give up passively. One victim from MV-3 tried to fake suicide and death to disconnect with offenders, and he said, ‘So should I send him the money or say I killed myself. Or should I send him the money and then say I killed myself??’ Separately from this case, the victim from MV-12 played the ‘underage’ card and kept begging offenders to give up this deal by saying that ‘I didn’t have any ID, nor the money he was asking for, and no Internet access’.
Stage 5: reappraisal
The final stage of reappraisal involves individuals engaging in personal reflections on the entire incident. Cognitive reappraisal entails individuals taking a step back and objectively reevaluating the provoking incident (Juang et al., 2016; Troy et al., 2010). In this study, since the data primarily rely on self-reports and notably lack substantial follow-up posts by victims, only a few individuals explicitly stated their reappraisal process. This scarcity of reappraisal reports by female victims may be attributed to the comparatively lower number of reports submitted by them. Specifically, there were only two reports in which female victims wrote about their reflections on the events they experienced, while 15 males provided their reflections and suggestions for individuals who might potentially encounter any forms of sextortion in the future.
When engaging in reappraisal of their situations, female victims tended to adopt a more passive tone and often engaged in self-blame for the problems they had encountered. For instance, a female victim from report 1 expressed, ‘I think the worst thing is just the guilt. He called me a slut and stuck-up bitch. And I feel like he’s right, and it’s so hurtful’ (FV-1). Although she acknowledged that she had ‘learned my lesson and won’t be showing strangers photos anymore’, her predominant mindset still involved self-blame for her actions that contributed to the sextortion. Similarly, a female victim from report 26 shared an identical reflection, labeling herself as an ‘idiot’ and stating, ‘I did not know if anything can be done about it on my end as I sent the picture first’, before concluding with a hope that her experience might serve as ‘a cautionary tale to young girls so they do not end up in my shoes’.
On the other hand, male victims who did express their reappraisals often conveyed a more assertive, proactive, and optimistic tone. For instance, a male victim from report 87 stated, ‘I acknowledge that things are shit at first but definitely get better . . . realised that they prey on your fear of social stigma to get you to pay up . . . do not felt guilt’. Or a victim from report 76 expressed that, ‘from everything I’ve seen, they’re the real deal when it comes to busting these fuckers. Hope I did the right thing because this dude deserves to be put behind bars’. Similar sentiments were clearly evident in the remaining 12 male reports.
The appraisal process involves not only personal reflections on one’s own responses to sextortion incidents but also both male and female victims offered advice on dealing with sextortion. In general, they recommended that when engaging with strangers online, one should ‘always keep your head as level as you can’ (MV-101), ‘be diligent for any more signs of them returning, be diligent, y’all’ (MV-13), and ‘not send any photos of you, even just normal ones’ (FV-1). Furthermore, when you do encounter the sextortion, victims in this sample simultaneously supported the fact that, ‘DONT PAY, then they’ll come back for more and the whole shebang’ (MV-101); ‘stall with them for as long as possible and lie to waste their time to reduce your worth to them, always remember do not pay’ (MV-12).
Discussion
Research demonstrates that cyber sextortion has increased over the last decade, affecting not just minors but adults as well, and causing significant harm to those victimized (Cross et al., 2023b; O’Malley and Holt, 2022; Patchin and Hinduja, 2020). Despite the prevalence of cyber sextortion, it is noteworthy that existing studies predominantly concentrate on the occurrence of cyber sextortion, the traits of those involved as offenders and victims, and the mechanisms involved. Criminological research has yet to delve into the examination of stress and coping mechanisms from the perspective of victims. This gap is a notable oversight, as it has the potential to provide valuable insights for developing targeted and proactive approaches to minimizing the harms brought by sextortion. To date, in research that examines individuals’ stress and coping processes, several researchers have discovered the significant applicability of Lazarus and Folkman’s (1984) stress theory in explaining various coping strategies in dynamic contexts (e.g. Ermasova et al., 2020; Green et al., 2005, 2010; Kelso et al., 2005; Quine and Pahl, 1991), including those in the realm of criminology (Colbert and Durand, 2016; Ermasova et al., 2020; Giurgescu et al., 2015). This theory is thus employed to comprehend the factors that trigger stress among victims and how they cope in cases of sextortion.
The findings presented herein conclusively demonstrate the appropriateness of Lazarus and Folkman’s (1984) original model in effectively detailing the experiences and responses of victims in the context of sextortion incidents (see Figure 1). Broadly during the person–environment interaction phase, offenders employ a diverse array of strategies to acquire the intimate images and videos of victims, subsequently leveraging this content to substantiate their ransom scenarios. These techniques encompass a spectrum ranging from the utilization of basic social engineering approaches to the more intrusive act of hacking, resulting in unauthorized access to victims’ mobile devices. Subsequent to the acquisition of explicit footage, the sequence of ransom scenarios unfolds, prompting victims to experience heightened stress as they attempt to mitigate the potential damage to their personal reputations and the well-being of their families. Within the sample of victims, two distinct coping pathways are discernible. The first pathway entails victims solely employing primary appraisal along with emotional-focused coping strategies. The second pathway encompasses victims initially undergoing primary appraisal, followed by a secondary appraisal where they opt for a more rational approach to manage stress, thus guiding their preference toward problem-focused coping strategies. While it is worth noting that a portion of victims, particularly those on the first pathway, may revisit the ransom scenario, almost all victims eventually gear toward the problem-focused coping strategy culminating the entire process with a stage of reflection, referred to as the reappraisal stage.
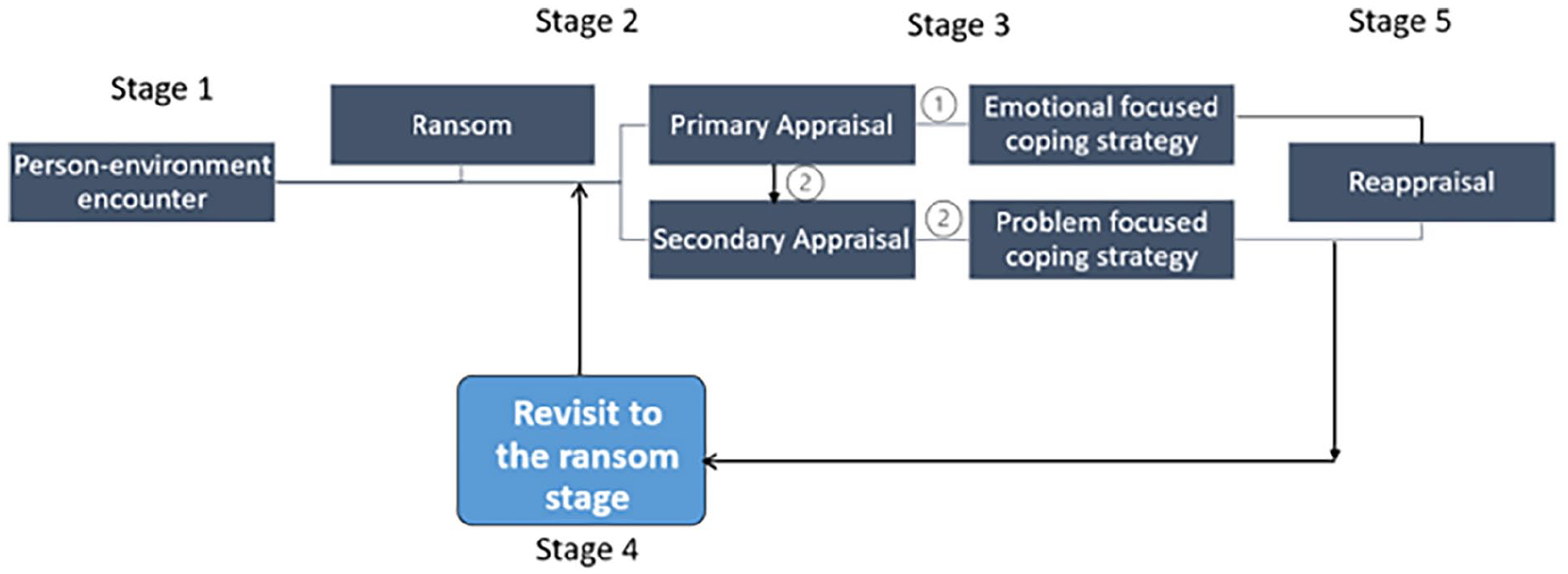
Adapted transactional model of stress and coping for cyber sextortion victims.
The model observed in this study also revealed a few differences in male and female victims specifically those before and after the coping stage. Specifically, a significant proportion of male victims are induced to voluntarily send explicit materials to offenders through manipulative emotional tactics. In contrast, the majority of female victims are lured through involuntary means (e.g. being exploited by acquaintances or hackers). Intriguing enough, during the second ransom stage, during the second stage involving ransom demands, females tend to encounter a higher prevalence of non-financial requests in exchange for their intimate content, whereas the majority of male victims are solicited for monetary payments to terminate the dissemination of their images. The reappraisal stage is also distinguishable based on male and female victims. Female victims often exhibit a greater reluctance to openly express the harm they have endured and are less forthcoming about their future prevention strategies. They tend to adopt a more self-critical approach, attributing blame to themselves for sharing images with the wrong persons online. Although it may appear that the varying reappraisal characteristics could result from a disproportionate sample with males being dominant, the underlying intrinsic personal, behavioral, and psychological traits that influence responses to crime incidents between males and females should also be counted as a justification (e.g. Chataway and Hart, 2019; Noon et al., 2019; Rountree and Land, 1996). Thus, there is a need for more extensive research exploration within the realm of sextortion victim experiences to facilitate the development of more effective group-specific interventions.
Furthermore, the findings from this study have contributed additional elements to the original model proposed by Lazarus and Folkman (1984), specifically pertaining to the phase involving individuals revisiting their responses to stress. In a few cases (despite gender), victims who were initially coerced into paying ransoms to the perpetrators in the first instance were observed to return to the same sextortion scenario with the same offenders. Those who reverted to the same scam were met with further financial demands, whether for the same purpose (e.g. preventing the dissemination of explicit content) or different reasons (e.g. law enforcement investigations). The researcher speculated that this stage would emerge when offenders have received payment from victims in the initial ransom scenario, suggesting that victims might be susceptible and amenable to continued stress imposition. Intriguing enough, this revisit stage seems to be a trigger for the majority of victims who had initially complied with the monetary demands. It prompts them to engage in a more rational assessment of the situation, realizing that these offenders are unlikely to cease their requests even after the distribution of their explicit footages. Nonetheless, a small subset of victims in this study continued to either comply repeatedly or struggle to comply, holding the belief that compliance might eventually lead to the cessation of further demands, regardless of the requested amount. Unlike the revisit or revictimization stage revealed in online romance scam (Whitty, 2013), the revisit stage here functions as a turning point for victims who initially complied, compelling them to make a more reasoned evaluation of the scam’s dynamics. In this context, these findings enhance the comprehensiveness of the original stress and coping model by introducing the unique elements associated with sextortion. In light of these observations, further research is warranted, including an expansion of the sample size, to determine the persistence of this revisit stage and to investigate potential significant distinctions among different groups (e.g. males versus females) in their encounters with this stage.
Cyber sextortion, in contrast to other types of online fraud crimes (e.g. advance fee fraud or online romance scams), presents a unique challenge for intervention by public sector entities through algorithmic solutions to alert potential victims and deter perpetrators. The distinguishing feature of cyber sextortion is its occurrence within private digital communication channels, where explicit content is obtained by offenders through either coercion or persuasion. Most importantly, as indicated by the majority of victims in the current sample, it is the potential adverse reactions of their close social circles that can ultimately influence victims’ decision-making regarding compliance with further demands from the perpetrators.
Consequently, the researcher proposes that an effective strategy against cyber sextortion implemented by either government or non-governmental agencies should target on providing awareness programs for the parents and guardians (e.g. friends or other relatives) about the complexities of this cybercrime phenomenon. These programs should specifically emphasize the critical importance of offering supportive guidance from responsible adults or close individuals when dealing with victims who have already experienced sextortion. The findings in this study highlight that victims in stages 4 and 5 are more prone to confide in family or friends, while also transitioning from emotional to rational thinking. If the transition is in a correct direction, it can potentially mitigate the harm and distress inflicted by cyber sextortion. Crucially, the support and guidance provided by individuals within the victims’ immediate social circles hold a position of utmost importance in shaping the victims’ self-agency when it comes to dealing with the situation. As a consequence, rather than placing blame on victims for sharing explicit content with strangers, it is imperative that guardians partake in the insights offered by these potential awareness programs by showing supportive insights on rectifying mistakes when victims confess to them about the incidents. This support can significantly impact the mental well-being of victims and influence their future life decisions.
Moreover, society should strive to establish specialized support centers for victims of sextortion, especially catering to those who lack immediate connections for seeking counseling. This type of support center could be of significant benefit, especially for the specific cohort of victims within our present research sample who may be disinclined to disclose their circumstances to family or friends due to strict parenting styles or religious beliefs. Similar to the human trafficking hotline, such a proposed sextortion help center need not necessarily have a physical location but could instead be implemented as a remote service offering telephone or video counseling. This service would be available 24/7, with experts providing guidance to sextortion victims. As the result of this endeavor, individuals subject to cyber sextortion are no longer subjected to remain silent and isolated by offenders. Instead, they could benefit from a robust support network within society, designed to aid them in effectively addressing such incidents, along with access to crucial psychological counseling during the aftermath. It is yet unknown which should be the responsible agency and the required source it will take to establish this center. Nonetheless, this proposed endeavor is indispensable and important in mitigating the potential tragic consequences associated with sextortion.
This study’s findings contribute to our understanding of stress and coping mechanisms in sextortion victims. They hold promise for expanding the existing stress and coping model (Lazarus and Folkman, 1984), offering valuable insights for future research and practical applications in addressing sextortion incidents. There are, however, several limitations of this study that must be recognized. First and foremost, there exists a notable gender imbalance, with fewer female victims than males, as is repeatedly emphasized throughout the study. This disparity, however, is predetermined by the volume of posts available on Reddit. Future research is needed with larger and more balanced sample of male and female victims to replicate and further explore individuals’ coping strategies in the context of sextortion. In addition, it is important to recognize that the posts made by victims in this study may lack comprehensive descriptions of their entire sextortion experiences. This limitation could be resulted from victims’ potential reluctance or selectiveness in revealing the complete scope of the sextortion events. It could also be possible that some victims may prioritize obtaining prompt responses from Reddit users, leading them to provide more succinct narratives. Most importantly, there is a possibility that some reports stem from the same victims who have posted multiple times, possibly seeking attention from the general public to help with their incidents. Validating this aspect becomes challenging. Consequently, due to these limitations, additional research is needed to utilize alternative data sources such as interviews or surveys, to establish a comprehensive understanding of stress and coping dynamics among sextortion victims.
Despite these limitations, the outcome from this study makes an important contribution by employing a psychological model centered on stress and coping (Lazarus and Folkman, 1984) to understand how victims of sextortion navigate and manage the various forms of stress associated with this online crime. In general, our results show that this original model effectively explains the significant themes related to sextortion, while also complementing the original model with unique insights into the characteristics specific to this crime. Given the dearth of criminological research focusing on the responses and reactions of sextortion victims, these results pave the path forward for future research on these topics. Finally, authorities and the general public should understand the complexities of sextortion, thereby enabling the development of evidence-based proactive strategies aimed at safeguarding the mental well-being of victims and, crucially, preventing future instances of sextortion from falling into becoming potential victims.
