Abstract
The development of effective socio-technical information systems requires designers to balance ethical goals with functional capabilities and business objectives. To address this challenge, we propose EDGE, a novel ethical design method that focuses on two key activities in the systems development process—ethical grounding and evaluation of ethical impacts. We provide an empirical example of the EDGE method by applying it to the redesign of a sustainable application in the energy industry. This empirical example reveals the need for ethical clarity to ground and evaluate the app to achieve improved ethical performance and social impacts. We conclude with the implications of the new ethical design method and future research directions for its application and enhancement.
Keywords
Introduction
The quickening pace of innovation has fundamentally altered the adoption curve of information technology (IT) applications in recent years. In the past, early adopters represented only a small portion of the eventual adopters of a given innovation (Rogers, 1962). However, innovations today may experience global adoption within months, if not weeks, of launching. For instance, ChatGPT gained 100 million active users in 2 months (Hu, 2023). This rapid change in innovation diffusion accentuates the need for foresight regarding potential ethical issues these innovations may encounter. Unlike the days when developers could react to red flags as they appeared among the small group of early adopters, harm caused by emerging innovations today may affect millions of users before the signs of bias and possible harm are recognized. Further, addressing harms caused at a global scale is much more complex than addressing local harms. Thus, now more than ever, it is urgent for designers and developers to preemptively ground emerging IT applications in moral values and develop systematic ways of evaluating the ethical impacts.
Moral values and ethics are often sidelined in the information systems (IS) development process because managers and developers are in a rush to beat competitors to market. The often-contagious nature of emerging IT can additionally trigger a race for the most groundbreaking application of an innovation. When IS developers focus on “What can we create?” rather than “What should we create?” they tend to prioritize technical capabilities over ethical considerations (McGrath, 2024; Young et al., 2021b). Thus, many IS are not grounded in ethics and may result in unintended, adverse effects on social good at a global scale.
Since a focus on the technical capabilities of an artifact may come at the cost of oversight of social good, there have been calls for greater consideration of social impacts in the design process (De Leoz and Petter, 2018). Considering social impacts is important because when moral value systems and beliefs are ambiguous or even missing in design theories, both developers and researchers struggle to justify the value of their designs (Peffers et al., 2018) and may even introduce unintended adverse effects on social good. In recent years, researchers in management and IS have argued for the importance of values awareness and the inclusion of ethical considerations in the design process (Friedman et al., 2013; Monson, 2023; Nussbaumer et al., 2023). Despite efforts to build awareness and better integrate moral values into designs, researchers and developers still lack rigorous methods and tools to ground designs in comprehensive ethical frameworks and evaluate the degree to which designs achieve ethical outcomes.
Compelled by the need for more actionable methods to achieve social good in the design process, we propose a novel, more comprehensive approach—Ethical Design through Grounding and Evaluation (EDGE). This new approach focuses on five key activities essential for determining the social impacts of IS applications. EDGE gives system development practitioners and researchers a systematic, critical method to add to their toolbox for evaluating whether design choices move a socio-technical system closer to or further from an ethically grounded state. We base EDGE on well-defined and thoroughly vetted theories and philosophies of ethics. Integrating the critical research methods of deconstruction and reconstruction (Martin, 1990) as evaluation techniques, we propose a rigorous method for the evaluation of the ethical effects of IS on users.
We present the next-generation research method, EDGE, using an empirical case from practice. The case involves a project within a German energy utility that faced a moral dilemma when introducing green energy tariffs. Customers did not understand the principles underlying these tariffs and believed they had become victims of greenwashing. To restore trust and enhance transparency, the energy utility developed a customer loyalty app to promote and explain the use of green energy tariffs. We describe how they evaluated their initial system design and system redesign in five steps: (1) selection of an ethical kernel theory, (2) development of overarching ethical design principles using the kernel theory, (3) derivation of context-specific design rules from overarching design principles, (4) development of condition statements to describe the social impacts of a design corresponding to each design rule, and (5) evaluation of social impacts through reconstruction of the condition statements.
A persuasive advantage of the EDGE approach is that it brings abstract ethical kernel theories to life by implementing them in a well-defined design context. As such, this method provides researchers with the opportunity to test hard-to-implement theories in ways that can reveal flaws or inconsistencies in the kernel theories. In our case, we find that the kernel theory originally selected to evaluate the design and redesign of the app was scoped too narrowly to meet the organization’s needs. This was revelatory and led to the discovery of additional overarching design principles, informing a contribution to our kernel theory. This paper demonstrates how implementing ethical kernel theories and evaluating outcomes using EDGE can lead to theoretical contributions and better practical outcomes. We conclude with a discussion of limitations and future research directions.
Background
There is a rich tradition of design research in IS (see Appendix A). Recent directions have focused on the use of ethical theories to incorporate non-functional, value-based requirements into the design process. For example, Bichler et al. (2021) study how truthfulness, efficiency, and fairness could guide the design of software for matching preferences, and Monson (2023) uses social kernel theories to develop design principles for sustainable development. Kane et al. (2021) draw on the Theory of Emancipatory Pedagogy to design principles for an emancipatory assistant to help users navigate oppressive information environments online. Other notable examples of how ethical theories can be used as kernel theory include Nussbaumer et al. (2023)’s paper about ethical emergency management and Wass et al. (2023)’s work on how social inclusion theories can inform design for more inclusive IT. These works provide examples of how specific ethical theories can inform the design of artifacts. However, they do not offer a comprehensive and actionable approach of how design can be ethically grounded using well-defined theory and then be evaluated systematically over time.
To improve the incorporation of values during the design process, Friedman et al. (2013) developed value sensitive design (VSD) as a research method. VSD has been employed in a wide variety of contexts, such as crowdsourcing (e.g., Deng et al., 2016), computer-mediated work (e.g., Boyd et al., 2016), health information systems (e.g., Walton and DeRenzi, 2009), and mobile technology (e.g., Le Dantec et al., 2009). VSD identifies which stakeholder values should be reflected in a system’s design (Deng et al., 2016; Friedman et al., 2013). The VSD method represents an important advancement in ethical design; however, its focus on individual stakeholder’s values brings a risk of overlooking values not championed by sampled stakeholders. VSD also risks conflating stakeholders’ benefits with moral values and ignoring important values that are not emphasized by the identified stakeholders (Le Dantec et al., 2009; Manders-Huits, 2011). The exclusion of other stakeholders (Le Dantec et al., 2009) and conflicting value systems among stakeholders (Manders-Huits, 2011) are additional challenges that VSD needs to address. The VSD method does not currently provide clear guidance on how conflicting values can be balanced to promote a higher-level ethical philosophy or framework that an organization desires to follow (Manders-Huits, 2011; Winkler and Spiekermann, 2018).
Comparing VSD and EDGE.
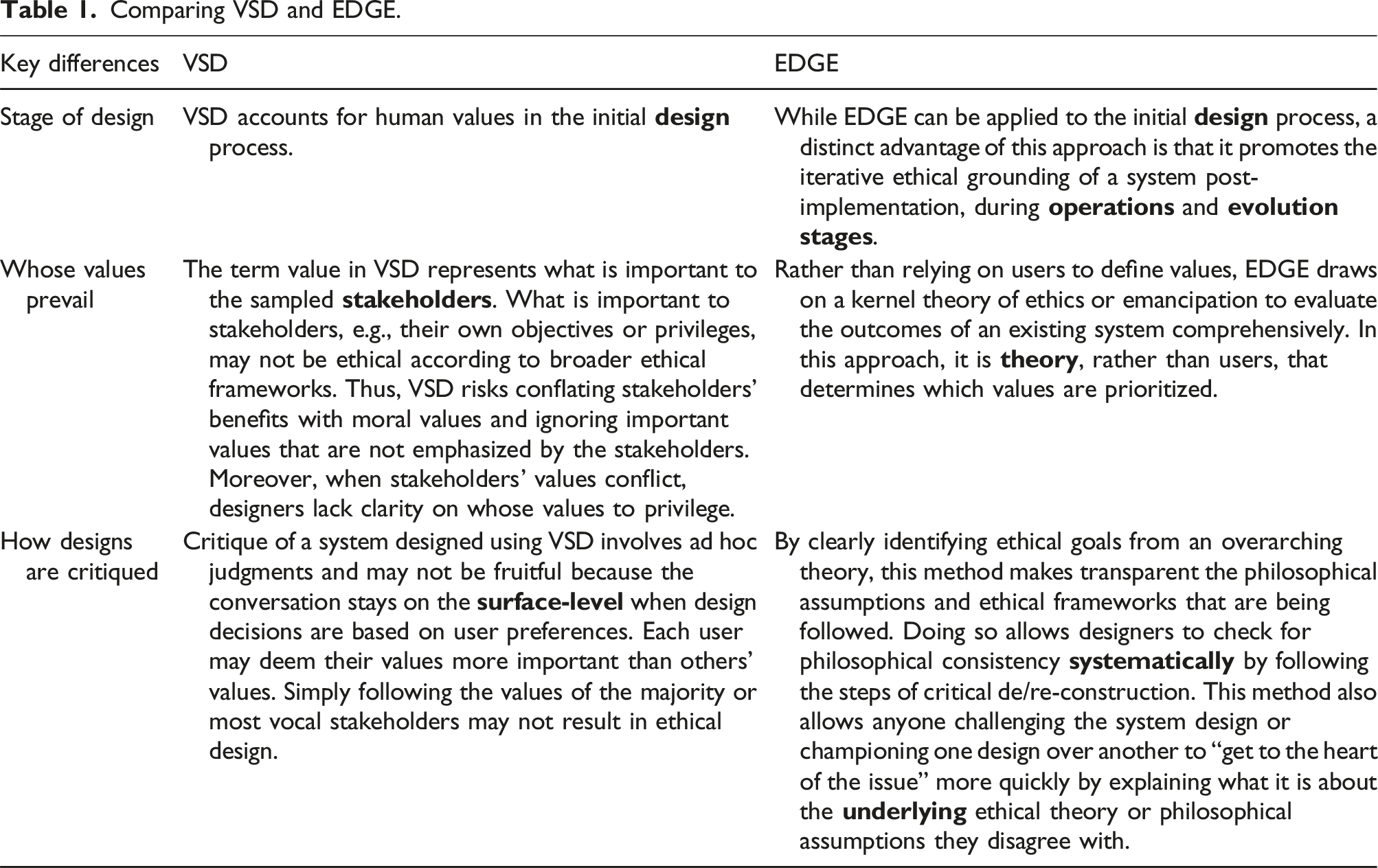
Critical Research Theory (Monson, 2023) outlines a structured approach to assessing the capability of an IS artifact to deliver its intended values effectively. This method represents another important step toward ethical design but focuses primarily on the problem formulation stage without guidance for evaluating or comparing different designs after implementation. The lack of a methodology to continually reevaluate the extent to which a design is rooted in, perhaps changing, values of an organization post-implementation is particularly problematic for those seeking to promote social good through IS. Our paper addresses this need for a more comprehensive method by proposing EDGE as a viable approach that can incorporate ethical frameworks in design and evaluate the design outcomes based on the ethical framework.
The EDGE approach
Ethical Design through Grounding and Evaluation (EDGE) provides a rigorous, comprehensive, and integrative approach to promoting the ethical grounding of information systems applications with compelling evidence of social impacts that can be measured using strong evaluation methods. We envision two scenarios for the use of EDGE by system development project teams.
In the first scenario, as shown in Figure 1, the project team can perform parallel activities to determine stakeholder needs and establish ethical grounding during the iterative development of the information system. Stakeholders provide detailed functional, quality, and value needs that are reconciled into system requirements via cost and tradeoff analyses. At the same time, these requirements must be tested against ethical kernel theories on which the entire information system is grounded. Building on the best practices of agile development, it is not only the information system but also the smaller component units that undergo iterative development and testing sprints. That is, the iterative testing of the information system includes an evaluation of social impacts at all levels of unit testing, subsystem testing, systems testing, and customer acceptance testing. In this way, the EDGE approach supports rigorous activities of ethical grounding and evaluation in the initial construction and operation of the information system. EDGE in the IS development process.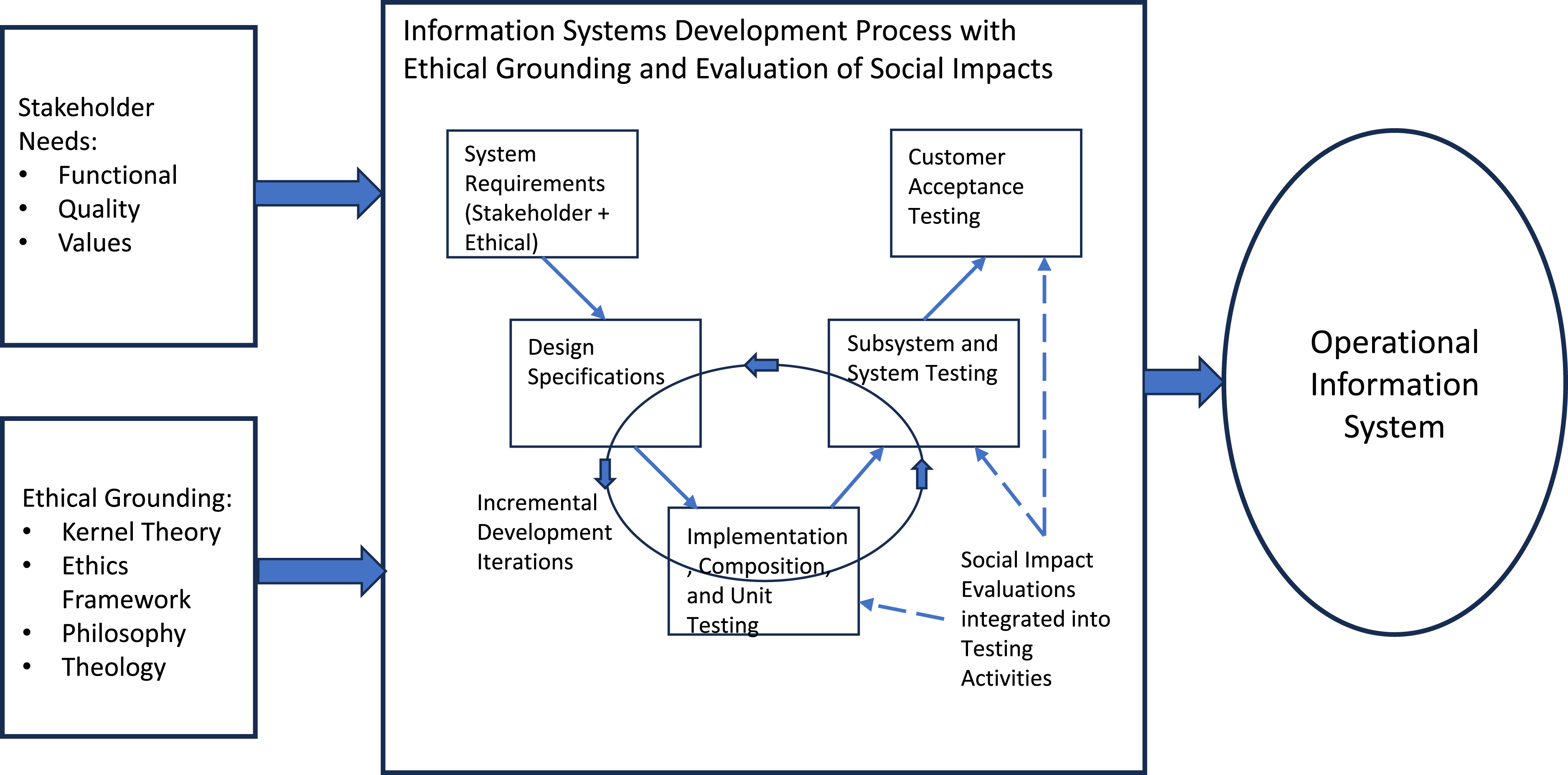
In the second scenario, as shown in Figure 2, operational information systems have been designed and implemented with little attention to ethical theories and social good. EDGE can evaluate the social impacts of the current system design and support its redesign to improve social outcomes. This requires ethical grounding—either based on an initial or retrospectively adjusted social goal—by selecting a suitable ethical kernel theory to inform the system’s redesign. The kernel theory supports the development of overarching design principles, context-specific design rules, and condition statements related to each design rule. Condition statements are similar to user stories or use cases as they describe the conditions experienced by any stakeholder including users, external stakeholders, or even the application environment. Developing condition statements to describe the system’s social impact requires deep knowledge of users’ experiences. Surveys, observations, and personal experience using methodological tools from ethnography, case studies, or action research can inform the development of this knowledge. System data can deliver additional information about, for instance, ethical violations of individuals, groups, or society through monitoring or data sharing. Once condition statements have been developed, critical reconstruction structures the evaluation of the system’s adherence to moral values imputed from the kernel theory. Reconstruction is the process of examining texts by substituting keywords in condition statements to reveal hidden values that are fostered by the information system. The reconstruction process challenges and reframes the existing ethical context and resulting social impacts while also uncovering social impacts that could be achieved through redesign. EDGE in evolutionary redesign of information systems.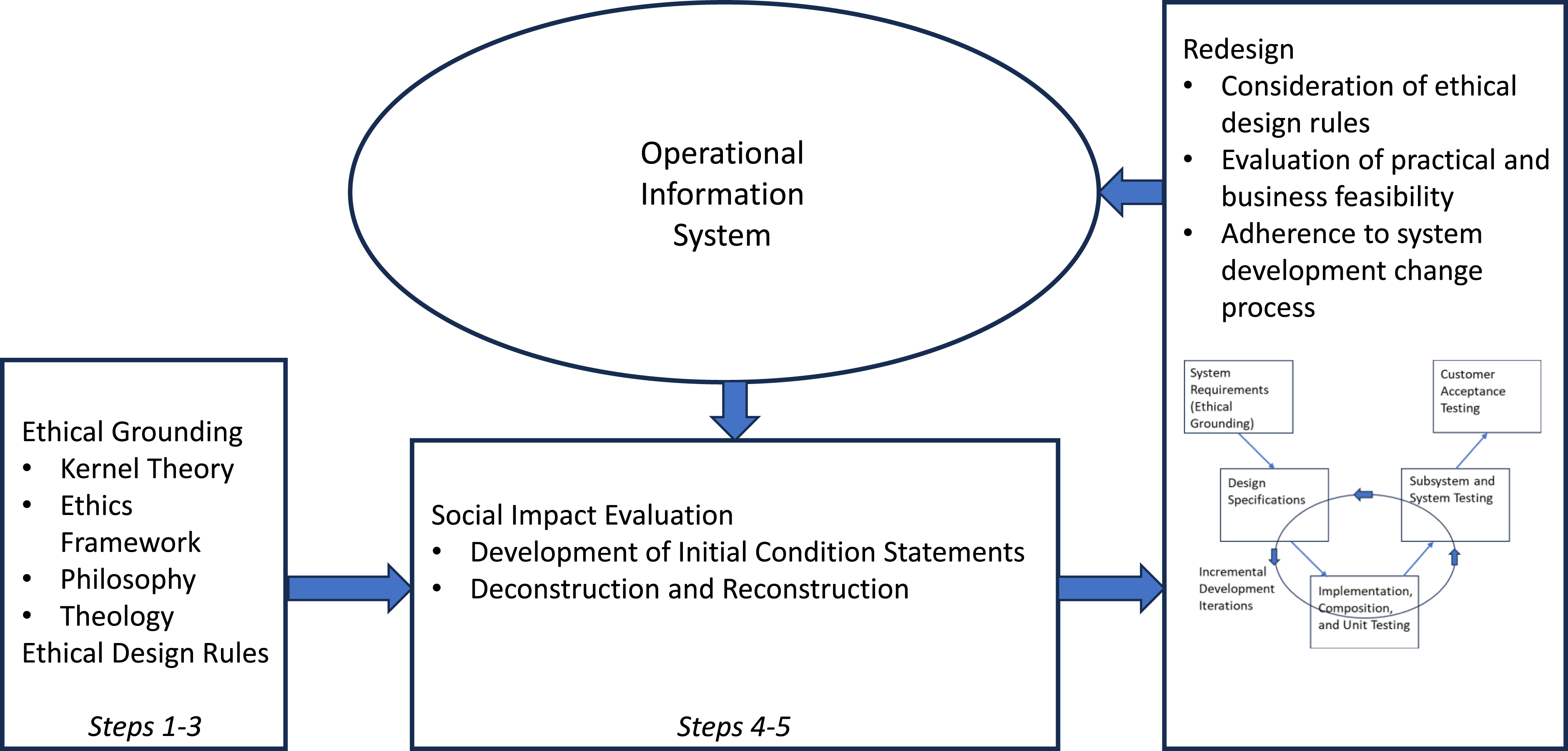
Abstracted into five steps that apply to both scenarios, EDGE describes how an ethical kernel theory can be chosen by the development team (
Once the grounding steps are complete (
EDGE in practice: An ethically grounded energy customer loyalty app
The best way to showcase the relevance and effectiveness of EDGE is through an empirical example. We analyze a longitudinal case from the energy industry, where we could observe the use of EDGE in evaluating the design and redesign of a customer loyalty app of a German energy utility. The Stadtwerke Leipzig (energy utility) developed the NexoEnergy (customer loyalty) app to improve customer trust and transparency after the introduction of green energy tariffs. Customers did not understand how these tariffs worked and suspected the Stadtwerke Leipzig of greenwashing. To re-establish trust, developers sought a new app design that met higher standards of ethical corporate responsibilities. The initial app design was developed in 2018 and redesigned in 2020 after customer feedback and in anticipation of a larger rollout. As an example of the second scenario in which EDGE is useful, we evaluate the NexoEnergy app.
Originally, NexoEnergy’s operational capabilities were designed and implemented without the guidance of a clearly articulated ethical kernel theory. Following the redesign, EDGE is used to help ground and evaluate the social impacts of the original and new app designs and provide practical guidance to the NexoEnergy team as they consider future upgrades of the app.
We selected this case because the ethical dilemma resulting from the initial app design illustrates the general difficulties and pitfalls that organizations face when aiming for ethical design. The initial lack of values awareness and clashes with enacted values encumbered the design process. One of the authors had full access to the project documentation, workshop minutes, interviews, and focus groups. We also had the opportunity to work with the development team lead to triangulate and validate our project observations. Since the development team adopted a design science research (DSR) approach (Utz et al., 2023), observations from this project were well suited to corroborate our proposed next-generation method for evaluating ethical designs. We explain how EDGE was used to evaluate both the initial design and redesign of the NexoEnergy app and provide insights to the project team about how to achieve a deeper ethical grounding in the future evolutions of the app. We outline the five steps of EDGE as applied in the NexoEnergy case below. The goal of including this empirical case is not to contribute a unique, empirical study to the literature but to illustrate how EDGE can be applied.
Step 1: Select an ethical kernel theory
Designers and evaluators can draw from a plethora of different ethical kernel theories. Which kernel theory an organization selects is a corporate and context-dependent decision. Throughout the design process, the chosen kernel theory champions specific philosophies and moral values. While no kernel theory is perfect, established theories promote philosophical consistency and provide transparency about who developed the underlying values framework and whose moral values receive the most attention.
For our empirical illustration of EDGE, we draw on critical social theories of emancipation as kernel theory. Observations from the project and the subsequent redesign of the app indicate that NexoEnergy aimed to re-establish customer trust by emancipating the customer and providing them with full transparency of their energy mix and freedom to control their energy consumption and loyalty tokens. We follow the design philosophy of Kane et al. (2021) in the selection of our kernel theory. They present critical theories of emancipation as kernel theories that can facilitate the change from potentially oppressive designs toward emancipatory designs. Appendix B provides more information about the prominent streams of critical emancipation research in IS with guidance regarding their application to different IS phenomena.
Competing theorists offer different definitions of emancipation, emphasize different components of emancipation, and consider emancipation at different levels (e.g., individual, group, organizational, and society). Critical theories of emancipation are diverse, falling into at least four paradigms, including functionalism, social relativism, neo-humanism, and radical structuralism (Hirschheim et al., 1995; Hirschheim and Klein, 1989). There is consensus among the paradigms acknowledging a tendency toward an oppressive status quo that can only be overcome with an active struggle toward emancipation (Brooke, 2002). Developers of critical IS must choose a concrete definition of emancipation and outline a pragmatic way to achieve it. Failure to set clear goals will result in the prioritization of power holders’ moral values over the values of those with less power. With this in mind, we now outline the basic tenets of the kernel theory of emancipation we adopted for the illustration of EDGE.
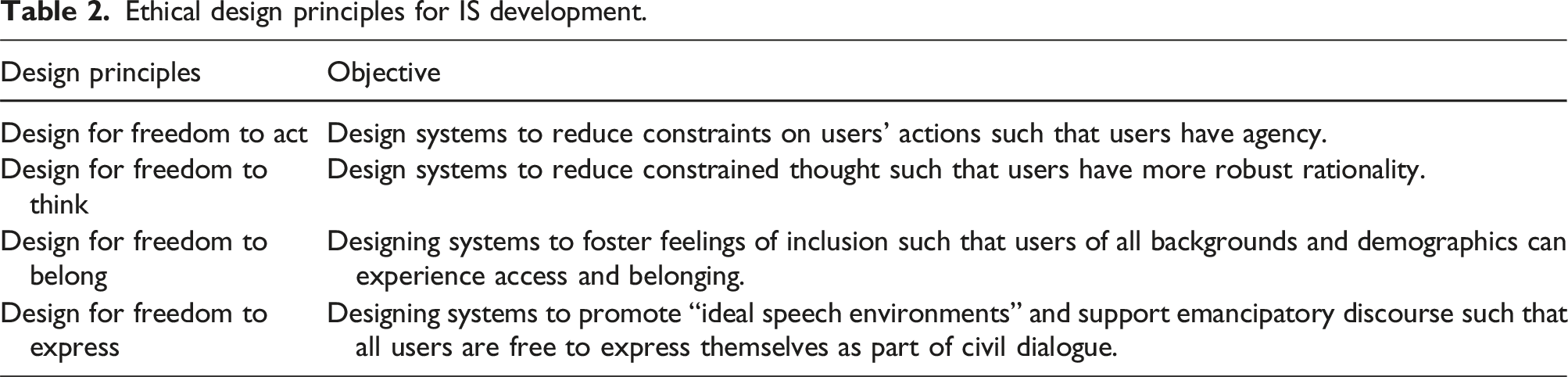
Young et al. (2021), in their literature review and synthesis of research on emancipation in IS, identified four types of freedom. These four types of freedom comprise a typology of emancipation including freedom to act, freedom to think, freedom to belong, and freedom to express.
Researchers applying the next-generation method of EDGE must identify underlying philosophical assumptions inherent to their chosen kernel theory. Though not all emancipatory theories distinguish between types of beings to give humans a special status above machines (e.g., Introna, 2009; Latour and Venn, 2002), we recognize special rights for sentient, living beings. In this research, we acknowledge human value and embrace the notion that humans and machines have distinct roles and rights. Therefore, the EDGE process focuses on how human users experience the four types of freedoms. We assume that humans inherently demand emancipation while machines do not. Thus, under this set of assumptions, it would be absurd to treat humans like machines or to treat machines like humans.
Prior research asserts that machines are useful for mindless tasks and humans for mindful tasks (Salovaara et al., 2019). Artificial intelligence blurs the lines between human and machine tasks (Young et al. 2021a). Yet, our distinction between humans and machines goes deeper than observations about the aptitude and task proficiency of each actor type. We draw on philosophical assumptions about the fundamental nature of humanity. Notably, this assumption may not be a great fit for all cases where EDGE can be applied. Evaluating other sophisticated systems may require the use of different ethical kernel theories and different philosophical assumptions. This is especially true for design theories related to innovative, intelligent technologies that excel at traditionally human tasks such as creating art, processing language, and composing music. Still, the steps involved in the EDGE method will remain the same regardless of the kernel theory and assumptions adopted by the researchers.
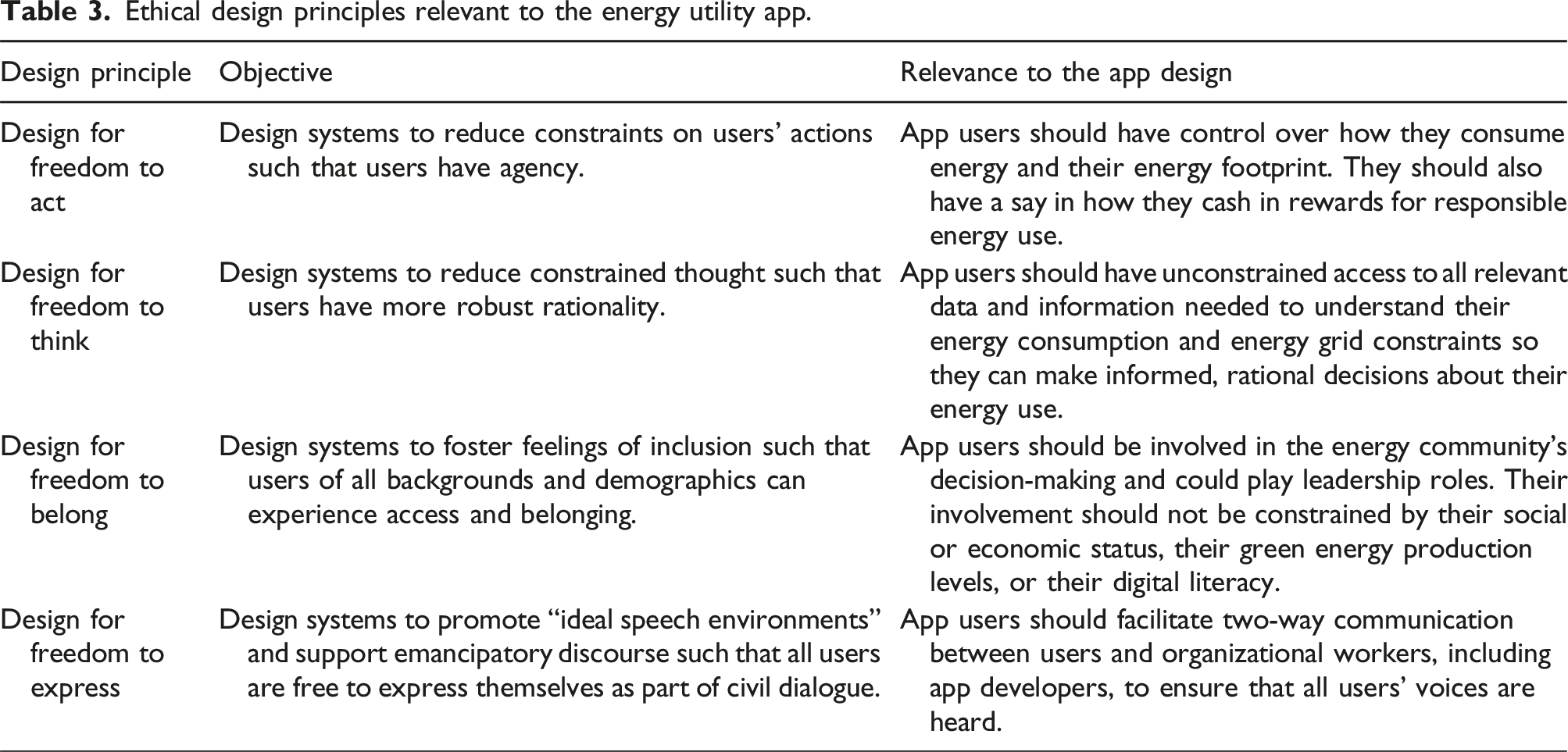
Step 2: Apply kernel theory to develop overarching, ethical design principles
Ethical design principles for IS development.
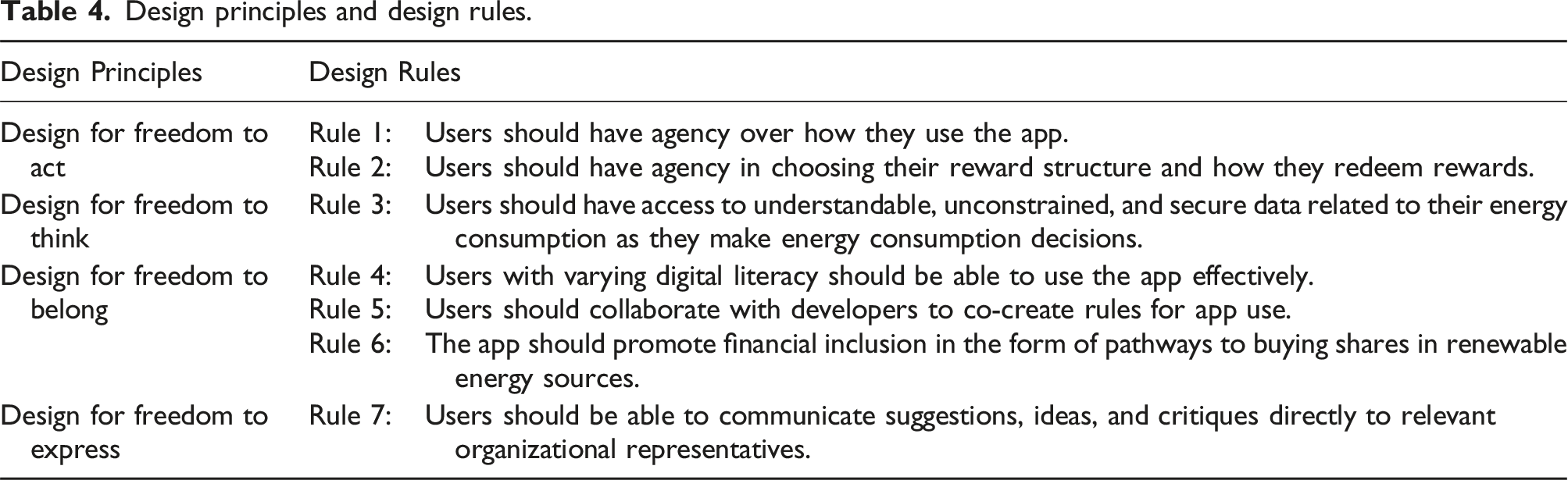
Step 3: Move from overarching design principles to context-specific design rules
Applying EDGE to our case study, we move from general design principles to context-specific design rules. We analyzed which functionalities of the NexoEnergy app involved or affected users’ agency. In consultation with the development team lead who worked on both the initial design and redesign, we discovered that freedom to act in this context means that users can control their energy consumption and, by tying the time of consumption to the presence of green energy in the grid, they have control over their energy footprint. It also means that users can control the incentive structure and how they redeem their rewards.
Ethical design principles relevant to the energy utility app.
Design principles and design rules.
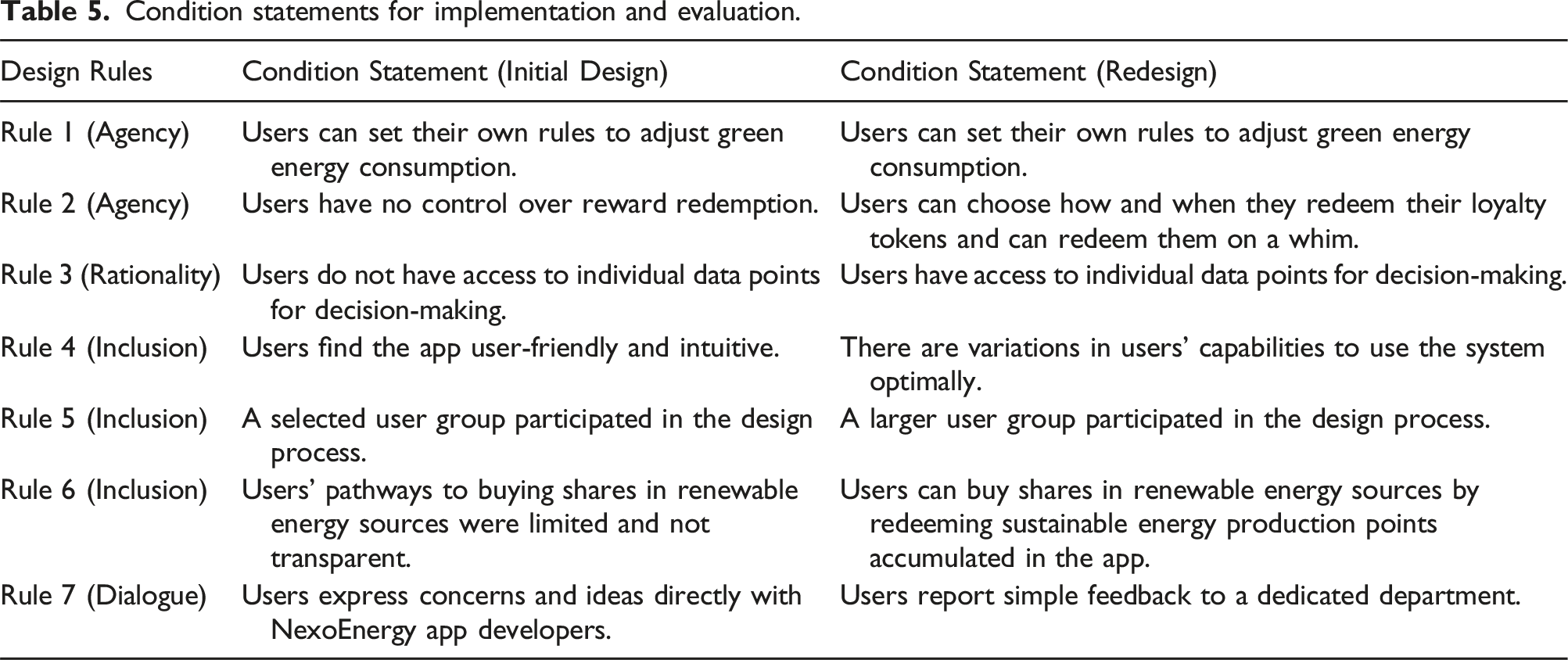
Step 4: Develop condition statements for each design rule
The development of condition statements allows actionable implementation and evaluation of design rules in the information system. Condition statements are descriptions of the experiences of one or more stakeholders who are affected by the information system. These condition statements must be carefully constructed to focus on the ethical impacts experienced by the stakeholders. Focusing on the stakeholders’ impacts and ethical considerations facilitates the reconstruction process described in step 5.
Design rule 1 in our case study is, “Users should have the agency over how they use the app.” For design rule 1, the initial design and redesign both resulted in users being able to set their own rules and adjust their energy consumption. To convert this rule to a condition statement, we wrote a statement about the conditions under each design. In writing the condition statement, it is important to use terms in the statement that can be substituted in the reconstruction processes. Considering these substitutions is probably the most challenging part of the EDGE method. It may involve the consideration of linguistic theories to identify which substitutions will reveal the moral values underlying a condition statement. Since we operate under the assumption that humans are distinct from machines in their rights to freedom, we decided to use the substitution terms “user” and “machine” to evaluate whether human users were given the freedoms they deserve. Being mindful of our desire to reconstruct the condition statements by substituting the term “user” with “machine,” we develop condition statements using the term “user.” For design rule 1, the condition statement is “Users can set their own rules to adjust green energy consumption.”
Condition statements for implementation and evaluation.
Step 5: Perform reconstruction to evaluate social impacts
EDGE draws on methods from critical research to evaluate the ethical grounding of system designs. Due to the abstract nature of ethics and the complexity of their evaluation, subjective interpretation is required to determine if a proposed ethical effort is, in fact, ethical in practice. Subjectivity in research has value, and subjective interpretations can be carried out systematically and rigorously (Sarker et al. 2018a, 2018b). Deconstruction offers a way to systematize and add rigor to the interpretation process. Deconstruction is an analytic strategy to examine language in texts. The term deconstruction has its origin in the works of French philosopher Jacques Derrida (Derrida, 1973) and is most associated with the practice of reading, interpreting, and writing texts. Essentially, deconstruction takes apart arguments, narratives, and plain language (Beath and Orlikowski, 1994). The resulting defamiliarization enables a close examination of different meanings that are socially constructed and brings hidden meanings to the fore (Wright et al., 2020). As such, deconstruction inherently involves challenging and reinterpreting the existing meaning of texts. Deconstruction also reveals “ideological assumptions in a way that is particularly sensitive to the suppressed interests of members of disempowered, marginalized groups” (Martin, 1990: 340).
Methods involving deconstruction have already guided IS researchers to develop theory from the study of systems design (Truex et al., 2000) and IT development documentation (Beath and Orlikowski, 1994). They can even help debunk myths surrounding fashionable IT (Howcroft, 2001). Though deconstruction has a longstanding tradition in management (e.g., Kilduff, 1993; Martin, 1990; Prasad and Mills, 2010), its full potential has not yet been leveraged within the IS discipline (Chiasson and Davidson, 2012).
An extension of deconstruction is reconstruction. Reconstruction is “a kind of proactive deconstruction” (Martin, 1990: 350) and supports the identification of ethical or unethical impacts of an operational socio-technical system. Reconstruction dissects statements to identify meanings through “an iterative process of rewriting that alters – using substitutions – only a few phrases of the text at any one time” (Martin, 1990: 350). When alterations fundamentally change the meaning of a statement, these small changes in wording can make adjacent phrases seem unnatural (Martin, 1990) or absurd. Reconstruction helps unveil tacit moral values and meanings in statements, providing a systematic process for challenging the status quo. It helps readers see how the world could operate under different ethical assumptions or moral values and supports the identification of de facto versus desired ethical outcomes. At the same time, reconstruction can identify where an organization’s claimed moral values do not align with the moral values they enact. A seminal example of reconstruction comes from Martin (1990), who reconstructed the statements of the Chief Executive Officer (CEO) of a large, multi-national corporation to reveal underlying gender discrimination and assumptions about the public and private spheres: original: “We have a young woman who is extraordinarily important to the launching of a major new (product) […]. She has arranged to have her Caesarean yesterday in order to be prepared for this event […].” reconstructed: “We have a young woman who is extraordinarily important to the launching of a major new child… She has arranged to have her product introduced early yesterday in order to be prepared for this birth.” The reconstructed statement provides a stark contrast to the CEO’s statement, making apparent the priorities and values associated with each statement relative to the other. By analyzing statements using reconstruction, EDGE gets to the heart of the values underlying each design.
The EDGE reconstruction process.
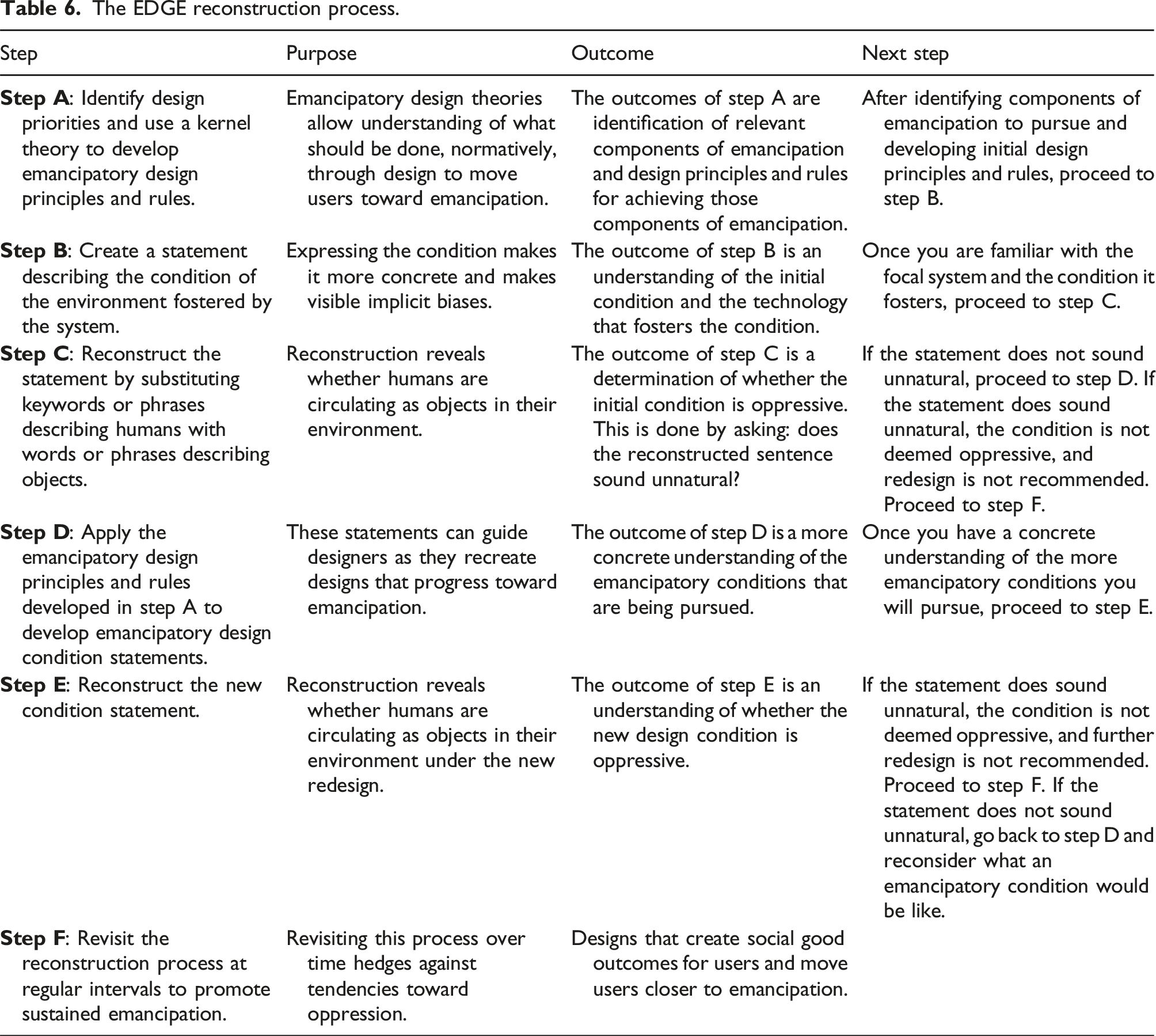
Thus, the initial condition statement “Users can set their own rules to adjust green energy consumption” is reconstructed to become “Machines can set their own rules to adjust green energy consumption.” This reconstructed statement sounds absurd. Machines do not have preferences. The absurdity indicates that humans are not being treated as equivalent to machines. Thus, our evaluation shows that the conditions fostered by the initial design satisfy the first design rule. Further redesign is not required. Users’ ability to set their own rules and adjust green energy consumption did not change from the initial design to the redesign.
The initial condition statement for design rule 2 is “Users have no control over reward redemption.” The reconstructed statement is “Machines have no control over reward redemption.” The reconstructed statement does not sound absurd. Machines are suitable for repetitive and mindless tasks where they do not have control over how a task is accomplished. The semantic congruency of the reconstructed condition statement is a red flag since the lack of absurdity indicates that users are treated like machines. Our design rule is unmet and shows that the development team should consider redesigning this feature to meet ethical goals. The energy utility app redesign incorporated options for in-app reward redemption, including options to invest in sustainable energy using earned reward tokens. Thus, the condition statement for the redesign is “Users can choose how and when they redeem their loyalty tokens and can redeem them on a whim.” The reconstructed statement is, “Machines can choose how and when they redeem their loyalty tokens and can redeem them on a whim.” This statement is absurd, suggesting that the system is ethically grounded and does not require a redesign.
Conditions and relative ethical grounding for each design rule.
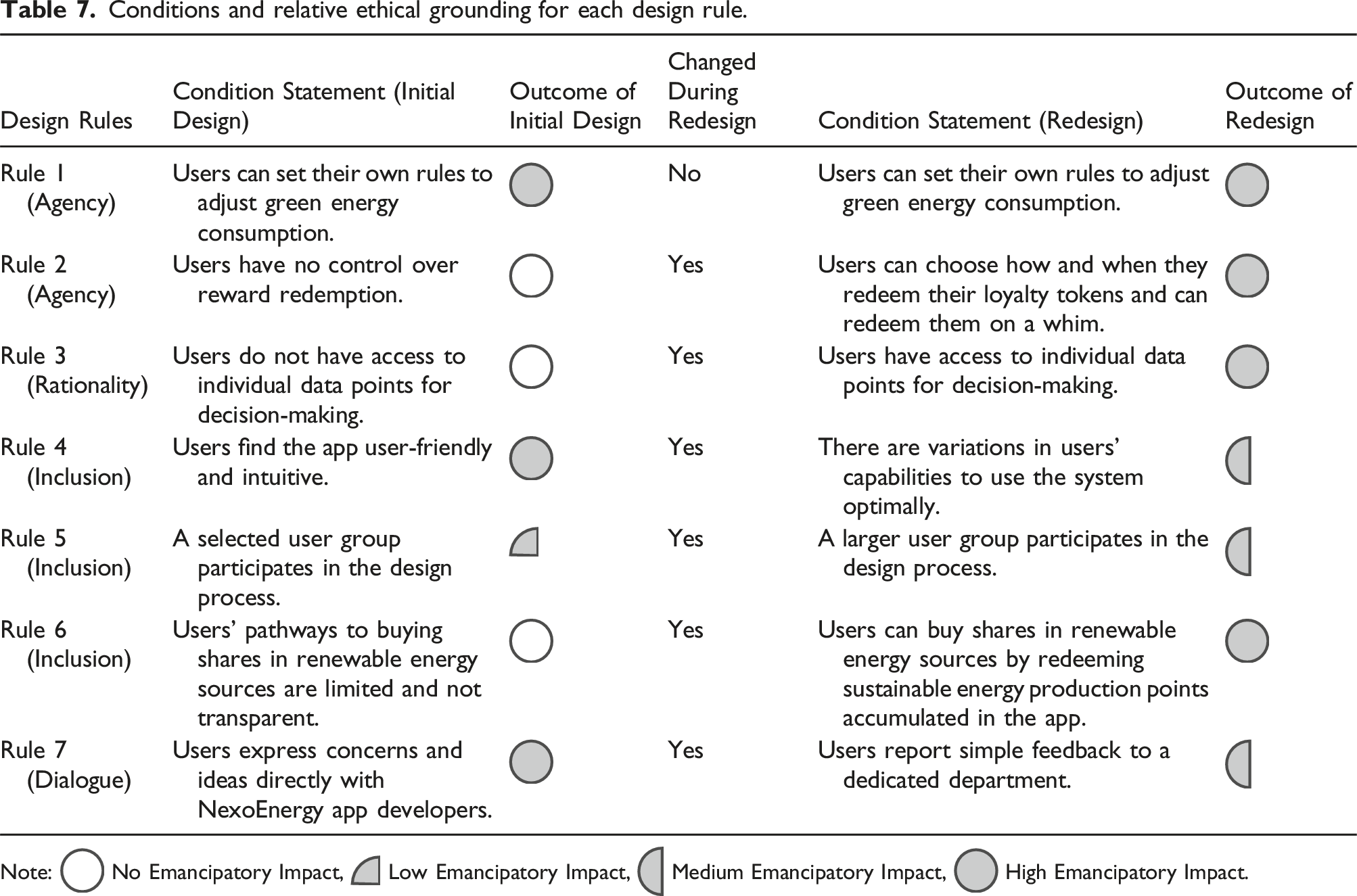
Note:  No Emancipatory Impact,
No Emancipatory Impact,  Low Emancipatory Impact,
Low Emancipatory Impact,  Medium Emancipatory Impact,
Medium Emancipatory Impact,  High Emancipatory Impact.
High Emancipatory Impact.
Discussion – EDGE impacts
EDGE can be applied to both the initial design of socio-technical systems and the continual monitoring and adaptation of existing systems. The energy utility illustration provides compelling evidence that EDGE can identify ethical issues in existing systems. For example, the initial design of NexoEnergy did not promote rationality (Design Rule 3), as the users could not access the detailed data about green energy sources that they needed to make informed decisions. The initial focus of the design team was to provide simplified and aggregated data. As part of the redesign, the design team provided access to more detailed data about the energy sources available to users. The outcome of this design change was an app that was more solidly grounded in the value of freedom to think.
The system’s redesign had a spillover effect on other design rules. For example, design rule 4—mandating inclusion based on users’ digital literacy—was affected by NexoEnergy’s redesign of data access to meet design rule 3. The redesign meant the app was a bit more complicated and less intuitive than the initial design to accommodate a higher degree of data transparency. Accessing and understanding these data required a certain level of digital literacy that not all users had. Thus, compared to the initial design, NexoEnergy’s redesign was less inclusive because a design choice that promoted freedom to think reduced freedom to belong in this illustration. This tradeoff reveals one practical limitation to achieving ethical grounding. That is, choices that ground the design in one value may downgrade the design from a competing value. This paradox of competing values demonstrates why the EDGE method is valuable. This method identifies which values are privileged and at what costs. It allows designers to make informed decisions about adherence to or departure from a pre-selected ethical kernel theory in a transparent manner.
Not only do values compete in design deliberation, but business objectives compete with ethical grounding objectives. For example, in the initial design users could express concerns and ideas directly with the developers of the app, promoting users’ freedom to express (design rule 7). However, the organization struggled to process the various forms of feedback they received from users. High coordination costs associated with filtering, digesting, and responding to high levels of direct feedback inhibited efficiency. Thus, in the redesign, the NexoEnergy team decided to communicate with users through a dedicated customer-facing department and aggregate information for developers based on user feedback. The ethical grounding and evaluation process reveals that by privileging the business needs to reduce coordination costs; developers sacrificed some grounding of the value of freedom to express. Again, this tradeoff is made visible through the systematic EDGE method, allowing the organization to confidently assess the tradeoffs they made and identify potential areas for future improvement.
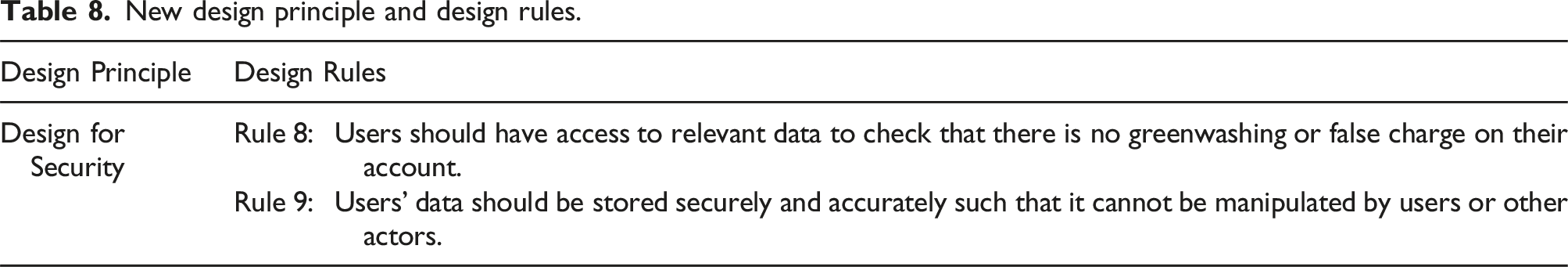
New design principle and design rules.
Contributions and future research directions
Socio-technical systems design is arguably the task most central to the identity of the IS field. Design science researchers excel at producing practical research solutions while reflecting on generalizable design principles (Hevner et al., 2004; Peffers et al., 2007). However, practical applicability does not guarantee grounding in values (Friedman et al., 2008). Therefore, there is a growing concern that values may be peripheralized during the design processes (De Leoz and Petter, 2018; Kane et al., 2021). Yet the problem of how designs can be grounded in values and evaluated for their social good or adverse effects persists. We proffer EDGE as a next-generation method for structuring the ethical grounding and evaluation of the socio-technical systems. This approach deviates from traditional methods to contribute to the diversifying of IS methods (Rai, 2018). While approaches, such as Value Sensitive Design (VSD), are effective when stakeholders’ values are of utmost concern; issues arise when values conflict and a limited selection of stakeholders do not result in the identification of key values. We propose EDGE as an improved approach when organizations seek to build on established, comprehensive, and well-vetted ethical frameworks.
We demonstrate the application of EDGE in the NexoEnergy case study, wherein EDGE provides the structure for rigorously comparing two competing designs. The EDGE method can be implemented multiple times over the life of an IT solution to structure researchers’ attempts to evaluate DSR artifacts in a way that is intentional, philosophically consistent, and transparent.
This research contributes to design science research literature by producing a method for developing more comprehensive overarching design rules for ethical design via the application of comprehensive ethical kernel theories. Our illustration of this method reveals a gap in existing emancipatory theories in IS literature related to the lack of emphasis on security. As Nelson Mandela said, “Freedom would be meaningless without security...” In fact, users would not trust or adopt the energy utility’s app if security were not enforced. This finding that freedoms could not be properly considered absent security considerations suggests future research should investigate the relationship between emancipation and security to better understand how best to study the tradeoffs. Empirical studies building on emancipatory theories report that efforts to promote emancipation are likely to fail without strong security provisions (e.g., Chu and Robey, 2008; Córdoba, 2009; Córdoba and Midgley, 2008). Our finding that the lack of consideration of security is a potential limitation of existing emancipatory theories suggests a possible explanation for the failure of emancipation efforts in current IS studies.
Finally, we discovered that there were times when business and practical considerations limited the extent to which practitioners could ground a system design in ethics per the kernel theory. Given the rapid and contentious trajectory of AI (Kane et al., 2021), we anticipate that business and practical considerations will increasingly conflict with ethical considerations, making EDGE more valuable than ever. This next-generation method, EDGE, guides researchers in weighing tradeoffs among ethical and practical concerns, emphasizing the importance of intentionality and transparency in design decisions. By illustrating EDGE in a business context grounded on the ethical kernel theory of emancipation, we demonstrate the applicability of our method from “ethics for social good” to “business value through ethics.” Our proposal of the EDGE approach is a starting point for IS researchers to address ethical design questions grounded in a consistent and actionable framework. We encourage researchers to apply EDGE to different application environments to demonstrate how different ethical theories can be applied to achieve ethical social impacts through information systems design.
Supplemental Material
Supplemental Material - Ethical design through grounding and evaluation (EDGE) of information systems to achieve social impacts
Supplemental Material for Ethical design through grounding and evaluation (EDGE) of information systems to achieve social impacts by Amber G Young, Syed Shuva, Tamara Roth, Yaping Zhu, and Alan R Hevner in Journal of Information Technology
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Supplemental Material
Supplemental material for this article is available online.
Author biographies
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.
