Abstract
Remote work has become a routine experience for many managers, forcing them to adapt to new ways of ensuring that employees follow company procedure and achieve job targets. Key among these changes have been to the move to computer-mediated surveillance (CMS), where managers monitor employees through electronic representations of work and computer-mediated interaction (CMI), where managers interact with employees through online communication. The outcome of this move is ambiguous and contradictory. CMS can strengthen control because of how effective it is at reporting on work. However, CMI can weaken control because of how effective it is at withholding work practice. We review the literature on remote work to explain how these apparently contradictory effects interact. We show that the joint effect of CMI and CMS goes beyond changing the amount of control over employees. Instead, this joint effect requires managers to ensure the accessibility necessary for control of remote work: that employees make their work visible and that they make themselves reachable for interaction with managers and peers. We use this new domain of control to outline a two-dimensional model of control.
Introduction
The quick and sweeping move to working from home caused by the COVID-19 pandemic turned the distant possibility of widespread remote work into an everyday reality for many employees and managers (Waizenegger et al., 2020).
Once people were allowed to return to the office, many organizations found that their employees valued this newfound working arrangement and were reluctant to come back to the office full time. Organizations also realized that remote work provided benefits for employee motivation and retention. Taken together, both sets of effects led organizations and managers to turn the temporary adaptation to remote work into enduring organizational policies and managerial practices (Kniffin et al., 2021).
This change imposed new challenges on the control of work. Control in conditions of remote work differs from control in face-to-face work because of the joint effects of computer-mediated interaction (CMI) and computer-mediated surveillance (CMS) (Zorina et al., 2021). What that joint effect is and how it impacts control is difficult to answer from research on technology and control. The problem is that CMS and CMI have been studied separately and these two streams of research have evolved a contradiction between the effects of CMS and CMI.
Research on CMS expects control to be more intensive for remote workers and require little if any effort from managers (Cascio and Montealegre, 2016; Zuboff, 1988). The technologies that employees use to work and also the technologies that they use to communicate provide extensive data and meta-data about their practices, interactions and interpretations (cf. Kellogg et al., 2020). This helps control mechanisms that rely on the relationship of authority and also mechanisms for peer control. However, research on CMI expects control to be weaker and more difficult as people gain more agency in the relationships with their managers and their peers where control is established and exercised, allowing them to keep some of their practices and outcomes away from scrutiny (Hu et al., 2021).
Research on remote work arrangements (RWAs) provides the empirical resources needed to specify the joint effect of computer-mediated surveillance and computer-mediated interaction on control (see Raghuram et al., 2019 for a review). It provides the foundation for a model of computer-mediated control that integrates the potentially contradicting effects of CMI and CMS which can help managers leading remote workers who have to address these effects in their everyday attempts at enforcing compliance and performance.
The review of research on control in RWAs that we present next shows that studies on these work arrangements do not address the tension between computer-mediated surveillance and computer-mediated interaction directly. However, they provide enough evidence to do so. Our review shows that these joint effects add a new axis to control in organizations. We show that managers need to enforce reachability and visibility, in addition to enforcing work procedures and targets. This new axis points towards a two-dimensional model of control that opens up new avenues for research and new opportunities to improve leadership practices.
A practice model control of computer-mediated work
The practice approach to IT effects is useful to incorporate the joint effects of computer-mediated interaction (CMI) and computer-mediated surveillance (CMS) into a model of computer-mediated control at work.
The practice approach integrates the role of structure, which constrains people’s actions, and the role of people’s agency in overcoming those constraints. Briefly, the practice approach specifies organizational processes, such as control, as the consequences of people’s use of norms, meanings, and resources to address their everyday challenges (De Vaujany et al., 2018). The view is that organizations prescribe procedures and resources for employees’ work. However, employees can improvise with and around these rules and resources when doing their job.
The practice approach has been used to study the separate effects of different uses of technologies for control because the tension between structure and agency maps onto the relationship between constraint and autonomy at work (e.g., Cunha et al., 2015; Mazmanian and Beckman, 2018; Sergeeva et al., 2017).
A practice approach to control at work
The practice approach to the control of work can be outlined by placing each set of control practices, and the way in which managers incorporate technologies therein, can be placed on an axis bounded by poles, which we call the axis of authority. One pole is “constraint,” where managers use technology to monitor and enforce compliance with prescribed procedure (we use “constraint” instead of “control” for clarity, as “control” is also used to label the set of mechanisms used for ensuring compliance). “Constraint” evokes the role of norms, rules, and meanings in structuring people’s practices and the power of CMS to enforce them (Kraus et al., 2017). The other pole is “autonomy,” where managers allow employees to decide on their own work practices. “Autonomy” evokes the role of agency and people’s ability to appropriate norms, rules and meanings, and the CMIs in which people share norms and meanings to coordinate their work and in which managers convey their own rules and interpretations (cf. Sewell and Taskin, 2015). Figure 1 provides a simplified illustration of the axis of authority. It shows that different teams in organizations can be placed at different points in this continuum according to the type of control that they are subjected to. Axis of authority in control.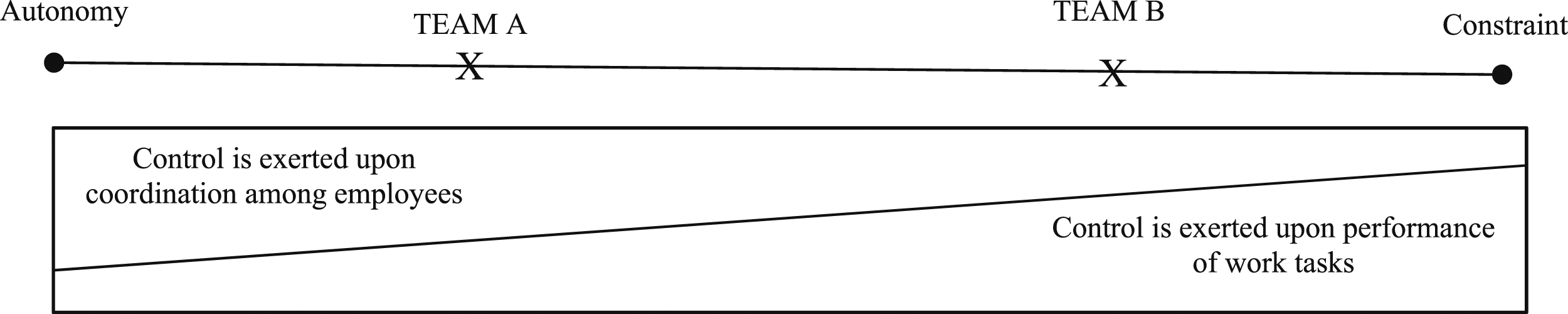
In the practice approach, control mechanisms that rely on prescribed goals and procedures (and therefore closer to the “constraint” end of the axis of authority) require managers take on the daily work of monitoring and correcting employees’ work practices (Hoogeboom and Wilderom, 2015; De Church et al., 2010). The rationale is that employees will not comply with prescribed procedure unless managers enforce it (cf. Lawrence and Robinson, 2007; Townsend, 2005). Moreover, managers need to adapt employees' practices to new challenges that are beyond the scope of work procedures (Dinh et al., 2014). Research on routines shows that complying with prescribed procedure is a skilled achievement. Compliance requires employees to adjust and change processes to cope with the variety of variations and differences that they encounter in the course of their everyday work. This opens up some room for employees to adapt prescribed procedure to their own work practice and even to their own individual ends at work.
Control mechanisms that rely on peer coordination and control front-load the work that managers have to put in into having employees do their job effectively. These are control mechanisms that rely on occupational or organizational socializations or on employees’ willingness and ability to monitor each other’s work and enforce norms and meanings upon one another (see Anteby, 2008). Research has shown that managers cannot just rely on employees to create and reinforce norms and interpretations that ensure compliance without supervision (Haas, 2010). Instead, managers have to specify and impose norms and meanings that supplant those that employees develop (Kamoche et al., 2014). The work required from managers is lighter. They only need to do punctuated corrections to the trajectory of group norms, rather than having to develop and enforce norms of their own (Galegher et al., 1998; Gersick and Hackman, 1990). Employees are the ones enforcing norms and meanings upon one another, which also affords them some room to adapt, and improvise with these norms when addressing their situated conditions for action.
In Figure 1, Team A is an example of a team subjected to control mechanisms that are more reliant on managers’ practices to affect peer dynamics. Team B is an example of a team subjected to control mechanisms that are more reliant on managers’ practices to exercise authority.
A “practice” specification of the effect of CMI and the effect CMS on control at work
Applying the practice approach to control to account for the effects of CMI and CMS consists of explaining how managers’ practices and employees’ practices mediate the effects of CMS and CMI on control.
A “practice” specification of the effect of CMS on control at work
Research suggests that the move to computer-mediated surveillance (CMS) impacts control mechanisms on the “constraint” end of the axis of authority. It does so by reducing the necessity, and consequently the potential of agency for managers. This is because CMS allows managers to delegate part of the work of control to the automatic production of data about work. When managers do so, they expect the automatic production of data in CMS to impose anticipatory conformity (Zuboff, 2015). The view is that the very knowledge that information systems collect detailed information about work in real time is enough to ensure compliance. This is the panoptical effect of information technologies at work. This effect leads to conformity with procedure and targets without the need for sanctions or incentives. It also discourages deviance and resistance (see Burton-Jones, 2014). For managers that still opt to exert surveillance under these conditions, CMS allows them to use electronic representations of work to monitor employees. This can reduce the cognitive burden of assessing compliance. It also reduces the labor involved in collecting data for surveillance (Zorina et al., 2021).
Employees reinforce control processes that rely on CMS when they use their company’s prescribed technology for work because it is these technologies that provide the data for computer-mediated surveillance. Research has shown how technology has an informating effect because it can record and report data about employees’ work as a subproduct of how employees use that technology to carry out their everyday work (cf. Burton-Jones, 2014).
However, employees may also find more autonomy than their managers allow them. Research has highlighted the power that employees can have over how their work is reported in the information systems that managers use for computer-mediated surveillance (Cunha, 2013; Mazmanian et al., 2013; Sergeeva et al., 2017). These studies suggest that employees can create a façade of compliance. This façade is an idealized electronic record of their work. This electronic representation allows employees to escape surveillance. It allows them to work around prescribed procedure without incurring in sanctions from their managers. However, managers can reduce the agency of employees over the representation of work by collecting and monitoring information about employees’ use of reporting tools (Sergeeva et al., 2017). When they do so, they informate the production of data about work, in addition to informating work itself and impose anticipatory conformity with reporting procedure in addition to imposing anticipatory conformity with work procedure.
The extent and quality of data and metadata about work and employees reports thereof turn CMS into a powerful means for managerial authority.
A “practice” specification of the effect of CMI on control at work
Research suggests that the move to computer-mediated interaction impacts control mechanisms on the “autonomy” end of the axis of authority. Moving to computer-mediated interaction helps managers delegate to employees the everyday work of enforcing norms and interpretations. Computer-mediated interaction allows employees to keep a record of their conversations. This record empowers and helps employees’ attempts at imposing practices and meanings upon one another (Butler et al., 2007). It opens up communication practices based upon a record of people’s participation in conversations at work rather than bounding these effects to the duration of, and the participants in each interaction. The key resource for control is people’s ability and disposition to store and use past communication in current interactions (cf. Macnamara and Zerfass, 2012; Orlikowski and Yates, 1994). Managers can still hold on to some of the everyday work of control under these conditions. Many of the technologies used for computer-mediated interaction (such as electronic mail and other similar technologies) and people’s practices with these technologies (such as using the “cc” function of electronic mail to keep their managers aware of their actions and achievements) allow managers to dip into the everyday flow of communication among employees (cf. Leonardi and Treem, 2020). These electronic communications can be used to convey rules and interpretations and to create the shared culture and shared norms that support peer control.
Employees reinforce peer control when they use computer-mediated interaction to carry out their everyday work. As they do so, they create the social interactions necessary to convey norms and meanings. They also feed the collective repository of interactions that they and their peers can use as an opportunity to assess and enforce each other’s compliance (Khan, 2012). Nevertheless, employees may also weaken and even resist prescribed norms and meanings. Research shows how employees can use computer-mediated interaction as an opportunity to carve a backstage for themselves where they can deviate from shared norms and collective meanings without the knowledge of their peers (Dery and Hafermalz, 2016). Employees can further weaken peer control by shaping or even sabotaging the data that their peers use for coordination but also for computer-mediated (peer) surveillance to ensure that some of their actions remain invisible to others (Fleming and Sturdy, 2011).
Employees’ agency over their openness to interaction with and the self-presentation they convey through communication technologies turn CMI into a powerful tool for employee autonomy.
Toward a “practice” specification of the joint effect of CMI and CMS on control at work
Taken together, research on CMI and research on CMS show that each has a significant, separate impact on control processes in organizations. However, there is very little about how these two powerful effects interact. Nevertheless, specifying the joint effects of both uses of technology is useful to advance research on control in organizations and the role of technology therein. It addresses a core contradiction between the difficulties imposed by the shift from face-to-face to computer-mediated interaction, and the help offered by the scrutiny afforded by the computer-mediated surveillance and interaction that support control over remote employees.
Specifying the joint effect of CMI and CMS to advance research thus is difficult to do by simply looking for common ground among research on their separate effects. The problem is that the technologies that support CMI and those that support CMS are different and they are used in different work contexts that require different types of control. Moreover, the potential for variation among managers’ practices and among employees’ responses to both CMI and CMS suggest that the extension of the effect of these two technologies on control that incorporates their interaction is best carried out by looking at a context where employees are subjected to both. Research on remote work arrangements reports on such a context.
Remote work arrangements and the joint effect of CMI and CMS
Research on remote work arrangements (RWAs) provides enough evidence to specify an integrated model of control that incorporates the joint effect of computer-mediated surveillance and computer-mediated interaction. These studies look at work arrangements based on computer-mediated interaction where work is monitored with through computer-mediated surveillance (Mazmanian et al., 2013; also, e.g., compare Brocklehurst, 2001 with Kurland and Cooper, 2002).
“Remote work arrangements” is an umbrella term for work arrangements where people work outside company premises. There are two broad types of computer-mediated RWAs. There are individual-level computer-mediated RWAs, such as telework. There are also group-level RWAs, such as virtual teams.
Both types of computer-mediated RWAs create the conditions for the contradictory effects of CMI and CMS on control. On the one hand, the tools that support computer-mediated RWAs make control easier. Technology provides a continuous flow of detailed and exhaustive information that can be used to monitor people’s work (Kurland and Cooper, 2002; Limburg and Jackson, 2007) and it offers means to establish a wide range of interactions where that information can be applied for control. On the other hand, computer-mediated interactions with supervisors and peers make that information difficult to use for control (e.g., Brocklehurst, 2001; Dambrin, 2004). The lack of co-presence hinders people’s attempts at initiating interactions with one another. The central role that data have in interactions also narrows the information that people give and give off about their actions and achievements at work.
Specified thus, remote work arrangements can help uncover the joint effect of computer-mediated surveillance and computer-mediated interaction on control and address the apparent contradictions that arise when these effects are studied separately. In the literature review that we present next, we specify this joint effect. We then use this literature review to extend the model of technology and control in organizations and explore its implications for practice and establish directions for future research.
Methods
We develop an integrated model of the joint effect of computer-mediated surveillance and computer-mediated interaction by reviewing the literature on control remote work arrangements. Our goal is to integrate and theorize upon the empirical evidence of the relationship between computer-mediated surveillance and computer-mediated interaction rather than just assessing prior knowledge and find research gaps (cf. procedures outlined in Simonsen et al., 2008).
To carry our literature review, we adopted a multi-stage procedure (cf. McSuga-Gage and Simonsen, 2015). We began with a systematic online database search. We then built a review set by screening titles and abstracts. Then, we coded the papers in our review set.
List of keywords for database search.
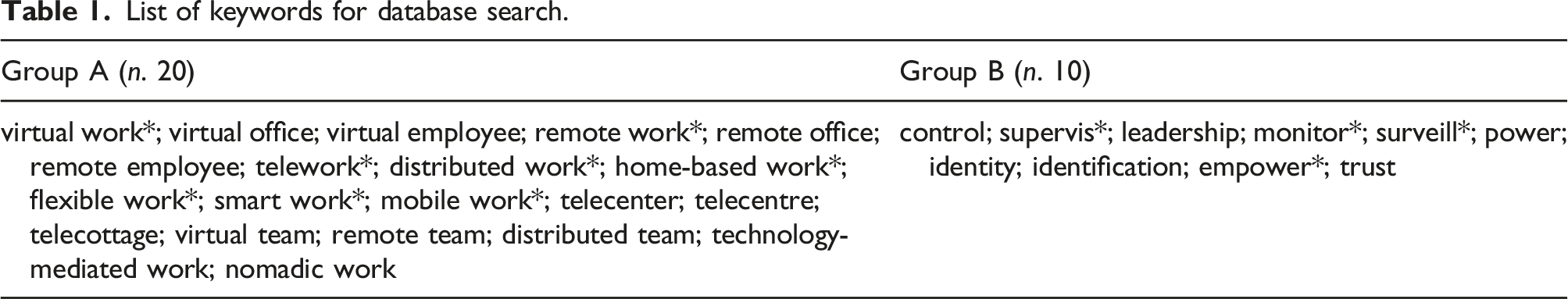
To specify our review set, we carried out a Boolean search (separated by “and”) to identity potentially relevant studies by combining each keyword from the first category (RWAs) with each keyword from the second category (control). The combination of keywords led to a total of 364 search strings.
Elsevier Scopus database was selected for building the review set from these search strings. We chose Scopus because it is one of the largest abstract and citation database of peer-reviewed scientific journals, books, and conference proceedings and one of the most comprehensive academic databases, containing papers from a number of fields, such as engineering, management, information systems, sociology, and psychology. We chose Scopus over alternative databases (e.g., Web of Science) since it provides stronger and richer results for economics and business research (Levine-Clark and Esther, 2008). Our keyword search of Scopus was limited to titles, abstracts and keywords. The search was limited to research published in the English language between 1987 and 2017 in the subject areas of “business, management, and accounting” and “social area” to cast as broad a net as possible while still ensuring relevance to management research and organizational studies.
The first stage of the search process produced over 2000 documents published up to January 2018. In order to refine the review set, we went over document abstracts in two stages. First, we took out studies that were either about RWAs or control but not about control in RWAs. This reduced our review set to approximately 700 documents. In a second stage, abstracts were carefully reviewed to exclude: (a) publications without an empirical component (i.e., theoretical or conceptual papers); (b) empirical studies where participant population consisted of students (since the research focus was on employees in organizations that adopted RWAs); (c) empirical studies where work arrangements did not include the possibility of working off-premises (mostly studies looking at shift-work and flexi-time). We read the abstracts of the remaining studies (and full text when needed) to exclude those that were not relevant to answer our research question (cf. Tranfield et al., 2003). Then we conducted a backward and forward search (Webster and Watson, 2002). The backward search consisted of examining the reference list of each paper to look for additional studies not found in the database search. The forward search achieved the same purpose by looking at studies citing the articles in the review set. Once we built our complete review set, each author read, separately, the full text of these studies in order to assess their quality and exclude those that did not meet various quality standards (cf. Tranfield et al., 2003). Quality appraisal was based on rating studies according to certain quality criteria and started by assessing them through screening their methodology. Minimum quality standards were specified following recommendations provided by various researchers (cf. Okoli, 2015 for a systematic reference guide) to build a shared standard evaluation grid that authors filled in independently to assess each study (Fink, 2015). Then, authors’ judgements were compared and discussed to decide which studies to consider for the subsequent coding process. Ultimately, 108 documents constituted the final sample. Appendix 1 provides objectives, key constructs, and a summary of findings for each of these studies. This database of articles was updated throughout the review process and now includes papers published up to mid-2021.
Much like previous literature reviews, we began by surfacing variables and constructs and the relationships among them. We used definitions of variables and explanations of their relationships to group both into the higher-level codes that we describe in our results section. The data for this coding process came from the results and discussion sections of the papers in our consideration set. The results section allowed us to specify the relationships among variables and constructs found in each paper. The discussion section allowed us to understand how to qualify and interpret those relationships. Although we did not code the theory sections, we did use the discussions therein to understand the links specified in quantitative papers and the coding structures outlined in qualitative papers.
In contrast to literature reviews that seek to describe an entire field, our literature review is narrowed down to a specific set of outcomes. We focused on the effects of CMI practices and CMS practices on control because our goal is to use our review of RWAs to map the joint effects of computer-mediated interaction and computer-mediated surveillance, rather than making a descriptive summary of research on control in RWAs. Therefore, we do not look at themes such as the effects of remote work arrangements on outcomes, such as motivation, satisfaction, and work–life balance.
Coding structure.
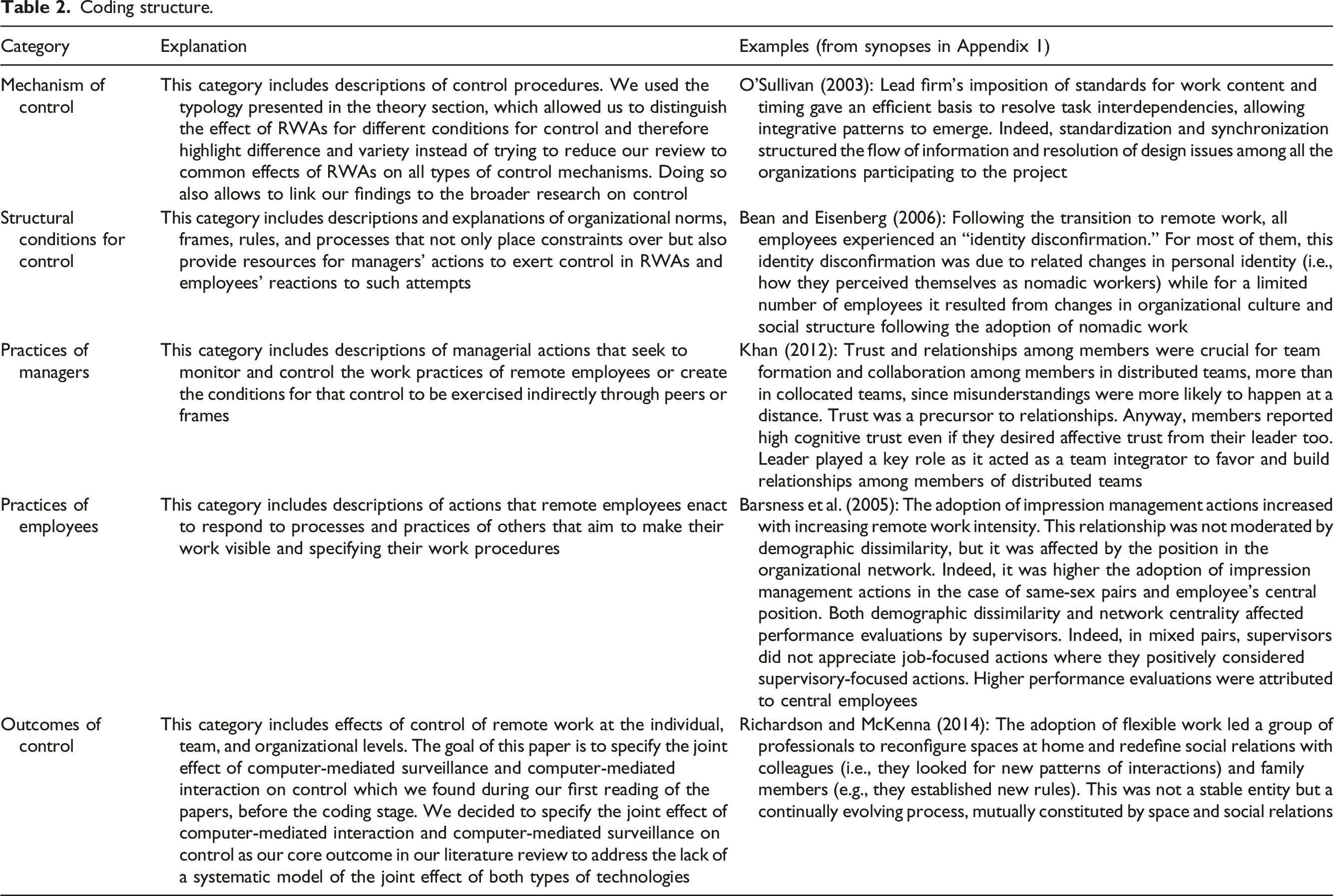
We arranged each of these categories according to the structure of antecedents, process, and outcomes used in other literature reviews and qualitative studies that use text for data. In doing so, we decided on a sequential specification of the actions of managers and employees. We did so to be able to incorporate phenomena such as resistance and appropriation in employees’ responses to managers' attempts at monitoring and enforcing work practice.
The results of this analysis are explained next.
Computer-mediated supervision and interaction in remote work arrangements
This section outlines the results of our review of research on control in remote work arrangements (RWAs). It provides the foundation for our specification of the joint effects of computer-mediated surveillance and computer-mediated interaction on control. We begin by specifying the control mechanisms that we surfaced in our literature review on RWAs. We then use our review to outline the joint effect of computer-mediated surveillance and computer-mediated interaction that underlies the control mechanisms in RWAs.
Control mechanisms and computer-mediated control in RWAs
Our review of research on RWAs surfaced three types of control mechanisms. Together, they establish multiple connections between computer-mediated interaction and computer-mediated surveillance for control. What is new in these mechanisms of control is how the intersection between the lack of co-presence and the abundance of data about work problematizes the everyday links between people and their organization, which are necessary for control to be effective. On the one hand, the lack of co-presence introduces a pull toward autonomy, even when the goal is to impose constraint. On the other hand, the abundance of data introduces a pull toward constraint, even when the goal is to allow autonomy.
The first control mechanism that we found in our review takes advantage of the short cadence of reporting in computer-mediated supervision (which may, in some cases, happen in real time) (Ofeldt and Kallman, 2003; Stanton and Barnes-Farrell, 1996) to improve compliance with performance targets. It adapts work practices by enforcing continuous compliance with performance targets, rather than specifying new work procedures (Charbonneau and Doberstein, 2020; Kinnie et al., 2000; Sewell et al., 2012). Its key challenge is to overcome the pull toward autonomy imposed by limitations of computer-mediated interaction. The goal is to establish enough of a relationship of authority for effective computer-mediated direct supervision. This is a control mechanism based on compliance with goals and procedures is closer to the “constraint” end of the axis of authority.
The second control mechanism in RWAs uses computer-mediated interactions to convey norms that ensure that employees do their work effectively without direct supervision (cf. Ashforth, et al., 2008). These norms are about how employees incorporate work into their identity, rather than about how to do their tasks (Thatcher and Zhu, 2006). The ancillary data about work practices produced by the technologies that support computer-mediated surveillance can be used to support this process of identification. These data establish ties between people’s sense of self and the electronic representations of their work. The goal of this control mechanism is to cope with the pull toward autonomy imposed by computer-mediated interaction. It does so by delegating to identification processes some of the control that is exerted by managers and peers in co-presence. This is a control mechanism based on compliance with procedures which is closer to the “constraint” end of the axis of authority because it uses identity to internalize the relationship of authority.
These two mechanisms are variations of control that focus on work tasks.
The third control mechanism we found in our review of research in RWAs is based on peer pressure, rather than managers’ attempts at imposing norms. Employees exert control over their peers by monitoring each other through regular computer-mediated interaction (Loughry and Tosi, 2008; Sewell, 1998). Employees also exert computer-mediated surveillance upon one another to compensate for the opacity (and therefore the pull toward autonomy) allowed by computer-mediated interaction. Here, people comply with goals and procedures to avoid social sanctions and to follow the norms shared in their virtual teams (Leclercq-Vandelannoitte et al., 2014). This is a control mechanism based on peer pressure, which is closer to the “autonomy” end of the axis of authority.
This third control mechanism is a variation of control that focuses on coordination.
These three control mechanisms scaffold the specification of the joint effects of computer-mediated surveillance and computer-mediated interaction on control in RWAs.
The joint effects of computer-mediated interaction and computer-mediated surveillance in RWAs
The joint effects of computer-mediated surveillance and computer-mediated interaction on control are enacted by managers and employees, as they address the challenges imposed by the joint effects of CMI and CMS.
The challenges imposed by the joint effects of CMI and CMS in RWAs
The challenges imposed by the joint effect of CMI and CMS can be grouped into two categories: challenges to the quality of ties at work and challenges to the quality of electronic representations of work.
Challenges to the quality of ties happen because of the effect of remote work can weaken employees’ people’s identification and impoverish people’s interactions at work (Belle et al., 2015). Weaker ties impact the structure of norms, rules, and interpretations wherein control is exercised.
First, RWAs can weaken employees’ ties to their organization. The main problem is the lack of co-presence (Dery and Hafermalz, 2016). People’s sense of belonging is also a material accomplishment. It is enacted through their bodily presence and agency within their organization’s premises. The lack of a physical manifestation of membership caused by the move to computer-mediated interactions can reduce employees’ sense of belonging to their organization (Gluesing, 2009). This effect can be worsened by changes in work processes. The impact is especially strong when employees’ relationship with managers and peers is mediated by a set of measurements used for computer-mediated surveillance (Lautsch and Kossek, 2011).
Second, RWAs can weaken employees’ ties with one another. Computer-mediated interaction may limit employees' ability to establish meaningful ties at work. The problem is the lower frequency and relative media poverty of online communication (Igbaria and Guimaraes, 1999). This disconnect among remote employees can be worsened by differences in the use of IT. It can also be worsened by differences in interpersonal skills, which can jeopardize the social context for peer control (Limburg and Jackson, 2007). Reliance on electronic representations of work that support computer-mediated surveillance for coordination compounds this effect. It reduces the need to establish meaningful ties to do work that needs information about what other people have done.
Third, RWAs can weaken the ties between employees and their leaders (Oertig and Buergi, 2006). Managerial authority is an everyday accomplishment (Ford et al., 2017). Computer-mediated interaction may limit the opportunities for the encounters that reproduce authority (Dambrin, 2004). Moreover, it may also limit managers’ ability to assess the strength of their formal and informal ties with employees. This further jeopardizes their ability to enact relational practices that strengthen those ties and using those ties to enforce norms of quantitative targets (Zhang et al., 2007). The exhaustive data provided by computer-mediated surveillance, and the anticipatory conformity that it engenders, may also discourage managers from attempting to improve their relationship of authority over employees, further weakening such ties.
These joint effects of computer-mediated interaction and computer-mediated surveillance require control to be exerted not only upon work itself but also on how employees relate to one another, to their company, and its leadership.
Some control mechanisms are more dependent on these ties than others. Control through identification and peer pressure both depend on tight ties between employees and their organization (Fonner and Roloff, 2012; Limburg and Jackson, 2007). Control through standardization can be effective when these ties are weak. However, it needs ties between employees and their leaders to be strong enough to enforce authority (Brahm and Kunze, 2012).
Challenges to the quality of electronic representations of work compound these challenges to the strength of ties at work.
The quality of electronic representations of work impacts the data that are used for control. Research on RWAs shows that computer-mediated interaction can reduce the quality of electronic representations of employees' work (Kurland and Egan, 1999; Leclercq-Vandelannoitte et al., 2014). In RWAs, managers and peers may only be able to get information about employees’ actions and achievements through the electronic representations of work that ground computer-mediated surveillance. The broader research on the effect of technology on control argues that this can provide exhaustive data about employees (see Burton-Jones, 2014). If this is so, then RWAs would actually improve the quality of electronic representations of work. However, computer-mediated surveillance is limited by the data collected by information systems. These data may be different from the data that managers need to enact their own leadership practices (Cunha and Carugati, 2018). Moreover, computer-mediated interaction may create obstacles for employees sharing information about their work that does not fit into the categories reported by information systems (Alsharo et al., 2017). More importantly, research has shown that employees can use technology to provide an idealized account of their work (Berente et al., 2010;den Nieuwenboer et al., 2017). When employees do so, they create a façade that jeopardizes computer-mediated surveillance.
Computer-mediated interaction makes this façade more difficult to peer through. This means that producing useful electronic representations of work is something that employees have to do with technology, in addition to something that technology does on its own (Bisbe and Sivabalan, 2017). This pushes managers to establish the relationship of authority and the relationships for peer control that allow them to enforce employees’ role in providing information about their work (e.g., Brocklehurst 2001; Fogarty et al., 2011).
Control through standardization coupled with direct supervision is especially sensitive to the quality of electronic representations of work. It requires managers to have enough information to monitor employees and enforce compliance (De Church et al., 2010; Hoogeboom and Wilderom, 2015). Trust-based peer control can work without much data about people’s work (Loughry and Tosi, 2008). However, employees do need to know enough about what other people are doing to ensure that they are contributing effectively to the team (e.g., Barker, 1999). Control through identification requires little if any data about employees’ work. Nevertheless, employees will still need at least part of their work to be visible. These are the data necessary to present a positive identity to peers and to leaders (cf. Lippert and Dulewicz, 2018).
Managers’ practices in control processes in RWAs
The joint effect of computer-mediated surveillance and computer-mediated interaction on the relationship between autonomy and constraint is mediated by managers’ control practices, as they enact their organization's control mechanisms while enforcing employees’ links to their organization and the representation of employees’ work.
In RWAs, control mechanisms that focus on tasks require managers’ to establish a relationship of authority through computer-mediated interactions. It is in computer-mediated relationships of authority that managers can use the data provided by computer-mediated surveillance to enforce compliance.
Research shows that new supervisory practices are needed when organizations move to remote work. The challenge is to deal with the reduced access to employees caused by computer-mediated interaction, while avoiding the trap that computer-mediated surveillance and its potential for anticipatory conformity are enough to enforce compliance with prescribed procedure.
Control through standardization and control through identification in RWAs requires managers to use computer-mediated interaction to build relationships with remote employees that reinforce managers’ leadership (Porter and van Den Hooff, 2020). Managers can no longer rely on the acceptance of the relationship of authority as part of everyday life of working in the company’s premises (cf. Aghion and Tirole, 1997). RWAs weaken authority because interactions between remote workers and managers are limited by the electronic representations of work that ground computer-mediated surveillance (Dambrin, 2004). RWAs also weaken authority because computer-mediated communication opens up informal interactions between employees and other managers across hierarchical levels. Employees can address their challenges at work without the support, or even the knowledge of their managers.
Managers can respond by doubling down on a transactional leadership style. They can use computer-mediated surveillance to exert supervision without encroaching on employees’ sense of independence (Overbey, 2013). However, managers can also overcome threats to work ties and quality of electronic representations of work by increasing the frequency of interaction with remote workers (Lautsch et al., 2009).
Overall, the view is that managers can still enforce work procedures under the joint effects of CMI and CMS. However, doing so requires managers to engage in the everyday work of creating the conditions of authority that direct supervision requires, in the difficult context created by computer-mediated interaction (Lautsch et al., 2009).
This type of control in RWAs is different to control via standardization and control via direct supervision in face-to-face, conventional work arrangements. One key difference is the cadence of data about employees. In remote work, there is more frequent data about employees' achievements (Malhotra et al., 2007). However, there is less frequent data about employees’ work practices (Andressen et al., 2012). This means that there is less of an effort in monitoring people’s achievements. Nevertheless, it also means that there is more of an effort in enforcing procedure. The problem is that not only because there is less information to do so. It is also because there is more work in reaching employees and shaping their work practices effectively because of computer-mediated interaction (Neufeld et al., 2010).
Managers may need more data and information about employees’ work than that which they can obtain through computer-mediated surveillance. Here, the key challenge is establishing the authority to monitor work (Whitford and Moss, 2009). This imposes additional work on managers. Managers need to build a relationship with employees that provides enough of a view of employees’ activities, in addition to providing enough authority to impose practices and outcomes (Howell et al., 2005).
In RWAs, the effectiveness of control that focuses on coordination among employees depends on managers’ ability to establish two types of links. One is the individual links between employees and their organization. The other is the links among employees.
Establishing links between employees and the organization supports a control mechanism based on identification. Establishing links among employees also supports a control mechanism based on the compliance that employees enforce upon one another. These two sets of links are mutually constituted, but each type of control mechanism hinges more on one than the other.
Our literature review shows that managers cannot rely on remote employees to develop an identification with their organization and to establish group norms on their own (cf. Jordan, 2009).
Identification does develop in everyday remote work and norms do emerge in the everyday computer-mediated interactions among the members of a virtual team (Chi et al., 2012). However, neither of these processes may lead to the level of control that managers require if left unchecked and unaided (cf. Kirkman et al., 2002). In the absence of deliberate efforts to have employees incorporate the organization into their identity, remote workers may find other axes of identification. In the absence of deliberate efforts at building the trust that is necessary to ensure the power of norms to enforce compliance by the anticipation of peer pressure rather than by sanctions or rewards from leaders, virtual teams may not develop the power to impose social sanctions on its members in computer-mediated interaction (Lockwood and Forey, 2016).
The problem is the difficulties that physical isolation compounded by computer-mediated interaction brings to both processes. Physical isolation lowers the perception of being respected by the organization (i.e., treated in accordance with organizational norms). This weakens employees’ identification with their organization (Bartel et al., 2012). It also lowers the sense of group affiliation necessary for peer pressure (Kurland and Cooper, 2002). These effects may be exacerbated by the properties of the technologies that people use and by the tasks that they do (Malhotra et al., 2007), especially when computer-mediated interaction impoverishes everyday interactions among employees (Katz, 1987).
Moreover, the performance data that supports computer-mediated surveillance can take over how people are seen by others and how they present themselves to others. This narrows the range of ties between people’s identity and their organization. It weakens the power of identification as a control process. It also reduces the quality of the information that employees draw upon when imposing peer pressure upon one another. New procedures, and the computer-mediated surveillance of compliance therewith, can also make identification and belonging difficult. Bean and Eisenberg (2006) showed that when changing to remote work, employees may experience an identity disconfirmation. This is caused by new work routines and procedures which are monitored through computer-mediated surveillance. The problem is the link between work identity and people’s everyday work practices. People may struggle to build their identity around new work practices. However, they cannot hold on the former work practices without incurring into formal sanctions imposed by their managers or informal sanctions imposed by their peers. New practices in the move to remote work can also reduce the need for interaction among team members. This reduces the number and frequency of encounters where identification processes unfold.
Our literature review emphasizes four resources that managers can use to develop identification with the organization and to strengthen ties among employees.
First, managers can do so by enforcing occasional face-to-face interaction (Kimble, 2011). Face-to-face interaction can prevent the disidentification threatened by remote work (Ruiller et al., 2019). Oshri et al. (2007) showed that managers can use face-to-face meetings to improve ties among members of virtual teams, and develop and reinforce shared norms and meanings (Sivunen, 2006).
Second, managers can enforce work procedures that use recurring computer-mediated interaction. Recurring interaction, even if computer-mediated, gives employees a shared trajectory at work which taps into identification processes based on people’s shared experience rather than on their affiliation to their organization. Recurrent interaction also offers a set of relational iterations that allow groups to develop norms. These interactions also member to monitor one another. Frequent encounters help because of difficulty of employee engagement across computer-mediated interaction and the limitations of online communication.
Third, managers can use the material properties of IT to engender trust, when the technology that their employees use for work allows them to do so. Thomas and Bostrom (2008) showed how leaders can adapt technologies that support computer-mediated surveillance into transitional artifacts for facilitating the development of trust in virtual teams. This study and the broader research on boundary objects (Carlile, 2002) show that managers can use technologies for computer-mediated surveillance as artifacts which emphasize dependencies and shared goals to coordinate the work among team members. The data produced by such technologies create a sense of collective fate that also improves identification.
Fourth, managers can use computer-mediated interaction to build a shared organizational culture. The goal is to align employees’ activities to organizational objectives tracked via computer-mediated surveillance and use computer-mediated interactions to offer a set of values and beliefs that can be used to scaffold identities at work (e.g., Felstead et al., 2003). Moreover, shared values and beliefs engender similarity-based trust. This type of trust allows managers to lead the development of shared norms among team members across a sequence of computer-mediated interactions, anchored on specific data sets that anchor computer-mediated surveillance (Cramton and Hinds, 2014). Team members can use these data as proxies for compliance with team norms. They can impose peer pressure on people whose data shows deviation from prescribed procedure or failure to reach prescribed targets.
Overall, the view is that identification and team norms are also a key leadership achievement. The effect of this leadership on the joint effect of computer-mediated surveillance and computer-mediated interaction on the relationship between autonomy and constraint depends on how employees appropriate these managerial practices.
Employees’ practices in control processes in RWAs
Our review suggests a broader specification of the role of employees in the joint effect of computer-mediated surveillance and computer-mediated interaction on control. Employees shape control processes by taking advantage of computer-mediated surveillance to make their own work visible and by using computer-mediated interaction to make themselves reachable by their peers and leaders (Barsness et al., 2005; Youngblood, 2009). This adds a new domain of compliance and resistance. It shows that managers need to control the reporting of employees work and how much employees make themselves available to interaction with peers and managers. Only thus can they ensure that computer-mediated surveillance and computer-mediated interaction are both viable means of controlling employees’ work (Kurland and Egan, 1999). The problem is that employees can take advantage of both processes to create enough of a backstage where they can improvise their own work practices and improve their image, and to manage boundaries at work. Our literature review points to three sets of practices that employees use to do so (Felstead et al., 2003; Ruppel et al., 2013).
First, there are practices that employees use to manage the amount of effort that managers and peers have to put in to initiate interaction. The goal is to specify the amount and the modalities of computer-mediated interaction that each employee affords to their manager and to their peers. Research on RWAs highlights the use of computer-mediated interaction to do so. These studies show that employees can decide on work location to manage their co-presence with other employees. Baker et al. (2006) showed how employees can enact a variety of different sequences of face-to-face interaction and computer-mediated interaction. These patterns are informed by the technology that they use for work, their organization’s processes, and their relationship with their leader. In Baker et al.’s (2006) study, productivity was the chief criterion that employees used to decide whether to work at the office or at home. Other studies surfaced other factors that shaped this decision such as the complexity of work tasks (Biron and Veldhoven, 2016) and the configuration of relational dynamics at work (Katz, 1987) and at home (Kossek et al., 2006).
Research on RWAs also shows that employees can enact different practices of computer-mediated interaction to make themselves easier or more difficult to reach. Some studies show how people can improvise their own practices of computer-mediated interaction to manage their how available they make themselves to others. However, Belle et al. (2015) showed that employees may also need to negotiate with their peers to avoid mismatches between expectations about each other's practices with and around computer-mediated interaction. These studies describe a wider range of criteria that underlies employees' attempts at increasing or reducing their availability to others. Some of these criteria are linked to productivity and coordination. However, other criteria are based on access to ancillary resources such as obtaining emotional support (Collins et al., 2016), managing stress (Fonner and Roloff, 2012), and maintaining a sense of belonging (Dery and Hafermalz, 2016).
Second, there are practices that employees use to specify the quality of electronic representations of work. These are practices that employees use to provide information about their work and to present a valuable identity for themselves and others (cf. Dery and Hafermalz, 2016). Some studies show that employees can do so to establish a sense of self. Strawn (2009) showed that the frequent changes in work location can disaggregate the identity of remote workers. Remote workers can respond by restructuring their identity by setting up a specific space at their home, which is devoted to work. Participants also spoke about the importance of electronic representations of work in restructuring their identity. They used and computer-mediated interactions to affirm their identity and develop a sense of belonging. Research shows that their ability to do so is shaped by the nature of their work tasks, the norms of their organization, and the practices of their managers for computer-mediated surveillance (Chi et al., 2012; Tietze and Nadin, 2011).
Employees may also take advantage of computer-mediated surveillance to manage the electronic representation of their work to impress their leaders. Barsness et al. (2005) found that remote workers enacted a set of practices to compensate for the limited data that supervisors had about their work. In their study, participants who spent more time working remotely made more efforts to improve their relationship with their supervisors. They used the material artifacts that constituted computer-mediated surveillance to make their accomplishments more visible to their managers. However, employees may also attempt to make their work less visible. Sewell and Taskin (2015) showed that, after the intensification of control following the introduction of remote work, employees “reterritorialized their experience” by making their actions and achievements more opaque to their company. In this study, remote workers worried about how they would be perceived by managers and peers. They used absence and distance to find refuge from managerial intrusion.
Third, there are practices that employees use to build a boundary between work and their personal life, which impact both how open they are to interaction and how visible their work is. The goal is to preserve their work/life balance. Lal and Dwivedi (2010) showed how remote workers separated the work and the home spheres by allocating specific time and space to each domain. Moreover, home-based teleworkers can enact different practices actions to reduce computer-mediated interaction with the office outside the work domain. Some of these are practices that people can enact on their own. Employees can use time, space, and technologies as cues to delineate work–life boundaries and to transition between professional and personal roles (Fonner and Roloff, 2012). However, employees may need to negotiate with managers and peers to ensure that their work life boundary is spared from recurrent work intrusions (cf. Collins et al., 2013). This is not only about interaction but also about reporting and monitoring. This boundary allows employees to present an image of professionalism and commitment even when interrupting work for personal activities that enabled recovery or that allowed them to deal with situated challenges in their personal sphere. Additionally, employees may also have to negotiate domestic duties (with partner) and emotional boundaries (with parents) to avoid domestic intrusions into work (Tietze and Nadin, 2011). This allows them to avoid, or at least limit, interruptions at work caused by the availability to others in their personal life enabled by co-presence at home.
Overall, our literature review suggests that the structural conditions for control in RWAs add a burden of representation in computer-mediated surveillance compounded by a burden of contact in computer-mediated interaction for employees. Employees who accept compliance with procedures, goals, norms, and rules still need to make an effort to participate in computer-mediated surveillance and computer-mediated interaction to make their work visible to and themselves available to their managers and to their peers. Employees who reject such compliance need to engage in the difficult challenge of participating in these two processes by keeping enough invisibility and unavailability for effective resistance, but not enough to invite sanctions and jeopardize their attempts at keeping and presenting a valuable identity.
Taken together, the above review of the practices of managers and the practices of employees in computer-mediated interaction and computer-mediated representation in remote work arrangements adds an accessibility axis to computer-mediated control, which we discuss next.
A dual-axis model of computer-mediated control
Our review of the literature on RWAs shows that computer-mediated interaction (CMI) and computer-mediated surveillance (CMS) have a powerful joint effect on control in organizations. The challenges that we surfaced for managers in RWAs show that together, CMI and CMS turn employees’ reachability (the extent to which employees are open to interaction) and their visibility (the extent to which there is information about employees’ work) from a subproduct of place and technology into an accomplishment of employees, impacted by the practices of their managers.
Described thus, the joint effects of CMI and CMS should not just be specified as a shift in the axis of authority towards more or less autonomy or control (cf. Zorina et al., 2021). Instead, the joint effect of CMI and CMS is best specified as imposing an additional burden on both managers and employees. This opens up a new, contested domain of control in organizations. Managers have to monitor, and do their best to enforce, whatever practices and processes are necessary to make sure that employees make themselves reachable and make their work visible, in addition to monitoring and enforcing compliance with procedures and targets.
Next, we specify this new domain of control, which we label the axis of accessibility, and the burden that it imposes on managers and employees. We then use this new domain of control to specify constraint and autonomy as a position in a two-dimensional space that links this new axis of accessibility with the axis of authority described above. The conclusion explores the broader implications of this new, dual-axis model of control.
The axis of accessibility in computer-mediated control
Accessibility is a new domain of control opened up by remote work which can be represented by a two dimensional space defined by employees’ openness to interaction (reachability) and their diligence in reporting on their work (visibility) (see Figure 2). Reachability and visibility are requirements for control which have been delegated to technology. They have been attributed to the functionalities for interaction of the technology that people use to communicate (e.g., Fay and Kline, 2011) and to the informating property of technologies that people use to work (e.g., Leclercq-Vandelannoitte A, 2020). The challenges imposed by the joint effects of CMI and CMS which we surfaced in our review of research of RWAs suggest that the joint effects of CMI and CMS weaken the quality of ties and lower the quality of electronic representations of work. These challenges require employees to take on the burden of making themselves reachable and make their work available. Employees may not be able or may not want to simply delegate these accomplishments to technology at work. Accessibility in technology-mediated control.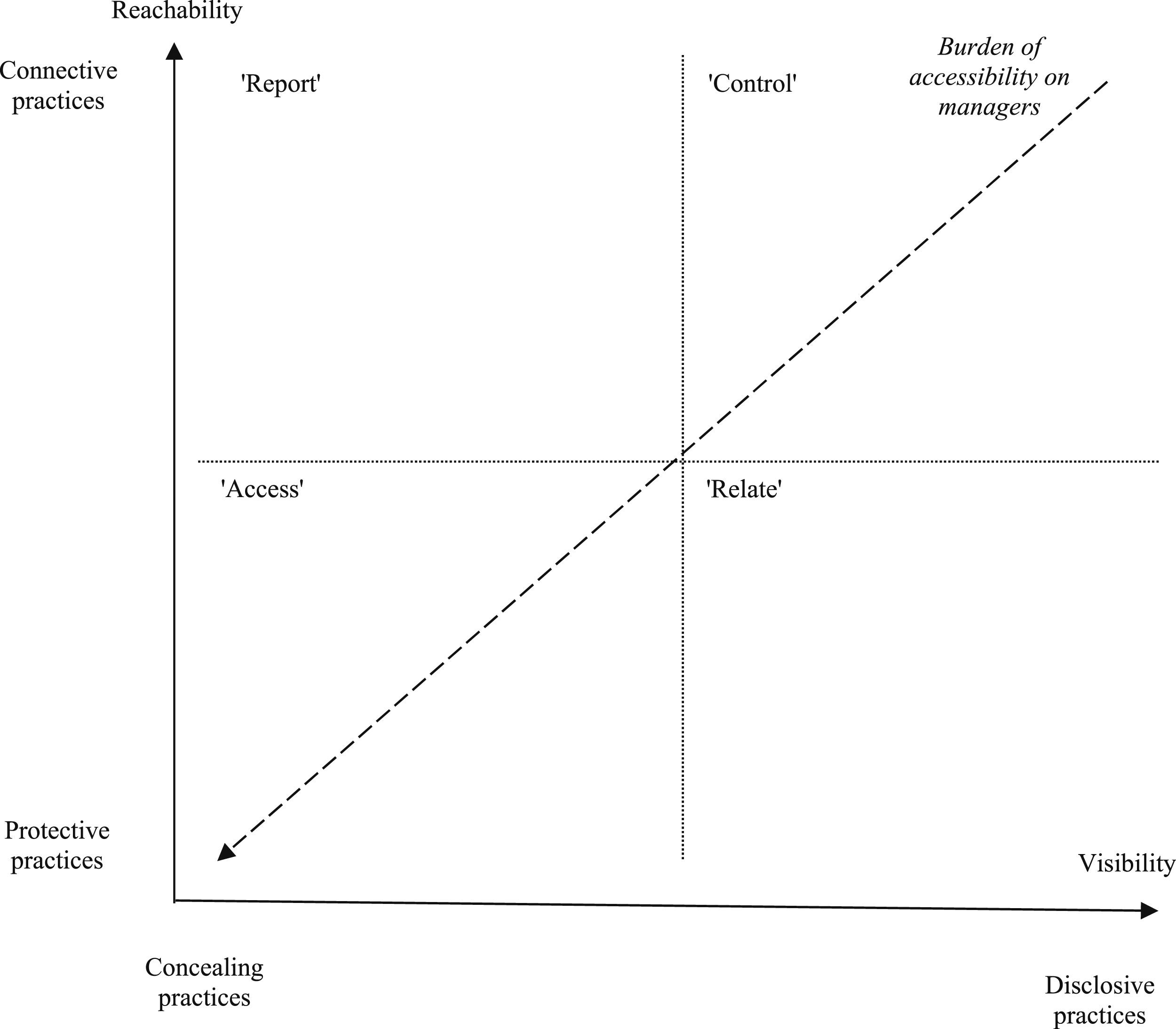
When employees do take on this burden, the power of control mechanisms (i.e., their ability to constrain and specify people’s actions and achievements at work) depends on employees’ position in a space specified by their reachability (which shapes the quality of ties at work) and visibility (which shapes the quality of electronic representations of work), depicted in Figure 2. This space maps the power which employees afford to their organization. It also which specifies the most effective path for managers to improve the power of control mechanisms, and ultimately maps the burden that the joint effect of CMI and CMS imposes on managers. This specification expands the opportunities for agency available to both employees and managers in control processes at work. However, it recasts agency in control as an additional obligation at work, rather than simply as an opening to further one’s own interests.
We outline each of these two dimensions of accessibility under the joint effect of CMI and CMS and discuss their relationship and their effect on control.
Employees’ visibility
Visibility specifies how easy it is to monitor employees’ practices and performance. Our literature review shows that employees’ decisions about the visibility of their work do not change the amount of effort that they have to put into making their work visible. Instead, they change the type of practices that they must enact to do so. Research on technology and control specifies visibility as an outcome of the technologies that support CMS (Sergeeva et al., 2017). The employee practices that we surfaced in our literature review add that when employees are subjected to both CMS and CMI, visibility is an outcome of the links between both processes.
The joint effect of CMI and CMS foregrounds the mutual constitution of interactions and data in how employees manage their visibility. The three control mechanisms that we surfaced in our literature review show that in work arrangements that combine CMI and CMS, it is upon interpretations of data shared in interaction that managers and peers assess compliance with prescribed procedures and prescribed outcomes. Two of the three types of employee practices in control processes in RWAs that we surfaced in our literature review specify this joint effect of CMI and CMS. First, the practices that employees use to report their work allow them to shape the data that others draw upon and those that they select away, and also the data that others pay attention to, and the data that they do not. Employees do so to develop and reaffirm their identification at work. Employees can also use interactions to further frame data about their actions and achievements and thus shape others’ interpretations of their effort and accomplishment. When they do so, they are also building and improving the image that others have of them. Second, the practices that employees use to manage work/life boundaries further empower them to manage the visibility of their work by offering them a backstage that others only see when employees report about their actions and activities and interpret them in interaction.
Moreover, the data about employees’ work that is shared in computer-mediated interactions with managers and peers may only partially be produced automatically as jobs that allow for CMI and CMS are more difficult to track through the informating effect of technology (e.g., Cunha and Carugati, 2018). This puts the relationship of authority at the core of the process of reporting in organizations, which provides the data that ground the computer-mediated interactions where managers and peers exert control over each employee’s work. It highlights that the informating property of technology may not be enough to provide data about employees’ actions and achievements (cf Burton-Jones, 2014). Our review on managers’ practices in control processes in RWAs shows that when this is the case, it is managers that have to enforce the frequency of reporting, the breadth of data collection, and the proportion of data that must be entered by employees. The interactions that managers use to do so offer employees opportunities to shape what and how much managers and peers see of their work by accepting, negotiating, or resisting the attempts of managers and peers at enforcing the burden of visibility.
Specified thus, reporting and interpreting data are not only roles that employees can profit from, they are also obligations that others impose upon them in interaction. The joint effect of CMI and CMS turns visibility from an automatic product of technology or an unintended outcome of co-presence (cf. De Vaujany et al., 2021) into a new additional type of work that requires effort. Employees may take on this burden to address the problems imposed by the key role that electronic representations of work play in computer-mediated surveillance. However, they may also do so to take advantage of the opportunities offered by this new form of interaction to improve their coordination with others and to enhance their participation in their relationship of authority with their managers.
Employees’ visibility practices that we surfaced in our review can be classified in one of two categories. First, employees can enact disclosive practices. These are practices where people report their work and use those data in computer-mediated interactions to improve the information, insight, and knowledge available to others. When doing so, employees improve others’ ability to act upon their own actions and achievements. However, they are also providing better resources for their managers and peers to monitor and control their work. For mechanisms at the “constraint” end of the axis of authority, disclosive practices such as following the reporting procedures that support computer-mediated surveillance, allow employees to provide evidence of compliance to their managers, and improve the data and the interpretations that contribute to decision making and to their organization’s strategy process. For mechanisms at the “autonomy” end of the axis of authority, disclosive practices such as the use of computer-mediated interactions to enforce group norms allow employees to display and impose on-norm behavior which is tracked by information systems and to provide the data and interpretations that improve coordination.
Second, employees can also enact concealing practices. These are practices where people under-report their work and where they pick self-serving performance data in their computer-mediated interactions with others. Some of these practices are for impression management. Their goal is to exclude data that would jeopardize the image that people want to present at work. Other practices are to improve work autonomy or at least to reduce the power of managers and peers to impose procedures and norms. For control mechanisms that impose compliance with procedures, concealing practices such as misrepresentation of their work in information systems allows employees to create enough of a gap between work practices and their electronic representation to present an image of compliance in interaction. For control tasks that allow for employee autonomy, concealing practices such as the enactment of off-norm behaviors away from the electronic front stage of computer-mediated interaction, allow employees to hide evidence of off-norm behavior which is tracked by information systems.
Specifying visibility as something that employees do further underscores employees’ agency in control processes under the joint effect of CMI and CMS. However, it recasts that agency as an additional obligation at work, rather than simply as an opening to further one’s own interests. Nevertheless, employees can take advantage of their role in recording and reporting data about their work to impress their leaders and to advocate for specific decisions and policies. Employees can also take advantage of the work that visibility entails to specify how much control managers exert on their work practice by providing evidence of compliance with procedures and processes, rather than providing accurate information about their work practice.
Employees’ reachability
Reachability specifies how easy it is to initiate the interactions where managers and peers can enforce compliance with processes and outcomes. Our literature review shows that making oneself difficult to reach may entail as much work as making oneself available for interaction with others because doing so is not simply about withdrawing from interaction. It also entails building and sustaining boundaries.
In computer-mediated environments, reachability is attributed to the functionalities and affordances of the technologies that support computer-mediated interaction (e.g., Collins et al., 2016). However, our literature review shows how the joint effect of CMI and CMS foregrounds the mutual constitution of interactions and data in how employees manage their reachability.
The three control mechanisms that we surfaced in our literature review show how in work arrangements where there is CMI and CMS, computer-mediated interactions are also prompted and mediated by data. The cadence and content of reports specify new opportunities and the challenges that employees face when making themselves more or less available for interaction with managers, for control through supervision or identification, and with other employees, for control through peer pressure. Performance data can prompt managers and peers to reach employees for interpretations, knowledge and insight. Performance data can also have managers and peers reach employees for addressing changes in performance and for enforcing prescribed processes and targets. When managers and other employees do so, they add to the demands on reachability that employees need to address in their everyday work for coordination. They may prompt employees to make themselves easier to reach through computer-mediated interaction. At the very least, they increase the difficulties that employees face when of fending off such attempts.
Two of the three types of employee practices in control processes in RWAs specify this joint effect of CMI and CMS. First, there are the practices that employees use to manage the amount of effort that managers and peers have to put in to initiate interaction. Employees may reduce their accessibility to improve productivity and reduce stress. They may increase accessibility to improve coordination, especially when working on complex distributed tasks. Second, there are practices that employees use to manage work/life boundaries. Employees can make themselves easier to reach to ensure that they build and develop the connections that afforded them a sense of belonging and allow them to participate in dynamics of informal power and politics at work. They may make themselves more difficult to reach to protect their personal time.
These practices show reachability is not simply a property of technology which employees enact as an unintended consequence of their everyday work. It becomes a burdensome outcome that requires effort. This effort, however, also allows employees to improve the structural conditions for the control of their work. Employees can enact reachability practices that overcome the limitations and constraints imposed by the joint effect of CMI and CMS. By doing so, they improve on the interactions that they would have face-to-face, instead of just dealing with the limitations of computer-mediated interaction anchored on electronic representations of work.
The reachability practices that we surfaced in our review can be classified in one of two categories. Employees can use connective and protective practices to manage their reachability. Connective practices are attempts at opening up communication channels with others at work. These channels are built in everyday computer-mediated interaction with and around the data that ground CMS. Employees’ connective practices are shaped by their organization’s control mechanisms. When the control of work is based on compliance with procedure and targets, connective practices such as using electronic communication with managers to convey information about their work allow people to enact a set of communication routines with their managers anchored around performance data that support the processes of control in relationships of authority and allow managers to enforce compliance. When the control of work is based on peer coordination, employees use connective practices such as enacting recurrent routines of computer-mediated interaction to provide interpretations of information about their work to help coordination and enact the identification processes that support this type of control.
Protective practices are attempts to close down communication channels with others at work. Employees close down communication channels by pacing their computer-mediated interactions with others. They can also do so by limiting the information that they share with others through technologies that support CMS. For control systems that enforce compliance with procedures and targets, protective practices such building and bolstering boundaries between work and personal life allow employees to deviate from prescribed procedure without incurring sanctions or enduring their managers’ attempts at enforcing compliance. For control systems that focus on coordination among employees, protective practices such as reterritorializing experience to keep some of their actions and achievements (or lack thereof) for themselves allow employees to protect the image that peers have of them while their team’s attempts to impose team practices and team norms.
Connective and protective practices show that specifying reachability as something that employees do uncovers a new set of opportunities for employees to achieve their own interests at work. Employees can shape their computer-mediated relationships with their managers and peers to specify the power that both sets of people have to impact their conditions for action. Employees can strengthen or weaken the relationships that are necessary for control, rather than change their work practices to cope with control. However, connective and protective practices show how agency in reachability is something that managers need to enforce, rather than fight against.
Managers’ response to employees’ practices for reachability and visibility
The foundational role that accessibility plays in the conditions for the control of work each of the three control mechanisms we surfaced in our literature review, means that managers need to enforce enough reachability and visibility to support the control mechanisms that ensure that employees comply with prescribed procedure and outcomes at work. This does not mean that the joint effect of CMI and CMS on the control of work is to reduce managers’ ability to enforce work procedures and targets. Instead, it means that there is more of a burden on managers to create the conditions for whatever control mechanisms they use.
Our literature review shows that the key challenge for managers is to establish a relationship of authority mediated by electronic representations of work and computer-mediated interaction. The relationship of authority is foundational for control mechanisms, no matter where they land in the axis between autonomy and constraint. Control mechanisms that enforce compliance then require managers to use the relationship of authority enforce visibility and reachability practices of work that allow managers to monitor whether employees follow prescribed procedure and impose conformity therewith.
Control mechanisms that allow autonomy require managers to use the relationship of authority to ensure that employees report enough information about their work and make themselves available enough to enforce compliance upon one another.
The specific mix of visibility and reachability practices that managers need to enact to ensure the conditions necessary for control depend on the position that their employees occupy in the two-dimensional space specified by reachability and visibility. However, the further employees’ accessibility is from the origin of the graph, the less work managers have to put in changing visibility and reachability practices because employees enact connective and disclosive practices in the course of their everyday work. This is represented by the dashed arrow in Figure 2 which shows that the burden of accessibility on managers is highest at the origin of the graph, where employees combine concealing practices with protective practices.
Figure 2 can be divided into four quadrants, named after the key goal for managers’ practices. In the “access” quadrant, employees provide very little visibility and reachability. This is the quadrant that requires more effort from managers because employees do very little of the accessibility work necessary for effective control. Our literature review emphasizes disidentification as the main driver for employees’ refusal to make their work visible and make themselves available. In the “report” quadrant, employees do not provide enough of information about their actions and achievements for managers and peers to enforce compliance. However, they do enough to make themselves reachable for coordination and leadership. In this quadrant, the challenge for managers is to enforce compliance with reporting procedures or risk that mechanisms of control are based on narratives and interpretations provided in interactions. These interpretations can be crafted to achieve a variety of goals, which may have little to do with compliance with procedures and targets.
In the “relate” quadrant, the challenge is the opposite. The information that control mechanisms require is there, but employees do most of their work in a backstage where they are difficult to reach by managers and peers attempting to coordinate their tasks and ensure that they comply with work procedure. The challenge for managers is to first connect with employees to establish a basis of authority and then enforce uses of communication technologies that ensure that employees can be reached by managers and peers for the different types of interactions required by each control mechanism. In the “control” quadrant, employees take on much of the burden of accessibility, allowing managers to focus on the everyday work required by whatever control mechanism they use to monitor and enforce compliance.
The practices that managers enact in each quadrant to improve accessibility, which we found in our literature review, can be classified in two different approaches.
Managers can take a directive approach to improve their employees’ accessibility. This approach attempts to shape the specific practices and processes that employees use to make themselves reachable and to make their work visible. The directive approach entails enforcing communication protocols which ensure that employees are available during work hours and beyond, much like companies did during COVID lockdowns (Kniffin et al., 2021). It also entails enforcing interaction to check upon and improve the data that employees report in information systems and framing this reporting work as an occasion for knowledge sharing and development rather than as an occasion for monitoring.
Managers can also take a permissive approach. This approach gives employees more autonomy in choosing the practices that they use to make themselves reachable and visible. Instead, managers attempt to improve employees’ availability indirectly. Managers do so by shaping the interpretations that specify how much employees are willing to improve their availability and by building trust with, and trust among employees. Managers can also increase employees' accessibility by improving employees’ identification with their work. Managers can improve employees’ identification with the organization, identification with their role therein (so as to be subjected to authority or peer pressure), and identification with the representations of their work. Higher levels of identification anchor employees’ self-worth in their relationships with others at work, and in the image they convey in interaction, prompting employees to make themselves easier to reach and to make their work more visible.
Overall, our literature review shows that the practices that managers use to improve reachability and visibility are different from the practices that they use to control the actions and achievements of remote workers. The latter are anchored on work procedures and goals and compliance therewith can be monitored through information systems (Leonardi and Treem, 2020). The former are anchored on interpretations, frames, and relational habits, and leave only indirect traces in reports and communication logs and in the metadata of the records of employees’ work in information systems. These differences between the mechanisms to control accessibility and the mechanisms to control work show that these are two different challenges for managers and that effort on the one axis of control does not exempt managers from effort on the other.
Reachability and visibility can be combined to specify the level of accessibility of each employee across a one-dimensional axis. This axis can be mapped against the axis of authority to provide a broader specification of the level of constraint and autonomy over employees that takes into account the joint effects of CMS and CMI and therefore asses this joint effect on control.
A two-dimensional model of computer-mediated control in organizations
The level of accessibility specified by the level of visibility and reachability of employees can be mapped against the level of autonomy specified by the control mechanisms that they are subjected at work. Together, they define a two-dimensional space that links the autonomy/constraint imposed by different control mechanisms with the power that people’s accessibility affords to each of those mechanisms, as illustrated in Figure 3. A dual-axis model of control under the joint effect of computer-mediated interaction and computer-mediated control.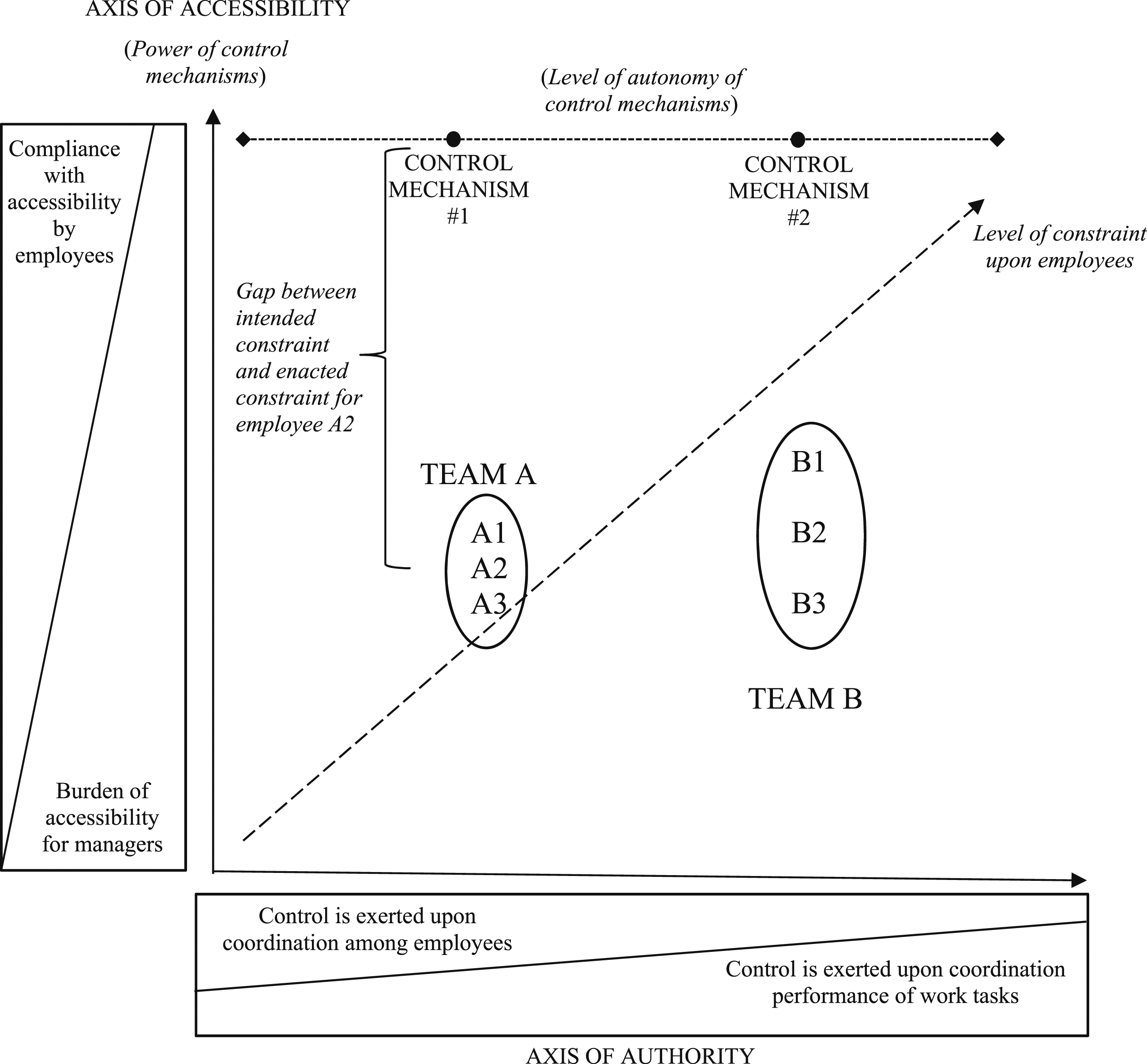
This two-dimensional space can be used to map the constraint that organizations, and managers as their agents, attempt to impose on employees, and the autonomy that employees are able to carve for themselves. For organizations, the position that they enforce upon employees is a choice about the level of autonomy in deciding work practices and also a choice about the burden of accessibility that they want to impose. The goal is not only to ensure that there is enough visibility and reachability for control mechanisms to be effective but also to improve coordination and to achieve broader organizational ends such as employee integration and knowledge sharing. This specifies accessibility as a design issue for control mechanisms, which is shaped by, but also shapes the control mechanisms that companies use to coordinate and control employees’ work. Figure 3 provides a simplified representation of the position of control mechanisms in this two-dimensional space by stipulating that control mechanisms expect full accessibility to employees, to their actions, and to their accomplishments. This is a simplified representation of control mechanisms to the extent that the literature on each control mechanism could be reviewed to assess the resistance that each may trigger and use this information to place each control mechanism in this two-dimensional model of computer-mediated control in organizations. However, for the purpose of outlining this model and assess its value, the key insight is that there is a gap between these prescribed positions and the positions specified by the individual level of accessibility that each employee enacts.
The simplest interpretation of the position of each employee on this space is that it is the effort that accessibility (distance on the vertical axis) adds to the effort that is imposed by procedures and targets (position in the horizontal axis). Specified thus, the position that each employee occupies in this space can also be used to assess their level of constraint, and therefore their difficulty in deviating from prescribed procedure and prescribed goals. Employees in the upper right quadrant of the graph have to achieve several prescribed targets following mandated procedures while at the same time reporting on those achievements and making themselves available to others. Deviating from prescribed procedure from this position is not just about improvising new work practices, but also improvising protective practices necessary to be able to do so without sanctions from managers and peers.
The position that each employee occupies can be compared with the position specified by the control mechanisms that they are subjected to and organizational expectations (or those that managers impose). The tension that results from the gap between these two positions completes the specification of the joint effect of CMI and CMS. This gap measures the extent to which employees weaken control mechanisms. It also maps the amount of accessibility work that managers need to impose to ensure that employees actually empower control mechanisms. Specified thus, this gap opens up a wide range of specifications for the joint effect of CMI and CMS on the relationship of authority. This gap can have managers come up with leadership practices that improve reachability while addressing the challenges imposed by computer/mediated work and reducing the burden that reachability imposes on employees. However, it can also lock managers and employees in an adversarial relationship as managers attempt to render employees and their work more accessible and employees hinder such attempts to maintain how much of a backstage their need for improvisation and impression management. It is the mix of practices to address this gap, rather than just its size, that specifies the everyday challenges that employees face when enacting practices for visibility and reachability in the course of their everyday work.
The next section looks at some of the implications for theory and practice of the dual-axis model of control that we specified from our literature review on control in RWAs.
Implications for theory and practice
Our dual-axis model of computer-mediated control suggests three research streams that can extend and expand research on technology and control in organizations. It also provides managers and employees with a set of practices to address the challenges that it uncovers for everyday work and leadership under computer-mediated control.
Implications for theory and directions for future research
First, our model argues for research on the key role of interactions in computer-mediated control. The focus of research on computer-mediated control has been on the production and use of data rather than on interactions (De Vaujany et al., 2018). The view is that the abundance of data in information systems allows managers to rely on control mechanisms that do not require interaction. Some studies suggest that abundance of data leads to anticipatory conformity, removing the need for monitoring and enforcing compliance entirely (cf. Burton-Jones, 2014). However, our review shows that employees’ interactions with peers and leaders are transformed rather than diminished in computer-mediated control. Our review shows how, in computer-mediated control, interactions are triggered and informed by data. Electronic representations of work prompt peers and leaders to reach to employees for interpretations and for coordination. Employees choose how to report data not only to inform others but also to manage how frequently others seek interaction and also to improve their autonomy and identification. There are two sets of studies that can help extend research by specifying the role of interactions in computer-mediated control. One set of studies can extend our explanation of employees’ practices in interactions for computer-mediated control into a relational process that acknowledges and explains the agency of leaders and peers in these interactions. Our model specifies peers and managers as sources of constraints on the practices that employees use to shape their availability for interaction. However, a comprehensive explanation of interactions in computer-mediated control requires an explanation of how managers and peers attempt to shape the extent to which employees make themselves available for interaction.
The other set of studies should explore the relationship between interactions for computer-mediated control and broader organizational processes. Our dual-axis model of control only incorporates proximate constraints such as the work procedures that specify employees’ job. However, the practices of employees and their managers are not only constrained but also enabled by broader organizational processes that cut across team and departmental boundaries. Incorporating the effect of these processes in the explanation of reachability (the extent to which employees make themselves available for interaction) and visibility (the extent to which employees make data about their work available to others) specifies a dual-axis model of control at the organizational level, rather than only at the level of the dyads of control with peers and leaders.
Second, our model enjoins research on the upward flow of information to overcome the divide between the production and the interpretation of data in the strategy process. The focus of these studies is on visibility (e.g., Cunha and Carugati, 2018). They show how employees can report their work to shape others’ interpretations of their performance and of the competitive challenges that their company is facing. The view is that electronic representations of work mediate the separate processes of producing data and of interpreting those data. Our review shows the value of considering the impact of reachability on visibility in the upward flow of information. It shows that the quality of data in a company’s information systems and the interpretations that peers and leaders build therefrom to monitor and control employees’ work is improved in interactions. Interactions allow peers and leaders to shape employees’ reporting practices. Interactions also allow employees to shape how peers and leaders interpret their data. Future research can explore how this mutual constitution of reachability and visibility impacts the production and interpretation of information in the strategy process, where the motivation for employees' representation of their work shifts from finding autonomy from control while ensuring coordination, into having a say in their company’s strategy.
Third, our review opens up accessibility (the joint effect of employees’ practices to report their work and their practices to make themselves available for interaction) as a new dimension of control which can be induced from previous research, but which remains largely unexplored. Our model offers the opportunity to open up the black box of the everyday labor that managers need to put in to make employees reachable and their work visible. Research on control has focused on how managers can use data about employees’ work to enforce compliance with work procedures and to improve work performance (e.g., Hafermalz, 021). The view has been that once employees adopt their company’s information systems, data about their work would be a subproduct of employees’ use of information systems to do their everyday tasks and that communication technologies allow managers to use these data to enforce procedure. Our review shows how managers may have to monitor and enforce the representation of work and also ensure that employees are available for the interactions where those data can be used to assess and enforce compliance. The focus of our review is on the burden that visibility and reachability impose on employees. Future research can expand the explanation of the labor of control by explaining the burden that it imposes upon managers and which managers need to carry out under the constraints imposed by employees’ reachability and visibility. By doing so, these studies can add a model of the everyday labor that control imposes on managers to that which it imposes on employees, improving the specification of the everyday labor required by reachability and visibility on the effectiveness of different mechanisms of control at work.
Implications for practice
Our review uncovers a set of shared challenges for managers and employees and points towards some practices that each group can use to address those challenges. Our dual-axis model of computer-mediated control warns managers and employees about the burden of reachability and visibility. It warns employees that when moving to remote work and other forms of computer-mediated control, they will need to cope with the burden of making their work visible and themselves available, but also exposes the new opportunities that employees have to carve more autonomy and to improve their participation in their company’s strategy process. It warns managers that the move to remote work imposes the additional labor of monitoring and enforcing visibility and reachability in addition to enforcing compliance with work targets and prescribed procedures, but offers opportunities to improve coordination and the quality of information.
Our review highlights the role of data-driven, computer-mediated interactions for managers and for employees to address the additional burden imposed by visibility and reachability in remote work and to take advantage of the opportunities that each offers.
Managers should focus on using their interactions with employees, rather than rethinking procedure and incentives, to have employees improve how they report their work and how they make themselves available to others. Managers should use interactions to get employees to share data that they use to do their work because it cannot be reported in their company’s information systems, and help managers and peers interpret these data. Managers should also use interactions to improve employees’ identification with their company and with their work, so as to reinforce managers’ authority and the power of peers to ensure that employees make their work visible enough, and themselves reachable enough to be able to monitor enforce compliance with targets and procedures.
Employees should focus on using interactions with managers to improve their career and carve autonomy by choosing the information that they share in interaction and by providing interpretations of those data in interaction that present an image of compliance and achievement. The goal is to reduce the motivation of others to monitor their work and to reach them for further information, while using data and its interpretation to present themselves as valuable members of their organization. Employees should proactively enact communication practices that set up a cadence that allows them to convey supplemental information and to share their interpretations of data which satisfies their managers and their peers, but which still leave enough of a backstage for employees to balance work/life and to be able to avoid sanctions for improvising with and around prescribed procedure.
The conclusion section next places the dual-axis model of computer-mediated control and its implications in the broader research on control in organizations.
Conclusion
Specified at its broadest, the joint effect of CMI and CMS on control is to anchor control on a set of representations that employees must produce and use in the context of the relationship of authority. This set of representations is built from records of employees’ work in information technologies and from traces of interactions in communication technologies. It is this set of representations that prompts, structures, and informs the interactions of managers and peers with individual employees where control is enforced and strategic challenges are interpreted. Employees build this set of representations when reporting their work in information systems and when giving and giving off expressions in the online communications which mediate the interactions where peers and managers monitor and enforce compliance with procedures and targets.
Our research shows that employees take on the burden of producing this set of representations and interpreting them in interaction first because this provides opportunities for agency over mechanisms of control, and therefore some agency over their autonomy at work. Second, employees also produce and use these representations in interaction because they allow them to deal with the personal challenges imposed by the joint effect of CMI and CMS, especially for their sense of identity and belonging. Third, employees also produce these representations because they allow them to comply with, or at least respond to, managers’ attempts at enforcing the visibility and reachability that control mechanisms need to be effective.
Looking at the production and use of representations of work and interactions in control processes and, more broadly in the relationship of authority, opens up a path to explore the burden of that IT imposes on control and its consequences. This burden has been understudied in research on IT and control because the panoptic effect of technology (Burton-Jones, 2014; Hafermalz, 2021), and the separate study of CMI and CMS (e.g., compare Macnamara and Zerfass, 2012; with Zorina et al., 2021), has hidden the axis of accessibility which we surfaced and specified through a review of control in RWAs. Exploring and explaining the work that accessibility imposes, and the tensions that it adds to the relationship of authority, open up a new set of challenges on how organizations design and managers enact control mechanisms. Control mechanisms need to expand from monitoring work into also monitoring and enforcing accessibility practices because the effectiveness of control mechanisms is contingent on employees’ visibility and reachability.
Overall, our message is optimistic (in the context of the bleak message of anticipatory conformity offered by research on computer-mediated control) as in spite of the burdens that it imposes, the joint effect of CMS and CMI offers employees more agency at work and it offers managers new challenges and opportunities for leadership.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
Appendix
Appendix 1—Summary of reviewed studies (listed in alphabetical order of first author).
Author(s)
Research goals
Type of remote work
Key constructs
Main control type
Summary findings
Alsharo et al. (2017)
Explain the relationship between knowledge sharing, trust, collaboration among members, and virtual team effectiveness
Virtual team
Knowledge sharing, collaboration, and trusting relationship among virtual team members
Trust-based peer control
The process of knowledge sharing was important to favor the development of a (cognitive) trust climate in virtual team. This increased members’ attitude to collaborate with each other, with positive effect on team effectiveness
Al-Ani et al. (2011)
Investigate the leader role in structuring group tasks and supporting socio-emotional processes in virtual team
Virtual team
Leadership role
- task role vs. socio-emotional process
- in communication
- in facilitating trustTrust-based peer control supported by leadership practices
The role of leaders regarding task and socio-emotional processes were the same for traditional and virtual teams. However, leaders in virtual teams (frequently identified by peers) were required specific competences (e.g., in organizing virtual meetings). As for communication, leaders initiated formal communications both in traditional and virtual teams while they had no role in facilitating informal communications among team members. Leaders supported trusting relationship among members, particularly they favored swift trust in virtual teams
Andressen et al. (2012)
Investigate the relationship between transformational leadership style, employees’ self-leadership, motivation, job performance, and affective commitment. Virtuality as the moderator
Virtual team
Transformational leadership style
Remote workers’ self-leadershipTrust-based peer control supported by leadership practices
The employees’ ability in self-leadership was important in all teams, particularly in virtual teams. When supported by a transformational leadership style, it allowed an increase of virtual team members’ motivation that, in turn, affected their job performance and commitment. However, the study found that the transformational leadership style was less effective when employees were too distant from their leaders
Baker et al. (2006)
Investigate the relationship between different forms of organizational support and employees’ reactions to home-based telework
Telework
Organizational support
- technology-related (e.g., IT support)
- somewhat technology-related (e.g., financial resources)
- no technological (e.g., trust)Input control based on teleworkers’ organizational identification
Employees’ satisfaction with teleworking is significantly influenced by both technological (i.e., IT support and appropriateness of technology) and non-technological (i.e., manager’s trust) organizational support. So, teleworkers believed that both the company’s investments in ICT were just as important as being empowered and trusted by their managers and colleagues
Barsness et al. (2005)
Explain the relationships among remote work, demographic dissimilarity, social network centrality, and the use and effectiveness of impression management actions
Telework
Performance assessment by supervisor
Impression management actions by remote workers (supervisory vs. job focused)Direct supervision#
The adoption of impression management actions increased with increasing remote work intensity. This relationship was not moderated by demographic dissimilarity, but it was affected by the position in the organizational network. Indeed, it was higher the adoption of impression management actions in the case of same-sex pairs and employee’s central position. Both demographic dissimilarity and network centrality affected performance evaluations by supervisors. Indeed, in mixed pairs, supervisors did not appreciate job-focused actions where they positively considered supervisory-focused actions. Higher performance evaluations were attributed to central employees
Bartel et al. (2012)
Investigate the relationship among employees’ degree of physical isolation, perceived respect in the organization, and organizational identification
Telework
Remote workers’ perceived respect and organizational identification
Input control based on teleworkers’ organizational identification
The amount of time employees spent working isolated by the organization had (negative) implication for perceived respect and organizational identification. Specifically, higher the physical isolation, lower the perception to be respected by the organization, thus resulting in lower level of employees’ organizational identification
Bean and Eisenberg (2006)
Understand changes in employees’ identity, organizational culture, and social structure during a major organizational transformation
Telework
Remote workers’ sense-making and identity disconfirmation
Organizational cultureInput control based on teleworkers’ organizational identification
Following the transition to remote work, all employees experienced an “identity disconfirmation.” For most of them, this identity disconfirmation was due to related changes in personal identity (i.e., how they perceived themselves as nomadic workers) while for a limited number of employees it resulted from changes in organizational culture and social structure following the adoption of nomadic work
Belle et al. (2015)
Understand the experience and the process of organizational belonging for a group of high-intensity teleworkers
Telework
Organizational belonging (and its relationship with organizational identification)
Input control based on teleworkers’ organizational identification
Organizational belonging is a concept that includes the employee’s need for a sense of community and organizational inclusion as well as organizational identification. Three avenues were relevant for high-intensity teleworkers’ organizational belonging: (1) they should choose telework as work arrangement; (2) they should negotiate with colleagues to preserve freedom and balance organizational and individual needs; (3) they should be informed about how they have to act, so as to maintain power and a state of confidence
Bentley et al. (2016)
Explain the role of organizational social support and specific support for teleworkers in influencing teleworker well-being
Telework
Organizational support as social support (i.e., colleagues and managers) and job-related support (i.e., ICT support)
Input control based on teleworkers’ organizational identification
Teleworkers appreciated—and thus felt more identified with the organization—when they perceived to be supported by the organization, managers, and colleagues. Organizational support reduced their perception of being socially isolated, limited psychological strain, and increased their job satisfaction
Biron and Veldhoven (2016)
Investigate the impact of work location on part-time teleworkers’ need for recovery and concentration
Telework
Remote workers
- job demand and control
- need for recovery and concentrationDirect supervision supported by standardization
Results demonstrated a lower need for recovery and higher ability to concentrate for teleworkers on home days than office-days, also in the case of high demanding jobs. However, the positive effect of home working on employees’ need for recovery was confirmed for medium job control but not for high job control. Indeed, too much control at home provoked anxiety, thus increasing the need for recovery. No differences emerged between medium and high control at the office. Finally, the ability to concentrate was higher at home than office in the case of high job demand, whatever the level of job control
Bisbe and Sivabalan (2017)
Understand the interplay between formal Management Control Systems (MCSs) and inter-personal trust in virtual teams
Virtual team
Interpersonal trust among virtual team members
Management Control System (MCS)Trust-based peer control supported by leadership practices
A formal MCS had been adopted in a virtual team whose members reported high inter-personal trust. As for trust-control nexus, MCS helped upholding inter-personal trust and, in turn, trust enabled the adoption and workability of incomplete and potentially sub-optimal formal MCS. It emerged a synergy between MCS and inter-personal trust since the former had a prominent decision-facilitating role where the latter decision-influencing role able to promote congruent behavior and provide motivational effects
Brahm and Kunze (2012)
Explain the relationship among virtual team goal setting, team cohesion, and team performance
Virtual team
Virtual trust climate
Virtual team goal setting and cohesion
Virtual team performanceTrust-based peer control
The capability to define common goals (goal setting) influenced positively the degree of cohesion among virtual team members and accordingly team performance. Virtual trust climate moderated the relationship between team goal setting and both team cohesion and team performance
Brocklehurst (2001)
Understand changes in power and identity following the transition to home-based telework
Telework
Home-based telework work identity
Peer control
Supervisory style and power re-distributionInput control based on teleworkers’ organizational identification
The introduction of telework provoked a change in power distribution that became more favorable to teleworkers. Indeed, they resisted to managerial control practices (e.g., home visits and electronic diaries) and escaped from peer control. Moreover, the introduction of telework led employees to build a new identity work, obtained through defining themselves as self-employed entrepreneurs and reproducing old habits and routines
Caillier (2013)
Investigate differences in teleworkers’ and non-teleworkers’ perceptions about management by objectives
Telework
Management by objectives (MBOs)
Teleworkers and non-teleworkers perceptions about
- to be managed by objectives
- managers’ ability to give feedbackDirect supervision supported by standardization
Results demonstrated that both teleworkers (both high and low intensity) and non-teleworkers perceived managers as able to manage by results and provide constructive feedbacks to employees, wherever they worked
Chi at al. (2012)
Explain the relationship among team characteristics, communication environment, and virtual team performance
Virtual team
Leader competence
Behavior control
Trust and communications among virtual team members
Virtual team performanceTrust-based peer control supported by leadership practices
Virtual team performances were affected by leaders’ ability in managing distant employees, the identification of standard norms and procedures to exert (behavioral) control, the level of trust among team members, task interdependence (team characteristics) as well as by available communication media and their easy to use (communication environment). Surprisingly, ICT information richness was not relevant to team performance. Leaders’ competences positively affected both task efficiency and communication satisfaction
Charbonneau and Doberstein (2020)
Investigate public employees’ and citizens’ perceptions about the reasonability and intrusiveness of electronic workplace surveillance tools implemented in the public sector for home-based telework
Telework
Surveillance
Trust
Performance management
BureaucracyDirect supervision
Electronic work surveillance tools, even if invasive, were accepted and tolerated when interpreted as related to support and monitor work productivity and performance (e.g., clickstream software and AI email analysis). In contrast, surveillance technologies outside the realm of work (e.g., photo capture and humanize badges) were generally viewed as too much intrusive and unreasonable. The study also revealed that “bureaucracy” affected the degree of technological surveillance adopted and accepted by employees in public organizations. Higher the bureaucratic environment, higher the electronic monitoring over employees. The perceptions of intrusiveness and reasonability of tools for workplace surveillance also depended from the people’s trust in colleagues and public employees. The more confidence people have in fairness of public workers, the more they consider intrusive and unreasonable the electronic work surveillance
Collins et al (2016)
Explore how home-based teleworkers, their office-based colleagues, and managers make sense of the social support relationships
Telework
Social support relationships with other teleworkers, office-based employees, and supervisor
Input control based on teleworkers’ organizational identification
The study demonstrated that perceptions and actions related to social support were different between office-based and teleworkers. Teleworkers developed stronger relationships with other teleworkers, mainly with those with whom they had a pre-existing relationship. They were proactive in exploiting ICT to obtain informational and emotional support from other teleworkers, while they disconnected from office-based workers seeing themselves as a distinct group with a distinct identity. Finally, most of them attached great importance to emotional support received by superiors. In contrast, office-based colleagues valued support from co-located staff (and not by supervisors) and, in their turn, felt to be a group distinct by teleworkers
Collins et al. (2013)
Explore the content of the employment relationship and expectations in terms of temporal flexibility and fairness of a group of homeworkers
Telework
Remote workers’ psychological contract with managers (e.g., for temporal flexibility)
Direct supervision
All full-time homeworkers desired temporal flexibility in order to achieve better work–life balance. Anyway, flexibility emerged as an ambiguous issue since supervisors, who had a great deal of control over homeworking conditions, differed in their implementation of temporal flexibility. Indeed, each home-based teleworker negotiated working hours with his/her own supervisor and did not perceive unfairness in the case colleagues obtained more favorable conditions as long as they achieved their own personal desired levels of temporal flexibility
Crossman and Lee-Kelley (2004)
Understand the role of trust and commitment in virtual organizations
Virtual team
Virtual team members’ trust and commitment
Trust-based peer control
All permanent or temporary virtual team members believed commitment and trust as fundamental in the work relationship. Anyway, they showed different level of commitment and trust that were affected by what each member perceived to receive from the group, the company, the European division (the so called reciprocity mechanism)
Dambrin (2004)
Explore the impact of telework on manager–employee relationship
Telework
Leadership style
Manager–employee relationshipDirect supervision supported by standardization
The adoption of telework had both positive and negative effects on manager–employee relationship. Specifically, it facilitated communications between distant hierarchical levels and increased employees’ ability in dealing with professional concerns without the manager. Then it increased teleworkers’ autonomy who were evaluated by results by their manager. However, telework reduced formal communication between employees and their direct manager thus favoring interpretation bias
Darics (2020)
Understanding how managers do leadership in through instant messages conversations considering non-verbal communications
Virtual team
Communication
Knowledge sharingTrust-based peer control
Non-verbal cues were important in digital communications to the same extent as to face-to-face interactions. In particular, the functions achieved by audio and visual nonverbal communications in face-to-face interactions were deliberately and creatively recreated in IM using orthographic and typographic means. These non-verbal cues served to emphasize, clarify, disambiguate meaning and intentions as well as to communicate hierarchical status
Dery and Hafermalz (2016)
Examine how remote workers use technologies to establish identity and favor organizational belonging
Telework
Remote workers’ organizational belonging and role of technologies, that is, mobile, social media, and cloud
Input control based on teleworkers’ organizational identification
Identity was intended as “the way we know ourselves and the way we would like to be known by the organization.” Remote workers used mobile, social media, and cloud-based technologies to “perform” their identity online with the aim of maintaining informal connections with colleagues and favor the recognition of their belonging to the organization
Dimitrova (2003)
Investigate the mediating role of work context on the relationship between the supervision style and teleworker’s autonomy
Telework
Supervision style
Manager–employee relationship
Work context (e.g., task)
Teleworkers’ autonomyDirect supervision supported by standardization
Supervisors’ style and control procedures depended on tasks, work schedule, and previous relationship between supervisors and employees (both teleworkers and office-based colleagues). Indeed, supervisors used the same supervision style and control procedures for employees performing the same activities and whom they had a similar previous relationship. The nature of task influenced teleworkers’ autonomy and flexibility
Drouin and Bourgault (2013)
Investigate which dimensions of organizational support contributed to the decision-making process and teamwork effectiveness in distributed project teams
Virtual team
Organizational support in—strategic staffing
- training and tools
- team autonomy
- top management monitoring
Local culture
Work practices
Decision-making process
Teamwork effectivenessTrust-based peer control
The decision-making process and related virtual teams’ work effectiveness were positively influenced by the appropriate selection of team members, following training about remote working, and provision of tools for effectively interacting and working with distant colleagues. The team autonomy was crucial to foster the quality of decision-making process in a highly cultural diverse context
Fay and Kline (2011)
Examine telecommuters’ relationships with office-based colleagues and how informal communication practices are associated with organizational commitment and job satisfaction
Telework
Remote workers’
- informal communications with colleagues
- communication satisfaction with office-based colleagues
- organizational commitmentInput control based on teleworkers’ organizational identification
Teleworkers did not appreciate complaining talks with office-based colleagues, and this compromised their job satisfaction and organizational commitment. An exception emerged in the case teleworkers had been able to establish a close relationship with office-based colleagues since they did not perceive complaining talks as stressing as it would be in the opposite case
Felstead et al. (2003)
Understand changes in traditional managerial control based on visibility and presence toward employees working at home
Telework
Managerial control
Manager–employees trusting relationships
Organizational cultureInput control based on teleworkers’ organizational identification
Supervisors adopted managerial practices to overcome the non-presence and non-visibility of home-based telework that included a great emphasis on trust and organizational culture as means to align teleworkers’ activities to organizational objectives. However, these managerial practices were frequently ineffective due to the lack of a strategic vision (not planned but emerging ad hoc) and the lack of understanding of the pre-existing social structures
Fogarty et al. (2011)
Understand office-based employees’ perceptions regarding formality and control towards remote workers
Telework
Control (formal and informal)
Employees’ perceptions about equity and organizational justiceInput control based on teleworkers’ organizational identification
Office-based employees preferred that the company adopt formal telework programs, that specifies in advance the rules related to teleworking, for example, they wanted to specify days of teleworking, even if this in practice could generate inflexibility for teleworkers in changing their plans to meet on-site colleagues’ needs. Finally, the study pointed out a paradox in equity perceptions, as formal telework programs guaranteed distributive and procedural equity, whereas informal programs guaranteed interactional justice
Fonner and Roloff (2012)
Investigate if communication media use affects teleworkers’ perceptions of social presence, stress from interruptions, and organizational identification
Telework
Remote workers’
- use of communication media
- perceptions of social presence
- stress from interruptions
- organizational identificationInput control based on teleworkers’ organizational identification
Connectivity increased stress from interruptions for high-intensity teleworkers and indirectly diminished their level of organizational identification
Fonner and Stache (2012)
Examine strategies used by home-based teleworkers to manage the work–home boundary and identify cues they rely upon to facilitate transition between work–home roles
Telework
Remote workers’ strategies for managing boundaries between work and private sphere (segmentation vs integration)
Input control based on teleworkers’ organizational identification
The strategy preferred by employees for managing the overlap between the professional and personal spheres at home (i.e., boundary management) was the “role segmentation.” In this regard, teleworkers preferred to engage in a complex process to separate work and family, rather than integrate the professional and personal roles. The study also evidenced that home-based teleworkers used time, space, technology/communications as cues to delineate work–life boundaries and aided transition between professional and personal roles
Gluesing (2009)
Explore remote workers’ identity evolution along with changes over time in job roles, work arrangements and technological development
Telework
Remote workers’ identity evolution
Input control based on teleworkers’ organizational identification
In examining her personal experience as remote worker, the author described how their identity evolved over time due to the changes in technologies and culture. She observed that the increasing availability of sophisticated technologies allowed her to maintain a unique identity, and not multiple mindsets and identities to manage different relationships and cultures. The author as evidenced a process of “cultural hybridization,” that is, different cultures had been integrated in the virtual space
Golden and Eddleston (2020)
Explore the relationship between telework and career success
Telework
Impression management
Career
Relationship of authority
Co-located vs. remote workersDirect supervision
Teleworkers did not differ from non-teleworkers in terms of promotions, although they did differ in salary growth. Teleworkers were penalized in terms of career success, mainly when they worked frequently at a distance (i.e., extensive telework). However, some contextual factors buffered this negative effect, and thus the “flexibility stigma.” Indeed, a greater number of promotions were received by extensive teleworkers in the case of high telework normativeness, additional time spent on work-related activities, and frequent face-to-face contact with supervisors
Golden and Fromen (2011)
Explain the impact of managers’ work mode (traditional, virtual work) on employees’ work experience and outcomes. Congruence of manager and subordinate work mode is investigated too.
Telework
Employees’
- work experience (e.g., professional development)
- work outcomes (e.g., job satisfaction)Direct supervision
Distant supervision and leadership was successful and impacted positively on work experience and outcomes when exerted over remote workers. In contrast, a less positive effect of distant supervision and leadership was registered when exerted over traditional office-based employees
Golden and Veiga (2008)
Investigate the moderating role of virtual work on the relationship between leader–member exchange and professionals’ commitment, job satisfaction, and job performance
Telework
Leader-member exchange (LMX, high VS low quality relationships between manager and employee)
Remote workers’
- organizational commitment
- job satisfaction
- job performanceDirect supervision supported by standardization
The degree of virtual work moderated the relationship between LMX and professionals’ outcomes. Indeed, in the case of a strong relationship between leader and member, an extensive virtuality affected positively professionals’ commitment, job satisfaction, and performance. In the case of low quality relationship, an extensive virtuality influenced negatively professionals’ commitment and job satisfaction but increased their performances
Goldmacher (2009)
Explore boundary management in the case of located mobility, that is, simultaneously (but temporary) living and working in more than one space (city/country)
Telework
Remote workers’ attempts in managing boundaries between work and private sphere and emotional connections
Input control based on teleworkers’ organizational identification
The author reported her own experience as remote worker living in one city, and working in another city. She felt to belong to both spaces (i.e., cities) and this implied the need of managing multiple work–family boundaries. As for emotional connections, she recognized the importance of being “flexible in emotional connections.” Anyway, she was interested in demonstrating her presence only to her community while she had no interest in building new relationships in the “temporary” city
Groen et al. (2018)
Investigate the relationship between the implementation of telework and the emphasis on output control
Telework
Technology adoption
Telework intensity
Performance evaluationOutput control
The intensity of teleworking was positively related to the adoption of output control by managers. This means that higher the number of hours spent teleworking, higher the adoption of evaluation systems where employees are assessed on the basis of the achievement of objectives. Nevertheless, employees who are allowed to telework reported less emphasis on output controls by their managers relative to those not allowed to telework
Hakonen and Lipponen (2008)
Explain the relationship between perception of procedural justice and virtual team identification
Virtual team
Virtual team members’ perceptions of procedural justice and team identification (at group level)
Trust-based peer control
Results evidenced a positive relationship between virtual team members’ perceptions of procedural justice and virtual team identification. This link was stronger in the case of teams whose members were highly dispersed and rarely met face to face
Halford (2005)
Explore the implications of hybrid workspace, that is, how spatial flexibility changed the nature of work, organization and management across domestic space, organizational space, and cyberspace
Telework
Working practices
Organizational relationships
Managerial practicesDirect supervision
Spatial hybridity implied distinctive power relations between supervisor and employees, and managerial practices across domestic space, organizational space and cyberspace. Anyway, emphasis was always put on the importance of building personal relations with staff whatever the space
Spatial hybridity also affected the nature of work practices that employees performed in each space, and the way they managed organizational relationships. Specifically, employees maintained two distinctive sets of working practices in terms of what they do in different spaces and how they do it. In terms of organizational relationships, hybrid workspaces strengthened sociability both in “place” (i.e., employees physically meet in the office) and in virtual space where employees used e-mail and phone calls for personal exchanges
Hall and Atkinson (2006)
Understand employees’ perceptions about flexible work
Telework
Employee control
Direct supervision
Teleworkers preferred informal flexible work programs (e.g., where the intensity of teleworking was not specified in advance), since they really appreciated to be autonomous and empowered by their organizations
Han (2006)
Explore the relationship between tenure diversity and individuals’ perception of leader support and the incidents of Organizational Citizenship Behavior in global virtual teams
Virtual team
Virtual team members’ perceptions of leader support
Organizational Citizenship behavior OCBDirect supervision
This study evidenced that the leader support was important for virtual team members’ Organizational Citizenship Behavior (OCB). Indeed, lower the team members’ perceptions of leader support, lower the collaborative behaviors with colleagues. In this regard, the study evidenced that employees’ tenure affected the perceptions of leader support. Indeed, higher the differences in tenure compared to others, lower the support a team member perceived to receive from the leader
Harris (2003)
Examine the experiences of salespeople following the transition to full time home-based telework, and related managerial challenges and dilemmas
Telework
Employer–employee relationship
Managerial practicesInput control based on teleworkers’ organizational identification
Findings revealed the importance for managers to support employees in coping with the difficulties in managing work–family boundaries and pay close attention to family-related issues in implementing a full time telework program. Indeed, salespeople perceived a trust violation when they transitioned to full time home-based telework. They perceived to have been abandoned by managers for work issues (e.g., they worked harder and longer and they felt more stressed) and mainly for family issue, that is, managing the blurring of work and family life
Hill and Bartol (2016)
Investigate the extent to which distributing leadership to team members (empowering leadership) favors virtual collaboration and performance in dispersed teams
Virtual team
Empowering team leadership
Virtual team collaboration and team performanceTrust-based peer control supported by leadership practices
At team level, empowering leadership (i.e., sharing power with team members) had a positive impact on team members’ aggregate virtual collaboration, and indirectly on team performance, that increased at higher level of team dispersion. At individual level, under condition of high empowering team leadership, a team member’s virtual teamwork situational judgement was positively associated with his virtual collaboration behaviors and indirectly with his individual performance in the team
Hoegl and Muethel (2016)
Investigate relationship between shared leadership behaviors and virtual team performance
Virtual team
Shared leadership style
Virtual team performanceTrust-based peer control supported by leadership practices
Shared leadership, and therefore the attribution of autonomy to team members, was paramount for virtual team performance. Indeed, team leaders who underestimated the shared potential of their team members unconsciously jeopardize team performance by not sharing leadership
Howell et al. (2005)
Explain relationship between leadership style and business unit performance, considering supervisor–follower distance
Telework
Leadership style
-Transformational
- Transactional
Business performanceDirect supervision supported by standardization
Transformational leadership affected positively business unit performance. Physical distance moderated this relationship since it largely depended on senior managers’ capabilities in inspiring subordinates at a distance. In the case of supervisor–follower distance, a transactional style was preferred since branch manager perceived higher freedom in choosing how to reach objectives
Hunton and Norman (2010)
Explain the relationship among alternative work arrangements, organizational commitment and task performance
Telework
Employees’ organizational commitment
Task performanceInput control based on teleworkers’ organizational identification
Teleworkers showed a higher level of organizational commitment than non-teleworkers, particularly when supervisors allowed to choose among multiple locations (i.e., not just home). Teleworkers’ commitment was crucial since it affected positively their job performance
Igbaria and Guimaraes (1999)
Explain the relationship among telecommuting and employees’ work stressor, job satisfaction, commitment, and turnover intentions
Telework
Telecommuters’ and non-telecommuters’
- perceptions about work stressor
- job satisfaction, commitment, and turnover intentionsInput control based on teleworkers’ organizational identification
This study evidenced positive effects of telework on employees. Compared to office-based colleagues, employees who had the opportunity of telework were less stressed, more satisfied, higher committed and had lower intentions to leave the organization
Jordan (2009)
Changes in behavioral patterns and social connections in the transition to remote work
Telework
Remote workers’
- behavioral patterns and social connections
- boundary keepers and integratorsInput control based on teleworkers’ organizational identification
In the initial transition to remote work, author reported an identity crisis resolved by a symbolic cue (a new business card). She had not specific office space at home, whereas she recognized wider opportunity in public spaces (e.g., lounges in airport). She identified 2 boundary management strategies, that is, keepings or integrators; both assumed new norms and rules in managing the work–family interface. She underlined that remote work required to invest greater energies in social relationships and reported the fear that colleagues do not appreciate her work
Julsrud (2008)
Understand the mechanisms that generate different types of trust among members of inter-organizational distributed work groups
Virtual team
Trust among members of distributed work groups
Trust-based peer control
Within inter-organizational distributed work group, cognitive trust was more widespread than affective trust, with several “boundary crossing” among members of the two groups. Affective trust was established only within the local group. Even if it seemed similar, cognitive and affective trust followed different patterns in inter-organizational distributed work with some members acting as “trust brokers,” crucial to develop both type of trust
Katz (1987)
Understanding changes in productivity, performance, morale, and interactions with peers and supervisors through a longitudinal study on a telecommuting pilot project
Telework
Remote workers’
- productivity
- communications with colleagues
- identity management
Supervision styleInput control based on teleworkers’ organizational identification
This study found a series of benefits during the period of home-based teleworking which allowed a reduction in absenteeism, interruptions, and distractions that affected the rate of finalization of (planned and unplanned) activities and improvement of projects quality. After an initial breakdown in communications (received and originated), calls with colleagues substantially increased after the telecommuter discussed this concern with her supervisor. Author found a fluctuation of home-based teleworker’s morale from identity conflict, transition I (office–home), steady state, transition II (home–office)
Kelliher and Anderson (2009)
Examine consequences of flexible work for a group of professionals
Flexible work
Remote workers’
- job satisfaction and commitment
- work intensificationInput control based on teleworkers’ organizational identification
Flexible workers reported higher levels of job satisfaction and organizational commitment than their non-flexible counterparts did. However, results demonstrated work intensification for flexible workers. Authors identified three means by which this intensification occurred: imposed intensification, enabled intensification, intensification as act of reciprocation, or exchange towards the organization
Khan (2012)
Explore the role of trust and relationships in virtual teams in the development sector
Virtual team
Trust among virtual team members leader as team integrator
Trust-based peer control supported by leadership practices
Trust and relationships among members were crucial for team formation and collaboration among members in distributed teams, more than in collocated teams, since misunderstanding were more likely to happen at a distance. Trust was a precursor to relationships. Anyway, members reported high cognitive trust even if they desired affective trust from their leader too. Leader played a key role as it acted as team integrator to favor and build relationships among members of distributed teams
Kimble (2011)
Explore the role of trust and identity in virtual teams and discuss technical and organizational solutions
Virtual team
Trust among virtual team members
Social presence
Virtual team identityTrust-based peer control supported by leadership practices
Case studies evidenced significant challenges to trust and team identity building in virtual team. Solutions for trust building can be: the organization of face-to-face meetings and the provision with technologies ensuring “social presence” (i.e., perception that available ICT allow effective interactions with colleagues). Communities of practice emerged as a (organizational) solution for building team identity
Kirkman et al. (2002)
Identify main challenges in establishing, maintaining, and supporting virtual teams
Virtual team
Managerial style
Virtual team successTrust-based peer control supported by leadership practices
Despite the several managerial challenges to virtual team success, according to managers of virtual teams the main issues regarded building trusting relationships among team members, maintaining synergies and collaboration at a distance; overcoming employees’ feeling of isolation; balancing employees’ technological and interpersonal skills; implementing correctly a performance review system
Kirkman et al. (2004)
Investigate relationship between team empowerment and virtual team performance, and moderating role of face-to-face meetings
Virtual team
Virtual team empowerment and performance
Trust-based peer control
The level of team empowerment had positive effect on both virtual teams’ performance measures. Anyway, it was particularly critical for the improvement of work processes in high virtual team, whose members rarely meet.
Kossek et al. (1999)
Investigate factors influencing the decision of managers to opt for flexible schedule (i.e., flextime, part-time, and leave)
Telework
Manager
- personal characteristics
- social influence of peer
- productivity concernsDirect supervision
This study evidenced that managers appreciated flexible work arrangements. They would like that in the next future companies will allow them full autonomy for the flexible scheduling of their activities. The study also found that the main factors influencing the managers’ use of flexible work arrangements were gender and age (personal factors) and peer use, that is, use by other managers (social factors)
Kossek et al. (2006)
Examine professionals’ use of telecommuting, perceptions of psychological job control, and boundary management strategies
Telework
Remote workers’
- psychological job control
- boundary management strategy
- work–family conflict
- turnover intentionsDirect supervision
Professionals preferred formal telework programs, where, for example, remote working days are clearly defined. At the same time, they appreciated to be autonomous and empowered by the company. Indeed, higher the perceptions of job autonomy, lower the turnover intentions, depression, and work–family conflict, excepted in the case work and personal life were too much integrated
Kurland and Cooper (2002)
Understand the nature of managerial control in telecommuting environments and its relationships with telecommuters’ professional isolation
Telework
Output control
Behavior control
Clan controlDirect supervision supported by standardization
Supervisors used a mix of control mechanisms that, excepted for clan, were the same for office-based employees and teleworkers. Teleworkers considered that management by objectives reduced the risks of career penalties. However, supervisors and a part of teleworkers evidenced that physical distance could reduce career opportunities in the long term due to the fewer opportunities to informally learn, develop skills, and interpersonal relationships. Therefore, they believed important to combine it with informal clan control
Kurland and Egan (1999)
Explain the relationships among telecommuting, monitoring strategies, organizational justice perceptions (as proxy of professional isolation)
Telework
Control
- output control
- job formalization
- formal communication
Remote workers’ perceptions of organizational justiceInput control based on teleworkers’ organizational identification
The adoption of telework affected the way employees (working remotely) perceived to be treated by the organizations (i.e., organizational justice). Anyway, teleworkers perceived to not be penalized, and thus treated equally to their office-based colleagues when they were controlled based on the standard procedures (behavioral control) and when they interacted and communicated frequently (also informally) with their supervisors
Kwon and Jeon (2020)
Examine whether managers’ commitment to telework and performance-oriented culture matter for federal teleworker satisfaction
Telework
Managerial support
Work–life balance
Employee satisfactionOutput control
Senior managers’ commitment to telework (i.e., support towards work–life balance) and the adoption of a performance oriented culture (based on an effective performance management, proper incentive and reward system, constructive feedback, and training) were crucial for the effectiveness of telework in a public organization. Likewise, the enactment of a formal Telework Act significantly increased teleworkers’ satisfaction by overcoming unexpected consequences posed by being distant from the organization
Lal and Dwivedi (2010)
Explore the homeworkers’ connectivity to work via mobile phones
Telework
Connectivity to work by mobile phone
Actions at home to separate work and family spheres (segmentation actions)Input control based on teleworkers’ organizational identification
Home-based teleworkers preferred to separate work and home spheres, by allocating specific time and space to each domain. Anyway, this was hampered by the fact that they were always connected and could be contactable anytime and anywhere via their mobile phones. The empirical investigation evidenced that teleworkers took various actions to reduce the possibility to be contacted by colleagues outside the work domain. For example, they switched on mobile phones only during working hours and screened incoming calls/texts to decide whether to respond
Lange (2009)
Explore individual attitude to multi-tasking and intertasking as well as strategies to negotiate interruptions
Telework
Ability to perform different tasks when working at home (inter tasking and multi-tasking)
Negotiation of work interruptionsDirect supervision
The study revealed that the attitude to multi-tasking depended on employees’ personal predisposition, and not on gender. It also found several strategies to manage interruptions when working at home but the most effective assumed a “negotiation of interruptions,” where a discretionary space was recognized to others (e.g., child and partner) based on the importance or urgency of their requests
Lautsch and Kossek (2011)
Identify supervisory issues in managing a blended workforce (including remote workers and office-based employees)
Telework
Supervisory issue in managing a blended workforce with remote workers and office-based colleagues
Input control based on teleworkers’ organizational identification
Authors underlined the importance that, in implementing telecommuting programs, managers consider the blended composition of workforce. Specifically, interviews to both managers and employees evidenced 5 main supervisory issues, that is, improving gatekeeping; identifying adequate systems for monitoring both groups of workers; favoring social integration among telecommuters and non-telecommuters; supporting telecommuters in managing the overlap between work and life domains; promoting a new work-group culture
Lautsch et al. (2009)
Explain the relationship between telework, supervisor style and individual outcomes (i.e., work–family conflict, job performance, and helping behaviors)
Telework
Supervisor monitoring behaviors (e.g., job formalization; feedback; contacts; family supportive style)
Employees’ performance, helping behavior, work–family conflictDirect supervision supported by standardization
Telecommuting was associated with lower work-to-family conflict. Both telecommuters and non-telecommuters appreciated the use of the same control mechanism (based on objectives). This positively affected performance and work–family balance but affected negatively the propensity to collaborate of both telecommuters and office-based colleagues. Managers succeeded in increasing telecommuters’ availability to collaborate by contacting them frequently and inviting them to contact other colleagues. The adoption of a family supportive leadership style favored teleworkers but penalized non-teleworkers. Indeed, telecommuters showed a better work-to-family balance while office-based colleagues reported a worsening in work-to-family balance
Leclercq-Vandelannoitte et al. (2014)
Investigate whether mobile Information Systems reinforce panoptic control or generate other types of control
Telework
Panoptic control
Free control
Allowed subjection
Contribution of Mobile IS to controlDirect supervision supported by standardization
Results evidenced that the adoption of mobile IS determined the emergence of an invisible but powerful form of free control, where professionals were in a position of allowed subjection. Indeed, in exchange of autonomy they received from management, professionals accepted an insidious and pernicious control on their activities
Lee-Kelley (2006)
Examine the influence of employees’ control expectancies on virtual team members’ job satisfaction and role conflict
Virtual team
Virtual team members’ control expectancies and related job satisfaction and role conflict
Trust-based peer control
The locus of control, that is, the individual perceptions about (internal or external) factors influencing the achievement of activities, was important for the job satisfaction of virtual team members. The study also showed that the role conflicts were important for team members who attributed their success or failure to their own ability, capabilities, etc., (i.e., internals) who experienced a deterioration of job satisfaction when they received not-compatible job requests
Leslie et al. (2012)
Investigate whether the use of flexible work practices (FWPs) affect employees’ career success
Telework
Supervisor’s attributions to requests of flexible work practices (organization serving or self-serving)
Supervisor’s perceptions about employee commitment and related career successInput control based on teleworkers’ organizational identification
Managers rewarded employees who believed that required remote work in order to improve their productivity and performance; indeed, they considered them more committed to the organization. Not always, they rewarded employees who believed that required remote work for personal needs; in this case, supervisors’ perceptions about employees’ commitment depended on both managers’ and organizations’ set of values
Limburg and Jackson (2007)
Explore the links between the management of remote workers (home-based, mobile and virtual team) and the use of Workflow management systems
Telework
Workflow Management Systems Control mechanisms (output, behavior, input, self, and peer control)
Direct supervision supported by standardization
Data and information provided by Workflow Management Systems supported different control mechanisms whose combination, however, depended on the typology of remote work arrangements (i.e., home-based telework, mobile, and virtual teams) and on the nature of task performed remotely
Lin et al. (2016)
Investigate the relationship between leaders’ affective tone and virtual team performance, via team identification and team cooperation
Virtual team
Virtual team leaders’ use of a positive or negative affective tone
Virtual team identification, cooperation and performanceTrust-based peer control supported by leadership practices
In hybrid virtual teams, leaders’ use of a positive affective tone had a positive effect on both team identification and team cooperation. Indeed, team identification increased members’ availability to cooperate with colleagues (team cooperation) thus positively affecting virtual team performance
Lippert and Dulewicz (2018)
Investigate the importance of trustworthiness, commitment, communication characteristics, cross-cultural communication style and structure effect on virtual team performance (i.e., high-performing virtual team)
Virtual team
Team success
Trust
Communication skills
National cultureTrust-based peer control
Findings revealed that trustworthiness was the main factor explaining the success of a virtual team. Although at a less extent, members’ interpersonal communication with colleagues, commitment, and cross-cultural communication style were important to high-performing teams too
Lockwood and Forey (2016)
Investigate how language in synchronous computer-mediated discourses (CMD) is used in virtual teamwork to create inter-personal meanings of dominance, power and solidarity among team members
Virtual team
Power and dominance
Role of language in virtual meetingsTrust-based peer control supported by leadership practices
Patterns of domination and control by the on-shore manager and off-shore team members were revealed in the high number of interactions and large amount of time spent talking in virtual meetings, with little contribution from the team members located in India. Significantly, specific on-shore manager’s linguistic choices, for example, use of proclamations, idioms, revealed a closing down of communication and very little effort to engage off-shore team members in any form of inclusion or negotiation. As a result, the offshore team feel marginalized and disempowered in the meetings
Madlock (2013)
Explore the use of motivational language by supervisors and effects on telecommuters’ communication satisfaction, job satisfaction, and organizational commitment
Telework
Leaders’ motivational language (direction giving; empathetic language; meaning making)
Remote workers’
- communication satisfaction
- job satisfaction
- org. commitmentInput control based on teleworkers’ organizational identification
The leaders’ use of a motivational language influenced positively telecommuters’ commitment, job, and communication satisfaction as well as their perceptions about supervisors’ communication competence. However, differently from traditional workplace, direction-giving language was the most frequently language adopted in telecommuting settings and had the highest impact on all individual outcomes. It followed the empathetic language, demonstrating that it was possible to send relationship-oriented communications through ICT. Finally, the meaning making languages was the less adopted in telecommuting settings, excepted during the process of socialization with new hired employees or when introducing new policies to favor their acceptance
Maduka et al. (2018)
Identify competencies required for effective leadership in virtual teams
Virtual teams
Virtual leadership
Trust
Shared goals
ResilienceTrust-based peer control supported by leadership practices
Authors identified some competences crucial to the effective leadership in virtual teams. Specifically, leaders must be able to develop trusting relationships among members, as well as to orient team members toward common objectives; they must be able to identify individual goals clearly communicated to members, and they should be able to effectively monitor performance, provide constant feedback, and resolve conflicts among team members. Virtual team leaders must have technical skills but also be able to transmit optimism, hope, and resilience to team members; they have to be aware of the teams overall mission, strengths and weaknesses, and group dynamics. Finally, they have to be good decision makers in complex situations and able to monitor changes in environmental conditions
Malhotra et al. (2007)
Identification of leadership practices to successfully manage virtual teams
Virtual team
Leadership practices
Virtual team successTrust-based peer control supported by leadership practices
Authors identified managerial practices relevant for virtual team success. Specifically, managers should learn how to establish and maintain trusting relationships among team members working at a distance, by exploiting technological tools and solutions. Moreover, they should ensure diversity among team members and learn how effectively manage virtual meetings and monitor virtual teams’ progress. Finally, they should enhance external visibility of the team and its members and ensure members benefits from participating in virtual teams
Martínez-Sánchez et al. (2008)
Analyze the contribution of human resource’s commitment practices and social benefits on firm performance
Telework
Human resource
- commitment practices
- social benefits
Firm performanceInput control based on teleworkers’ organizational identification
The adoption of telework programs in the context of HR practices aimed at improving employees’ personal life, was really appreciated in the company and reflected on an increased firm performance, in terms of, for example, financial performance and innovation capabilities
Meerwarth (2009)
Explore changes in patterned behaviors regarding physical spaces and social relationships in the case of nomadic work
Telework
Patterned behavior in
- physical space
- social relationships
Work identity constructionInput control based on teleworkers’ organizational identification
Author initially distinguished between “home” and “away,” both referred to the physical space and to the emotional and symbolic areas. After a while, she attempted to resolve this distinction by duplicating the same work and house habits in both cities and optimizing the transitional space (e.g., airport) that signed the passage from one city to the other one. Regarding social relationships, she reported that she did not feel truly connected and integrated with both cities, since “all perceive she was passing through.” So, she had to invest a lot of effort to maintain long-dated relationship with colleagues and friends. Finally, according to the author, the main challenge concerned the multiple conflicting roles emerged from nomadic work, which are not individually defined but socially constructed based on people expectancies
Morris and Connaughton (2017)
Investigate which managerial competences are perceived to be more effective by remote workers
Telework
Effective managerial competences and behaviors
Input control based on teleworkers’ organizational identification
Authors found that, according to managers and employees, some managerial competences are crucial in the context of remote working. These competences referred to cultivate interpersonal trust and encourage employees’ identification with the organization, support employees in using technologies, promote a supportive culture, revise the communications and the evaluation of performance of remote employees, and modify the knowledge management process and the selection criteria
Mortensen and Hinds (2001)
Investigate group conflicts and shared team identity among members of collocated and distributed teams, and related effects on team performance
Virtual team
Shared team identity
Group conflicts
Team performanceTrust-based peer control
Findings found that (affective and task) conflicts among members were more frequent in collocated than distributed teams. However, conflicts were more detrimental for performance of distributed teams than co-located teams. The study evidenced that a shared team identity among members was effective in reducing both affective and task conflicts in distributed teams. No differences were found in the frequency and types of technology-mediated communications. Anyway, results suggested more task conflict in teams that relied heavily on technology to communicate with colleagues
Mumbi and McGill (2008)
Explore the role of trust in virtual project teams and investigates how trusting relationship influences project outcomes
Virtual team
Virtual team trust
Members’ trusting intention
Managers’ trust building skills and previous project experienceTrust-based peer control supported by leadership practices
Trust was demonstrated to be crucial to project success in virtual teams. Specifically, virtual team trust was influenced mainly by their members’ trusting intentions (in their turn affected by institution-based trust and perceived trustworthiness of project manager). In contrast, managers’ trust-building skills and their previous experience with managing project, as well as deterrence-based trust had a small effect on virtual team trust. Surprisingly swift trust appeared not to have a direct influence on team trust
Munir et al. (2016)
Investigate the impact of interpersonal trust and leadership style on workplace isolation in the context of virtual workplace
Telework
Interpersonal trust
Transformational leadership style
Employees’ perceptions about their self-efficacy in virtual workplaceInput control based on teleworkers’ organizational identification
Salespeople participating in the study reported to experience a negative feeling of “virtual workplace isolation” due to the physical distance from colleagues. Anyway, they reported that the existence of a trusting relationship with their manager, along with a transformational leadership style helped to mitigate this negative feeling. This was even stronger in the case of self-efficacious people, that is, employees trusting in their own abilities and skills to meet job requirements
Neufeld and Fang (2005)
Investigate the relationship between home-based teleworkers’ beliefs and attitudes towards remote working and their productivity
Telework
Homebased teleworkers’ beliefs and attitudes towards remote working and related productivity
Input control based on teleworkers’ organizational identification
Home-based teleworkers believed important to have positive interactions with colleagues, managers, and also with family members. This influenced their attitudes toward remote working, which were strongly associated with productivity
Neufeld et al. (2010)
Investigate the relationship between leadership style and remote workers’ perceptions about leader performance
Telework
Leadership style (transformational vs transactional style)
Communication effectiveness between leader–followerDirect supervision supported by standardization
Transformational leadership style influenced positively remote workers’ perceptions about leader performance. This relationship was mediated by the degree of effectiveness perceived by remote workers about communication exchanges with leaders. Therefore, distance did not affect remote workers’ perceptions neither about leaders’ ability in communicating effectively with them, nor about their leaders’ performance
Newman et al. (2020)
Investigate how virtual team members’ perceptions of their leaders’ effective use of communication tools and techniques affect team performance outcomes
Virtual team
Member-to-member communication
Leader-member communication
Trust in leadership
Reporting for impression managementTrust-based peer control
The study found five communication techniques and attributes that positively influenced the virtual team members’ perceptions of leader communication abilities. These are: frequency (i.e., number of time the leader communicate with team members), predictability (i.e., predictable communication), responsiveness (i.e., timely response), clarity (i.e., transparent communication) and mode (i.e., identification of the most effective communication tool). Higher the perceptions of leaders’ communication abilities and trust in leaders, higher the perceptions of virtual team performance. Interestingly, this perceptions about team performance not always match with the actual performance as reported at organizational level
Ng and Tung (2018)
Understand the leaders’ perspective regarding reward and recognition, and how reward system affect virtual project team effectiveness
Virtual team
Incentive systems
Work motivation
Knowledge sharingTrust-based peer control
Reward and recognition were positively related to virtual team effectiveness as they served as encouragement and satisfaction for team members. According to leaders, individual and team-based rewards were important to motivate virtual team members, reinforce relationships, generate team cohesion, enhance communications and favor knowledge exchange. Leaders also believed that informal recognition system had a symbolic meaning, as perceived by team members as an appreciation of their efforts and contribution to team performance
Oertig and Buergi (2006)
Understand the challenges in managing cross-cultural virtual project teams within a matrix organization
Virtual team
Managerial challenges
- Leadership without authority
- Trust
- Virtual communicationTrust-based peer control supported by leadership practices
Authors identified 3 main challenges in managing virtual project teams in a matrix organization. These were the frequent lack of formal authority in exerting leadership on virtual team members; difficulties in communicating with members working at a distance; the difficulty in building trusting relationships with colleagues due to high turnover. Another relevant challenge was associated to the need to manage language and cultural differences among team members.
Olson et al. (2014)
Explore the impact of web-based video via webcams on virtual team trust and effectiveness
Virtual team
Virtual team trust
Virtual team perceived effectiveness
Role of webcam and web-based videoTrust-based peer control
The use of webcam during virtual meetings helped to increase the level of trust among team members. Indeed, web-based video via webcam enabled team members to increase their availability to share common goals and improved their ability to focus on tasks. The perceptions about the effectiveness of web-based video increased over time, until the introduction of a new technological application (i.e., screen sharing) which forced them to review their practices and process during the virtual meetings
Oshri et al. (2007)
Understand the socialization process, mainly the role of face-to-face meetings, in globally distributed teams
Virtual team
Socialization process
Face to face meetingsTrust-based peer control supported by leadership practices
Face-to-face meetings were crucial for favoring socialization among members of globally distributed teams as long as they were carefully organized and a number of activities were carried out before and after meetings (e.g., short visits, relocation of experts, and language courses). Moreover, re-socializing activities were fundamental in long projects to confirm and maintain team members’ behaviors, norms, and attitudes
O’Sullivan (2003)
Analysis of work patterns in a virtual multi-lateral development organization (multi-organization, multi-team, VMDO)
Virtual team
Standardization of work content (i.e., norms for design output and processes)
Synchronization of workflow (time-based norms)Trust-based peer control supported by leadership practices
Lead firm’s imposition of standards for work content and timing gave an efficient basis to resolve task interdependencies, allowing integrative patterns to emerge. Indeed, standardization and synchronization structured the flow of information and resolution of design issues among all the organizations participating to the project
Overbey (2013)
Explain the relationship between perceived leadership styles and telecommuters’ intent to leave an organization
Telework
Leadership style (transformational, transactional, laissez-faire style)
Telecommuters’ turnover intentionsDirect supervision
Differently from traditional workplace, it resulted that telecommuters were less willing to leave the organizations in the case of transactional and laissez-faire leaders. In contrast, turnover intentions resulted to be greater in the case of leaders that adopted a transformational style
Park and Cho (2020)
Investigate the behaviors and perceptions of supervisors in the telework context
Telework
Co-located vs. remote workers
Formal and informal communication
Leader communication
Perceptions of supervisor leadership skillsDirect supervision
The study found no differences between teleworker and non-teleworkers supervisors for what concerned the frequency of formal and informal communication flux, as well as the organization of meetings with subordinates. This was essentially due to the availability and use by telework supervisors of a variety of ICT communication tools. Authors also found that subordinates’ perceptions about telework supervisors were positively affected by the ability of their supervisors to assign fair objectives, as well as by their proficiency and experience in managing at a distance
Paul (2006)
Understand how sense-making can be effectively and efficiently carried out in a distributed environment
Virtual team
Distributed environment
Sense-making (at group level)Trust-based peer control supported by leadership practices
Sense-making was challenged in distributed environments. However, it was efficiently managed through the adoption of a holistic approach and a series of measures ranging from an adequate design of ICT tools (e.g., to extract salient cues or allow retrospect analysis) and to the organization of sessions reproducing face-to-face interactions (i.e., create a sensible environment)
Pauleen (2003a)
Development of a three-steps model for leader-initiated relationship building with virtual team members
Virtual team
Virtual team
Leader-initiated relationship buildingTrust-based peer control
Author identified 3 steps for leader-initiated relationship building with virtual team members. The first step consisted of assessing conditions to relationship-buildings (in terms of, e.g., team issues and available ICT). The second step regarded the definition of the level of relationships (low, medium, and high). The third step referred to create strategies for building relationships in terms of messages and tools (e.g., phone calls and e-mail)
Pauleen (2003b)
Explore communication and trusting building relationships in a virtual teams whose members had relevant cultural differences
Virtual team
Relationship building
Communication practices (face to face, e-mail, and phone calls)
Cross-cultural boundariesTrust-based peer control
The choice of communication practices was influenced by virtual team members’ preferences (in their turn affected by culture), then by familiarity, skills, and availability of specific technological tools. Communications preferences may change over time due, for example, to deadlines that are required to speed up the process. Face-to-face meetings were crucial for building trusting relationships among team members
Peasley et al. (2020)
Investigate the effects of personal stress (family-to-work) on work performance in the case of salespeople
Telework
Stress
Work–family boundary
Performance managementDirect supervision
Personal stress strongly affected the burnout of a group of salespeople and reflected on their performance. Specifically, health stress increased exhaustion and calloused disposition towards clients and colleagues. It also led to the gradual diminishing of a salesperson’ sense of importance for stakeholders. Likewise, when personal non-work relationships underwent strains, the resulting stress increased exhaustion and perception of diminished personal accomplishment due to the failure in private relationships. Finally, financial stress provoked in salespeople emotional exhaustion and depersonalization
Peters and Karren (2009)
Investigate the relationship among trust in team member, functional diversity, and team performance in a virtual environment
Virtual team
Trust in team member
Functional diversity
Virtual team performanceTrust-based peer control supported by leadership practices
The study evidenced different perceptions for virtual team members and managers. The former believed that trust in team members and functional diversity are both relevant for team performance. The latter did not agree as, according to them, the effect of functional diversity on team performance depended on knowledge exchange and competence complementarity among members; the impact of trust on team performance depended on swift trust, communications among members, previous experience with distributed work etc. In the end, managers believed that trust moderated the relationship between functional diversity and team performance so that higher the functional diversity, higher the effect of trust on virtual team performance
Porter and van den Hooff (2020)
Understand the “complementary control system,” that is, role of mobile technologies for enhancing employees’ autonomy while increasing managerial control
Telework
Employee autonomy
Perceived fairness
Performance managementDirect supervision
By comparing pre- and post- implementation of a mobile IS, this study found that the mobile Sales Force Automation tool led to an “informational affordances” (automation of sale information, real-time access/visibility of sales and customer information, and auditable performance information) that increased both employees’ autonomy (over content, timing, location, and work performance) and managerial control. Autonomy and control were not opposite concepts, rather they were balanced in a “system of complementary control” where sales agents and managers were connected in a positive relationship based on increased fairness, relatedness, and trust
Presbitero (2020)
Understand whether (and how) employees’ foreign language skill influences individual task performance in global virtual teams
Virtual team
National culture
Conflict
Performance management
CollaborationTrust-based peer control
In globally dispersed work environment, virtual team members’ foreign language skills were crucial for their performance. Specifically, higher their knowledge of a foreign language, lower the anxiety and stress in interacting with foreign colleagues, thus resulting in a higher individual task performance. Anyway, the “cultural intelligence,” that is, ability to interact effectively across cultural contexts, was found to act as a moderator, so that high cultural intelligence reduced the negative effects of foreign language anxiety on task performance
Raghuram and Fang (2014)
Explain the relationship between employees’ perceptions about supervisory power and telecommuting intensity in China
Telework
Supervisory power in term of—legitimate power
- reward power
Telework intensityDirect supervision
The intensity of remote working connected positively with perceptions of supervisory power and with the fact that supervisors were themselves teleworkers. Interestingly, power conceptualization emerged as specific of each country and influenced by the socio-cultural context; for example, Chinese employees recognized higher power to supervisors adopting a paternalistic approach
Rapp et al. (2010)
Explain if team leaders empowering behaviors and team experience influence virtual team processes, commitment and performance. Moderator role of the degree of virtuality is investigated
Virtual team
Leader empowering behaviors
Team experience
Virtual team processes (planning, actions)
Virtual team outcomes (i.e., commitment and team performance)Trust-based peer control supported by leadership practices
Empowering leadership improved team planning processes. This relationship was moderated by previous team experience. Indeed, in the case of high team experience, team members were less likely to engage in effective planning. These effects were attenuated as long as the team was virtual
Richardson and McKenna (2014)
Examine how professionals reorder their home and work lives through the process of becoming flexible workers
Telework
Reordering
- spatial relations
- social relations (both with colleagues and family members)Input control based on teleworkers’ organizational identification
The adoption of flexible work led a group of professionals to reconfigure spaces at home and redefine social relations with colleagues (i.e., they looked for new patterns of interactions) and family members (e.g., they established new rules). This was not a stable entity but a continually evolving process, mutually constituted by space and social relations
Rico et al. (2009)
Investigate how communication behaviors among virtual team members interact with task interdependence in relation to the building and changing of trust
Virtual team
Communication behaviors (task-oriented or socially oriented communication)
Communication enthusiasm
Predictable communication
Substantive communication
Trust building (and changes) among virtual team membersTrust-based peer control
In the “early on” phase, task oriented communications were fundamental for building trusting relationships among virtual team members. Enthusiastic communications were relevant only in the case of low task interdependence activities. Predictable and substantive communications were both relevant to trust among team members during the “later on” phase, mainly in the case of high task interdependence. The study evidenced the importance to consider that trusting relationships change over time and therefore include temporal dimension in their analysis
Riedl et al. (2012)
Investigate the relationship between virtual team members’ perceptions about leader status and power, and trust in leader and team performance. Moderator effect of team size and team culture
Virtual team
Virtual team member’s perceptions of leader status or power
Virtual team culture
Trust in virtual team leader
Virtual team performanceTrust-based peer control supported by leadership practices
Trust in leader depended on virtual team members’ perceptions of its status. Relationship between leader status and trust in leader was moderated by team culture. Trust in leader was crucial in virtual teams for its positive effect on team performance
Romeike et al. (2016)
Investigate the effects of social comparison processes on virtual team members’ trust and job satisfaction
Virtual team
Virtual team members’ perceptions about their own contribution to team performance and job satisfaction
Trust among virtual team membersTrust-based peer control
In the case that virtual team members perceived that their performance was higher compared to team performance (over performance), they experienced lower level of trust toward team and lower level of job satisfaction, as they perceived that colleagues invested less effort and contributed less to virtual team performance. Trust mediated the negative effect of social comparison processes on job satisfaction
Ruiller et al. (2019)
Identify managerial practices able to develop and maintain the perception of proximity of teleworkers
Telework
Perception of proximity to peers
Identification
Relationship with peersDirect supervision
Teleworkers’ perceptions of proximity from colleagues represent a relevant issue for managers. According to this study, the adoption of an “e-management mode” (that, e.g., combines virtual and face-to-face communications) is able to favor shared identification among distant colleagues and improve the quality and quantity of exchanged communications. Together they increased the proximity perceived by teleworkers while ICT use (e-mail, phone, etc.) supported the quality of relationships established with colleagues
Ruppel et al. (2013)
Explore how members of a global virtual team chose communication media for managing multiple boundaries. Focus on home-based US managers who communicated with virtual team members located in office in India
Virtual team
Work–life balance
Boundary management
- time, language, and cultural boundaries
- challenges and strategies
- communication media choiceTrust-based peer control supported by leadership practices
Managers chose those communication media that met task requirements and allowed them to maintain the boundaries and clearly separate work and personal lives. Their decisions about communication media did not take into account the exigencies and preferences of Indian colleagues. Therefore, they extensively used e-mail and instant messaging, followed by phone calls for more complex issues. They did not appreciate videoconferences
Sewell and Taskin (2015)
Examine the tension between teleworkers' experience of being physically absent from the workplace while being simultaneously under close managerial and peer control
Telework
Organizational control
Spatiotemporal scaling
Re-regulation of existing controlDirect supervision supported by standardization
Both technical and professional teleworkers developed similar strategies of spatiotemporal scaling as a response to change in managerial control after telework introduction. These changes (i.e., re-regulation) consisted of a formalization of technocratic control, extension of hierarchical relationship (i.e., supervision) and development of stronger social and normative pressure to conform that lead to perceptions of reduced autonomy. Both groups attempted to reterritorialize their experience through establishing their visibility and presence in a remote setting, so as to feel more integrated into the social relations of work. Distantiation leads teleworkers' to challenge existing norms such as trustworthiness and since they worried about how they would be perceived by managers and peers, that were trying to put themselves into the minds of other rather than using the domestic scale as a refuge from managerial intrusion
Sivunen (2006)
Identify tactics implemented by virtual team leaders to strengthen the employees’ team identification through computer-mediated communication
Virtual team
Virtual team leaders
Team identification
Computer-mediated communication
Virtual team leaders’ identification-promoting tacticsTrust-based peer control supported by leadership practices
Author identified several identification-promoting tactics adopted by virtual team leaders. These included: catering for the individual; giving positive feedbacks to members; bringing out common goals and workings; talking up the team activities and organizing face-to-face meetings. Author recognized the crucial role of technological tools and warned about the need to provide a variety of ICT tools allowing both synchronous and asynchronous communications among virtual team members
Staples et al. (1999)
Investigate relationships between antecedents to remote workers’ self-efficacy assessments and their behavioral and attitudinal consequences
Telework
Remote work
- self-efficacy assessment
- attitude (job satisfaction, ability to cope, and commitment)
- behavior (performance and job stress)Direct supervision
The study evidenced the importance of taking into account the employees’ perceptions of being able to work remotely (i.e., self-efficacy assessment), which emerged to be affected by their previous experience with remote working, their ability to use ICT as well as by training courses organized by the company for those who accessed to remote work. The self-efficacy assessment influenced the employees’ ability to cope, effectiveness, productivity, and job satisfaction
Strawn (2009)
Understand the process of identity structuration in the case of a remote workers
Telework
Sense of fragmentation and disjuncture
Identity structuration
Re(structuring) identityInput control based on teleworkers’ organizational identification
The transition to remote work and the continuous commuting from one place to another one caused a fragmentation and disjuncture in author’s identity. She reported that she restructured her (new) identity by identifying at home specific space devoted to work; by setting the same routines in both cities to control chaos (e.g., same cereals). However, she reported a work intensification and a desire to restore the visibility by organizing frequently formal face-to-face meetings with her own team members
Symon and Pritchard (2015)
Understand the socio-materiality of connectivity, that is, how smartphones are used by mobile workers to maintain “connections” to the organization and how the entanglement of social and material aspects of technology and work practices shape work identity
Telework
Connectivity
Identity work
Socio-material perspectiveInput control based on teleworkers’ organizational identification
Connection viewed as a socio-material assemblage that performed a particular work identity, that is, contactable, responsive, committed and authoritative. The concept of connectivity was developed taking into account material agency and human actions. Analysis suggested that connected identity emerged from the mangle of practice, that connectivity can be viewed as an entanglement of different agencies that produces connection, that alternative socio-material performances are achieved by questioning ideational identities and position in relation to others
Taskin and Edwards (2007)
Understand the relationship between the adoption of telework and work re-regulation, in terms of changes in rules of control and work relationships
Telework
Changes in rules of control and relationship
Direct supervision supported by standardization
Findings revealed that telework programs could be suitable to public bureaucratic environments. However, they needed to be planned adequately in order to be successful. Indeed, results evidenced the emergence of new control mechanisms both horizontal (i.e., reinforcement of social control) and vertical (i.e., introduction of new control by supervisors) that needed to be coherent and not conflicting with pre-existing control mechanisms
Thomas and Bostrom (2008)
Explore the technology adaptation by leaders to build and maintain trusting relationships among members of virtual teams
Virtual team
Virtual team leader style (forcing style vs linking style
Trust change
Project outcomesTrust-based peer control supported by leadership practices
Trust was essential to collaboration and knowledge transfer among virtual team members. Leaders used ICT as transitional objects (technology adaptation) for building trusting relationships among VT members. Technology adaption (mainly combined with a forcing style) positively affected trust and collaboration. Leader linking style, even if positively related to trust and collaboration, required higher technology adaptation
Tietze and Nadin (2011)
Explore how the transition from office-based to home-based work impacts upon the psychological contract (i.e., relationship with employer, colleagues, and family members) of employees
Telework
Home-based teleworkers’
- psychological contract
- relationships with employer, colleagues, and family members
- job satisfaction and life satisfactionInput control based on teleworkers’ organizational identification
Employees expected to obtain a series of benefits from telework, that is, better work–life balance but also the opportunity to escape from tensions of office environment. As for the type of relationships in the new work context, home-based teleworkers reinforced the transactional-oriented relationship they already had with their employer, thus they worked more intensively only to obtain to prolong the telework program. Likely, teleworkers maintained a transactional-oriented relationship with office-based colleagues by avoiding to contact them if not necessary, as well as with managers because they felt they did not trust those working at home. Interestingly, home-based teleworkers improved the relationships with other teleworkers and the harmony in the family context, even if it required a continuous renegotiation of domestic duties (with partner) and emotional boundaries (with parents)
Timms et al. (2015)
Investigate employees’ use of flexible work and relationship with work engagement, turnover intentions and psychological strains
Telework
Organizational culture (hindering or supportive)
Employees’ work engagement, turnover intentions, and psychological strainsInput control based on teleworkers’ organizational identification
Supportive organizational culture was fundamental to the actual use of flexible work. Indeed, it reduced the inconsistence between formal and informal organizational messages. A negative relationship between flexible work use and work engagement was found, probably due to economic crisis in Australia. Flexible use resulted to be a predictor of turnover intentions
Virick et al. (2010)
Investigate factors related to employee (job and life) satisfaction with telecommuting. Moderator role of performance outcome orientation and worker type are investigated
Telework
Performance outcome orientation
Worker type, job satisfaction, and life satisfactionInput control based on teleworkers’ organizational identification
Teleworkers showed a high level of job and life satisfaction when there was a moderate intensity of telecommuting. Individual orientation to results (i.e., performance outcome orientation) moderated the relationship between extent of teleworking and job satisfaction. It emerged that the level of job satisfaction stayed the same regardless the extent of telecommuting when teleworkers showed a high orientation to results. In contrast, job satisfaction was higher for those with low performance orientation when there was a moderate level of telecommuting. Worker type moderated the relationship with life satisfaction; specifically, those who tended to workaholic behaviors reported a high level of life satisfaction regardless of the intensity of telecommuting
Vuolle (2010)
Understand and evaluate the impact on productivity following the adoption of a mobile office service in the context of mobile workers
Telework
Mobile office service
Productivity impacts (at individual level)Direct supervision
The use of mobile office services increased the teleworkers’ ability to collect information to understand complex situations, to utilize idle time while on the move, as well as to accomplish tasks that needed a rapid response
Youngblood (2009)
Communication strategies implemented by remote workers to overcome professional isolation and be part of the “workplace community” created among collocated workers
Telework
Remote workers’ communication
Workplace community
Professional isolation
Career progressionInput control based on teleworkers’ organizational identification
In order to feel to be part of the workplace community, remote worker communicated continuously (often carefully timed) with co-located colleagues and used various tools and channels, that is, email, IM, and phone calls. These communications were very detailed, in order to give visibility of work done, and very formal in order to avoid misunderstandings with colleagues
Webster and Wong (2008)
Compare identity, communications and trust in co-located, pure virtual and hybrid project teams
Virtual team
Team members’ perceptions about—group identity and trust
- perceived task skills
- project satisfaction
CommunicationTrust-based peer control
Members of traditional and pure virtual teams behaved in a similar fashion in terms of communications, and perceptions of colleagues’ task skills and group trust and identity. This study revealed important differences in the case of hybrid teams, where members communicated more and show higher trust, task skills and better group identity with local members than with remote workers. Finally, VT members reported project satisfaction higher than traditional teams
Whitford and Moss (2009)
Investigate the relationship between transformational leadership and employees’ work engagement and job satisfaction. Moderating role of employees’ regulatory focus and goal orientation in distributed and collocated work are investigated
Virtual team
Transformational leadership style
Employees’ regulatory focus and goal orientation
Employees’ work engagement and job satisfactionTrust-based peer control supported by leadership practices
The transformational leadership style operated differently depending on whether it was a virtual or a co-located team. In distributed teams, a transformational leadership style improved the job satisfaction and work engagement of members who were driven by a desire for fulfilling their personal aspirations (i.e., promotion focused). In contrast, in co-located teams this leadership style worked better for the job satisfaction and engagement of those who were motivated by the fulfill of duties and obligations (i.e., prevention focused)
Whittle (2005)
Explore the relationship between being preacher and practitioner of flexible work for a group of consultants. To this end, their (back stage and front stage) discourses are analyzed
Telework
Organizational discourse
Manager as producers of organization discourseInput control based on teleworkers’ organizational identification
Consultants emphasized the virtues and many benefits of flexible work when talking with their clients. However, by analyzing their discourses, this study found evident contradictions about what they preached publicly (front stage) and what they reported during interactions with colleagues (back stage). Author evidenced that they sustained positive discourses on flexible work rather than discrediting it only for career reasons, even if they failed in reconciling the contradictions and ambivalence they experienced
Wiesenfeld et al. (2001)
Investigate the relationship between individual differences in need for affiliation and virtual workers’ organizational identification
Telework
Virtual workers’
- need for affiliation
- perceptions of work-based social support
- organizational identificationInput control based on teleworkers’ organizational identification
Personal attributes helped explain the level of remote workers’ organizational identification. In fact, remote workers, with high personal need for affiliation, showed high levels of organizational identification. Instead for those with less need for affiliation it was critical the support they perceived to receive from supervisors and colleagues in office
Wiesenfeld et al. (1999)
Investigate the role of electronic communication in obtaining that virtual workers identify with their organization
Telework
Communication of virtual workers with organizational members (frequency and type of media)
Virtual workers’ organizational identificationInput control based on teleworkers’ organizational identification
Degree of virtuality moderated the relationship between communication media and organizational identification. Electronic communication (mainly email) resulted to be more important to OI for those extensively working at a distance. Phone calls resulted to be more important to OI for less virtual telecommuters. F2F meetings were not important to OI in virtual work. However, authors invited to consider those results as affected by the state of implementation of telecommuting programs (e.g., F2F could be important during the initial adoption)
Workman (2007)
Empirically investigate global virtual team performance through boundary permeability theory and organizational culture framework
Virtual team
Organizational culture
Control (tightly vs loosely controlled)
Virtual team performanceTrust-based peer control supported by leadership practices
Process-oriented teams had better performance of result-oriented teams when adopting procedural structure. Openness moderated such relationship. Tightly controlled teams had better performance than loosely controlled teams
Zhang et al. (2007)
Explore how formal and informal control play out in distributed IT work where teams are composed of subgroups that are distributed across countries and cultures
Virtual team
Formal and informal control
Organizational culture
Relationship transfer
Popular culture
Social brokersTrust-based peer control supported by leadership practices
Formal control was complemented with informal control in distributed IT work. Informal control had additive powers that improved the effectiveness of formal control. Formal control supported organizational culture diffusion. Clan control could be increased by personal relationship buildings, face-to- face meetings, pop up culture training, and social brokers
