Abstract
Being connected to the Internet through various mobile devices is pervasive in our daily professional and private lives. Yet, the way people connect, including when, with whom and through which communication channels differs, manifesting individuals’ idiosyncratic connectivity patterns. In team collaboration, where individuals are dependent on each other’s availability and responsiveness, differences in team members’ connectivity patterns can lead to clashing expectations concerning connectivity. This, in turn, can compromise individuals’ well-being and productivity and threaten team collaboration outcomes. In this paper, we address the question of how to manage connectivity in interdependent teams and align connectivity patterns to facilitate successful collaboration while at the same time safeguarding individuals’ connectivity boundaries. To address this question, we conducted a qualitative case study that involved 39 semi-structured interviews with employees and members of the management board of an international consultancy headquartered in Germany. Building on concepts established in boundary theory, we coined the term “connectivity boundaries” and identified the six boundary work tactics, externalizing, accommodating, adapting, pushing, sacrificing, and enforcing that allow team members to create, maintain, temporarily change, and reclaim their connectivity boundaries and achieve team collaboration success. We developed propositions that highlight which contextual factors and goals are associated with which boundary work tactic.
Keywords
Introduction
“Did you get my email?!”—or something similar—is a message we have received or sent at some point in time. In fact, “not sure if you saw my last email” is the most annoying phrase that proliferates in emails, according to a study with over 1000 white-collar workers in the US in 2017 (Naragon, 2018). In most cases, the sender of such a message uses this rhetorical question as a way to request a response but also signals that the sender anticipated an earlier reply from the receiver. Taken further, it is often an indicator of different sender and receiver expectations concerning connectivity (Kolb et al., 2008, Mazmanian, 2013, Obushenkova et al., 2018). In other words, it is often a mismatch between individual connectivity patterns, that causes a multitude of problems in collaborative work settings, such as inefficiencies and productivity loss (Murphy, 2007).
Imagine a project team in which a person who is almost constantly connected via a variety of devices and applications works with a person whose communication is limited to checking emails once a day (MacCormick et al., 2012, Gruber et al., 2018). This could become problematic, especially in critical collaboration phases that require close coordination and frequent information exchange. On the one hand, the person who is constantly connected and who expects a short response time cannot continue with their task if their communication partners do not respond in a timely manner with the required information. This could lead to delays, conflicts, and drops in productivity (Tarafdar et al., 2007). On the other hand, the person who checks their emails once or twice a day might experience their work colleagues and superiors frequently pushing for more connectivity and regularly violating their connectivity boundaries. Clearly, the misalignment of connectivity patterns causes such tensions and conflicts and triggers a range of negative outcomes, from higher stress levels and work-life conflicts (Nurmi and Hinds, 2020), to productivity losses (Mazmanian, 2013, MacCormick et al., 2012, Murphy, 2007, Karr-Wisniewski and Lu, 2010). Against this backdrop, the question surfaces how individuals can align their connectivity patterns to improve their collaboration while at the same time not overstepping their individual boundaries.
There is a growing body of research focusing on the phenomenon of connectivity (Vorderer et al., 2018), and its often negative effects on individuals and groups caused by too much connectivity, such as techno overload and invasion (Tarafdar et al., 2010). Within this stream, researchers have addressed the challenge of how to manage connectivity in collaborative settings with the help of connectivity norms (Collins and Kolb, 2012), coordination norms (Ghosh et al., 2004), use of multiple media (Leonardi et al., 2012), and a shared understanding of heterogeneous connectivity patterns (Mazmanian, 2013). While those concepts provide frames of how connectivity in teams could be managed, they do not explain why, when, and how individuals in collaborative settings safeguard their connectivity boundaries while at the same time meeting the expectations of other team members in terms of availability and responsiveness. However, it is important to gain insights into how individuals navigate such situations, as a mindful use of technologies with regard to connectivity (Gardner et al., 2017) could lead to improvements in communication efficiency and effectiveness (Papa et al., 2007), information sharing and therefore work productivity (Fawcett et al., 2007, Kolb et al., 2008).
Thus, the goal of this study is to understand and theorize how highly interdependent individuals align their connectivity patterns in order to improve collaboration and protect their connectivity boundaries using established concepts of boundary theory (Nippert-Egg, 1996, Clark, 2000, Ashforth et al., 2000). We define connectivity patterns as recurring individual behavior tendencies, including when individuals request or signal availability, when they request and respond to others’ communication requests, which application they use, over what network access, and on which device. We also see connectivity as an interpersonal concept that can only emerge when at least two people have the potential to interact with each other. Creating boundaries or so-called “mental fences” (Zerubavel, 1991) creates psychological safety for individuals as these borders allow them to simplify and make sense of the environment they are in; in our case, how to deal with the often high expectations towards availability and responsiveness. Using a qualitative case study approach (Benbasat et al., 1987) in an international professional services firm, we address the research question, “How do individuals in collaborative settings align their connectivity patterns in order to improve collaboration outcomes and protect their connectivity boundaries?”
We contribute to the body of knowledge on connectivity (Dery et al., 2014, Obushenkova et al., 2018, Kolb et al., 2012) and collaboration (Boughzala et al., 2015, Cheng et al., 2016) by (a) introducing the concept of connectivity boundaries, (b) illustrating boundary work tactics that individuals in collaborative settings can use to align their connectivity patterns whilst safeguarding their connectivity boundaries, (c) explaining how those tactics can be used to create, maintain, temporarily change, and reclaim connectivity boundaries, and (d) developing propositions that show which boundary work tactics are associated with various contextual factors, that is, when certain boundary work tactics are usually applied, and with results that are conducive for team collaboration success. Building on Majchrzak and Jarvenpaa (2010) and Chang et al. (2010), collaboration is considered successful if teams achieve a common purpose and accomplish the associated tasks at hand through acquiring useful information as part of open and direct communication and through coordinating their activities effectively.
The dynamics of connectivity
The phenomenon of connectivity
We define connectivity as ICT-facilitated capacity to purposefully reach or be reached by others. Our definition of connectivity is bilateral and comprises the ease of getting in contact with or being contacted by others. Connectivity has been conceptualized with regard to the technical infrastructure (Kietzmann et al., 2013, Bajwa et al., 2005) and the structural network perspective (Whelan, 2007, Merali, 2006, Gebauer et al., 2010). Connectivity has also been linked to the social ties between actors (Breidbach et al., 2013, Haythornthwaite, 2005) and the inter-connectivity of social media platforms (Alaimo et al., 2020) and therefore implies technical, structural, and social relations between parties that form a potential, which can be activated in actual communication. As such, the concept of connectivity can be represented through the attributes of availability and responsiveness. We frame availability here as the existence, reliability, and potential of a connection (Crepaldi et al., 2009, Kolb, 2008) between two nodes so that each node is reachable when access is required (On et al., 2003). For example, switching the status on instant messaging platforms to “online” signals availability and therefore the potential to communicate. Furthermore, responsiveness is defined as the rate, timing and ability (Adjei et al., 2016, Kleinbaum and Stuart, 2014) with which the potential of the connection between two nodes can be activated by each node. For example, if a project team leader sends a message on an instant messaging platform, she assumes that based on previous interactions, her counterpart will respond within one hour. When individuals interact, they develop expectations about when and in which timeframe their counterpart comes back to them, which we call responsiveness. In contrast, we argue that communication is the activated potential of a connection, the enacted speech act (Searle, 1969) between counterparts, for example, by actually texting or speaking with each other on social media.
Connectivity in collaborative settings
In this study, we focus on connectivity in collaborative settings as collaboration has a significant effect on productivity and outcome quality (Colazo, 2010). Collaboration is conceptualized as a fixed arrangement of team members with a clear, predefined goal leveraging communication, coordination and shared work spaces to achieve their goal (Aron, 2009). Connectivity is crucial for any project success, in particular when it comes to interactions with key stakeholders (Vaaland, 2004). Therefore, we take a process perspective on collaboration and adopt the definition of Boughzala et al. (2015), who frame collaboration as “a process in which two or more agents (individuals or organizations) share resources and skills to solve problems so that they can jointly achieve one or more goals” (p. 133). Researchers have proposed several factors that facilitate successful collaboration, including sharing a common purpose, establishing shared governance and decision-making, having a clear understanding of roles and responsibilities, fostering open and frequent communication, being equipped with adequate financial and human resources, and establishing trust and compatibility with project partners (Czajkowski, 2007, Mattessich and Monsey, 1992). In our case study, we particularly focus on hybrid collaboration, which refers to situations where individuals collaborate virtually as well as face-to-face (Cheng et al., 2016).
Connectivity as capacity to get online everywhere and anytime brings considerable benefits in collaborative settings but also carries some risks. On the one hand, connectivity enables seamless communication, information exchange, and coordination of tasks when collaborating across organizations, industries, countries, and continents (Fawcett et al., 2007, Gosain et al., 2004, Kolb et al., 2020). Therefore, connectivity facilitates the exchange and retrieval of information and knowledge in a quick, efficient, and effortless manner overcoming temporal and spatial barriers (Hansmann et al., 2003, Dery et al., 2014). On the other hand, employees in many industries face rising expectations towards constant availability due to the technological innovations in terms of networked and wireless computing, psychological drivers, cultural imperatives, and social dynamics, especially temporal norms and how individuals and groups negotiate availability and responsiveness. These group norms result in restricted autonomy of individuals as they specify when and how long individuals should be available and how quickly they should respond. Therefore, they cannot decide freely how and when they should be connected, which negatively affects employee well-being and can lead to adverse health effects (Mazmanian and Erickson, 2014, Nurmi and Hinds, 2020, Büchler et al., 2020, Becker et al., 2018). Rising expectations towards availability and responsiveness can trap individuals and groups in a spiral of escalating engagement (Mazmanian et al., 2013). This spiral describes the whipping up of collective and individual ICT use, where people may lose their autonomy and control of when and where to get online. This has negative consequences for groups and individuals and can lead to increased stress levels, absent presence, job creep, and work-life conflict (MacCormick et al., 2012), which may negatively affect collaboration and work productivity (Karr-Wisniewski and Lu, 2010).
In order to leverage connectivity between individuals and to curtail the risks, especially negative group dynamics such as the spiral of escalating engagement (Mazmanian et al., 2013), researchers have proposed different solutions. One solution to address this situation is the implementation of connectivity norms. Connectivity norms imply a shared understanding of and compliance with a certain approach (how and how much) as well as responsiveness (when) to connect that would guide individuals’ behavior. These norms are important and have a positive effect on the innovativeness of teams (Collins and Kolb, 2012). Another solution is the development of coordination norms, that is, norms that guide the interdependent use of multiple media in the everyday work context, which are particularly crucial in distributed teams for effective coordination over distance and time (Ghosh et al., 2004). These authors point out that in the initial stages of a project, team members may establish preventive norms by discussing and reflecting on prior work experiences. They claim that over the course of the project, when members may face difficulties or problems, they develop corrective coordination norms. Furthermore, due to the ongoing interactions among the project team members, they will establish a couple of adaptive norms which reflect the members’ continuing learning about the communication patterns (i.e., the way they communicate with each other) of their counterparts, their tasks, and their media usage (Ghosh et al., 2004).
Besides connectivity and coordination norms, the development of a shared understanding of heterogeneous practices, meaning that colleagues accept and respect different connectivity patterns when interacting with each other, is another solution. Mazmanian (2013) studied how the adoption of BlackBerrys evolved differently in two occupational teams in one company. She showed that the sales team developed a shared understanding of heterogeneous connectivity patterns, which evoked various positive effects. They were able to develop different connectivity patterns as they worked independently from each other and did not see how and when their colleagues were available. In contrast, the lawyers in her study had developed assumptions of homogeneous communication practices and constant availability, which led to unreasonable expectations of availability and responsiveness. For the lawyers, availability was a sign of dedication to their job and because they saw when and how long their colleagues were available, mainly through cc’ing on emails, this increased the pressure on each other. The mutual understanding of different connectivity patterns like in the sales team enhances the effectiveness of individuals at work without creating pressure towards constant availability and responsiveness (Mazmanian, 2013).
A more intrusive approach to solve the issue of different connectivity patterns was shown in a study where managers with and without positional power used persuasion to influence the behavior of their counterpart. In case of a discrepant event, which the managers perceived as a threat to the project plans, they asked their subordinates to change their work routines (Leonardi et al., 2012). The managers increased the connectivity between themselves and their team members to include them in the sensemaking process, so the whole team realized that an event threatened the success of the project.
To summarize, although these studies provide different means to generally improve connectivity and explain the benefits of shared connectivity norms and expectations, they (a) do not focus on highly interdependent teams, that is teams with high task interdependencies (Mazmanian, 2013) and (b) do not provide insights into the workings of the underlying strategies, techniques, or frameworks that individuals can apply to improve their connectivity while avoiding the negative consequences of too much connectivity such as information overload, increased stress, and blurring of work-life boundaries (Mazmanian and Erickson, 2014, Mazmanian et al., 2013). These are the gaps our research aims to address in this study.
For example, while Collins and Kolb (2012) pointed out the importance of connectivity norms and individual agency, they leave open how exactly individuals and teams can develop these norms and empower their members to take independent decisions in terms of when and where to connect. Further, Ghosh et al. (2004) elaborate on the kind of norms project team members can apply and when they should develop them in order to improve the collaboration; however, they did not explain how individuals actually develop these norms. The sales team in Mazmanian’s (2013) study was able to develop a shared understanding of heterogeneous connectivity patterns mainly because they worked independently from each other. However, the lawyers, who worked much more interdependently, developed a homogeneous trajectory of use where everyone in the group expected from their peers to be available and responsive around the clock, which led to an increase in pressure and stress. Such interdependencies with regard to connectivity, as experienced by the lawyers, is illustrative of the problem our study wants to address and where our contribution to the fields of connectivity and collaboration lies. We respond to Mazmanian’s (2013) call for future research to illustrate solutions where team members take a proactive approach to establish situation-adequate connectivity patterns while safeguarding them from too much or too low connectivity levels and their associated negative effects (Kolb et al., 2008, MacCormick et al., 2012) in interdependent teams that require close collaboration where individuals are dependent on each other’s availability and responsiveness.
Connectivity boundaries
In order to theorize how teams can improve their collaboration by aligning their connectivity patterns while avoiding detrimental amounts of connectivity, that is, too much or too little, we conceptualize the term connectivity boundaries. Originating in boundary theory (Nippert-Egg, 1996, Ashforth et al., 2000), boundaries represent “physical, temporal, emotional, cognitive and/or relational limits that define entities as separate from each other” (Ashforth et al., 2000, 474). Translating the concept of boundaries in the connectivity context, we define connectivity boundaries as cognitive and emotional frontiers that separate the connectivity patterns that align with an individual’s preferences, are situation-appropriate, and are perceived as conducive for collaboration from those connectivity patterns that oppose one’s preferences, are situation-inappropriate and are regarded as hampering collaboration. In this case, “situation-appropriate” refers to the adequate type and amount of connectivity required in a specific situation. For example, while an individual is engaged in focused work that requires in-depth thinking, low amounts of connectivity in the sense of few interactions with counterparts would be appropriate. Yet, in case of a conflict between two team members, a higher amount of connectivity would be appropriate so that both parties can share their perceptions of the situation at hand and solve the underlying issue. We intentionally chose this oxymoron combining the two incongruent concepts connectivity and boundary, to reflect the complex tensions between appropriate amounts of connectivity and excessive or too low amounts. Analogously to the saying “too much of a good thing” describing that many things or activities are beneficial and useful in certain amounts, but harmful and detrimental in excessive amounts, we claim that while a certain amount of connectivity is regarded as conducive to facilitating collaboration and work outcomes, excessive amounts lead to constant interruptions and intrusion of private lives (MacCormick et al., 2012, Mazmanian and Erickson, 2014). As such, connectivity boundaries are idiosyncratic for each individual and may differ depending on the role the individual occupies at a specific point in time.
Similar to Kreiner et al. (2009), we adopt the social construction approach, which treats individuals as active agents in the co-construction of boundaries. Therefore, we claim that people socially construct and shape their idiosyncratic connectivity boundaries. Connectivity boundaries allow individuals to make sense of various availability and responsiveness expectations in their private and professional context and serve as a framework to decide when, how and to whom to connect and when, how and from whom to disconnect. These boundaries are real for individuals in the sense that individuals perceive them as real and act upon them (Ashforth et al., 2000). For example, when a person constantly receives emails from their counterpart on the weekend and they ask their colleague to stop, they act upon their connectivity boundary that is real for them but invisible and perhaps not reasonable for their counterpart. These boundaries, their features, and meanings are not static but negotiated and transformed through interactions with other actors over time. Furthermore, boundaries might differ depending on the specific roles individuals occupy (Ashforth et al., 2000, Bulger et al., 2007). People usually not only play one but several roles. In our case, the participants occupied the role of a consultant for the client, a subordinate and team member to their manager, a peer to their colleagues, a manager to their subordinates, and their roles in their private lives such as a wife, a mum, or a sister to name just a few.
Boundary work “consists of the strategies, principles and practice that we use to create, maintain and modify cultural categories” (Nippert-Egg, 1996, 564), in our case, connectivity boundaries. It involves the sorting, assigning, and defending of the inclusion or exclusion of aspects into the respective categories or domains (Nippert-Egg, 1996). For example, individuals may set a rule to still respond to text messages after 9 pm (inclusion), however, do not accept any calls after 9 pm (exclusion). Therefore, receiving and responding to text messages in the evening is still regarded as acceptable behavior and within connectivity boundaries, whereas receiving a call after 9 pm is perceived as intrusive and outside one’s connectivity boundaries. Individuals’ idiosyncratic boundaries are less likely to be institutionalized (socially shared) and therefore individuals must diligently apply boundary work tactics to defend their boundaries against erosion or incursion (Ashforth et al., 2000).
We claim that connectivity boundaries are not static but evolve over time depending on the professional and private demands and needs individuals face. Kreiner et al. (2009) explored how people manage their boundaries and found that people use different tactics, including behavioral, and communicative tactics in order to find the optimum between segmentation and integration of two spheres, in their case home and work. Behavioral boundary work tactics enable people to protect or relax their boundaries by leveraging technology, invoking triage, and allowing differential permeability. Communicative boundary work tactics include communicating clear expectations by outlining the preferences through nuanced signals or direct conversation before any violation occurs. Translating this concept in the connectivity context, boundary work tactics refer to strategies that individuals apply to create, maintain, and modify their connectivity boundaries through aligning, adapting, and changing their and/or their counterpart’s connectivity patterns.
Kreiner et al. (2009) define boundary violations as behaviors, events, or episodes that either breach or neglect the desired boundary. In case a violation has occurred, individuals used the tactic of confronting violators to correct other people’s behavior that reflects the disrespect or ignorance of one’s boundaries (Kreiner et al., 2009). We refer to boundary violations in the context of connectivity, as the breach or neglect of an individual’s connectivity boundaries through the application or request of connectivity patterns that do not align with the individual’s connectivity preferences, are regarded as situation-inappropriate or hamper the collaboration.
We use three established concepts that are commonly used in boundary theory (Nippert-Egg, 1996, Ashforth et al., 2000), which are boundaries, boundary work tactics, and boundary violations and translate them in the connectivity context to inform our theorizing process to explain how individuals in collaborative settings align their connectivity patterns and create, maintain, temporarily change, or reclaim their connectivity boundaries.
Methodology
We conducted a case study with an interpretive lens to collect and analyze data (Myers and Walsham, 1998, Walsham, 1995, Walsham, 2006, Klein and Myers, 1999). We chose the consultancy industry as our research setting as this industry is well known for its attitude of constant availability and responsiveness, which is often sold as part of the “product” (Mazmanian and Erickson, 2014). It is what we call a “high-connectivity” context, which is characterized by (a) norms of near-constant availability and timely responsiveness (Murphy, 2007, Mazmanian, 2013, Mazmanian et al., 2013, Kolb et al., 2020), (b) work intensification including the attitude to work anywhere and anytime (Dery et al., 2014, Wajcman and Rose, 2011), and (c) frequent online or in-person interruptions (Wajcman and Rose, 2011) by IT immersion and intrusion (Mazmanian et al., 2013).
Our case study took place in an international consulting company, where co-located and distributed project teams collaborated very closely within and between their project teams but also with the clients and were dependent on each other’s availability and responsiveness. Due to this dependency, this case was suitable to explore the consultants’ boundaries and the boundary work tactics (Kreiner et al., 2009) that they applied to align connectivity expectations, improve efficiency and productivity plus avoid conflicts and intrusion into their private lives.
Data collection
We conducted 39 semi-structured interviews and observed the consultants during their daily work practices. The data collection covered three phases. The first one took place in November 2014, the second in December 2014, and the third in February 2015. We developed and discussed the interview guideline in the author team in three iterative circles and carried out two pilot interviews with the employees to check clarity and comprehensibility. The interviews were conducted in a semi-structured manner (Wengraf, 2001) by asking questions about (a) the general connectivity patterns of the user, taking into consideration possible different connectivity patterns with various stakeholders, for example, project team members, clients or managers, (b) the advantages and disadvantages of ICT usage in the private and work-related context, and (c) the alignment of connectivity patterns within the teams the participants were working in, including the interactions with clients. However, we remained open to any new phenomena and topics that fit our research topic.
Our first 2-week phase of data collection took place at the host company’s headquarters, which is located in Germany and the client’s site, where we conducted 16 face-to-face interviews and observed their office behavior routines. The interviews of the second round of data collection were held via Skype as we interviewed the consultants in America and China or other interviewees were are rarely available in the office of the consultancy. The third round of interviews took place during another onsite stay at the consultancy for one week in February 2015.
The interviews were recorded and transcribed after completion of all interview rounds. The average interview took 60 min, whereas the duration ranged between 30 min and up to two hours depending on the availability and the interest of our interviewees. The interviews were conducted with executive board members, project team leaders, project team members, IT experts, and HR employees to capture a diverse range of perspectives across the organizational hierarchy and across different professional backgrounds. We further aimed to interview project team members from different teams to capture potential differences in team norms and rules and connectivity patterns depending on the nature of the project, the strategic importance, and the criticality of the project deliverables. We ensured demographic diversity by selecting interviewees from every age cohort, such that the majority of our interviewees were between 25 and 40 years old (25 participants), which reflects the age distribution of the company. Many of them grew up with (mobile) ICT (17 participants) and had worked with mobile devices such as smartphones, laptops, and tablets over a considerable timeframe. Therefore, our interviewees were generally tech-savvy and interested in new ICT and applications that helped them in their daily work processes and in their private lives. As the company operated in three different geographical markets (Europe, America, and Asia), we were able to observe and/or interview participants from three different cultural environments. We interviewed 10 women and 29 men, which reflects the gender distribution of the company and is in line with the male-dominated workforce in the consultancy industry, in particular on the leadership level (Statista, 2022, Statista, 2021a, Statista, 2021b). Please find a detailed overview of the participants, including their demographic details in Table 1 in the Appendix.
Besides the interviews, the first author observed the consultants onsite during their daily work, participated in meetings and discussion rounds, accompanied them to a client and engaged in informal water-cooler conversations. Also, as the first author spent time between the interviews in the organization’s communal areas like the kitchen, she got to know many employees, learned more about their professional and private backgrounds, and listened to their honest opinion about the communication but also connectivity issues within the organization and in the various project teams. Employees were more open during those informal conversations that were not recorded, hence shared their experiences and perspectives more freely. Besides those social interactions, she also participated in a workshop on how to better align and incorporate the work of the task forces that work on topics such as quality assurance, time management, and data management into the daily project work. This showed that there were missed opportunities how to leverage the expertise of those task forces in the project teams. The observations were important to get a holistic picture of how the consultants connect with each other and with clients, to be able to interpret the statements of the interviewees, and to see how their described connectivity patterns were carried out in practice.
To ensure trustworthiness of our findings, we followed three strategies. First, for data triangulation, we collected secondary data, including the organizational structure, the strategy and vision of the consultancy, the company’s internal and external communication strategy, and the project teams internal communication rules and norms mainly in the form of power point presentations or photos of flipchart drawings. The secondary data helped us to learn about the internal organizational structure, the internal communication paths, the communication strategy with clients and allowed us to identify prevalent weaknesses which should be resolved. Second, we conducted member checks so that we requested feedback about the accuracy of the write-up (Brink, 1993). Third, we provided thick descriptions (Brink, 1993, Curtin and Fossey, 2007) of the motivation of the research, how the researcher stands in relation to the participants and the impact the researcher might have had on the participants (limitation section), how the data were collected and analyzed and we provide a very rich context of the consultancy to understand when, how and why the strategies to align connectivity patterns were applied.
Data analysis
The main data analysis using NVIVO software was conducted after completion of all data collection rounds following the abductive logic (Bygstad et al., 2016). We analyzed the interview notes between the data collection phases and discussed the preliminary outcomes within the author team. We took our insights from the first and second interview rounds into consideration in the consecutive rounds so that we could ask more specifically or check if there was any ambiguity in the answers to our previous interviews.
Figure 1 visualizes the different steps in the data collection and analysis process. Data collection and data analysis process.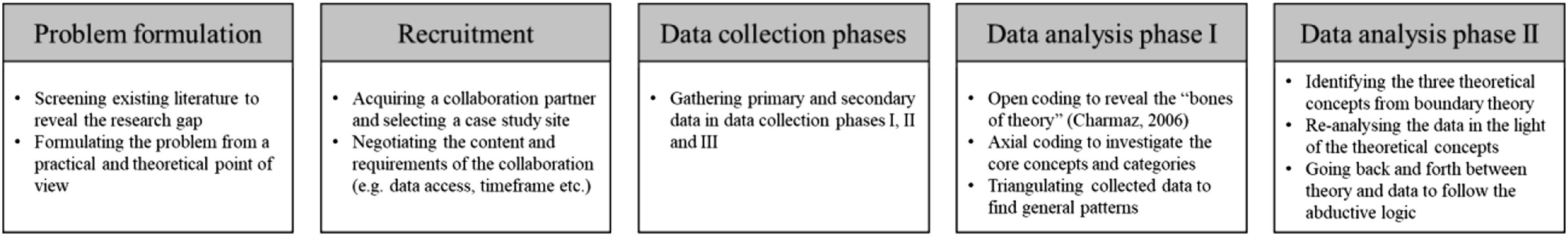
The data analysis took place in two phases. In the first phase, we used techniques from the grounded theory approach, such as open and axial coding (Charmaz, 2010, Strauss and Corbin, 1998) to identify the main dimensions as well as their relationships. We used the open coding technique (Babchuk, 1996, Glaser, 1992) to analyze the interview transcripts, field notes, and secondary data. In doing so, we read the transcripts carefully and coded each paragraph using telling open codes that were as close to the data as possible yet were tinted with our own interpretation as scholars. We then used the axial coding technique (Strauss and Corbin, 1998) and started to theorize about the different strategies people use to improve the connectivity with their counterparts and what they do when someone crosses their connectivity boundaries. Furthermore, we had a closer look at when and how they changed their connectivity patterns. We also found that applying these strategies had led to various positive outcomes, which we further explored.
In the second phase, we looked for suitable theoretical concepts to better explain the strategies that people apply when creating, aligning, and negotiating their connectivity patterns as well as creating, maintaining and changing their connectivity boundaries. We decided that the concepts boundaries, boundary work tactics, and boundary violations originating from boundary theory (Nippert-Egg, 1996, Ashforth et al., 2000) are helpful for the framing and theorizing of our strategies. It is important to note that the qualitative process analysis was not straightforward but involved a lot of iterations, discussions amongst the authors and the refinement of codes and categories. In order to illustrate our coding process (including phases 1 and 2), we provide an example and an illustrative coding table as the chain of evidence in the Appendix. This shows how we coded the original voices using open and axial codes that served as input for theorizing the different boundary work tactics taking into consideration the theoretical concepts from boundary theory.
Case description
The consultancy had been founded in 1999 and grew quickly to become a medium-sized company at the time of the study. The majority of the employees were in their 20s and 30s, technology affine and with high professional expectations. The consultancy’s core businesses were project management and process optimization in various industries. The company had 10 project teams that differed considerably in terms of location (distributed vs co-located), nature of the project, size, time working together, etc. Although the main communication channels were still face-to-face meetings, email and phone calls, a lot of teams used Lync, Skype, or WhatsApp to connect to each other for professional and private purposes.
The consultancy generated 80% of its turnover from one major client who was a global leader in the automotive industry. The majority of employees worked for this particular client. The consultancy was specialized in operational consulting and supported the client in their daily work and management processes. The consultants intensively collaborated with their colleagues within and between the project teams as well as with clients. Both consultants and clients were highly dependent on their counterpart’s availability and responsiveness in order to complete their work tasks or make decisions. If they were not in the same office or at the client’s site, they coordinated the tasks and discussed their topics using skype, email or phone calls. As the consultancy was specialized in project management, they supported their clients not only in the operational but also in strategic project management tasks. They planned and discussed the next work packages with the client, scheduled milestones, allocated and executed tasks, and kept each other updated on the current status of the project. This required almost constant information exchange and as the consultants mainly worked in the project management office or in the head office, they communicated extensively through ICT with their clients requiring mutual availability and responsiveness. Overall, the study setting was well-suited to understand how individuals adjust their connectivity patterns to improve their collaboration practices.
Findings
In order to align their connectivity patterns, establish an efficient and productive collaboration environment and create, maintain, or change their connectivity boundaries, our participants applied six boundary work tactics: externalizing, accommodating, adapting, pushing, sacrificing, and enforcing. We show that these boundary work tactics were applied by stakeholders of various professional backgrounds, including executives, project managers, consultants, and employees of support functions such as HR and IT. In turn, their professional background and the associated power determined by the organizational hierarchy impacts one of the contextual factors, that is, power distance, which plays a key role in three out of six boundary work tactics.
Our participants usually observed the connectivity patterns of their counterparts first and then used the different boundary work tactics to align their connectivity patterns in order to achieve efficient information exchange and to protect their connectivity boundaries. These connectivity boundary work tactics facilitated collaboration success as the aligned connectivity patterns enabled effective communication among project team members, which is crucial to accomplish tasks and solve problems at hand. The observations of the counterparts’ connectivity patterns were based on the participants’ subjective perceptions, which might or might not be in line with the counterparts’ perceptions of their own connectivity patterns. In the following, we elaborate on the six boundary work tactics that differ in terms of when they are applied (contextual factors) and why (goals).
Externalizing
At the beginning of a new project, the consultants often do not know the client and the client’s team. They do not know how they work, how they coordinate tasks, how they interact and how they connect. In order to avoid any conflicts or inefficiencies, the company has developed a method for successful project management that the consultants apply in their projects. The company method promotes common factors for collaboration success such as building shared governance structures, establishing clear roles and responsibilities and facilitating open and frequent communication. One important part of the project set-up is to define the “reporting and communication paths.” John, the CEO of the American affiliation, explains that they want to establish a low power distance between the client and the consultants as well as a good working atmosphere between the client’s team and the consultants as they need to collaborate closely.
Transparency and setting expectations are key and help the collaborating parties to develop a shared understanding of whom to approach in a certain situation, when, that is, timing of approach, and through which communication media. The key to
John explains, “You need to align with your client and within your group what is the definition of urgent, … what is the definition of normal… Because you don’t want to send false leads where it’s normal communication, but you are doing it as an urgent communication. So you just need to clarify and define. What a lot of the company method is if you’re familiar with it, …We have as one of the nine steps the communication escalation paths so we need to define what is urgent for you. Is the same (thing) urgent for me? That way, I’m not calling you on my urgency level but by your standard, that’s just a normal communication. We’re already creating conflict by you having definition one and I’m having definition two. We try to align that with the communication and escalation profiles.” (John)
Besides the timing of approach and the communication media, the consultants also discuss the meeting time and frequency with their co-workers and clients. Scheduling meetings often requires “I try to tell the client that it makes sense to establish regular meetings at the beginning and at the end [of the project] to exchange ideas, to talk about our opinions and perspectives, and to get on the same page. I also ask him how he sees that. That is exactly what I meant with “picking him up” and then we find a common ground. If he then says, that is too much for me, I don’t need that, I actually feel good with that. Then we can reduce [the number of meetings]. But at the beginning, it is important that you “walk next to each other.” If we then have a mutual understanding, we can “walk independently.” (Mike)
The consultants also apply externalizing when they introduce a new employee. The consultancy has established a mentorship program so that each new employee gets a mentor, who should help the new employee during the first couple of weeks, show them around, introduce them to other colleagues, tell them about the general work processes, and also discuss the company and project-related connectivity rules and norms as well as the institutionalized connectivity boundaries that are socially shared, with them. Introducing new entrants to the governance structures, clarifying their responsibilities and explaining to them the common purpose of their team creates a fertile ground for successful collaboration. As externalizing is part of the onboarding phase, it is used every time a new employee joins the company. In line with this, unknown connectivity norms and rules and lack of time working together were strong predictors for externalization, as seen in our data. Tamara, who did an internship with the company right after finishing her studies, worked on the China team. She was based in Munich while the consultants were alternating between Germany and China. When she started her internship, they also discussed the time zone differences and how it impacts their connectivity and especially the timing of getting in contact with each other. Her mentor set the expectations right at the beginning: “I knew that if it is 12 pm here [in Munich], it was 6 pm for them [in China]. That meant that if there were any urgent topics, I contact them. We talked about that [rule]. “So you know how the time zone difference is, if there is anything urgent where you need our help.” (Tamara)
Casper, who was working in the China team as a consultant and alternating between Germany and China, mirrors Tamara’s statement on how the team managed the time zone differences of six hours or even seven hours during wintertime. He explains that if there are any important topics to discuss, he would call the German team at 2 pm in China as he knows that they will then have arrived at the office. “If there are very important topics to discuss, then I would call the people in Munich at 2 pm [China time] and exchange ideas on those topics. In any case, they usually have a full inbox with everything I worked on and sent them during my morning.” (Casper)
Accommodating
The consultancy has specific connectivity norms and rules about when and through which communication media the firm expects the consultants to be available in order to establish a seamless information flow and knowledge exchange among the consultants and a good customer service for their clients. Selina, who is part of Patrick’s team, explains, “We have internal rules of the game, which also include responding to emails, calls etc. within 24 h. Also, if you just confirm that you read it, but you do not have the answer yet, so you tell your counterpart that you come back to them by a specific time” (Selina). The consultants have incorporated the connectivity norms and rules when creating their own connectivity patterns and connectivity boundaries. That means that they expect that everyone complies with those norms and rules so that they can interact effortlessly and productively and maintain their connectivity boundaries. The established trust and certainty and the open and timely communication in turn facilitate collaboration success. We define accommodating as a mutual boundary work tactic where two or more people adopt established connectivity norms and rules and maintain their connectivity boundaries. Accommodating is a strategy that is engrained in their professional identity as consultants and was therefore commonly observed in the data.
In teams that have worked together for a considerable time, the project team members sense and evaluate the current situation and then switch to the appropriate communication medium depending on the circumstances. Rainer, who is one of the well-established consultants in the company and has a lot of project experience in national and also international projects, explains that some project teams are so well attuned it seems that their interactions follow a script, which determines what communication media to use in which situations. The common work history and the existing connectivity norms in those established teams were common predictors of accommodating. Rainer notes that when the consultants in his team sensed that the medium they were using was not conducive to solve the problem or a project team member was not available in person, they seamlessly switched to an adequate one without giving notice or discussing it. This flexibility allowed them to discuss the topics more efficiently and to maintain their mutual availability and responsiveness.
“We were all sitting at the same place and mainly communicated face-to-face. We just had to turn around, talk across the table and could coordinate ourselves in the best possible way. If one of us was not at her place, it was really easy to get an info by email. In general, if we wrote two emails back and forth and we realized that we cannot solve that by email we immediately called each other to synchronize the communication and to clarify the issue. The same happened when we couldn’t call each other, we just switched to SMS or something similar. So, we communicated very efficiently, very quickly and also quite considerately. So we knew that there are certain rules of the game and we also knew how we can reach each other through which media and we used that knowledge.” (Rainer)
Having strong social ties was another powerful predictor for applying accommodating. Till and Nick are both on the management board of the consultancy, have known each other for over 11 years and have worked together on various projects. They claim to have the same work attitude and are almost constantly available through various communication channels. Nick explains that it is easy for them to adapt because they are good friends and have worked together for such a long time. “Some words are enough. With some colleagues it is like this. For example with Till, Till and I are sitting in a meeting, and I just have to look at him or shake my head, and he knows exactly what I want. I don’t have to wait a long time, suddenly a file pops up on my Laptop, as he knew exactly, that I wanted this one. The longer you work together, the more you get attuned to one another.” (Nick)
The same sentiment is reflected by Till, who prioritizes requests from Nick as he knows it is important: “There are definitely differences. For example, with Nick. I respond the next minute or answer my phone if I know he needs a response as I know it is important or urgent if he has a request. For others, I wouldn’t always do it this way. For others, I will respond within a day [in line with the company norms].” (Till)
By working together for such a long time and spending time together outside work, they have learned about each other’s connectivity boundaries and have developed common norms and rules of how to interact most efficiently. This, in turn, allows them to communicate effectively and solve problems in a timely fashion contributing to their successful collaboration.
Adapting
Within the consultancy, junior consultants usually adapt to their senior colleagues, consultants adapt towards their project team leaders, and the project team leaders align their connectivity patterns with those of the management board members. Power distance is an important driver for adapting and the strategy is commonly applied by the subordinate in the organizational hierarchy or by the consultant in the client–consultant relationship. The person who is in a lower position of the hierarchy or in a service position usually explores the connectivity patterns of the superior or of their client and adapts their connectivity patterns accordingly.
We define adapting as a unilateral boundary work tactic where one person voluntarily adapts to the connectivity patterns of their counterpart or group and thereby cooperatively complies with the connectivity boundaries of the counterpart whilst maintaining theirs.
Adapting is not only a sign of respect and acknowledgement but also increases the likelihood to get the information they require, therefore affording seamless information exchange which in turn facilitates their collaboration success. Mareen, who has worked at the consultancy for many years, explains that she first tries to explore when and through which channels her project leader Frederick is available. She then accommodates Frederick not only because he is in a higher position in the company but also because she needs information from him. In this case she, in her role as subordinate, is adapting to his connectivity patterns in his roles as manager while staying within and maintaining her connectivity boundaries as she is applying connectivity patterns she feels at ease with. “So I think from our side [project team members’ side] it is difficult to influence the project leader. I think it is rather the other way round. That we are influenced by his connectivity patterns, that we orientate ourselves towards him, how available he is and most of the time we want something from him. And so you try to comply with his behavior.” (Mareen)
By adapting her connectivity patterns and using his preferred communication media, she increases the likelihood that he responds and therefore improves his responsiveness.
Besides the communication media, the consultants also adapt their communication style to facilitate the interaction and to avoid misunderstandings, which in turn facilitates collaboration with their counterparts. They do not just adapt to their superiors but also to their colleagues and especially to their clients, which is in line with their high professional expectations. Those high professional expectations in turn were a strong predictor for adapting as observed in our data set. If the communication partner is sensible and pays a lot of attention to politeness and form, they usually adapt by describing the task in more detail and politely. Selina, one of the project team members, explains that she first tries to sense her counterpart’s preferred way to interact. Depending on that, she will adjust how many details she will provide for a specific task or how quickly she can send out new requests or information. By adjusting the frequency of interaction, she is still within her connectivity boundaries as for her it does not matter how quickly and in which detail she provides the information. She emphasizes that it is not a straightforward process; there is a lot of trial and error involved to find the most conducive way of interaction. “I certainly adapt to the client in this respect. Well, that has nothing to do with client or not client, but with the communication partner himself. If I know the communication partner is someone who prefers short sentences or clear instructions or anything else, it is easier for me when I comply with that without twisting myself too much. If I know someone needs a little bit more time between the things [topics], then I know I address every topic individually and if I know the person can handle it I rattle the topics without periods or commas in any speed that works. I think that has to do with experience, a lot of trial and indeed a lot of trial and error.” (Selina)
By pleasing the client and adapting to their preferred way of interaction, consultants create an atmosphere of trust and open communication as clients feel at ease which in turn contributes to their successful collaboration.
Pushing
Pushing is a boundary work tactic that individuals apply to change the counterpart’s connectivity patterns as they are not conducive for collaboration or the project situation. Pushing is usually applied by those who occupy a higher position in the organizational hierarchy or by clients as they are aware that accommodating is part of consultants’ etiquette. They know that they have the power to influence or even enforce the consultant’s connectivity patterns. Therefore high power distance and high professional expectations were common predictors of pushing as observed in the data. We define pushing as a unilateral (and generally temporary) boundary work tactic where individuals persuade or force their counterparts to change their connectivity patterns to the extent that changes or even violates their connectivity boundaries.
The China team is in general known for having long working hours, a lot of travel time, and for being very committed to their team and to the client. However, the team went through a critical phase, as they got a new contact person in the client’s team who was very difficult to work with. The new representative of the client did not accept the consultants and refused to collaborate. During that time, the new client representative escalated a lot of issues to his superior and the team had to work late nights and had appointments with the client until 10 pm. In this difficult period, one of his project team members approached Finn, the project team leader, and told him that he could not handle this constant pressure anymore. Finn, who is usually sensitive and empathetic, told him he understood his situation, but that they had to push through this critical project phase together, which required longer working hours and constant availability. By doing so Finn asked the project team member to change his connectivity patterns in order to deal with this difficult project phase, which required his team member to change his connectivity boundaries. “Especially in China it was really extreme having appointments with the client till 10 pm and I didn’t force him to anything, and he openly said that this is too much for him and we figured out a solution in some way. … I remember that I talked to him that I think it is important that he is honest with me, but on the other hand that I require that he pushes through these critical phases with us. Because that is the expectation.” (Finn)
Critical project phases were another predictor for applying pushing, which enabled the consultants to establish temporary norms and rules to facilitate efficient information exchange and demonstrate outstanding work ethics towards the client. This in turn established trust in the consultants which consequently improved the collaboration with the client.
Pushing is not only applied to change the counterpart’s availability and responsiveness but also to switch communication channels that are deemed more appropriate for collaboration. For example, a project leader asked his employee to call instead of emailing to clarify certain issues, while the consultant actually preferred to write emails as it gave her time to craft her response. In doing so, the project leader used the power that is associated with his role as project leader, pushed the consultant beyond her connectivity boundaries and asked her to use a channel with which she is less comfortable. Despite being out of her comfort zone, calling instead of emailing provides a better opportunity to discuss issues in a more timely manner and provide more context information which has a positive effect on collaboration outcomes.
In some cases, pushing is also used by senior managers to alter the connectivity patterns of their clients to interact more efficiently. It is important to note that power distance is not only related to hierarchical power but can also originate in knowledge or expertise differences. For example, senior consultants usually have more experience and expertise in a specific subject matter or management of projects than clients, which provides them with power and consequently the ‘right’ to demand certain connectivity patterns from their customers. For example, due to regulatory issues, the consultants had to move from the clients’ offices to a project office which was also on the car manufacturer’s premises, yet 10 min walk away. As the clients couldn’t just quickly talk to the consultants who used to sit close by, the consultants had to “educate” them to collect all their requests and discuss them in meetings or through email, which pushed them out of their comfort zone “The nice thing is that since we are sitting away from the client now, we do not have the face-to-face interruptions from the client anymore. We are currently educating them that they collect all their requests for the regular meetings or in emails and do not bother us anymore all day long. Therefore, we got more freedom from my perception.” (Frederick)
Sacrificing
Sacrificing is a boundary work tactic where individuals change their connectivity patterns in order to accommodate the person or situation at hand at the expense of their own connectivity boundaries. Sacrificing differs from adapting as in the case of adapting, people do not violate their connectivity boundaries and can adapt their connectivity patterns easily. We define sacrificing as a unilateral (and generally temporary) boundary work tactic where individuals amend their connectivity patterns to the extent that violates and/or changes their connectivity boundaries.
In line with their high professional expectations, the “customer is king” attitude is deeply embedded in the consultant’s attitude and therefore they often compromise their own private time to accept customers’ calls or respond to text messages to comply with their role of being a consultant. In doing so, they violate their own connectivity boundaries in order to provide excellent customer service. “Yes, I’ve even had customers call at 11 pm, at night, I do not want to say you do not think about it, but it’s more than a normal occurrence, it happens a lot. And it’s texting, it’s texting on the phone, it’s emails, it’s a phone call sometimes, but generally the earlier it is or the later it is, it’s a text or an email… ”(John)
While the consultants accept the intrusions in their private life and allow for frequent interruptions, they thereby facilitate open and frequent communication, which is an antecedent for successful collaboration. Sacrificing was particularly often applied when the customer was very important for the company and they couldn’t afford to lose the contract. Therefore high professional expectations and commercial risk were strong predictors of sacrificing.
Consultants also violated and changed their own connectivity boundaries in extreme project situations that required the project team members to step “outside their comfort zone” themselves. For example, the China team often had to escalate problems or discuss the next steps for time-critical tasks late in the evening. “Previously, I had to call the CEO late at night, around 11 pm, as the client somehow had another problem with our work.” (Casper)
By sacrificing their after hours, the consultants established timely communication within the team to discuss critical issues and solve problems which in turn facilitated their team collaboration but also allowed the team to comfort the client.
The consultants did not just violate their connectivity boundaries in critical phases during the project but also and especially at the beginning of the project, where they had to prove to the client that they were worth their money. One of the motivated junior consultants is narrating about his “hard work will pay off” boundary work tactic by trying to always be available for and responsive to the client. “Yes, that depends on the project situation. So there might be projects from colleagues where it isn’t the case, but if you just started as a new consultant with a client, we have the goal that we want to gain that client as a long-term customer, therefore you exceed the 100%.” (Thilo)
Enforcing
Enforcing is a boundary work tactic that is applied by individuals whose connectivity boundaries have been (repeatedly) violated, and they persuade or force their counterpart to change their connectivity patterns in order to re-establish compliance with their connectivity boundaries. This violation can materialize as too much connectivity, for example, too many incoming emails at inadequate times or too little connectivity, for example, not responding in a timely fashion that compromises collaboration efforts, yet the underlying activity of reclaiming one’s connectivity boundary remains the same. The main trigger of enforcing is the (repeated) violation of someone’s connectivity boundaries. We define enforcing as a unilateral boundary work tactic where individuals whose connectivity boundaries have been violated force their counterparts to adapt their connectivity patterns and thus reclaim their (the enforcer’s) connectivity boundaries.
Nick, who is part of the management board, has a “buddy-type” personality and is friends with many other consultants. However, when he transitions from his role as colleague to project manager, he is absolutely serious and committed when it comes to his projects and the interactions with his clients. “But you have to be aware, that I get nervous in certain cases. So in my world, it is not logical at all, so when I write you an email and you do not respond to this email within three days I get really nervous. Then I give you a call, write another email as I do not know what is happening now, did he get it, did he read it. Therefore, I have certain expectations towards my team, so that we all commit to one work model, we want everyone to respond to emails within 24 hours, for example.” (Nick)
If his counterparts do not comply with the norms and rules he has set and therefore violate his connectivity boundaries, he pushes them to adapt by sending out follow-up emails, calling them or reminding them of the company’s 24-h rule to put pressure on them. Such violation of his connectivity boundaries and the company’s connectivity norms and rules were strong predictors of enforcing. Nick reclaims his boundaries by asking his colleagues to commit to the agreed response time to decrease uncertainty but also to reduce his own effort to get the required information. By enforcing timely and open communication, he facilitates frequent information exchange which affords better collaboration. Nick cares a lot about when and how people contact him, and if he does not like how they talk to him, he confronts them directly as his connectivity boundaries were violated. “Yes, everyone has that time. That are 5 letters [Danke - word for thank you in German] you have to type. Nobody will lose face when doing it. But you have to educate the people a little bit. Leadership is always a bit of adult education. We have to teach them what the parents didn’t manage to do.” (Nick)
In cases where individuals perceive that their counterpart’s connectivity patterns intrude into their private life or put too much pressure on them with regards to availability and responsiveness, they reclaim their connectivity boundaries. Constantin, who works at the American affiliation as a project manager, is very annoyed by people sending out emails in the evening or during the weekend as he thinks they are engaging in “impression management” and want to show off. The transparency aspect of virtual communication allows people to demonstrate how “hard they work” and how committed they are by emailing or messaging at unconventional hours. This, however, creates a lot of stress and pressure on the counterparts, especially the young ones as they think 24/7 availability and responsiveness might be expected from them. “It happens too often, yes! Many people send out emails in the evening or during the weekend. I don’t like that at all. This is so swanky. I don’t like that. If there is nothing urgent, I try to avoid working on the weekend and start not until Sunday night. I try to finish as much as I can on Friday so that I don’t have to work during the weekend and if I can’t avoid it, I start on Sunday evening. But 95% of the time I don’t have to work on the weekend. I don’t want to expect that from my employees. If someone has to work every single weekend, I talk to him about it and tell him to avoid that.” (Constantin)
By directly addressing this issue and confronting his counterparts, Constantin tries to reclaim his connectivity boundaries and asks for compliance. In doing so, he tries to signal reduced availability and responsiveness and wants to reduce stress levels, protect their work-life boundaries, and ease off the pressure from the employees to be constantly available and responsive. Hence, he creates a psychological safe environment with clear responsibilities on when and when not to be available and responsive which in turn facilitates collaboration success. Enforcing is commonly observed if there is a high power distance between the person who is applying enforcing and those that are asked to accommodate.
Discussion
The goal of this study was to answer the research question: “How do individuals in collaborative settings align their connectivity patterns in order to improve collaboration outcomes and protect their connectivity boundaries?”
We found that all our observed stakeholder groups, that is, executives, project leaders, consultants, and members of HR and IT, engage in boundary work (Nippert-Egg, 1996) and used six boundary work tactics (Kreiner et al., 2009) to (a) make sense of the counterpart’s connectivity patterns, (b) adapt their connectivity patterns or force their counterpart to accommodate and (c) create, maintain, temporarily change, and reclaim their connectivity boundaries in order to enhance collaboration. Specifically, they used externalizing to create shared connectivity boundaries, accommodating and adapting to maintain, pushing, and sacrificing to change their counterpart’s connectivity boundaries and their own and enforcing when their connectivity boundaries have been violated and they want to recover them.
Individuals try to safeguard their connectivity boundaries by using the boundary work tactics externalizing, accommodating, adapting, and enforcing, however, as they are also aware that they have to meet their professional expectations and go the extra mile in specific projects or critical project phases they use pushing and sacrificing to change their counterparts’ and their own connectivity boundaries temporarily.
The boundary work tactics can be regarded as tools in a toolbox. We found that individuals use the various tactics with different counterparts, for example, client versus colleague, and depending on the situation they are currently facing. For example, a consultant might use adapting and makes himself available for client calls in the evening, whilst at the same time uses enforcing with one of his team members, who frequently emails him on the weekend. Further, team members might use accommodating under normal circumstances, but pushing and sacrificing to work and be available during the weekend to finish urgent project tasks. Therefore, we conclude that people are interacting in a dynamic, interdependent system and use different boundary work tactics in parallel with different counterparts in order to improve collaboration whilst at the same time protecting their connectivity boundaries.
Connectivity boundary work tactics.
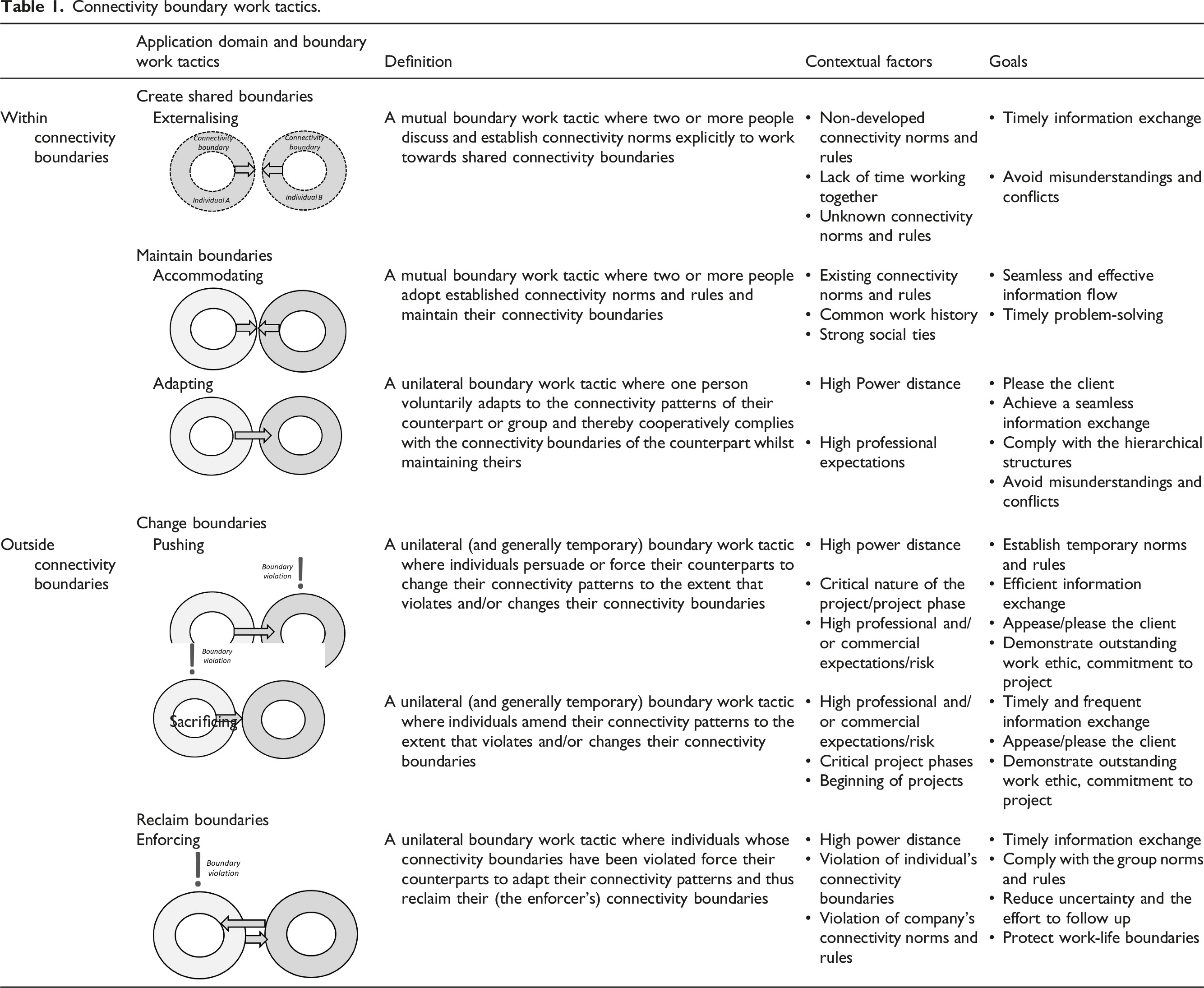
In the following, we elaborate on the contextual factors associated with each boundary work tactic and develop propositions that outline the relationships between the factors and tactics.
Create shared connectivity boundaries
Externalizing was mainly applied when teams started a new project with the client or when a new employee joined the company and the senior employees clarified their expectations. This strategy is in line with Kreiner et al.’s (2009) boundary work tactic “setting expectations” to avoid any boundary violations. However, whilst the tactic in Kreiner et al.’s (2009) study is used by one individual to clarify their expectations to avoid boundary violation, externalizing in our case can be used by one or more individuals to find a common ground and agree on connectivity patterns that are conducive for their collaboration and allow them to form their connectivity boundaries.
Usually, when starting a new project, team members in our study did not have explicit norms and rules to rely on or those were unknown to new hires. Norms are generally defined as behavior patterns or beliefs that are formally or informally established as appropriate by a group (Raven and Rubin, 1976). We found that consultants in their project teams, and also with their client, developed and complied with different connectivity rules and norms that were idiosyncratic to their various groups which is in line with the social identity approach (Turner, 2010). These rules and norms act as a guideline and code of conduct for the consultants and direct the way they connect among themselves or with their clients.
When developing the idiosyncratic connectivity rules and norms in their teams or with the client, individuals engage in externalizing to find a way to interact that is conducive for their collaboration and allows them to shape their connectivity boundaries. The main goal of this boundary work tactic is to allow a timely information exchange and to avoid misunderstandings and conflicts. Therefore, we propose:
Individuals that work in teams with unknown connectivity rules and norms and individuals that have only worked together for a short amount of time tend to apply externalization and create shared connectivity boundaries to achieve timely information exchange and avoid misunderstandings.
Maintain connectivity boundaries
We found that accommodating was applied when the consultants and the client had worked together for a considerable time and/or have formed strong social ties (You and Hon, 2019, Granovetter, 1973). During their collaboration they have developed idiosyncratic connectivity rules and norms that guided their interactions and determined when and how they accommodate their counterpart. These outcomes are consistent with Collins and Kolb’s (2012) study, where the connectivity norms regarding approach and responsiveness determined project team members’ behavior. In their study, established connectivity norms led to an ad-hoc accommodation as the project team members have internalized the norms and knew how they were expected to behave in certain situations. Their accommodative behavior is based on the reciprocity norm (Gouldner, 1960), which obliges the counterpart to return a favorable treatment that they received (Rhoades and Eisenberger, 2002), in our case to accommodate their collaboration partner to allow for seamless information exchange. For example, a team member is in a meeting but still available for her team members through email to answer urgent questions or process requests. When applying the accommodating tactic, individuals are able to maintain their connectivity boundaries while also meeting the expectations of others. The main goal of this boundary work tactic is to achieve a seamless and effective information flow and timely problem-solving so that all counterparts can complete their tasks and solve issues efficiently. Therefore, we state:
Individuals that work in long-established teams with existing norms and rules and strong social ties tend to apply accommodating to achieve seamless and effective information flow and timely problem-solving while maintaining their connectivity boundaries. Adapting is usually applied when individuals face high power distance between counterparts, along with high professional expectations, to please the counterpart and achieve timely information exchange. Power distance indicates the extent to which an individual accepts differences in status, such as formal titles, qualifications, age and/or experience levels (Clugston et al., 2000). We found that our participants usually adapt when they collaborate with a colleague who is higher in the organizational hierarchy, has more power and/or a higher status in the organization. Further, consultants adapt to their clients, which is often seen as part of their service (Mazmanian and Erickson, 2014). For example, consultants tended to adapt their time schedule to be available and responsive to the client and/or respond in a timelier fashion when asked by a more senior consultant. Therefore, power is taken seriously in connectivity boundary management and powerful people are ascribed more “rights” to push for their preferred connectivity patterns whilst maintaining their and their counterparts’ connectivity boundaries. Overall, the main goals of this boundary work tactic are to please the client and superior, to achieve a seamless information exchange, to comply with the hierarchical structures, and to avoid misunderstandings and conflicts. We propose:
Individuals that work in teams with high power distance and high professional expectations tend to apply adapting to please their counterpart, achieve seamless information exchange, comply with the hierarchical structures, and avoid misunderstandings and conflicts while maintaining their connectivity boundaries.
Change connectivity boundaries
Individuals use the boundary work tactic pushing when there exists a high power distance between counterparts (Clugston et al., 2000), if the nature or the phase of the project is critical and when they have high professional expectations. When individuals apply pushing, they force their counterparts to change their connectivity patterns in a way that violates, or at least alters, their original connectivity boundaries to accommodate the current situation they are in. Pushing is similar to the boundary work tactic “allowing differential permeability” where individuals choose which aspects of their two spheres, for example, work–home life are permeable or not (Kreiner et al., 2009). In our context, the consultants demand temporal permeability of the counterpart’s boundaries and ask them to temporarily change their connectivity boundaries to achieve collaboration success. Therefore, whilst “allowing differential permeability” is applied by an individual to compromise some aspects of their boundaries, pushing is applied to compromise the counterpart’s connectivity boundaries. The main goals of this boundary work tactic are to establish temporary norms and rules that allow efficient information exchange, please the client and demonstrate an outstanding work ethic. Therefore, we suggest:
Individuals that work in teams with a high power distance, with high professional expectations and/or commercial expectations/risk, and in critical projects or during critical project phases tend to apply pushing and ask their counterpart to temporarily change their connectivity boundaries in order to establish temporary norms and rules, efficient information exchange, appease/please the client and demonstrate an outstanding work ethic and commitment to the project. Sacrificing is usually applied when individuals are aware and want to comply with their high professional expectations, which become particularly prevalent when they are working on “high stake” projects where it would be extremely costly and reputation damaging to lose the customer. Usually, individuals also sacrifice their connectivity boundaries at the beginning of projects to show that they go the extra mile and are outstanding collaboration partners. Sacrificing is in line with Kreiner et al.’s (2009) boundary work tactic “invoking triage” that involves the prioritization of urgent and important demands of one of the spheres, for example work or life in their case. In the connectivity context, this translates into prioritizing projects and/or counterparts’ demands such as those of the clients over one’s own connectivity demands and preferences. The main goals of this boundary work tactic are to establish timely and frequent information exchange, appease/please the client and demonstrate an outstanding work ethic and commitment to the project. Therefore, we propose:
Individuals that work in teams with high professional expectations and/or commercial expectations/risk, where the project just started or is in critical project phases tend to apply sacrificing and temporarily change their connectivity boundaries in order to establish timely and frequent information exchange, appease/please the client and demonstrate an outstanding work ethic and commitment to the project. However, while pushing and sacrificing, which are often applied to increase connectivity, may facilitate collaboration success (Majchrzak and Jarvenpaa, 2010, Chang et al., 2010), in the short term, it is important to note that these strategies push people out of their connectivity boundaries, either by their counterpart or self-inflicted, so that they are required to apply connectivity patterns that do not match their own preferences. If people operate outside their own connectivity boundaries for too long, it can evoke the negative consequences associated with hyper-connectivity, that is, too much connectivity (Kolb et al., 2020, Mazmanian, 2013) or hypo-connectivity, that is, too little connectivity to work effectively (Kolb et al., 2008, Kolb et al., 2012). These include increased stress levels, loss of autonomy and control of when and how to connect, low work focus, constant distractions, work-life conflict, absent presence, and even affect their social relationships outside work (MacCormick et al., 2012, Büchler et al., 2020, Nurmi and Hinds, 2020). Our participants also realized that the high expectations towards near-constant connectivity (Kolb et al., 2020) in many project teams, on the one hand, but also working with colleagues that do not respond in time on the other hand, can backfire if they are operating outside their preferred connectivity boundaries over extended periods. For example, Casper, who was working on the China project and was almost constantly connected, explained: “I was on holiday when it dawned on me that it [being connected all the time] doesn’t make any sense, takes it all out of me and robs my energy. I was on holiday with my girlfriend in Barcelona for four days, but instead of enjoying the holiday, I was emailing back and forth with the project team for two days straight. That wasn’t nice at all. But then I realized OK I have to stop that and now I don’t send any emails during the weekend” (Casper). Hence it is important to be aware of the negative implications of those strategies and not to overuse them to avoid detrimental effects on employees’ health, productivity, and job satisfaction in the long run.
Reclaim connectivity boundaries
Enforcing is usually applied by individuals who have a high power distance between them and their subordinates, whose connectivity boundaries have been violated and/or the norms and rules of the company have been transgressed. Translated from Kreiner et al. (2009) this could be intrusion violation, that is, that someone crosses the boundary and for example calls the individual late at night or on the weekend, or distance violations where individuals try to reach their counterparts but do not receive a response leading to a lot of uncertainty. Such violations affect the work progress and ultimately collaboration success. Although not stated specifically in their paper, we interpreted Kreiner et al.’s (2009) communicative boundary work tactic “confronting violators” as being in line with our enforcing tactic, where individuals tell the violator to stop or change their behavior during or after the boundary violation. In our context, individuals ask their counterpart to change their connectivity patterns and highlight their original connectivity boundaries which the violator should acknowledge and respect. The main goals of this boundary work tactic are to achieve a timely information exchange, to comply with group norms and rules, to reduce uncertainty and the effort to follow up, and to protect work-life boundaries. We propose:
Individuals with power in the company, whose connectivity boundaries have been violated or who work with someone who doesn’t comply with the connectivity norms and rules of the company tend to apply enforcing and reclaim their connectivity boundaries to achieve timely information exchange, comply with group norms and rules, reduce uncertainty, and the effort to follow up, and protect work-life boundaries.
Theoretical contributions
Our study offers three theoretical contributions to the body of knowledge on connectivity (Dery et al., 2014, Kolb et al., 2012) and collaboration (Boughzala et al., 2015, Cheng et al., 2016). First, the concept of connectivity boundaries extends connectivity (Dery et al., 2014, MacCormick et al., 2012) and collaboration literature (Boughzala et al., 2015, Cheng et al., 2016, Czajkowski, 2007) by showcasing our subjective frontiers separating connectivity patterns that are aligned with our individual preferences, are situation-appropriate and perceived as conducive for collaboration and those that are not. Introducing this concept is important to understand (a) why some teams collaborate very well as their connectivity patterns are aligned, and they respect each others’ connectivity boundaries, (b) why misunderstandings and conflicts in teams can occur in the case of boundary violations, and (c) why individuals might request or even enforce others to change their connectivity patterns to improve collaboration outcomes.
Second, we built on the boundary work tactics developed by Kreiner et al. (2009) and identified the six boundary work tactics externalizing, adapting, accommodating, pushing, sacrificing, and enforcing, which are idiosyncratic to the connectivity context. Those tactics are used by individuals to manage expectations towards availability and responsiveness to achieve successful collaboration whilst safeguarding their connectivity boundaries. In doing so, we are contributing to the literature on connectivity by providing tactics team members can use to manage dysfunctional connectivity states such as hyper-connectivity (too much connectivity) and hypo-connectivity (too little connectivity) to work efficiently and productively (Kolb et al., 2008, MacCormick et al., 2012). We further introduce the possibility to reclaim and temporarily change connectivity boundaries which are new concepts and extend the existing literature on creating, maintaining and crossing boundaries (Kreiner et al., 2009, Ashforth et al., 2000).
While we identified similarities between Kreiner et al.’s (2009) boundary work tactics (allowing differential permeability, setting expectations, invoking triage, and confronting violators), our connectivity boundary work tactics differ in several significant ways, in particular in terms of (a) the individual(s) that are using the tactics, (b) the underlying mechanics, that is, aligning collective connectivity patterns, and (c) goals (e.g., collaboration success) while safeguarding individual connectivity boundaries.
Third, we explain under which circumstances individuals are likely to choose which boundary work tactics and which goals they can achieve when applying those. These insights are presented as propositions that highlight the associations between the contextual factors, the boundary work tactics and goals. Overall, we extend the connectivity literature by highlighting when and under what conditions specific boundary work tactics are applied. These connectivity boundary work tactics allow us to address the two identified research gaps, that are (a) lack of existing research on highly interdependent teams that require mutual availability and responsiveness to be able to collaborate successfully (Mazmanian, 2013), and (b) the missing insight into the workings of strategies, techniques and frameworks that individual can apply to improve their connectivity while circumventing the negative consequences (Mazmanian and Erickson, 2014, Mazmanian et al., 2013). Our identified strategies can be applied in highly interdependent teams to improve collaboration outcomes (Czajkowski, 2007), and we outline specifically how those strategies can be applied to align or realign the counterparts’ connectivity patterns to facilitate successful collaboration.
Managerial implications
The six boundary work tactics can serve as a reference for employees and teams. People can choose a tactic depending on the contextual factors they are facing and depending on what they want to achieve, for example, please the client, achieve seamless information exchange, or protect their work-life boundaries. Therefore, knowing about the different boundary work tactics and when to apply them can help employees and teams in their self-management to establish effective collaboration while at the same time protecting their connectivity boundaries.
While all of the boundary work tactics can be used to improve information exchange and therefore team collaboration, externalizing is used to make the connectivity patterns of each counterpart transparent and to find a common ground on how to collaborate in the best possible manner. This boundary work tactic leads to transparency that allows people to better understand the behavior of their counterpart, reducing misunderstandings and improving productivity (Bertschek and Niebel, 2016).
Accommodating is mainly used by counterparts that are well-attuned and that need to solve problems in a timely manner without violating their connectivity boundaries. Consultants can use adapting in order to make the interaction with their counterpart more convenient and decrease the counterpart’s stress level especially those of their clients, while maintaining their connectivity boundaries. Pushing is mainly applied in critical project phases or situations, where the person that uses the boundary work tactic asks his counterpart(s) to temporarily change their connectivity boundaries to enhance collaboration. Consultants can also use sacrificing and push beyond their connectivity boundaries temporarily, especially in critical project phases or at the beginning of the project being aware of the benefits of their sacrifice and knowing that the situation is only temporary. Enforcing can be used to remind the counterpart of established norms and rules in order to improve cooperativeness (Feldman, 1968), but also to avoid misunderstandings and uncertainty (Berger and Bradac, 1982).
Conclusion
The research has some limitations that must be acknowledged. First, we had to rely on retrospective data from the interviewees, which could be biased by their perception of how and when they or their counterparts adapted their connectivity patterns and if these connectivity patterns were facilitating collaboration. An ethnographic long-term approach to be able to investigate the projects from beginning to end would be required to better understand the triggers and consequences of the boundary work tactics. Second, we could not always interview pairs in order to get the perspective on the applied boundary work tactics from both sides. In the majority of cases, we could only capture the perspective of one counterpart. Third, the main interviewer had similar characteristics such as age, IT affinity, and educational background as the majority of the interviewees, which could have biased their statements towards how they believe they should behave and interact rather than their actual behavior.
In line with the principle of contextualization (Klein and Myers, 1999), we acknowledge that our boundary work tactics were developed in a competitive, male-dominated, high-performance, high-connectivity work environment (Dery et al., 2014) that has influenced not only the nature of our identified boundary work tactics but also the scope of the connectivity boundaries of the consultants. While this was not the case in all project teams, many teams, especially those with important clients, required near-constant connectivity (Kolb et al., 2020) materialized in high levels of availability and responsiveness. The expectations towards near-constant connectivity are highlighted particularly in the boundary work tactics pushing and sacrificing as well as in the wide connectivity boundaries where consultants still respond to text messages at night or respond to client calls while being in meetings. These high expectations regarding connectivity are in line with the standards in the consultancy sector (Mazmanian and Erickson, 2014). However this “electronic leash” that prevents employees from psychologically disengaging from work can be increasingly observed in other industries as well (Büchler et al., 2020).
Therefore, acknowledging that our boundary work tactics are context and time-bound (Neuman, 2000) and hold true in a context of highly interdependent individuals, we welcome further inquiry to extend our understanding of creating, maintaining, changing, and reclaiming connectivity boundaries and the application of boundary work tactics over time, in larger samples and other industry sectors. This might yield to the further refinement of our boundary work tactics or the identification of additional ones. We want to encourage further research to develop our propositions into hypotheses that explore the relationship between the contextual factors and the different boundary work tactics as well as the respective goals. It is important to note that not all collaborations were successful. In a few instances, the counterparts reduced their interactions to a minimum or even ended their collaboration as they could not align their connectivity patterns, which ultimately led to a lot of misunderstandings and conflicts. However, these incidents were exceptions and therefore we focused on the teams where the boundary work tactics have produced positive effects. Studying boundary work tactics that are not successful, in particular those that result in conflict and misunderstanding, is another avenue for future research.
Many of us have received the message “Did you get my email?!” (or words to that effect) at some time in our experience of working with others. Hopefully, our endeavor to decode such messages offers new insights and perspectives on this common, but important act of interpersonal communication. The implications for team collaboration are enormous, especially in a time when virtual collaboration is increasing exponentially (Waizenegger et al., 2020). As connectivity increases, so does the importance of creating, maintaining, and re-establishing personal and professional boundaries. As the old adage goes, “good fences make good neighbors.” We live in an age where boundaries are still essential, but how we co-create and manage those demarcations without sacrificing shared values, information exchange, and service to one another is a challenge that will be with us for a long time in the future.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: Funding has been received through the Austrian Ministry of Education, Science and Research by issuing the Marietta Blau grant to the first author.
Author biographies
Appendix
Demographic details of participants. Coding example and illustrative coding table.
In the following quote, we provide an example of how we coded. We indicate our open codes in square brackets to shed light on our interpretation of the raw data. We usually coded more comprehensively, i.e. the entire paragraph to capture the context, yet in the example below, we indicate the sentences that mainly encouraged us to use the specific open code.
“It’s not good if he [the client] is calling me ten times and he cannot reach me [client-consultant relationship, pressure from client]. That is not good at all. That means when I am sitting in a meeting – especially if it’s an internal meeting – I mean it’s always pretty bad and you shouldn’t do it actually, but when the client is very pushy and important, for example, the CEO of the client company, then I have to leave and I have to answer. [prioritizing according to the counterpart’s role, urgent communication, pressure from client] There are no two ways about it, that is just the way it is. [urgent communication, prioritizing according to counterpart’s role]” (Clemens)
We then followed the axial coding process by comparing and clustering the codes, guided by our research goal, searched for suitable theoretical concepts in the literature and refined our axial codes as the axes of our theoretical framework. Taking into consideration other codes and raw data, the axial codes that those open codes were aggregated into were “unilateral alignment”, “high power distance”, “critical project phase”, “high professional expectations”, “commercial expectations/risks” and “violated connectivity boundaries”. We then derived the three contextual factors “high professional and/or commercial expectations/risks”, “critical project phases”, and “beginning of projects” for sacrificing from those axial codes.
aAfter the completion of the data analysis, we recoded the interview transcripts again to show how many participants elaborated on the respective strategies. The number of participants mentioning the respective strategies should not be regarded as an indicator of importance but should provide transparency about how widespread the respective strategy was applied or encountered according to our participants. Yet we cannot preclude that those interviewees who did not mention the strategies also did not apply or encounter them.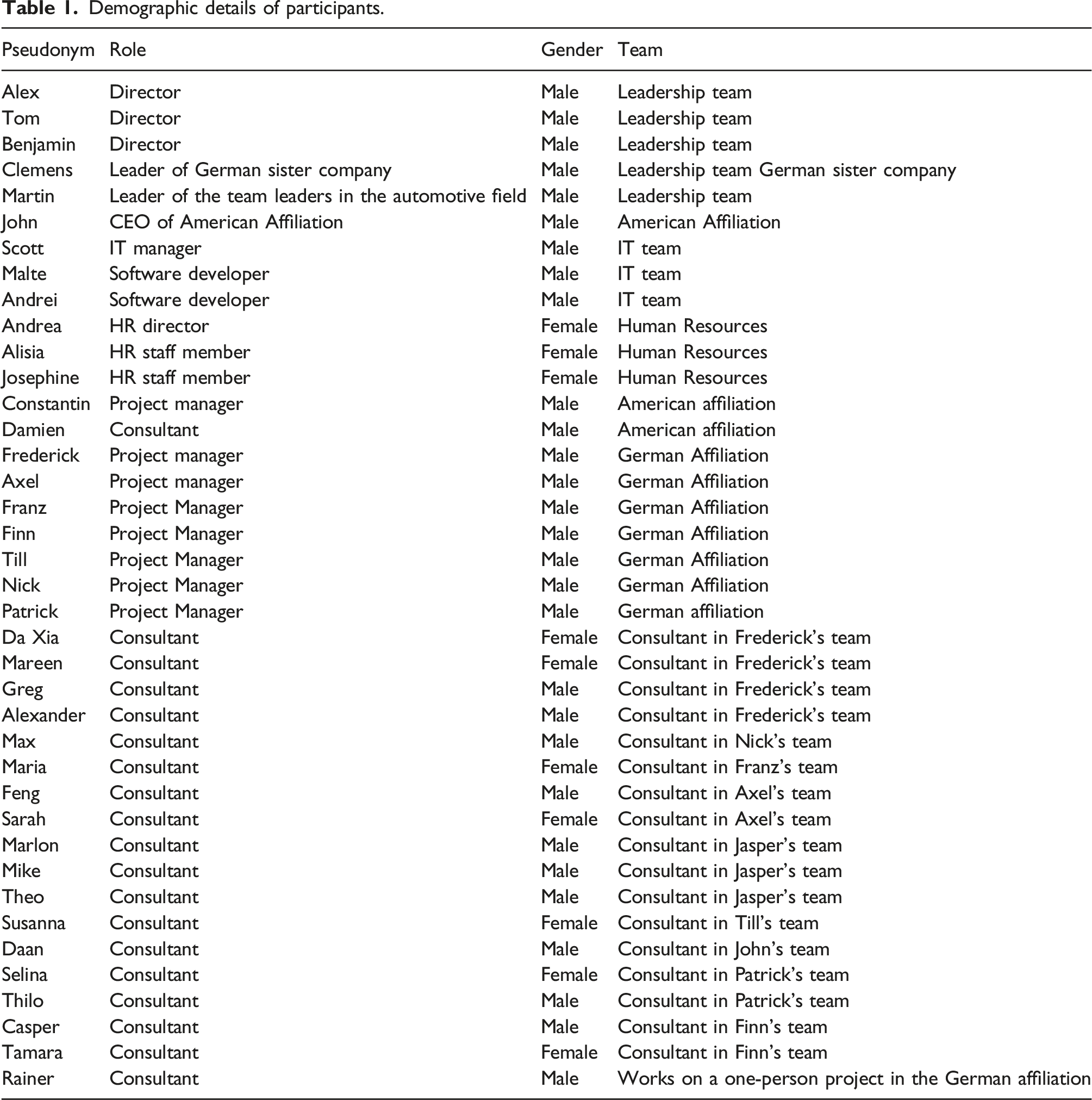
Pseudonym
Role
Gender
Team
Alex
Director
Male
Leadership team
Tom
Director
Male
Leadership team
Benjamin
Director
Male
Leadership team
Clemens
Leader of German sister company
Male
Leadership team German sister company
Martin
Leader of the team leaders in the automotive field
Male
Leadership team
John
CEO of American Affiliation
Male
American Affiliation
Scott
IT manager
Male
IT team
Malte
Software developer
Male
IT team
Andrei
Software developer
Male
IT team
Andrea
HR director
Female
Human Resources
Alisia
HR staff member
Female
Human Resources
Josephine
HR staff member
Female
Human Resources
Constantin
Project manager
Male
American affiliation
Damien
Consultant
Male
American affiliation
Frederick
Project manager
Male
German Affiliation
Axel
Project manager
Male
German Affiliation
Franz
Project Manager
Male
German Affiliation
Finn
Project Manager
Male
German Affiliation
Till
Project Manager
Male
German Affiliation
Nick
Project Manager
Male
German Affiliation
Patrick
Project Manager
Male
German affiliation
Da Xia
Consultant
Female
Consultant in Frederick’s team
Mareen
Consultant
Female
Consultant in Frederick’s team
Greg
Consultant
Male
Consultant in Frederick’s team
Alexander
Consultant
Male
Consultant in Frederick’s team
Max
Consultant
Male
Consultant in Nick’s team
Maria
Consultant
Female
Consultant in Franz’s team
Feng
Consultant
Male
Consultant in Axel’s team
Sarah
Consultant
Female
Consultant in Axel’s team
Marlon
Consultant
Male
Consultant in Jasper’s team
Mike
Consultant
Male
Consultant in Jasper’s team
Theo
Consultant
Male
Consultant in Jasper’s team
Susanna
Consultant
Female
Consultant in Till’s team
Daan
Consultant
Male
Consultant in John’s team
Selina
Consultant
Female
Consultant in Patrick’s team
Thilo
Consultant
Male
Consultant in Patrick’s team
Casper
Consultant
Male
Consultant in Finn’s team
Tamara
Consultant
Female
Consultant in Finn’s team
Rainer
Consultant
Male
Works on a one-person project in the German affiliation
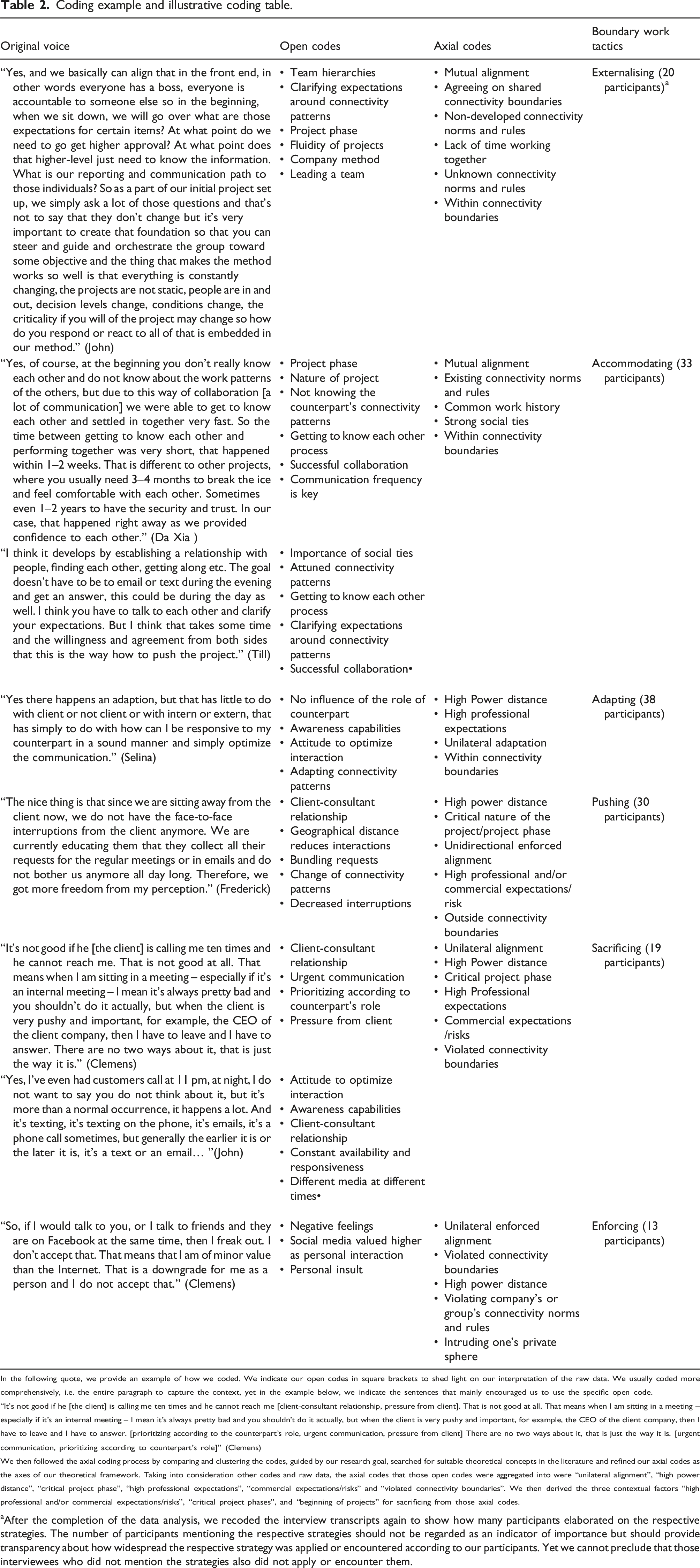
Original voice
Open codes
Axial codes
Boundary work tactics
“Yes, and we basically can align that in the front end, in other words everyone has a boss, everyone is accountable to someone else so in the beginning, when we sit down, we will go over what are those expectations for certain items? At what point do we need to go get higher approval? At what point does that higher-level just need to know the information. What is our reporting and communication path to those individuals? So as a part of our initial project set up, we simply ask a lot of those questions and that’s not to say that they don’t change but it’s very important to create that foundation so that you can steer and guide and orchestrate the group toward some objective and the thing that makes the method works so well is that everything is constantly changing, the projects are not static, people are in and out, decision levels change, conditions change, the criticality if you will of the project may change so how do you respond or react to all of that is embedded in our method.” (John)
• Team hierarchies
• Clarifying expectations around connectivity patterns
• Project phase
• Fluidity of projects
• Company method
• Leading a team• Mutual alignment
• Agreeing on shared connectivity boundaries
• Non-developed connectivity norms and rules
• Lack of time working together
• Unknown connectivity norms and rules
• Within connectivity boundariesExternalising (20 participants)
a
“Yes, of course, at the beginning you don’t really know each other and do not know about the work patterns of the others, but due to this way of collaboration [a lot of communication] we were able to get to know each other and settled in together very fast. So the time between getting to know each other and performing together was very short, that happened within 1–2 weeks. That is different to other projects, where you usually need 3–4 months to break the ice and feel comfortable with each other. Sometimes even 1–2 years to have the security and trust. In our case, that happened right away as we provided confidence to each other.” (Da Xia )
• Project phase
• Nature of project
• Not knowing the counterpart’s connectivity patterns
• Getting to know each other process
• Successful collaboration
• Communication frequency is key• Mutual alignment
• Existing connectivity norms and rules
• Common work history
• Strong social ties
• Within connectivity boundariesAccommodating (33 participants)
“I think it develops by establishing a relationship with people, finding each other, getting along etc. The goal doesn’t have to be to email or text during the evening and get an answer, this could be during the day as well. I think you have to talk to each other and clarify your expectations. But I think that takes some time and the willingness and agreement from both sides that this is the way how to push the project.” (Till)
• Importance of social ties
• Attuned connectivity patterns
• Getting to know each other process
• Clarifying expectations around connectivity patterns
• Successful collaboration•
“Yes there happens an adaption, but that has little to do with client or not client or with intern or extern, that has simply to do with how can I be responsive to my counterpart in a sound manner and simply optimize the communication.” (Selina)
• No influence of the role of counterpart
• Awareness capabilities
• Attitude to optimize interaction
• Adapting connectivity patterns• High Power distance
• High professional expectations
• Unilateral adaptation
• Within connectivity boundariesAdapting (38 participants)
“The nice thing is that since we are sitting away from the client now, we do not have the face-to-face interruptions from the client anymore. We are currently educating them that they collect all their requests for the regular meetings or in emails and do not bother us anymore all day long. Therefore, we got more freedom from my perception.” (Frederick)
• Client-consultant relationship
• Geographical distance reduces interactions
• Bundling requests
• Change of connectivity patterns
• Decreased interruptions• High power distance
• Critical nature of the project/project phase
• Unidirectional enforced alignment
• High professional and/or commercial expectations/risk
• Outside connectivity boundariesPushing (30 participants)
“It’s not good if he [the client] is calling me ten times and he cannot reach me. That is not good at all. That means when I am sitting in a meeting – especially if it’s an internal meeting – I mean it’s always pretty bad and you shouldn’t do it actually, but when the client is very pushy and important, for example, the CEO of the client company, then I have to leave and I have to answer. There are no two ways about it, that is just the way it is.” (Clemens)
• Client-consultant relationship
• Urgent communication
• Prioritizing according to counterpart’s role
• Pressure from client• Unilateral alignment
• High Power distance
• Critical project phase
• High Professional expectations
• Commercial expectations /risks
• Violated connectivity boundariesSacrificing (19 participants)
“Yes, I’ve even had customers call at 11 pm, at night, I do not want to say you do not think about it, but it’s more than a normal occurrence, it happens a lot. And it’s texting, it’s texting on the phone, it’s emails, it’s a phone call sometimes, but generally the earlier it is or the later it is, it’s a text or an email… ”(John)
• Attitude to optimize interaction
• Awareness capabilities
• Client-consultant relationship
• Constant availability and responsiveness
• Different media at different times•
“So, if I would talk to you, or I talk to friends and they are on Facebook at the same time, then I freak out. I don’t accept that. That means that I am of minor value than the Internet. That is a downgrade for me as a person and I do not accept that.” (Clemens)
• Negative feelings
• Social media valued higher as personal interaction
• Personal insult• Unilateral enforced alignment
• Violated connectivity boundaries
• High power distance
• Violating company’s or group’s connectivity norms and rules
• Intruding one’s private sphereEnforcing (13 participants)
