Abstract
While indigenous theorizing in information systems has clear merits, theory borrowing will not, and should not, be eschewed given its appeal and usefulness. In this article, we aim at increasing our understanding of modifying of borrowed theories in IT-rich contexts. We present a framework in which we discuss how two recontextualization approaches of specification and distinction help with increasing the IT-richness of borrowed constructs and relationships. In doing so, we use several illustrative examples from information systems strategy. The framework can be used by researchers as a tool to explore the multitude of ways in which a theory from another discipline can yield the understanding of IT phenomena.
Keywords
Introduction
The role of information systems (IS)-specific theory and its contribution to the state and direction of the IS field remains a topic of extensive debate. A resounding constant within the debate is that IS theory development is essential, yet with little consensus on how this should be achieved (Hong et al., 2014). Indeed, IS is charged by its critics as engaging in habitual theory borrowing from other/allied disciplines at the expense of indigenous theory building; an abundance of middle-range theories at the expense of generalizable, grand theories, and persistent undertheorizing of the IT artifact (Grover and Lyytinen, 2015; Hassan and Lowry, 2015; Orlikowski and Iacono, 2001). In addition, the heavy reliance on theories not founded on IT-related constructs is deemed “distracting” (Benbasat and Zmud, 2003: 192). Accordingly, a strong and active stream of research encourages developing indigenous theories (Grover and Lyytinen, 2015) that are unlikely to be products of theory borrowing from other fields. Such theories will be “above and beyond the theories we import from other fields” (Markus and Saunders, 2007: iv).
While the merits of such theorizing are apparent, we argue that theory borrowing in IS will not, and should not, cease completely, particularly due to its appeal (Grover and Lyytinen, 2015) and potential usefulness (e.g. see Weber, 2003: x). Therefore, in addition to the searches for indigenous IS theories, attention to the nature and quality of borrowing is also crucial.
We build on the premise that theory borrowing is legitimate if constructs are owned and if borrowed theories are adapted appropriately to our distinctive subject matter (Hassan, 2011; Markus and Saunders, 2007). Drawing from the studies within (Hong et al., 2014) and outside IS (Oswick et al., 2011), such borrowing can be characterized as IS recontextualization. In demarcating our subject matter, we note the debates on whether and what constitutes the field’s intellectual core (King and Lyytinen, 2006; Whinston and Geng, 2004). While acknowledging critical commentaries (e.g. Galliers, 2003, 2006), in this article we consider what IS recontextualization would look like in cases where the borrowed materials are not silent about the IT artifact.
In establishing a foundation for our study, we note that three key modes of theory borrowing in IS have been articulated: instantiating, extending, and modifying (Grover and Lyytinen, 2015). By definition, instantiating is unlikely to provide a basis for offering much IS-related theoretical insights as theory is foreign to IS and the recontextualization efforts are only minor. Extending encourages theory development to go beyond the borrowed theory by adding new constructs and relationships that are IS-related. It is in modifying, where “The model modifies constructs, configurations, and/or logic from the borrowed theory to the IS context” (Grover and Lyytinen, 2015: 278), that IT-rich recontextualization becomes key.
In pursuing our aim, we build on the literature on theorizing the IT artifact (Benbasat and Zmud, 2003; Grover and Lyytinen, 2015; Orlikowski and Iacono, 2001; Straub, 2012), develop a framework of IT-rich recontextualized modifying of borrowed theories, and demonstrate this framework within the domain of IS strategy. The first dimension of the framework recognizes two approaches to IT-rich recontextualization: specification and distinction. Specification considers how the resulting theory can confer rich insights concerning the IT artifact, enabling non-nominal views of IT (Orlikowski and Iacono, 2001). Distinction involves how to make the borrowed instance uniquely different from other possible IS instances (internal distinction) and non-IS instances (external distinction) of the same borrowed theory. The second dimension of the framework recognizes that recontextualization can occur across two key elements of the borrowed theory: 1 constructs and relationships (Bacharach, 1989). Construct recontextualization is concerned with relabeling, redefining, redimensionalizing, and exemplifying constructs to offer rich insights about the IT artifact. Relationship recontextualization is chiefly about explaining theoretical mechanisms (namely, causal links, conceptual assumptions, and boundary assumptions) for the influence of one construct on another by explicitly referring to particular aspects of the IT artifact.
To illustrate the adoption of these IT-rich recontextualization approaches, we use several examples chiefly from IS strategy (ISS) research. Our focus on ISS has several motivations: there is much discourse around IS as a conglomerate of subtopics and more in-depth discussions of each subtopic can provide a rich understanding that can guide future research. ISS has been seen to be a top concern of Chief Information Officers (CIOs) over the decades (e.g. Luftman et al., 2015), and continues as a dominant concern with such ISS subtopics as alignment of IT with the business remaining a top concern for over 10 years (Kappelman et al., 2019). It is a particularly important topic in the current digital era in which many businesses are becoming increasingly digitally enabled and transformed (Barley et al., 2017; Davison and Ou, 2017; Vial, 2019). Moreover, ISS is generally recognized as adopting a nominal view to the IT artifact (see Grover and Lyytinen, 2015: 279; also, Orlikowski and Iacono, 2001: 128), so we seek examples of the capturing of IT in the ISS research.
Our contribution is twofold. First, we contribute to studies on embedding IT in IS research (e.g. Akhlaghpour et al., 2013; Grover and Lyytinen, 2015; Orlikowski and Iacono, 2001; Straub, 2012) by further clarifying and formalizing IT-rich recontextualized approaches of specification and distinction. Second, we contribute to ISS research by exploring several specific examples of how the IT artifact is embedded in it, demonstrating that IT is not always nominal in this domain. Overall, we add to the debate on theory borrowing within IS (Truex et al., 2006) and provide some further directions for moving away from nominal views of IT in ISS.
IT-rich recontextualization of borrowed theories—a framework
When theories from outside a reference discipline are borrowed, they are subject to recontextualization. As Oswick et al. (2011) put it, “Effectively, recontextualization involves a process of repackaging, refining, and repositioning a discourse (or text) that circulates in a particular community for consumption within another community” (p. 323). Researchers who have studied similar borrowing modes, including contextualization (Hong et al., 2014), domestication (Oswick et al. 2011), and modifying (Grover and Lyytinen, 2015), consider that some core constructs and relationships might be added or removed from the borrowed theory. What we mean by IT-rich recontextualization is much narrower, however. Here, we delve into how unique IS insights can be infused in the constructs and relationships of the borrowed theory.
To increase our understanding of IT-rich recontextualized modifying of borrowed theories, we draw from past research on developing IS theories (Benbasat and Zmud, 2003; Grover and Lyytinen, 2015; Orlikowski and Iacono, 2001; Straub, 2012) to develop a 2 × 2 framework (Table 1). The first dimension, recontextualization approach, distinguishes specification and distinction. The second dimension, borrowed theory element, considers that specification and distinction can be applied to the borrowing of both the key components of a theory—constructs and relationships (Bacharach, 1989). Given our speculation that, when borrowing theories in IS, the IT artifact often remains nominal until the empirical part of a paper, this framework excludes recontextualized operationalizations to emphasize recontextualized theorizing. Below, we explain each dimension of the framework in detail.
A framework of IT-rich recontextualized modifying of borrowed theories.
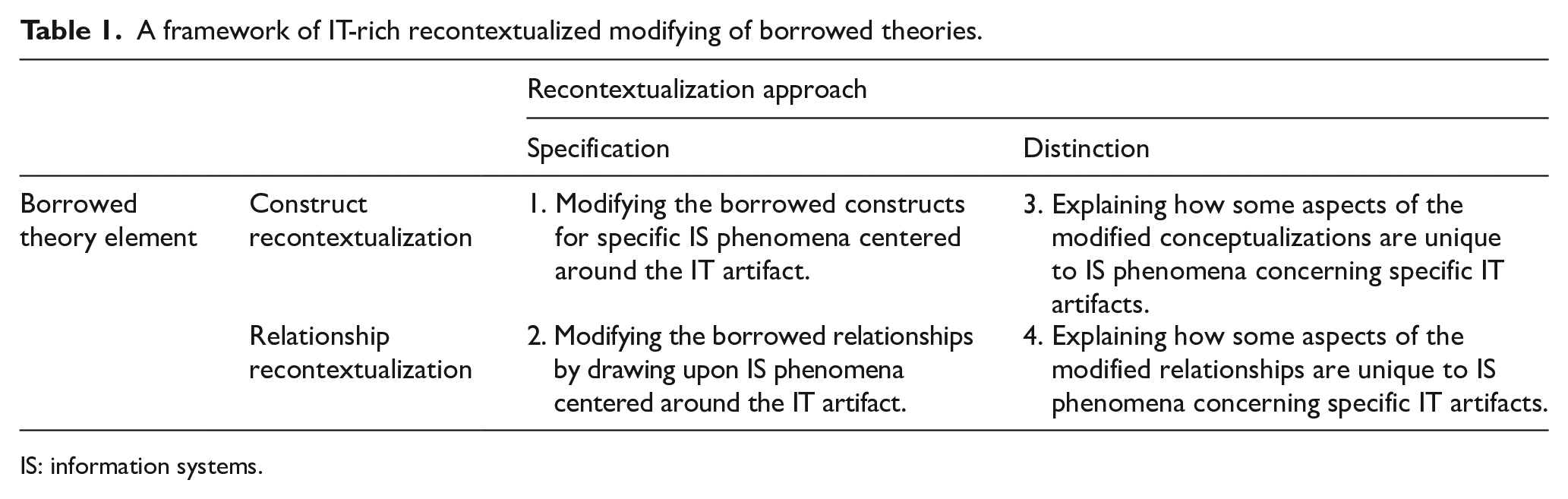
IS: information systems.
Specification
Specification refers to the efforts made to describe the IT artifact per se or that is embedded in the surrounding IS phenomena. Specification recognizes that, were the IT artifact absent in a theory, the study might be subject to the “error of exclusion” (Benbasat and Zmud, 2003: 189). From this perspective, a study might be criticized for having “no reference to any specific technology” (Orlikowski and Iacono, 2001: 128). Specification is therefore a necessary (but insufficient) condition for adopting the non-nominal views of IT (e.g. the ensemble view). While such specificity is recognized as a key characteristic of native IS theories (Straub, 2012), we explore specification in theory borrowing.
By considering the IT artifacts as technical objects (Markus and Silver, 2008: 625), we recognize six ways in which the IT artifact could be specified. Specifying the taxonomic nature of the IT artifact adopts a pluralistic view of the IT artifact (recognized as the IS artifact—Lowry et al., 2017) and explains how an IT artifact belongs to one taxon or a combination of taxa. When an IT artifact is labeled accordingly, attention is shaped to a particular (although often vaguely defined) subset of artifacts. Specifying the IT artifact as a specific IS product distinguishes two related but differing forms of technical objects: IT and IS (in terms of products not the research disciplines—Hassan, 2006). While IT can be any digital technology (e.g. the Internet), IS is a particular category of IT used by organizations to represent their business processes according to Weber (2003). Specifying key configurations within and across IT artifacts regards the IT artifact as an assemblage of key subcomponents. Orlikowski and Iacono (2001) explain that, “IT artifacts are usually made up of a multiplicity of often fragile and fragmentary components, whose interconnections are often partial and provisional and which require bridging, integration and articulation in order for them to work together” (p. 131). Furthermore, key configuration of multiple IT artifacts can be specified as a system of systems (e.g. in specifying enterprise architecture). Specifying holistic attributes of the IT artifact focuses on describing an IT artifact using some of its attributes or that of its key subcomponents. Specifying features/functionalities views the IT artifact as a collection of various interrelated features/functionalities 2 that, individually or taken together, could enable or support users to perform certain tasks. Decomposing an IT artifact into features/functionalities allows researchers to avoid having a black box view of technology (Benbasat and Zmud, 2003; Jasperson et al., 2005; Orlikowski and Iacono, 2001). The purposeful nonspecificity of the IT artifact recognizes that when research claims are generalizable to all IT artifacts, researchers might opt to justify the lack of IT specificity.
Table 2 provides several illustrative examples from the IS strategy context.
Specification approaches: illustrative examples from IS strategy research.
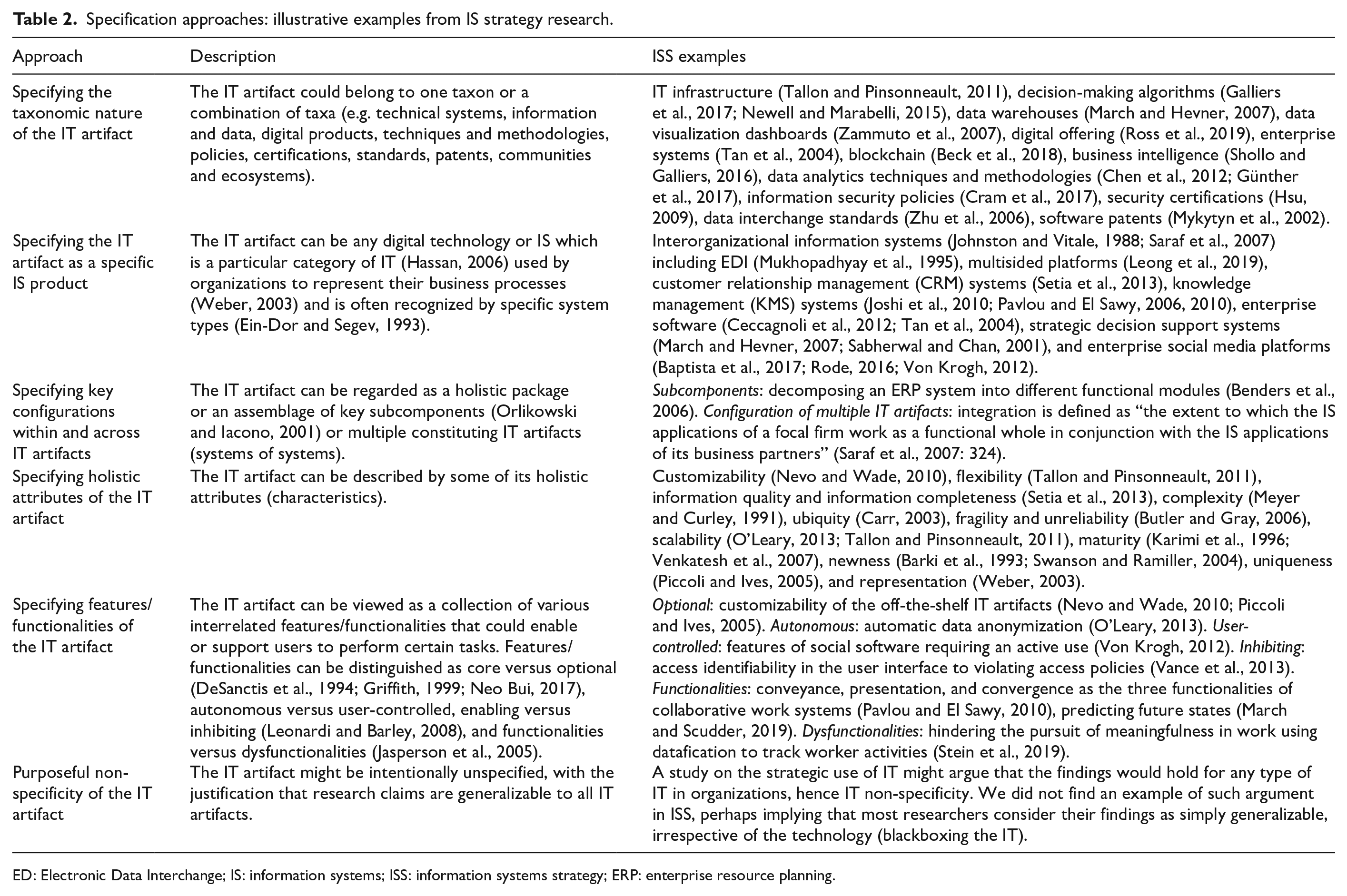
ED: Electronic Data Interchange; IS: information systems; ISS: information systems strategy; ERP: enterprise resource planning.
Distinction
Distinction refers to efforts dedicated to delineating the various instances of borrowed constructs and relationships by highlighting what is unique to the particular IT artifact (or its surrounding IS phenomena) under study. Distinction leverages specification, for example, in order to differentiate features and functionalities of two IT artifacts. We discuss two approaches of internal and external distinction and their subcategories.
Internal distinction is within IS and builds on the idea that “Information technologies differ with respect to their intrinsic characteristics” (Piccoli and Ives, 2005: 760). To make an internal distinction, specification can be used to capture the variations between different ITs rather than adopting a homogeneous view of IT. Internal distinction can also be used to theorize, for example, varying perceptions, abilities, and actions about similar IT artifacts.
External distinction can be made between the IS and non-IS versions of the borrowed theories, recognizing that “we should look to how uniquely the theory base applies to IS” (Straub, 2012: v). Giving the example of the replaceability of “IS” with “marketing” in some IS strategy theories, Orlikowski and Iacono (2001) suggest that the IS and non-IS distinction made in a theory must be evident. We identify four external distinction approaches. Distinguishing IT from non-IT instances of the same theories involves explaining what is unique to an IS take on the borrowed theory. Distinguishing IT from non-IT technologies explains how the way a theory is borrowed to examine an IT artifact can be distinguished from such borrowing for a non-IT. Recognizing the similarity (hence the concurrent value added) to non-IT technologies, in contrast to the other external distinction strategies, involves explicitly acknowledging and explaining the generalizability of the modification of a non-technology-related theory to IS to the understanding of non-IT technologies (e.g. manufacturing technologies). Distinguishing the IS angle from other angles for the same IT artifact recognizes that various cognate disciplines, such as computer science, have a vested interest in the IT artifact (Hassan and Will, 2006). The last approach is purposeful non-distinction, which pairs with the purposeful non-specificity approach explained above. Table 3 summarizes the above and provides several examples from the IS strategy context.
Distinction: illustrative examples from IS strategy research.
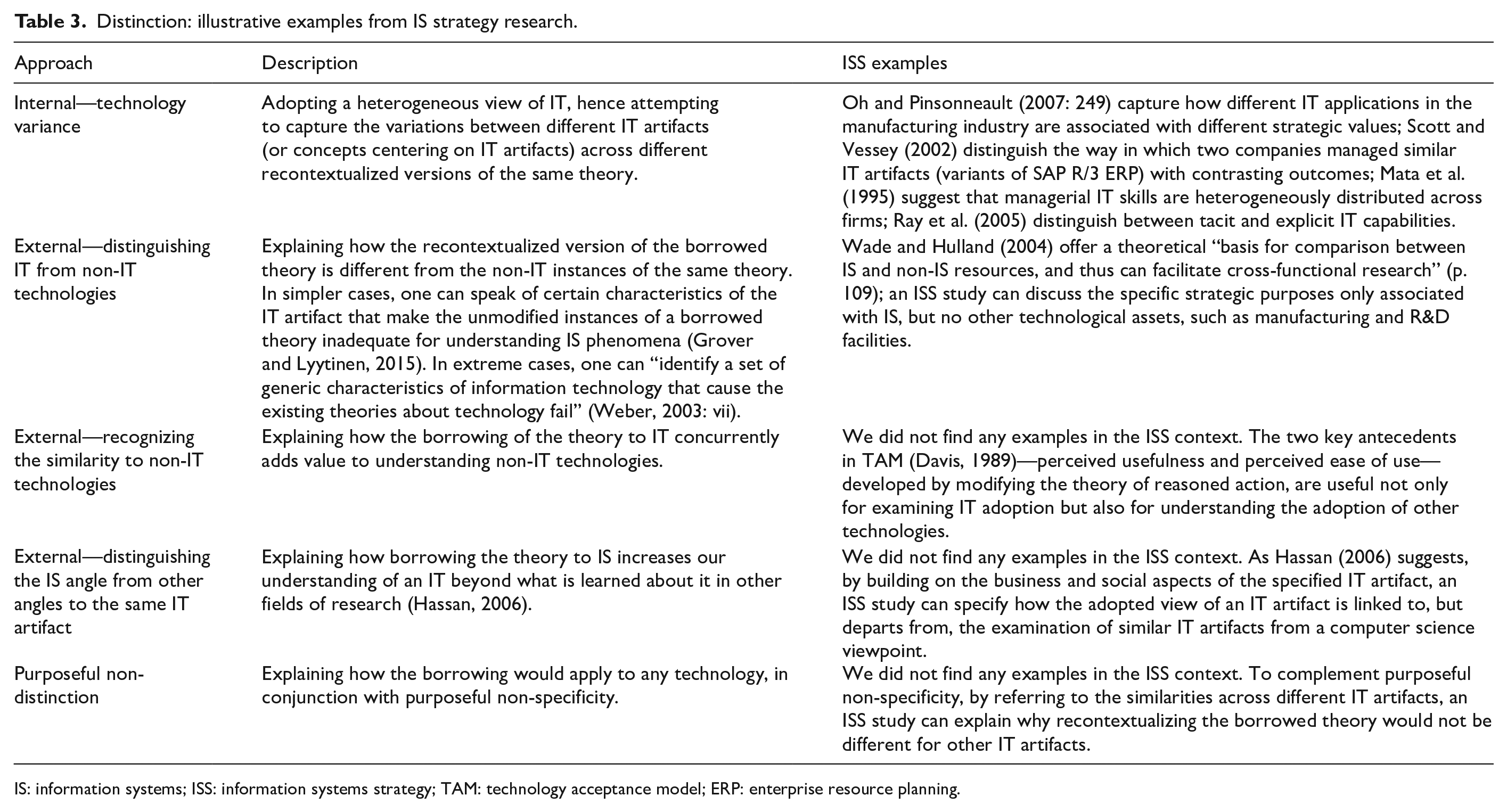
IS: information systems; ISS: information systems strategy; TAM: technology acceptance model; ERP: enterprise resource planning.
Having discussed the specification and distinction approaches, we next take a closer look at how these approaches can be applied in recontextualizing constructs and relationships.
Construct recontextualization using specification and distinction
Constructs refer to “conceptual abstractions of phenomena that cannot be directly observed” (Suddaby, 2010: 346). To recontextualize borrowed constructs for use in an IT-rich context, one should “adapt them to reflect a unique IT or IS component” (Benbasat and Zmud, 2003) with a view to “clarifying the IS nuances involved” (p. 193). Construct recontextualization considers that the specification of an IT artifact can appear in four complementary forms: construct labels, definitions, dimensions, and exemplifications. Recontextualizing construct labels involves revising the labels of borrowed constructs with the specified IT artifact in mind.
A good practice in theorizing is ensuring construct clarity according to Barki (2008) and Suddaby (2010), especially by offering formal definitions (Wacker, 2004). Thus, recontextualizing construct definitions concerns modifying construct definitions by making explicit reference to the specified IT artifact (per se or embedded in surrounding IS phenomena). General rules for offering a formal conceptual definition (Wacker, 2004) apply. A multidimensional construct can be modeled in different ways, including the latent (higher order) and aggregate (multiplicative or additive) approaches (Law et al., 1998). Thus, recontextualizing construct dimensions of a borrowed multidimensional construct can involve adding or removing dimensions. Furthermore, we note that exemplification via providing concrete examples is vital for developing theoretical ideas (Jaccard and Jacoby, 2009). Accordingly, recontextualization by exemplification complements recontextualized construct labels and definitions and provides a further opportunity for specification. Examples can also be used to make a distinction between various takes on the same construct.
Table 4 summarizes the above and provides several examples from the IS strategy context.
Construct recontextualization using specification and distinction approaches: examples from IS strategy research.
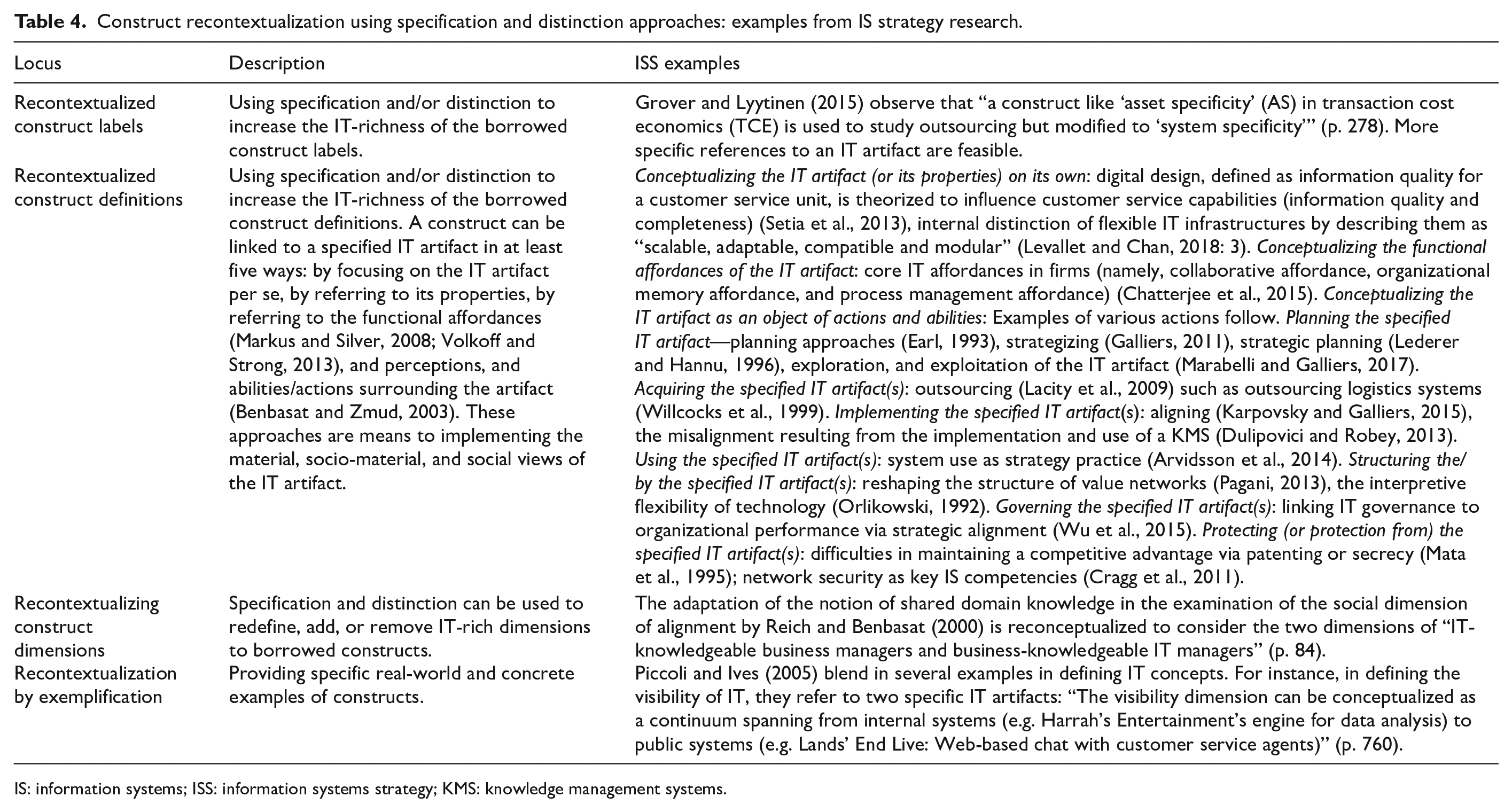
IS: information systems; ISS: information systems strategy; KMS: knowledge management systems.
Relationship recontextualization using specification and distinction
From a variance view to theory, relationships are construed as propositions at more generalizable (abstract) levels and hypotheses at less generalizable (concrete) levels (Bacharach, 1989). Relationships refer to the explanations of what constructs are related, as well as how and why they are related (Whetten, 1989). We suggest that borrowed relationships can be recontextualized by applying specification and distinction to four elements of a relationship: constructs in various structural positions, causal links, assumptions, and boundaries.
Recontextualizing the constructs in various structural positions of a theory considers different roles that constructs play in a proposition, namely, being independent, dependent, and path-modifying variables and explains the implications of making these IT-rich. For example, exercising distinction to a path-modifying variable can illustrate how a relationship would be different for different IT artifacts. While the views on causality in IS research are several, our focus on recontextualizing causal links stems from our causal ontology of mechanisms: the “real physical, psychological, and/or social processes that connect inputs and outputs under certain conditions” (Markus and Rowe, 2018: 1263). For brevity, we particularly focus on a subset of these processes: causal links as a common practice in specifying such process. We view causal links as hidden mediators and consider them subject to IT recontextualization. Conceptual assumptions are made to explain why there is a relationship between two constructs (Whetten, 2002). For example, when proposing that A influences B, including a causal link (C) usually means that two theoretical assumptions (that A impacts C, and C influences B) are described but are taken-for-granted as being true. When theories are borrowed without being challenged, their underlying assumptions are inherited (Alvesson and Sandberg, 2011). The borrowed assumptions can be relaxed, denied, and revised, however (Rivard, 2014). Boundary assumptions involve the assumptions about values, time, and space within which a theory works as specified (Bacharach, 1989). In recontextualizing such assumptions, one can build on the nature of the specified IT artifact, suggesting why a particular causal link does not hold or works differently in the IT context.
Table 5 summarizes the above and provides several examples from the IS strategy context.
Relationships recontextualization using specification and distinction.
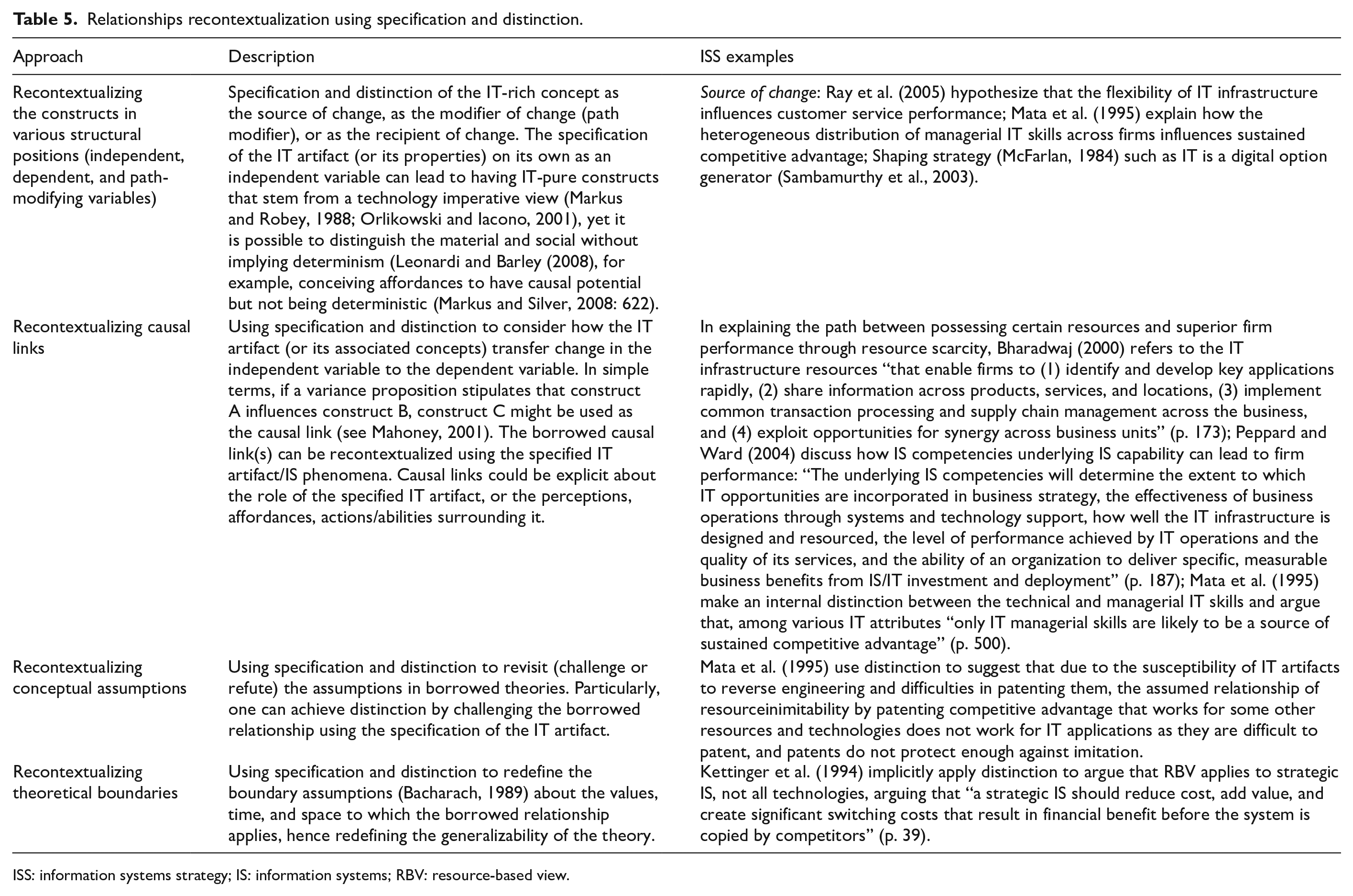
ISS: information systems strategy; IS: information systems; RBV: resource-based view.
In conclusion
In this article, we build on the literature that theorizes the IT artifact and develop a 2 × 2 framework for IT-rich recontextualized modification of borrowed theories in IS. The framework considers implementing specification and distinction to make the borrowed constructs and relationships IT-rich. It provides some pathways of embedding more IT in IS research, with particular reference to examples from the IS strategy literature.
We make two contributions. First, through formalizing specification and distinction, we provide a deeper appreciation of embedding the IT artifact in borrowed theories in IS. This has important implications for how IS scholars adapt theories from other disciplines. It renders visible a wide range of options available to IS researchers. The addition of elements within specification and distinction provides a language to describe and how borrowed theory is constructed. Indeed, enabling researchers to “own” borrowed theory through specification or distinction unlocks—and stratifies—different ways to develop theory.
The framework enables us to appreciate how some recontextualized theories are “IT-light,” while others are “IT-rich.” IT-rich studies are specific about unique aspects of IT/IS phenomena and demonstrate a deep engagement with the IT artifact (Orlikowski and Iacono, 2001). For example, a study on IT investment that focuses only on a general dollar amount (the “proxy-capital” view in Orlikowski and Iacono, 2001) is IT-light. Yet it can be more IT-rich if, rather than just reporting an aggregated value, it uses specification and examines the value invested in various system types such as security and cloud systems, corresponding to the top concerns of IT leaders (Kappelman et al., 2019).
Furthermore, we suggest that, whether a theory is instantiated, modified, or extended (Grover and Lyytinen, 2015) or provides a light or rich understanding of the IT artifact, are separate (although interrelated) matters. On the one hand, even an extension of a borrowed theory might not be IT-rich as it might extend with constructs remote from the IT artifact and its surrounding phenomena. The extension is an IT-rich contribution if it enriches our understanding of IT/IS phenomena; otherwise, the contribution is likely to have significant overlaps with other disciplines. On the other hand, even instantiation can be IT-rich. The true difference between being IT-rich or IT-light is in implementation (i.e. the extent to which construct conceptualizations and theoretical assumptions are enriched with IT-related phenomena).
It is noteworthy that, as specification involves a tradeoff between too narrow and too broad IT artifact descriptions, we acknowledge the specificity dilemma. Like any other system, which is composed of subsystems that can be decomposed into lower level subsystems, IT artifacts (and their attributes) can be decomposed into more detailed elements—an issue referred to as the repeating decomposition problem (DeSanctis and Poole, 1994; Markus and Silver, 2008). The specificity dilemma is also visible in the argument that while IT is usually unspecified in IS studies (Orlikowski and Iacono, 2001), when it is specified, it often provides “overly narrow views of technology” (p. 122). The specificity dilemma escalates into challenges in specifying the nomological network surrounding the IT artifact. In the ISS context, for example, Wade and Hulland (2004) explain the challenges in defining IT resources: “Broadly defined resources have the advantage of being readily generalized beyond a specific research situation but can lose their explanatory value when applied to overly narrow or specific situations” (p. 128). Yet, “Narrow definitions help to fine-tune our understanding of specific resources and their effect on competitive position and performance in given settings” (Wade and Hulland, 2004: 129). While acknowledging this dilemma, our view is that it should not stop all research from attempting to be specific about the IT artifact being studied. Specification will enable researchers to demonstrate which aspects are salient, and without it, “we have no language for making clear distinctions between types of constraints and affordances” (Leonardi and Barley, 2008: 166).
Our second contribution is to ISS research and this is achieved by exploring several specific examples of how the IT artifact has been captured from a non-nominal view. In doing so, while Orlikowski and Iacono (2001) (similarly Akhlaghpour et al., 2013; Grover and Lyytinen, 2015) were looking for how researchers have viewed the IT artifact, we have looked for “spelled-out” specifications of the IT artifact that clearly demonstrate how researchers have captured its material nature when linking it to social phenomena. Recognizing IT-light versus IT-rich borrowing enables us to note that, even when the same theories are borrowed, the level of IT-rich recontextualization can vary significantly. For example, we note that the same RBV theory has been borrowed in several different ways. In terms of constructs, asset capabilities and competencies have been specified on a range of nominal IT to attributes to specific systems, and distinction has been used for assets by mentioning six characteristics. Future studies could explore the variance in IT recontextualization by various studies that borrow the same theories.
Our study has some limitations that can be addressed by future research. First, in defining specificity, other ways of capturing the IT artifact, for example, based on context (e.g. manufacturing, healthcare), organizational level of use (e.g. interorganizational networks), or intended/realized user groups can be explored. Also, richer specifications can be provided by combining multiple approaches (e.g. by referring to specific features/functionalities of a particular system type). Second, while we attempted to provide examples of each approach from the IS strategy context, further systematic literature review is required to ensure certain approaches (such as distinction) are indeed less frequently used. Furthermore, we did not identify many applications of external distinction. This provides a partial explanation to the question of why IS struggles to position itself as a distinct field. As distinction plays a key role in highlighting how the contributions of a study are IT-related, wider and more explicit applications of that are warranted. Through owning borrowed theories, the IS field can reinforce its identity by addressing the (false) dichotomy of pure borrowing versus indigenous theorizing.
Footnotes
Acknowledgements
The authors would like to thank Leslie Willcocks, Lynne Markus, and Nik Hassan for their constructive comments on earlier versions of this paper.
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) received no financial support for the research, authorship, and/or publication of this article.
