Abstract
Security of premises, assets and personnel form an essential requirement for commercial organisations. Lack of security impacts beyond the bottom-line, signalling a joint failure of organisation’s leadership and public governance, attracting more crime. The overloaded government’s police force can hardly dedicate resources to specific businesses. Private security firms, while offering a way out, create legal and socio-political challenges when, in line of duty, they resort to the use of firearms. In this article we research a manufacturing firm whose different security paradigm offers a rare insight into the hitherto relatively unexplored world of industrial security in an Indian context.
Executive Summary
Premises security is essential for organizations to function efficiently and effectively. The sanctity of space and its associated perimeter not only signals a boundary for outsiders but also serves as a second home for organizational members. These members cannot meet organizational requirements if they are constantly on guard, protecting themselves and the organization’s property. However, the gradual encroachment of industrial space by squatters, while reflecting uneven economic development, presents significant security challenges, as some inhabitants of informal settlements find pilfering and other petty crimes financially rewarding. The dominant security strategy typically involves armed guards, whose presence may act as a deterrent. However, the death of an intruder or trespasser due to a guard using his firearm has far-reaching implications due to prevailing legal doctrines and stakeholder dynamics. In India, the legal system treats death as a serious matter, out of proportion to the crime of theft, and the socio-political environment echoes this perspective. Such deaths often lead to collective protests from citizens, often in the form of a dharna or a gherao, which not only disrupts the firm’s operations but also poses a challenge to legal and administrative authorities and management. Dispersing the dharna and preventing it from escalating into a violent mob typically requires the management to negotiate compensation with the aggrieved family, alongside a commitment to legal authorities to impose strict restrictions on the use of firearms. The erosion of deterrence following such negotiations renders security guards ineffective. Their response to trespassing and pilfering is reduced to physical confrontation, attempting to evict individuals, which places guards at risk when faced with armed intruders. Our case study illustrates how an organization restored deterrence, and thus the sanctity of its perimeter, by incorporating attack dogs into its security strategy.
Security forms the foundation of modern economic society by ensuring unhindered economic transactions, business processes and customers’ ability to derive the benefit of ownership of assets. Private security is a necessity in many geopolitical contexts due to overwhelmed public security apparatus (Ketchell, 2017; OSACa, 2020), inefficiencies, corruption (e.g., Clark, 2018; OSAC, 2020a, 2020b) or a heightened feeling of insecurity (e.g., Loader, 1997; McDowall & Loftin, 1983). Increased economic activity, often accompanied by inequitable prosperity, attracts criminal activity (Bergholt & Lujala, 2012; Hemley & McPheters, 1975; Hobbs et al., 2005; Moser, 2004; Østby, 2016), increasing demand for security. The iron and steel industry in the United States, with its violent workers’ unions (Spitzer & Scull, 1977) and organized crime, is a significant example. Stagnant economies marked by income inequalities often ferment tendencies to engage in crime, often perceived by perpetrators as justified, given their deprived economic status. The increased demand for security, along with distinctive provisions for businesses and high-net-worth individuals, can hardly be met by public legal agencies (Blau & Blau, 1982; Ouimet, 2012). The proliferation of private security and the outsourcing of security, globally, as well as in Indian organizations (FICCI, 2018) is proof of organizations turning towards private security for their needs.
What strategies do private individuals and businesses adopt? The most common measures are high walls and security guards. Drones, CCTVs and remote-operated gates (Lee & Kim, 2017; Srivastava et al., 2017; Tan & Luo, 2018; Welsh et al., 2019) have brought sophistication to primarily an infrastructure-oriented-strategy aimed at preventing unauthorized access to premises or business assets. While the advent of robots in intruder-detection promises to be another evolution in technology-based security, the abilities in simulated tests reveal a long path to be travelled before the robots can substitute for human guards, especially in handling exceptions (e.g., Everett & Gage, 1999).
Despite the changes in technology, human guards have remained indispensable in the overall scheme of things. Humans bring to the security strategy their perceptual capabilities in analysing the similarities and variations in an environment and the ability to decide both the applications of general rules and the exceptions, responding to specific demands of the situation.
What are the operating procedures in most situations? Faced with typical non-violent threats, security guards’ initial responses are limited to verbal warnings, physical deterrence and non-lethal physical aggression (Button, 2003). Acknowledgement of these initial mild security tactics by criminals who choose to ‘delay, divert, or forgo’ (Greer & Bartholomew, 1982) implies the existence of psychological deterrence. Ineffectiveness of these tactics, or increased aggression by perpetrators, necessitates severe, or in certain cases, lethal tactics (Anthony, 2004) to inflict increased ‘punitiveness’ (Cavadino & Dignan, 2006; Singh, 2005).
While these lethal tactics (Anthony, 2004) achieve the objective of ensuring security, the resultant fatalities bring up debates on security governance and call for security agencies to develop non-fatal responses towards transgressors (Stenson, 2005). The subject is further complicated due to varied socio-political contexts, with divergent legal and political attitudes towards the right of self-defence (Yeo, 2000).
In this article, we present a case study of an Indian that has witnessed two contrasting security paradigms with different results. The article first presents the literature on security. Though the existing literature is dominated by research in the Western context, it updates us with the relevant debates in the field and its theoretical frameworks. Then we outline the research design and our analytical approach. We structure our analysis around the concept of psychological deterrence examined from the Bourdieusian perspective, using the concepts of habitus and practice as analytical concepts (Bourdieu, 1977, 1998) to understand how security guards perceive and live their worldviews and take decisions. Finally, we integrate the findings with the previous literature and discuss implications for business leaders and researchers.
LITERATURE REVIEW
Psychological deterrence (Bodnar, 1990; Tiffany & Ketchel, 1979), signifying a criminal’s sense of the situation as ‘being threatening, difficult, unfavourable or not right’, represents one of the important concepts in security. Shaped by the history of offensive or defensive practices as part of security strategy, psychological deterrence, we argue, forms a critical factor in defining the security guards’ habitus (Bourdieu, 1977; Reay, 2004), predisposing them to either passive acquiescence of security violations or proactively challenge the perpetrators.
Contrasted with an efficient judiciary with a distinct bias towards maintaining the constitutional right of citizens towards gun ownership and the exercise of their right to self-defence in the United States, Indian organizations and citizens are faced with a judicial system where 3.7 million cases have been pending for over ten years in Indian High Courts (Krishnan, 2020). The law of the land, including the de facto departures, influences both the practice and the habitus (Bourdieu, 1977, 1998) for the security agencies. ‘Nothing is an offence which is done in the exercise of the right of private defence’, as articulated in section 96 of the Indian Penal Code, might seem in alignment with the conservative ideology of the West, particularly that of the United States. For an organization, or an individual security guard employed in a non-governmental entity, the challenges of negotiating an overloaded legal system problematizes judicial ratification of the use of firearms.
Apart from being vulnerable to verbal and physical abuse (Button, 2003), guards are constrained by limits of human intelligence, staff turnover (Zedner, 2006), corruption (Sykes, 1956; Ungar, 2013) and fear of legal penalties, all of which are not overcome by an increase in numbers (e.g., Kleck & Barnes, 2014). The doctrine of reasonable force, typically defined as the use of force as necessary to protect oneself or one’s property, offers no guidance to the person on the field when faced with an unknown perpetrator. Theories of rational decision-making ignore potential threats, incomplete information, and the limited window for action by security guards (Miethe, 1995). Obligated to work within the constraints of the prevailing discourse, the ethical and human-rights dilemmas (Beckley, 2018) conflict with their need for self-protection (e.g., Giblin, 2008), leading to unfortunate consequences for guards and bystanders.
Our discussion recognizes the challenges of the socio-political context and the role of government legal agencies which are constrained in their action choices yet held responsible for controlling crime. The challenges faced by private security firms are greater than those faced by government agencies, which have a modicum of legal protection by virtue of being part of the government. The dominant socio-political environment and the legal apparatus present the habitus for security guards’ practices, the success of which in the form of a successful guardianship determines their motivation and self-efficacy (Reynald, 2010), in turn revising the habitus in a dynamic fashion.
In the remaining part of this article, we present our case-based research focusing on an Indian organization which transitioned from the mainstream security paradigm, that is, based on armed security guards, supported by technology, to an attack dog–based security paradigm.
RESEARCH METHOD
With its inherent ability to explore complex phenomena and underlying relationships, the case study method was the logical choice to explore this intrinsically interesting case (Stake, 1995). Guided by the proprietor of the dog agency, informants willing to discuss were contacted. The search for informants was not a publicized one in the industrial area, to avoid potential hindrances to the study, as well as to avoid any potential repercussions on the participants. The anonymity of informants was further ensured due to the existence of multiple cement plants, numbering approximately 51, in the eastern part of the country.
Data were gathered over a three-month period involving multiple discussions with informants. Each discussion ranged from 40 to 90 minutes. The discussions, carried out in a semi-structured format, were guided to obtain a chronology of the events, and decisions as taken by different stakeholders.
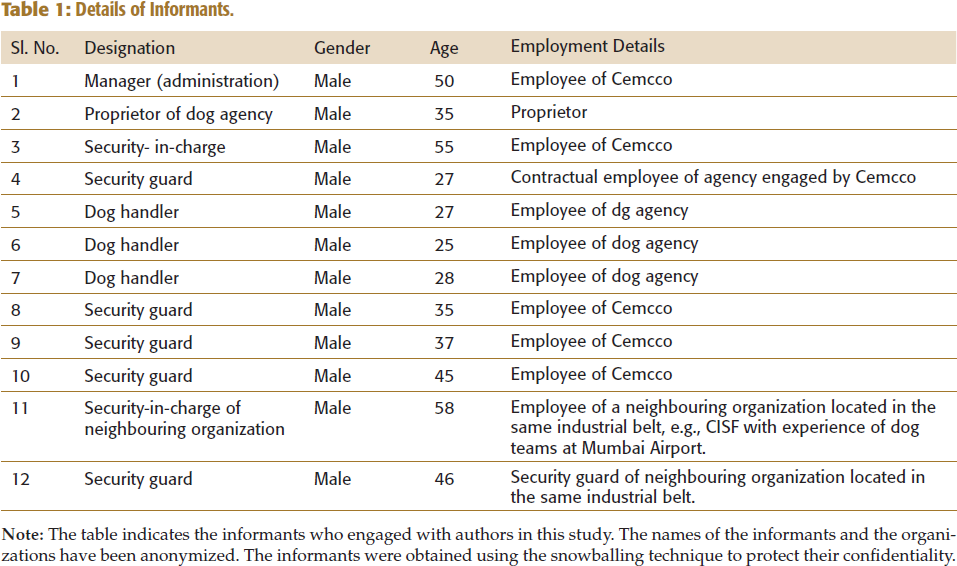
The informant pool for this study is detailed in Table 1. The limited informant pool signifies the limited number of people who were aware of the chronology of events, and the decisions taken by different stakeholders. We found that, given its sensitive nature, organizational security decisions hardly involved the majority of the employees. Avoiding employees who were involved peripherally and restricting our informant pool to those who were intimately involved, we avoided getting entangled in a Roshomonian conundrum. The informant pool included security staff (security-in-charge and a security guard) of a neighbouring organization located in the same industrial belt. This allowed us to understand and validate the socio-political environmental factors and challenges.
Details of Informants.
The small informant pool is an evident limitation of our study. Contrasted to a common social phenomenon, which by its very nature would engender multiple respondents, our case study is more of Yin’s ‘revelatory case’ (2003, p. 43), providing an opportunity to study a rarely investigated topic. Given the nature of the case, we stressed on achieving data saturation (Francis et al., 2010; Guest et al., 2006) from our limited pool of informants.
ANALYTICAL APPROACH
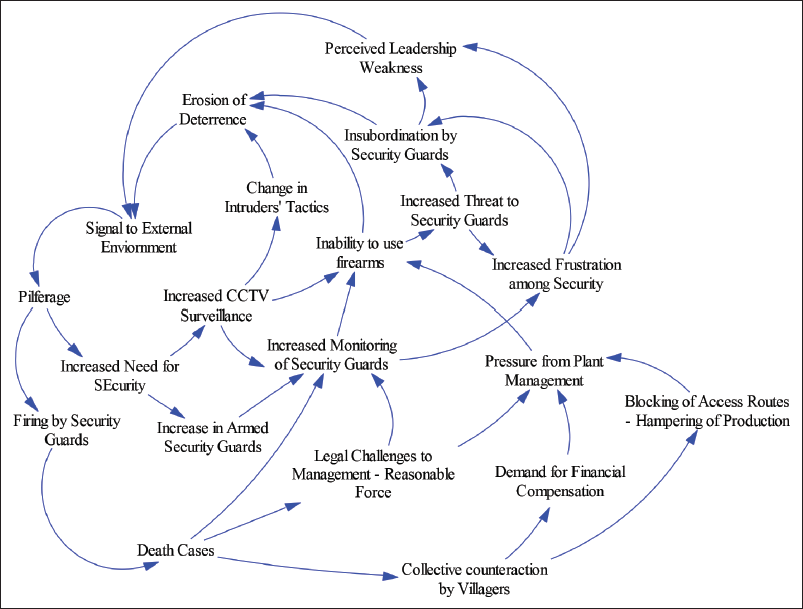
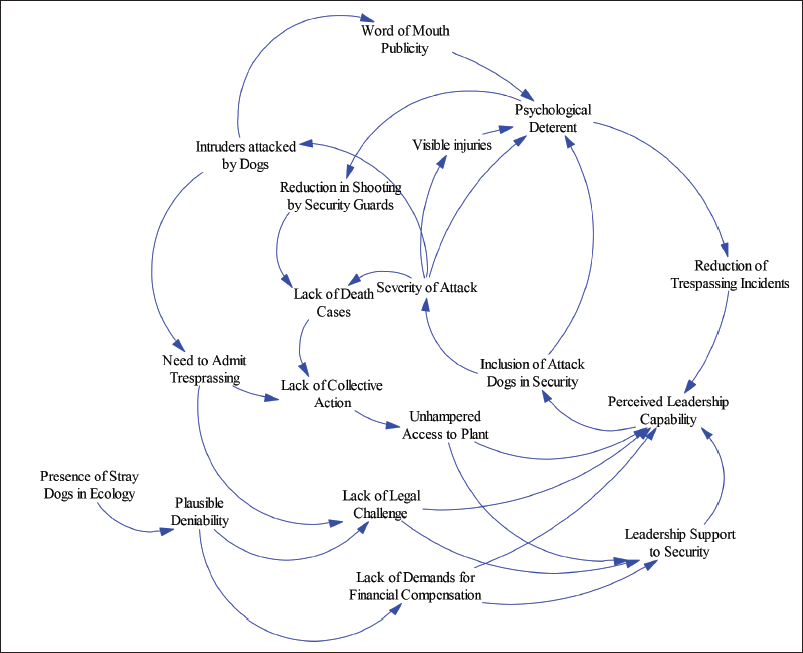
In this article, we first present the story, as true to facts as a reconstructed story can be, with a description of the context within which the events occurred (Dyer & Wilkins, 1991). The development of the story has been supported by developing a causal diagram parallel to data gathering. Widely used in organizational studies (e.g., Perlow et al., 2002; Sastry, 1997), causal diagrams allowed us to concisely capture decisions, and consequences of the same, presenting a visual picture illustrating the complex dynamics within the situation. This allowed us to visually summarize different chunks of information into a coherent whole (Miles & Huberman, 1994).
THE CASE
Cemcco (anonymized), a cement manufacturing company in the eastern part of India, has its plant situated outside the municipal limits of the city. It is surrounded by a slum comprising almost 3,000 families, which skirts the 10 km of the plant’s boundary wall. These families typically comprised migrant villagers from rural areas settled over a period of time. An inventory of malfunctioning equipment and spare parts inside the boundary wall has attracted intruders on a regular basis, as copper, aluminium and other metals in these parts fetched good prices in the grey market.
With the increase in thefts, the leadership mandated an increase in the number of armed security guards. This was duly provided by the private security agency. Cemcco also invested in additional floodlights and CCTVs that were monitored in a centralized control room. Additionally, loudspeakers were operated from the control room.
Typically (traditional approach), when intruders were detected, they were warned via loudspeakers and asked to retreat. They were warned that they would be shot if they did not go back. On occasion, security guards were ordered to fire warning shots. More commonly, security guards were sent to the spot as directed by the control room, and the security guards would confront the intruders physically and force them out. In most cases, when the intruders were isolated individuals, this strategy worked. Sometimes, the intruder would pick up the nearest item he could lay his hand on, throw it across and run across the boundary wall.
However, the intruders had increased in frequency, and small groups coordinated to spread out the security guards. This changed the dynamics as the security guards were outnumbered. There were instances when the intruders had attacked the security guards with brickbats. Forced to defend themselves, the security guards fired in self-defence, which led to the death of intruders. In another incident, the security guards fired a warning shot in the dark in the direction of the intruders which resulted in a fatal injury. The consequent collective backlash in the form of a dharna had led to a complete prohibition on all shooting, including that of warning shots, by Cemcco leadership.
AFTERMATH OF A FATALITY
A procession of nearly a hundred persons headed by the bereaved family members brings the body along and places it in front of the main gate. Imagine the situation and you representing the company and asking the people to peacefully disperse so that the plant’s operations are not hampered. (Manager, Admin)
The dharna became a rallying point, bringing out anger and frustration against the company. It also became an expression of collective grief and solidarity at what was considered a disproportionate reaction to a down-to-earth crime of stealing. The local politicians joined the dharna, which made it more aggressive. The crowd was unwilling to discuss or reach a settlement. It was intent on getting their hands on the ‘person who fired the shot’. Faced with an emotionally charged crowd, the local police were reduced to idle bystanders. Often the senior officials preferred to wait and watch, consistent with their approach that as long as the crowd was not indulging in violence, the police did not have a locus standi for getting involved. A death in front of local elections is dreadful experience, as the politicians want to extract the maximum political mileage from the situation. They prolong the negotiation, preventing the body from being sent to post-mortem…unless adequate compensation has been paid, and management has apologised. Most of the police force are employed from the middle and lower-middle strata…. Even if they do not support the criminal activities, a death case is a highly emotional issue. (Manager, Admin)
Security Guards’ Firearms: A Contested Domain
When incidents flared up, like a gherao that stopped all movements from the plant, officers from the administrative departments would try to resolve the situation. Often countenancing the emotional anguish expressed by the families and apologizing on behalf of the company, they would offer apologies and monetary compensation, negotiating with the family members and the crowd to resolve the issue. However, by that time, the plant would have witnessed all stoppage of movement from the gates for a couple of days.
Post such gheraos, discussions between CEO and top managers often witnessed managers expounding the cost–benefit argument and advocating a more accommodating approach. The cost of the item stolen was in hundreds of rupees. But the cost of one day of blockage is in lacs [Indian term 1 Lac = 100,000]. So, most managers argue that security guards are causing a loss to the company. Another relevant point is the incentive. All management personnel are incentivised on sales achieved. So, a day of lost sales is lost incentive. (Manager, Admin)
The prevalent discourse was more in terms of preventing disruptions to operations and accommodating what was considered a minor cost.
We explored the worldview of a security guard who had fired shots at the intruders, either in the line of duty or in self-defence. This elicited the following responses from the proprietor of the private security agency. …the slum dwellers filed a criminal case against the security guard… A police case filed under section 299 of the Indian Penal Code of culpable homicide. Luckily, the police constable had given an early warning, and the person packed his bags and absconded. There was no other way to keep himself out of jail. Neither he, nor we as a security agency, have financial resources to hire a criminal lawyer to fight his case. This incident has demotivated the security guards a lot. For them, it is a question of a paltry 12,000 rupees per month as salary plus all the risks …Even we [as agency] are forced to pay as penalty for any item stolen…It is deducted from our bill. …So, we are caught in the middle.
The security guards’ position reflected an unenviable power inequity, forced to act to stop trespassing and yet constrained not to inflict any injury which could turn into a fatality. As the blame shifted towards the security guards, Bourdieu’s notion of habitus as a theoretical lens cogently incorporates the security guards’ concerns and the managers’ anxieties illuminating the power dynamics, within the context of the Indian socio-political milieu. The guards’ rationality of acquiescence, providing a modicum of meaning and well-being, emanates from the habitus structured by leadership’s decisions and managers’ focus on maintaining peace.
Existing Security Paradigm and Commitment Escalation
Fearful of being assaulted outside the plant, the managers collectively advocated a pacifist approach and structured the issue as a failure of the security guards. Within this discourse, the use of firearms became a confirmation of the guards’ incompetence. The extant discourse hinging on increasing manpower in the field was based on increasing deterrence via increased numbers of security guards. The premise remained unchallenged despite consistent evidence of failure. Most management personnel argued for increasing the numbers of armed guards. … Most managers never understand the situation, since they are confined to their arm-chair thinking. An armed guard who cannot shoot is absolutely no different from a guard holding a plastic toy gun. (Security in-charge officer)
Satisficing and Consequences
The capitulation by the company’s leadership to the compensation demands in cases of death, and the pressure on the security guards to not shoot, signalled the weakness of the leadership among external stakeholders. It was like an open invitation to come and take what-ever you wanted…. Soon the losses went up. Forget small tools and metal pieces. A 24-ft industrial ladder was carried over the boundary wall…’. (Security in-charge officer)
The same was confirmed by the security staff of the neighbouring organization. The question related to additional CCTVs elicited the following response:
The CCTVs allow me to understand what is going on a real-time basis. I know who is coming and what is he about to steal. I can inform the security guard to stop him, or if he has picked up something and is about to cross the boundary wall, give chase. It is physical brawling with the groups of intruders.
The situation becomes threatening when we know a group of intruders come, steal in a methodical manner, and we all know that they are not afraid of us….there is a high probability that they will be armed. (Security in-charge officer of neighbouring organization)
Perpetuating the discourse centred on blame attribution disempowered the guards, creating a deleterious vicious cycle within the organization as illustrated in Figure 1. With no support from any significant stakeholder, the powerless security guards represented an unwelcome constituent of the organization, relegated to the fringes of organizational discourse.
The doctrine of reasonable force provides no functional guidelines to a security guard at night.
‘The response has to be proportionate to the threat’ is the legal doctrine that can get a security guard killed, or in the best case, to resign from the job and take refuge in a less arduous role. A security guard can be, and in case of death is, often reprimanded for not following a scaled response. A criminal case filed against a security guard is an effective threat by intruders, ensuring a complete standstill of the guard’s career. He is faced with an imprecise situational analysis regarding the number of intruders, the possible arms the intruders might be bearing, and the chance that there are multiple groups the presence of which he may be unaware of. How many groups have entered the premises, which one is the diversion, and which one is armed—these are issues, which often are discussed by the arm-chair managers but are of little help to a security guard in the field. (Security in-charge officer)
Bourdieu’s notion of habitus provides us with a nuanced insight into the security guards position, a complex situation bounded within the organization’s concern for the security of its assets, managers desire for uninterrupted operations and protection of their bonuses and the outsiders’ concerns for economic survival forcing them to trespass. The guards’ acquiescence reflected their powerlessness within their habitus, an interplay of embodied asymmetric power hierarchy (Bourdieu, 1977).
LEADERSHIP CHANGE AND A BREAK FROM THE PAST
Around 2016, Cemcco was taken over by another conglomerate. Along with this change, there was also a change in CEO. To handle the problem with intruders, the CEO’s initial steps involved taking stock of the situation from the security guards, and head of the departments (HODs) of the plant. The CEO also interacted with the police. The CEO disregarded the narratives put up by HODs. The HOD’s view was to accommodate the pilferage and treat it as a cost of business, that is, normalize the pilferage and treat it as a cost item. The HODs wanted the CEO to accommodate the trespassing since the aftermath of strict action by the security led to a disruption in operations that also impacted the HOD’s incentives. …the CEO talked to the senior officers of police. These police officers come from a variety of backgrounds and with experiences in different fields. The core issues impressed upon the CEO by the officers, it seems, was that in no case there can be firing. (Manager, Admin)
The security guards getting a preferential audience signalled a new paradigm. This simple act rendered the old discourse defunct by ignoring the legacy and the collective decision-making process that incorporated the management. The new CEO, based on his interactions, advocated a new security strategy—the introduction of attack dogs. After interacting with the police officers, we got to know that an attack-dog–based firm has been awarded the contract of security. The contract required the agency to provide a certain number of dogs, along with handlers. Never it was announced that these were attack dogs. It was simply informed that we now have security dogs. (Manager, Admin)
The inclusion of attack dogs in security led to an effective force—continuum for the security guard. The verbal warnings over the loudspeaker were not followed by warning shots, as was the earlier protocol. Under the new paradigm, the guards informed the intruders that they would release the dogs. After giving the intruders enough time to retreat across the wall, they would do so. An attack-dog is different from a guard dog/ or a security dog. It is trained not to bark. It is trained for only one thing—to attack. …When we think that the intruders are more in numbers, we release multiple dogs. (Dog handler)
To understand the behaviour of attack dogs, we requested elaboration from the proprietor of the dog agency. For the dog it is just a target – not a human. A single attack-dog first goes for the limbs to disable the target. Once the target is down, throats, necks or other soft muscle areas like the groin will be targeted. Specific targeting is also by training…But then, do not forget, the instinct takes over … a dog will attack the way it is driven by its instinct. A pack of dogs is another story altogether. If you have watched National Geographic, you would have noticed that the target is a meal. Each dog starts to tear at the target, trying to eat as much as possible, that is the instinct in group attacks. (Proprietor, dog agency)
What would happen if the person jumped over the wall?
‘Dogs, once they have tasted blood, do not follow boundaries. Nor are they, at that time, in mood to obey the handlers. If there are multiple dogs following, there is a high chance the pack will follow beyond’.
The security system worked on the condition of complete information sharing between the organization and the dog handlers. Reminiscing about an incident that highlighted the ferocity of the dogs when employees entered the site without prior information, the proprietor laughingly recalled:
Once a couple of officers came in a Maruti Gypsy. We were not informed, [as was the new protocol] and the dogs had been let loose. One of the dogs had climbed on the canvas roof, while the others surrounded the jeep. Once the handlers reached, it took some time to get the dogs under control…. The officers were sweating inside the jeep.
Extreme Aggression: The Essence of the New Paradigm
The new security paradigm implied a higher probability of physical injury for the trespassers. The impact of a dog attack is more than a physical injury. The rapid charge of multiple dogs, and the inability to retaliate against a pack of dogs, is a visceral experience, triggering a primordial fear reaction. Those who can run away safely would remember the chase for a long time. However, those who could not—they literally have nightmares. Imagine your leg caught in a pair of jaws which digs till the bone and crushes it. A person would limp for life in cases where veins and arteries are torn apart. (Proprietor, dog agency) ‘Everyone who has survived discusses the attack, and how they survived. The fear spreads easily…(Dog handler)
Earlier, the security guards’ passivity reflected the learned experience within an unsupportive socio-cultural and historical context. With the change in leadership, they found themselves in the hub of activities, with the attack dogs liberating them from their earlier reticence.
A New Level of Psychological Deterrence
Dogs’ ability to cover large areas, supported by their hearing ability and exceptional olfactory function, have made them preferred companions of law enforcement agencies (Van Jaarsveld-Schalkwyk, 2015).
The adoption of attack dog–based security paradigm brought in a heightened level of psychological deterrence. With their superior sensitivity, a dog is in complete sync with the situation. The combined animal intelligence of a pack of dogs provides an exponential increase in situational awareness. Multiple attack dogs behave like a pack of wild dogs, going back to their primal instincts of attacking to protect their territory. It is about changing the narrative. Do we think more about the intruders’ human rights or the security of organisational resources, employees and security guards’? (Manager, Admin.)
The boundary wall, which earlier had ended up as a mere symbolic barrier, now had a new meaning. The presence of attack dogs across the boundary heightened psychological deterrence replacing the earlier moribund situation.
Tacit Sanction by the Government Authority
Implementation of the new security paradigm brought its own casualties, in the form of people who had suffered dog bites (Fonseca et al., 2015). Though the dog bites were serious injuries, the police did not intervene in the entire exercise. Compared to a fatality from a gunshot, a dog bite was not a fatal injury in most cases, relieving the police of any involvement. The legal dimension of a dog bite was discussed. A dog bite to be traced to a particular dog, and for a police case to be filed, it requires evidence from different forensic professionals such as pathologists, odontologists, veterinarians, biologists, and police investigators. … He must prove that it was not a stray dog that bit him. And we have a lot of stray dogs in the surrounding garbage dumps, as well as in the slums. And most important of all, the person must admit that he crossed the boundary wall. If he admits, immediately the question the police ask, what business did you have across the company boundary wall? So, unless they answer, they do not file cases. (Manager, Admin.)
The success of attack dogs has boosted the morale of the security guards, which sometimes has led to certain excesses, an act of revenge for what they suffered earlier. Security guards have their own lives. I am their boss, but they have their own subculture, and their peer-influences…. Let us be honest. Some of the security guards had been beaten up by intruders. So, these guards influence our handlers to, you know, be easy on the dogs. It is a way to hit back at the intruders...However, we regularly instruct the handlers to reach the spot as fast as possible. (Proprietor, dog agency)
Figure 2 shows the changed scenario that prevailed after the inclusion of attack dogs in the security.
Discussion on the reaction of the police elicited an accommodative stance towards the organization’s new security paradigm. Often, the territory guarded by the dogs doubled up as an informal punitive measure for the police. Police are happy with us. Now they know that the grey economy has reduced, and therefore the nonchalant attitude of the slum-based gangs has come down. For the criminal, it is like ‘police can pick us and throw us across the boundary wall’, a way for the police to bypass the judicial process and give a ‘lesson’ to some criminals. (Manager, Admin.)
Conclusions
Organizations and their members are not passive consumers of security (e.g., Goold et al., 2010; Loader, 1999), but are active architects of communal habitus with multiple stakeholders in the security narrative. Our research establishes how different stakeholders, apart from the organizational leaders, sway the narrative. The initial dominance by managers, despite their inexperience in security and possible strategies, had escalated commitment to the technology and guards-based stratagem, despite recurring evidence of its failure as witnessed by a lack of psychological deterrence. Psychological deterrence and implementation of reasonable force by security guards, the essential facets of security strategy, depend on the fear of ‘dire consequences’ (Greer & Bartholomew, 1982) established by punitive consequences. The doctrine of reasonable force, an essential component of security discourse, is linked not only to subject resistance (Boivin & Lagacé, 2016), but, as our research identifies, the acceptance by different stakeholders within the habitus.
Compared to Figure 1, Figure 2 illustrates evidence of reinforcement and recalibration of psychological deterrence, provided by the primal fear and the panic aroused by the dogs (Van Jaarsveld-Schalkwyk, 2015). The attack dogs (Begeç, 2012) restored the guardianship and the authority, the essence of a security guard’s worldview, as compared to the earlier disempowered existence. While the firearms had been reduced to mere artefacts, the attack dogs’ savagery was crucial in the re-establishment of the security guards’ authority, as evidenced by the new protocol of managers having to pre-inform the security guards before venturing out in the plant yards.
The police, by discouraging the futility of trespassers’ filing cases against the company, provided a sanction to the organization in an informal exchange for its unconventional contribution towards undermining the criminal ecosystem (Dorn & Meerts, 2009). Constrained due to official compunctions and yet charged with the responsibility of ensuring public law and order, and minimizing criminal resistance (Boivin & Lagacé, 2016), police’s accommodation of strong responses, that would be ‘acceptable’ within the current socio-political environment, by private guards indirectly implies maintaining an agency for enforcing punitiveness beyond the official purview.
DISCUSSION AND IMPLICATIONS
We consider our study to be significant to practitioners and researchers in multiple ways. For the first time, we have presented a case highlighting the failure and adaptation of security strategy, which can only be understood by considering the nuances of the context within which the entire case is embedded. Second, we have highlighted the role of leadership and leadership discourse, which inconspicuously binds leaders and managers to a failing course of action. Another significant contribution is that our research provides a rare inside view of the challenges in maintaining security in the Indian context with its myriad stakeholders.
We classify our case as critical as well as revelatory (Yin, 2003), challenging the dominant view of private security as being non-punitive and defensive in nature. Our research has highlighted how collective action by citizens in the Indian context can overwhelm the organization, and constrain the security guards, with a resulting erosion of psychological deterrence. We believe this is one of the rare research projects that highlight the possibility of external stakeholders halting the organization’s security strategy.
The consequences of a lackadaisical security in a community go beyond the immediate stakeholders. The ‘reputational risk’ (Dupont, 2014) that goes beyond the organization, with a crime against specific private organizations morphing into a general breakdown in law and order, has significant implications for practitioners and policymakers. The spread of knowledge of failure in guardianship, despite the implementation of a technology-based and firearm-driven strategy (Luxenburg et al., 1994), among different stakeholders leads to a vicious downward spiral in criminality and crime-based economy. This insight from our study points out the potential of spill-over to society at large as emboldened criminals move from softer targets and broad base their activities.
While commitment to failing strategies has been a widely researched area (Staw, 1981), our research has illustrated how a failing paradigm can be reinforced and strengthened by the dominant discourse of internal stakeholders, like senior managers, who are not accountable for resulting consequences (e.g., Posen, 1993). Organizations tend to suffer double jeopardy—stoppage of production due to retaliatory actions, and individualization of risk borne by the security guard (Gray, 2009) leading to a security guard who absconds to protect himself and thus engendering negative morale for the remaining security guards.
The implicit accommodation and advocacy by police for strong action by their private counterparts to preserve law and order is another area where our study makes a significant contribution. Conceptually distinctive from police brutality (e.g., Worden, 2015), or private violence to advance the objectives of certain stakeholders (e.g., Porteux & Kim, 2016), this tacit approval of borderline methods has its ramification of creating parochial security regimes (Dupont, 2014). Our study has highlighted situations when faced with politicization of law and order (McLaughlin et al., 2001), or breakdown in urban governance (MacLeod, 2011), police expect their private counterparts to act on their behalf, provided the consequences are controlled. While it does help to prevent lawlessness from spreading due to the convergence of objectives of official police and private security, as compared to strained relationships (Morley & Fong, 1995), it can establish its own political economy, with its own rules and practices.
An aggressive security apparatus raises questions regarding the legal status of private security staff as agents of property owners (Button, 2003; De Waard, 1999) and the legal rights of criminals. The legitimacy of the principal that contracts the security agency is restricted to the private domain (Phelps, 2014) and does not necessarily empower the agency to be a punishing authority. However, with police as sponsors of a new security paradigm in the community questions, further research is needed to settle the questions about accountability and control (Gill & Hart, 1999; Stenning, 2000). With economies becoming more complex, the possibilities of increased socio-political inequities triggering the evolution and adoption of unconventional security paradigms offer significant challenges for practitioners and researchers (Dupont, 2014).
The evolution of the social and cultural capital (Bourdieu, 1986), including the stakeholders’ challenge to a dominant stakeholder’s ‘private property’ (Shearing & Stenning, 1983), is another unexplored area unearthed by our research. It is not yet known what path stakeholder activism would take in the face of private coercive apparatuses and how it would modify social and cultural capital. As contrasted to a conflict-driven paradigm characterized by perpetual hostility, adopting collaborative and cooperative strategies would require organizations to invest significantly in the social and economic development of the perceived ‘outsiders’. There is scant research on such approaches that can guide practitioners, including the probability of the success of such paradigms. However, the evolution of the socio-cultural capital (Dupont et al., 2003) along with the redefinition of practice by myriad stakeholders in the context of security cannot remain untouched by the security paradigm adopted. While being a relatively unexplored area, with its potential for extensive impact on broader society, we think that it would be an important area for exploration for policymakers, apart from researchers.
Footnotes
DECLARATION OF CONFLICTING INTERESTS
The authors declared no potential conflicts of interest with respect to the research, authorship and/or publication of this article.
FUNDING
The authors received no financial support for the research, authorship and/or publication of this article.
e-mail:
e-mail:
