Abstract
Knowledge hiding, the deliberate withholding of knowledge, can undermine team effectiveness and organizational performance. However, little is known about its diffusion within organizational teams. Drawing on social contagion theory, this study uses Autologistic Actor Attribute Models (ALAAMs) to examine knowledge hiding across workplace and social communication networks. Whole-network survey data from 200 employees in 31 teams in the U.S. and China reveal that, overall, knowledge hiding does not spread through communication networks. Certain network structures, however, facilitate its transmission: individuals centrally connected to multiple teammates or embedded in closed triads with both a hider and a non-hider are more likely to hide knowledge, whereas those bridging structural holes between hiders and non-hiders tend to avoid it. These findings advance social contagion theory and knowledge hiding research by showing how norm-violating behavior diffuses across different network structures and by characterizing knowledge hiding as network-embedded rather than solely an individual act.
Keywords
Introduction
Knowledge is widely recognized as a critical organizational asset (Nahapiet & Ghoshal, 1998). Its effective sharing facilitates innovation (Guo et al., 2022), accelerates problem-solving (Xu et al., 2023), and fosters collective learning (Lefika & Mearns, 2015), all of which are essential for sustained organizational performance. However, not all employees are equally willing to share their knowledge (Evans et al., 2015). A growing body of research has identified knowledge hiding (hereafter referred to as KH), defined as the intentional withholding of knowledge requested by others in the work environment (Connelly et al., 2012), as a substantial barrier to knowledge sharing and collaboration. The phenomenon has gained considerable scholarly attention, with over 400 empirical studies explicitly examining its antecedents and outcomes since the mid 2020s (Shen et al., 2025). Yet, despite this substantial research progress, one critical question remains largely unanswered: Is KH contagious in the workplace?
The prevailing perspective in the existing KH literature conceptualizes it as an individual-level behavior influenced by factors such as demographics, personality traits, leadership styles, and human resource practices (see Shen et al., 2025 for a review). However, this view may be insufficient in today’s relationally intensive work environments, where formal teamwork is increasingly intertwined with informal social networks (Susskind & Odom-Reed, 2019). In such interconnected contexts, behaviors, both cooperative and counterproductive, may diffuse through communication patterns and interpersonal proximity (Reagans & McEvily, 2003).
Drawing on social contagion theory (Burt, 1987; Centola, 2018; Fowler & Christakis, 2010), this study posits that individuals may not engage in KH in isolation but adopt such behavior through interactions with others who do. Social contagion theory suggests that attitudes, emotions, and behaviors can spread through social interactions via mechanisms such as imitation, conformity, and normative pressures (Centola, 2018). Foundational work on the diffusion of innovations (Rogers, 2003), structural holes (Burt, 1992), and social influence processes (Marsden & Friedkin, 1994) underscores the role of network structures in facilitating or constraining behavioral diffusion. More recent research further demonstrates that strategically targeting individuals within networks, such as using friendship-nomination techniques, can amplify the adoption and propagation of behaviors (Airoldi & Christakis, 2024). Together, these insights highlight the critical role of structural features such as centrality, density, and clustering of social networks in shaping the dynamics of contagion across various social settings.
Following this theoretical framework, this research proposes that individuals’ KH behavior can be influenced by others within their communication networks. To test this proposition, we examine the diffusion of KH through workplace and social communication networks using Autologistic Actor Attribute Models (ALAAMs), a network-based method for modeling behavioral contagion through network ties (Parker et al., 2022; Robins et al., 2001). Using whole-network survey data from 200 employees in 31 organizational teams across the U.S. and China, we analyze whether and how KH propagates within these teams. Our findings reveal that specific network configurations either promote or constrain the spread of KH, emphasizing that behavioral diffusion is contingent on network structures and that KH arises from relational and structural contexts. This study advances understanding of social contagion and KH by linking micro-level behaviors to meso-level network structures (Contractor et al., 2006; Kush et al., 2025) and characterizing KH as network-embedded rather than solely rooted in individual propensities. Building on this overview, the next section reviews the theoretical framework of social contagion and presents the study’s hypothesis and research question, followed by sections on methodology, results, and theoretical and practical implications.
Theoretical Framework
Social Contagion
Social contagion theory encompasses an established theoretical framework for understanding how human behaviors, attitudes, and emotions spread through their social interactions (Centola, 2018; Fowler & Christakis, 2010). Rooted in diffusion of innovations theory (Coleman et al., 1957) and social comparison theory (Festinger, 1954), it highlights the interpersonal transmission of behavioral patterns via both direct and indirect social connections. While often discussed alongside broader social influence theories (e.g., Cialdini & Goldstein, 2004), social contagion theory is distinguished by its emphasis on the structural properties of networks as well as their role in shaping behavioral diffusion across a variety of social settings (Friedkin & Johnsen, 2011; Parker et al., 2022).
At its core, social contagion theory states that individuals tend to adopt the attitudes or behaviors of those with whom they are socially connected (Fowler & Christakis, 2010). This diffusion can occur through two primary pathways: contagion by cohesion, which stems from frequent, emotionally close interactions (Reagans & McEvily, 2003), and contagion by structural equivalence, where individuals imitate the behavior of others in similar network positions even without direct contact (Burt, 1987). Granovetter’s (1973) foundational work on tie strength highlights a critical structural distinction: strong ties, marked by trust and repeated interaction, versus weak ties, which often serve as bridges between otherwise disconnected groups. While weak ties are crucial for accessing novel information (Granovetter, 1973) and facilitating knowledge sharing (Hansen, 1999), strong ties are generally more influential in transmitting behaviors that involve risk, trust, or emotional resonance (Centola & Macy, 2007). Another important structural dimension of contagion is interaction exclusivity, based on Krackhardt and Brass’s (1994) refinement of contagion theory. Beyond the idea that more interaction generally increases similarity, they highlight that the wider a person spreads their interactions, the weaker their influence on any single individual. Thus, social influence tends to be greatest when interactions are not only frequent but also concentrated within a relatively small group.
Social contagion theory has been widely applied to examine the diffusion of a diverse range of organizational behaviors. Studies have shown that employee moods (Totterdell et al., 1998), burnout and work engagement (Bakker et al., 2006), and unethical behavior (Gino et al., 2009) can spread through workplace interactions. Employee turnover has also been found to diffuse through social networks (Feeley & Barnett, 1997). Similarly, job seekers and organizational employees often make decisions in light of peers’ behavior and preferences (Kilduff, 1992). Collectively, these research findings reveal that individual actions in organizations are shaped not only by internal traits or rational choices but also by social influence and one’s position within a social network. More recent research has extended this lens to digital and hybrid work environments by exploring how collaboration, resistance to change, and affective expressions can propagate across both physical and virtual communication networks (Miraglia & Johns, 2021). Advances in communication technologies have thus broadened the reach and accelerated the pace of social contagion, which make behavioral diffusion faster, farther-reaching, and often less visible.
By highlighting how behavior diffuses through interpersonal influence and network structures, social contagion theory provides a well-suited foundation for investigating complex social behaviors in the workplace. Unfortunately, so far it has received limited attention in explaining workplace behaviors that are intentional, covert, or relationally sensitive. Such a gap presents new opportunities for both theoretical development and empirical investigation. This study addresses that gap by examining how KH, a norm-violating behavior, spreads within organizational work teams. In the following section, we review existing scholarship on KH and apply the social contagion perspective to analyze its diffusion across workplace and social communication networks.
Knowledge Hiding and Its Diffusion Through Communication Networks
Knowledge hiding, defined as the intentional withholding of knowledge in response to a direct request, manifests in three primary forms (Connelly et al., 2012). Evasive hiding entails deliberately misleading the knowledge seeker, either by providing false information or by promising to share the knowledge later without intending to follow through. Playing dumb involves pretending not to possess the requested knowledge even when one does. Rationalized hiding occurs when individuals justify their refusal to share knowledge by citing reasons such as confidentiality or insufficient authority. These behaviors reflect different tactics individuals use to withhold knowledge, shaped by their intentions and situational factors (Connelly et al., 2012).
An abundance of literature has linked KH to a range of negative psychological and behavioral outcomes. Engaging in KH can lead to emotional distress such as guilt and shame (Burmeister et al., 2019), reduced well-being (Khoreva & Wechtler, 2020), and higher turnover intentions (Connelly et al., 2012). Behaviorally, knowledge hiding has been shown to undermine organizational commitment (Garg & Anand, 2020), suppress innovation and creativity (Guo et al., 2022), and damage workplace relationships by reducing trust and collaboration (Arain et al., 2021). However, the effects of KH are not uniformly negative. In competitive environments where knowledge is tied to individual success, perceived KH can sometimes motivate knowledge seekers to perform more diligently. Wang et al. (2019) found that KH may boost individual sales performance, especially in interaction-rich contexts. Similarly, Shen et al. (2025) emphasize that contextual factors, such as team dynamics, leadership style, and organizational norms, critically influence whether KH proves harmful or beneficial. These findings underscore the need for a nuanced, context-sensitive understanding of KH and its outcomes.
Existing research has also uncovered a wide array of antecedents to KH, which reflect its complex and multi-dimensional nature. A key category involves motivational and attitudinal factors. For example, individuals with a strong sense of psychological entitlement may engage in KH to assert control, protect status, or demonstrate superiority (Khalid et al., 2022). Personality traits also play a critical role: higher levels of agreeableness, conscientiousness, and neuroticism have been associated with KH, potentially due to tendencies toward conflict avoidance, rule adherence, or anxiety-driven self-protection (Iqbal et al., 2020). Moreover, the Dark Triad traits (Machiavellianism-narcissism-psychopathy) could promote KH as these traits often prioritize manipulation, self-interest, and control (Pan et al., 2018).
Beyond individual dispositions, KH is strongly influenced by interpersonal dynamics and organizational context. High levels of interpersonal trust, social interactions, and perceived justice have been shown to reduce KH (Su, 2021). Leadership style plays a critical role in this process. Ethical leadership fosters a culture of openness and collaboration, thereby discouraging KH, while abusive supervision tends to create fear and mistrust, which can intensify KH behavior (Xiao & Cooke, 2019). Task interdependence has also been associated with greater KH. Gagné et al. (2019) found that it heightens external regulation to share knowledge, which in turn is positively associated with KH. More broadly, organizational climate, political dynamics, and human resource practices significantly shape KH tendencies. Cultures that promote psychological safety and transparency reduce the likelihood of KH, while those marked by secrecy or internal competition tend to foster KH (Shen et al., 2025).
Despite growing scholarly interest in the antecedents and consequences of KH, much of the literature remains focused on individual-level factors or dyadic dynamics (i.e., interactions between a specific pair of individuals without considering the influence of a third actor or the broader network). In contemporary organizational environments, where formal hierarchies deeply intersect with informal social networks (Susskind & Odom-Reed, 2019), employee behaviors are shaped, reinforced, and diffused through repeated patterns of professional collaboration and social engagement with multiple colleagues. From this perspective, KH is not merely an individual or dyadic act, but a socially transmissible and networked behavior (Reagans & McEvily, 2003). Although prior research has acknowledged its relational nature, the social transmission of KH through communication networks remains largely understudied. To address this gap, this study integrates social contagion theory with social network analysis to examine how KH emerges and spreads not as isolated acts of self-interest, but as socially reinforced patterns embedded within team interactions and network dynamics.
Social contagion theory posits that behaviors, attitudes, and emotions can diffuse through social systems via interpersonal influence (Centola, 2018), much like the transmission of infectious diseases. In organizational work teams, where individuals are embedded in densely connected communication networks characterized by close interpersonal ties and shared work responsibilities, KH may spread through a combination of cohesion-based influence and normative reinforcement. A primary mechanism is cohesion-based contagion, which suggests that individuals are more likely to adopt the behavior of those with whom they interact frequently and intensely (Friedkin & Johnsen, 2011). Repeated communication with trusted peers facilitates behavioral visibility and provides opportunities for observational learning and social comparison, two foundational processes through which individuals adjust their own actions in relation to those around them (Bandura, 1986). When an employee witnesses a close colleague consistently withholding knowledge in conversations or collaborative tasks, the behavior may be interpreted not only as acceptable, but also as strategically adaptive, especially if it appears to protect valued resources or confer status advantages. Such interpretations are reinforced in contexts where ambiguity exists around performance expectations, peer norms, or the psychological safety of knowledge sharing (Edmondson, 1999). Over time, such behavior can be internalized as implicit norms within the dyad, reinforcing the idea that KH is a legitimate response to competitive or ambiguous team environments. Given these dynamics, the likelihood of behavioral mimicry increases, even in the absence of direct coercion or formal sanctioning (Connelly et al., 2012). Therefore, we propose the following hypothesis:
Moving beyond the dyadic perspective, individuals’ KH behavior may also spread through normative reinforcement within their immediate communication network, which extends beyond pairwise exchanges to encompass clusters of interconnected ties that collectively shape their behavior (Robins et al., 2009). From a social network perspective, an individual’s immediate network consists of direct ties between the ego and two or three alters (Carrington et al., 2005). Within a triad involving the ego and two alters, two structures are particularly prominent: openness, represented by structural holes, and closure, represented by transitivity. A structural hole occurs when the ego connects to two alters who do not interact with each other directly (Burt, 1992). In this open configuration, the ego serves as a bridge between two alters, accessing behavioral cues from each alter that the other cannot observe. Because the alters act independently, their contrasting behaviors become more salient, providing the ego with clearer insight and greater flexibility in responding (Obstfeld, 2005). Transitivity, by contrast, occurs when the ego and both alters are fully connected (Burt, 2005). In this closed configuration, all members can observe each other’s behavior. This visibility may increase social pressure on the ego to align with the alters’ behavior, and when the alters behave inconsistently, the ego may face uncertainty in deciding how to respond (Flynn et al., 2010).
Within these triads, the ego’s KH tendency may vary with the alters’ KH behavior and the openness or closure of the immediate network. When both alters hide, the ego is likely to withhold knowledge in both structural hole and transitive configurations, as the absence of visible prosocial behavior reduces normative pressure and makes KH a safe choice. When neither alter hides, the ego may hide in structural hole configurations where the lack of interconnected oversight reduces accountability, but is less likely to hide in transitive triads where strong social pressure and visibility encourage knowledge sharing. When one alter hides and the other does not, conflicting cues create ambiguity in structural hole configurations, with the ego potentially either mirroring the KH behavior or aligning with the non-hiding alter. In transitive configurations, overlapping visibility amplifies these effects: strong social pressure can curb KH by reinforcing cooperative norms, whereas inconsistencies among alters can heighten uncertainty and prompt cautious, protective behavior, such as KH, to safeguard the ego’s interests. Thus, a team member’s KH behavior can be dynamically associated with both the structure of their immediate communication network and the KH behavior of the alters. To explore these dynamics, we propose the following research question:
Method
Sample and Procedures
This study utilized online survey data collected from 200 employees nested within 31 organizational teams located in the United States and China. The sample comprised 95 individuals from 16 teams based in the U.S. and 105 individuals from 15 teams in China. We selected the U.S. and China, the world’s two largest economies with distinct political and cultural systems, to extend KH research beyond its traditional focus on Western organizations and enhance the generalizability of findings across diverse organizational and cultural contexts.
Data were collected prior to the COVID-19 pandemic (2016–2018), when all teams were working in person. Participating teams, ranging in size from three to 14 employees, were recruited via convenience sampling through the researcher’s personal and professional networks. Organizational leaders were invited to nominate a single work team, either from the same functional unit or collaborating across units on a shared project, to participate in the study. These teams belonged to different organizations (approximately 50–200 employees) across a range of industries, operated independently, and neither their members nor leaders had connections with other teams. To facilitate the construction of individualized surveys tailored to each team member, detailed team-level information, including team members’ names and email addresses, was collected from organizational leaders prior to survey distribution. These customized surveys were then distributed to team members via email for individual completion. Further details regarding team composition, organizational background, survey response rates, and respondents’ demographic characteristics are presented in Table 1. This study was approved by the IRBs and other regulatory bodies overseeing human subjects research in both countries.
Background Information of Participating Team Members.
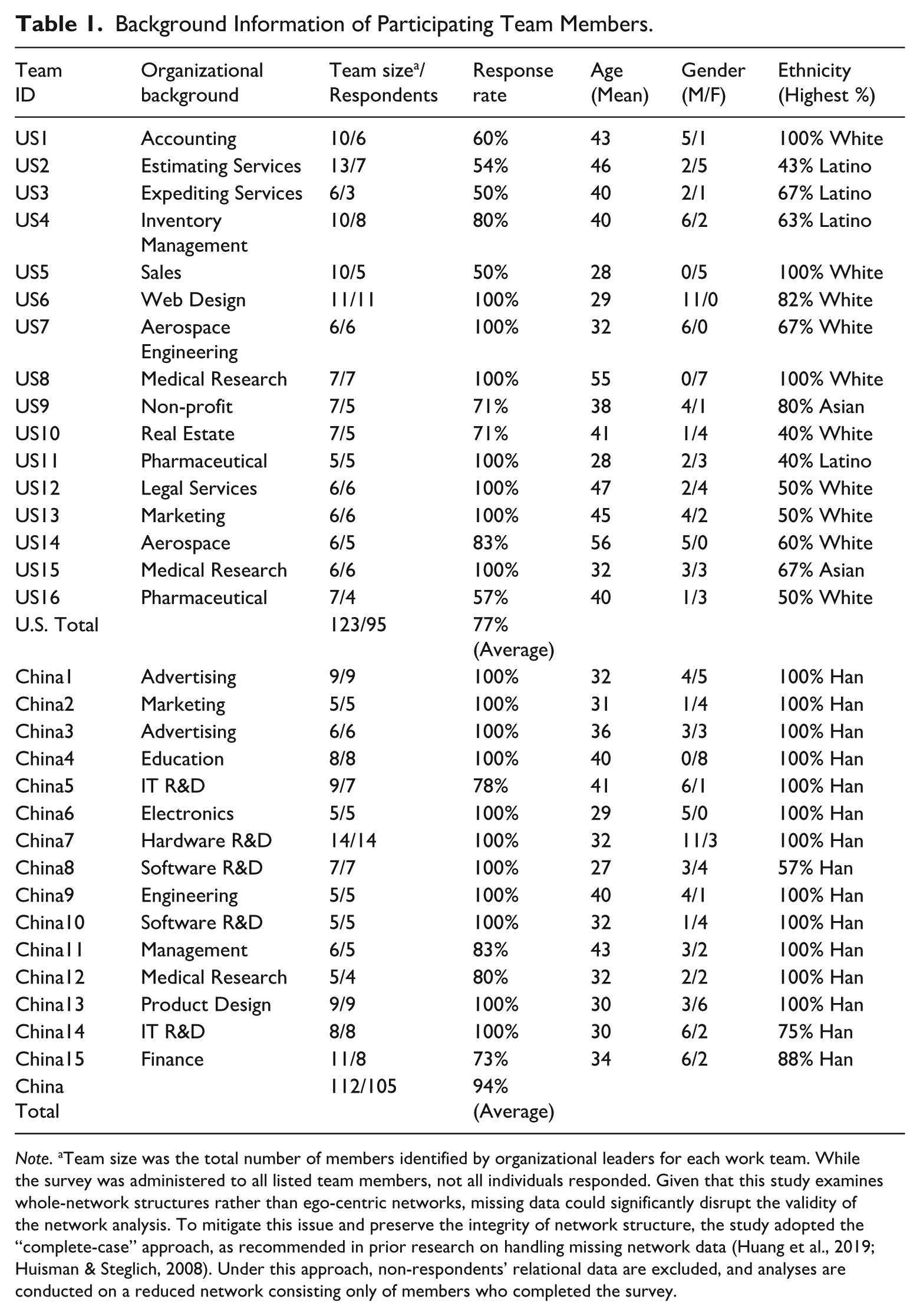
Note. aTeam size was the total number of members identified by organizational leaders for each work team. While the survey was administered to all listed team members, not all individuals responded. Given that this study examines whole-network structures rather than ego-centric networks, missing data could significantly disrupt the validity of the network analysis. To mitigate this issue and preserve the integrity of network structure, the study adopted the “complete-case” approach, as recommended in prior research on handling missing network data (Huang et al., 2019; Huisman & Steglich, 2008). Under this approach, non-respondents’ relational data are excluded, and analyses are conducted on a reduced network consisting only of members who completed the survey.
Measures
Knowledge Hiding
Knowledge hiding was measured using a 12-item scale developed by Connelly et al. (2012), which is widely adopted in KH research. The scale captures three dimensions of individual KH behaviors: evasive hiding (4 items), rationalized hiding (4 items), and playing dumb (4 items). Participants rated each item on a 5-point Likert scale ranging from “Strongly Disagree” (1) to “Strongly Agree” (5). A full list of question items is provided in Table 2.
Measurement Items.
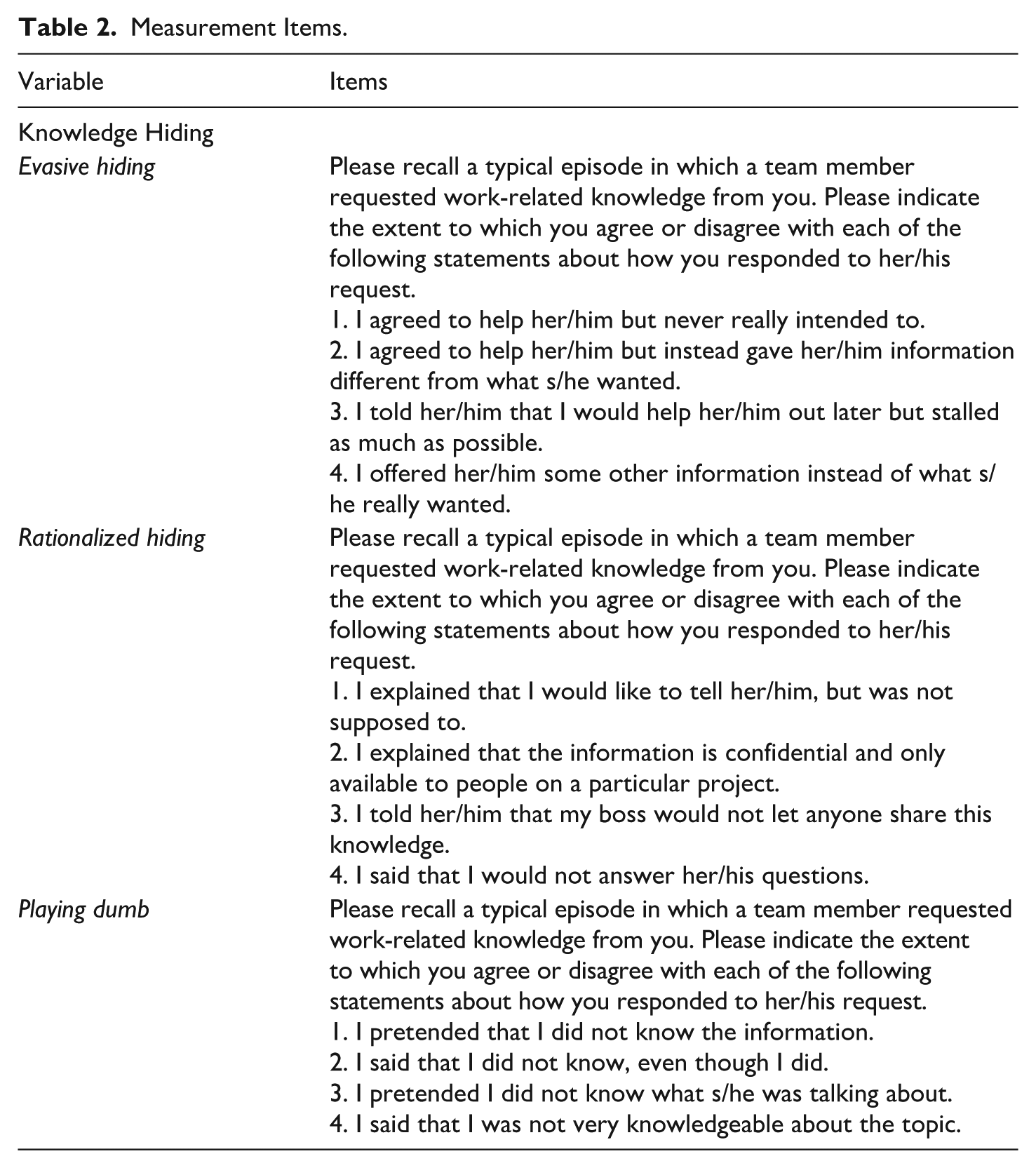
To construct an overall measure of each participant’s KH behavior, we calculated the mean score across all 12 items of the scale (Cronbach’s alpha was .82). Given that the analytical approach employed in this study, Autologistic Actor Attribute Models (ALAAMs), requires binary attribute data for network analysis, we dichotomized participants’ KH scores within each team. Specifically, we used the team-level mean KH score as the threshold for dichotomization. Participants whose individual scores exceeded their team’s average were coded as “1” (knowledge hiders), signifying a higher-than-average propensity to engage in KH relative to their teammates. In contrast, participants whose scores were below the team mean were coded as “0” (non-hiders), indicating a comparatively lower tendency to engage in such behavior.
Communication Networks
To capture the communication patterns among team members for both work-related and social purposes, this study collected data on two types of communication networks: workplace and social communication networks. The rationale for this dual focus lies in the recognition that formal task-related interactions and informal social connections may exert different, yet complementary, influences on behavioral diffusion within teams (Kilduff & Tsai, 2003). While workplace communication networks often reflect formal task dependencies and collaboration structures, social communication networks capture the relational context in which norms, attitudes, and behaviors may be reinforced or contested through more affective, trust-based exchanges. Studying both network types allows for a more nuanced analysis of how work-related and socially driven interpersonal dynamics shape behavioral diffusion in organizational settings.
Workplace Communication Network
For the workplace communication network, each survey respondent received a name roster of their team members and was asked: “How frequently do you communicate with each of the following team members for work-related purposes (e.g., face-to-face, or via telephone, email, and other electronic media)?” Responses were recorded on a 5-point Likert scale ranging from 1 (“Never”) to 5 (“Very Often”). Individual responses were compiled into an n × n matrix per team (n = team size), with each cell ij representing member i’s reported frequency of work-related communication with member j. This procedure scales up individual-level responses into a complete whole-network representation for each team by aggregating dyadic perceptions of communication frequency. Since each team member reports on all pairwise interactions, the full set of responses provides information to construct the entire network structure at the team level.
As this study focuses on non-directional ties (i.e., mutually acknowledged communication relationships), the matrix was symmetrized by averaging the values reported by members i and j, so that cell_ij equaled cell_ji, reflecting the dyad’s perceived frequency of work-related communication. Given that the current development of ALAAMs requires binary network data for analysis, the symmetrized matrix was then dichotomized using the mean communication frequency across all dyads in the team as a threshold. In the final binary matrix, a value of 1 in cell_ij (and cell_ji) indicated a frequent work-related communication tie between member i and member j, whereas a value of 0 in cell ij (and cell_ji) implied the absence of a frequent work-related communication tie between member i and member j. A sample illustration of one team’s workplace communication network is shown in Figure 1.
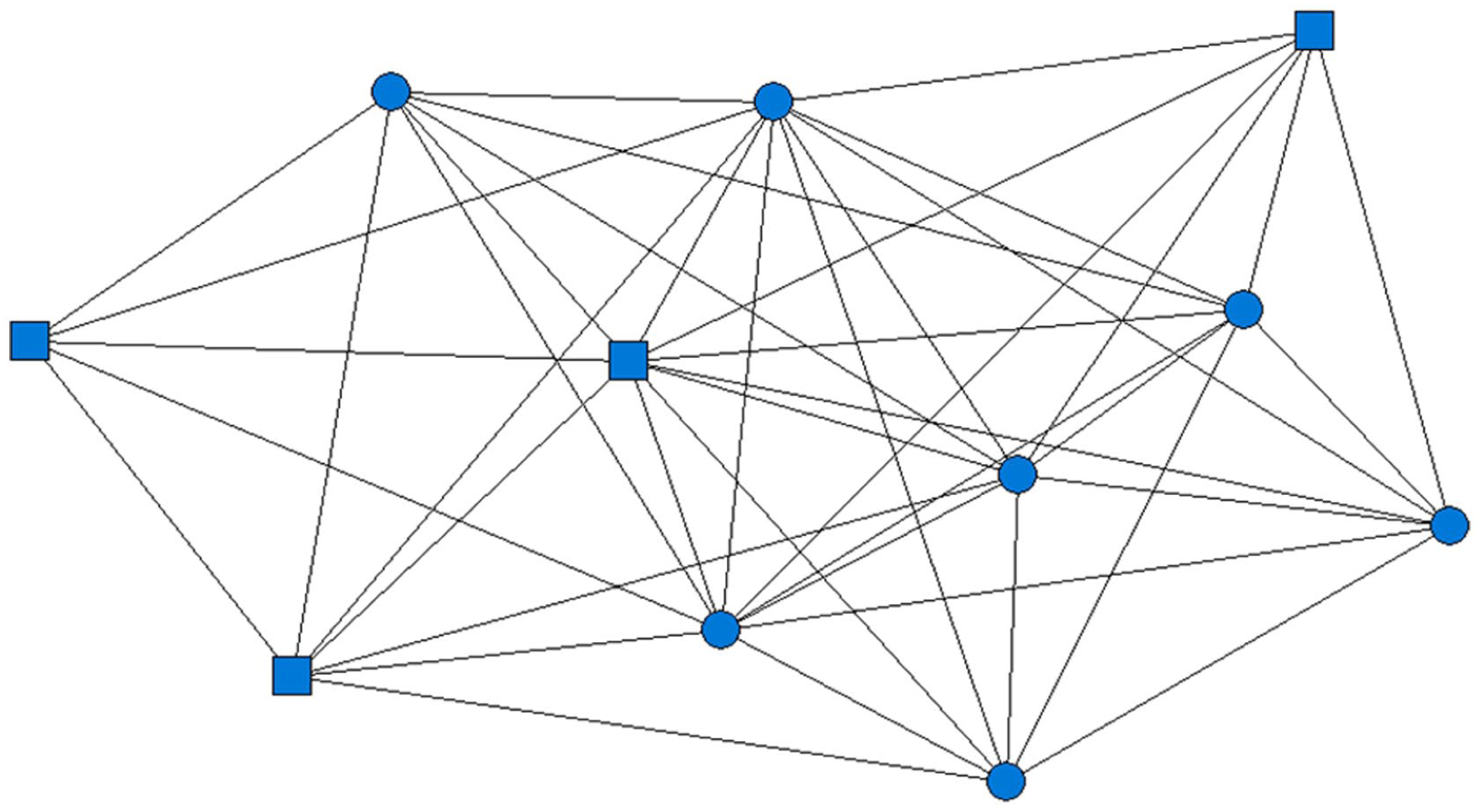
An illustration of one team’s workplace communication network.
Social Communication Network
Social communication network data were collected and processed following the same procedure as the workplace communication network. In the survey, each respondent was asked: How frequently do you communicate with each of the following team members for social purposes (e.g., face-to-face, or via telephone, email, and other electronic media)? Responses were recorded on a 5-point Likert scale (1 = Never, 5 = Very Often). An n × n matrix (where n = team size) was created, with each cell_ij representing the self-reported frequency of social communication from member i to member j. The matrix was symmetrized by averaging cell_ij and cell_ji to reflect mutual perceptions of social communication frequency. It was then dichotomized using the team-level mean as a cutoff: a value of 1 indicated a frequent social communication tie, and 0 indicated its absence. A sample illustration of one team’s social communication network is shown in Figure 2.
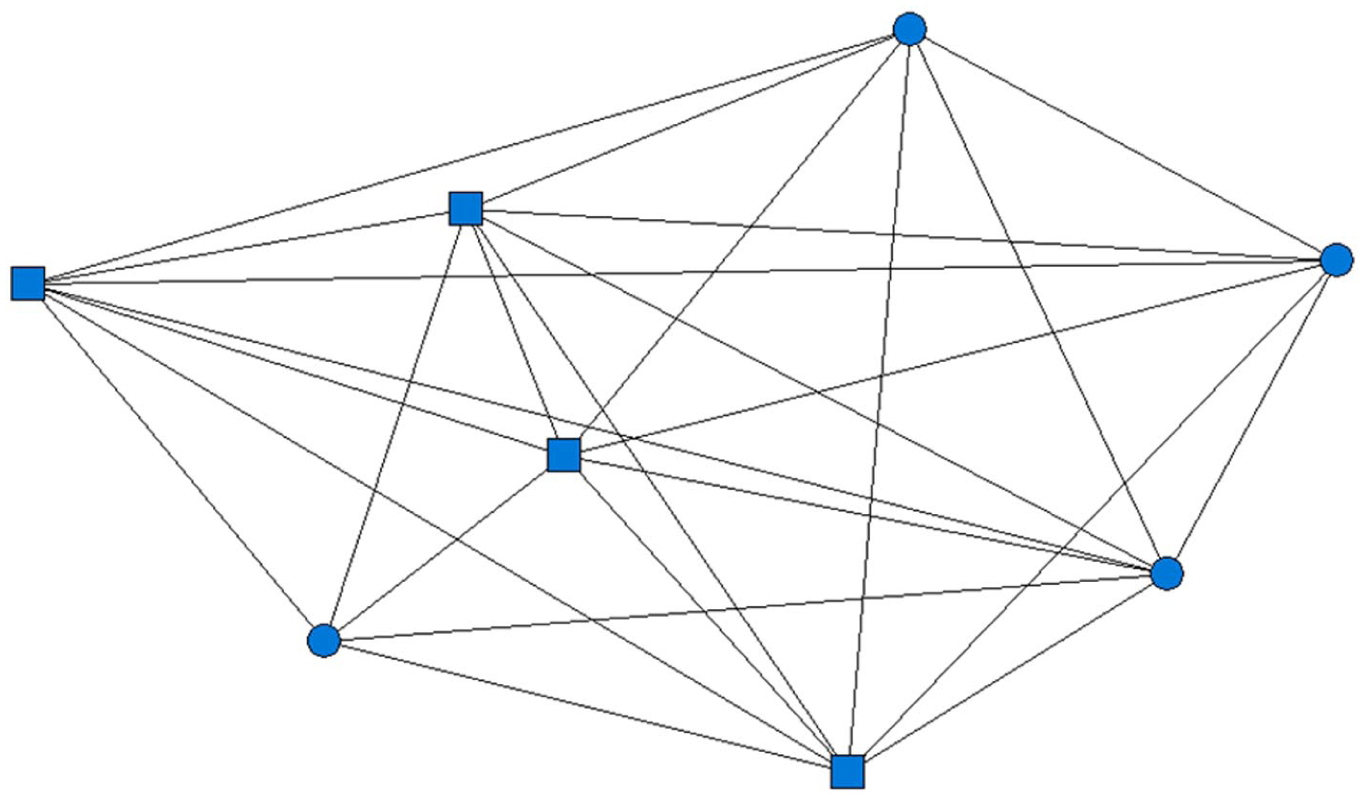
An illustration of one team’s social communication network.
Control Variables and Analytical Scope
The survey also collected demographic information from team members, including age, gender, education, job title, race, and tenure. Since the study focuses on the diffusion of KH through team members’ communication networks, independent of individual demographics, these variables were included as covariates and statistically controlled for in the analysis.
The nested structure of this study’s data (teams within organizations across two nations) provides broader contextual diversity and recognizes that factors such as national culture or organizational characteristics may influence KH behavior. However, because the study focuses on team-level network dynamics, integrating these factors would require a distinct theoretical framework and multilevel approach; therefore, national, cultural, and organizational variables were not included in the analysis.
Analysis
To examine the diffusion of KH through team communication networks, this study uses Autologistic Actor Attribute Models (ALAAMs), statistical models designed to capture social contagion and influence processes (Robins et al., 2001). ALAAMs are a variant of Exponential Random Graph Models (ERGMs) which estimate the probability of tie formation based on network structure and individual attributes or behaviors (i.e., social selection) (Robins et al., 2001). While ERGMs model how actor attributes shape network ties, ALAAMs reverse this logic by modeling how existing ties influence the likelihood that individuals adopt certain behaviors or attributes (Parker et al., 2022). Specifically, ALAAMs estimate the probability that a behavior or attribute will be adopted by an individual, conditional on its presence among connected peers and the broader network structure (Robins et al., 2001). A key advantage of ALAAMs is their ability to account for the interdependence of observations, a defining feature of social network data that violates the independence assumption in traditional models. Conceptually, ALAAMs extend logistic regression analysis by incorporating network dependencies (Letina et al., 2016), which makes them well-suited for analyzing behaviors driven by social interactions. It is important to note that while ALAAMs capture network attribute patterns consistent with contagion (such as clustering or dispersion of individual attributes within network structures), they are not intended to infer causal influence, especially when based on cross-sectional data (Parker et al., 2022).
In this study, ALAAM analyses were conducted using MPNet (Wang et al., 2022), a specialized software for modeling both ALAAMs and ERGMs. Since our data comprised 31 work teams, each constituting a distinct communication network, the study adopted the “meta-level” approach proposed by Zhu et al. (2013) to analyze these networks collectively. In this approach, individual team networks were entered as diagonal blocks within a larger meta-network matrix, while off-diagonal elements were set as structural zeros and controlled for (i.e., explicitly excluded) during estimation in ALAAMs. This approach generates a unified set of parameter estimates across all teams, which helps enhance the generalizability of the analysis while preserving the structural integrity of individual networks.
To test the hypothesis and address the proposed research question, we estimated a set of structural parameters using ALAAMs in MPNet. Each parameter represents a specific network configuration linked to an underlying mechanism that explains its formation, and these parameters were selected from the predefined set offered in MPNet based on their theoretical relevance to social influence models (Robins et al., 2001; Wang et al., 2022). To test the hypothesis, the primary focus of the model estimation was on the contagion parameter, which estimates the likelihood for an individual (ego) to engage in KH when frequently communicating with a team member (alter) who also conducts KH. Parameter estimation was conducted using the stochastic approximation method based on Markov Chain Monte Carlo (MCMC) maximum likelihood estimation (Snijders, 2002). A significantly positive estimate indicates that the corresponding network configuration occurs more often than expected by random chance, while a significantly negative estimate suggests it occurs less frequently. To address the research question, additional higher-order structural parameters, particularly at the triadic level, were included in the ALAAMs to capture more complex mechanisms of KH diffusion within the ego’s immediate communication network. For a detailed description of all structural parameters estimated in the ALAAMs, their network configurations, and the underlying theoretical mechanisms they reflect, please see the first three columns of Table 4.
Results
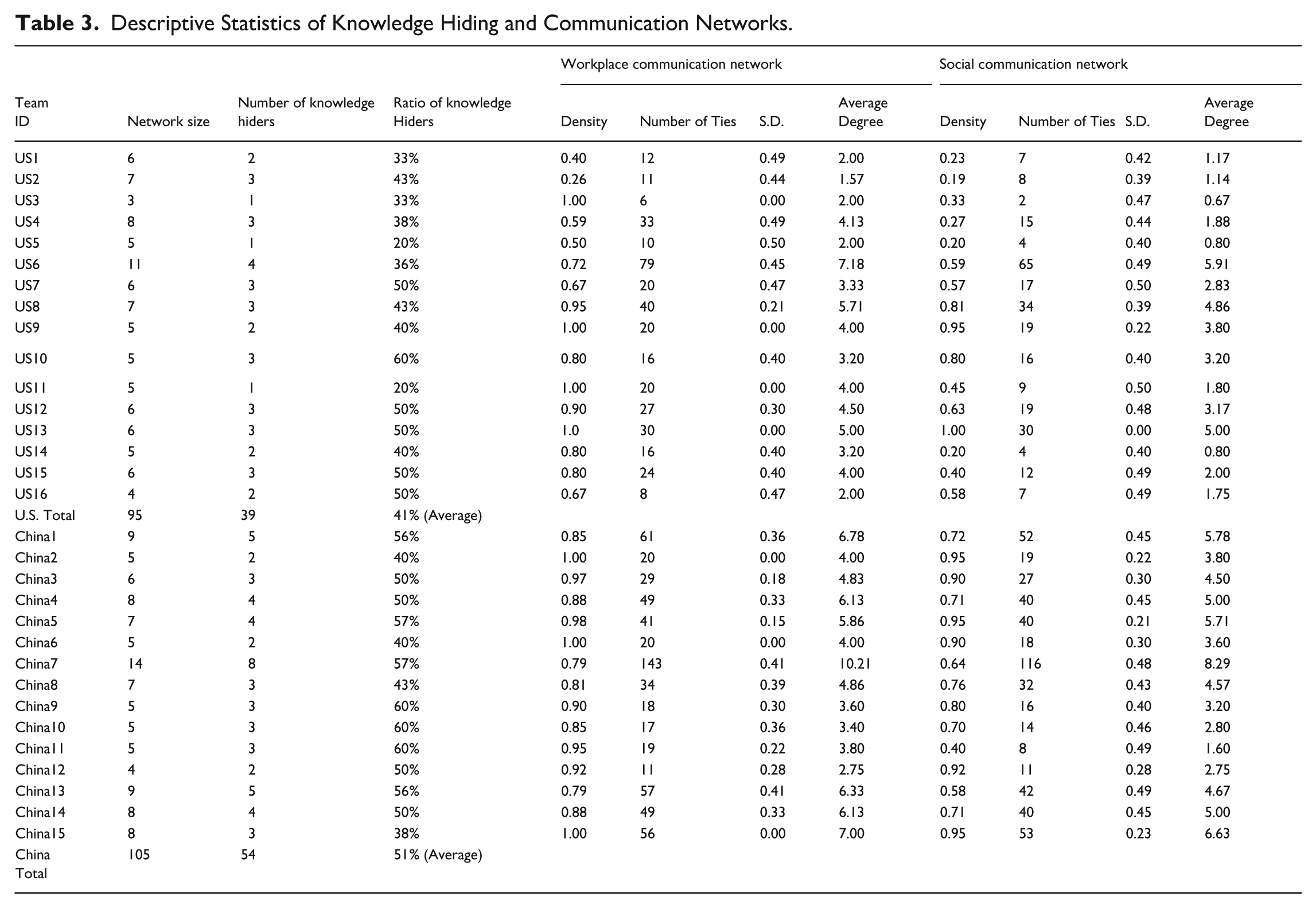
Table 3 shows the count and proportion of knowledge hiders across 31 teams, alongside descriptive statistics of workplace and social communication networks, such as network density and tie counts. Table 4 presents ALAAMs results, including parameter estimates and goodness-of-fit tests. The models controlled for demographic and positional covariates (age, gender, education, job title, race, tenure), none of which were statistically significant, suggesting the structural effects were unlikely to be due to these confounding factors.
Descriptive Statistics of Knowledge Hiding and Communication Networks.
ALAAMs Analyses Results (Estimates of ALAAMs for Knowledge Hiding Propensity in Workplace Communication Networks vs. Social Communication Networks).
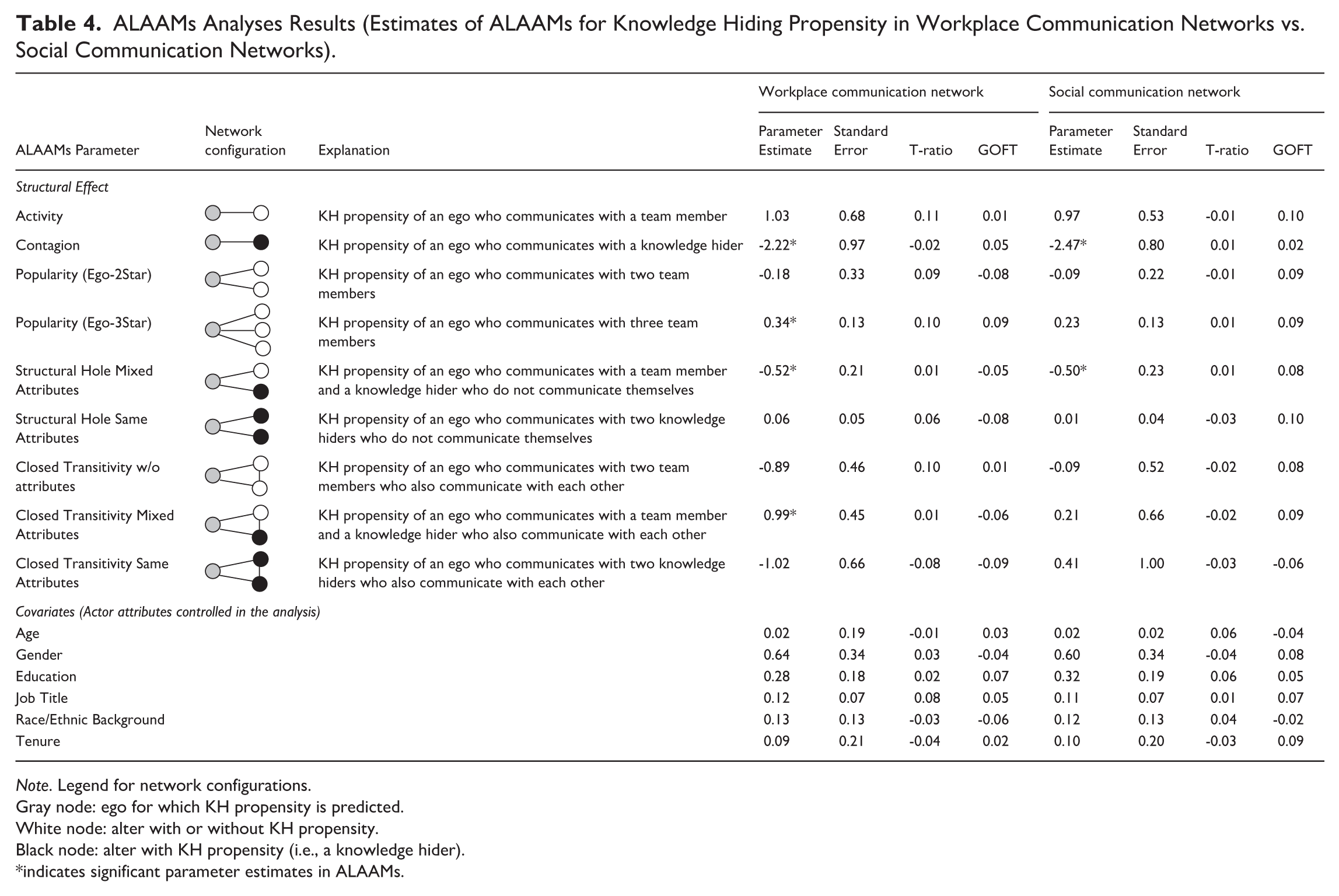
Note. Legend for network configurations.
Gray node: ego for which KH propensity is predicted.
White node: alter with or without KH propensity.
Black node: alter with KH propensity (i.e., a knowledge hider).
indicates significant parameter estimates in ALAAMs.
To test the hypothesis, the Contagion parameter was estimated using ALAAMs. The results revealed a statistically significant negative contagion effect of KH in both workplace and social communication networks. Specifically, the parameter estimate of the Contagion parameter for the workplace communication network was -2.22, indicating that a team member was about 89% less likely (exp[-2.22] = 11%, 89% less than the 100% baseline probability) to engage in KH when communicating with a knowledge-hiding teammate for work-related purposes. Similarly, in the social communication network, the Contagion parameter estimate was -2.47, suggesting a 91% decrease (exp[-2.47] = 9%, 91% less than the baseline) in the likelihood of KH when communicating with a knowledge hider for social purposes. Thus, our hypothesis was not supported. These estimates, along with all subsequent parameter estimates, satisfied the model convergence criterion, defined as a t-ratio (i.e., the difference between observed and expected statistics divided by the standard deviation) less than 0.1 (Wang et al., 2022).
To address our research question, additional higher-order structural parameters, particularly at the triadic level, were selected and estimated in ALAAMs analysis. The results showed a significant, positive estimate (0.34) of the Popularity (Ego-3Star) parameter in the workplace communication network. This finding indicates that the odds for a team member to conduct KH increased by 41% (exp[0.34] = 141%, 41% more than the baseline) when communicating with three other teammates (regardless of their KH propensities) for work purposes within the team. When estimating the Structural Hole Mixed Attributes parameter in both the workplace and social communication networks, the ALAAM analyses revealed a significantly negative tendency for this structure to occur in the observed networks. Specifically, in the workplace communication network, the parameter estimate was -0.52, which indicates that a team member was 41% less likely (exp[-0.52] = 59%, 41% less than the baseline) to engage in KH when communicating with both a knowledge hider and a non-hider who did not communicate with each other for work purposes. Similarly, this parameter estimate was -0.50 in the social communication network, which suggests that the odds for a team member to conduct KH decreased by 39% (exp[-0.50] = 61%, 39% less than the baseline) when communicating with both a knowledge hider and a non-hider who did not communicate with each other for social purposes. Finally, in the workplace communication network, the Closed Transitivity Mixed Attribute parameter estimate was significantly positive (0.99). This result indicates that a team member was 170% more likely (exp[0.99] = 270%, 170% more than the baseline) to conduct KH when communicating with both a knowledge hider and a non-hider who also communicated with each other for work purposes.
To evaluate the goodness of fit of the model estimations, a Goodness-of-Fit T-ratio (GOFT) was calculated, which assessed how well the model was able to reproduce key structural features of the observed networks. Specifically, T-ratios were calculated by comparing the observed network statistics to the mean statistics obtained from a distribution of simulated networks generated under the fitted model. An absolute GOFT value below 0.1 is generally considered evidence of adequate model fit, indicating that the model effectively captures the underlying patterns in the network data (Robins et al., 2009). Table 4 presents a summary of the ALAAMs parameter estimates along with their corresponding GOFT values.
Discussion
Grounded in social contagion theory, this study employs Autologistic Actor Attribute Models (ALAAMs) to examine whether and how team members’ KH behavior diffuses through their workplace and social communication networks. Analyzing whole-network survey data from 200 employees across 31 organizational teams in the U.S. and China, the results revealed that KH was not simply transmissible through dyadic communication ties. Instead, its diffusion depended critically on the structure of team members’ immediate communication networks: those bridging structural holes between hiders and non-hiders were less likely to engage in KH, whereas members who were centrally connected—either popular among colleagues (communicating with at least three teammates for work purposes) or embedded in a closed triadic structure linking a hider and a non-hider—were more likely to do so.
These findings contribute to social contagion theory and KH research in two primary ways. First, this study shows that contagion is not a uniform, automatic process of interpersonal imitation but depends on structural conditions shaping how individuals interpret and respond to competing behavioral cues. Consistent with Cappella (2017), the mere presence of social networks does not guarantee contagion; norm-violating behaviors like KH may resist dyadic transmission yet still emerge from specific network configurations. This advances social contagion theory by moving beyond interpersonal exposure to highlight the structural and contextual contingencies that can facilitate or hinder behavioral diffusion. Second, this study reinforces the importance of conceptualizing KH as a network-embedded behavior rather than an isolated individual act. Beyond individual traits, team members’ KH behavior reflects their strategic and normative responses to their positions within the immediate communication networks. Structural features such as centrality, structural holes, and triadic closure affect individuals’ exposure to conflicting norms, resource demands, and evaluative pressures, which in turn shape their perceptions of KH as a viable option. In this sense, KH is less a transmissible behavior than a structurally conditioned coping and influence strategy, embedded in the ecology of communication networks. Together, these insights underscore that the diffusion of norm-violating behaviors such as KH cannot be understood solely through dyadic interpersonal influence but must be theorized as the outcome of network-structured opportunity and constraint.
Knowledge Hiding Is Not Contagious
A key finding of this study is that team members’ KH behavior did not appear to diffuse within either the workplace or social communication networks. This absence of social contagion was even more pronounced in social than in workplace communication networks. The lack of diffusion of KH suggests that not all behaviors are equally susceptible to social contagion, likely due to contextual and structural inhibitors, for which several plausible explanations may exist. First, KH is widely perceived as a norm-deviant behavior that violates the collaborative and trust-based norms essential to effective teamwork (Connelly et al., 2012). Exposure to this behavior may elicit a normative counter-response that prompts individuals to reject imitation and engage in compensatory knowledge-sharing behavior to reinforce group norms and affirm their prosocial identity (Peng, 2013). This process aligns with the moral cleansing perspective (Perkins et al., 2024) that suggests individuals who perform or witness norm violations are motivated to reestablish moral order through their own corrective or cooperative actions.
Second, the specific tactics employed by knowledge hiders in this study may further limit the diffusion of KH. The descriptive results indicate that not all KH behaviors were equally common: rationalized hiding (providing an explicit justification for withholding information, often framed as a procedural or confidentiality requirement) was the most prevalent tactic (M = 1.91, SD = 0.91), followed by playing dumb (pretending not to know the requested information; M = 1.48, SD = 0.64) and evasive hiding (giving vague, misleading, or delayed responses to explicitly avoid sharing knowledge; M = 1.45, SD = 0.66). The predominance of rationalized hiding may help explain the absence of contagion effects, as this form of KH can be framed as legitimate or situationally justified (Connelly et al., 2012), leading observers to interpret it as an exception rather than a normative cue and thus reducing the likelihood of imitation. By contrast, more overtly deceptive tactics such as playing dumb or evasive hiding may convey stronger negative social signals (Wasko & Faraj, 2005). However, because these behaviors occur so rarely, they do not form a stable normative pattern and thus have limited potential for contagion.
Lastly, the stronger deterrent effect observed in social communication networks likely reflects the elevated role of informal norms, peer monitoring, and reputational dynamics in these settings. Compared to formal work-related interactions, social communication networks often involve higher levels of affective trust, emotional closeness, and identity-based commitment (Krackhardt & Hanson, 1993). In such environments, individuals are particularly motivated to maintain a positive social image and avoid behaviors that may invite informal sanction, social exclusion, or reputational damage (Ma et al., 2020). Consequently, communicating with knowledge hiders in these networks may activate informal social controls that reinforce collective values and suppress the spread of counterproductive practices.
In short, our finding challenges the core assumption of social contagion theory that behaviors naturally diffuse through communication networks. Instead, it demonstrates that certain behaviors, such as KH, may be inherently resistant to social contagion due to their perceived violation of norms and the social penalties they carry, especially within social communication networks characterized by strong interpersonal ties and informal oversight.
Workplace Connectivity Increases KH
Although this study finds no evidence of a broad contagion effect of KH, the results suggest that its occurrence is contingent on the structural features of networks and the social conditions in which individuals are embedded. Specifically, team members directly connected to three or more colleagues in the workplace communication network demonstrated a significantly higher propensity to engage in KH compared to those with fewer communication ties, which implies a potential threshold at which increased connectivity is associated with higher levels of KH behavior. Notably, this effect was unique to the workplace communication network and did not emerge within the social communication network.
These findings imply that KH diffusion may not solely arise from behavioral mimicry or normative influence but also from the structural pressures associated with central network positions. Social capital theory highlights how individuals in central positions of the network benefit from greater access to information, influence, and social resources (Burt, 2005). However, this elevated visibility can also expose them to increased knowledge requests from colleagues, leading to informational overload and cognitive fatigue (Oldroyd & Morris, 2012). In such contexts, KH may serve as a coping mechanism to manage resource demands and maintain productivity. Resource dependence theory further complements this perspective by emphasizing that individuals in central network positions may strategically withhold knowledge to preserve autonomy and exert control over critical resources (Pfeffer & Salancik, 1978). This behavior is especially prevalent in formal workplace communication networks, characterized by instrumental ties and performance-driven exchanges (Flynn et al., 2006). In contrast, it is less common in social and informal communication networks built on emotional bonds and reciprocity where opportunism is discouraged (Molm, 2010).
Bridging Structural Holes Reduces KH
This study finds that occupying a structural hole, where the ego serves as a bridge between two unconnected alters, can significantly reduce the ego’s tendency to engage in KH. A key condition for this effect to emerge is that the two alters differ in their KH behaviors, with one engaging in KH and the other not. Moreover, this effect is stronger in workplace communication networks than in social communication networks. In contrast, when the ego bridges two unconnected knowledge hiders or non-hiders, occupying a structural hole does not yield a comparable reduction in KH behavior.
These results suggest that network position and behavioral diversity are jointly associated with diffusion outcomes. While traditional contagion theory emphasizes exposure, mimicry, and reinforcement within cohesive clusters (Centola & Macy, 2007), this study points to a complementary pathway: diffusion may also emerge through contrastive exposure in structurally diverse positions. This highlights the role of heterogeneity, alongside cohesion, in shaping diffusion dynamics. When the ego occupies a brokerage role between a knowledge hider and a non-hider, the pronounced contrast between the hider’s KH behavior and the non-hider’s willingness to share knowledge creates informational asymmetry, making each behavioral pattern more salient to the ego. In such contexts, the non-hider’s openness to knowledge sharing becomes not only more visible but also more attractive and normatively appealing, especially in performance-oriented workplace settings where collaboration, transparency, and accountability are institutionally valued (Hansen, 1999). This contrast may trigger a reappraisal of KH as socially costly, which leads the ego to align with the more cooperative behavioral norm.
On the other hand, when the ego bridges two team members who both engage in KH or both refrain from it, the lack of behavioral contrast weakens the reappraisal mechanism. In the absence of a visible alternative, KH may appear normative or at least acceptable within the ego’s immediate network context. Without motivational incentives or informational cues to question the prevailing pattern, the ego is less likely to challenge it, which results in the continued reinforcement and diffusion of KH practices.
Divergent Behaviors in Closed Triads Promote KH
In contrast to the structural hole configuration, this study finds that KH behavior tends to increase when the ego is embedded in a fully connected triad in which both alters communicate with each other but differ in their KH behavior. Specifically, when one alter hides knowledge and the other does not, the ego demonstrates a higher propensity to engage in KH. This transitivity pattern, like the structural hole effect, emerges only within the workplace communication network and not in the social communication network. By comparison, when both alters in the triad exhibit the same behavior, either both hiding or both sharing, the ego’s behavior remains stable, showing no significant increase or decrease in KH.
These findings add nuance to social contagion theory by showing how norm conflict in cohesive structures can disrupt conformity rather than reinforce it. While traditional contagion models emphasize adherence to dominant behavioral norms within cohesive networks (Burt, 1987; Centola & Macy, 2007), exposure to conflicting cues within closed triads—such as one alter hiding knowledge and another sharing—creates normative ambiguity. The visibility and behavioral comparison inherent in such triads make these contradictions salient, increasing uncertainty about appropriate responses. In high-stakes workplace contexts, where time pressures and competition are intense (Argote & Ingram, 2000), this ambiguity often prompts defensive retreat in the form of KH. Consistent with Social Information Processing Theory, which posits that individuals actively observe and interpret social cues to construct meaning and guide behavior in ambiguous contexts (Walther, 1992), egos confronted with mixed signals tend to respond more cautiously and adopt risk-averse strategies rather than simply mimicking dominant behaviors.
Moreover, social comparison theory suggests that individuals embedded in close-knit networks are particularly sensitive to how their behaviors align or deviate from their peers (Garcia et al., 2013). When confronted with conflicting behaviors, the ego often adopts a defensive, self-protective strategy, particularly when one alter’s KH signals that open sharing could create risk or disadvantage. By contrast, when both alters behave consistently, either hiding or sharing, normative clarity emerges, which helps reduce interpretive uncertainty and stabilize the ego’s behavior. This effect is not observed in social communication networks because social settings are more relational and emotionally grounded, making them less susceptible to strategic KH in response to ambiguity. In such environments, conflicting behaviors tend to be perceived as individual style differences rather than as signals of group norms, which exerts less impact on the ego’s behavior.
Reconciling the Paradox: Openness vs. Closure
Although the findings related to structural holes and transitive triads may seem contradictory, a closer examination reveals how different structural configurations may shape the ego’s interpretation of social cues and behavioral norms. On the one hand, structural holes place the ego in a brokerage position between two otherwise unconnected alters, which grants the ego unique access to divergent behavioral cues without the constraints of a tightly knit group (Burt, 1992). This structural openness reduces conformity pressure and allows the ego to evaluate the alters’ behaviors more independently (Garcia et al., 2013). On the other hand, transitive triads embed the ego in a closed structure where all interactions are mutually observable. Such closure typically reinforces conformity through heightened exposure and peer pressure (Walter et al., 2019). When conflicting behaviors coexist, such as one alter engaging in KH while the other does not, the ego faces normative ambiguity and interpretive tension.
Descriptive statistics provide additional context for how these dynamics unfolded in this study. In workplace communication networks, transitive triads far outnumbered structural holes (1,761 transitivity, team M = 56.81, SD = 61.94, vs. 109 structural holes, team M = 3.52, SD = 7.33), indicating that closure was much more common than openness in work-related interactions. In these highly interconnected triads, normative ambiguity arising from conflicting behaviors among alters increased the ego’s perceived uncertainty about appropriate conduct, making defensive KH more likely. By contrast, social communication networks exhibited a more balanced mix of closure and openness (1,098 transitivity, team M = 35.42, SD = 41.81, vs. 322 structural holes, team M = 10.39, SD = 14.71), providing more opportunities for egos to occupy structural hole positions. When bridging two unconnected alters with contrasting KH behaviors, the pronounced behavioral contrast made knowledge sharing more salient and normatively appealing, which helps reduce the ego’s likelihood of KH.
In sum, the apparent paradox between structural holes and closed triads reflects not a contradiction, but a demonstration of how open and closed network configurations shape distinct psychological and behavioral dynamics. Structural holes afford individuals greater autonomy by exposing them to divergent behaviors without the cohesive pressures of a tightly connected group. This openness fosters selective norm adoption through behavioral contrast. In comparison, transitivity structures create closures that amplify exposure to conflicting cues and increase conformity pressure, particularly under normative uncertainty.
Methodological Implications
Unlike its earlier and more widely used counterpart, the Exponential Random Graph Model (ERGM), Autologistic Actor Attribute Models (ALAAMs) are a relatively recent and innovative approach in social network analysis. Since their introduction, ALAAMs have primarily been applied in educational and behavioral science contexts, for example, to model the diffusion of academic performance (Parker et al., 2022), second language communication (Gallagher, 2019), learning descriptive norms about community engagement (Kashima et al., 2013), and social movement participation (Ocelík et al., 2021). However, the application of ALAAMs in organizational and group research remains extremely limited, despite their considerable potential to analyze how communication network structures co-evolve with individual behaviors (Lomi et al., 2011). In communication studies specifically, only one known application exists, focusing on interorganizational networks of civil society organizations rather than on interpersonal communication networks (Sommerfeldt et al., 2023).
This study showcases the methodological strengths of ALAAMs in advancing social contagion theory and social network analysis by capturing how behaviors, such as KH, are shaped not only by peers’ actions but also by local network structures like triadic closure and structural holes. Unlike traditional regression methods, ALAAMs explicitly model endogenous dependencies and behavioral interdependencies within networks (Robins et al., 2001), making them especially suited for analyzing patterned communication within workplace teams. By applying ALAAMs in this context, this research contributes to a growing literature bridging micro-level organizational behaviors with meso-level network structures (Contractor et al., 2006; Kush et al., 2025). It positions ALAAMs as a powerful yet underutilized methodological tool for examining how individuals interpret and respond to social cues embedded in specific network contexts, which helps offer a more integrated understanding of behavioral diffusion in communication networks.
Practical Insights
This research offers practical insights for organizational managers and team leaders seeking to foster knowledge sharing and mitigate counterproductive behaviors such as KH. One encouraging implication is that team members do not appear to readily engage in KH when communicating with others who do. This means managers need not fear a “viral” spread of KH behavior due to a few bad actors (Connelly et al., 2012). Instead, the focus can shift to designing team structures and communication environments that discourage KH and promote knowledge sharing.
One actionable takeaway is the value of promoting structural openness in workplace communication networks. When team members act as bridges between otherwise disconnected colleagues, especially when those colleagues differ in their KH behaviors, they are less likely to hide knowledge themselves. Managers can leverage this finding to identify individuals in brokerage positions and support them in facilitating knowledge sharing. Encouraging these brokers to connect diverse subgroups, along with promoting cross-functional collaboration, informal mentoring, and inter-team projects, can foster transparency. Such practices also help clarify norms and set expectations in dense triads with mixed KH and non-KH behaviors, reducing the likelihood of isolated subcultures where KH is tolerated (Zhao et al., 2016).
However, team cohesion alone is not a safeguard. Fully connected triads, where one member shares openly while another withholds, may create conflicting behavioral cues that increase ambiguity and trigger self-protective behaviors. In such tightly knit groups, leaders must clarify expectations and build psychological safety by reinforcing shared goals, recognizing collaboration, and addressing hidden tensions through regular team debriefs. Additionally, managers should support highly central team members who may hide knowledge not due to contagion, but as a coping response to excessive information demands. Indeed, relationship-oriented leadership that fosters trust and emotional security helps reduce such behavior by encouraging openness and discouraging rationalized or evasive KH (Shen et al., 2025).
Limitations and Future Directions
A major limitation of this study is its reliance on cross-sectional data, which limits our ability to infer causality between network ties and KH, and leaves open the possibility of alternative explanations for our findings. Without a rigorous longitudinal or experimental design, it remains unclear whether network structures drive individuals’ KH behaviors or whether these behaviors shape network formation. For example, the theory of homophily suggests that individuals with similar attributes tend to network with one another (Aral & Nicolaides, 2017). Thus, shared KH or non-KH behavior may facilitate the formation of communication ties. Additionally, active knowledge sharing may make individuals more approachable and popular, which increases their opportunities to bridge structural holes and link otherwise disconnected clusters within the organization. As Christakis and Fowler (2007) emphasize, disentangling these relationships requires longitudinal data capturing both tie formation and attribute changes over time. Although cross-sectional network analysis is common and acceptable in empirical ALAAMs applications, the ideal approach involves collecting data at two time points (Parker et al., 2022), with network data collected before the contagion outcome data. Such an approach enables a more robust examination of the dynamic co-evolution of social networks and individual behaviors (Huisman & Steglich, 2008), particularly how network structures influence actor attributes over time. Therefore, our findings should be interpreted with caution, and future longitudinal and experimental research is needed to strengthen causal claims for the relationship between individual KH behavior and their communication networks.
Another limitation involves the use of self-reported measures of KH. Self-report bias may be particularly pronounced in this context, as KH is generally viewed negatively by peers and can even result in organizational sanctions (Connelly et al., 2012). As a result, participants in this study might have under-reported or denied their engagement in such behavior. Additionally, using the team-level mean to dichotomize KH behavior and communication networks may limit the granularity of behavioral and relational variation. Future research should consider employing alternative data sources or methods such as peer reports, behavioral tracking, or experimental designs, and explore alternative dichotomization strategies to enhance measurement accuracy, capture greater behavioral nuance, and strengthen the robustness of findings. Moreover, because participants were not provided with formal definitions of “work-related” versus “social” communication in the survey, this study relied on respondents’ interpretation to distinguish between these types of communication, which may introduce some measurement imprecision.
Third, while this study focuses on how KH emerges from a team member’s dyadic connections and immediate communication network, future research should explore the potential influence of more distal or macro-level network structures. For example, social contagion theory emphasizes the role of indirect ties (e.g., friends of friends), structural equivalence, and emergent team norms that may transcend direct interpersonal interactions. These broader mechanisms could be particularly relevant in larger teams or loosely connected networks where behavioral influence travels beyond immediate neighbors. Due to the methodological constraints of ALAAMs and the scope of the data, this study was unable to examine these extended pathways. Future studies using alternative modeling techniques such as stochastic actor-based models (Kalish, 2020) or multi-level network approaches (Lubbers, 2003) could offer deeper insights into how KH norms are formed and maintained across broader team or organizational contexts.
Finally, although this study collected multi-level data from organizational teams in both the U.S. and China, it does not specifically examine how KH behaviors vary across teams, organizations, or national boundaries. The data indicated that U.S. team members (M = 1.36, SD = 0.40) reported lower levels of KH than their Chinese counterparts (M = 1.84, SD = 0.65), suggesting that national or cultural contexts may influence KH patterns. A rigorous examination of such effects, however, would require a multilevel modeling framework beyond the current ALAAMs approach. Moreover, the use of convenience sampling entails potential bias and may limit the generalizability of the findings, since the participating teams may not adequately reflect the broader organizational or cultural contexts in either country. A wealth of literature suggests that contextual factors such as team climate, organizational structure, and national cultural characteristics can significantly influence KH practices. For example, Cerne et al. (2014) demonstrated that a team’s psychological safety climate could reduce KH, particularly when leadership promoted openness and trust. Similarly, Babič et al. (2018) explored how national cultural dimensions, such as uncertainty avoidance and cultural tightness, influenced KH behavior in different cultural contexts. Furthermore, Shen et al. (2025) identified power distance as a key cultural variable that moderated the relationship between leadership style and KH. These findings point to the need for future multilevel research that systematically explores how individual, team, organizational, and cultural dynamics intersect to influence KH diffusion across diverse contexts.
Conclusion
Understanding knowledge hiding is essential because it directly affects collaboration, innovation, and trust within organizations (Guo et al., 2022). As interpersonal communication becomes increasingly networked and interdependent in today’s workplace, even subtle acts of KH can ripple through communication networks. This study emphasizes that KH is not merely an individual action, but a socially embedded behavior shaped by social networks and conditionally subject to processes of social contagion. Future research should continue to examine the structural mechanisms and interpersonal dynamics that drive KH, with the goal of designing interventions that promote openness and resilient knowledge-sharing cultures.
Footnotes
Ethical Considerations
The Institutional Review Board (IRB) at the University of Texas at Arlington approved this research (2015-0746) on June 5, 2015. The United States Army Medical Research and Materiel Command (USAMRMC), Office of Research Protections (ORP), Human Research Protection Office (HRPO) approved this research (A-18973) on August 17, 2015.
Consent to Participate
All participants provided written informed consent prior to participating.
Consent for Publication
Not applicable
Funding
The author disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by the United States Army Research Office (Grant W911NF-15-1-0258).
Declaration of Conflicting Interests
The author declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data Availability Statement
The data of the current study are not publicly available in accordance due to agreement with the funding agency. Data are however available from the author upon reasonable request and with permission of the United States Army Research Office.
