Abstract
In the era of data-driven communication, managing one’s online privacy is a necessary, yet burdensome challenge. While individuals have concerns about firms’ data collection practices, they sometimes appear to disclose personal information for relatively small rewards. We demonstrate that privacy cynicism—an attitude toward privacy protection characterized by frustration, hopelessness, and disillusionment—explains this paradox by moderating the relationship between the appraisal of privacy threats and privacy coping behaviors on one side, and privacy protection behaviors on the other side. Results of a U.S. national survey (N = 993) show that privacy cynicism is negatively related to privacy protection behaviors and significantly moderates relationships of perceived vulnerability, response efficacy, disclosure benefits, and response costs on protection behaviors. Hence, this work has important implications for communication theory by extending existing models of privacy management behaviors, as well as for communication practice, by stressing the importance of creating awareness about privacy cynicism.
Keywords
In the era of data-driven communication, institutions, firms, and individuals can reap the benefits of new information technologies (e.g., increased relevance of content and increased time efficiency). However, as privacy-invasive data collection practices and data breaches have become a widespread phenomenon, the management and control of individuals’ online privacy has become an ongoing and burdensome challenge. Individuals need to keep investing significant effort into managing their online privacy (e.g., by reading extensive privacy policies); however, these efforts seldom appear to adequately inform them or protect their online privacy (cf. Acquisti et al., 2015; Hargittai & Marwick, 2016; Van Ooijen & Vrabec, 2019). Despite the apparent ease with which individuals often seem to disclose their information in exchange for being able to use online services (i.e., Carrascal et al., 2013; see also Kokolakis, 2017), individuals worry about their privacy. For instance, when individuals realize that organizations target them with messages that are based on their personal data, this may result in distrust toward the firm, as well as feelings of vulnerability (Aguirre et al., 2015), intrusiveness (Van Doorn & Hoekstra, 2013), and surveillance (Segijn & Van Ooijen, 2020). Nonetheless, individuals seem to take minimal action vis-à-vis the protection of their online privacy, such as turning off (tracking) cookies, restricting location-based services, and/or changing privacy-invasive default settings on websites (Boerman et al., 2021).
This phenomenon of diverging privacy attitudes and privacy concerns on one side and privacy behaviors on the other side is also known as the privacy paradox and has been studied extensively (Barnes, 2006; Brown, 2001; Dienlin & Trepte, 2015; Kokolakis, 2017; Norberg et al., 2007). The evidence for the existence of the privacy paradox in terms of the absence of a direct link between privacy attitudes and behaviors is mixed (for reviews, see Baruh et al., 2017; Kokolakis, 2017). As concluded by Kokolakis (2017), researchers have explained the (absence of the) privacy paradox, or more generally individuals’ (lack of) privacy protection behavior by taking into account, for instance, the role of a rational risk–benefit assessment (e.g., Dinev & Hart, 2006; Xu et al., 2011), social structures (e.g., social norms related to disclosure; Nissenbaum, 2004; Zafeiropoulou et al., 2013), cognitive biases and heuristics (e.g., Acquisti & Grossklags, 2003; Brandimarte et al., 2013; Van Ooijen, in press), disclosure context (e.g., the use of social network sites vs. usage of online services; Baruh et al., 2017), information asymmetry (Buck et al., 2014), and/or perceptions of ways to cope with privacy threats (Boerman et al., 2021; Ham, 2017; Lee et al., 2013; Mousavi et al., 2020; Wottrich et al., 2019). These studies, however, do not account for a recent phenomenon that inhibits privacy protection behavior among Internet users—that is, privacy cynicism (Hoffmann et al., 2016; Lutz et al., 2020).
In the era of Big Data, it has become challenging for individuals to participate in online environments while safeguarding their privacy. In response to this challenge, Internet users may develop a cynical attitude toward privacy protection as a coping mechanism that strengthens the divergence between their privacy concerns and their data disclosure behaviors. We pose that privacy cynicism may be an important explanation for individuals’ lack of privacy protection behavior. As individuals increasingly lose control of their personal information in the expanding contemporary online environment, privacy cynicism may become an important reason that privacy attitudes and behaviors diverge. Recent work on privacy cynicism indicates that privacy cynicism may directly decrease the extent to which individuals protect their online privacy (Choi et al., 2018; Hoffmann et al., 2016; Lutz et al., 2020). In the current work, we take a different approach by arguing that privacy cynicism moderates the decision process that determines privacy behaviors.
We examine the privacy decision-making process by using Protection Motivation Theory (PMT; Maddux & Rogers, 1983; Rogers, 1975) as a theoretical framework. PMT states that protection behaviors are a result of the judgment of a privacy threat (i.e., threat appraisal) and the judgment of how well a person can cope with that privacy threat (i.e., coping appraisal). In the current work we pose that high levels of privacy cynicism within individuals may explain why the known antecedents of protection behaviors (Maddux & Rogers, 1983) might not result in actual privacy protection behaviors. Specifically, we propose that the extent to which the appraisal of a privacy threat and the coping appraisal for dealing with that threat result in privacy protection behaviors is different for highly privacy-cynical individuals.
Recent studies that use PMT to explain privacy behaviors find mixed evidence on how well the threat and coping appraisal predict protection behavior (cf. Boerman et al., 2021; Ham, 2017; Mousavi et al., 2020; Wottrich et al., 2019). Therefore, the aim of this study is to examine whether privacy cynicism may help to explain these discrepancies in the literature. Considering the role of privacy cynicism as a justification mechanism that prevents individuals from acting against experienced privacy threats (Hoffmann et al., 2016), we examine the moderating role of privacy cynicism in the decision-making process that ultimately leads to privacy protection behaviors. Specifically, we examine how privacy cynicism moderates the relationship between perceptions of privacy threats and perceptions of privacy coping behaviors on one side, and actual privacy protection behaviors on the other side. We examine this notion in the context of personalized communication (i.e., where individuals are confronted with the collection and usage of their data for the purpose of presenting them with personalized advertisements).
This research contributes to the communication literature in three ways. First, an increasing number of messages are personalized to their target audience, such as in personalized advertising (Aguirre et al., 2015), political microtargeting (Zarouali et al., 2020), and health tailoring (Bol et al., 2020). Therefore, it is important to advance knowledge on how individuals respond to such (invasive) personalization techniques. By examining privacy cynicism as a moderating variable of the privacy decision-making process, we increase our knowledge on why individuals (do not) protect their online privacy. Second, current research into privacy decision-making finds contradictory results. For example, although Mousavi et al. (2020) find that vulnerability and self-efficacy predict privacy protection behaviors, Boerman et al. (2021) find that those factors have no effect on privacy protection. Privacy cynicism could potentially explain these contradictory results. Finally, by introducing privacy cynicism as a moderator of the antecedents of privacy protection behavior, we provide an explanation for the diverging privacy attitudes and behaviors (i.e., the privacy paradox). As examined by Kokolakis (2017) in a comprehensive review, the relationship between privacy attitudes and privacy behaviors is absent or weak at best. This work will provide an explanation to this privacy paradox, by examining to what extent privacy cynicism moderates the effect of antecedents that inhibit or increase data disclosure, such as perceived vulnerability to privacy threats, perceived severity of privacy threats, and privacy self-efficacy (Maddux & Rogers, 1983; Rogers, 1975).
Understanding the role of privacy cynicism in privacy decision-making also is of societal importance because awareness about the role of privacy cynicism in privacy behaviors may help children and adults in protecting their own privacy. That is, when privacy cynicism turns out to be a (moderating) determinant of the mechanism that predicts privacy protection behavior, educational programs could aim more at decreasing privacy cynicism, instead of merely informing individuals on how they should protect their privacy (see also Park, 2013; Segijn et al., 2021). Privacy cynicism might arise especially in the context of “data capitalism” by large institutions, such as Google or Facebook (see also Hoffmann et al., 2016; Lutz et al., 2020). Since the power of such institutions is growing and individuals increasingly lose control of their personal information in such expanding online environments, privacy cynicism may become an increasingly important phenomenon and driver of privacy behaviors.
Theoretical Framework
Privacy Cynicism
Hoffmann et al. (2016) introduced the concept of privacy cynicism as “an attitude of uncertainty, powerlessness, and mistrust toward the handling of personal data by digital platforms, rendering privacy protection subjectively futile.” As argued by the authors, cynicism entails an individual’s assumption that the other party is motivated by self-interests that are different from one’s own and might take disadvantage of or mislead the individual. Privacy-cynical individuals may, instead of protecting their privacy, develop such attitudes to cope with the specific challenges of (institutional) privacy threats (Lutz et al., 2020). They tend to engage in (privacy) risks while not trusting the company that is collecting their data but at the same time grant that party access to their data. In their qualitative panel study, Hoffmann et al. (2016) found privacy cynical participants stating that privacy protection is futile and that this caused them to engage in open or even careless self-disclosure practices. For instance, it was argued that “It’s illogical to think that you can somehow obfuscate your digital footprint given the number of activities we do online. You would have to become some kind of dropout living in the mountains.” (p. 7). Hence, privacy cynical participants justified to themselves that they did not attempt to protect their privacy, illustrating the role of privacy cynicism as a coping mechanism. Therefore, privacy cynicism may be one of the explanations of the incongruence between privacy attitudes and concerns and privacy behaviors (Barnes, 2006; Kokolakis, 2017; Lutz et al., 2020).
Although privacy cynicism is a relatively new construct, mechanisms similar to privacy cynicism have been described in the literature before. For instance, Dencik and Cable (2017) describe the concept of surveillance realism, which is defined as “a simultaneous unease among citizens with data collection alongside the active normalization of surveillance that limits the possibilities of enacting modes of citizenship and of imagining alternatives.” Moreover, Hargittai and Marwick (2016) used focus group data to analyze individuals’ privacy protection behaviors and introduce the concept of privacy apathy to describe the lack of individuals’ privacy protection behaviors. According to the authors, individuals express privacy apathy by an attitude of resignation about privacy violations. For instance, one participant stated “I feel like [pause], then you have the choice between not using the Internet and therefore keeping free of the surveillance, or living with it. So, I do care [about privacy]; but I guess I don’t care enough not to use the Internet. And I’m not sure what the alternative is at the moment.” (p. 3751). However, despite that some participants came across as “quite cynical” (p. 3751), participants were still motivated to protect their privacy while expressing privacy apathy—an attitude that the authors describe as “resigned pragmatism” (p. 3752; see also Draper & Turow, 2019). Privacy resignation is also seen as one of the dimensions of privacy cynicism (Hoffmann et al., 2016; Lutz et al., 2020). Lutz et al. (2020) found a negative relationship between the attitude of resignation and privacy protection behaviors, indicating that an attitude of resignation toward privacy is “capable of preventing users to act on their concerns” (p. 1128). Choi et al. (2018) were the first to measure the concept of privacy cynicism in a survey-based study and defined cynicism as “an attitude toward [privacy] that is characterized by frustration, hopelessness, and disillusionment” (p. 43). They examined the influence of privacy fatigue – a related construct consisting of the core component of privacy cynicism and emotional exhaustion—on intentions to disclose personal data among Korean respondents. They found that privacy fatigue predicts individuals’ intention to disclose information and that a high level of fatigue can even partly explain the weak relationship between concerns about privacy and intentions to disclose information. When privacy fatigue (i.e., cynicism) is high, the negative relationship between privacy concerns and disclosure intention becomes weaker. These findings suggest that even when individuals are concerned about their privacy, privacy cynicism may prevent them from taking action, thus making privacy cynicism a so-called buffering or contributory moderator (see Andersson et al., 2020; Holbert & Park, 2020). That is, privacy concerns may affect privacy protection behaviors differently for individuals high and low in privacy cynicism. Additionally, Segijn and Van Ooijen (2020) measured privacy cynicism using Choi et al.’s (2018) developed scale in a survey-based U.S. study and found that individuals’ privacy cynicism is related to an increased acceptance of online privacy-invasive practices, such as online profiling, location-based communication, and watermarking. This indicates the importance of privacy cynicism in collection of people’s personal information.
Protection Motivation Theory
This study examines the role of privacy cynicism in the decision-making process that ultimately leads to privacy protection behaviors by using Protection Motivation Theory. Privacy is defined as the “selective control of access to the self” (Altman, 1975, p. 18), whereby controlling access to the self is characterized by a process in which individuals determine the boundaries of information disclosure in their interactions with others. According to Protection Motivation Theory (PMT; Maddux & Rogers, 1983; Rogers, 1975), whether individuals protect their privacy in a possible privacy-threatening situation is dependent on their appraisal of the privacy threat (i.e., the judgment of how privacy threatening the situation is where one discloses personal data in order to be able to use online services), as well as their coping appraisal in that specific situation (i.e., how well one feels able to prevent that one’s personal data will be collected by companies). Specifically, the threat appraisal comprises the perceived severity or “noxiousness” of the threat (i.e., how harmful to the self the outcome of the privacy threat is), as well as the vulnerability to the threat in terms of the likelihood of its occurrence (i.e., how likely the perceived risk is that one’s privacy is compromised) and is according to PMT negatively affected by the benefits that are associated with data disclosure behavior (i.e., being able to use online services). In contrast, the coping appraisal is positively affected by an individual’s self-efficacy and response efficacy. While self-efficacy is the individual’s belief that they are personally able (i.e., have the skills) to execute the necessary actions to protect their online privacy, response efficacy is their belief that certain actions will generally be effective in removing the threat (i.e., whether installing an ad-blocker can be considered as an effective remedy). In addition, the response costs of executing the privacy protective actions (e.g., in terms of time and effort) negatively influence the coping appraisal according to PMT (see Figure 1; Maddux & Rogers, 1983).
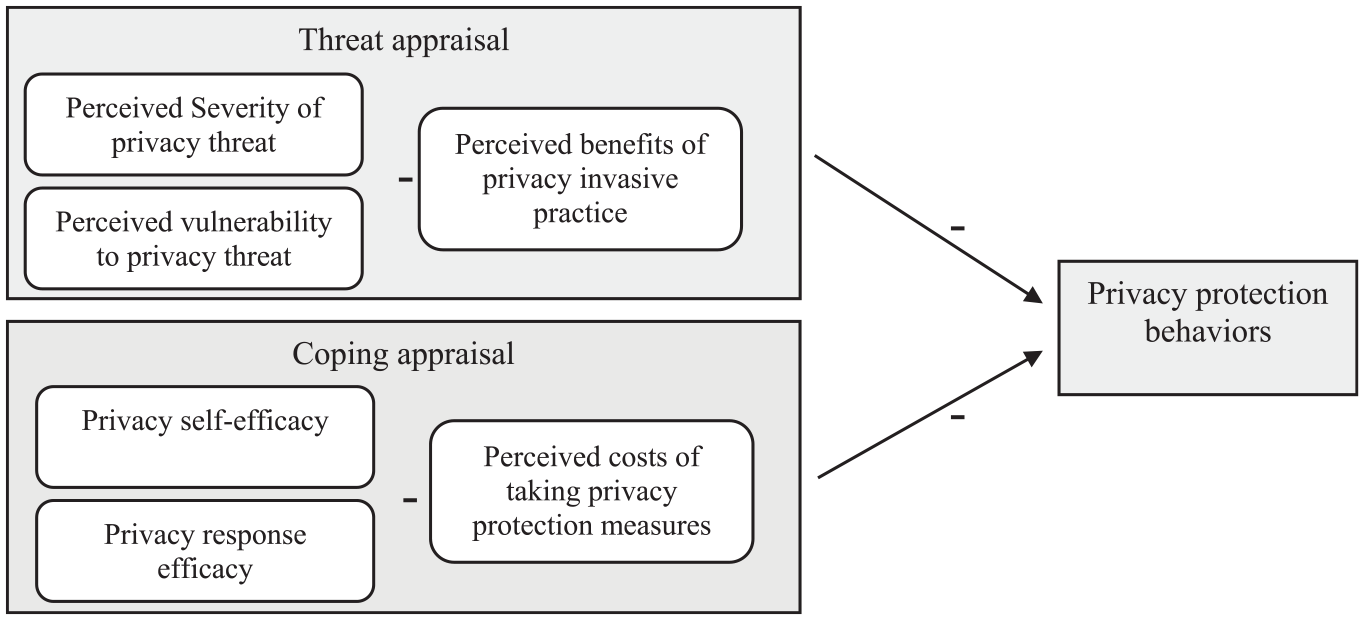
Protection motivation theory applied to online privacy protection behaviors.
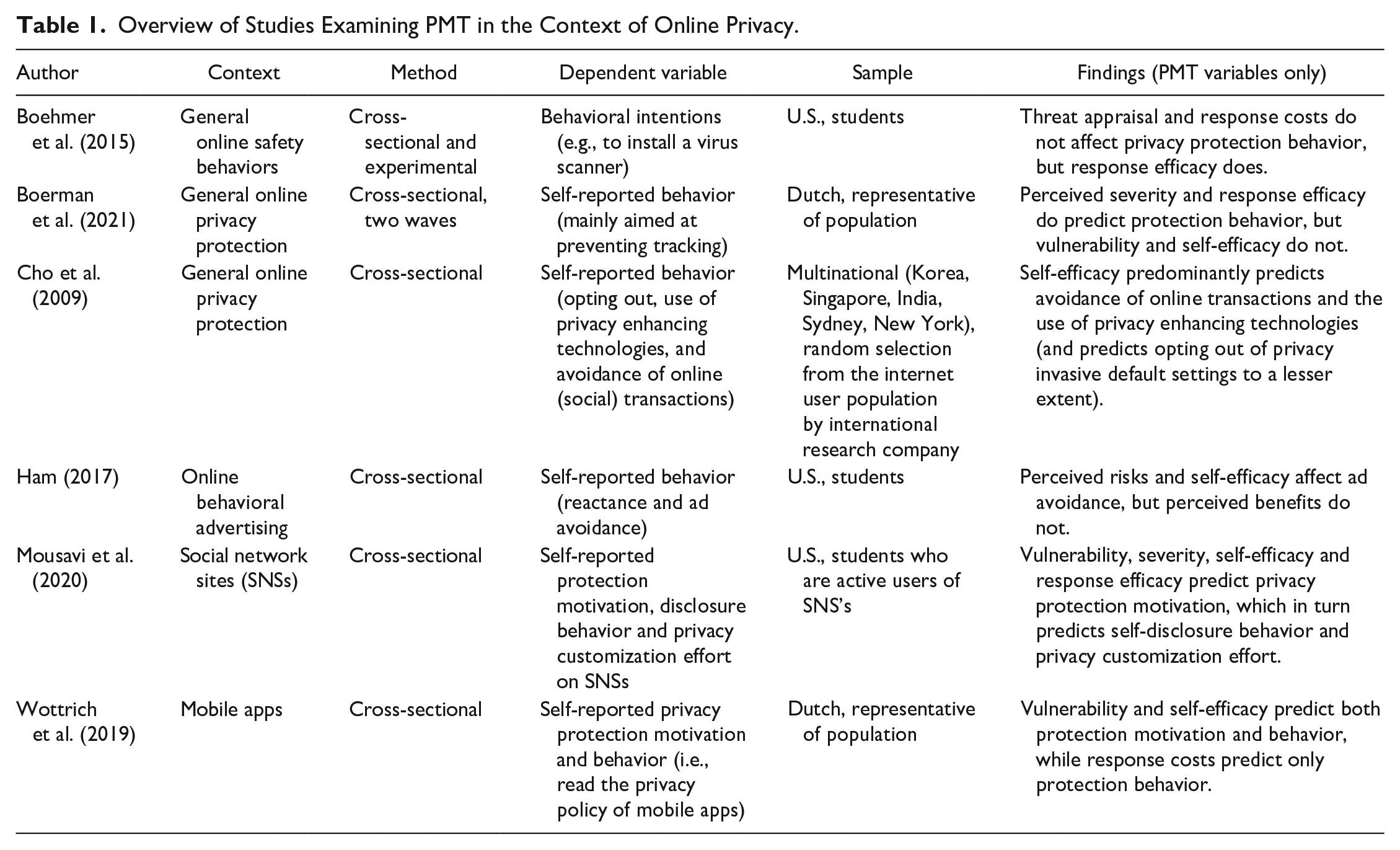
Scholars have applied PMT to study various questions related to privacy protection behaviors (Boehmer et al., 2015; Boerman et al., 2021; Cho et al., 2009; Mousavi et al., 2020; Wottrich et al., 2019). For example, Mousavi et al. (2020) 9 used PMT to examine the antecedents of information disclosure on social network sites, Wottrich et al. (2019) applied PMT in the context of mobile apps, Boerman et al. (2021) used PMT to predict online privacy related behaviors (e.g., installing ad-blockers, blocking cookies), and Ham (2017) applied PMT to predict ad avoidance. However, most of these studies have not tested the full model and have omitted predictors from the model when applying PMT to privacy protection models. Mousavi et al. (2020) did not include perceived benefits of disclosing information and response cost of protecting personal information, and Wottrich et al. (2019) omitted response efficacy from the model, while privacy knowledge was included as an additional predictor. Boerman et al. (2021) also omitted perceived benefits and response costs from the model. In addition, Ham (2017) confirmed that severity, benefits, and self-efficacy affected privacy protection behavior, but omitted vulnerability and response efficacy from their model.
Moreover, these studies found contradictory results regarding the effects of specific PMT antecedents. For example, Mousavi et al. (2020) found evidence in a U.S. student sample that threat appraisal (i.e., severity and vulnerability) and coping appraisal (i.e., self-efficacy and response efficacy) influence protection motivation and actual disclosure behaviors. Similarly, Ham (2017) demonstrated in a U.S. student sample that vulnerability, benefits, and self-efficacy influence privacy protection behavior. However, Boerman et al. (2021) found in a Dutch representative sample that although the threat appraisal was generally high in their study (i.e., individuals perceived the collection of their personal data as a threat to which they were susceptible), the coping appraisal for dealing with the privacy threat was less than optimal (i.e., individuals experienced low self-efficacy in dealing with the threat). Furthermore, although Boerman et al. (2021) found that perceived severity and response efficacy affected privacy protection behaviors, vulnerability, and self-efficacy did not influence protection behavior. This contrasts with the results of research by Wottrich et al. (2019), who found in a Dutch representative sample that in the context of mobile apps, perceived severity and self-efficacy were the strongest predictors of both privacy protection motivation and actual privacy protection behaviors. Possibly, the different characteristics of each of these studies might affect the extent to which the threat and coping appraisals influence privacy protection behaviors (See Table 1 for a more extensive overview of the (methodological) differences between these studies). For example, the difference could be explained by the type of sample (student vs. general sample), given that students are more homogenous and younger people seem to be more accepting of data collection practices (Segijn & Van Ooijen, 2020). However, privacy cynicism may partly explain the mixed results in the literature to date. For instance, while vulnerability and self-efficacy affect privacy protection behaviors in some studies (Ham, 2017; Mousavi et al., 2020; Wottrich et al., 2019), Boerman et al. (2021) found no effects of vulnerability and self-efficacy on privacy protection behaviors. Possibly, the level of privacy cynicism—which may be dependent on contextual as well as individual factors—might determine the effects of PMT’s antecedents on privacy protection behaviors.
Overview of Studies Examining PMT in the Context of Online Privacy.
Privacy Cynicism and its Relation to Privacy Protection Behaviors
Considering the role of privacy cynicism as a justification mechanism that prevents individuals from acting against experienced privacy threats (Hoffmann et al., 2016), we ask to what extent privacy cynicism might determine the decision-making process that ultimately leads to privacy protection behaviors (e.g., blocking cookies, altering default privacy preferences, reading privacy policies, etc.). In line with Lutz (2020), who find support for a negative effect of privacy cynicism on self-reported privacy protection behaviors, and Choi et al. (2018), who demonstrate that privacy cynicism negatively predicts intentions to protect one’s online privacy, we expect that higher levels of privacy cynicism negatively predict self-reported privacy protection behaviors (H1). Moreover, we predict that privacy cynicism moderates the relationship between the threat appraisal and coping appraisal on privacy protection behaviors. We will first discuss how privacy cynicism might determine the threat appraisal (i.e., severity, vulnerability, and benefits; H2a–H2c) before discussing how it might determine the coping appraisal (i.e., self-efficacy, response efficacy, and costs; H3a–H3c).
Previous research has found that severity—an individual’s belief about the seriousness (Witte, 1992) or “noxiousness” of the threat (Maddux & Rogers, 1983)—increases privacy protection behaviors (Boerman et al., 2021; Mousavi et al., 2020). In the online environment, individuals might perceive a privacy threat to be severe when they perceive that the collection and usage of their personal data might have negative consequences for them (for instance, their data might be misused for purposes that were unintended by the individual). Although individuals might feel that a privacy threat is severe because it intrudes on their personal space, privacy cynicism might prevent them from acting on these perceptions, as cynical individuals might think that privacy protection is ultimately futile. As cynicism functions as a coping mechanism, it might support “inaction in the face of potentially harmful circumstances” (Lutz et al., 2020, p. 1174). Therefore, we expect that the positive relationship between severity and privacy protection behavior is weaker when cynicism is high (H2a).
Similarly, vulnerability –the perceived likelihood that a privacy threat will occur—is likely to be positively related to privacy protection behaviors, according to PMT literature (Boerman et al., 2021; Cho et al., 2009; Maddux & Rogers, 1983). However, when individuals are highly cynical about their ability to protect their privacy, even a high-risk threat might result in individuals disclosing their information. Similar as for severity, cynicism might act as a coping mechanism as it is argued to result in an attitude of resignation with regards to the inevitable privacy risks in the online environment (Hoffmann et al., 2016; Lutz et al., 2020). Therefore, we expect that the positive relationship between vulnerability and data protection behavior will be weaker when individuals are more cynical about online privacy (H2b).
Regarding the use of privacy-invasive online services, when the perceived benefits of data disclosure are high, the advantages of data disclosure should be higher compared to when perceived benefits are low, which should decrease privacy protection behaviors. Benefits in PMT refer to the rewards that individuals expect to gain by disclosing their personal information (i.e., being able to use certain services or apps; Ham, 2017; Phelps et al., 2000). As argued by Ham (2017), higher perceived benefits might reduce the motivations for privacy protection. In addition, when individuals are highly privacy cynical, they might be less motivated to scrutinize the cons and pros of data disclosure and hence they might be inclined less to weigh the benefits of data disclosure critically (i.e., also small perceived benefits might result in data disclosure). For less cynical individuals, critically evaluating the benefits (and cons) of data disclosure might still be perceived as a worthwhile enterprise. Therefore, we expect that the negative relationship between benefits and privacy protection behavior will be stronger for less cynical individuals as opposed to more cynical individuals (H2c).
We also expect privacy cynicism to moderate the influence of the coping appraisal on privacy protection behavior. According to PMT, higher levels of self-efficacy and response efficacy are associated with more (privacy) protection behavior. In the context of privacy behaviors, it has been established that higher levels of response efficacy predict more privacy protection behavior. When people perceive privacy protective measures to be generally effective for privacy protection (i.e., high response efficacy), this seems to increase their privacy protection behaviors (Boehmer et al., 2015; Boerman et al., 2021; Mousavi et al., 2020; Wottrich et al., 2019).
Similarly, positive relations between self-efficacy—the belief that one personally has the skills to perform privacy protection behaviors—have also shown to be positively related to privacy protection (Cho et al., 2009; Ham, 2017; Mousavi et al., 2020; Wottrich et al., 2019; but see Boerman et al., 2021 for an exception). However, when individuals are highly frustrated, and disillusioned about their online privacy (i.e., highly cynical), their levels of privacy protection behavior may be low; this even applies to those individuals who believe they have the personal skills to take privacy protective actions (such as being able to install software that blocks tracking) and individuals who feel that taking certain privacy protective measures are effective (response efficacy). Even when people think they can effectively manage their privacy, their lack of motivation could prevent them from taking action (Segijn et al., 2021). Based on this argumentation, we expect that the effect of self-efficacy (H3a) and response-efficacy (H3b) is conditional. Specifically, we expect that both self-efficacy and response efficacy affect privacy protection behaviors, but not when privacy cynicism is high.
Finally, individuals who experience more response costs for dealing with the privacy threat are less likely to engage in privacy protection behavior compared to individuals who experience less response costs. However, highly cynical individuals are expected to feel that privacy protection is ultimately futile, even if it costs them little time or effort. That is, privacy-cynical individuals have an attitude characterized by frustration, hopelessness, or disillusionment toward privacy protection behavior, even if they feel that the time and effort that it takes to perform behaviors with the aim to protect their privacy are reasonable. Therefore, we expect that highly cynical individuals might refrain from protecting their privacy anyway—even if the response costs are low. Hence, we predict that the negative relationship between response costs and privacy protection behavior is weaker for highly cynical individuals (H3c).
In summary, we argue that privacy cynicism negatively moderates the relationships between severity, vulnerability, self-efficacy, and response efficacy and privacy protection behavior, and positively moderates the relationships between the perceived benefits of data disclosure and the response costs, and privacy protection behavior (see Figure 2 for the conceptual model).
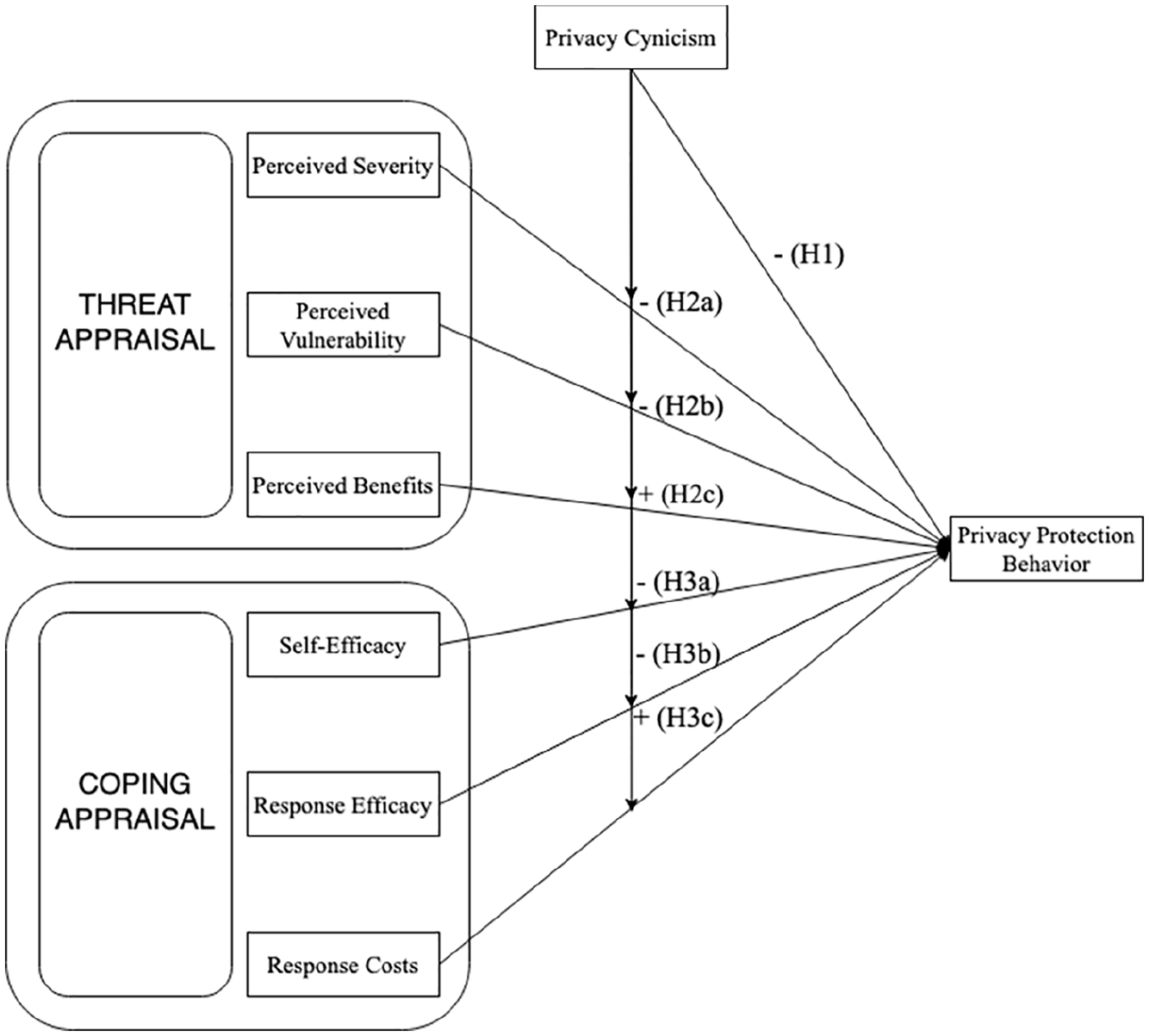
Conceptual model.
Method
Sample
Once ethical approval was obtained from the large Midwestern university, an online survey was distributed via the Dynata (previously known as ResearchNow or Survey Sampling International) online panel in Spring 2019. The sample was balanced by age (18+), gender, ethnicity, and census region (U.S.). Each respondent received an incentive with a value of $1.25 through the panel company for completing the questionnaire. In total, 1,362 U.S. participants completed the survey. Of these participants, 1,008 passed at least three of the four attention checks 1 , and 993 respondents subsequently completed all the questions pertaining to privacy protection behavior, threat appraisal, coping appraisal, and privacy cynicism. These respondents were included in our final sample, which is comparable to Census Figures. However, our sample is slightly higher educated (Table 2).
Demographics of the Final Sample (N = 993).
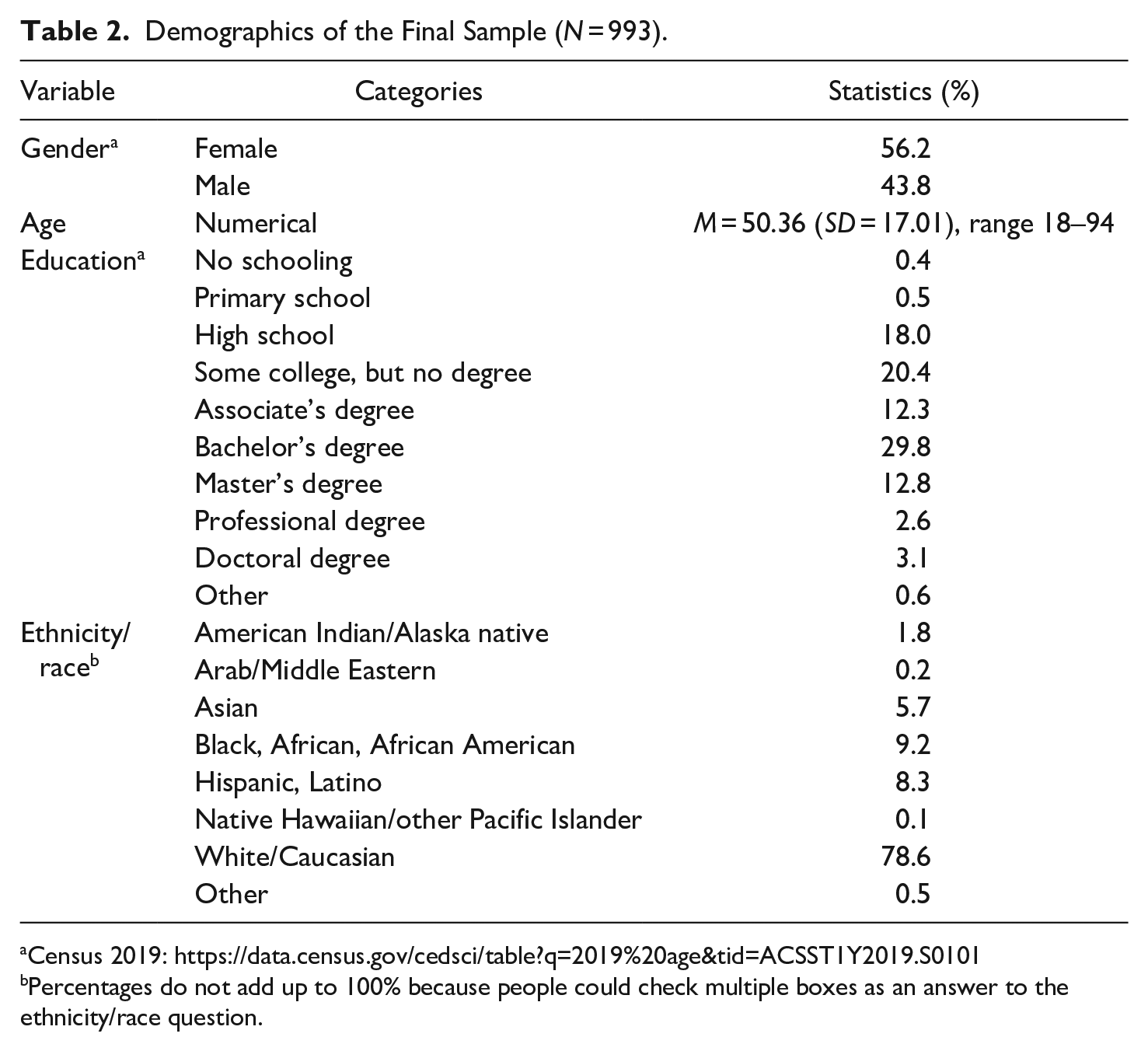
Percentages do not add up to 100% because people could check multiple boxes as an answer to the ethnicity/race question.
Procedure
The participants were informed about the nature of the study and their right to withdraw from participation at any time; they were also assured that their data would be anonymized. Upon granting consent to participate, the respondents were informed that “The questionnaire concerns questions about the perceptions of the participant. There are no right or wrong answers. We are interested in your opinion.” They were subsequently informed that “Personalization means the creation, modification, and adaption of content to optimize the fit of the message with you as a person.” Moreover, the following explanation was provided: The term “personal data” refers to any kind of online data about individuals, including demographic information, but also behavioral data, such as website visits, location data, and social media activity, as well as data about your personal interests. When you visit websites or use apps (e.g., Facebook or a news website), companies might collect your personal data with the purpose of providing you with personalized advertisements.
Subsequently, participants answered questions that were part of the scales measuring the threat appraisal (vulnerability, severity, and benefits), the response appraisal (self-efficacy, response efficacy, and response costs) and privacy cynicism. Finally, respondents were asked to fill out demographic questions regarding their gender and age, and were thanked for their participation upon completion.
Measurements
Vulnerability was measured by a 5-item scale (Dinev & Hart, 2006) asking the respondents “How likely are the following situations, do you think”? Participants were asked to indicate to what extent they felt it was likely that a number of undesirable situations occurred that related to the possible misuse of their data (e.g., “My personal data could be used in ways I do not foresee”; 1 = extremely unlikely–7 = extremely likely).
Subsequently, severity was measured by a 5-item scale asking respondents “When I realize that online companies and advertising agencies have collected and use personal information about me, I feel [. . .]” (i.e., exposed; unprotected, unsafe; susceptible; vulnerable; 1 = not at all, 7 = very much; Aguirre et al., 2015).
Respondents’ self-efficacy and response efficacy pertaining to online privacy protection behaviors was measured using scales based on Herath and Rao (2009); for example, “I feel I have the skills to take measures to protect by online privacy by myself” (self-efficacy; 3 items); “I feel that following the available guidelines for protecting my online privacy would be effective to actually protect it” (response efficacy; 4 items); 1 = not at all–7 = very much).
Perceived benefits were measured using a 3-item scale that was constructed by the authors. Participants were asked “To what extent do you disagree/agree with the following statements?” (e.g., “I find it useful that ads shown on my devices are personalized to my interests”; 1 = strongly disagree–7 = strongly agree; for an overview of all items, see Table 3).
Measurement Scales.
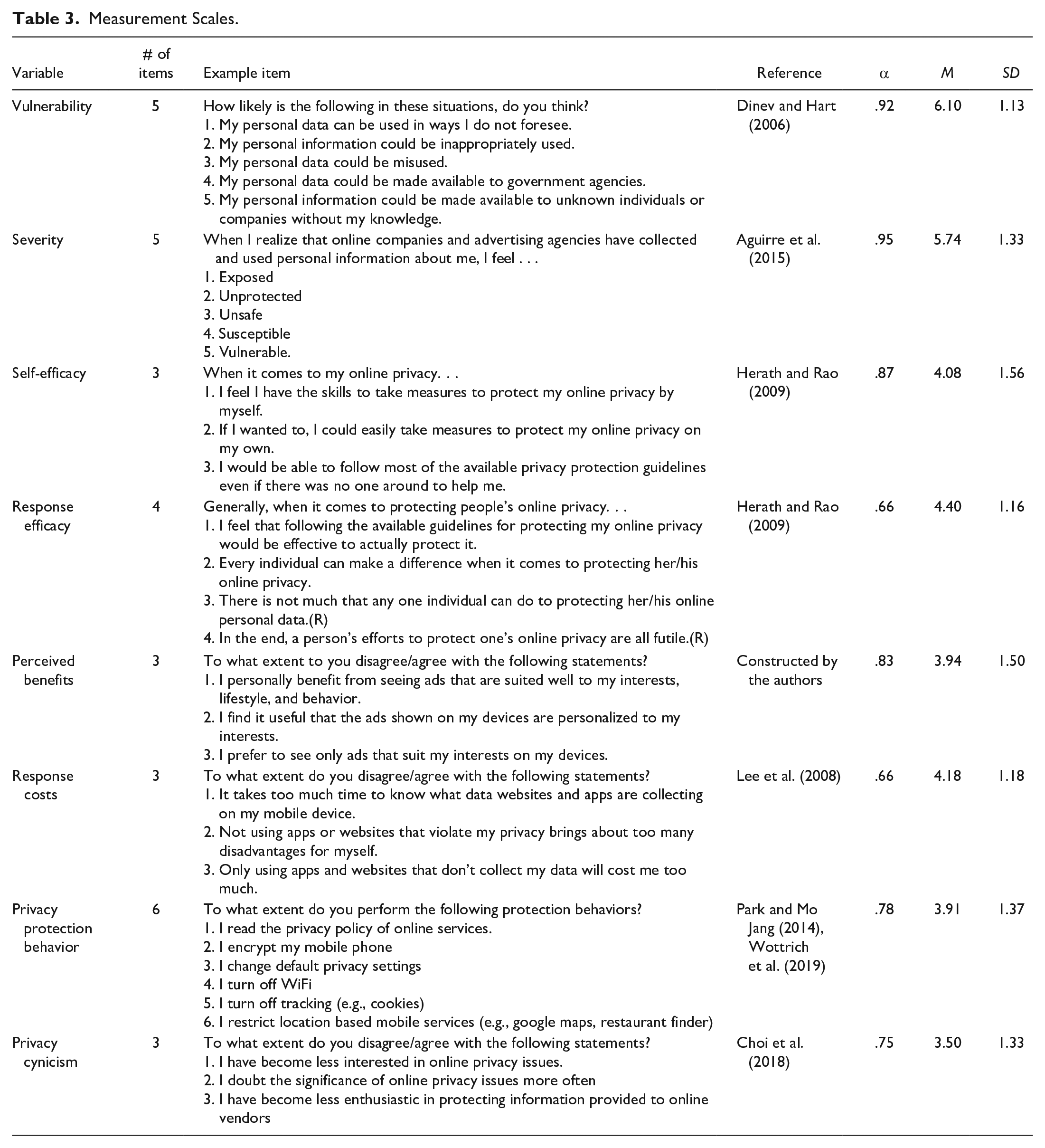
Response costs were measured using a 3-item scale based on Lee et al. (2008); for example, “It takes too much time to know what data websites and apps are collecting on my mobile device”; 1 = strongly disagree–7 = strongly agree).
To measure privacy protection behaviors, participants were asked to indicate how often they engaged in six types of online privacy protection behaviors (based on Park & Mo Jang, 2014; Wottrich et al., 2019; e.g., “I turn off tracking cookies”; 1 = never–7 = all the time).
Privacy cynicism was measured using 3 items (Choi et al., 2018; e.g., “I doubt the significance of online privacy issues more often”; 1 = strongly disagree–7 = strongly agree).
For an overview of all the scales including scale statistics, see Table 3. A correlation matrix is provided in Appendix 1.
Analytical Procedure
The model was tested using structural equation modeling in Amos 25 in two consecutive steps. First, considering potential cross-loadings between the concepts in the model and to establish whether the concepts fit the data well, we tested a measurement model in which all the concepts (i.e., perceived severity, perceived vulnerability, perceived benefits, self-efficacy, response efficacy, response costs, privacy cynicism, and privacy protection behavior) were modeled as correlated latent variables. The measurement model had a good fit to the data: χ2 (DF = 436, N = 993) = 1,658.931, CMIN/DF = 3.805, CFI = .928, and RMSEA = .053 (see guidelines by Kline, 2015). All items had a significant factor loading with p < .000 on their designated factor. Furthermore, an inspection of the modification indices revealed that none of the items was associated with another factor.
Second, based on the results above, we designed and tested our model according to the manifest variables. We computed the centered scores for all the concepts, except privacy protection behavior. We then made six interaction variables by multiplying the participants’ centered scores for privacy cynicism with their centered scores for perceived severity, perceived vulnerability, perceived benefits, self-efficacy, response efficacy, and response costs, respectively. Considering the relationship between the demographic variables age (e.g., Joinson et al., 2010; Li, 2011; Zhang et al., 2002) and gender (e.g., Hoy & Milne, 2010; Janda, 2008; Li, 2011) and privacy protection behaviors in the literature, we decided to add age and gender as control variables. Therefore, the demographic variables age and gender were included as exogenous control variables and used as predictors for the centered variables for perceived severity, perceived vulnerability, perceived benefits, self-efficacy, response efficacy, response costs, and privacy cynicism, as well as for the six interaction variables and privacy protection behavior. Furthermore, the centered scores for perceived severity, perceived vulnerability, perceived benefits, self-efficacy, response efficacy, response costs, and privacy cynicism, as well as the interaction variables, were also used as predictors of privacy protection behavior. The scores for gender and age were allowed to correlate with each of the variables in the conceptual model, and each interaction variable was allowed to be correlated with the two centered variables on which it was based. Like the measurement model, this structural model had a good fit to the data: χ2 (DF = 30, N = 993) = 120.134, CMIN/DF = 4.004, CFI = .966, and RMSEA = .055. In the results section below, we elaborate on the standardized effects that were observed within this model, providing the sample estimate along with the results of a bootstrap analysis of 1,000 samples, for which a 95% confidence interval was obtained.
Results
After providing an overview of the direct relationships between perceived severity, perceived vulnerability, perceived benefits, self-efficacy, response efficacy, response costs, and privacy cynicism on one side and privacy protection behavior on the other side, we will discuss the moderating role of privacy cynicism on each of the six variables and provide plots for the significant interaction effects to interpret the moderation effects that were present.
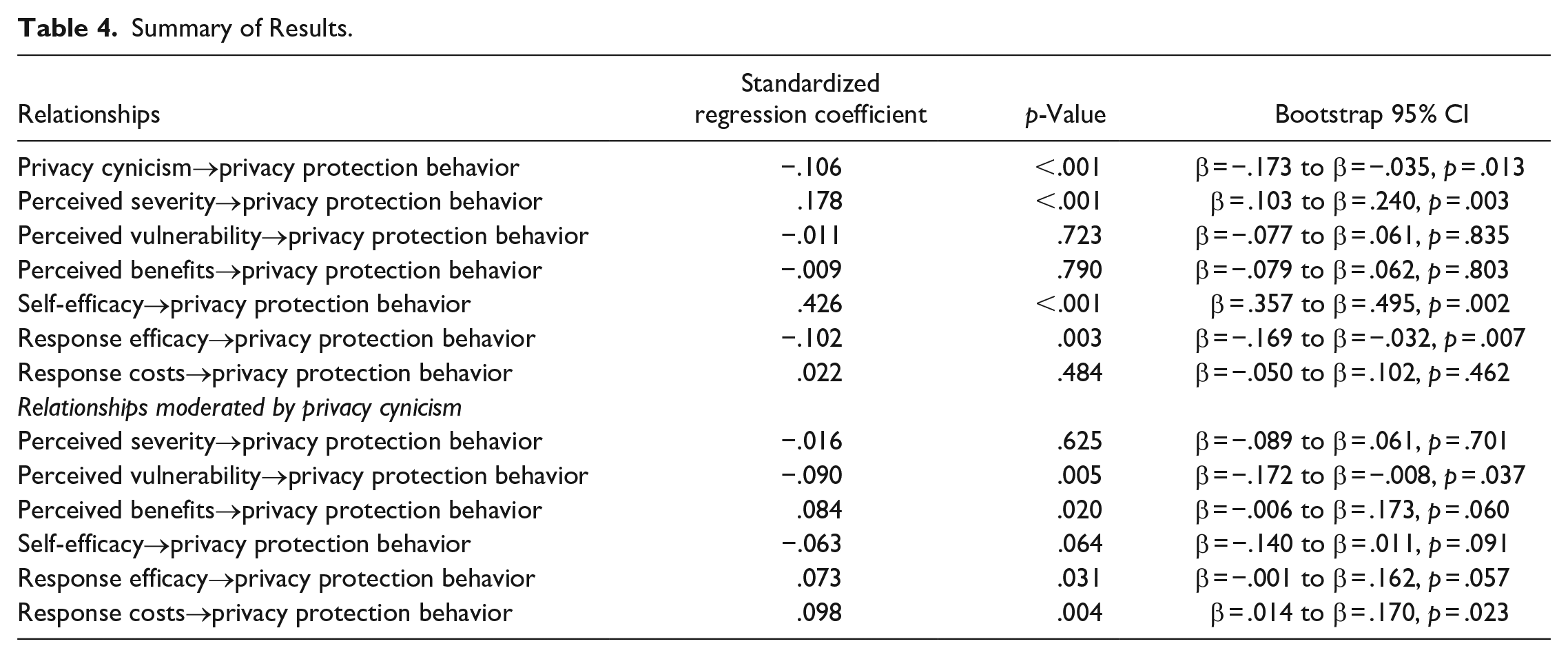
Main Effects
As expected, the results from our structural model reveal that privacy cynicism had a significant negative relationship with privacy protection behavior (β = −.106, p < .000), supporting H1. Furthermore, significant relationships with privacy protection behavior were found for severity (β = .178, p < .000), self-efficacy (β = .426, p < .000), and response efficacy (β = −.102, p = .003). These effects were all in the anticipated direction according to PMT, except for response efficacy, which could be explained by the interaction with cynicism as discussed below. No significant relationship with privacy protection behavior were found for vulnerability (β = −.011, p = .723), perceived benefits (β = −.009, p = .790), and response costs (β = .022, p = .484).
Interaction Effects
To test H2, we examined the interaction of cynicism with severity (H2a), vulnerability (H2b), and benefits (H2c) on privacy protection behavior. The interaction term with perceived severity (H2a) was not significant (β = −.016, p = .625), which does not confirm H2a. Thus, the relationship of severity with privacy protection behavior was positive and significant regardless of the level of privacy cynicism. The interaction term of cynicism with perceived vulnerability was significant (β = −.090, p = .005), supporting H2b. Higher perceptions of vulnerability increased privacy protection behavior, but higher levels of privacy cynicism diminished this relationship (see Figure 3 for a graphical representation of these results). The interaction term with perceived benefits was also significant (β = .084, p = .020), supporting H2c. As shown in Figure 3, lower perceived benefits associated with the disclosure of personal information resulted in more privacy protection behavior compared to high perceived benefits, but this negative relationship turned around for individuals with high levels of privacy cynicism. For individuals with higher levels of cynicism, the negative relationship between benefits and privacy protection behavior turned positive.
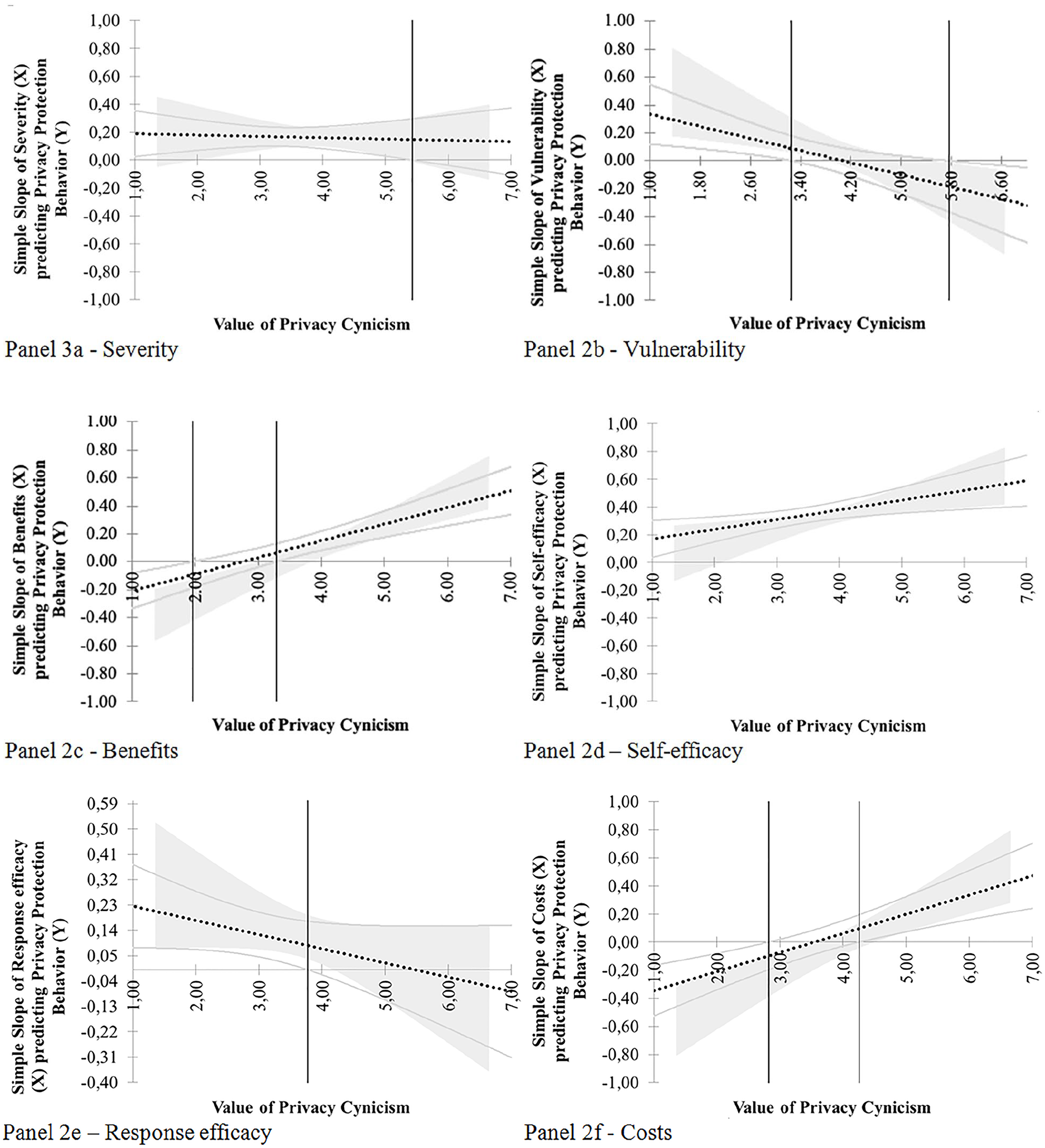
Graphic Representation of the Effects on Privacy Protection Behavior Under Different Values of Privacy Cynicism. Panel 3a—Severity, Panel 2b—Vulnerability, Panel 2c—Benefits, Panel 2d—Self-efficacy, Panel 2e—Response efficacy, and Panel 2f—Costs.
To test H3, we explored the interaction of cynicism with self-efficacy (H3a), response efficacy (H3b), and response costs (H3c) on privacy protection behavior. The interaction term with self-efficacy was not significant (β = −.063, p = .064), not confirming H3a. Thus, individuals with high self-efficacy tended to engage in more privacy protection behavior regardless of their levels of privacy cynicism. The interaction term with response efficacy was significant (β = .073, p = .031). Response efficacy was positively related to privacy protection behavior for individuals whose levels of cynicism were low, but this effect diminished when levels of privacy cynicism were high, thus supporting H3b. The interaction term with response costs was also significant (β = .098, p = .004). The relationship between response costs and privacy protection behavior was negative, but particularly when privacy cynicism was low. That is, when the subjective costs of protecting one’s privacy were low, this resulted in increased privacy protection behavior, but only among less cynical individuals. A complete overview of the effects, including Bootstrap 95% Confidence Intervals, can be found in Table 4.
Summary of Results.
To visualize the moderating effect of privacy cynicism on the relationship between each of the six predictors and privacy protection behavior, we provided additional analyses using plots (Figure 3a–f) that indicate the Johnson-Neyman regions of significance (Carden et al., 2017). Each plot represents the relationship of an antecedent in the model on privacy protection behavior (y-axis) under different levels of privacy cynicism (x-axis). For any values of privacy cynicism for which the confidence bands did not contain zero (outside the vertical lines), the effect of the antecedent on privacy protection behavior was significantly different from zero. A negative value indicates a negative relationship between the antecedent and privacy protection behavior, while a positive value indicates a positive relationship between these variables.
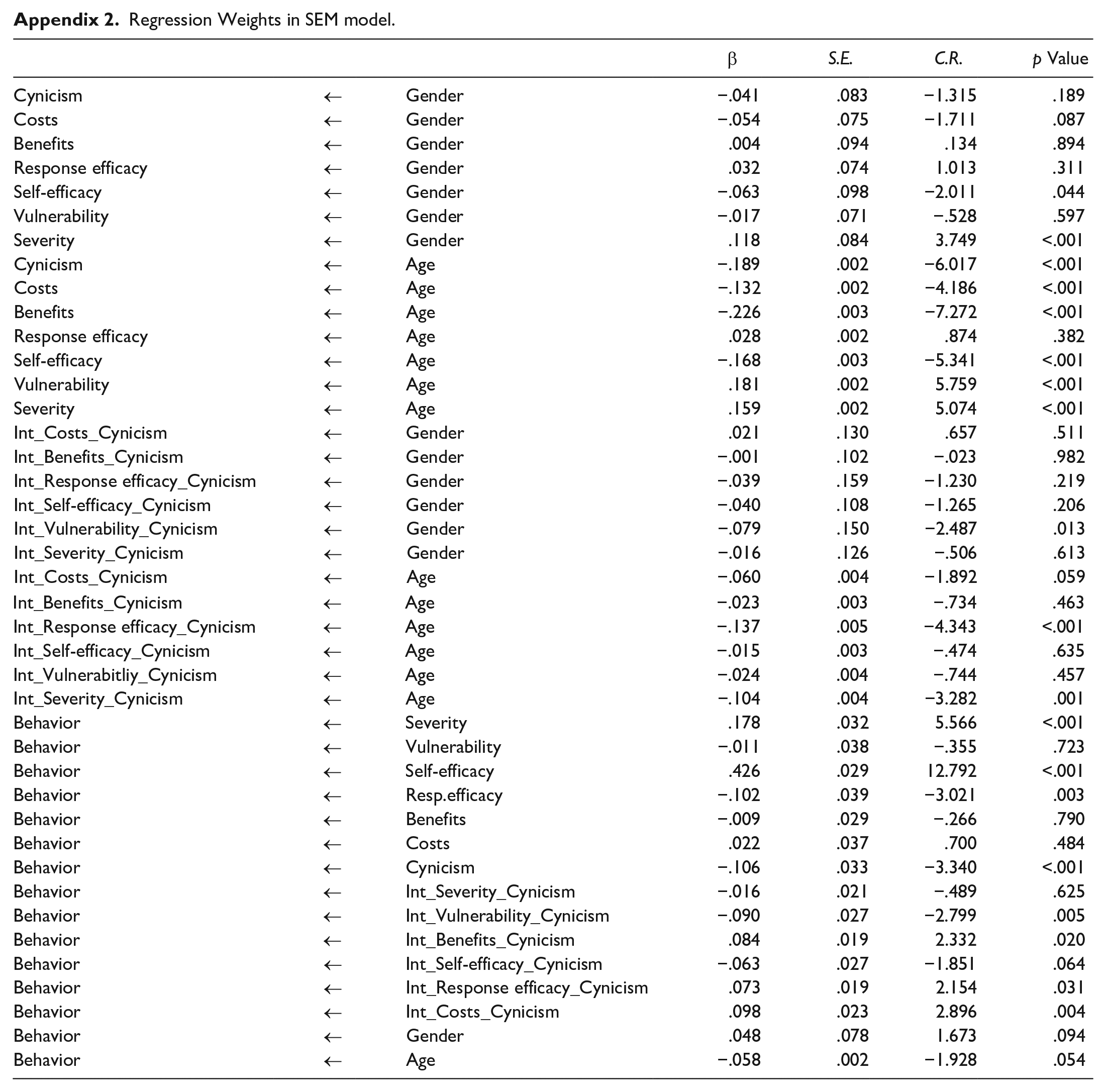
To complete, we want to mention that gender and age did not affect privacy protection behavior directly (gender: β = .048, p = .094; age: β = −.058, p = .054). However, gender (male, female) was found to predict self-efficacy (β = −.20, p = .044), and age affected all PMT variables except response efficacy (all p’s < .000; see Appendix 2 for a complete overview of the results).
Conclusion and Discussion
The current work advances theory on online privacy behaviors by examining the role of privacy cynicism in individuals’ privacy decision-making. Our findings demonstrate the importance of including privacy cynicism in future work on online privacy behaviors. We found that privacy cynicism negatively predicts privacy protection behavior and that vulnerability, benefits, response efficacy, and response costs are moderated by privacy cynicism. First, we will discuss the supported moderation effects of privacy cynicism as predicted by H2b (vulnerability), H2c (benefits), H3b (response efficacy), and H3c (response costs) before discussing the moderation effects on severity (H2a) and self-efficacy (H3a) that were not significant. Second, to further interpret the results and provide more insights into the role of privacy cynicism, we will discuss the direction of the relationships under high levels of cynicism.
Vulnerability in relation to the privacy threat positively predicts privacy protection behaviors, as described by PMT; moreover, in line with our prediction (H2b), privacy cynicism moderates this relationship. Vulnerability increases privacy protection behaviors when privacy cynicism was low, no relation was found when privacy cynicism is moderate, and for individuals with extremely high levels of privacy cynicism, the relationship between vulnerability and privacy protection behavior turned negative. This finding is significant because it demonstrates that it is important for individuals to not become cynical in order to be able to act on their perceptions of vulnerability when facing privacy-threatening circumstances. Moreover, for highly cynical individuals, their privacy cynicism might prevent them from acting when facing online threats, which could explain the discrepancy between privacy attitudes and privacy protection behaviors (i.e., the privacy paradox).
Further, PMT suggests that the lower perceived benefits of engaging in (privacy) threatening actions result in more (privacy) protection behaviors. However, this study demonstrates that the influence of perceived benefits depends on individuals’ level of privacy cynicism (H2c). Lower perceived benefits of data disclosure resulted in more privacy protection solely for individuals with extremely low levels of privacy cynicism. However, this pattern was reversed for individuals with moderate to high levels of cynicism. For those relatively cynical individuals, the lower perceived benefits of data disclosure resulted in more privacy protection behavior. A similar pattern was observed for response costs. Lower perceived response costs of protecting online privacy in terms of effort, time, and money were associated with more privacy protection for individuals with less privacy cynicism, but less for individuals with high privacy cynicism, supporting H3c. These results support the notion that cynicism neutralizes how much weight individuals attach to both the benefits and costs associated with their decisions about their online privacy protection.
Privacy cynicism also moderated the effect of response efficacy on privacy protection behavior, which is in line with H3b. These results indicate that a higher response efficacy resulted in more privacy protection behavior solely for individuals who are less cynical. For individuals who are moderately to highly cynical, it does not matter whether they believe that taking online privacy measures is effective in protecting their privacy (i.e., response efficacy). These results support the notion that privacy cynicism may prevent individuals from protecting their privacy even if they feel that there are ways to effectively manage their privacy online (e.g., by installing ad blockers and deleting tracking cookies).
Cynicism did not moderate the relationship between severity and self-efficacy with privacy protection behaviors, which is not in line with H2a and H3a, respectively. It was found that the relationship between severity and privacy protection behaviors is not dependent on cynicism (not supporting H2a). This could be explained by the high average levels of severity found in this study. Privacy cynicism may not influence the relationship between severity and privacy protection behaviors for individuals who perceive the privacy threat to be highly severe. When individuals feel that a privacy threat is very intrusive and makes them feel vulnerable and unsafe, they may attempt to protect their online privacy regardless of whether they are cynical. Although future research should further explore this possibility, the notion that privacy cynicism might not prevent individuals who experience more severe consequences of data disclosure from acting on their concerns might be reassuring.
According to PMT, self-efficacy positively influences privacy protection behaviors. In this study, among all the predictors, the relationship between self-efficacy and privacy protection behavior was the strongest. Contrary to our prediction (H3a), privacy cynicism did not moderate this relationship as the relationship between self-efficacy and privacy protection was significant for individuals with low, moderate, and high levels of cynicism. This may be reassuring in terms of safeguarding individuals’ privacy because it indicates that increasing self-efficacy through education might be an effective way to help individuals protect their online privacy, even if they are highly privacy cynical. Privacy self-efficacy could for example be enhanced by means of programs or campaigns that aim to empower Internet users, for instance by increasing their internet skills or familiarity with exercising privacy protection behaviors (e.g., Eastin & LaRose, 2000; Livingstone & Helsper, 2010). The enhancement of “privacy self-efficacy” might even be a strategy that can compensate for the possible negative effects of high levels of cynicism (Rimal & Real, 2003).
Our study has at least three important theoretical implications. First, our model may account for the contradictory results of past studies. For instance, although Boerman et al. (2021) found no positive effect of vulnerability on privacy protection behaviors, Mousavi et al. (2020) did find a positive effect. Our study indicates that privacy cynicism might be responsible for these contradictory results: Vulnerability may affect privacy protection, but only when individuals are less privacy cynical. Moreover, although earlier studies found positive effects of response efficacy on privacy protection behaviors (Boerman et al., 2021; Mousavi et al., 2020), this study indicated that these effects are conditional for individuals with low levels of privacy cynicism. In addition, it was found that only severity and self-efficacy predicted privacy protection behaviors unconditionally (i.e., regardless of privacy cynicism). Our results provide further support for the importance of perceived severity and self-efficacy in explaining privacy protection behavior.
Second, our results demonstrate the importance of including privacy cynicism in future work on privacy protection motivation and privacy behaviors in general, especially because our results indicate that the effects of many determinants of privacy protection behaviors are dependent on privacy cynicism. For instance, the perceived benefits of using privacy-invasive services and the perceived response costs of undertaking action to protect one’s privacy increase privacy protection behavior solely when individuals are a bit privacy cynical. This may be explained by the “resignation” phenomenon, which is associated with privacy cynicism (Hoffmann et al., 2016). When highly cynical individuals see no benefit to using privacy-invasive services, this, combined with their cynical attitudes, makes them think that they “do not care about any of it” in terms of their privacy. In contrast, acknowledging some benefits of personalization could make them slightly more involved in decision-making about their privacy, which might increase their inclination to protect their data. This emphasizes the importance of taking privacy cynicism into account when privacy behaviors are studied using cost–benefit models, such as the privacy calculus model (Dinev & Hart, 2006). Future research should further explore this notion.
Third, we advance theory by providing an explanation for the discrepancy between individuals’ privacy attitudes and behaviors (i.e., the privacy paradox). Although individuals’ might feel vulnerable or concerned about their online privacy, they are inclined to disclose their information nonetheless. Our results indicate that privacy cynicism may be an explanation for the privacy paradox. Researchers have argued that the privacy paradox exists because privacy attitudes are often based on beliefs about privacy in general that do not correspond to attitudes toward privacy in specific circumstances (for reviews, see Barth & de Jong, 2017; Li, 2011). However, our results support the notion that privacy cynicism may be one of the factors that contributes to this paradox by attenuating the relationship between privacy attitudes (i.e., vulnerability, benefits, etc.) and behaviors.
It should be noted that this study used cross-sectional data. Because of this, results in terms of causal relationships should be interpreted with caution. Given that this is, to our knowledge, the first study to examine the moderating role of privacy cynicism in privacy protection behaviors, this study should be seen as a first step to unravel the relationship and role of privacy cynicism in this context. In order to find additional empirical support for our findings, longitudinal and experimental studies should be conducted. Moreover, privacy protection behaviors were measured in this study using self-reported privacy protection behaviors and not actual behaviors. Therefore, future research on this topic could use observational studies to enhance measurement validity of privacy protection behavior (cf. Spiekermann et al., 2001). Furthermore, the participants in the study were higher educated than the U.S. population. Previous research showed that the higher one’s education, the more knowledge people have on personalized communication techniques (Segijn & Van Ooijen, 2020) and that more knowledge or awareness leads to more privacy protection behaviors (Arachchilage & Love, 2014; Hu & Dinev, 2005). Therefore, it is recommended that future research replicates the findings in a lower educated sample. In addition, the data for the survey were collected in the United States. While this contributes to existing empirical studies that examined privacy cynicism outside of the United States (e.g., Choi et al., 2018; Hoffmann et al., 2016; Lutz et al., 2020), future cross-national studies should be done to examine the effect of privacy cynicism across countries. For instance, the United States and Europe are known to differ in attitudes toward online privacy in their culture, society, and legislation (Smith, 2001).
Importantly, educators and policy makers should consider the notion that privacy cynicism could be a factor that prevents individuals from acting in accordance with their concerns, attitudes, and abilities in regard to protecting their privacy. Our findings suggest that efforts to empower individuals to manage their privacy should be geared specifically toward either lowering their cynicism or enhancing their self-efficacy or perception of severity, as these factors seem to affect privacy protection behaviors regardless of privacy-cynicism level. We believe that privacy cynicism is and will become an even more important explanatory factor vis-à-vis people’s lack of online privacy protective behaviors. As the amount of data collected from individuals through apps, websites, and other platforms continues to grow, individuals increasingly experience a loss of control over their privacy in the online environment (Sundar & Marathe, 2010; Van Ooijen & Vrabec, 2019). In other words, it becomes increasingly troublesome for Internet users to participate in online activities while protecting their privacy. This is likely to result in highly privacy-cynical individuals, whose attitudes toward privacy are characterized by resignation.
Policy makers should take this into account and strive to regulate or at least address the seemingly limitless possibilities for Big Data companies to continue to expand their data usage practices. Initiatives such as data vaults or data platforms, on which consumer data can be exchanged while consumers retain some degree of control over their data (Karjoth et al., 2002), may provide opportunities to reduce privacy cynicism. In addition, educators should consider privacy cynicism when educating individuals about online privacy. For instance, educating individuals about the possible privacy risks of disclosing data online may increase perceptions of vulnerability; however, our study showed that among highly cynical individuals, this did not increase privacy protection behavior. Therefore, education should be aimed at increasing not only perceived vulnerability but also individuals’ awareness of their own privacy cynicism. It is possible that once highly cynical individuals become aware of their use of privacy cynicism as a coping mechanism to deal with their loss of control in the online environment, the negative effects of cynicism on privacy protection behaviors might disappear. Thus, when privacy cynicism can be decreased, the factors that affect privacy protection behavior, such as response efficacy or perceived vulnerability, may empower individuals to continue to protect their privacy.
Footnotes
Appendix
Regression Weights in SEM model.
| β | S.E. | C.R. | p Value | |||
|---|---|---|---|---|---|---|
| Cynicism | ← | Gender | −.041 | .083 | −1.315 | .189 |
| Costs | ← | Gender | −.054 | .075 | −1.711 | .087 |
| Benefits | ← | Gender | .004 | .094 | .134 | .894 |
| Response efficacy | ← | Gender | .032 | .074 | 1.013 | .311 |
| Self-efficacy | ← | Gender | −.063 | .098 | −2.011 | .044 |
| Vulnerability | ← | Gender | −.017 | .071 | −.528 | .597 |
| Severity | ← | Gender | .118 | .084 | 3.749 | <.001 |
| Cynicism | ← | Age | −.189 | .002 | −6.017 | <.001 |
| Costs | ← | Age | −.132 | .002 | −4.186 | <.001 |
| Benefits | ← | Age | −.226 | .003 | −7.272 | <.001 |
| Response efficacy | ← | Age | .028 | .002 | .874 | .382 |
| Self-efficacy | ← | Age | −.168 | .003 | −5.341 | <.001 |
| Vulnerability | ← | Age | .181 | .002 | 5.759 | <.001 |
| Severity | ← | Age | .159 | .002 | 5.074 | <.001 |
| Int_Costs_Cynicism | ← | Gender | .021 | .130 | .657 | .511 |
| Int_Benefits_Cynicism | ← | Gender | −.001 | .102 | −.023 | .982 |
| Int_Response efficacy_Cynicism | ← | Gender | −.039 | .159 | −1.230 | .219 |
| Int_Self-efficacy_Cynicism | ← | Gender | −.040 | .108 | −1.265 | .206 |
| Int_Vulnerability_Cynicism | ← | Gender | −.079 | .150 | −2.487 | .013 |
| Int_Severity_Cynicism | ← | Gender | −.016 | .126 | −.506 | .613 |
| Int_Costs_Cynicism | ← | Age | −.060 | .004 | −1.892 | .059 |
| Int_Benefits_Cynicism | ← | Age | −.023 | .003 | −.734 | .463 |
| Int_Response efficacy_Cynicism | ← | Age | −.137 | .005 | −4.343 | <.001 |
| Int_Self-efficacy_Cynicism | ← | Age | −.015 | .003 | −.474 | .635 |
| Int_Vulnerabitliy_Cynicism | ← | Age | −.024 | .004 | −.744 | .457 |
| Int_Severity_Cynicism | ← | Age | −.104 | .004 | −3.282 | .001 |
| Behavior | ← | Severity | .178 | .032 | 5.566 | <.001 |
| Behavior | ← | Vulnerability | −.011 | .038 | −.355 | .723 |
| Behavior | ← | Self-efficacy | .426 | .029 | 12.792 | <.001 |
| Behavior | ← | Resp.efficacy | −.102 | .039 | −3.021 | .003 |
| Behavior | ← | Benefits | −.009 | .029 | −.266 | .790 |
| Behavior | ← | Costs | .022 | .037 | .700 | .484 |
| Behavior | ← | Cynicism | −.106 | .033 | −3.340 | <.001 |
| Behavior | ← | Int_Severity_Cynicism | −.016 | .021 | −.489 | .625 |
| Behavior | ← | Int_Vulnerability_Cynicism | −.090 | .027 | −2.799 | .005 |
| Behavior | ← | Int_Benefits_Cynicism | .084 | .019 | 2.332 | .020 |
| Behavior | ← | Int_Self-efficacy_Cynicism | −.063 | .027 | −1.851 | .064 |
| Behavior | ← | Int_Response efficacy_Cynicism | .073 | .019 | 2.154 | .031 |
| Behavior | ← | Int_Costs_Cynicism | .098 | .023 | 2.896 | .004 |
| Behavior | ← | Gender | .048 | .078 | 1.673 | .094 |
| Behavior | ← | Age | −.058 | .002 | −1.928 | .054 |
Author Note
The data used in this paper is part of a bigger project on personalized advertising.
Declaration of Conflicting Interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
