Abstract
The employment of Electronic Medical Records is expected to better enhance health care quality and to relieve increased financial pressure. Electronic Medical Records are, however, potentially vulnerable to security breaches that may result in a rise of patients’ privacy concerns. The purpose of our study was to explore the factors that motivate hospital information technology staff’s compliance with Electronic Medical Records privacy policy from the theoretical lenses of protection motivation theory and the theory of reasoned action. The study collected data using survey methodology. A total of 310 responses from information technology staff of 7 medical centers in Taiwan was analyzed using the Structural Equation Modeling technique. The results revealed that perceived vulnerability and perceived severity of threats from Electronic Medical Records breaches may be used to predict the information technology staff’s fear arousal level. And factors including fear arousal, response efficacy, self-efficacy, and subjective norm, in their turn, significantly predicted IT staff’s behavioral intention to comply with privacy policy. Response cost was not found to have any relationship with behavioral intention. Based on the findings, we suggest that hospitals could plan and design effective strategies such as initiating privacy-protection awareness and skills training programs to improve information technology staff member’s adherence to privacy policy. Furthermore, enhancing the privacy-protection climate in hospitals is also a viable means to the end. Further practical and research implications are also discussed.
Keywords
Introduction
To improve health care quality and to ease increased financial pressure, it is widely acknowledged that the health care industry should extensively leverage health information technologies (IT) to overcome such challenges.1-3 One assumed method to meet these initiatives is through the adoption of Electronic Medical Records (EMR) systems. 4 Generally, EMR refers to a collection of software applications commonly utilized to communicate orders for medical care, record related facts concerning a patient’s medical history, and to circulate results of laboratory testing. 5 Via EMR, health care professionals can access patient information instantly without the set limitations of time and location. 3 More important, they may acquire support to improve the quality of clinical decision-making. 3 Along with the development of more comprehensive EMR, a highly increased volume of medical records will become easily accessible to both authorized and unauthorized users both inside and outside the health care facilities. 6 EMR are, thus, potentially vulnerable to security breaches that may result in a rise of patients’ privacy concerns. 7 This issue needs special attention due to the fact that EMR adoptions are currently widespread, and they have been well acknowledged as a cost-effective investment tool.8-10 It is, thus, an important mandate for hospitals to effectively secure the privacy of EMR to diminish their patients’ overall privacy concerns. The literature has further asserted that the reason why security breaches continue to occur in most organizations is due to administrative employees remaining as one of the primary sources of threat.11,12 Specifically, most violations of patient privacy in medical facilities result from staff abuse or misuse of the right to access patient records13,14; even so, medical facilities are legally bound and ethically obligated to protect the privacy of EMR regardless of the existence of any internal regulations. Many countries, including Taiwan, have even externally regulated hospitals to ensure the relative safety of EMR.14,15 Furthermore, any noncompliance with those privacy rules may involve both civil money and criminal penalties. For example, in the United States, the amount of civil monetary penalty is US$100 to US$50 000 or more per violation, and the criminal penalty may result in a fine of US$250 000 and up to 10 years of imprisonment. 14 In Taiwan, the maximum civil monetary penalty can result in a payment of more than US$6 million and 5 years of imprisonment. 16 Hospitals’ employees are thus wholly mandated to protect the privacy of EMR; nevertheless, they may still not act as preregulated.13,14 Hence, all hospital employees who have EMR access privileges are still to be considered as possible threats to EMR privacy, in addition to those intrusive individuals who are outside the system domain.
Previous privacy-related studies in an EMR context can be roughly classified into three major categories: (1) technical solutions to avoid or secure privacy problems in EMR, (2) patients’ privacy concerns and responses regarding EMR, and (3) privacy-protection from a law perspective. In the first type of study, the primary objective is to propose a sound mechanism or an optimal algorithm useful to secure expected EMR privacy.17-20 The second type of study focuses on exploring the privacy concerns of patients/health care professionals and/or the results of such privacy concerns throughout the EMR process.7,21-24 The last type of literature emphasizes the potential limitation of privacy law and how to respond to such limitation from a legal perspective.25,26
By reviewing privacy-related studies in an EMR context, we have obtained a deeper understanding of how to technically and lawfully design EMR that affords better characteristics that preserve data integrity and also address patients’ concerns related to general EMR privacy constraints. However, the nature of how hospitals can effectively secure the privacy of EMR through “other-than-technical” solutions seems to have been insufficiently investigated to date. Literature, indeed, has begun pointing out the relative importance of employee compliance to organizational rules, or set policies and procedures, which may provide a useful mechanism in modeling employees’ proper attitudes or behaviors concerning how organizational resources should be used.11-13,27 However, results often reveal that employees do not choose to adhere to such rules or policies as a matter of course. Further, little study has specifically been focused on IT staff in hospitals, who are the administrators of and have full control of EMR systems. More important, IT staff knowledge of how users protect EMR privacy is found to mismatch how users really operate in practice. 28 Consequently, the perceptions of IT staff toward the privacy of EMR should be carefully investigated. The privacy policy of EMR refers to a formal statement articulating the privacy rules of the hospital and concerns to all employees who have access to EMR and such related information assets. 29 Any adherence to stated EMR policy by IT staff is always a matter of interest to their employer.
The primary purpose of our study was to investigate the factors that effectively motivate, rather than coerce, hospital IT staff’s compliance with a stated EMR privacy policy. We proposed a research model on a basis of well-recognized and fitting theories. More specifically, we drew upon the literature of protection motivation theory (PMT)30,31 and theory of reasoned action (TRA) 32 to investigate IT staff perceptions regarding their widespread compliance with EMR privacy policy in a health care setting. Previous literature 33 of systematic review suggests that behavioral science theories such as PMT used to explain individuals’ choices as to whether or not to apply specific protective measures regarding possible threats,30,31 and TRA may be used to predict individuals’ behaviors 32 for investigating policy-compliance behaviors.
Research Model and Research Hypotheses
Conceptual Model Formulation
To capture the essence of IT staff’s compliance intention of EMR privacy policy, we integrated PMT30,31 and TRA 32 to form our theoretical underpinning. First, the PMT explains how delineating an individual’s protection motivation can be aroused through his or her appraisal mechanisms whenever confronting a threat, which seems suitable for explaining how IT staff can avert the potential threat of EMR breaches. The PMT postulates that protection motivation is the result of two cognitive mediating processes, namely, threat appraisal (referring to the assessment of the probability of and severity of a threat), and coping appraisal (meaning the assessment of one’s ability to cope with and to avert the threat).30,31 Furthermore, fear arousal, which assesses how much fear the threat evokes for an individual, 34 is an emotional response to threat appraisal34-36 and, in its turn, influences an individual to undertake protective behaviors. 34 An individual may, however, decide not to take such protective behaviors. 33 And such a dichotomous decision is precisely why there is a compliance of EMR privacy policy in place, which makes the PMT an appropriate theoretical underpinning for our study. Second, the TRA illustrates that an individual’s behavior intention is directed by his or her attitude, and the attitude is a function of an individual’s beliefs, and can thereby predict IT staff’s policy-compliance intention. Beliefs, or cognitions, represent the information he or she has about an object, issue, or event while attitude, or affect, refers to a person’s feelings toward and assessment of some objects, issues, or events. 32 Furthermore, a person’s intention is also a function of certain beliefs. 32 Accompanying TRA, PMT can, thus, be regarded as a more comprehensive model for predicting protective behavioral intentions. 33
In our study context, any EMR breaches may be considered as a perceptible threat to both hospitals and health care employees, including IT staff, because such an event would negatively infringe on a hospital’s positive reputation and even with its profit-driven business climate. In just such a situation, the IT staff may, thus, stand to lose their jobs or even suffer legal ramifications if they were somehow connected to possible EMR breaches, rightfully or wrongfully. In facing such conflictive situations, IT staffers have to elect to cope with the perceived threat (ie, in full or partial accordance with the stated EMR privacy policy) or not choose to cope with the threat at all. In other words, IT staff will undergo the threat appraisal process. An emotional feeling of fear may then be aroused after evaluating a potential threat and the level of severity the potential EMR breaches may pose. Besides the support of PMT, such a presumed relationship between threat appraisal and fear arousal can further be evidenced from the manner in which an individual’s belief (threat appraisal) can predict his or her attitude (fear arousal, an emotional response), as articulated by the TRA. 32 The IT staff member will then generate his or her behavioral intention to comply with a given privacy policy through direct action or affirmation.
Furthermore, they may also evaluate the efficacy of, or their ability to comply with, the cost of compliance to a given privacy policy, and a behavioral change (ie, protection motivation) regarding which coping responses will then occur according to PMT. 30 Furthermore, such compliance intention can also be determined by adherence to a subjective norm as posited by TRA. 32 Finally, we include three control variables in the proposed model, namely, those of age, gender, and the education of respondents to eliminate those unknown influences.36,37 Figure 1 shows our research model integrative of both PMT and TRA.

Research model.
Research Hypotheses
The relationships of perceived vulnerability and perceived severity with fear arousal
In our study, perceived vulnerability refers to the IT staff member’s probability assessment of a threat resulting from noncompliance with EMR privacy policy, while perceived severity pertains to the understood consequences of a threat originating from noncompliance with privacy policy. 38 Fear arousal refers to the extent to which IT staff members are concerned with EMR being threatened. 39 In line with PMT, perceived vulnerability and perceived severity can trigger an individual’s protection motivation to manifest.30,31 In an EMR privacy setting, these threats can be conceived of as the IT staff’s appraisal of the probability of exposure to and the consequences stemming from an EMR privacy threat. Furthermore, we favored the assertion by Tanner et al 36 that the state of fear (eg, conceptualized as fear arousal in our study) is assumed to be aroused after assessing the vulnerability and severity of any threat. In other words, fear arousal may mediate an individual’s threat appraisal and protection motivation to a threat. Applying such a rationale to our study, if the IT staff perceive that the EMR privacy may be violated after assessing the probability of and severity of the occurrence of an EMR privacy threat, IT staff members may become concerned that the injury posited by the threat is substantiated because such a threat may negatively influence the hospital’s reputation, business climate, and even personal work settings. In their study of juveniles’ response to health hazards typically associated with smoking, Arthur and Quester 40 found that juveniles’ perceived vulnerability to, along with a perceived notion of severity of, health hazards has a significant and positive relationship with fear. Furthermore, Boss et al 35 also reported that information system users’ perceived threat vulnerability and perceived threat severity significantly and positively associated with their fear of possible negative results due to unsafe security behaviors. Thus, the present study hypothesizes the following:
The relationships of fear arousal, response efficacy, self-efficacy, response cost, and subjective norm with behavioral intention
In their study of online users’ intention to use strong passwords, Zhang and McDowell 41 found that fear arousal will change online users’ behavior consistently. Furthermore, fear has also been characterized as an emotional state. 30 According to TRA, an individual’s attitude (ie, one kind of feeling) can predict his or her behavioral intention. 32 Consequently, if IT staff members reveal a higher level of fear concerning the perceived threat of EMR breaches, they are supposed to become much likelier to comply with a specified privacy policy. Furthermore, they will hold a positive attitude/intention toward individual compliance with a privacy policy to avert any perceived threat. Prior literature 40 also confirmed that juveniles’ fear of health hazards associated with smoking significantly predicts the nature of their protective behaviors. Boss et al 35 found that information system users’ fear of possible negative results due to unsafe security behaviors is significantly associated with their protective motivation. Thus, the third hypothesis postulates the following:
In addition, according to PMT, coping appraisal is composed of response efficacy, self-efficacy, and response cost. In our study, response efficacy refers to IT staff’s compliance with a privacy policy as being a useful means for diminishing the threat of EMR breaches, while self-efficacy is used to measure IT staff member’s judgment of himself or herself to be capable of compliance with privacy policy. Response cost is defined as IT staff member’s perceived cost of complying with privacy policy and may be inclusive of the money, time, or personal effort involved. Logically, if IT staffers perceive that compliance with privacy policy can effectively avert the threat of EMR breaches, and he or she is confident of adherence to privacy policy, they are more likely to possess a positive attitude/intention toward that given privacy policy. Furthermore, if they consider themselves as being incapable of compliance with a privacy policy due to inherently complicated procedures, or if the compliance behavior requires inordinate amounts of time and effort, they may, thus, be unlikely to adhere to the given privacy policy. Prior studies42,43 found that response efficacy and self-efficacy positively and significantly predict government employees’ compliance with protective strategies concerning information security. Herath and Rao 39 also reported that response cost correlated negatively with employees’ attitudes toward security policy. Boss et al 35 and Ifinedo 38 both found that response efficacy and self-efficacy significantly and positively linked with information system users’ safe security behavioral intentions, respectively. Boss et al 35 further confirmed that response cost negatively related with information system users’ safe security behavioral intentions. According to the above discussion, we postulate the following hypotheses:
In our study, subjective norm refers to the IT staff’s subjective beliefs about the extent of disapproval for nonadherence to EMR privacy policy among those members who are of paramount importance to the IT staff. According to TRA, an individual’s intention toward a specific behavior can be collectively predicted by his or her attitude toward that behavior and subjective norm posed by important others. Hence, if IT staff members hold affirmative feelings toward personal compliance with a privacy policy, and other considered-important people (ie, top management or esteemed colleagues) also think that the IT staff should obey the privacy policy, IT staff members may then be more likely to support the privacy policy of the EMR. In several studies of organizational security behavior, subjective norm has consistently been a significant predictor of one’s intention to comply with security policy.38-39,44 Based upon the previous discussion, this study, therefore, states the following hypothesis:
Methods
Measures
This research followed Churchill’s 45 approach for generating questionnaires, with the research constructs reflectively measured using previously validated instruments.38,39 We adopted reflective measurements for the following reasons: (1) the indicators are manifestations of the construct, (2) removing an indicator does not alter the conceptual domain of the construct, and (3) indicators can be interchangeable. These characteristics are, therefore, more demonstrative of a reflective construct. 46
The instruments for perceived vulnerability utilized four items and were adapted from Ifinedo. 38 The perceived severity and fear arousal constructs were measured by using two items, respectively, and they are to be found in Herath and Rao. 39 Response efficacy and self-efficacy were measured by using three items, respectively, and they were also adapted from Herath and Rao. 39 We measured response cost by using two items adapted from Ifinedo. 38 Subjective norm and intention to comply were measured by using four items and three items, respectively, and they were adapted from Herath and Rao. 39 Excluding demographic questions, all items were based on a 7-point Likert-type scale (eg, 1 = strongly disagree, and 7 = strongly agree).
A pretest, a preliminary trial of the instrument used to ensure that there are no unexpected difficulties before formal investigation, 47 was conducted to establish the scales via a convenience sampling of 10 IT staff members belonging to a major medical center. Based upon subsequent feedback, modification of words and phrases was made to items resulting in a final scale (see Appendix A), which was justified for further testing.
Sample and Data Collection
Permission from the Institutional Review Board of a large hospital in Taiwan was obtained prior to investigation. In Taiwan, medical centers are assumed to be the most sophisticated in their implementation of EMR vis-à-vis other types of medical facilities (eg, regional and district hospitals). Furthermore, Taiwanese hospitals that have adopted EMRs are mandated to formulate policies or rules that can secure the privacy of EMRs according to the governmental regulation, and the hospitals should inform their staff with these policies or rules. 15 Our study’s purpose was to explore the determinants of hospital IT staff compliance with EMR privacy policy. Participants within the study must have been granted access to EMR at some point in time. Hence, our primary participants will be the IT staff of these medical centers as they usually have EMR access privileges for at least maintenance purposes. Prior to the administration of the questionnaires, we successfully contacted 7 medical centers to secure their collaboration. We assigned a coordinator for each hospital to help with the distribution and collection of the questionnaires. IT staff in the seven hospitals, including the managerial-level staff who are also IT literate, were invited to participate in a paper-and-pencil survey. A total of 350 questionnaires were distributed to these coordinators according to their respective numbers of IT staff in these 7 hospitals, and a total of 320 questionnaires were returned to the researchers. Excluding 10 incomplete questionnaires, 310 usable questionnaires were left for subsequent analysis.
Results
Descriptive Statistics
Of the 310 valid responses, 62.3% of responses were from male respondents, and 37.7% were from female respondents. Nearly 77.4% of the total respondents were 30 to 49 years of age. Furthermore, the majority of respondents were university educated or graduate school educated (90.0%). Programmers made up the largest group of respondents (41.0%), and more than 48.1% of respondents reported having more than 10 years of prior work experience within the health care industry. Furthermore, all respondents were said to understand relevant EMR privacy policy, with 32.6% of respondents being not very clear about the detailed contents of the codified policy as it might exist. Details of the respondents are shown in Table 1.
Descriptive Statistics of Respondents’ Characteristics.

Note. EMR = Electronic Medical Records.
Structural Equation Modeling
We first employed a Kolmogorov-Smirnov test to check for the normality of collected data, and the results showed non-normal distribution (P < .001) to some extent. We, therefore, adopted partial least squares (PLS), which is a method that makes no distribution assumption, 48 to analyze the collected data. We used R software, 49 with the semPLS package, 50 to inspect both the measurement model and the structural model of PLS, respectively. 48
Measurement model
The measurement model in PLS is usually assessed according to three tests: reliability, convergent validity, and discriminant validity.48,51 Reliability can be evaluated via composite reliability (CR).48,51 In our study, the CR values of all constructs (see Table 2) were above the threshold of 0.7, 48 indicating sufficient reliability (see Table 2). Although the CR values of the four constructs (ie, perceived vulnerability, perceived severity, subjective norm, and behavioral intention to comply) were all higher than 0.95, they may still indicate an invalid measure of a construct, and it is usually caused by using redundant items. 45 However, the items used in our study were semantically different and, as such, tapped into different aspects of the constructs (see Appendix A), so they were still highly correlated. Furthermore, other literature 52 regards a reliability of 0.95 as a desired standard. Hence, this may imply the measurement model remains valid. For convergent validity, all items in our study had outer loadings >0.7 on their posited factors and loaded highly on the posited factors, suggesting sufficient convergent validity on the indicator level. 48 Fornell and Larcker 51 further suggested that the value of average variance extracted (AVE) of at least 0.5 demonstrates sufficient convergent validity of each construct. As per this criterion, the constructs used in this study demonstrated sufficient convergent validity (see Table 2). Because the factor loadings of perceived severity and behavioral intention to comply were higher than 0.95, we further checked for a collinearity problem. The results revealed that the tolerance value of each construct ranges from 0.24 to 0.81, indicating that collinearity should not be an issue in our study. 53 Furthermore, the inter-construct correlations matrix (see Table 3) exhibited that the square root of AVE for each construct was larger than the correlation of the specific construct with any other constructs in the model, thus indicating the occurrence of adequate discriminant validity. 51
Reliability and Validity.

Note. CR = composite reliability; AVE = average variance extracted.
Correlations Among Constructs.

Note. Diagonal elements show the square root of average variance extracted (AVE).
Structural model
Regarding the assessment of the structural model, the 7 proposed hypotheses were all supported, with the exception of H6 (Response cost → behavioral intention). Overall, the model explained about 45% and 76% of the determined variance in the fear arousal and behavioral intention, respectively. Furthermore, the effects of the three control variables (ie, age, gender, and level of education) were also tested, along with the hypotheses. The results indicated that no one control variable possessed a significant effect on intention, and the results regarding the hypotheses remain unchanged with, or without, these control variables being present. We then assessed the structural model with three key criteria, namely, the predictive relevance Q2, the f2, and the q2 effect size. 48 The Q2 values for fear arousal and behavioral intention were 0.34 and 0.70, respectively, indicating the structural model had predictive relevance for both constructs. 48 Furthermore, the relationship between perceived vulnerability and fear arousal had a large effect size (f2 = 0.57) and a large predictive relevance (q2 = 0.35), while perceived severity had a small effect size (f2 = 0.06) and a small predictive relevance (q2 = 0.04). 48 Regarding the relationship with behavioral intention, only subjective norm had a medium effect size (f2 = 0.26) and a medium predictive relevance (q2 = 0.20) while other predictor constructs had small effect sizes and small predictive relevance (see Appendix B). Furthermore, as there is no overall fit index in PLS path modeling, 54 we used the global fit measure (GoF), appropriate for reflective measurement modelling, 54 to assess the PLS model. 55 The resulting GoF = 0.71, which surpassed the 0.36 standard for large effect sizes, implied that our model was valid. Figure 2 demonstrated the structural model results.
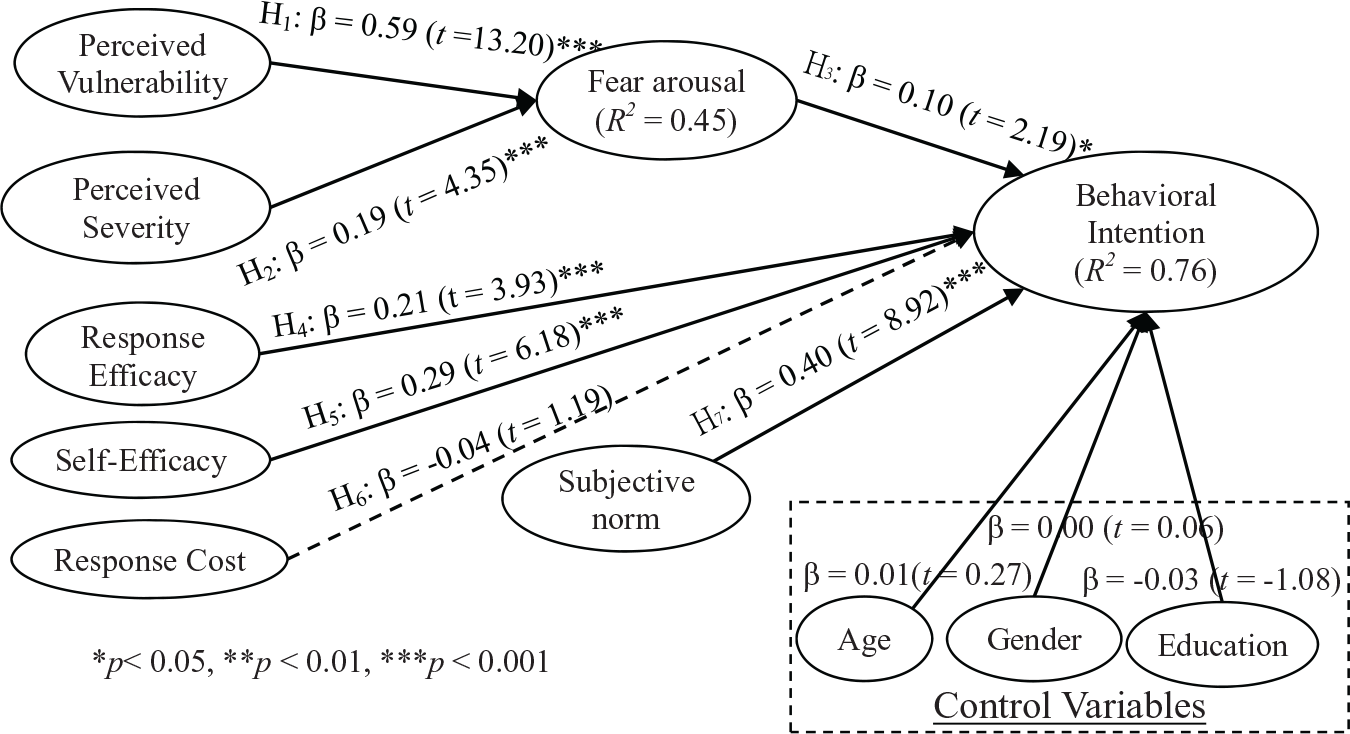
Structural model results.
A Comparison of Differing Models for Predicting Organizational Policy Compliance
Several prior studies33,38,39,56-59 have also researched employee’s compliance of organizational policy from differing theoretical perspectives such as protection motivation theory, theory of planned behavior, deterrence theory, principal agency theory, social cognitive theory, social bond theory, control theory, regulatory focus theory, and reactance theory. The findings of these studies have absolutely added to the knowledge of organizational policy compliance. In general, the variances explained by these models range from 30% to 70% (see Appendix C). Among these models, protection motivation theory and theory of planned behavior are most used to predict employee’s behavioral intention, and usually have a good explanatory power than other models. For example, Ifinedo 38 combined protection motivation and theory of planned behavior to predict information system security compliance and is the only study that explained it is comparatively large (R2 = 70%). Our study integrated protection motivation theory and theory of reasoned action to examine hospital IT staff’s intention to comply with EMR privacy policy and also explained about 76% of the variance of behavioral intention. The reason why PMT has such a high variance explanatory power might be due to the fact that PMT fits well with our study context, because PMT was originally proposed to demonstrate how an individual may cope with a potential threat, which are the EMR breaches in our study.
Discussion
In line with the assertion of PMT, we found that perceived vulnerability and perceived severity significantly and positively correlated with fear arousal, respectively. The result matches those observed in prior studies of differing disciplines.39,40 Ifinedo 38 also found that perceived vulnerability significantly predicted security policy compliance intention of employees. Similar to perceived vulnerability, if the IT staff considers EMR breaches to be a serious threat, not only to the hospitals but also to themselves, they may fear that such a threat might endanger the hospital’s profitability and also the security of the workplace. This finding supports previous literature. 40 Other studies also confirmed the link between perceived severity and individuals’ behavioral intention.38,43 Hence, both perceived vulnerability to and perceived severity of the threat of EMR breaches jointly arouse IT staff’s fear, while perceived vulnerability had a stronger relationship with fear arousal than that of perceived severity.
We also found that fear arousal was a significant predictor of behavioral intention. The more IT staff members are concerned with the threat of EMR breaches, the more they will hold an increased positive intention toward privacy policy. This finding is in line with the study of Zhang and McDowell. 41 Herath and Rao 39 also found that the concern level (akin to fear arousal in our study) of employees significantly predicts their attitude toward security policy. Further, response efficacy was also a strong determinant of behavioral intention. If the IT staff believes that privacy policy is an effective countermeasure in dealing with the threat of EMR breaches, the more likely they will be to comply with existing organizational privacy policy. This also accords with earlier observations.38,43 Regarding the relationship between self-efficacy and behavioral intention, the results of structural model analysis supported that an increased confidence to comply with privacy policy perceived by the IT staff can improve their intention toward compliance with privacy policy. The findings are in line with earlier studies.39,42,43 However, the findings of the relationship between response cost and behavioral intention do not support the previous research39,43 but were in line with the results of Ifinedo. 38 One possible reason for the insignificant results arrived at might be that IT staff understand that whoever uses EMR will be fully logged-in and, therefore, visible to system administration. Any illegal attempts could be interdicted, so IT staff will, thus, adhere to privacy policy at any cost and might not view the cost to protect the privacy as an issue of particular importance or of personal interest. Moreover, as the original TRA states, an individual’s behavioral intention can be determined through a subjective norm. Our findings also corroborate the notions of TRA and other studies.38,39 Several implications for the literature and for practice can be drawn from the findings comprised in our study.
Academic Implications
For academics, our study aids in the accumulation of knowledge related to the issue of compliance with a privacy policy in an EMR context. This study further empirically validated the appropriateness of integrating PMT originated from the health domain and TRA from the psychology discipline to address IT staff’s adherence to a given privacy policy. To the best of our knowledge, there is little extant study accomplished to explore privacy policy issues based on the tandem PMT and TRA aspects. By incorporating the intention construct adapted from TRA, the concept of protection motivation can be more clearly expressed than in the original PMT. Furthermore, PMT can be made more useful by the inclusion of other social norms such as with the subjective norm, which is also adapted from TRA. The result showed that the combination of the two theories allows for a better understanding of the determinants that motivate IT staff to comply with a privacy policy related to EMR. Future research may further refine our proposed model to better predict other hospital employees’ compliance with an institutional privacy policy. Further, our study revealed that perceived vulnerability and perceived severity can stir IT staff’s fear regarding the threat of EMR breaches, and fear arousal mediates with intention to form an adherence toward a privacy policy. Future studies may be used to explore the role that fear arousal plays in those relationships that are in conjunction with perceived vulnerability, perceived severity, and protection motivation to obtain improved understanding.
Practical Implications
There are also several practical implications that may be derived from our study. First, the support of fear arousal may imply that hospitals can initiate EMR privacy-protection awareness programs to elicit an IT staff member’s sense of possible deleterious consequences resulting from the threat of EMR breaches. These privacy-protection awareness programs may be concentrated on the belief that vulnerability to, and the severity of, negative consequences are directly related to the threat of EMR breaches. A stronger emphasis can be placed on the direct probability of EMR breaches because perceived vulnerability had the highest influence on fear arousal. IT staff members may, thus, undergo a rational bout of emotional fear, which can in turn realize adherence to privacy policy to diminish the perceived threat. Furthermore, an overriding support of response efficacy may demonstrate that the above-mentioned privacy-protection awareness programs have the marked ability to educate the IT staff to the purpose, and as to the effects of, privacy policy implementation. This demonstration can help the IT staff understand the significant benefits of a privacy policy and exactly how such a privacy policy can settle the threat of possible EMR breaches. The significant result of self-efficacy may also imply that these privacy-protection awareness programs have the potential to equip individuals with sufficient knowledge, skills, or tools requisite for compliance with a stated privacy policy. Both the implications for response efficacy and self-efficacy can convince IT staff members to have positive feelings regarding any personal adherence to privacy policy. With exhibited positive attitude, IT staff are more likely to comply with a privacy policy specifically geared to EMR. Our results further demonstrate that subjective norm affects IT staff’s intention to adhere to privacy policy. Hence, managers can improve IT staff’s compliance intention by enhancing the relative privacy climate in hospitals and encouraging colleagues to advocate compliance with a privacy policy for EMR, as IT staff’s compliance intention can be motivated by the opinions of supervisory staff, colleagues, and also the general staff of both small-scale and large-scale medical record departments.
Limitations
Several common limitations may exist in this study. First, the sample is drawn from only 7 medical centers in Taiwan, and it does not comprise a more representative sampling. Consequently, inferences to the larger population cannot be safely made. Furthermore, the survey conducted in this study was based on self-reporting rather than through observation or through the recording of participants’ routine behavioral patterns. We did not investigate the actual compliance behavior of IT staff as it might occur. Future research can, thus, investigate the issue to better elucidate the relationships among these reported constructs.
Conclusions
By integrating PMT and TRA, our study proposed and then empirically validated a model to investigate compliance with EMR privacy policies among hospital IT staff members. Regarding the constructs adopted from PMT, perceived vulnerability and perceived severity, both variables in the threat appraisal process, significantly explain the IT staff’s fear arousal concerning the threat of EMR breaches. Furthermore, most variables belonging to the IT staff’s coping appraisal process (ie, response efficacy and self-efficacy) also significantly predict the IT staff member’s intention to comply with stated privacy policy in addition to response cost. The construct from TRA, namely subjective norm, also significantly predicts the IT staff’s intention to comply with a given privacy policy.
The results of this study add to the literature in several ways. First, our study contributes to the literature of EMR privacy policy by integrating PMT and TRA, which may provide a theoretical basis useful in examining privacy policy adherence intentions. Second, our study confirmed that perceived vulnerability and perceived severity may also be regarded as predictors of fear arousal 36 instead of protection motivation.30,31 Such factor structure may provide a different perspective useful toward an understanding of behaviors related to overall privacy-policy-compliance issues. Third, the findings of this study also provided recommendations for health authorities and hospitals in their planning and design of effective strategies to improve IT staff adherence to privacy policy to ensure the overall safety of EMR.
Footnotes
Appendix
A Comparison of Theoretical Models Used for Organizational Policy Compliance.

| Literature | Dependent variable | R 2 | Significant predictors | Theory | Sample |
|---|---|---|---|---|---|
| Ifinedo 38 | Information systems security policy (ISSP) compliance intention | 0.70 | Self-efficacy, attitude toward compliance, subjective norms, response efficacy, perceived vulnerability | Theory of planned behavior + PMT | Multiple industries |
| Vance et al 43 | Intention to comply with security policy | 0.44 | Perceived severity, rewards, response efficacy, self-efficacy, response cost | PMT + Habit | One municipal organization |
| Sommestad et al 33 | Intention for IS compliance | 0.36-0.45 | Perceived norm, perceived behavioral control, Threat appraisal, coping appraisal, anticipated regret | PMT + theory of planned behavior | One defense research organization |
| Son 59 | Compliance | 0.42 | Computer self-efficacy, perceived legitimacy, perceived value congruence | Deterrence theory | Multiple industries |
| Ifinedo 56 | ISSP compliance behavioral intentions | 0.61 | Attitude toward ISSP compliance, subjective norms, locus of control, self-efficacy | Theory of planned behavior + social cognitive theory social bond theory | Multiple industries |
| Liang et al 57 | Compliance behavior | 0.35 | Punishment expectancy, promotion focus × reward expectancy, prevention focus × punishment expectancy | Control theory + regulatory focus theory | Iron and steel industries |
| Lowry and Moody 58 | Intention to comply with new IS policy | 0.57 | Existing organizational formal control, new IS policy mandate, reactance to new IS policy | Control theory + reactance theory | Multiple industries |
Note. PMT = Protection Motivation Theory; IS = Information Systems.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work has been supported by the Ministry of Science and Technology (Grant MOST-105-2410-H-214-008-MY2), Taiwan, R.O.C.
