Abstract
Understanding the diffusion of military capabilities is a central issue in international relations. Despite this, only a few works attempt to explain this phenomenon, focusing on threats. This article explains why threats alone cannot account for cybercapacity-development diffusion and introduces a more consistent explanation: the role of alliances. Allies with cybercapacity help partner-countries without cybercapacity start developing their own capacity to increase the alliance’s overall security by reducing mutual vulnerabilities in cyberspace. Partner-countries that lack cybercapacity are eager to accept this option because it is more favorable than developing cybercapacity on their own. Partner-countries may also start investing in cybersecurity to reduce the likelihood of being abandoned in other, conventional, domains. My new cross-sectional time-series dataset on indicators of a state’s cybercapacity-development initiation for 2000–18 provides robust empirical support for this argument and offers important implications for scholarship on arms, allies, and diffusion.
Understanding the diffusion of military capabilities is a central issue in international relations because it has important implications for global peace and stability. Since the 1990s states have overtly started developing their military cybercapacity, which I define as the ability of a nation-state’s military to effectively conduct operations in cyberspace, including defense of its own networks and systems from cyber-threats and execution of offensive cyber-operations for various purposes, including intelligence gathering and disruption of adversarial networks. Despite the significance of military cybercapacity for international security, few works have attempted to explain what drives its global spread.
Building on prior scholarship on the determinants of conventional military capacity (Early, 2014; Fuhrmann and Horowitz, 2017; Posen, 1984), most existing studies focus on the neorealist model, which highlights a state’s external threat environment and its material constraints as the main explanations (Calderaro and Craig, 2020; Gomez, 2016). But this explanation does not seem sufficient. If a state’s wealth conditions its ability to develop capacity to address threats (Nordhaus et al., 2012), we should have seen states with similar resources initiating cybercapacity investment at the same time, with wealthier nations preceding less wealthy ones. But some instances defy this: resource-strapped nations (e.g. Bulgaria and Albania) started developing their capacity around the same time as some resource-richer nations (e.g. Denmark and Estonia), whereas countries similar in their resource bases (e.g. Lithuania and Armenia) initiated this process more than a decade apart.
To explain why and when nations start developing their military cybercapacity, this article introduces the role allies play as drivers of this capacity-development initiation. Building on the diffusion literature, (Horowitz, 2010; Simmons and Elkins, 2004; Simmons et al., 2018; Shipan and Volden, 2008), I argue that, while threat and resource levels do play a significant role, a state’s decision to begin developing its cybercapacity is most reliably a function of its allies’ cybercapacity-development initiation for the following reasons.
Allies with cybercapacity have an incentive to help their partner-countries without this capacity develop cybercapacity in order to increase the alliance’s overall security. Given the peculiarities of cyber-capabilities, an alliance’s overall cybersecurity amounts to reducing mutual vulnerability in cyberspace. Instead of sharing and transferring capabilities to weaker partner-countries like in the conventional case, allies have an incentive to help partner-countries without cyber-capabilities build cyber-capabilities. Partner-countries are eager to accept this assistance because it is a more favorable option than developing such capabilities on their own. Partner-countries that lack cybercapacity and are also weak in other, conventional domains, have an additional incentive to develop cybercapacity, reducing the probability of being abandoned in those other domains. Partner-countries who cannot afford to develop certain – often extremely expensive – conventional capabilities (Gannon, 2021) might decide to develop their cybercapacity as a bare minimum contribution to their alliance’s military strength in order to continue to reap alliance benefits in conventional domains.
To test this theory, I have collected the first comprehensive cross-national, time-series data for 198 countries, from 2000 and 2018, on state organizations – specifically Ministries/Departments of Defense (MoD/DoD) – that had added cybersecurity to their missions during the studied period. I focus on overt organizational mission change, rather than publicly attributed cyber-operations, as a proxy for capacity-development initiation because the former identifies a publicly visible intent to increase organizational capacity, in terms of a state’s ability to readily produce its military capabilities and not simply to exploit an isolated, time-limited vulnerability, as is the case for non-reproducible cyber-operations (Kostyuk, 2021). Since I am interested in the initiation of military cybercapacity development, I focus on MoD/DoD – rather than on the specific agencies within these departments that might be primarily responsible for the new cyber mission – because the departments themselves are the umbrella organizations ultimately responsible for defending national interests against cyber-threats. I also remain agnostic about how quickly or effectively the organization develops cybercapacity and when or whether that capacity becomes operational.
Consistent with my theory, I find that initial military-cybercapacity development by a country’s allies is associated with an increased probability that the country starts developing its own capacity. Importantly, I show that, when states start developing their capacity, both diffusion mechanisms – imitation and learning – are at work. Empirical support for the imitation mechanism suggests that some countries tend to rush to start developing their cybercapacity immediately after their most powerful ally has started developing its own, while empirical support for the learning mechanism suggests that some countries tend to take their time when initiating cybercapacity development, paying particular attention to the entire group of their allies, rather than just the most powerful one(s).
While my results present only correlations – not causation – they withstand a number of robustness checks. Furthermore, I gain greater leverage on the plausibility of the diffusion-via-alliance argument by demonstrating that randomly generated networks of alliances do not affect outcomes to the same extent as existing networks of alliances. Lastly, my diffusion-via-alliance explanation succeeds in predicting which countries will develop their cybercapacity next (i.e. out-of-sample prospective predictions). Using this evidence, I can confidently conclude that the existence of threats and resource availability are insufficient to explain cybercapacity diffusion. Instead, the initiation of military-cybercapacity development by a country’s military allies most consistently explains this diffusion.
This study advances our understanding of military cybercapacity-development initiation by introducing a new proxy for this initiation. Given that existing research uses case studies of large cyber-attacks as a capacity-investment indicator, these studies limit their inferences to wealthier, more powerful states and omit weaker states, which may also invest in cybercapacity development (Lindsay, 2013; Valeriano et al., 2018). Focusing on global capacity-initiation diffusion, this research explains the cyber behavior of a larger group of nations, not a few individual states. Importantly, it provides a new theory explaining why, when, and how nations develop their military cyber-capabilities. In addition, the opacity of cyber-operations has made it difficult for political scientists to substantiate pervasive theoretical conjecture surrounding cybercapacity with robust empirical data (Akoto, 2024; Oppenheimer, 2024; Shandler and Canetti, 2024; Shandler et al., 2022). This research adds a layer of empirical data and evidence to clarify the extensive speculation in the literature.
My findings also help clarify the dynamics that exists within alliances (Leeds, 2003; Olson and Zeckhauser, 1966; Snyder, 1984), by illuminating how the presence of cybercapability, which is less fungible than conventional military strength, makes countries less likely to free-ride on allies’ capabilities. Additionally, they contribute to the literature on the spread of military technologies and innovation (Fuhrmann and Horowitz, 2017; Horowitz, 2010; Jo and Gartzke, 2007) by showing that allies are both a stimulus and a source of information for military capacity development in cases when weapons supply and/or purchase are not an option. By doing so, my findings also contribute to the debate on demand/supply drivers of military technologies, showing the salience of both supply- (i.e. influence of allies as information providers) and demand-side factors (i.e. a country’s wealth) in cybercapacity diffusion. They furthermore contribute to the political science literature on diffusion 1 by showing that despite the unique features of cyber-capabilities, allies still matter in the global spread of these capabilities.
This article starts by defining state military cybercapacity and explaining the importance of studying a state’s decision to initiate the development of this capacity. Next, I describe the limits of existing explanations of military-cybercapacity drivers. I then outline my theory that a state’s cybercapacity-development initiation is primarily and most consistently a function of the cybercapacity-development initiation of its allies. I then introduce my data and empirical theory. Last, I summarize my findings and offer a discussion of the broader significance of these results.
State military cybercapacity, its initial development
This article aims to explain what drives a state’s decision to start developing its military cybercapacity. I define state military cybercapacity as the ability of a nation-state’s military to effectively conduct operations in cyberspace, including defense of its own networks and systems from cyber-threats and execution of offensive cyber-operations for various purposes, including intelligence gathering and disruption of adversarial networks. Most prior works that focus on state military cybercapacity use this concept as an independent variable to explain a state’s ability to coerce an opponent into granting concessions (Valeriano et al., 2018). The few recent publications that focus on state military cybercapacity as a dependent variable prioritize studying the full evolution of the state military cyber apparatus, explaining dynamics for cyber forces across militaries, for instance (Blessing, 2020).
Studying a state’s initial decision to develop its cybercapacity within its military is important for the following three reasons. First, this research extends theories of weapons proliferation beyond a predominant focus on nuclear weapons (Jo and Gartzke, 2007), drones (Fuhrmann and Horowitz, 2017), and other emerging technologies, to a less studied realm, improving our understanding of military decisionmaking processes and their implications for global politics. Second, the majority of prior studies limit their inferences to wealthier, more powerful states (Lindsay, 2013; Valeriano et al., 2018). Even the few studies that focus on militaries that have been integrating cyber technologies are limited in their scope to about a third of the world’s countries. By focusing on global capacity diffusion, this research explains the cyber behavior of a larger group of nations, providing a more inclusive view of worldwide developments. Finally, by providing a better idea of how states decide to allocate their limited budgets, it offers insight into how they view the various challenges and opportunities presented by cyberspace. Because cyberspace affects every area of modern society, a state’s decision to allocate funds to its military institutions rather than, say, its economic institutions, suggests that a state perceives cyberspace more as a source of threats than of economic development, leading to a cyber strategy centered on ‘guns’ and not ‘butter’. Understanding which factors drive this particular decision have important implications for the global economy, peace, and stability.
Limits of existing explanations of military-cybercapacity drivers
The question of how conventional military capabilities proliferate has been a central part of international relations literature for decades (Horowitz, 2010; Huntington, 1958). Scholars interested in understanding military-technology adoption have examined the relative importance of supply- and demand-side factors (e.g. see Jo and Gartzke, 2007; Most et al., 1989). In this review, I prioritize discussing the limits of the neorealist model, which remains the primary explanation of cybercapacity drivers and mainly focuses on a state’s material constraints (supply) and its threat environment (demand). 2
In particular, the neorealist position argues that a state’s threat environment explains the proliferation of its conventional capabilities (Waltz, 1979). The anarchic nature of the international system creates a security dilemma, where ‘one state’s gain in security often inadvertently threatens others’ (Jervis, 1978: 170). For instance, if state A increases its security through building arms, state B is forced to build its own arms because B is not certain that A will not use its capabilities against B. In this way, mutual insecurity drives an arms buildup.
If states develop their conventional capabilities in reaction to threats, then we should see states that face similar threats building similar militaries (Goldman and Andres, 1999; Waltz, 1979). In practice, however, convergence to similar conventional capabilities does not always take place (Gannon, 2021). Neorealists argue that any lack of ‘sameness’ is due to each state’s resource constraints that condition its ability to build arms through increased military spending (Nordhaus et al., 2012). Thus, if resource-rich A and resource-poor B face the same level of external threats, A is able to invest more in military capability and is therefore more likely to develop the same military innovations as its adversaries (like-for-like development).
Focusing on the neorealist position, scholars argue that states’ external security concerns over increasing cybercapabilities among adversaries combined with their material constraints drive states’ likelihood to develop their own cybercapabilities (Calderaro and Craig, 2020; Gomez, 2016). But if, as neorealists argue (Resende-Santos, 2007: 5), threats and material constrains explain the timing, pace, and scale of military cybercapacity development, then we should see countries with similar threats and similar resource bases initiate military-cybercapacity development around the same time. However, in reality, resource-constrained Bulgaria and Albania started developing their cybercapacity around the same time as resource-rich Denmark. But countries similar in their resource bases initiated this process at different times (e.g. Lithuania (2008) and Armenia (2019)).
This example represents a larger pattern: given similar threat environments, (1) some states with dissimilar resource bases respond to their threat environment with like-for-like capacity initiation; and (2) some countries with similar resource bases do not respond to their threat environment with like-for-like capacity initiation. Given these realities, the neorealist explanation, which prioritizes threats and resources, seems insufficient to elucidate global military-cybercapacity initiation diffusion. If this diffusion is not primarily and consistently based on the threat environments countries face and the resources they have to address them, what drives it?
Allies and global diffusion of military cybercapacity
I view the global spread of capacity-development initiation as a process of diffusion, defined as a ‘prior adoption of a trait or practice in a population [that] alters the probability of adoption for remaining non-adopters’ (Strang, 1991: 325). Given this definition, the goal of this article is not to explain why the US, as the first mover, started developing its cyber power. Instead I aim to elucidate why certain countries decided to follow its lead and why certain countries did not.
I argue that a country’s allies influence this process – nations start developing their cybercapacity after their allies have already initiated this process. It is important to clarify that when I refer to allies, I mean only defensive allies – those that assist each other ‘militarily in the event of attacks on the ally’s sovereignty or territorial integrity’ (Leeds, 2005: 11).
A natural question to ask is: who is driving the diffusion process: allies who have some cyber-capabilities or partner-countries that do not have cyber-capabilities but would like to acquire them? I argue that both push and pull factors are at play. Allies with cyber-capabilities push or incentivize their partner-countries to develop cyber-capabilities. Partner-countries without these capabilities pull or develop their own cyber-capabilities after their allies. Since both sets of actors have an incentive to participate in this process, I argue that it does not matter who moves first; either of them can be the initiator as long as the other actor is at least agnostic to the decision. Let us examine the intuition behind the actions of each set of actors in turn.
Allies with cybercapabilities
Literature on conventional capabilities argues that in order to increase an alliance’s overall security, strong allies (i.e. allies with capabilities) have an incentive to share and transfer their capabilities to weaker alliance members (i.e. those without capabilities) (Yarhi-Milo et al., 2016). Given the peculiarities of cyber-capabilities, an alliance’s overall cybersecurity amounts to reducing mutual vulnerability in cyberspace. Instead of sharing and transferring capabilities to weaker partner-countries like in the conventional case, allies with cyber-capabilities have an incentive to help those without cyber-capabilities build their own cyber-capabilities. Below, I unpack this further.
Many actors who are connected to the Internet share the same types of vulnerabilities as they rely on the same types of systems and networks. We have seen how these common vulnerabilities have been exploited time after time. For example, the same malicious code that targeted Ukrainian power grids in 2015 and 2016 was later found in the US grid system (Koehler, 2018). In 2020, hackers targeted the Texas-based SolarWinds company that provided software used by thousands of enterprises and government agencies worldwide (Willett, 2021). These examples suggest that an adversary can exploit a weak partner-country’s unprotected systems to target its strong ally’s systems. Mutual vulnerability is a unique feature of cybersecurity. Given this peculiarity, an alliance is as cyber-strong as its weakest partner-country’s cybersecurity.
To increase the alliance’s overall cybersecurity, a cyber-strong ally has an incentive to work with its cyber-weak partner-country to make it cyber-stronger. In the case of conventional capabilities, stronger allies can share and transfer these capabilities to weaker partner-countries. In other words, the partner-country is able to free-ride off the ally’s conventional capabilities – rely on the ally’s capabilities without developing those of their own. The peculiar features of cyber-capabilities – a sharper decay function of their effectiveness, given adversarial adaptive learning; and higher asset specificity, which often requires tailoring to a specific target (Weiss, 2012) – make it difficult to free-ride off the ally’s cyber-capabilities. Here is why.
If an ally decides to use its cyber-capabilities to exploit a vulnerability in an adversarial network to help the partner-country, there is a higher likelihood that the adversary will discover this vulnerability and will close it, making the cyber-capability obsolete. Given this sharper decay function of the effectiveness of cyber-capabilities compared with conventional military tools, the ally is unlikely either to use its cyber-capabilities against an adversary on the partner-country’s behalf or to share its cyber-capabilities with the partner-country. High asset specificity of cyber-capabilities further complicates free-riding. A tank, for instance, has low specificity because it can be readily used against various targets with relatively similar effects. Importantly, once one learns how to use a tank, one can keep using it until a different version of a tank is invented (which often takes years). As a high specificity asset, code, on the other hand, needs to be tailored to different targets. It also requires more frequent learning and updating, given that actors keep working on improving their cyber-defenses.
This inability to free-ride means that a partner-country needs to develop its own cyber-capabilities. As explained earlier, the ally is willing to help. Given the peculiarities of cyber-capabilities, the ally is unlikely to share its exact cyber tools with the partner-country. Instead, the ally is willing to share its knowledge and expertise in the form of training, joint military exercises, and institutions (Smeets, 2022a). The ‘hunt-forward’ operations during which the US government receives consent from other countries to work on their networks and systems to discover and close vulnerabilities is one example of such assistance. Not only is the US government able to make its allies cyber-stronger via hunt-forward operations, but the US government is also able to discover vulnerabilities that it can apply to its own systems, cyber-proofing them in advance. Through exercises like Cyber Coalition, NATO works with member-states to improve interoperability and resilience of their cyber-capabilities. The cyber-capable members of the Organization of American States and the Arab League help their cyber-less partners develop national cybersecurity strategies and build new organizations responsible for cybersecurity based upon their examples.
Partner-countries without cyber-capabilities
A country’s main goal is to increase its security; this is true for both conventional and cyber-capabilities. Literature on conventional military capabilities distinguishes two options that a country can use to increase its security: form an alliance or arm itself (Waltz, 1979). Free-riding off the allies’ capabilities is a relatively quick way of increasing one’s security. But that option is off the table given the difficulty of free-riding in cyberspace. As a result, the country is left with arming itself by either buying or making cyber-capabilities. Buying cyber-capabilities is quite costly due to the high asset specificity of cyber-capabilities which often requires tailoring to a specific target, opaqueness of the market for cyber-exploits (Perlroth, 2021), and a recent move by governments and the industry to implement tighter controls on the sale and development of hacking tools. Alternatively, the country can make its own cyber-capabilities.
Works on the diffusion of conventional military capabilities show that nations tend to develop their capabilities either after adversaries or allies have done so (Posen, 1984; Resende-Santos, 2007; Waltz, 1979). Following adversaries requires a nation to develop capabilities on its own after observing its adversaries. Given that mutual vulnerability drives allies’ incentive to help their weaker partner-countries, working with allies on developing cyber-capabilities is a more favorable option than developing such capabilities on their own or buying them.
Weaker partner-countries’ fear of abandonment is another incentive that drives the cybercapacity-initiation diffusion process through an alliance network. Prior research shows that to reduce the fear of abandonment, a country may attempt to increase its value to the ally by developing a particular capability on which the ally may become dependent (Gannon, 2021). Specifically, small nations tend to specialize in niche conventional capabilities to increase larger partners’ commitment to their security.
Using this logic, a country that is not able to contribute sufficiently in terms of conventional capabilities, due to high costs of these capabilities or other constraining factors (Gannon, 2021), might decide to develop cybercapacity, viewing this as the bare minimum it can do (vis-à-vis military-capability development) to continue to reap alliance benefits in conventional domains. Estonia’s cybercapacity development illustrates this point. Even prior to Russia’s 2007 cyber-attacks, Estonia worried that large NATO allies might fail to provide support in the event of a conventional Russian attack. The 2007 attacks only increased this sense of urgency. To boost its value to NATO partners, Estonia has spent the last 15 years developing its cybercapacity.
Due to the relative non-fungibility of cyber (as compared to conventional) tools, NATO’s reliance on Estonia’s cybercapacity does not imply that NATO partners can simply apply Estonia’s cyber-defenses to its networks; instead, partners tend to learn Estonia’s defensive techniques via meetings and military exercises, often sponsored by the NATO Cooperative Cyber Defence Centre of Excellence, located in Estonia’s capital, Tallinn. Neither is it the case that Estonia developed any cyber weapons that its NATO partners could not have developed on their own. However, by creating cyber-capabilities of its own, Estonia reduced the probability that NATO nations will abandon it, despite the country’s persistent weakness in other military domains.
Mechanisms of capacity-initiation diffusion
The above discussion suggests that a state’s cybercapacity is primarily and most consistently a function of the cybercapacity of its allies. Allies are both a stimulus and a source of information for military capacity development, suggesting the importance of supply-side factors for diffusion. If a government’s decision to develop its capacity is systematically conditioned by its allies’ prior decision to develop this capacity, what mechanism drives this process? Two mechanisms – imitation and learning – seem to be the most relevant. 3
Imitation involves copying the actions of another state to appear more like them (Simmons et al., 2006). Scholars point to two characteristics of imitation. First, nations tend to imitate others that lead in a particular policy area. Second, imitation tends to begin soon after the leading state adopts its policy as nations rush to quickly follow without waiting to see how effective policies are in the leading state. As Shipan and Volden (2008) describe, imitation has short-lived effects. These two characteristics suggest that if imitation drives the initial capacity diffusion, we should see nations rush to start developing military cybercapacity shortly after their most cyber-capable allies do. Hypothesis 1 summarizes this discussion.
Hypothesis 1 (Imitation mechanism): The likelihood of a country starting to develop its military cybercapacity increases in the period immediately after its most capable allies started developing this capacity.
I next interrogate the possibility that learning drives diffusion. Learning involves the adoption of policy solutions that other states have proven successful (Simmons et al., 2006; Walker, 1969). 4 This definition points to two unique features that help us empirically distinguish learning from imitation. First, unlike imitation, learning focuses on a group of nations, not a few, most capable, countries (i.e. leaders). Instead of focusing on only the most capable allies (e.g. the United States), a country will pay attention to cybercapacity development by all allies (e.g. NATO countries). Second is the timeliness of the adopted change. Learning yields more delayed adoption or has long-lived effects, as states choose to observe the effects of a policy on a group and do not rush to quickly imitate the leader. These two characteristics suggest that if learning drove capacity diffusion, we should see some time pass before nations started developing military cybercapacity after a group of their allies have done so. Hypothesis 2 summarizes this discussion.
Hypothesis 2 (Learning mechanism): The likelihood of a country starting to develop military cybercapacity increases as its allies started developing this capacity.
Data and empirical strategy
Here I briefly introduce my data and empirical strategy. Online appendix sections 1–3 include more details.
Dependent variable: Initiation of the military cybercapacity development
Some scholars have used publicly attributed cyber-operations as the main proxy for state military cybercapacity (e.g. Center for Strategic & International Studies’ Significant Cyber Incidents Data). 5 This approach, however, has two limitations. First, considering that cyber operations strive for secrecy and deception and often require these characteristics to succeed (Gartzke and Lindsay, 2015), discovery and attribution can be understood to constitute failure. Meanwhile, there is the possibility that other states have succeeded in keeping their operations secret. As a result, using attributed cyber-operations as a proxy for capacity would, misleadingly, suggest that states that are better at keeping their operations secret have less capacity than those with many known operations. Second, focus on cyber-operations as a proxy for cybercapacity assumes that countries that have such capabilities are likely to use them. The example of nuclear weapons suggests that this is not necessarily the case.
Scholars have also used institutions (e.g. the presence of programs devoted to weapons development) as indicators of military capabilities (Early, 2014; Fuhrmann and Horowitz, 2017; Kostyuk, 2021). Recent research, however, shows that institutionalization does not necessarily correlate with a state’s actual capacity (Smeets, 2022b). For instance, most military cyber commands may be ‘paper tigers’, with a high level of organizational investment yet very little capacity to mount cyber operations in practice. Thus, it remains unclear whether, when, or to what extent institutionalization (investment in a state’s organizational capacity) will be followed by operational capacity. For instance, it took the US cyber command about eight years to develop its actual cyber-capabilities and become fully operational. This article, therefore, in seeking to identify the determinative factors of a state’s decision to begin development of military cybercapacity, posits institutions not as a proxies for a country’s military cybercapacity but as proxies for that development-initiation decision. When any developed capacity will be ready for use in operations, and how effective it might be, lie beyond the scope of this article.
Specifically, my dependent variable is the addition of a new cybersecurity 6 responsibility to a Ministry/Department of Defense (MoD/DoD) 7 during the 2000–18 period, based upon State Cybersecurity Organizations data (v1.0). 8 I call this variable Capacity Initiation. A country is coded as a 1 if, during the 2000–18 period, a new cyber responsibility was added to its MoD portfolio and 0 if it was not. Generally, an MoD’s mission is to ensure a nation’s security. I argue that, when it adds a new cybersecurity responsibility – explicitly assuming responsibility for defending national interests against cyber-threats, specifically – it constitutes a decision by the country to develop capacity within its military to address those threats. I remain agnostic about how the country will do that and whether or how quickly this capacity becomes operational after the decision is made. Ninety-two nations out of the 160 nations 9 included in this analysis added cybersecurity as responsibilities of their MoDs during this time. Figure 1 displays the global initiation of military cybercapacity during the four five-year periods.
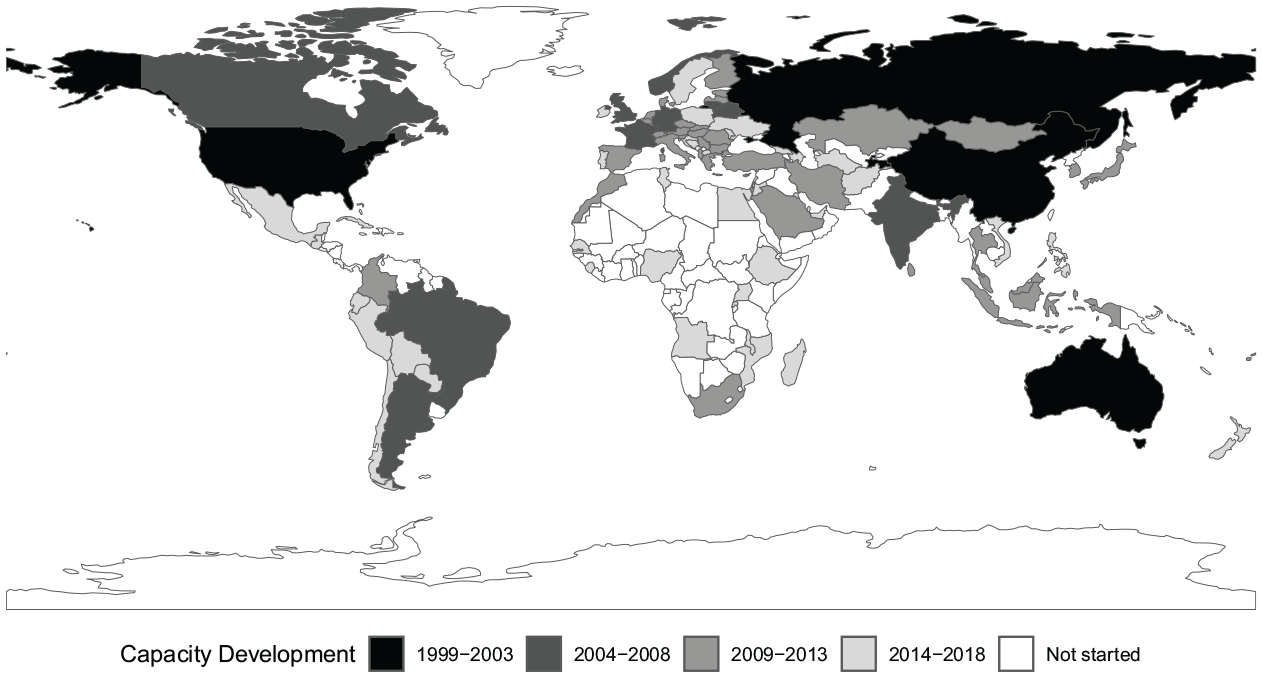
Initiation of the military cybercapacity development (1999–2018).
Even though I used well-established practices when creating my dependent variable (Woolley, 2000), the fact that my data are necessarily limited to what is publicly observable – i.e. to overt organizational mission change – might constrain the validity of my findings to some degree. It is possible that some states covertly add cyber responsibilities to their defense organizations, and, because such covert organizational change is not captured in my data, my findings regarding determinative factors of capacity-development initiation do not apply to any such cases. However, this is nowhere near as large a threat to validity for my study as is the observability (discovery and attribution) of cyber-operations for studies that have attempted to use cyber-operations as proxies for state cybercapacity, largely because organizational changes are far less likely than cyber-operations to be covert.
Not only is secrecy less critical to the success of organizational change than of cyber-operations, shifts in organizational focus also require more significant shifts in budget and personnel allocation than do cyber-operations, obliging a government to communicate to the public – if only in general terms – its rationale for this shift. For instance, in 2022, when President Biden requested from Congress an 11% increase ($10.9 billion) in cybersecurity funding over the previous year’s request, he publicly announced that the increase was intended to address ‘potential Russian cyber-attacks amid the war in Ukraine’ (Schaffer, 2022). Generally, countries identify such changes in announcements, press releases, military doctrines, or national strategies, among other venues. Another critique of focusing on public information could be that, since allies might have access to private information via unofficial channels, they do not necessarily need to wait for a public announcement to know what their ally is doing. However, as the Snowden and more recent US leaks have shown, this is not necessarily the case.
Independent variables: Influence of allies
As explained earlier, the roles of allies differ in capacity development process depending which diffusion mechanism is at work. To remind, imitation is concerned with short-lived or immediate influence of a country’s most capable allies (Imitation of Allies) whereas learning is concerned with long-lived influence of a country’s allies (Learning after Allies). To construct these variables, I need the following three components: allies, major powers, and short/long-lived effects. To identify allies, I use the Alliance Treaty Obligations and Provisions (v5.0) data. To identify which allies are major powers, I use the Correlates of War project’s State System Membership index. 10 Lastly, to account for short-lived effects I consider the fraction of the country’s allies that have started developing their cybercapacity in a year prior to the year during which the country starts developing its cybercapacity. To account for long-lived effects I consider the fraction of the country’s allies that have started developing their cybercapacity at least two years prior to the period during which the country started developing its cybercapacity.
To capture the fraction of the country’s allies that have started developing their cybercapacity, I follow Simmons and Elkins (2004) and use lagged network-weighted effects that capture the weighted average of a country’s allies’ initial cybercapacity development. This weight captures the importance of an ally’s influence on this country. For instance, if a nation has only one ally, then its alliance has a weight of 100%; consequently, the ally will most likely have a significant influence on this country’s military decisions. On the other hand, if a nation has 20 allies and each relationship has a weight of 5%, then the influence of an individual ally on the country’s military decisions will most likely be limited. Online Appendix Section 3.1 provides more details on how I created this weighted average effect. I also consider a number of alternative weighting schemes (see Online Appendix).
Control variables
To account for external threats, I consider the influence of adversarial initiation to develop cybercapacity. Specifically, I use short- and long-lived effects of adversaries’ initial cybercapacity development prior to the country’s decision to start developing its own cybercapacity (Adversaries’ Cybercapacity Initiation (SE/LE)). To identify the country’s adversaries in both conventional and cyber spaces, I use Maoz’s (2005) data on Militarized Interstate Disputes (MID) and Valeriano et al.’s (2018) Dyadic Cyber Incident Dataset (DCID) (v1.5). 11 To account for a country’s material resources, I use a country’s GDP per capita (logged), taken from the World Bank (GDP per capita).
I also include a number of additional supply- and demand-side factors that are known to contribute to military capacity diffusion and could influence my outcome of interest. Since democracies are more transparent, I account for the effect of the country’s regime type. I use Marshall, Gurr and Jagger’s (2019) Polity IV score to create a dummy variable that takes the value of a 0 if this score is less than 6 representing an autocracy, and 1, if this score is more than equal to 6 representing a democracy (Democracy). 12 Since cybercapacity development can be a matter of prestige (Smeets, 2017), I use a commonly used measure of prestige – a country’s membership in intergovernmental organizations (IGOs) whose primarily focus is security, defense, and peace from Pevehouse et al. (2020) (Membership in Military IGOs). 13 Since cyber-capable NATO countries are quite proactive in encouraging capacity development by their cyber-less members, I include a dummy variable for NATO countries (NATO Member).
Event history analysis: Cox proportional-hazards model
I use an event history model 14 that focuses on the spell of time until a country develops its military cybercapacity. Specifically, I employ a Cox Proportional-Hazards (CPH) model which identifies conditions that create a greater risk of capacity development. 15 This semi-parametric model leaves the baseline hazard unspecified, allowing it to handle changes in absolute rates of capacity development over time. My unit of analysis is the country-year. Following prior research (Blessing, 2020), I chose to begin the analysis in 2000 due to the fact that the Internet became an international commercial network around that time, at least in Western Europe and the US. The analysis ends in 2018. If the country has not developed its capacity by 31 December 2018, it is right-censored in my dataset. Lastly, since many of the covariates change over time, I use interval censoring to capture time-varying covariates (Therneau and Grambsch, 2000).
Findings
My central finding is that the decision by a country’s military allies to initiate the development of military cybercapacity most consistently explains the global diffusion of military cybercapacity initiation. Table 1, which presents the results, shows positive, statistically significant associations between Imitation of Allies and Capacity Initiation, as well as between Learning after Allies and Capacity Initiation with hazard ratios consistently larger than 1, 16 suggesting that both diffusion mechanisms – imitation and learning – are at work. Below, I review these findings in detail.
Influence of a country’s allies’ military cybercapacity initiation on its decision to start developing its own military cybercapacity (hazard ratios).
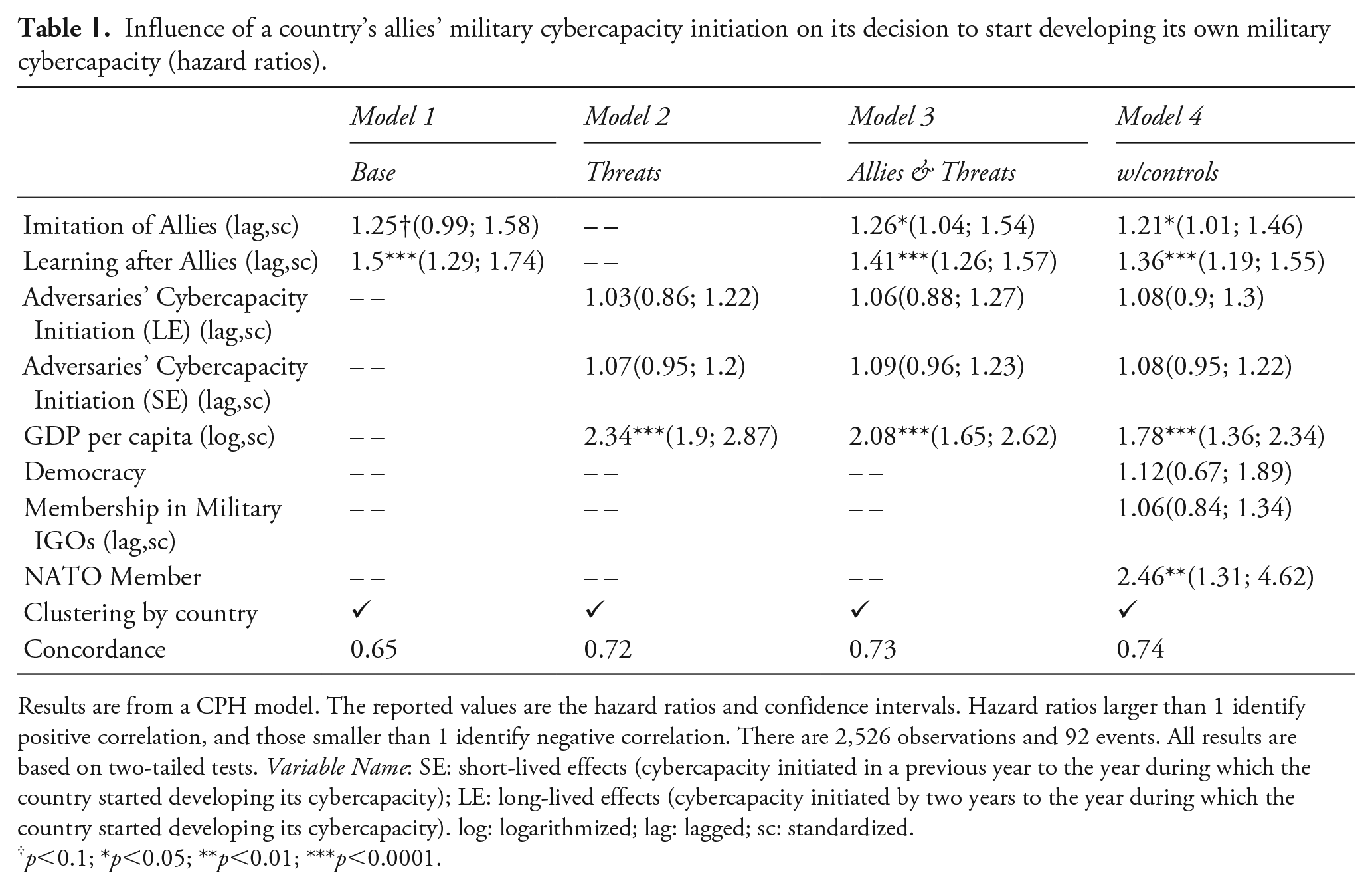
Results are from a CPH model. The reported values are the hazard ratios and confidence intervals. Hazard ratios larger than 1 identify positive correlation, and those smaller than 1 identify negative correlation. There are 2,526 observations and 92 events. All results are based on two-tailed tests. Variable Name: SE: short-lived effects (cybercapacity initiated in a previous year to the year during which the country started developing its cybercapacity); LE: long-lived effects (cybercapacity initiated by two years to the year during which the country started developing its cybercapacity). log: logarithmized; lag: lagged; sc: standardized.
p<0.1; *p<0.05; **p<0.01; ***p<0.0001.
Model 1 accounts only for the influence of allies’ cybercapacity initiation. A positive, marginally statistically significant correlation between Imitation of Allies and Capacity Initiation (HR:1.25; CI: (0.99; 1.58)) suggests that imitation is likely to take place, providing preliminary support for H1. A positive, statistically significant correlation between Learning after Allies and Capacity Initiation (HR: 1.5; CI: (1.29; 1.74)) suggests that learning is likely to take place, providing preliminary support for H2. Both mechanisms confirm the influence of allies on the studied process.
In addition to allies’ cybercapacity, Model 2 also accounts for the influence of external threats and a country’s material constraints – the two alternative explanations suggested by the previous research. I find no statistically significant association between Adversaries’ Cybercapacity Initiation (SE/LE) and Capacity Initiation (HR: 1.03; CI: (0.86; 1.22); and HR: 1.07; CI: (0.95; 1.2)). A positive, statistically significant correlation between GDP per capita and Capacity Initiation (HR: 2.34; CI: (1.9; 2.87)) suggests that countries are likely to be constrained by their material resources when considering the development of military cybercapacity. Each additional unit (standard deviation) increase in a country’s GDP per capita (log) increases the hazard that the country will develop its cybercapacity by more than twice.
Adding the influence of allies’ cybercapacity to this model (Model 3), I find a positive, statistically significant association between the variables that identify the influence of allies’ cybercapacity and the country’s decision to develop its capacity. This result suggests that, more likely than not, an increase in allies’ capacity accounts for the global capacity diffusion (HR: 1.26; CI: (1.04; 1.54) and HR: 1.41; (1.26; 1.57)). Last, I add a number of additional controls (Model 4). Similarly to Model 1 and Model 3, allies’ cybercapacity initiation is positively statistically significant with Capacity Initiation (HR: 1.21; CI: (1.01; 1.46) and HR: 1.36; CI: (1.19; 1.55)), providing additional support for the diffusion-via-alliance argument and for H1 and H2. Threats remain statistically insignificant (HR: 1.08; CI: (0.9; 1.3) and HR: 1.08; CI: (0.95; 1.22)) whereas GDP per capita remains positive and statistically significant (HR: 1.78; CI: (1.36; 2.34)). Out of all additional controls, only NATO Member is statistically significant (HR: 2.46; CI: (1.31; 4.62)). A positive, statistically significant coefficient of NATO suggests that NATO countries are about twice as likely to develop military cybercapacity as non-NATO countries.
Additional analyses
I have also conducted a number of additional analyses to further confirm the plausibility of my diffusion-via-alliance argument. Here I briefly review only a few of them; Online Appendix Section 4 includes all the details.
To gain greater leverage on the plausibility of the diffusion-via-alliance argument, I investigate the effect of an alternative network of alliances. In this set-up, I would not expect the weighted effect of this alternative network of allies to affect outcomes to the same extent that existing networks do. To create these randomized networks, I permute the position of countries within the network by sampling country names without replacement. I create 10,000 such networks and fit my model using each of them. This process builds up a null distribution for the diffusion coefficient, which I then use to estimate a p-value for a two-tailed randomization test. This allows me to understand whether the coefficients obtained from my original model are larger than would be expected if allies were randomly assigned. I reject my null hypothesis, according to which there is no difference between the observed increase in relative risk of cybercapacity initiation from allies and the same risk associated with the randomly generated network of alliances (p<0.05;). This result further confirms the plausibility of my diffusion-via-alliance argument.
I further confirm the plausibility of my diffusion-via alliance argument by considering a negative control, or an outcome that I do not expect to be related to cyber conflict. I use Ministries of Education because they deal with the issues related to the internet, but, unlike Ministries of Defense that are responsible for cyber conflict, Ministries of Education aim to develop a framework for the protection of children as the latter engage with the Internet. I find that allies’ military cybercapacity initiation is unlikely to play a role in the development of cyber education.
I also consider two alternative explanations that I am able to refute with robust empirical evidence. First, given that the NATO countries have been actively building their military cybercapacity over the last decade, I have considered the possibility that the capacity-development initiation by NATO countries is driving the results. Second, if the growing prevalence of cyber as a military issue leads militaries to invest more in cyber, I would naturally see that the number of countries that have started developing their cybercapacity has grown over time; but this default pattern would have nothing to do with the influence of allies. I find no support for either explanation.
Identifying future developers of military cybercapacity
To what extent does my model predict future events? I identify the likely candidates for 2019 and 2020, using the estimates from Model 4 in Table 1 trained on data from 2000 to 2018. Figure 2, which depicts the relative rank of countries that started developing their military cybercapacity in the years 2019 through 2020, presents the results. The y-axis displays the percentile rank (out of 100%) of relative risk for initiating cybercapacity development as predicted in Model 2 fit using data from the 2000–18 period. The 2019 and 2020 events are out-of-sample, prospective predictions. Since a CPH model provides predictions of relative (and not absolute) annual risk, I convert relative risk into percentile ranks within each year for ease of interpretation. The horizontal gray line represents the 50% percentile.
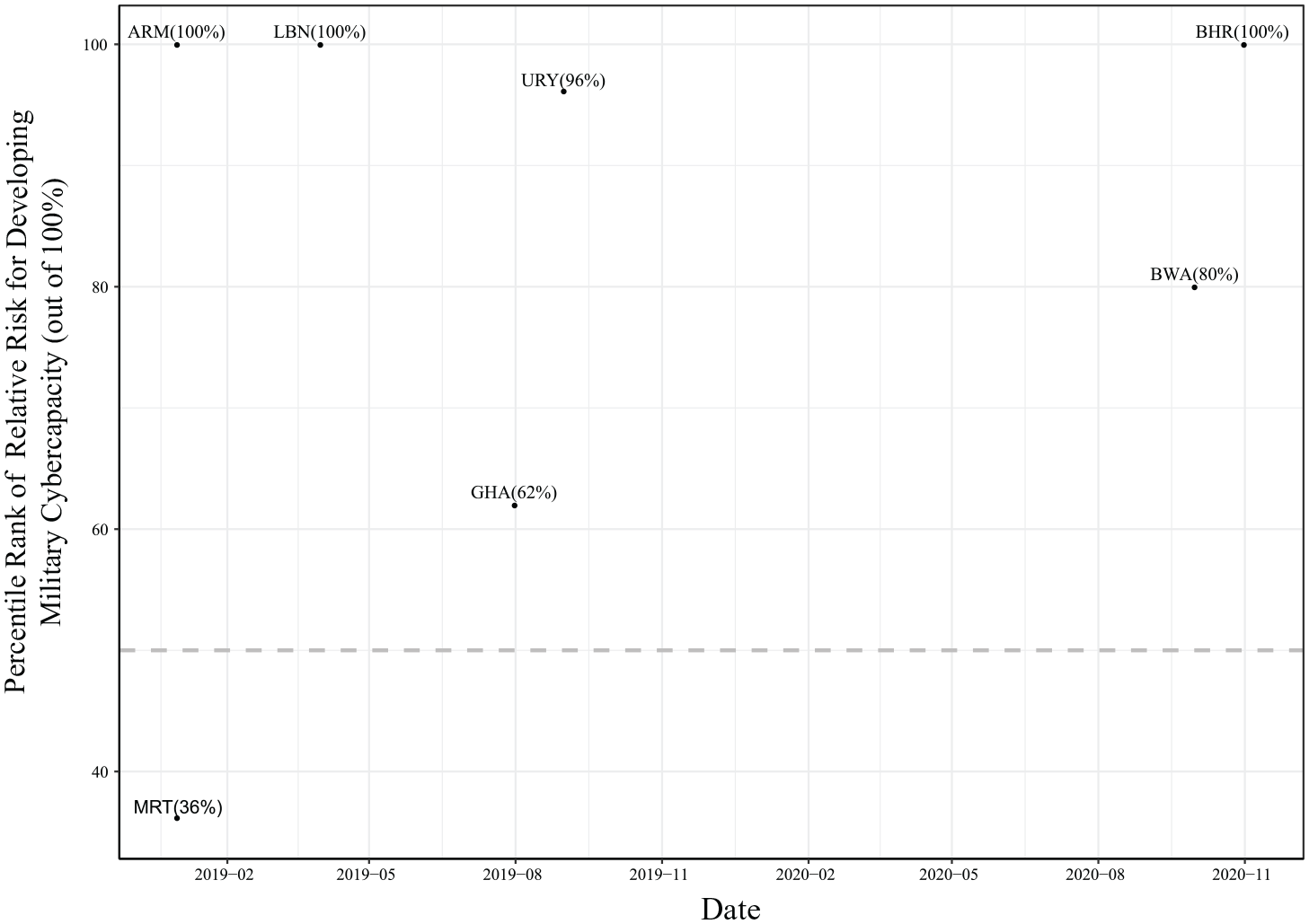
Predictions: Percentile rank of relative risk for initiating military cybercapacity development.
The obtained results illustrate the potential predictive power of my model. Specifically, of the five countries that started developing military cybercapacity in 2019, my model ranks three at least at 96%. Of the two countries that started developing capacity in 2020, my model ranks both at 80% or above. To assess overall quality of the predicted ranks, I compute the C-statistic, which identifies that the average probability that the country has an event is ranked higher than the country without an event at that time. The C-statistic (0.81, CI: (0.63–0.96)) suggests that predictions are valuable in predicting future events. 17
Discussion
This article asks a basic question: What drives a state’s decision to initiate development of military cybercapacity? Contrary to existing works that prioritize the cyberthreat environment (Calderaro and Craig, 2020; Gomez, 2016), I show that a mere presence of threats is insufficient to explain capacity diffusion. Instead, it is the presence or absence of cyber-capable allies that most powerfully conditions diffusion. Importantly, my results show that diffusion happens via both imitation and learning mechanisms. In addition to simply imitating allies, countries tend to pay attention to the effectiveness of allies’ actions. This result suggests an alternative diffusion venue, which complements earlier findings that view the development of military cyber organizations as merely symbolic (Gomez, 2016).
Since the obtained results present aggregated relationships and do not focus on exceptions to this general trend, future research should also investigate these exceptions. Moreover, while this article shows that changes in allies’ cybercapacity systematically explain state capacity diffusion, future research should investigate capacity diffusion that might not follow this general rule – e.g. capacity proliferation to criminal actors or states that mostly lie outside of the alliance system, like the United Arab Emirates.
This study has limitations shared by other observational studies that use cross-national time-series data, namely non-random assignment of the exposures, or, in this case, alliance networks used to construct diffusion exposures from lagged dependent variables. Following common practice in the discipline, I sought to minimize the potential for bias by identifying and controlling for key confounders, including a country’s wealth, and regime type, among others.
This article contributes to the literature on the arms versus alliance trade-off (Morrow, 1993; Yarhi-Milo et al., 2016). Unlike works that focus on the dichotomous choice between building your own arms and relying on your allies (i.e. Morrow, 1993), this research highlights that countries choose a third option – a mixture of the two – to address cyber-threats. But unlike existing works that focus on this third option for conventional threats (i.e. Yarhi-Milo et al., 2016), I explain why the transitory nature of cyber-operations makes the choice of relying on allies’ cyber-arms is limited at best because allies generally serve as a supplier of information and training.
This research has implications for policymakers crafting responses to challenges of the digital domain. First, my findings show that countries generally pay attention to their allies when they start publicly developing their military cybercapacity. But the influences of various alliances are not equal. This insight could be useful in helping government officials predict when and where new innovations in military cybercapacity are likely to emerge and how they will diffuse throughout the international system.
Second, my findings show that the theory of free-riding is less likely to explain the behavior of military allies when it comes to the cyber domain. In these situations, countries often must rely on their own cyber-capabilities because their allies are less likely to be able to help (Kostyuk, 2021). This self-reliance reduces both weaker allies’ fear of being abandoned by their stronger allies and the possibility that stronger allies will be entrapped into helping weaker allies. However, while the diffusion of non-fungible cyber-capabilities offers these immediate benefits, policymakers should seek ways to overcome potential hurdles: non-fungibility might complicate coordination between allies, reducing the possibility that alliance members specialize in and complement one another’s military cyber-capabilities.
Third, my findings suggest that, in addition to cyber powers, policymakers should pay attention to small and middle powers that might be more reluctant or unable to use cyber-operations to demonstrate their cybercapacity. Agencies that develop cybercapacity might send an informative signal about the state’s priorities in cyberspace. For instance, if a state develops cyber organizations within law enforcement, that demonstrates concerns with cyber-crime. If it develops them within its military, that sends the message that it prioritizes cyberwarfare. If it develops them within its Ministry of Foreign Affairs, that indicates that it is working on diplomatic means to address challenges of cyberspace. Since cyber-threats require cooperation, policymakers should also pay attention to who works with whom inside and outside the government, which will help them gain a holistic view and better understanding of how different states develop cybercapacity.
By examining the initial development of military cybercapacity, this study takes a first stab at the main causes and effects of this capacity-development initiation and advances our understanding of a state’s intent in cyberspace. Many nations started developing cybercapacity by building up their bureaucracies (92 out of 160 nations, according to the SCO data), pointing to a state’s desire to rapidly develop this capacity for military conduct. This trend might suggest that cybercapacity is analogous to a tank – something that any modern military possesses. It remains to be seen whether this capacity stops at the level of Little Willie – the world’s first tank – or advances to the level of Leopard 2A7 – one of the most advanced battle tanks in existence. As countries continue building cybercapacity, enhanced understanding of this capacity will be critical for international security.
Footnotes
Acknowledgements
I thank Jason Blessing, Andres Gannon, Erik Gartzke, Miguel Gomez, Jon Lindsay, Erica Lonergan, James Morrow, Ryan Shandler, Brandon Valeriano, Chris Whyte, Yuri Zhukov, and the participants of the Digital Issues Discussion Group. This paper was presented at the 2021 American Political Science Association conference.
Replication data
Notes
NADIYA KOSTYUK, b. 1987, PhD in Political Science and Public Policy (University of Michigan, Ann Arbor, 2020); Assistant Professor, School of Public Policy, School of Cybersecurity and Privacy, Georgia Institute of Technology (2020– ); research interests: international security, technology, cyber conflict.
