Abstract
Why did some American citizens choose to travel to fight in Syria and Iraq rather than engage in Islamic State of Iraq and Syria (ISIS)-inspired terrorism in the United States? We conducted a social network analysis (SNA) on a sample (n = 224) of extremists who either plotted ISIS-inspired attacks within the United States or attempted to travel to Syria or Iraq to join the group between 2013-2020. We test how network size, network interconnectedness, and the importance of trusted network members impact the choice of American ISIS offenders to travel or plot terrorist attacks. Our results show that Americans were more likely to choose to travel to fight when they had access to large, dense networks that were embedded with trusted associates. Those without access to similar networks abandoned their preferences for foreign fighting and instead plotted attacks within the United States. The findings provide pertinent policy implications for countering violent extremism.
From 2011 to 2016, it is estimated that at least 42,000 people traveled from 120 countries to fight alongside jihadist groups in Syria and Iraq (CISAC 2021). While estimates vary, among them were as many as 300 Americans who either traveled or attempted to travel to join the Islamic State of Iraq and Syria (ISIS; Barrett 2017; Meleagrou-Hitchens, Hughes and Clifford 2018). During the same period, nearly 100 individuals who were inspired by ISIS plotted to commit terrorist attacks in the United States. Among these was the 2016 Pulse nightclub shooting, which resulted in 49 fatalities and 53 injuries, and remains the deadliest terrorist attack on U.S. soil since 9/11. The actions taken by American jihadists to support ISIS underscore a fundamental choice that individuals make when they decide to assist foreign terrorist organizations: they can travel to be fighters in other countries, or they can stay at home and plot attacks. Both behaviors help foreign groups wage their campaigns of terror. Both involve the risk of jail or death. And both promise glory, adventure, and a sense of purpose. What, then, persuades individuals to choose one course of action over the other?
Unlike the vast body of research estimating the antecedent factors that promote engagement in violent extremism (e.g., Ferguson and McAuley 2020; Jensen, et al. 2016; LaFree et al. 2018; McCauley and Moskalenko 2017; Moghaddam 2005), little has been written about the fundamental choice to fight at home or abroad. Indeed, while there is a rapidly growing literature on foreign fighters (Frenett and Silverman 2016; Gurski 2016; Hegghammer 2010; Malet 2015), most of it has focused on country-by-country statistics (Haner, Wichern and Fleenor 2018; Marone and Vidino 2019; Pokalova 2019; Reynolds and Hafez 2017; Shtuni, 2015), or comparisons across regions (Orozobekova 2016; Rosenblatt 2020). Some studies have explored the pathways and demographic risk characteristics associated with foreign fighting more generally (Boutin et al. 2016; Dawson 2021; Fritz and Young 2020; Reed, de Roy van Zuijdewijn, and Bakker 2015; Weggenmans, Bakker and Grol 2014). Others have analyzed the return and reintegration of fighters or have provided recommendations on how to counter the potential threats that returnees pose (Bakker, Paulussen and Entenmann 2014; Barrett 2017; Greenwood 2019). However, to our knowledge, the existing literature on foreign fighters has not provided an empirical assessment of the decision to fight abroad rather than at home.
Similarly, research on terrorist decision-making has been largely limited to explaining why terrorist groups adopt specific attack methods, such as suicide bombings (Hoffman and McCormick 2004; Pape 2005), or choose controversial targets, like children (Bieberman and Zahid 2019; Fahey and Asal, 2020). However, this body of work has not addressed the fundamental choice that jihadists make when they decide where to join the fight.
The purpose of this research is to determine why some American jihadist extremists in recent years decided to plot attacks in the United States on behalf of ISIS, while others attempted to join the group overseas. We examine 224 ISIS-inspired American jihadists, 39.7% of whom plotted terrorist attacks within the United States between 2013 and 2020 and 60.3% of whom attempted to join ISIS abroad. Controlling for several expected determinants of the decision to become a foreign fighter, we find that three characteristics of local social networks help explain why some ISIS supporters plotted attacks in the United States while others attempted to join the group in Syria and Iraq. We find that subjects were more likely to attempt to travel if they were embedded in large networks, networks in which many of the individuals were directly connected to each other (i.e., high ego density), and networks that were based on personal relationships rooted in family ties and trust.
By providing their members with the resources, knowledge, and relationships necessary for travel abroad, these networks made foreign travel a more viable option. In comparison, we find that the individuals who plotted domestic attacks in the name of ISIS typically had few or no co-offending ties to other U.S. extremists. While these individuals may have preferred to join ISIS, they lacked the social network connections that would have facilitated traveling abroad. Instead, they plotted attacks in the United States on behalf of ISIS that did not require help from others.
Social Networks and Becoming a Foreign Fighter
Although there is limited empirical research on the decision-making of Western jihadists, studies demonstrate that the flow of Westerners to foreign conflicts has outpaced the number of individuals who launched attacks in their own countries on behalf of international terrorist groups (Hegghammer 2013). Hegghammer (2013) provides the most common explanation as to why traveling to fight rather than engaging in terrorism at home has been favored among Western jihadists: foreign fighting is depicted as a legitimate activity within Islamic teachings and thus it is the preferred behavior for those wanting to wage jihad. While there is debate among clerics on the legitimacy of committing attacks in non-conflict zones, there is almost no debate among Islamist religious authorities about fighting within war zones. Hegghammer also points out that jihadist propaganda imagery is almost exclusively drawn from conflict zones, indicating that the propagandists expect these images to be more appealing to potential recruits. Venhaus (2010) aligns with Hegghammer’s view of foreign fighting, arguing that it is often portrayed as a heroic pursuit to protect Muslim populations abroad and provides young men with an avenue to fulfill desires for revenge, status, identity, and adventure. According to these authors, Western jihadists only choose terrorism at home when travel abroad is not practical.
While Venhaus and Hegghammer provide a cogent rationale for the shared preferences of Western jihadists, their arguments are less useful in explaining the specific choices that individuals make. Why would someone ignore their preferences to engage in a less desirable behavior, as nearly half of the jihadists in our sample did? What makes travel impractical for some jihadists but not others?
In this article, we explore the possibility that local social networks play an important role in mobilizing individuals to foreign conflict zones and, conversely, that the lack of local connections is a major factor in the decision to plot attacks at home. Prior research has shown the importance of social networks to explaining political violence (e.g., Gade et al. 2019; Krebs 2002; Perliger and Pedahzur 2011; Sageman, 2004; Zech and Gabbay 2016). Thus far, however, social networks have only been analyzed a handful of times in studies of foreign fighters. Saal’s (2021) examination of travelers from Germany, Austria, and Switzerland is the most thorough investigation to date. Using social network analysis (SNA), the author finds that nearly 90% of the fighters from Germany and Austria, and more than 80% from Switzerland, who joined foreign terrorist groups between 1998-2018 had connections to other extremists. Many of the subjects had ties to more than 20 other local jihadists. In a similar study, Kanol (2022) found that less than 20% of the travelers from Germany, France, and the United Kingdom who joined jihadist conflicts between 2000-2016 could be classified as lone actors. Saal and Kanol note that the foreign fighter networks they reviewed often consisted of relationships between travelers and local facilitators who acted as bridges to conflict groups in other countries. Holman (2016) reached similar conclusions about the importance of facilitators in his study of French foreign fighters from 1992-2014, while Dragon (2015) notes that facilitators were often critical to the recruitment of fighters in the early days of the ISIS caliphate.
Beyond these general studies of social networks and foreign fighting, the local connections of ISIS fighters have been described in several recent accounts. Reynolds and Hafez (2017) studied 99 German foreign fighters who joined ISIS and found that nearly 80% were mobilized within a single interconnected network. Bergema and van Sans (2019) found similar results in their study of Dutch ISIS fighters, noting that more than half had overlapping social ties. Harris-Hogan, Amarasingam, and Dawson (2022) note that 81% of Australian and 46% of Canadian ISIS fighters were connected to at least one other foreign fighter. And Rostami et al. (2020) found that 46.3% of deceased Swedish fighters in ISIS-held territories had ties to other travelers.
These studies illustrate that social networks are often a key dynamic in the mobilization of fighters abroad, including those who traveled to Syria and Iraq to join ISIS. However, this research has been limited by a key omission: it excludes a focus on individuals who could have become foreign fighters but instead attempted attacks in their own countries. For instance, while Saal, Kanol, and Holman use social networks to explain why some fighters successfully traveled while others failed, they do not explore whether networks factored into the fighters’ initial decisions to join groups abroad. Similarly, while recent studies of Western ISIS foreign fighters describe their connections, they do not compare the fighters and their social networks to those who acted on behalf of the group in their own countries. By only considering individuals who traveled to join terrorist groups, extant research on foreign fighters has not ruled out the possibility that social networks are just as important to the mobilization of individuals who plan to wage terrorism at home (Dawson 2021). 1
The Importance of Social Networks for Foreign Fighters
In this article, we extend earlier work on terrorist decision-making, social networks, and foreign fighters by examining the roles that local networks play in the decision to fight abroad or at home. We start with the assumption that aspiring jihadists share a preference for foreign fighting but argue that social networks act as an intervening variable, making travel possible for some but not others. We argue that individuals who are embedded in large networks, networks that are dense, or networks that include family members, romantic partners, and close friends are more likely to attempt to travel to foreign conflict zones than they are to plan attacks in their home countries. There are three reasons why we believe that individuals in these types of networks consider foreign fighting to be a viable option. First, as Malet (2013) has noted, individuals in these types of networks are more likely to have family or personal ties to conflict zones, increasing the chances that they are in contact with individuals in the places to which they hope to travel. These contacts can help aspiring fighters with travel logistics, provide them with plausible alibis for traveling to war torn areas, escort them into conflict zones, and afford them sanctuary as they establish relationships with fighters on the ground.
Second, there is a greater chance that individuals in these types of networks will be connected to former fighters or have trusted relationships with local contacts who can provide expertise on how to travel successfully. Indeed, as Saal (2021) and Holman (2016) note, facilitators, including those who previously fought abroad, are often the keys to successful travel. These actors know how to avoid detection by law enforcement, they are familiar with travel routes and safe houses, and they act as gatekeepers who connect legitimate travelers to transnational networks of fighters.
Finally, networks built on close personal relationships are more likely to provide their members with the resources and operational security necessary for becoming a foreign fighter. For instance, Daymon, de Roy van Zuijdew, and Malet (2020) found that fighters who joined ISIS often had assistance from family members, friends, and other trusted partners. These relationships, which often existed offline, helped aspiring fighters avoid detection and gave them access to the resources necessary to obtain passports, purchase airline tickets, and mobilize abroad. Connections based on family and friendship ties also serve as a key vetting mechanism for terrorist groups that need to separate trustworthy travelers from those who seek to infiltrate and undermine the organization (Holman 2016).
Conversely, we argue that individuals who have few or no connections to local jihadists are more likely to plot terrorist attacks in their home countries since they do not have access to the expertise or overseas contacts to make travel a viable option. In the Western jihadi context, these networks are often made up of newly radicalized individuals and converts to Islam who do not have familial ties to, or intimate knowledge of, conflict zones. Instead, these aspiring jihadists disproportionately rely on online communities for information, partnerships, and motivation. While information about traveling abroad is plentiful online, it is of varying quality and would-be fighters may not be connected to trusted narrators who can separate the good advice from the bad. Moreover, establishing relationships with fighters online is difficult and aspiring travelers, as well as fighters in conflict areas, can never be completely sure who they can trust. In the U.S. context, jihadists who attempt to expand their networks online often unknowingly establish relationships with confidential informants and undercover law enforcement agents. Law enforcement actors can disrupt individuals’ plans by persuading them to abandon travel in favor of plotting attacks on U.S. soil.
Although domestic attacks require access to weapons and some familiarity with potential targets, they do not require the skills, expertise, or trusted co-conspirators that local networks provide (Hegghammer 2013; Hegghammer and Nesser 2015). Indeed, most ISIS-inspired attacks in the United States have been perpetrated by individuals who used readily accessible weapons and exploited soft targets with unrestricted access to civilian victims (Bergen, Sterman, and Salyk-Virk 2019).
Our argument, therefore, expands upon prior research that suggests practical considerations and social relationships act as critical intervening variables between shared preferences and individual decision-making. Importantly, we test these arguments by examining a sample of jihadist offenders that includes individuals who attempted to fight abroad and those who plotted attacks at home. Below we examine the social networks and extremist behaviors of 224 American jihadist offenders who made attempts to join ISIS or plotted ISIS-inspired attacks in the United States. We use these data to test three related hypotheses.
First, we test the hypothesis that American jihadists embedded in large networks with many connections are more likely to attempt to travel to join foreign terrorist organizations. In SNA, having many connections, or high degree centrality, is typically associated with popularity, influence, and access to resources (Wasserman and Faust 1994). Similarly, due to their sheer size, large networks provide well-connected members with access to a range of skills and expertise. Thus, individuals with many ties are more likely to be known and trusted by members of the network, allowing them to satisfy the vetting procedures that make it possible to form connections to fighters abroad. There is also a greater chance that they will have, or can form, relationships with local facilitators who provide access to the financial and logistical resources needed to travel.
Individuals embedded in large local networks are more likely to attempt fighting abroad.
Second, we test the hypothesis that individuals who are members of networks that have high ego density are more likely to attempt to join foreign terrorist groups overseas. Ego network density refers to the percentage of all possible ties in a network that are present. Studies have shown that networks with high ego density provide their members with access to resources, knowledge, and opportunities (Burt 1992; Surowiecki 2004). Moreover, criminal co-offending networks with high redundancy can promote specialization in different tasks (McGloin and Piquero 2010), providing members with access to critical resources that help them achieve their goals. Networks with high ego density, therefore, may be more likely to include individuals with specialized expertise in joining foreign terrorist organizations. These networks can include members who play the role of recruiters who identify prospective fighters, mentors or facilitators who provide aspiring travelers with critical knowledge on how to travel successfully, or past fighters who maintain contacts with individuals in conflict zones (Holman 2016). Importantly, aspiring travelers in networks with high ego density often have direct connections to these nodes, eliminating the need to work through intermediaries to gain the resources, information, and contacts necessary to travel abroad.
Individuals who are embedded in networks with high ego density (i.e., interconnectedness) are more likely to attempt to fight abroad.
Finally, we test the hypothesis that jihadists who are embedded in networks that include family members, romantic partners, or close friends are more likely to attempt to travel. Studies of terrorism using SNA emphasize the critical role trust plays in the formation and function of networks (Eilstrup-Sangiovanni and Jones 2008). Given their secretive nature and inability to openly recruit new members, terrorist groups often rely on personal connections to vet aspiring members. Thus, individuals who are tied to a network by kinship or friendship are more likely to be deemed trustworthy and to receive the help of fighters in conflict zones (Holman 2016; Saal 2021). Moreover, networks based on trust are less likely to be infiltrated by law enforcement or outside actors who might otherwise influence their members’ decision-making.
Individuals who are embedded in networks that include family members, romantic partners, or pre-radicalization friends are more likely to attempt to fight abroad.
Data and Research Design
Our data on ISIS offenders in the United States comes from the Profiles of Individual Radicalization in the United States (PIRUS) dataset (Jensen, Yates, and Kane 2020). Profiles of Individual Radicalization in the United States is a representative database that captures the relevant aspects of individuals’ backgrounds to explain their radicalization trajectories. To be included in PIRUS, an individual must have engaged in illegal acts to achieve political, economic, religious, or social goals. Profiles of Individual Radicalization in the United States data are based on court records, news articles, and other public sources. For this study, we updated PIRUS to include a comprehensive list of U.S. ISIS offenders who were publicly identified as having committed crimes through 31 December 2020. To ensure the dataset of U.S. ISIS offenders was comprehensive, we relied on news sources and federal court documents, and consulted other political extremism datasets (e.g., Vidino and Hughes 2015; Bergen, Sterman, and Salyk-Virk 2019; Kurzman 2021; Intercept 2022). We identified 320 U.S.-based subjects whose crimes were inspired by, or linked to, ISIS. Of these offenders, 224 either attempted to travel abroad to join ISIS or were inspired by ISIS to plan terrorist attacks in the United States. 2
We coded each subject according to the protocols of the PIRUS dataset, as well as a forthcoming database on extremist social networks—Social Networks of American Radicals (SoNAR). Social Networks of American Radicals analyzes the social relationships between extremists, allowing users to graph co-offending networks. Social Networks of American Radicals records information on relationship types, asymmetrical influence within relationships, and records whether individuals communicated with each other online and/or offline.
Dependent Variable
The dependent variable used in this study is a dichotomous measure that is coded “1” if individuals attempted to travel to join ISIS and “0” if they plotted terrorist attacks on U.S. soil. To be considered a foreign fighter, a subject must have expressed an interest in joining ISIS and taken substantial steps toward achieving that goal. This includes purchasing airline tickets; raising money for travel; applying for a passport; attempting to contact fighters in Syria or Iraq or other individuals with knowledge of traveling; and/or researching travel routes, crossover points, or safe houses. In Figure 1, we show the total number of domestic plots and foreign travelers by year. Of the 224 subjects that we identified for inclusion in this study, 135 (60.3%) made serious attempts to join ISIS abroad. Number of United States ISIS-inspired domestic terror plots and United States ISIS foreign fighters by year of terror plot or travel.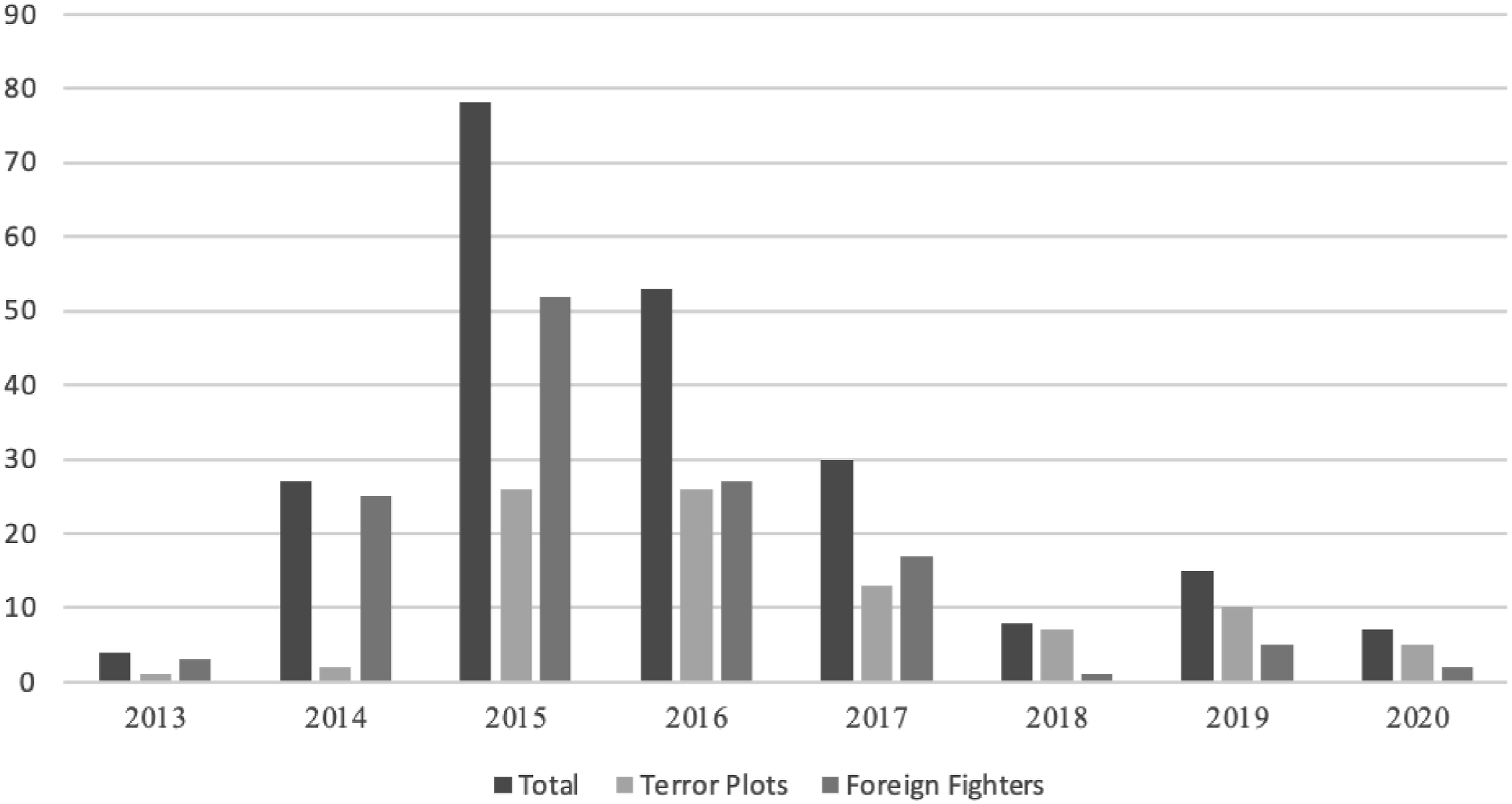
We coded subjects as being involved in U.S terrorist plots if they identified targets and took at least one additional step toward carrying out attacks. This includes acquiring weapons or weapons making materials; researching how to breach security deterrents; raising funds to carry out attacks; or recruiting co-offenders for plots. Of the 224 subjects included in the database, 89 (39.7%) were involved in plots to carry out terrorist attacks in the United States. Of these, seven had previously attempted, but failed, to join ISIS abroad. We discuss how these cases were treated in the methods section below. The data show that the largest number of U.S. ISIS cases took place at the height of the caliphate in 2015 and 2016. Foreign fighters outnumbered domestic attackers from 2013 through 2017, but domestic attackers were more common in 2019 and 2020. To date, no ISIS foreign fighter has successfully returned to the United States and then plotted an attack on U.S. soil.
Independent Variables
Descriptive Statistics and Variable Coding Schemes.
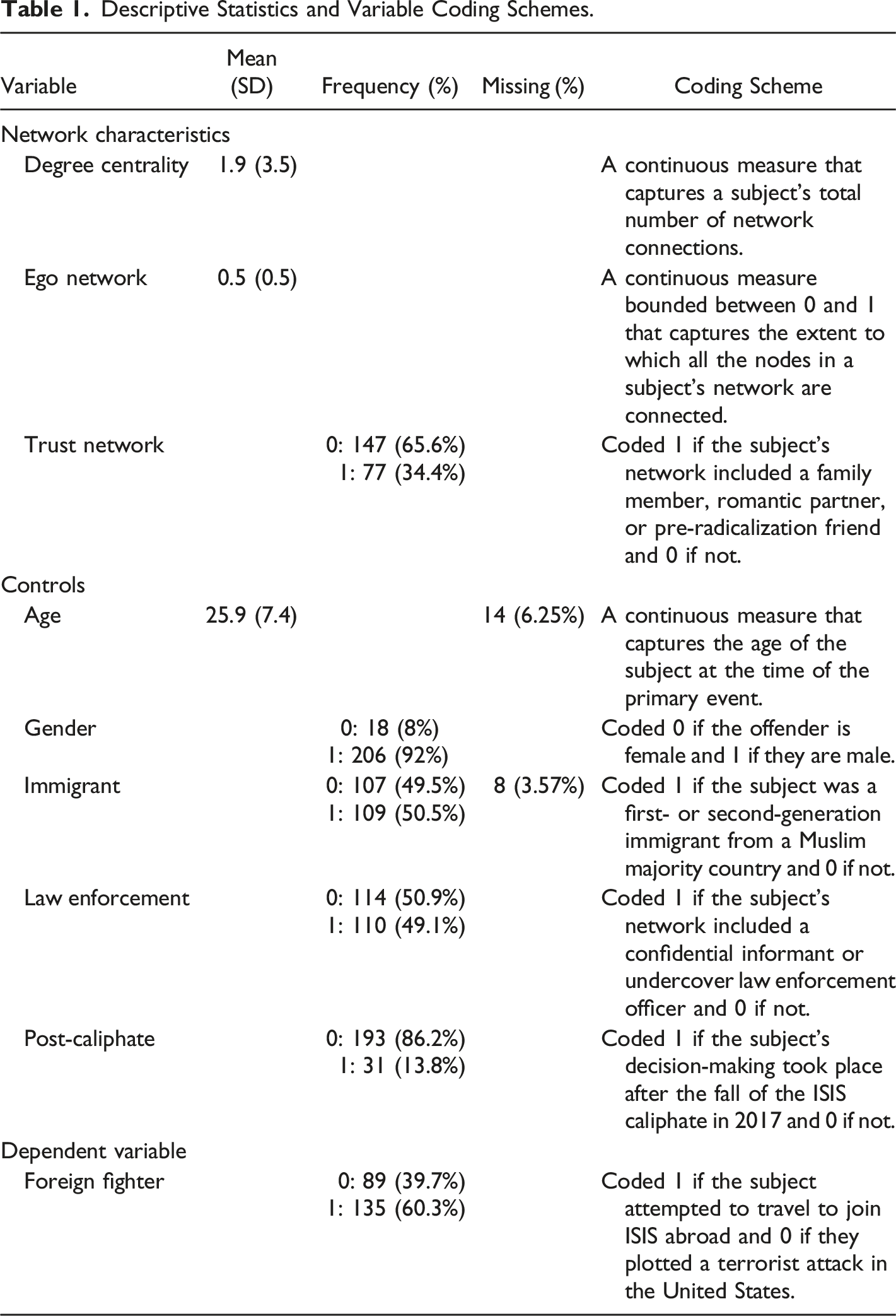
The second independent variable is ego network density, which is a continuous measure bounded between 0 and 1 that captures the extent to which all the nodes in a subject’s network were connected to each other. Lower values indicate a network where only a small percentage of all possible connections were present, while higher values indicate a network in which most of the nodes were directly connected.
The final independent variable is trust network, which is coded “1” if the subject’s extremist network included a family member, romantic partner, or pre-radicalization friend and “0” if not. We conceptualized pre-radicalization friend as an individual who established a friendship with the subject prior to either of them radicalizing.
Control Variables
We control for several other variables that may have influenced the perpetrators’ decisions to fight at home or abroad. First, younger individuals may be more inclined to travel abroad because they have fewer bonds tying them to their communities in the United States (Dragon 2015). Indeed, a common theme in research on foreign fighters is that young adults with limited educational or work prospects disproportionately make up the travelers from Western countries (Bakker and Grol 2015; Bergema and van Sol 2019; Gustafsson and Ranstorp 2017; Weenink 2015; Weggemans et al. 2014). Moreover, younger subjects are often targeted by recruitment narratives that emphasize travel as a means of satisfying their desires for adventure, status, religious fulfillment, and marriage (Dawson and Amarasingam 2017). To account for these dynamics, we control for the age of the subject when they made their travel attempt or began plotting an attack in the United States.
Second, we control for gender to account for the possibility that women may be more likely to travel to fulfill maternal roles (Peresin 2018), while males may see fighting at home as a more legitimate option.
Third, we control for whether the subjects were first- or second-generation immigrants from Muslim-majority countries. Following the argument of Malet (2013), we anticipate that jihadist recruitment narratives that emphasize traveling to protect Muslim populations in conflict areas will resonate with those who have kinship ties to Muslim-majority countries. Furthermore, regardless of their local social networks in the United States, individuals who have familial ties to conflict zones may be more capable of establishing contacts in those areas, making travel easier.
Fourth, we control for whether the subjects’ local social networks were infiltrated by law enforcement. Observers who have been critical of counterterrorism techniques after 9/11 argue that the terrorist plots that have been foiled would not have progressed as far as they did without the help of undercover agents and informants (Mueller 2006; Norris and Grol-Prokopczyk 2015). Law enforcement, according to these critics, is often pivotal in helping perpetrators identify targets, engage in military-style training, and acquire what the perpetrators believe are real weapons. Thus, subjects’ whose social networks include law enforcement actors may be swayed to plot attacks in the United States, even if their preference is to travel abroad.
Finally, we control for whether subjects were making their decisions before or after ISIS lost most of the territory it controlled in Syria and Iraq. According to Byman (2019), perceived success was a major motivator for those who sought to join ISIS abroad. However, by the end of 2017, ISIS had lost much of its territory (Wilson Center 2019), making it less appealing, and perhaps even impossible, to join the group abroad. We control for the effects of the fall of the ISIS caliphate on the subjects’ decision-making by including a dummy variable that captures whether perpetrators were making their plans before or after July 2017. We chose July 2017 as the end of the caliphate because by this time ISIS had lost most of Mosul and Raqqa (Wilson Center 2019), which were the most important areas under the group’s control.
Analytical Methods
Since we are utilizing observations from social networks with interconnected nodes, our data violate the assumption that observations are independent, which is common to standard statistical techniques. Using single-level methods with interdependent data commonly yields underestimated standard errors, which can lead analysts to incorrectly reject null hypotheses (Hox 1998; Singer and Willet, 2004). We therefore use generalized estimating equations (GEE) to avoid these pitfalls (Ghisletta and Spini 2004; McNeish 2014). We chose GEE over other multi-level methods that are designed to be used with interdependent data because it has been shown to perform better when the data include clusters with only a few observations (McNeish 2014). As we note below, the local networks of ISIS supporters in the United States often included less than three subjects.
Descriptive and Bivariate Results
According to Table 1, the subjects in this study were on average connected to two other U.S.-based extremists (Mean = 1.9, SD = 3.5) when they were making their decisions to travel abroad or commit attacks in the United States. However, as shown in Figure 2, the range of local extremist connections in the sample varied considerably. Many of the subjects were lone actors who did not have any connections to other U.S. extremists (n = 100; 44.6%). Others were embedded in large networks and had connections to as many as 19 other extremists residing in the United States. Local networks of United States ISIS foreign fighters and ISIS-inspired domestic plotters from 2013-2020.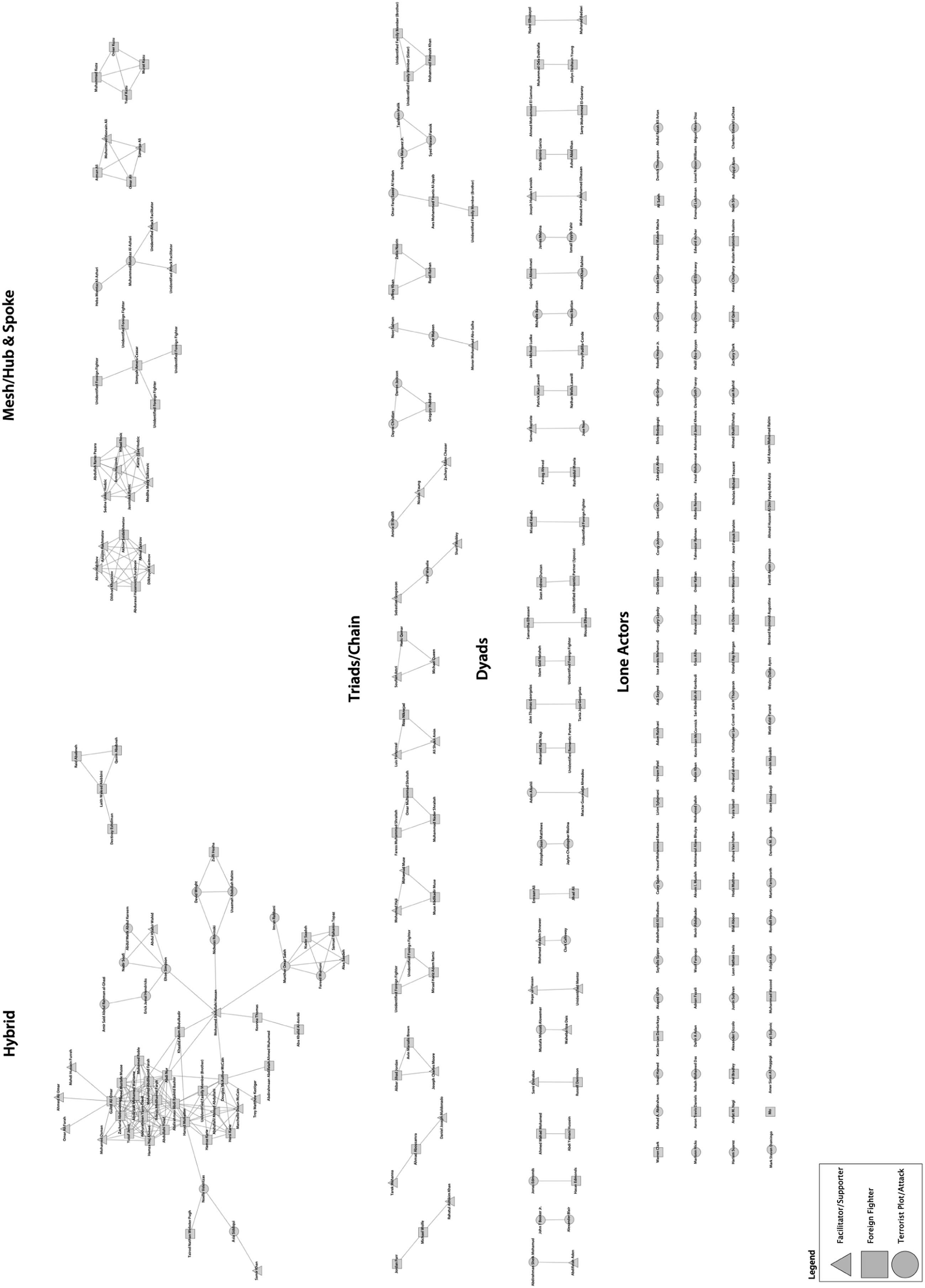
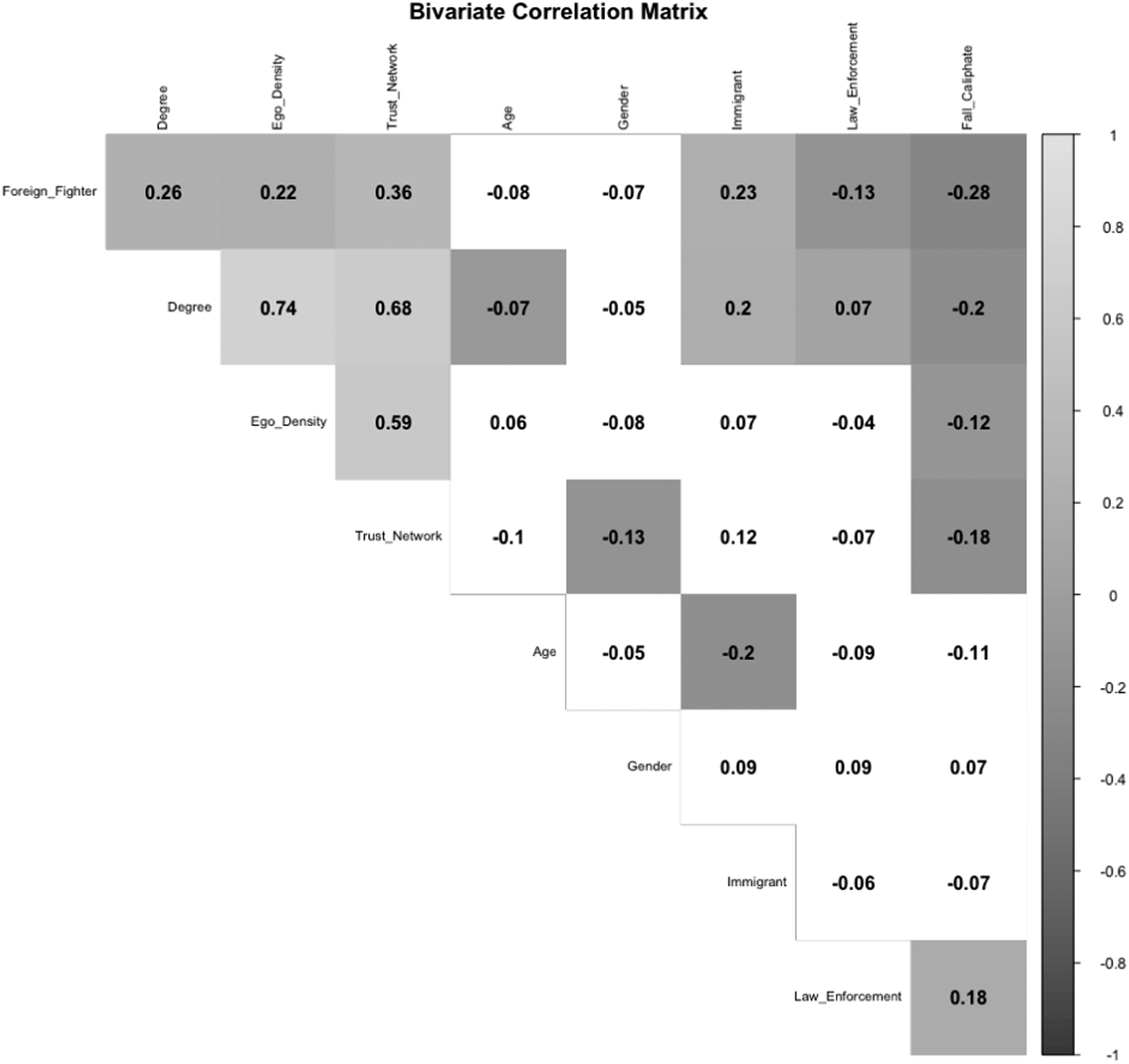
Bivariate Correlation Matrix of Network Measures and Control Variables for United States ISIS Foreign Fighters and ISIS-inspired Plotters.
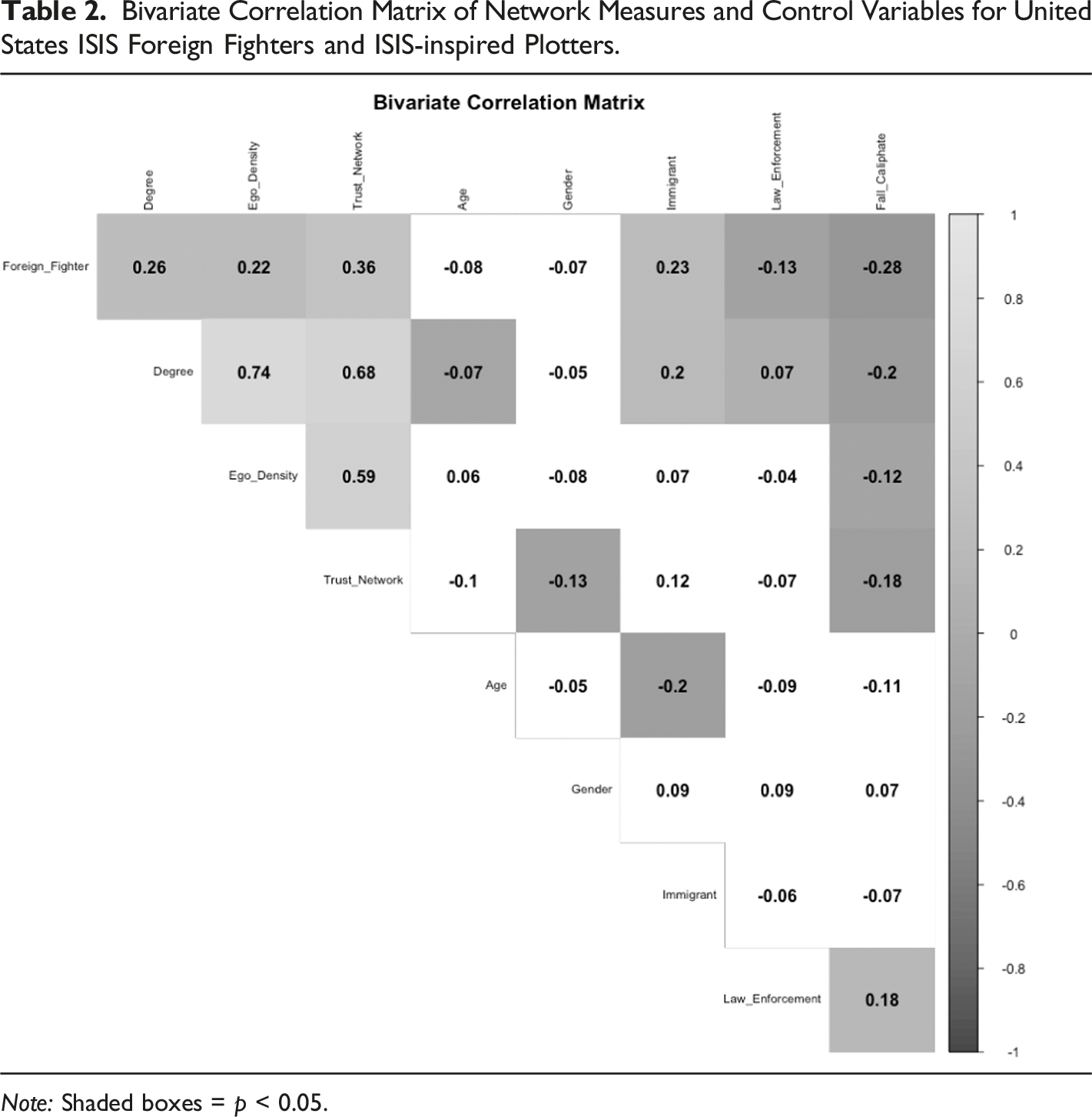
Note: Shaded boxes = p < 0.05.
Similarly, in support of our second hypothesis, we find that the redundancy of local extremist networks was greater for individuals who attempted to become foreign fighters than it was for those who plotted attacks in the United States. Foreign fighters had an average ego network density score of 0.601, indicating that a substantial portion of all possible connections were present in their networks. Islamic State of Iraq and Syria-inspired attack plotters, on the other hand, had an average ego density score of just 0.369. Moreover, according to Table 2, the bivariate association between ego network density and foreign fighting is positive and significant, indicating that subjects with dense networks were more likely to attempt to join ISIS abroad.
In terms of connections to trusted associates, 24.6% of the subjects in the study were in extremist networks that included family members, 12.9% had networks that included pre-radicalization friends, and 9.4% had networks that included romantic partners. Lending support to our third hypothesis, we find that these types of trusted relationships were more common among the foreign fighters in the data. For instance, 33.3% of the foreign fighters were in networks that included at least one of their family members, while only 10.1% of attack plotters had similar familial relationships to extremists. Moreover, the foreign fighters in the data were the only subjects to be coded as having friendships with network members that began before either person radicalized. Overall, 65 of 135 foreign fighters in the study (48.1%) had connections to extremist family members, pre-radicalization friends, or romantic partners, while only 12 of the 89 attack plotters (13.5%) had similar relationships. The bivariate results in Table 2 show that relationships based on trust have the strongest positive correlation with the decision to become a foreign fighter.
We note that several of the control variables were significant in the bivariate results. While the majority (50.4%) of the 224 individuals in the data were first- or second-generation immigrants from Muslim majority countries, most were concentrated in the subgroup of foreign fighters. Indeed, 60% of the subjects who attempted to travel to join ISIS had familial ties to Muslim majority countries, while only 36.5% of attack plotters were first- or second-generation immigrants from countries with predominantly Muslim populations. Moreover, among the ISIS-inspired U.S. attack plotters, 50.6% were converts to Islam born in the United States.
The bivariate results also support the argument that subjects whose extremist networks were infiltrated by law enforcement were less likely to attempt to travel abroad. Approximately half of our sample had been infiltrated by law enforcement (n = 110). Most of these connections were with confidential informants (n = 84), but nearly a quarter of the subjects were connected to undercover law enforcement agents (n = 50). Importantly, these subjects were more likely to plot attacks in the United States than to attempt to travel. Nearly 60% of the ISIS-inspired attack plotters were connected to confidential informants or undercover law enforcement, while just over 40% of the foreign fighters had similar connections.
Our results also suggest that the decision to become a foreign fighter in part depends on the perceived success of foreign terrorist groups and their ability to control territory. While most of the subjects in the study were acting during the time of the ISIS caliphate (n = 193), 31 plots and travel attempts happened after ISIS lost control of large swathes of territory in 2017. However, nearly all (94%) of the foreign fighters in the data attempted travel between 2013 and 2017 when the caliphate was still active. By comparison, more than one quarter of the ISIS-inspired attack plotters made their plans after ISIS had lost most of its territory.
Finally, it is worth noting that the subjects in the data had nearly identical age and gender profiles. The attack plotters were on average 26.1 years old when they offended, while the foreign fighters were on average 25.7 years old when they attempted to travel abroad. Regardless of their decision-making, both samples were overwhelmingly male (90.4% for foreign fighters versus 94.4% for attack plotters). Neither age nor gender, therefore, appear to be meaningful to the explanation of decision-making among these American jihadists.
Multivariate Results
Generalized Estimation equation Models: Foreign Fighter Travel Attempt.
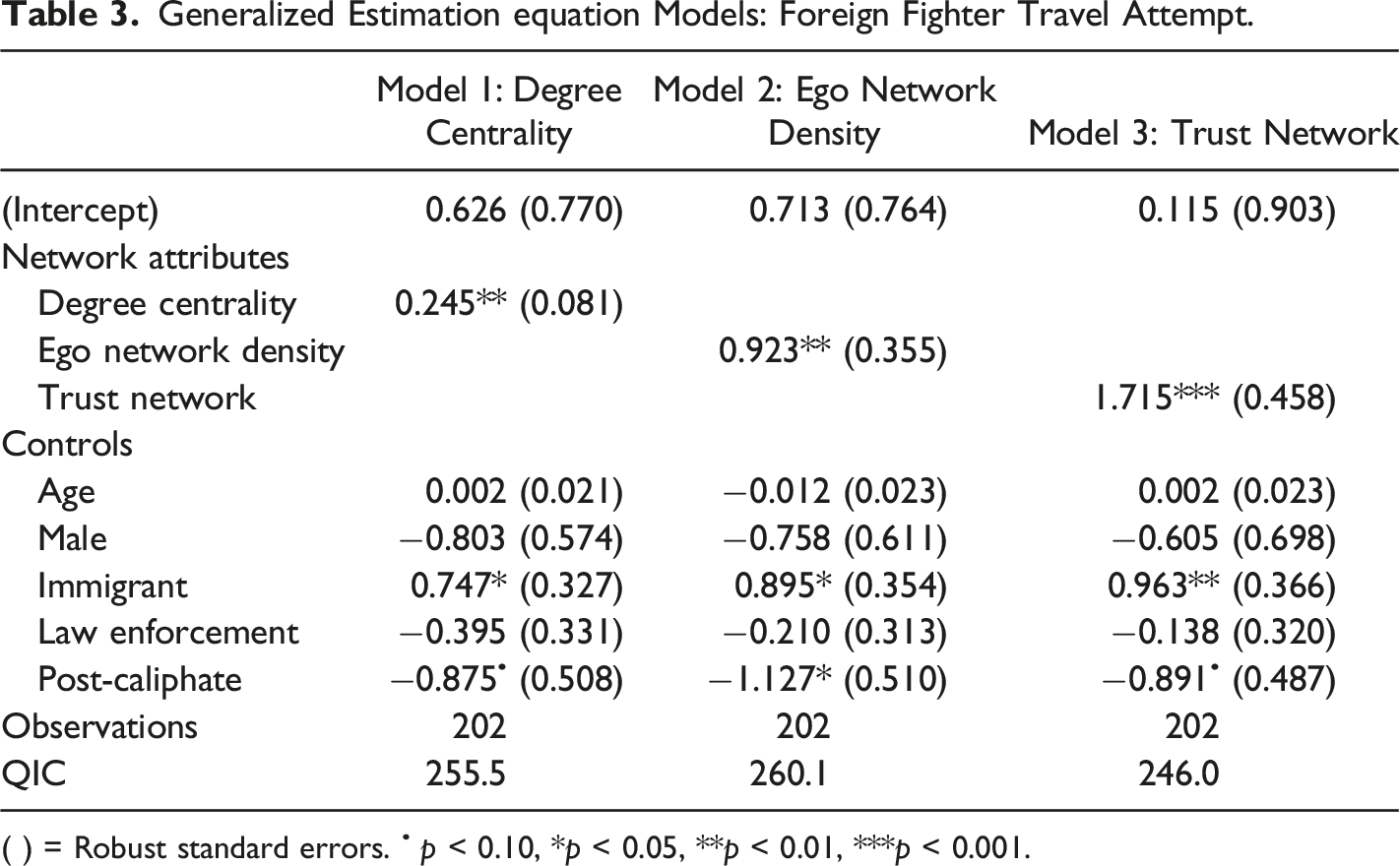
( ) = Robust standard errors. • p < 0.10, *p < 0.05, **p < 0.01, ***p < 0.001.
In Model 1, there is a positive and significant relationship between degree centrality and the decision to become a foreign fighter. Indeed, this association is stronger in the multivariate model than it was in the bivariate results. The results from Model 1 suggest that with every additional local extremist connection, the odds that a subject in the data was classified as a foreign fighter increased by 28%. According to Table 3, immigrants from Muslim majority countries were twice as likely to attempt to join ISIS abroad, whereas those who were making their decisions after ISIS lost most of its territory were approximately 58% less likely to become foreign fighters. Interestingly, the variable that captures connections to law enforcement is no longer significant in the multivariate model; though, its coefficient runs in the hypothesized direction.
Model 2 uses the same control variables but substitutes degree centrality for ego network density. Again, the results show a positive and significant relationship between network density and the decision to travel abroad. Subjects who were embedded in dense networks were 2.5 times more likely to become foreign fighters than subjects who were embedded in loosely connected groups or who acted alone. Being an immigrant from a Muslim majority country was again positive and significant in this model (odds ratio [OR] = 2.45). Similarly, the variable capturing the fall of the caliphate was negative and significant, again suggesting that subjects were less likely to attempt to travel abroad after ISIS lost most of its territory.
In Model 3 we analyze whether individuals who were part of networks based on trust were more likely to become foreign fighters. We again find that this network measure is positive and significant. In fact, of the three network measures used in these models, relationships based on trust have the strongest association with becoming a foreign fighter. Subjects with these types of social connections were 5.6 times more likely to attempt travel than individuals who did not have close, personal relationships to fellow extremists. Being an immigrant from a Muslim majority country is again positive and significant (OR = 2.6), while engaging in decision-making after the fall of the ISIS caliphate is again negative and significant (OR = 0.41).
Discussion
This study highlights the importance of local networks to the decision-making processes of American jihadists. Our results show that from 2013 to 2020 jihadists who were embedded in large networks, networks with high ego density, and networks based on trust were more likely to attempt to join ISIS abroad than to plan terrorist attacks in the United States. These results suggest that while aspiring jihadists might have a shared preference for becoming foreign fighters, travel is often only a viable option for individuals who have local associates who can assist them with finances, visas, travel routes, safe houses, and establishing foreign contacts. Moreover, local networks are often key to providing the operational security that is necessary for aspiring fighters to avoid detection and relocate overseas.
As Models 1 and 2 show, individuals who are embedded in large and dense networks are more likely to have relationships with local extremists who can facilitate their travel abroad. The foreign fighters in this study often had connections to individuals with experience facilitating the movement of fighters overseas (n = 41, 30.4%). Indeed, we find that the odds that an ISIS-inspired or affiliated subject in our data was connected to a local travel facilitator increased by 37% for each additional node in the subject’s network. Individuals who were embedded in networks with high ego density were 17 times more likely to be connected to a travel facilitator than those with loose or indirect affiliations with other members of their networks. By comparison, none of the individuals in our study who plotted attacks in the United States were connected to experienced travel facilitators.
Similarly, Model 3 shows that individuals whose networks include family members, romantic partners, and pre-radicalization friends are more likely to become foreign fighters. In our data, networks based on interpersonal trust were the most likely to include individuals with kinship ties to Muslim-majority countries (n = 44, 58.7%), which is correlated with an increased probability of travel in all models. Moreover, the subjects whose networks included close personal relationships were less likely to be connected to law enforcement actors. For example, only 15.6% of the individuals whose extremist networks included family members, friends, or romantic partners were also connected to undercover law enforcement officers, while more than one quarter (25.9%) of the subjects without ties based on interpersonal trust were connected to undercover agents.
The importance of local networks in the decision to become a foreign fighter is nowhere more apparent than in the collection of individuals from Minneapolis, Minnesota, who attempted to join ISIS between 2013 and 2020. The Minneapolis network included 38 individuals, several of whom played critical roles as recruiters, facilitators, and mentors. For example, Abdi Nur, who joined ISIS in 2014, served as a travel facilitator and mentor for 11 other network members (Shane 2015). The Minneapolis network also demonstrates the importance of relationships based on trust for jihadist decision-making. For example, the Karie brothers recruited three of their cousins into the network and all of them later played important roles radicalizing additional local jihadists (Huncar 2018).
Our results suggest that American jihadists who are not embedded in large, dense, or trust-based networks often plot attacks at home. In addition to maintaining relatively few connections to other local extremists, the ISIS-inspired attack plotters in our data rarely radicalized alongside family members and none of them were connected to friends prior to radicalization. Furthermore, nearly 60% of the ISIS attack plotters in our study were converts to Islam who lacked any discernable kinship or network ties to conflict zones. As a result, ISIS-inspired attack plotters between 2013 and 2020 were either lone actors or those with a small number of newly established online connections.
Lacking the local help that is needed to travel, evidence suggests that many of these offenders opted to plot attacks that were low in sophistication and did not require specialized skills or the participation of others. For example, Munir Abdulkader, who had no known connections to other U.S. extremists, originally intended to travel to Syria to join ISIS. He attempted to obtain a passport, researched logistics, and saved money to purchase airline tickets (United States Department of Justice 2016). However, he became concerned about his ability to travel successfully to Syria without established contacts in ISIS-held territories. After an informant asked him if he had “considered other jobs if he could not be a fighter,” Abdulkader began planning a low sophistication firearms attack on a military employee and a police station in Ohio (USA v. Abdulkader 2015). In coordination with the informant, Abdulkader purchased materials for the attack, conducted surveillance, and carried out firearms training.
The case of Abdulkader highlights the important role that local networks play in providing operational security for individuals to pursue their preferences. Similar to Abdulkader, Christopher Lee Cornell abandoned his travel plans after infiltration by law enforcement. Cornell was a Muslim convert who was arrested in 2015 for plotting to attack government officials during President Obama’s State of the Union address. Cornell, who had no family members or friends involved in extremism, posted online his desires to travel to Syria to join ISIS, but he lacked the money and contacts that he needed for travel (USA v. Cornell 2016). Cornell tried to establish relationships online with other U.S.-based jihadists who shared his interest in making hijra to Syria (USA v. Cornell 2016). He was eventually contacted by an FBI informant online and their discussions turned to the possibility of Cornell conducting an attack in the United States. During preparation for the Cornell trial, it was revealed that Cornell told the informant that he did not believe committing an attack in the United States was justifiable under Islamic teachings. At that point, the informant allegedly fabricated a story about being in contact with an ISIS Emir who had blessed operations on U.S. soil (USA v. Cornell 2016). After hearing this, Cornell, with the encouragement of the informant, began crafting his plot.
Limitations and Future Research
While this paper has demonstrated the significance of networks to the decision-making processes of American ISIS offenders, we acknowledge several limitations of the study that provide avenues for future research. First, our goal in this paper has been to demonstrate how social networks intervene between a shared preference for foreign fighting and the actual decisions that aspiring jihadists make. Thus, we do not offer or test hypotheses that explain why someone’s first preference might be to commit an attack in their home country. Similarly, we cannot test the possibility that an individual who prefers to wage terrorism at home has less of an incentive to form relationships to other jihadists, thus explaining their lack of local connections. Finally, given our use of open sources, we cannot guarantee that all the ISIS attack plotters in our sample preferred foreign fighting over terrorism at home but opted for the latter for practical reasons. While we found evidence of this type of decision-making in multiple cases of U.S. ISIS-inspired attack plotters, without the ability to speak to each subject in our sample, many of whom are no longer alive, we are forced to make assumptions about their preferences from the available evidence. Future studies, therefore, can build on our work by interviewing former jihadists about their decision-making and testing alternative models that challenge the accepted wisdom that foreign fighting is a preferred behavior.
Second, this study attempts to explain why some jihadists make the decision to travel abroad while others decide to plot domestic attacks, but our analysis does not explain the outcomes of those behaviors. The success or failure of any action is dependent on several structural and law enforcement variables that are beyond the scope of this study. These include airport security, vetting procedures for passports and visas, border security in crossover countries, and investigative resource allocation. Nevertheless, it is possible that terrorist decision-making reflects a process of learning (e.g., Jackson and Baker 2005; Kettle and Mumford 2017), whereby individuals consider the past successes and failures of others when weighing their own choices. Future studies should consider this possibility to assess its merit as an alternative, or perhaps a complimentary hypothesis, to the ones we offer in this article.
Third, we do not know how generalizable our results are outside of the United States. While Reynolds and Hafez (2017) show that local networks were instrumental to the movement of foreign fighters from Europe to ISIS-controlled territories, Nesser, Stenersen and Oftedal (2016) demonstrate that local networks may have also played key roles in facilitating attacks in European countries. Moreover, given its comparatively long distance from conflict zones, networks could be more critical to foreign fighters from the United States than they are to fighters elsewhere. Therefore, future research should replicate this study in other parts of the world to determine if our results hold.
Finally, our analysis only considers local networks and does not map the connections of American jihadists to foreign contacts. Although expanding the data to include ISIS contacts abroad would be useful, the online and secretive nature of foreign communications make such comparisons very challenging. Thus, it remains an open question as to whether distant networks can replace the functions of local ones and similarly influence the decision to become a foreign fighter.
Conclusions
While ISIS has been effectively dismantled as a major geographic entity and fighting force, the international community continues to have grave concerns about the threat posed by returnees from its former caliphate (Bakker, Paulussen and Entenmann 2014; Barrett 2017). Islamic State of Iraq and Syria-affiliated foreign fighter returnees have been involved in several terror attacks in Europe, including the coordinated 2015 Paris attacks, the 2016 Brussels airport and metro attacks, and the Manchester Arena bombing in 2017. Some researchers argue that returnees present a long-term threat due to their ability to import terrorism back to their home countries (Clarke 2017; Malet and Hayes 2018). While the claims of returnee effectiveness are contested (Leduc 2016), it is widely acknowledged that plots involving veteran foreign fighters are more likely to be successful and are more lethal (Hegghammer 2013; Sageman 2009).
However, our analysis suggests that, at least in the U.S. context, the concern about foreign fighter returnees is overstated, largely because it fails to consider the dynamics of terrorist decision-making. Our data show that no ISIS returnees have perpetrated attacks in the United States. Rather, the largest threat to the security of U.S. residents has come from individuals who were inspired by the organization but lacked the requisite local networks to join the group abroad. Indeed, according to the Global Terrorism Database (2020), from 2013 to 2019, there were a total of 29 successful ISIS-inspired attacks in the United States. These attacks include the San Bernardino shooting in 2015, which resulted in the deaths of 14 people and 24 injuries, and the 2016 Orlando nightclub attack. Outside of the Orlando attacker having a tenuous connection to a Florida-based foreign fighter who conducted a suicide attack in Syria in 2014, 4 there is little evidence to suggest that the perpetrators of these attacks had the types of relationships that would have allowed them to join ISIS overseas.
Terrorism inspired by foreign groups will likely continue to be a major security concern for Western nations. Given the challenges it poses, the data and findings presented here can provide potential policy responses. First, the network analysis demonstrates the importance of community and social context in decision-making and, therefore, underscores the fact that interventions and counter-narratives need to be localized. This will require support from within diasporic communities in order to reach and impact at-risk individuals and groups. Successful implementation will require a multi-agency public health approach, with important roles for community partners and civil society.
The rehabilitation and reintegration of returnees and domestic terrorists may need more specialist tailoring as our analysis demonstrates different support structures, motivations, and experiences for these two groups. Having a better understanding of the networks, the individuals involved, and their roles could offer greater opportunities to interdict travel and plots, especially as members of networks can use their influence to block, as well as facilitate, terrorist behaviors (Meleagrou-Hitchens, Hughes and Clifford 2018).
Finally, our findings suggest that U.S. law enforcement employing undercover agents or informants might have a direct effect on would-be travelers’ decisions to plot attacks. As domestic plots have the potential to cause significant destruction, this is not a risk-free alternative, and more research is needed to assess the merits of this policy. At a minimum, the use of informants and undercover agents to influence terrorist decision-making risks reputational fall-out for security agencies and further alienation of law-abiding Muslim communities.
Although this study is based on recent data, social networks, especially those that are formed around kinship and emotional bonds, are likely to continue to influence terrorist decision-making for the foreseeable future. This study demonstrates the utility of leveraging SNA and related methods for modeling the micro, meso, and macro interactions that drive terrorist behavior. While considerable work remains to be done, exploring the complex nature of terrorist decision-making can put us in a better position to prevent the next wave of foreign fighting and jihadist terrorism.
Supplemental Material
Supplemental Material - Choosing Where to Fight: Do Social Networks Distinguish American ISIS Foreign Fighters from ISIS-Inspired Terrorists?
Supplemental Material for Choosing Where to Fight: Do Social Networks Distinguish American ISIS Foreign Fighters from ISIS-Inspired Terrorists? by Michael A. Jensen, Neil Ferguson, Sheehan Kane, and Gary LaFree in Journal of Conflict Resolution
Footnotes
Acknowledgements
The authors would like to thank two anonymous reviewers for their helpful comments during the review process.
Declaration of Conflicting Interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This project was supported by Award No. 2017-ZA-CX-0001, awarded by the National Institute of Justice, Office of Justice Programs, U.S. Department of Justice. The opinions, findings, and conclusions or recommendations expressed in this publication are those of the author(s) and do not necessarily reflect those of the Department of Justice.
Supplemental Material
Notes
References
Supplementary Material
Please find the following supplemental material available below.
For Open Access articles published under a Creative Commons License, all supplemental material carries the same license as the article it is associated with.
For non-Open Access articles published, all supplemental material carries a non-exclusive license, and permission requests for re-use of supplemental material or any part of supplemental material shall be sent directly to the copyright owner as specified in the copyright notice associated with the article.