Abstract
This essay investigates justifications for the “necessity” of official secrecy, by tracing and structuring the rationales underlying it. Justifications will be investigated through the case of “national security secrecy,” a prominent example of official secrecy. While the literature generally treats “national security secrecy” as unidimensional, this analysis demarcates several distinct rationales. Specifically, three justifications for national security secrecy are identified: the logic of crisis demanding the suspension of normal democratic processes (threat frame); the need for enabling and enhancing governance (effectiveness frame); and the delegation to and protection of decision makers (elite governance frame). The paper illustrates possible frictions, overlaps, and synergies between different rationales for national security secrecy, thus broadening the existing conceptualization away from transparency and secrecy as direct opposites. It further contributes to ongoing research on national security secrecy from a frame analysis perspective, thus linking theories, justifications, and practices of secrecy.
The current governance literature considers secrecy a deviance from conventional norms of openness and transparency. Academic discourses regularly start from the presumption that secrecy is undesirable and problematic. 1 Publicity and openness are heralded as the precondition for democracy, since it is “only when citizens know the content of state policies they can hold state officials to account for them.” 2 In consequence, secrecy is assumed to undermine the very foundation of democracy. Closed-door decision-making in “smoke-filled rooms” is associated with unaccountable leadership or corrosion of the public interest. 3 Secrecy in the context of governance is associated with corruption, mismanagement, and inefficiency. 4 Hence, Woodrow Wilson famously declared “secrecy means impropriety.” 5 However, secrecy in government affairs persists; for instance, in the form of exemption clauses in freedom of information legislation, classification regimes, or information prerogatives. The question of how to reconcile a seeming “necessity” for secrecy with the democratic norms of transparency and accountability constitutes a persisting problem in the field. Transparency scholars and advocates are concerned with the scope and justification for secrecy in addition to the ways in which secrecy can be contained and limited 6 —in short, how an adequate balance between secrecy and transparency can be struck. Yet, the boundaries between legitimate and illegitimate secrecy are frequently blurred. Ultimately, the perceived legitimacy of secrecy can be expected to depend on the perspective from which a speaker is arguing. Transparency advocates will have a different understanding of what constitutes legitimate secrecy from most public officials.
Democratic states are generally required to justify imposed requirements in order to enforce them and maintain legitimacy. Secrecy, just like other requirements of governance, needs to be convincingly presented to constituencies. Legitimizing secrecy requires explaining why the state restricts the flow of information and by what means concealment is enforced. Generally, legitimacy is achieved if governance rationales are consented to and, thus, “naturalized.” If, as Hurrelmann suggests, legitimation relies on broader political justification processes that occur in a society, it is necessary to identify the roots of such justifications. 7 Here, Waldron suggests exploring the common beliefs that may be appealed to in the justification of institutional arrangements. 8 This analysis sets out to explore the beliefs underlying claims for official secrecy, presuming that not one, but several rationales are employed to establish the necessity of secrecy.
For reasons of feasibility, this analysis will focus on a specific type of government secrecy, which has been labelled “national security secrecy,” 9 referring to the non-disclosure of information for the safeguarding of security and in military or intelligence matters. Safety, security, and defence considerations form the basis of common exemption clauses within transparency legislation and are the reason why classification regimes exist. While transparency scholars have frequently addressed the question of “national security secrecy,” they rarely discuss the ideational foundations of these rationales for secrecy. The understanding of how security and secrecy relate remains relatively vague, a shortcoming that has been acknowledged by several authors.
Analytical approach
The present analysis explores the rationales underlying the “necessity claim” of official secrecy, more specifically national security secrecy, in order to (1) trace the roots of some commonly occurring legitimacy claims for secrecy; (2) map the multiplicity of rationales underlying the “necessity claim”; and (3) examine the ways in which different rationales diverge or overlap. The critical literature review explores not only the ideational dimension of secrecy claims but also ways in which these rationales might be challenged and how secrecy and accountability can be reconciled. The discussion section of the paper takes a comparative approach to the different rationales identified. The conclusion broadens the perspective, discussing the implications of the analysis for the conceptualization of transparency and secrecy as mutual opposites.
Besides the literature on government secrecy, the analysis reviews relevant scholarship from the field of international relations, and military, and security studies. Not only does the literature in this field provide a nuanced approach to the concept of security itself, it also offers various discussions on national security secrecy, such as the role of public opinion in the use of military force, civil-military oversight, and the role of information in warfare. The literature on national security secrecy has only selectively drawn on these insights; a systematic integration of security and secrecy research is so far missing.
For the purpose of the analysis, secrecy rationales are understood as frames. Frames are schemata of interpretation, 10 which offer a “central organizing idea or story line that provides meaning to an unfolding strip of events.” 11 The act of framing requires “selecting and highlighting some facets of events or issues and making connections amongst them so to promote a particular interpretation, evaluation, and/or boundary.” 12 Consequently, a frame constitutes a specific mode of perceiving reality.
Since frames are often implicit or elusive, frame analysis requires an in-depth engagement with the textual data, making it at times “difficult to neutralize the impact of the researcher.” Therefore, to enhance the validity and reliability, this analysis follows Matthes and Kohring, who propose to identify frames not as a whole but by locating frame components that in conjunction work as an interpretive scheme. 13 The components used for this study are: (1) ideational roots, (2) problem representation, and (3) response strategies. Beyond the identification of secrecy frames, the analysis further considers (4) how specific frames are challenged as well as (5) remedies to address such framing conflicts.
Borrowing again from Matthes and Kohring, the identification of these analytical components outlined above builds upon the understanding of framing itself. Given the study’s focus on government secrecy, the analysis will specifically draw on the literature on policy frames. Policy frames are understood as “coherent interpretations of a policy issue containing a problem definition and a matching strategy to solve it.”
14
The definition of policy problems allows political actors to identify, make sense of, and publicize issues.
15
The way in which a policy problem is defined will ultimately shape proposed solutions to the issue.
16
This analysis seeks to understand against what
Further, this analysis explores the theoretical assumptions underlying a particular problem definition. Rein and Schön argue that policy frames are not emerging from nowhere but are usually nested within larger metacultural frames,
17
which this analysis will define as the
This analysis also recognizes the multiplicity of social realities, by equally considering how identified secrecy
Finally, the analysis considers how such framing conflicts can be solved, notably, how the need for secrecy emerging from a specific problem perception can be conciliated with the view that accountability is an essential component of democratic governance. Here, the study moves beyond a framing analysis, considering
Critical literature review
This analysis identifies three possible justifications for the “necessity” of national security secrecy. The first rationale justifies secrecy as a provision against latent or imminent security threats, to which governments can respond through extraordinary measures, including secrecy. In the following, this rationale will be labelled threat frame. The analysis will primarily draw on critical security studies for its elaboration. The second justification is the need for secrecy to enable or to enhance governance (hence, the label effectiveness frame). While this rationale is not limited to security and defence governance alone, it certainly constitutes the domain in which strategic secrecy is most proliferated. This rationale for secrecy is primarily embedded in the military and strategic studies literature. The third justification of secrecy is based on the idea that foreign and security policy is a complex field, best dealt with by officials who have the necessary expertise to decide what is in a country’s interest. Secrecy here serves as a protection against the uninformed general opinion. This rationale will be referred to as the elite governance frame and can be traced primarily in the realist literature.
Threat frame: “Security as a primary value”
Ideational roots
The threat frame is embedded in the perception that the world is a violent place, in which the security of the individual is guaranteed through overarching political structures. 20 States provide protection against “outside” threats and, as such, generate the precondition for other societal values, such as prosperity or democracy. 21 Following this logic, ensuring security is the primary task of any government and thus precedes other goals and values a state might pursue. The primacy of security is also reflected in the conventional justifications for national security secrecy. Schoenfeld, for instance, argues that “when one turns to the most fundamental business of democratic governance, namely, self-preservation […] the imperative of secrecy becomes critical, often a matter of survival.” 22
Problem representation
Inasmuch as security is considered a primary value, the means to achieve security are justifiable, even if they deviate from normal democratic practices. “Emergencies and other unusual threats,” writes Schulhofer, “almost invariably prompt nations to free their executive authorities from many ordinary constraints.” 23 Specifically, it is the notion of survival that legitimates the “exceptionalism” of security governance: Existential challenges to a polity or its constituent eclipse any other values and goals because, if security is not achieved, nothing else will matter. Accordingly, Agamben describes the state of exception as a “no-man’s-land between public law and political fact,” analogous to the principle necessitas legem non habet (necessity has no law). 24
The response to threat scenarios is a program of exceptional measures of which secrecy is a key component. This includes the suspension of openness, scrutiny, and participation for the benefit of speedy, assertive government actions. Kreuder-Sonnen argues that, in times of crisis, governments may feel compelled to employ secrecy to manage crisis-induced challenges, a strategy which he refers to as reactive secrecy. 25 Aradau thus concludes that “it is in relation to the procedural ‘normalcy’ of democratic politics that the ‘exceptionalism’ of security can be theorized.” 26
Therefore, mechanisms of threat response are rarely established ad hoc, but the anticipation of a threat and the exceptionalism of security is built into a variety of provisions, either latent or ongoing.
Response strategies
The logic of exceptionalism is reflected in multiple policy provisions: state of emergency statutes empower government beyond their usual mandate and equally allow for the suspension of rights and freedoms in times of crisis. But the idea of exceptionalism is also embedded in regular governance processes, such as document classification systems, specifically setting apart public sector information in need of protection, primarily based on security arguments. Even transparency provisions reflect the exceptionalism of security, since most freedom of information laws have so-called exemption clauses that “recognize that there are circumstances under which information should not be released because it would harm public or private interests.” 27
Notably, there appears to be a close link between the introduction of secrecy provisions and imminent threats facing a state. For instance, the United States’ classification regime was initially established in the context of the First World War. 28 Similarly, the British Official Secrets Act of 1911 emerged from a war-scare situation. 29 Similarly, the discourse on survival and latent threat during the Cold War culminated in higher degrees of secrecy. 30
Frame challenges
As a primary value, security is described by Wadham and Modi as the “trump card of secrecy.” 31 Critiques, however, argue that it is not always clear whether statements about the importance of security are empirical observations—benchmarking security against other policy objectives—or simply a result of the attributed importance security enjoys. 32 “The national security mind-set will […] make security trump, even if the security gains are at best marginal or speculative or a political performance designed to reassure us that we are doing something in the face of panic or unease.” 33 Amiri notes that the polyvalent meaning of security causes an uncertainty about which information requires protection for security reasons. 34
Moreover, the logic of security “has been used to justify suspending civil liberties, making war, and massively reallocating resources” 35 or establishing a permanent state of emergency. Agamben notes that “the declaration of the state of exception has gradually been replaced by an unprecedented generalization of the paradigm of security as the normal technique of the government.” 36 In a similar vein, Bigo talks about the constant normalizing of exception that justifies almost any governmental intervention. 37 Secrecy also expands across sectors, framing issues as potential “existential” threats that lie beyond questions of “traditional” security. 38
Remedies
A prominent remedy to the problem of secrecy in the face of security threats is the temporal limitation of secrecy. “Disclosure in retrospect” means that previously secret information is released when it has lost its sensitive character. States either set time limits for classification periods (“sunset clauses”) or conduct regular reviews. Thus, control and accountability can be exerted ex post. 39 While the implementation of emergency measures is not hampered by the inertia of democratic processes or ex ante check and controls, decision makers are not incentivized to shirk, since they know that they will be scrutinized later on in the process. However, “accountability in retrospect” has the disadvantage that it offers little room for remedial measures.
Effectiveness frame: Secrecy as a strategic resource
Ideational roots
In a democratic context, the relationship between citizens and states is conventionally thought of as that of a principal and an agent, respectively. This relationship primarily entails for agents (states) to achieve a set mandate. In order to avoid shirking in this pursuit, agents are generally expected to be accountable vis-à-vis citizens (principals). Therefore, transparency, either in the form of monitoring or reporting, provides a precondition for ensuring accountability. In some instances, however, achieving a set mandate might not be possible under scrutiny. “[S]ome policies, if they were made public, could not be carried out as effectively or at all.” 40 In other cases, transparency can create detrimental effects for the efficiency or performance in achieving a governance objective. As Ansell and Torfing observe, “‘Getting things done’ is also a core democratic value, which—under certain circumstances—might call for privileging secrecy over transparency.” 41 Such defences of secrecy rely on a consequentialist justification: secrecy is justified when its benefits clearly outweigh the benefits of open governance.
Problem representation
While the efficiency rationale for secrecy applies to various areas of governance, security affairs is the most prominent example. The importance of information control in defence and intelligence affairs is emphasized throughout the history of strategy. Sun Tzu, for instance, stresses foreknowledge and the employment of secret methodologies to undermine one’s rival. 42 In wartime, Michael Herman argues, secrecy hides the fact that the adversary’s plans have been detected and are being countered. 43 Colaresi points to the importance of security for deceiving a potential enemy or suppressing their capabilities. 44
Not only is secrecy thought to enhance the effectiveness of military and defence operations, but also publicity might effectively undermine security governance. Secrecy is needed for concealing both plans and vulnerabilities from adversaries. 45 Similarly, the disclosure of technical data or tactical information can promote the military capabilities of an adversary. 46 Finally, the enhanced vulnerability of security personnel or infrastructure might jeopardize the implementation of security policies. 47 In the case of intelligence services, the threat of publicity requires the protection of sources and methods since they are the most vulnerable to countermeasures or manipulation. 48
Secrecy might be needed not only for the implementation of policies, but also for the proceeding deliberation. For instance, Cross argues that confidentiality in deliberations among security experts have enhanced the effectiveness of the security and defence policies within the context of the EU. 49 Shielding deliberations from publicity can also be vital for protecting early or delicate discussions, especially around intractable problems or contentious issues. 50
Response strategies
Concrete examples of the effectiveness rationale of national security secrecy can be found throughout current and past military operations. The design of advanced or innovative military technology, intelligence programs, and espionage operations are all protected through secrecy. Covert operations, such as drone strikes, are intended to fulfill their objective without being acknowledged and the rules of engagement are kept secret. Furthermore, back-channel negotiations are a preferred approach as visibility could also undermine delicate bargaining processes pertaining to security issues, such as international peace negotiations.
Frame challenges
While information protection is deemed an essential component for goal attainment and effectiveness in security governance, recent years have shown that secrecy can also have adverse effects. Quill notes that citizens as much as—or even more than—external enemies are the primary target of secrecy measures. 51 The case of the National Security Agency scandal, for instance, illustrates how officially approved surveillance policies, under a secrecy umbrella, are deviating, turning against citizens they set out to protect. Under the auspices of secrecy, the implementation of security policies might also deviate from existing laws or standards, as seen in the human rights abuses in the case of Abu Ghraib. Finally, secrecy can become a problem when it is used to cover failures, thus undermining the effectiveness its use was meant to facilitate. As Aftergood argues, secrecy is abused when it is employed “to advance a self-serving agenda, to evade controversy, or to thwart accountability. In extreme cases, political secrecy conceals violations of law and threatens the integrity of the political process itself.” 52 Consequently, a tension emerges between the desire of transparency versus the need for secrecy, and the question arises as to whether secrecy can undermine other objectives of a polity or the public interest more generally.
Remedies
In the efficiency rationale of secrecy, accountability throughout a governance process might—in lieu of direct observability—be ensured through indirect control. These mechanisms for “guarding the guards” may arise in the form of oversight bodies. For instance, the German parliament institutionalized an oversight committee that has access to classified documents and operates on the premise that “opposition parties must be able to check that majority parties are not using the intelligence services for their own political purposes.” 53 Oversight might also be enabled through ad hoc mechanisms, such as whistleblowing or investigative journalism. 54 Thus, accountability and defence of the public interest might be ensured without jeopardizing the effectiveness of a security policy. While, given the need for goal attainment and effectiveness of operations, transparency might not be guaranteed, it is still possible to ensure event transparency (i.e., the publicity of general policy inputs, outputs, and outcomes). 55
An additional solution is presented by Thompson, who proposes second-order publicity (about the decision to make a process or policy secret) for first-order secrecy (concerning the secret implementation of policies) to bridge the accountability gap created by secrecy. “Publicity about secrecy allows officials to admit that they resort to secrecy, pursuant to which processes, and to explain the reasons for the secrecy even though they do not disclose the specific contents of a secret policy.” 56 This second-order publicity allows citizens to review and potentially challenge secrecy justifications.
Elite governance frame: Secrecy as a privilege
Ideational roots
Contrary to the responsiveness of political representation necessary for the principle–agent framework mentioned above, the elite governance frame presents a trustee model of political representation, in which elected leaders have the autonomy to act in their own conscience, even if decisions go against the preferences of their constituents. The underlying assumption is that political leaders are wiser and more far-sighted than their constituents and, for this reason, more fit to rule. 57 Such ideas can be found in the writings of Joseph Schumpeter, who expressed his disdain for the typical citizen, open to manipulation and engaged only in matters related to their own personal interest. 58 Thus, the idea of elite governance does not only put forward a paternalistic approach, shifting responsibility away from citizens, but also entails a fundamental suspicion of constituents themselves. Proponents of an elite-centric perspective on foreign and security policy 59 promote the conduct of foreign policy through officials with the necessary expertise on the matter, since the stakes are too high to allow uninformed reason to enter the debate. They would be able to identify and protect the genuine “national interest” against smaller, sectional interests.
Problem representation
In the context of elite governance, elected leaders are entrusted to act on their own consciences, identifying the best interest of a polity. Here, secrecy is justified as a protection of governments against the ebbs and flows of public opinion or “tyranny of the majority.” Decision makers need to be protected from popular pressures so that reason can guide their decision-making. It is feared that deliberations under the public gaze would necessarily be reduced to simple heuristics and emotional cues (“plebiscitory reason”), thus leading to suboptimal policy outcomes. 60
The suspicion of the public is especially prominent in the context of security governance, since it is removed from the daily life of ordinary citizens. Their lack of insight, it is assumed, makes them unable to adequately weight their own security interests. 61 Besides a lack of judgment, domestic public opinion is seen as a liability to good political reasoning since it is led by emotion and does not exert constant, objective judgment. 62 A prominent example here is the so-called body-bag syndrome, implying that public support for military engagement decreases with rising casualties. 63 According to Morgenthau, it is the task of responsible leadership to form public opinion and not give in to its pressures. 64 Effective foreign and security policy, in this view, would be prohibited by inclusive, deliberative decision-making and should, instead, be guided by national interest considerations.
The elite governance approach reflects to a degree the rationale that security governance is somehow exceptional in as much as foreign and security policy is thought of as “high politics,” and thus is subject to different considerations and processes than ordinary politics.
Response strategies
An elite governance rationale is underlying many provisions for prerogative powers. The United States’ state secrets privilege (also executive privilege) is the right of the president to withhold information from Congress, the courts and, ultimately, the public if the disclosure would gravely harm national security or undermine deliberations in the public interest. 65
In Germany prerogative powers are granted through the Kernbereich exekutiver Eigenverantwortung (core of executive responsibility) that defines an arcane space for government to deliberate and develop policies without external disturbances. Conventionally, information should be provided only to Parliament after closure of the process, yet exceptions can be granted here, as well as in security-relevant cases.
Frame challenges
The claim for elite governance is countered with the objection that small-group decision-making leads to suboptimal decision-making and power abuse. 66 Notably, the term “groupthink” was coined after a United States military fiasco: the 1961 Bay of Pigs invasion of Cuba. Schlesinger wrote of the preceding deliberations that “meetings were taking place in a curious atmosphere of assumed consensus.” 67 Gibbs illustrates through an analysis of historical cases that, under the disguise of national security reasoning, citizens were led astray into conflicts that did not serve national interests and wasted national resources in unfruitful campaigns. 68
Besides an overestimation of elite decision-making, there appears to also be an underestimation of “crowd intelligence”: Contrary to the elite governance rational, a knowledgeable public is found to be consistent and rational in its attitude toward foreign policy matters. 69
Remedies
Democratic representation requires at least some degree of responsiveness to the demands and preferences expressed by a state’s constituents 70 so that governments are not persistently at odds with the wishes of the represented. If not integrated into the details of decision-making, the public may set at least a “region of acceptability” that sets bounds on politically feasible options. 71 Then, the right to rule, as proposed by Mokrosinska, would be predicated on the condition that the authoritative directives and policies remain within the substantive and procedural scope of limitations determined by citizens. 72
Mansbridge proposes a more communicative approach to accountability that requires that decision makers give reasons, explanations, facts, and improving notification. 73 Such “transparency of rationale” allows for some kind of exchange with constituents and thus a limited form of accountability.
Frame comparison
Overlaps and differences between frames
The specification of frames in the previous section seeks to demonstrate that national security secrecy can be legitimatized not through one, but a variety of rationales. Having disentangled the rationales embedded in the “necessity claim” for secrecy, the analysis now moves on to identify divergences and overlaps of the frames presented above. In a second step, the analysis discusses implications of each frame for democratic values, participation, transparency, and accountability.
The analysis identified divergences between the threat, effectiveness, and elite governance frames. Differences pertain to the way in which secrecy is legitimized and the purpose it serves. The threat frame constructs the legitimacy for secrecy on the basis of a social contract logic, in which the essential tasks of a state is the provision of security. Once security is guaranteed, democratic benefits such as transparency and accountability can follow. From the perspective of the effectiveness rationale, the logic of secrecy is much more dispersed, as it might serve as a strategic tool for enabling policies that are in the public interest and are reviewed by the public, either at the input or output stage. In contrast, proponents of an elite governance rationale perceive secrecy as a bulwark against the ebbs and flows of public opinion, thus enhancing the quality of decisions in the public interest. From this perspective, secrecy is justified by referring to the expertise and experience of democratically elected leaders.
The frames further differ in the way that security is understood and evaluated. In the threat frame, the logic of security is a sine qua non: if security is the precondition for democracies to exist, then security interests override other democratic values. In contrast, the effectiveness frame is less absolute; security does not always trump, but it has to be carefully balanced against other public interests and its de facto benefits. Moreover, the effectiveness frame is not limited to the area of security governance but might serve as a strategic tool even in other policy fields (e.g., when states have to protect the privacy rights of their citizens). This is also the key distinction between the effectiveness and the elite governance frame. The latter is—similar to the threat frame—constructing a difference between normal and exceptional or “high” politics. Compared with the threat frame, however, it is not the logic of security that determines governance choices but the expertise of decision makers.
Despite the differences, however, secrecy rationales are not fully mutually exclusive. First and foremost, all frames argue from a perspective that secrecy is required to enable security. Further, the analysis also identifies overlaps defined as the situational, structural, and public interest functions of secrecy. Both the elite governance frame and the threat frame perceive of secrecy in security affairs as a structural function, meaning that withholding information is a recognized privilege of the political system—either as perennial or a latent mechanism. Yet, as a latent crisis response mechanism, secrecy in the threat frame also has a situational function, applied specifically during imminent danger. Likewise, the effectiveness frame presents secrecy as a strategic instrument applied situationally to serve a specific security-relevant policy objective. Finally, both the effectiveness and the elite governance frame share a perspective that secrecy can serve the public interest, while differing in their understanding of how the public interest emerges: the former solely appeals to secrecy to implement publicly agreed policies, while the latter seeks to protect the policy-making process itself. The overlaps and differences between each frame discussed so far are visualized in Figure 1.
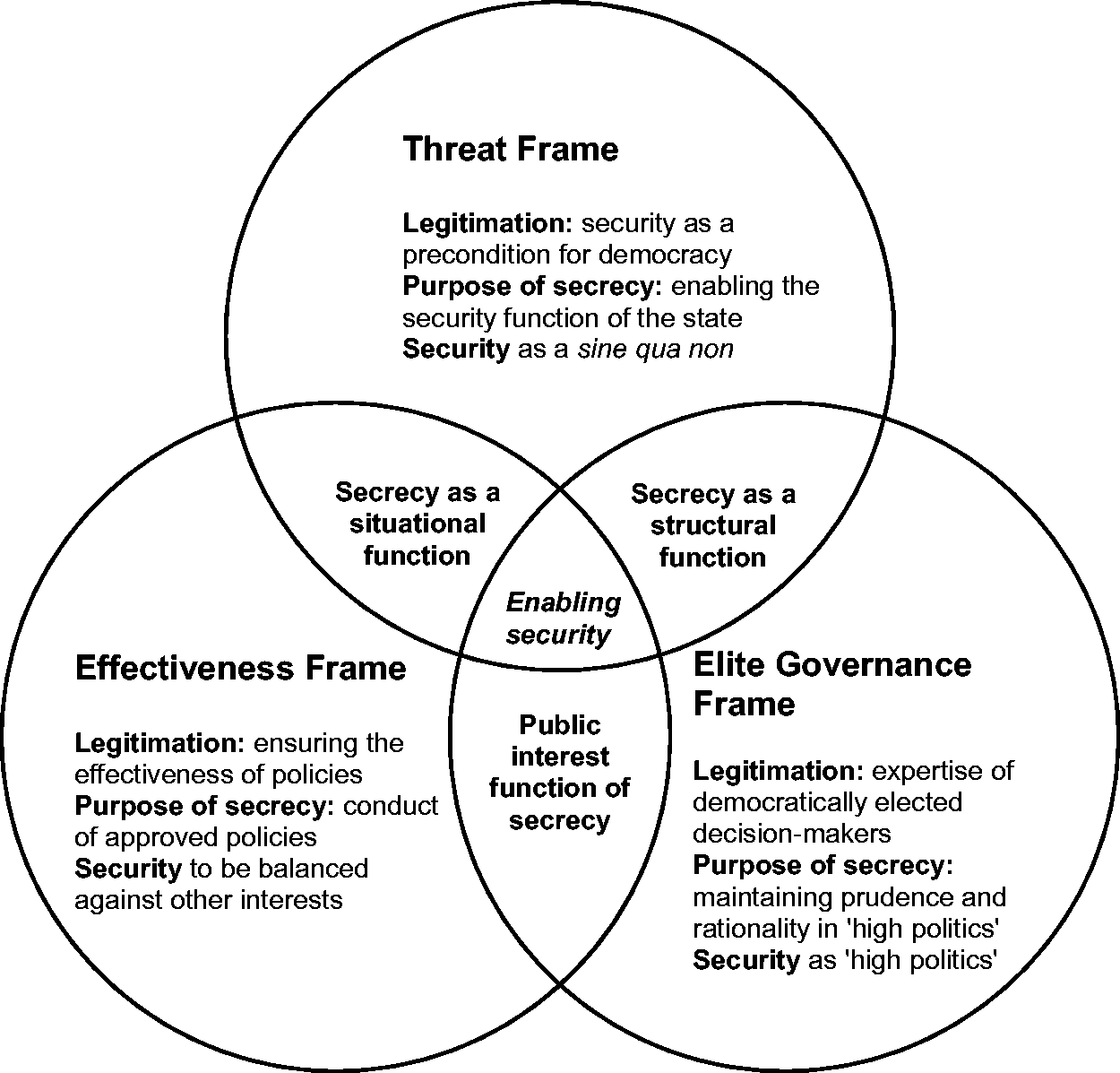
Framing logics—overlaps and differences.
In practice, isolated frames might be used in cases where stakes are low, for instance the implementation rational to justify secrecy in stabilization operations. More often, a conflation, or sequence, of frames is used by decision makers to justify the need for secrecy. Notably, during a crisis all three frames of secrecy might be motivated, appealing to rationales of self-preservation, logics of military effectiveness, and arguments in favour of a centralization of control in closed cabinets. Situational rationales for secrecy might evolve into structural functions, as seen in the case of 9/11. Disentangling different framing rationales is therefore key for ensuring a space for accountability and public involvement.
Appreciation of transparency, participation and accountability per frame
The critical literature review illustrates that some justifications for national security secrecy are more contentious than others, most notably from the transparency–accountability perspective. Since the claim to secrecy is more or less absolute, this leads to a varying scope for public participation and control. What’s more, not all frames fit into the commonly known conceptualization of secrecy as an antipode of transparency.
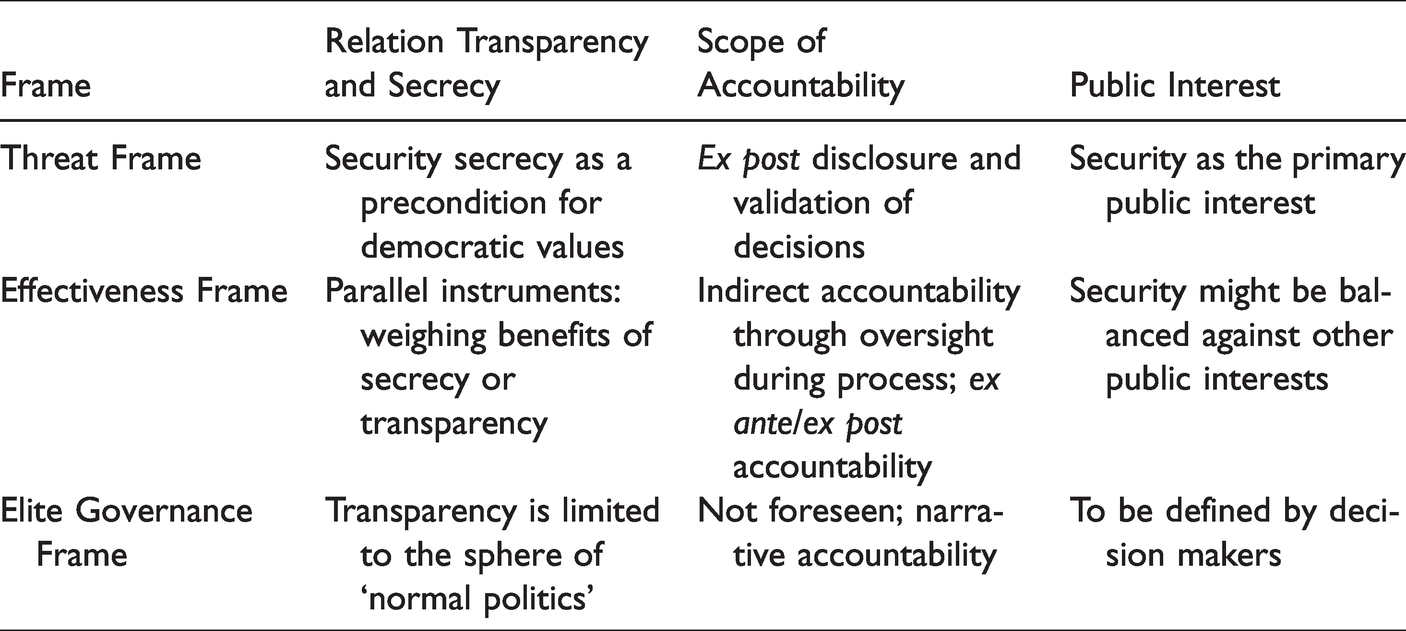
In each frame, the relationship between transparency and secrecy is defined differently. Both the threat and effectiveness frame conceive of secrecy as a strategic function. The effectiveness perspective, however, allows for weighing the benefits of secrecy over transparency within a given situation, whereas in crisis and threat settings, security trumps. Conversely, the elite governance frame perceives of secrecy as an essential continuous function for ensuring rationality and continuity in foreign and security affairs.
Moreover, all three secrecy frames provide different possibilities for public participation and exertion of accountability. Within a threat logic, secrecy is limited to specific scenarios or types of information. In the case of an acute crisis, the problem occurs once a security need—and hence a state of exception—is institutionalized. Here, the public might provide ex post accountability. Equally, the effectiveness frame does not exclude the public per se. Rather, it allows for a discussion of inputs and review of outputs, but not the process of either policy development or implementation. Within an elite governance rationale, the public is, in principle, marginalized as a contributor in questions of international affairs and security issues. Narrative accountability might be provided if decision makers explain and justify their decisions.
Finally, the understanding of the public interest varies quite decisively across frames. The threat frame assumes that security is always in the public interest. The effectiveness frame, in contrast, provides the scope for balancing security against other public interests. The elite governance frame equally grants that the public interest might vary but leaves it to decision makers to weigh different options. Table 1 below illustrates the implication of certain understandings of secrecy of transparency, accountability, and participation.
Implication of framing rationales for transparency, accountability, and public interest considerations.
Implications
The literature on government transparency, including critical publications, generally treats national security secrecy as a unidimensional phenomenon. From this perspective, a tension emerges between transparency proponents, on the one hand, and secrecy proponents on the other hand. The former are concerned with the scope of secrecy provisions, advocating the need for the containment and justification of exemptions. Secrecy proponents, rather, are concerned with national security or foreign relations and thus value the executive’s ability to control access to information. 74
This analysis seeks to illustrate that this binary logic might be too simplistic. The perceived “necessity” for secrecy might be based on very different rationales. While different frames might ultimately support non-disclosure, secrecy frames might contradict one another in their particular propositions and assumptions, such as the role of the public or the objective of secrecy. Further, the tension between transparency and secrecy proponents might be better addressed at the level of such propositions and assumptions rather than the mere dichotomy between provision or non-provision of information.
If national security secrecy constitutes a matter of “necessity,” as the prevalent literature on the topic puts it, one might ask what kind of necessity this claim refers. That is, there is a need to specify at what level the necessity occurs: situational (during imminent crisis), strategic (as a most suitable approach to achieve a political objective), or political (as the most appropriate way to govern more generally). Hence, if, as suggested by Thompson, one asks for a justification of the necessity to render secrecy accountable, such justifications should operate on the proper level.
Finally, the analysis seeks to provide a basis for further investigating legitimation discourses that pertain to national security secrecy. It allows for the identification of dominant framings of national security secrecy (e.g., in a cross-country comparison of secrecy practices, framing conflicts surrounding secrecy practices, and the strategic use of specific frames by government actors). Moreover, a nuanced understanding of frames provides us with a specific understanding of rules and regulations that provide for government secrecy, such as the presence or absence of emergency or secrecy laws and the ways in which exemption regimes are conceptualized.
Conclusions and further research
This paper contributes to ongoing research efforts that aim to better understand the complexities of transparency and secrecy for legitimacy, accountability, and democracy of governance. 75 Specifically, this analysis seeks to provide a nuanced understanding of the role of secrecy, which is conventionally described as a flipside of transparency, inasmuch as transparency is understood as “lifting the veil of secrecy.” While the literature and public discourse conventionally presents transparency and secrecy as binaries, both concepts are actually ambiguous, politicized, and at times parallel, shaped by context and concrete interpretation. Disentangling national security secrecy, as done in this analysis, points to ways in which the complex nature of government secrecy in general can be understood. Through the example of national security secrecy, this analysis illustrates that secrecy does not necessarily undermine accountability and legitimacy, but might, following other rationales, be perceived as a precondition for all benefits conventionally associated with transparency.
Transparency itself is not one dimensional and solely beneficial to democratic governance, but “laden with symbolic value, irrespective of [its] political significance.” 76 This paper argues that future research might investigate secrecy, not in relation to transparency, but instead focused on the dynamics, impact, and structures of secrecy as a mechanism per se, thus bypassing any normative assumptions regarding its desirability. It might be beneficial to investigate secrecy as a governance instrument that exists in concert with transparency, not in opposition. Here, secrecy, like transparency, might be motivated by values such as accountability or legitimacy.
This analysis might be a useful tool for practitioners and advocates of transparency to critically disentangle governments’ claims for national security secrecy, identifying mismatches between rhetoric and concrete action. Diverse secrecy rationales are often muddled together as one; for instance, using an implementation rationale to justify secrecy at the decision-making level or needlessly transferring exceptionalism rationales to promote a more national interest rationale in the long term.
Another consideration this paper raises is the relevance of embedding questions of transparency, accountability, or secrecy within the specific field to which they apply. As the example of national security secrecy shows, legitimations for concealment cannot be discussed in isolation, but might be embedded in the specific rationales of a sector and, therefore, other academic disciplines. Future research might need to take a more interdisciplinary perspective to fully appreciate the dynamics of good and accountable governance within specific policy fields.
Besides a more nuanced understanding of the relation between transparency and secrecy, this paper also sought to illustrate the central role of rationales and ideas that determine the way in which political legitimacy might be achieved. It includes the presence of prevailing narratives and rationalizations of national security secrecy that might determine the way in which transparency and secrecy operate in practice. Dominant rationales might be understood as tacit institutions in as much as they display system-stabilizing functions, such as the idea of a “national interest” as a means to normalize foreign policy choices and generate support for international action.
Footnotes
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
1
Jana Costas and Christopher Grey, “Bringing secrecy into the open: Towards a theorization of the social processes of organizational secrecy,” Organization Studies 35, no. 10 (2014): 1423–1447.
2
Dorota Mokrosinska, “Why states have no right to privacy, but may be entitled to secrecy: A non-consequentialist defense of state secrecy,” Critical Review of International Social and Political Philosophy 23, no. 4 (2018): 21.
3
Marlen Heide and Ben Worthy, “Secrecy and leadership: The case of Theresa May’s Brexit negotiations,” Public Integrity 21, no. 6 (2019): 582–594.
4
Albert Meijer, Paul ’t Hart, and Ben Worthy, “Assessing government transparency: An interpretive framework,” Administration & Society 50, no. 4 (2018): 501–526.
5
Sissela Bok, Secrets: On the Ethics of Concealment and Revelation (New York: Pantheon Books, 1982).
6
7
Achim Hurrelmann, “Empirical legitimation analysis in International Relations: how to learn from the insights – and avoid the mistakes – of research in EU studies,” Contemporary Politics 23, no. 1 (2017): 63–80.
8
Jeremy Waldron, Liberal Rights: Collected Papers 1981–1991 (Cambridge: Cambridge University Press, 1993), 56.
9
Steven Aftergood, “Reducing government secrecy: Finding what works,” Yale Law and Policy Review 27 (2009): 399–416.
10
Erving Goffman, Frame Analysis: An Essay on the Organization of Experience (Cambridge, MA: Harvard University Press, 1974).
11
William. A. Gamson and Andre Modigliani, “The changing culture of affirmative action,” in Richard Raungart, ed., Research in Political Sociology (Greenwich, CT: Jai Press, Inc., 1987), 143.
12
Robert Entman, “Cascading activation: Contesting the White House's frame after 9/11,” Political Communication 20, no. 4, (2003): 415–432.
13
Jörg Matthes and Matthias Kohring, “The content analysis of media frames: Toward improving reliability and validity,” Journal of Communication 58, no. 2 (2008): 258–279.
14
Rianne Dekker, “Frame ambiguity in policy controversies: Critical frame analysis of migrant integration policies in Antwerp and Rotterdam,” Critical Policy Studies 11, no. 2 (2017): 127–145.
15
Francesco Olmastroni, Framing War: Public Opinion and Decision-Making (New York: Routledge, 2014).
16
Deborah Stone, Policy Paradox. The Art of Political Decision-Making (New York: W.W. Norton & Company, 1988).
17
Donald Schön and Martin Rein, Frame Reflection: Toward the Resolution of Intractable Policy Controversies (New York: Basic Books, 1994).
18
Donald Schön and Martin Rein, “Frame-critical policy analysis and frame-reflective policy practice,” Knowledge and Policy 9, no.1 (1996): 85–104.
19
Merlijn van Hulst and Dvora Yanow, “From policy ‘frames’ to ‘framing’: Theorizing a more dynamic, political approach,” The American Review of Public Administration 46, no. 1 (2016): 92–112.
20
Colin Elman and Michael Jensen, The Realism Reader (London: Routledge, 2014).
21
Mikkel V. Rasmussen, “Reflexive security: NATO and international risk society,” Millennium 30, no. 2 (2001): 287.
22
Gabriel Schoenfeld, Necessary Secrets: National Security, the Media and the Rule of Law (New York: Norton & Co., 2010), 21.
23
Stephen Schulhofer, “Secrecy and democracy: Who controls information in the national security state?” NYU School of Law, Public Law Research Paper, no.10-53 (2010): 4.
24
Giorgio Agamben, State of Exception (Chicago: University of Chicago Press, 2004).
25
Christian Kreuder-Sonnen, “Political secrecy in Europe: Crisis management and crisis exploitation,” West European Politics 41, no 4 (2018).
26
Claudia Aradau, “Security and the democratic scene,” Journal of International Relations and Development 7, no. 4 (2004): 388–413.
27
David Banisar, “Public oversight and national security: Comparative approaches to freedom of information,” in Hans Born and Marina Caparini, eds., Democratic Control of Intelligence Services: Containing Rough Elephants (UK: Ashgate, 2007), 223.
28
Harold C. Relyea, “Government secrecy: Policy depths and dimensions,” Government Information Quarterly 20, no. 4 (2003): 395–418.
29
Christopher Moran, Classified: Secrecy and the State in Modern Britain (New York: Cambridge University Press, 2012), 24.
30
Thomas S. Blanton, “National security and open government in the United States: Beyond the balancing test,” in Campbell Public Affairs Institute, ed., National Security and Open Government: Striking the Right Balance (New York: The Maxwell School of Syracuse University, 2003), 33–74.
31
John Wadham and Kavita Modi, “National security and open government in the United Kingdom,” in Campbell Public Affairs Institute, ed., National Security and Open Government: Striking the Right Balance (New York: The Maxwell School of Syracuse University, 2003), 97.
32
Rasmussen, “Reflexive security,” 286.
33
Lawrence Quill, Secrets and Democracy: From Arcana Imperii to WikiLeaks. (Basingstoke: Palgrave Macmillan, 2014), 60.
34
Amin P. Amiri, Freedom of Information and National Security. A Study of Judicial Review Under US Law (München, Germany: Herbert Utz Verlag, 2014), 20.
35
David Baldwin, “The concept of security,” Review of International Studies 23, no. 1 (1997): 9.
36
Agamben, State of Exception.
37
Didier Bigo, “Security, surveillance and democracy,” in Kirstie Ball, Kevin D. Haggerty, and David Lyon, eds., Routledge Handbook on Surveillance Studies (New York: Routledge, 2012), 277–284.
38
Berthold Rittberger and Klaus H. Goetz, “Secrecy in Europe,” West European Politics 41, no. 4 (2018): 825–845.
39
40
Dennis F. Thompson, “Democratic secrecy,” Political Science Quarterly 114, no. 2 (1999): 182.
41
Christopher Ansell and Jacob Torfing, “Transparency,” in Christopher Ansell and Jacob Torfing, eds., Handbook of Theories of Governance (Cheltenham, UK: Edward Elgar, 2016), 219.
42
Quill, Secrets and Democracy, 18.
43
Michael Herman, Intelligence Power in Peace and War (Cambridge: Cambridge University Press, 1996), 88.
44
Michael P. Colaresi, Democracy Declassified. The Secrecy Dilemma in National Security (Oxford: Oxford University Press, 2014).
45
David E. Pozen, “Deep secrecy,” Stanford Law Review 62, no. 2 (2010): 277.
46
Cass R. Sunstein, “Government control of information,” California Law Review 74, no. 3 (1986): 895.
47
Ibid., 895.
48
Mark A. Chinen, “Secrecy and democratic decisions,” Quinnipiac Law Review 27, no. 1 (2009): 1–53.
49
Mai’a. K. Davis Cross, ‘Secrecy and the making of CFSP,” West European Politics 41, no. 4 (2018): 914–932.
50
Deidre Curtin, “Overseeing secrets in the EU: A democratic perspective,” Journal of Common Market Studies 52, no. 3 (2014): 684–700.
51
Quill, Secrets and Democracy, 30.
52
Aftergood, “Reducing government,” 403.
53
Kim Scheppele, “We are all post-9/11 now,” Fordham Law Review 75, no. 2 (2006): 607–629.
54
Raul Sagar, Secrets and Leaks: The Dilemma of State Secrecy (Princeton, NJ: Princeton University Press, 2013).
55
David Heald, “Varieties of transparency,” in Christopher Hood and David Heald, eds., Transparency: The Key to Better Governance (Oxford: Oxford University Press, 2006), 246.
56
Dorota Mokrosinska, “Democratic authority and state secrecy,” Public Affairs Quarterly 33, no. 1 (2019): 10.
57
Jane Mansbridge, “A ‘selection model’ of political representation,” The Journal of Political Philosophy 17, no. 4 (2009): 386.
58
Ibid., 387.
59
Walter Lippmann, Essays in the Public Philosophy (Boston: Little Brown, 1955); and John J. Mearsheimer, “Back to the future. Instability in Europe after the Cold War,” International Security 15, no. 1 (1950): 5–56.
60
Simone Chambers, “Behind closed doors: Publicity, secrecy, and the quality of deliberation,” The Journal of Political Philosophy 12, no. 4 (2004): 398–410.
61
Kenneth Ward, “The fog of war: Checks and balances and National security policy,” Maryland Law Review 67, no. 1 (2007): 38, https://digitalcommons.law.umaryland.edu/cgi/viewcontent.cgi?referer=&httpsredir=1&article=1058&context=schmooze_papers (accessed 22 April 2020).
62
Thomas Knecht and M. Stephen Weatherford, “Public opinion and foreign policy: The stages of presidential decision making,” International Studies Quarterly 50, no. 3 (2006): 707.
63
Leonie Murray, “Somalia and the ‘body bag myth’ in American politics,” International Politics 44, (2007): 552–571.
64
Hans J. Morgenthau, Politics Amongst Nations (New York: Knopf, 1967), 142.
65
Sagar, Secrecy and Leaks, 41; Mark Rozell, “Executive privilege and the modern presidents: In Nixon's shadow,” Minnesota Law Review 83, no. 5 (May 1999): 1069–1126.
66
Simone Chambers, “Behind closed doors: Publicity, secrecy and the quality of deliberation,” The Journal of Political Philosophy 12, no. 4 (2004): 405; and Irving L. Janis, Victims of Groupthink: A Psychological Study of Foreign-Policy Decisions and Fiascos (New York: Houghton Mifflin, 1972).
67
Arthur M. Schlesinger, A Thousand Days: John F. Kennedy in the White House (Boston: Houghton Mifflin, 1965), 250.
68
David N. Gibbs, “Secrecy and international relations,” Journal of Peace Research 32, no. 2 (1995): 213–228.
69
Cigdem V. Sirin, “Public support for military interventions across levels of political information and stages of intervention: The case of the Iraq War,” Armed Forces and Society 38, no. 2 (2012): 252–272.
70
Nadia Urbinati and Mark E. Warren, “The concept of representation in contemporary democratic theory,” Annual Review of Political Science 11, no. 1 (2008): 387–412.
71
Knecht and Weatherford, “Public opinion and foreign policy,” 707.
72
Mokrosinska, “Why states,” 5.
73
Mansbridge, “A ‘selection model’.”
74
Mark Fenster, “The implausibility of secrecy,” Hastings Law Journal 65, no. 2 (2014): 314.
75
see e.g. Mark Fenster, “Transparency in search of a theory,” European Journal of Social Theory 18, no. 2 (2015): 150–167; Albert Meijer, “Understanding the complex dynamics of transparency,” Public Administration Review 73, no. 3 (2013): 429–439; Clare Birchall, Radical Secrecy: The Ends of Transparency in Datafied America (Minneapolis: University of Minnesota Press, 2021); Dorota Mokrosinska, D., ed., Transparency and Secrecy in European Democracies: Contested Trade-offs (Routledge, 2020); Berthold Rittberger and Klaus Goetz, “Secrecy in Europe” West European Politics, 41, no.4, 825–845.
76
Ben Worthy, On the Politics of Freedom of Information (Manchester, UK: Manchester University Press, 2017), 2.
