Abstract
With the widespread deployment of smart meters in smart grids and the transformation of communication methods from wired to wireless, the communication security issues are becoming more and more prominent, especially facing dynamic attack threats such as malicious signal interference and meter data corruption, but there are also problems of low detection efficiency and resource waste. To address this problem, this paper proposes a dynamic attack and defense detection model based on Bayesian game under resource-constrained conditions. In order to characterize the game behavior of attackers and defenders under incomplete information conditions, a two-stage game process is designed to simulate attack scenarios such as eavesdropping and interference, and the Beta distribution is introduced for dynamic belief update to enhance the defender’s adaptability to attack situations. Combining the performance and communication characteristics of heterogeneous nodes, a bipartite graph matching mechanism is introduced, and the optimal allocation of defense resources is achieved based on the Hungarian algorithm, thereby reducing the overall defense cost while ensuring system security. The simulation experimental results show that the proposed model can effectively improve the defense success rate in a dynamic environment, which is better than random defense, full coverage defense and traditional machine learning methods. The strategy optimized by the Hungarian algorithm reduces costs and increases benefits. Its feasibility and efficiency in actual smart grid applications are verified.
Introduction
The world faces the challenges of climate change and energy sustainability, achieving dual carbon goals critical for sustainable development. Smart meters are essential for energy management, providing accurate data, facilitating intelligent regulation, and enhancing efficiency. They monitor consumption, reduce costs, influence habits, and optimize industrial and commercial processes. Smart meters also play a crucial role in innovative city development and energy market regulation, supporting sustainable energy systems and transforming the energy industry.
With the rise of new load terminals like electric vehicles, smart meter deployment is growing. Power companies are leveraging wireless technology for cost savings in data transmission. Wireless smart meter systems, which include meters, communication modules, data processing units, and remote monitoring systems, are integral to smart grids. 1 As shown in Figure 1, meter devices are responsible for real-time collection of electrical energy data, communication modules achieve remote communication with power companies, data processing units process the collected data and generate reports, while remote monitoring and control systems handle monitoring and control functions of the meters.
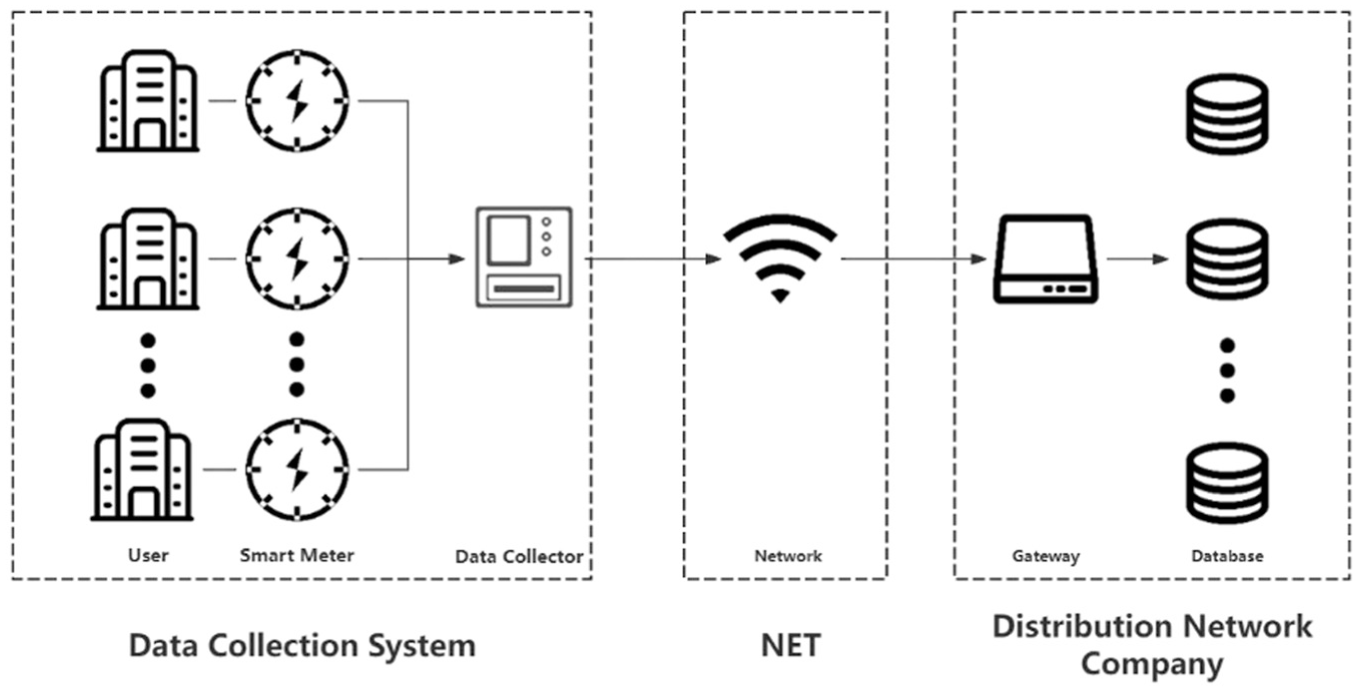
Smart meter transmission system.
The use of wireless channels in smart meter systems can reduce the deployment cost of smart meter data transmission. they also introduce new problems. Compared to wired transmission, wireless channels are more susceptible to interference and eavesdropping, allowing unauthorized third parties to access or tamper with user electricity data potentially. Such interference can lead to data transmission interruptions or errors, affecting the operation and management of the power system. Moreover, the physical security of smart meters faces challenges, such as being susceptible to tampering or destruction, resulting in forged or stolen electricity consumption data. The security of power data has always been a major challenge facing the power security industry. The widespread use of smart meter systems has made the manipulation of electricity data more subtle and complex. According to industry statistics, electricity theft and abnormal data behaviors lead to significant economic losses each year. For example, China reports annual losses of nearly 10 billion yuan, while India experiences the most severe power data falsification globally, with losses exceeding 16.2 billion dollars. 2 These figures highlight the urgent need for effective security mechanisms in smart meter systems.
There have been numerous studies on attacking smart meters at home and abroad. To detect cyberattacks on a single smart meter, Du et al. 3 proposed a novel data-driven method based on dimensionality enhancement of recursive graphs (RP) and visual geometry group networks (VGGNet) for detecting false data injection in smart meters. Wang et al. 4 introduced honeypot technology into the smart grid AMI network to deal with DDoS attacks. They considered the anti-honeypot problem from the attacker’s perspective and proposed a honeypot game strategy to analyze the strategic interaction between attackers and defenders. Jim Solomon Raja et al. 5 proposed an intrusion detection and prevention system designed to be implemented on a real-time AMI testbed. Transmission Control Protocol (TCP) synchronization (SYN) attacks of different intensities were simulated, and data packets were captured. The optimality was ensured by verifying the existence of a Nash equilibrium in a two-player non-cooperative game. Ryu proposed a physical unclonable function (PUF) lightweight encryption method to enhance the wireless connection security of smart meter sensor nodes. 6
In the case of abnormal electricity consumption data, it is crucial to consider the security of smart meter systems in wireless environments. Haq et al., 7 Chen et al., 8 and El-Toukhy et al. 9 proposed theft detection models based on historical data, but these models react after theft occurs rather than preventing it. Wang et al. have proposed a game model under node capability differences, 10 which can reduce the detection cost for intruders while ensuring a specific detection rate. However, they did not consider the impact of channel parameters in wireless environments on the model. Kumar et al. 11 studied the performance of smart meters under wired and wireless network security attacks and evaluated the performance of wired and wireless smart meters under network security attacks. Tu et al. 12 proposed a secure network architecture based on cognitive radio (CR) as a countermeasure. By dynamically utilizing unused PU bands, it is more difficult for data streams to be intercepted. Dai et al. presented the implementation of Quantum Key Distribution (QKD) in smart grids. 13 Through theoretical analysis and application scenario evaluation, we demonstrated the feasibility of using QKD to ensure wireless security in smart grids. Xu et al. proposed a cooperative jamming attack strategy for the smart grid, 14 in which a team of mobile attackers interferes with the electricity price signal sent by the control center to the power user, and stops the jamming when the real price value detected by the attacker changes significantly. Ma et al. 15 proposed a multi-behavior dynamic game strategy between attackers and defenders to initiate interference attacks in the power market. Gai et al. 16 proposed an attack strategy against Cognitive Wireless Network (CRN) in Wireless Smart Grid Networks (WSGN). The proposed method using the Maximum Attack Strategy for Spoofing and Jamming (MAS-SJ) optimizes the allocation of power in spoofing and jamming attacks by applying dynamic programing. Mensi et al. 17 used a hybrid beamforming design for wireless communication in smart grids. Design and evaluate the Gradient Ascent algorithm to find the best combiner/waveform to maximize the confidentiality of smart grid communications.
Based on the above research status of smart meters at home and abroad, the author believes that the following aspects need to be further explored and clarified:
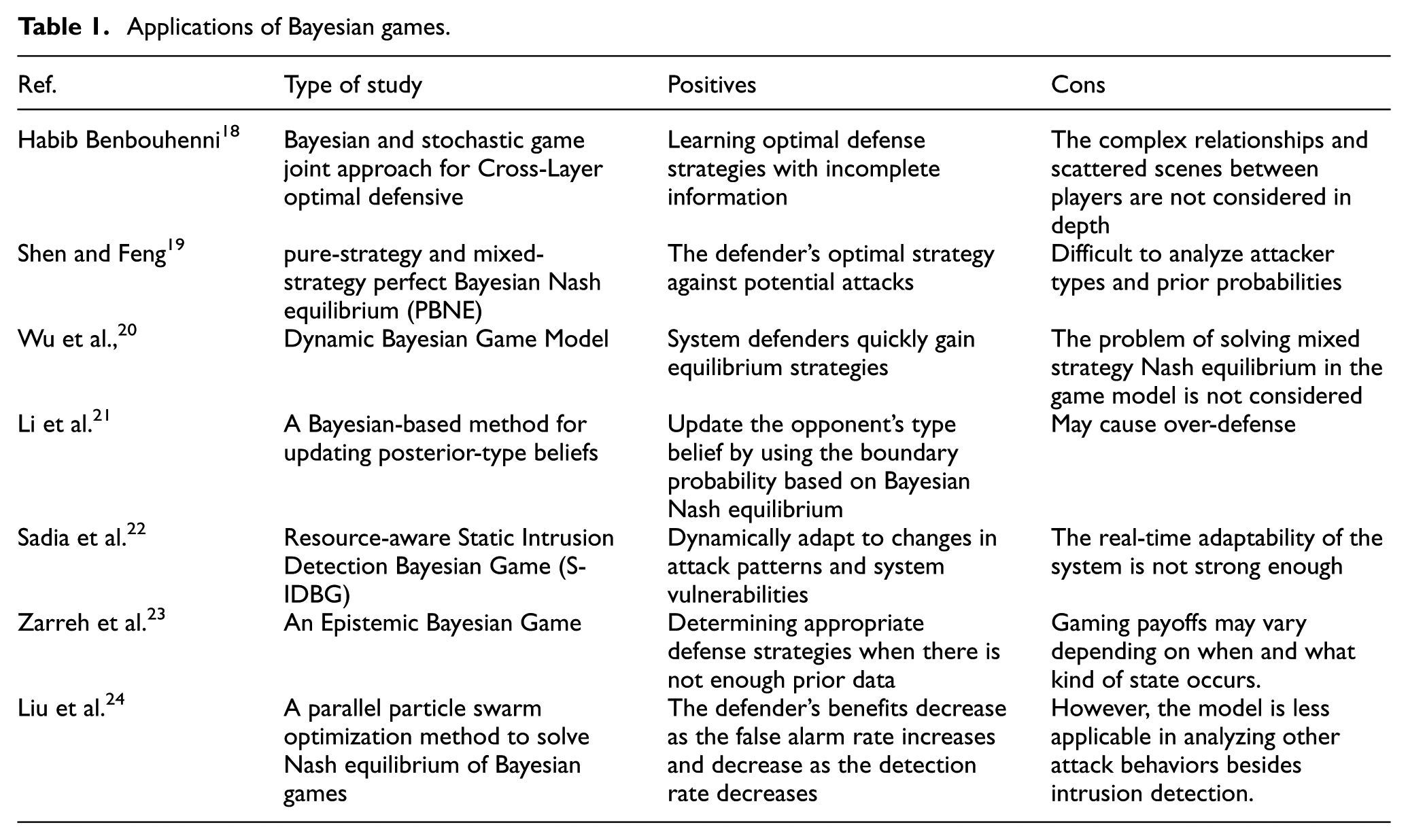
In response to these problems, this paper focuses on improving detection accuracy by studying malicious modifications to electricity usage data in real time, even under resource-limited conditions. By analyzing the strengths and weaknesses of various models and algorithms listed in Table 1, the authors introduce a game-theoretic model to optimize the security of smart meter systems through a dynamic attack-defense game. Specifically, the main contributions of this paper are as follows:
Applications of Bayesian games.
Through this study, the author hope to provide valuable insights for the security design of smart meter systems, better cope with the challenges faced by the power industry, and ensure the reliable operation of smart grids.
The paper is structured as follows: Section 2 reviews the technical overview of smart meter systems, security challenges, and research gaps. Section 3 constructs the game model, analyzes pure strategy and Bayesian equilibrium, and considers the impact of attack and defense capabilities in wireless channels. Section 4 optimizes the model using the Hungarian algorithm to derive the optimal defense strategy. Section 5 discusses experimental design and result analysis. Section 6 concludes the research and explores future directions.
Related work
Overview of smart meter systems and security research
Several scholars have explored the security issues of smart meter systems. Bhattacharjee et al. 25 used false injection attacks to manipulate consumption data, while Kumar et al. 26 focused on denial-of-service attacks on commercial-grade smart meters. Díaz Redondo et al. 27 investigated vulnerabilities by conducting denial-of-service and malicious software attacks on residential smart meters. Studies on grid attacks have examined various attack types, including man-in-the-middle attacks on smart meters, 28 denial-of-service attacks, 29 and electricity load attacks, showing that authentication alone does not protect meters. 30
While most existing research focuses on technical vulnerabilities and attack strategies, relatively little attention has been paid to the resource cost of attackers. However, attacker resource consumption (such as computation and communication overhead) can affect the sustainability of large-scale attacks. Considering these factors can provide a more realistic perspective for defense strategy design, although this paper primarily emphasizes the defense efficiency under limited defender resources. as it relates to the sustainability, cost, and potential impacts of attacks. Research should not only focus on technical attack details and system vulnerabilities, but also consider the resources attackers use during implementation. Modeling attacker resource consumption will offer new insights for power system security research, helping to develop more comprehensive and sustainable defense strategies.
Application of game theory in power systems
Game theory, widely used in fields like operations research, economics, and ecology, focuses on decision-making methods to maximize individual interests. Recently, game theory has been applied to smart grids,31–33 particularly in power system security. Hasan et al. 34 used game theory to design an attacker-defender model where attackers determine attack timings to maximize system damage. Ge et al. 35 proposed a resource allocation method based on game theory for defending against potential network attacks in smart grids. Pilz et al. 36 introduced a false data injection attack on demand prediction data and its effects on system parameters, with proposed monitoring strategies and game theory support for utility companies’ defense resource allocation.
Existing research mainly focuses on the benefits of both sides in the game, but lacks in-depth analysis of target node values and the actual capabilities of attackers and defenders. More research is needed to explore these elements in the dynamic game process to improve understanding and help develop more effective defense strategies for power systems.
Attacks and defenses in wireless channels for smart meters
Common signal interference attack methods
In wireless channel environments, interference attacks are a means of causing denial of service by preventing data packet exchanges between legitimate nodes. 37 Interferers may choose to occupy the channel or cause collisions, disrupting data packets and forcing nodes to retransmit. 38 The following are introductions to standard interference attack models for wireless sensor networks:
Constant Interference Attack 39 : The basic strategy of this attack is to transmit random bits on the channel to occupy the transmission channel. Attackers occupy channel resources by continuously sending random bits, thereby preventing standard data transmission between legitimate nodes.
Deceptive Interference Attack 40 : Unlike constant interference attacks, attackers in deceptive interference attacks do not send random bits but continuously transmit data packets on the channel. This method may mislead legitimate nodes, causing them to fail to identify valid data packets, thereby degrading communication quality correctly.
Random Interference Attack 41 : This method allows attackers to save energy by transitioning from active to sleep states at random time intervals. Attackers can selectively interfere with channels based on specific strategies to maximally affect the communication of target nodes while minimizing energy consumption.
These interference attack methods pose significant threats to wireless communication in smart meter systems, disrupting data transmission and potentially compromising the security and reliability of the entire system. Therefore, effective defense mechanisms need to be developed to mitigate the impact of such attacks and ensure the secure and reliable operation of smart meter systems.
Introduction to detection mechanisms
The overall idea of detecting interference attacks on wireless channels involves analyzing changes in sensitive attributes of senders or receivers before and after the occurrence of interference attacks.
Signal Strength 42 : Signal strength is a parameter that measures the communication quality between devices. An abnormal change in signal strength may indicate external interference affecting communication between devices.
Packet Loss Rate 43 : The packet loss rate reflects the reliability of data transmission, and abnormal packet loss may be caused by signal interference.
Spectrum Analysis 44 : Spectrum analysis is used to observe the distribution of signals in the wireless spectrum. Abnormal activity suggests possible external interference.
Carrier Sense Time 45 : Carrier sense time refers to the time during which wireless communication devices listen to the spectrum before transmitting data to detect whether other devices are using the spectrum. During interference attack monitoring, abnormal carrier sense time may indicate the presence of illegal signals on the spectrum, that is, interference attacks.
In practical smart meter attack and defense scenarios, few people combine specific wireless channel attack defense with energy consumption considerations. Although the design of modern smart meter systems is increasingly focused on security, when considering attack and defense, more attention is often paid to aspects such as data security and encryption of communication protocols.46,47 Defense against wireless channel attacks is often underestimated, with relatively less attention paid to energy consumption. Defense measures against wireless channel attacks may impact the energy consumption of smart meters. For example, to combat malicious persistent interference attacks, smart meters may need to continuously monitor channel status and take additional protective measures, which would increase device energy consumption. Additionally, some efficient defense mechanisms may require more computational resources and communication overhead, further increasing the energy consumption of smart meter systems.
Therefore, in the design of smart meter attack and defense, in addition to focusing on security and functionality, consideration should also be given to the impact of defense measures on energy consumption. If these factors are considered during the design phase, a balance between security and energy efficiency can be achieved, ensuring that smart meter systems can maintain stable operation when facing security threats without excessively consuming of energy resources.
Two-stage Bayesian dynamic game model in wireless channel
This section presents a two-stage Bayesian dynamic game model for wireless channels, illustrating the strategic interactions between defenders and attackers in a smart meter environment. We begin by analyzing the two-stage attack-defense game, focusing on the defenders’ and attackers’ strategic choices before and after monitoring. Next, we extend the model to a dynamic Bayesian game, employing Bayesian methods and Beta distributions to update the defender’s understanding of the game state. Finally, the authors study pure and mixed strategy Nash equilibria, identifying optimal strategies for attackers and defenders under different cost and probability scenarios. This model provides valuable insights into attack-defense dynamics in smart meter systems, offering both theoretical and practical support for tackling various attack strategies.
Strategic interaction
In the two-stage attack-defense game model, the strategic interaction between defenders and attacker present a complex dynamic relationship. In smart meter systems, the defender’s task is to monitor and protect the meter from illegal operations, while the attacker attempts to implement illegal operations through various means. Figure 2 illustrates the four possible scenarios of strategic interaction between the two sides.
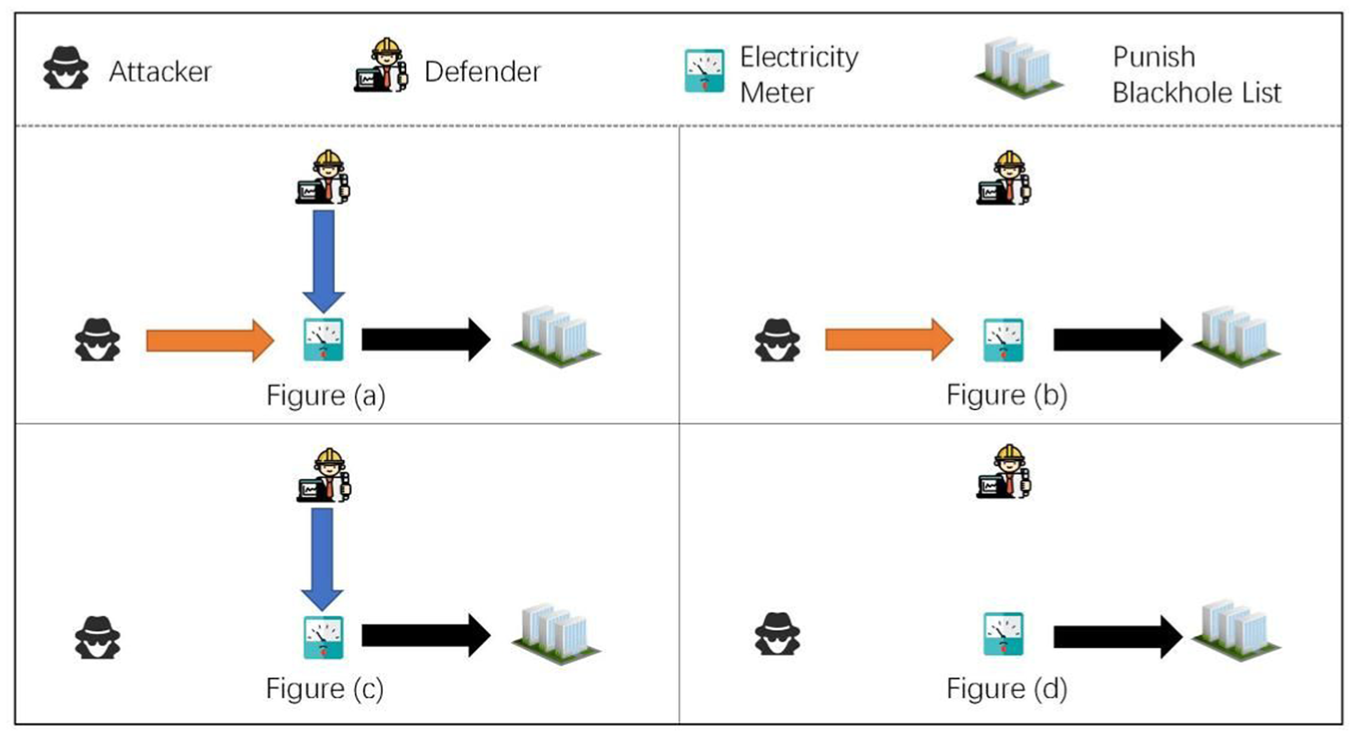
illustrates the strategic interaction between defenders and attacker.
Figure 2 shows four strategic interactions between defender and attacker. The defender monitors meters, while the attacker attempts illegal actions. Figure (a) illustrates a successful defense, where the attacker is discovered and penalized. Figure (b) illustrates the absence of monitoring, allowing the attacker to attack undetected. Figure (c) illustrates wasted resources, as the defender monitors but the attacker’s actions are not carried out. Figure (d) shows no attack or monitoring. These scenarios highlight the interdependence of strategies, where defenders aim to optimize monitoring, and attacker adapt to avoid detection.
Model parameters
The game model defines the strategic interaction between the attacker and the defender (power distribution company). The attacker attempt to disrupt smart meter energy data through signal jamming, while the defender aims to detect and punish such behavior through monitoring. The model parameters are defined as follows:

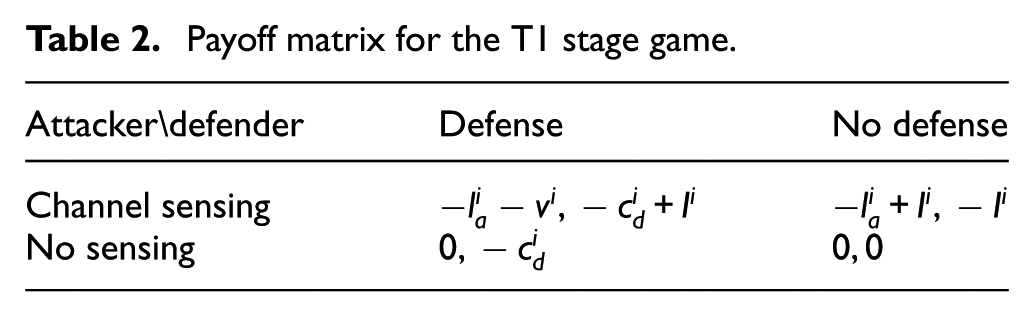
In the Non-Eavesdropped State (T1), the attacker has not monitored the channel and lacks information about the meter. The attacker can choose to monitor or not, while the defender can choose to defend or not. The corresponding payoff matrix is as follows:
In this context,
In state T1, the payoffs for both the attacker and the defender are determined by their respective strategy combinations. Firstly, suppose the attacker chooses to eavesdrop on the channel while the defender opts for defense. In that case, the attacker’s payoff is the eavesdropping cost
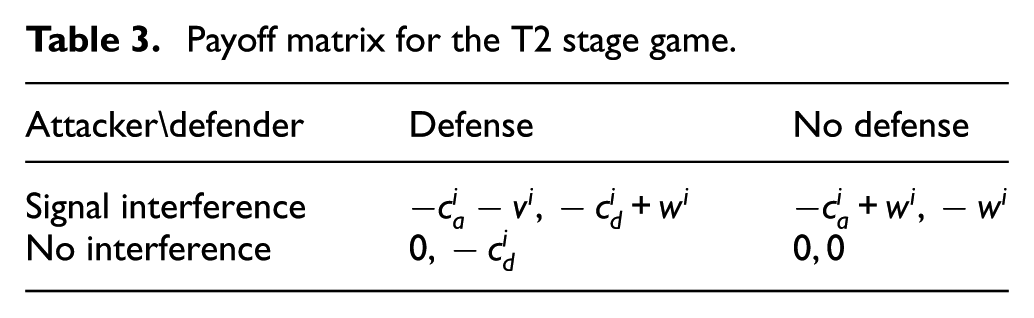
Eavesdropped State (T2) In this state, the attacker has successfully eavesdropped on the channel and obtained information about the smart meter. They might have learned the operating patterns, communication protocols, and potential vulnerabilities of the meter. This enables the attacker to devise and execute a signal interference strategy more effectively to achieve their objectives. Therefore, in the T2 state, the attacker can choose to interfere with the signal or not, and the defender can choose to defend or not. Table 3 presents the payoff matrix for the participants in the T2 state. Here,
In the T2 state, the payoffs for both the attacker and the defender are determined by their respective strategy combinations. Firstly, if the attacker chooses to interfere with the signal while the defender opts for defense. In that case, the attacker’s payoff is the interference cost
Belief Function:
Utility Weighting: The utility function,
Based on the situations in Tables 2 and 3, we have derived the final utility functions for both the attacker and the defender in each round of the game. Here,
Payoff matrix for the T1 stage game.
Payoff matrix for the T2 stage game.
Calculation of Attacker’s Payoff in the Non-Eavesdropped State (equation (2)):
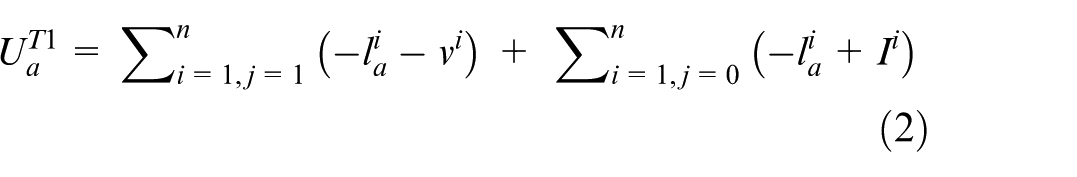
Here,
Then the calculation of Attacker’s Payoff in the Eavesdropped State (equation (3)):
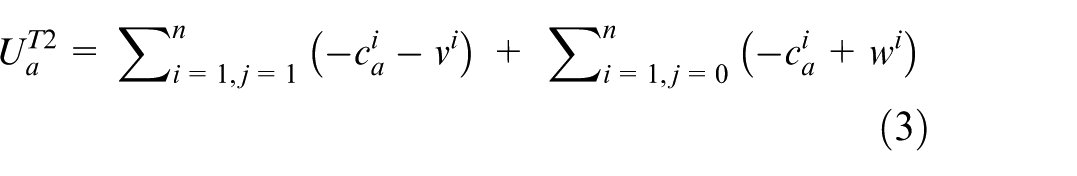
Here,
The total Utility Function of the Attacker can be calculated by equations (2) and (3) (equation (4)):
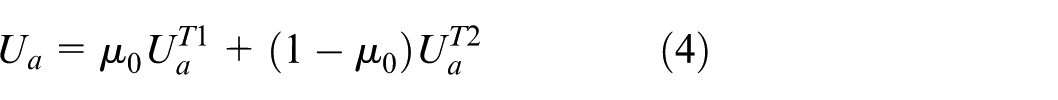
This equation is derived based on the payoff matrix in the game model, which includes costs and benefits for different action combinations. The attacker can choose different actions in each state and obtain corresponding payoffs or incur costs based on the outcomes of these actions. Ultimately, the total utility of the attacker is obtained by weighting the payoffs in each state, where the weights are determined by the defender’s belief function
Following calculation of Defender’s Payoff in the Non-Eavesdropped State (equation (5)):
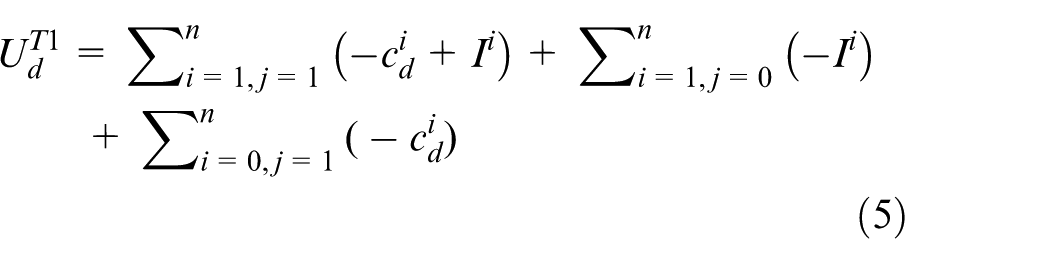
In the non-eavesdropped state, the defender can choose to defend or not. If the defender chooses to defend and the attacker chooses to eavesdrop on the channel, the defender’s payoff is the defense cost minus the penalty upon detection, that is,
Defender’s Payoff in the Eavesdropped State (equation (6)):
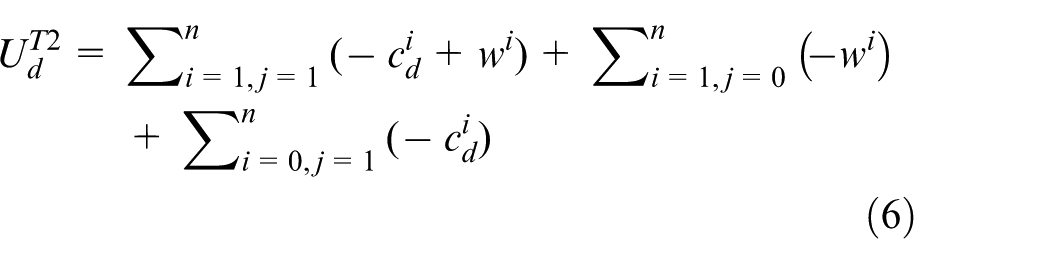
In the eavesdropped state, the defender can also choose to defend or not. If the defender chooses to defend and the attacker chooses to interfere with the signal, the defender’s payoff is the defense cost minus the penalty upon detection, that is,
Finally, the total utility function of the defender is obtained by weighting the payoffs in the non-eavesdropped and eavesdropped states according to the defender’s belief about the attacker’s behavior:
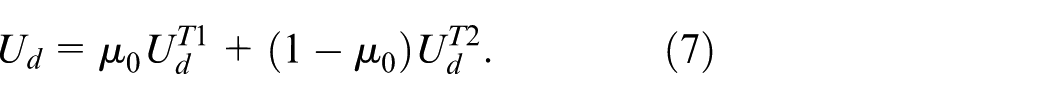
This equation integrates the defender’s payoffs in different states, considering the defender’s beliefs about the attacker’s behavior, to derive the defender’s total utility.
In equations (4) and (7),
Dynamic Bayesian game model
While the static game in Subsection 3.2 solves the strategy selection problem between defenders and attackers in a single stage, dynamic games more accurately reflect the evolution and adjustment of strategies in real-world attack-defense scenarios. Therefore, this section extends the single-stage game into a dynamic Bayesian game model to better describe defenders’ decision-making in multi-round games.
To better describe the decision-making process of the defender in multi-round games, we employ Bayesian statistical methods and the
In this model, the
Suitable for Describing Probability Distributions: The domain of the
Flexibility and Adjustability: The
Integration with Historical Data: By appropriately selecting values for
Conjugacy and Simplicity: The
This flexibility makes the
In each round of the game, the observed data of the attacker are used to update the posterior probability. The attacker’s behavior in each round is recorded using the definition (8)

The prior probability reflects the defender’s subjective judgment on whether the attacker will execute an attack in the current round. We will use a

Here,
We use Bayes’ theorem to construct the belief update formula for the defender (equation (10)):
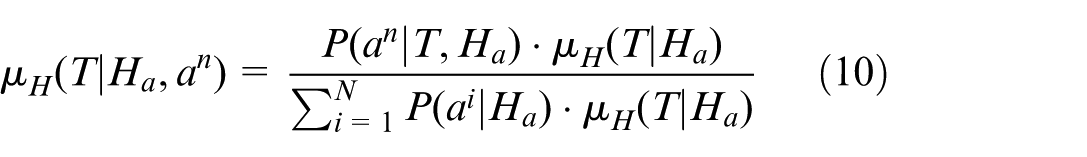
Here,
In equation (10), the defender updates their belief about the current game state based on the observed attacker behavior, combining prior knowledge with new information to make an updated assessment of the game state.
To intuitively illustrate the belief update process and the transition between game states, we present a flowchart in Figure 3. The flowchart shows how the game transitions from the Non-Eavesdropped state (T1) to the Eavesdropped state (T2) based on the attacker’s behavior, and how the defender dynamically updates its belief using the Beta distribution.
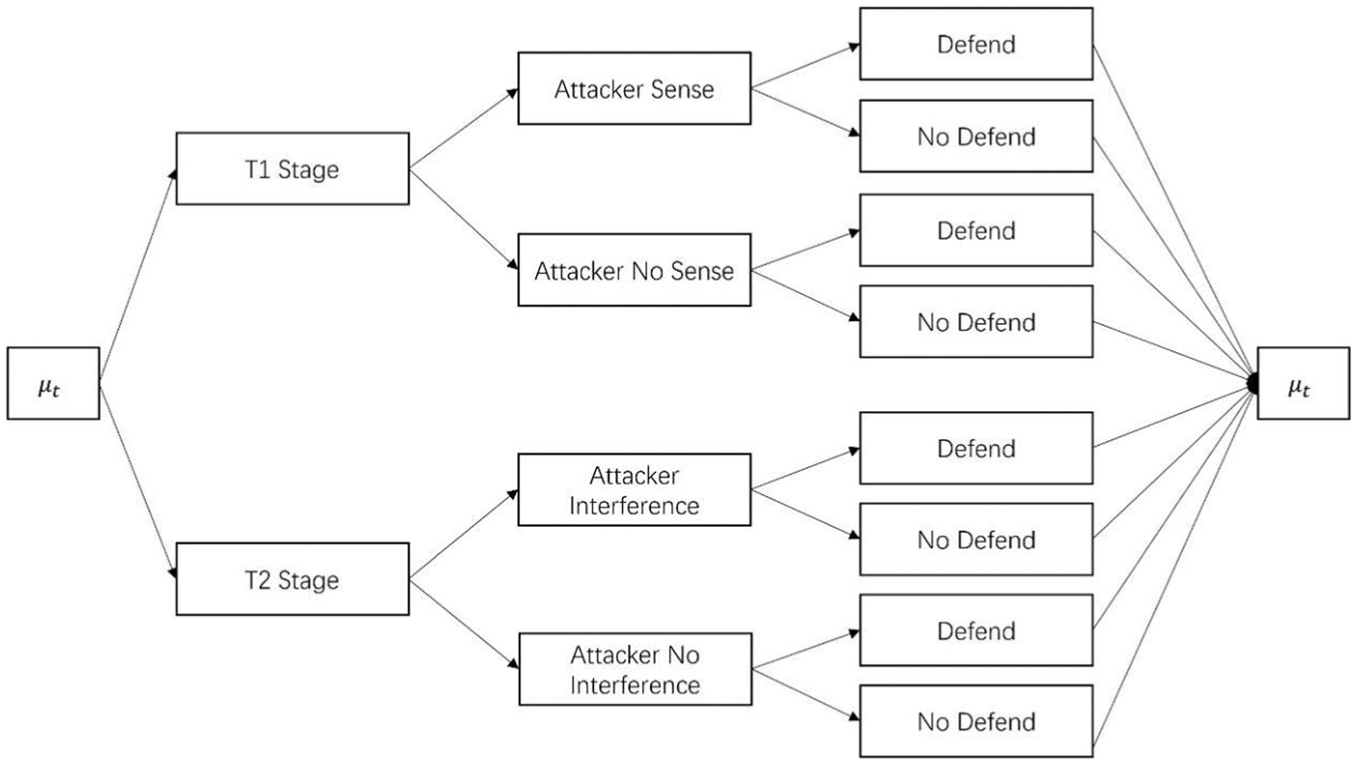
Dynamic Bayesian game tree for smart meter security.
Figure 3 illustrates the dynamic Bayesian game process between the attacker and the defender in a wireless smart meter environment. The game begins with the defender’s belief state
Nash equilibrium
This subsection will explore the important concept in game theory -the Nash equilibrium. First, the basic concept and definition of Nash equilibrium will be introduced. Then, the possibility of a pure strategy Nash equilibrium will be discussed in detail and analyzed accordingly. Next, the concept of mixed strategy Bayesian Nash equilibrium will be introduced, and the equilibrium point that may exist between the two parties in the game will be sought through mathematical derivation and analysis. Finally, the results will be explained and discussed to understand better the possible game behaviors in the smart meter system.
Pure strategy Nash equilibrium
Nash equilibrium is a stable state where no player can improve their payoff by unilaterally changing their strategy. In the smart meter system, the attacker aims to disrupt the meter via signal interference, and the defender aims to detect and penalize this interference. We look for a state where both players’ strategies are stable, meaning neither can improve their payoff by changing their strategy. There is no pure strategy Nash equilibrium in the two-stage wireless channel game model of the smart meter system. The complete derivation and explicit mathematical formulations are provided in Appendix 2.
Although pure strategy Nash equilibrium does not exist, there may still be mixed strategy Nash equilibrium, where participants mix different strategies with certain probabilities. The introduction of mixed strategies can alter the dynamics of the game and may lead to a state of equilibrium under certain probability distributions. Therefore, the next research direction is to find mixed strategy Bayesian Nash equilibrium by considering participants’ uncertainty about their opponents’ strategies, further deepening the understanding of game behaviors in smart meter systems, and proposing corresponding strategy designs and security defense measures.
Mixed strategy Bayesian Nash equilibrium
In the previous subsection, a clear pure strategy equilibrium point was not found in the simple Nash equilibrium analysis, which means that the attacker and the defender do not have only a single optimal strategy choice. Therefore, we turn to the mixed strategy Nash equilibrium. In this case, participants can choose different strategies with a certain probability, making it difficult for the opponent to adopt a clear advantage strategy. In the smart meter system, this mixed strategy equilibrium is more realistic because the behavior of participants is often affected by various factors, including uncertainty and the actions of the opponent. Therefore, the mixed strategy Nash equilibrium provides a more comprehensive analysis framework to help us better understand and predict the behavior patterns of participants, thereby guiding the formulation of system security and defense strategies. There exists a mixed strategy Bayesian Nash equilibrium in the two-stage wireless channel game model G of smart meter systems. The complete derivation and explicit mathematical formulations are provided in Appendix 3.
Attack and defense costs under different node capabilities
In Subsection 3.3, a Bayesian game model was constructed, and the stable solution of the smart meter system under Nash equilibrium was discussed in Subsection 3.4. However, it was found that the model did not take into account the ability differences between participants and the connections between participants and various types of meters, which may be important influencing factors in practical applications. Therefore, these factors will be further explored in Subsections 3.5–3.7. Specifically, the value assessment method of smart meters and the cost analysis of the attacker and defender under the difference in node capabilities will be focused on.
First, we analyze the value of smart meters, focusing on the power load and the connection between the meter and key equipment. In order to quantify the value of smart meters, we introduce the following calculation equation (11):
Here,
Cost analysis of attackers under node capability differences
In the cost analysis of attackers in smart meter systems, the attackers’ behavior patterns and their impact on the system are studied in depth. When conducting eavesdropping, attackers may be more focused on collecting information rather than launching attacks directly, so the capability differences between nodes are relatively small. Therefore, the model does not particularly emphasize the cost and utility in this scenario, but focuses on the game strategy of attackers when implementing signal interference attacks and the cost-benefit relationship between the two parties. By introducing the channel attenuation model and analyzing the energy consumption of signal interference attacks, the costs and benefits of attackers’ interference behaviors can be more accurately evaluated. In addition, by incorporating the attacker’s benefits under wireless channel modeling into the utility function of the game model, the differences in attacker attributes can be considered, so as to better understand the actual costs of the attackers. Next, we will study in depth how the channel attenuation model and energy consumption-related factors affect the attacker’s cost, and how to calculate the attacker’s benefits under wireless channel modeling. The signal attenuation model considers factors such as the distance between system nodes, and the calculation method of the signal strength of the wireless channel in the normal smart meter system is given based on the free path loss formula in the wireless channel. See Appendix 4. The calculation method of Signal Interference Attack Energy Consumption Analysis is shown in Appendix 5. The whole process and calculation of Attacker Profit under Wireless Channel Modeling shown in Appendix 6.
Defender’s cost analysis under node capability differences
In the environment of wireless channel interference, defenders face challenges that involve not only effectively detecting and preventing attacks but also managing the associated costs. This section provides a detailed analysis of the energy consumption of defenders in detecting interference attacks and the costs under different wireless channel conditions. By establishing energy consumption and cost models, we can gain a deeper understanding of the economic benefits of defense strategies, providing theoretical basis and practical guidance for devising more effective defense measures.
Energy consumption analysis of defenders in interference attack detection. Based on the analysis in the previous article, an energy consumption formula for interference attack detection is proposed. The calculation process is shown in Appendix 7. Comprehensive consideration can more comprehensively evaluate the overall energy consumption of defenders when facing interference attacks. This energy consumption analysis is crucial for designing effective interference attack defense strategies.
Defender benefits under wireless channel modeling. This model more comprehensively considers the various costs of defenders in the background of wireless channel interference. The overall calculation process is shown in Appendix 8, which provides a basis for further optimizing defense decisions.
Optimized response strategies for smart meter systems under wireless channel influence
In Section 3, a Bayesian game model of the smart meter system was constructed, and the stable solution under the Nash equilibrium was explored. However, in practical applications, the differences in the capabilities of the participants and their connections with the smart meters are crucial. Therefore, the system is further modeled in a wireless channel environment, and the impact of these factors on the attack and defense costs is analyzed. In this chapter, based on the previous model, we will explore in depth how to generate the optimal response strategy through optimization algorithms. First, the Hungarian algorithm is introduced, which optimizes the target selection of the attacker and the defender respectively by constructing a bipartite graph model and a weight matrix. Next, the dynamic update of the observation data and its application in the generation of the optimal strategy are analyzed. Finally, the optimal strategies of the attacker and the defender under different conditions are proposed and verified. This comprehensive strategy optimization process will provide effective theoretical support and practical guidance for the security protection of the smart meter system.
Bipartite graph construction
The Hungarian algorithm is a mature graph theory method that is widely used to solve the maximum weight matching problem. Its application in game theory models can more efficiently match participants and smart meters, thereby improving the overall performance of the system. Based on previous research, a Bayesian game model was developed that takes into account the differences in node capabilities. In each round of target selection, the traditional strategy of “more capability, more workload” may not be able to obtain the optimal strategy. Therefore, the Hungarian algorithm was introduced to optimize the strategies of the attacker and defender in each round of target device selection.
In the game model, two bipartite graphs: one for attackers and smart meters, and another for defenders and smart meters, as illustrated in Figure 4. In the bipartite graph of attackers and smart meters, attackers are represented as one set of nodes, while smart meters constitute the other set. An edge exists between an attacker and a smart meter if the attacker can target the smart meter. Similarly, in the bipartite graph of defenders and smart meters, defenders form one set of nodes and smart meters the other. An edge exists between a defender and a smart meter if the defender needs to protect the smart meter.
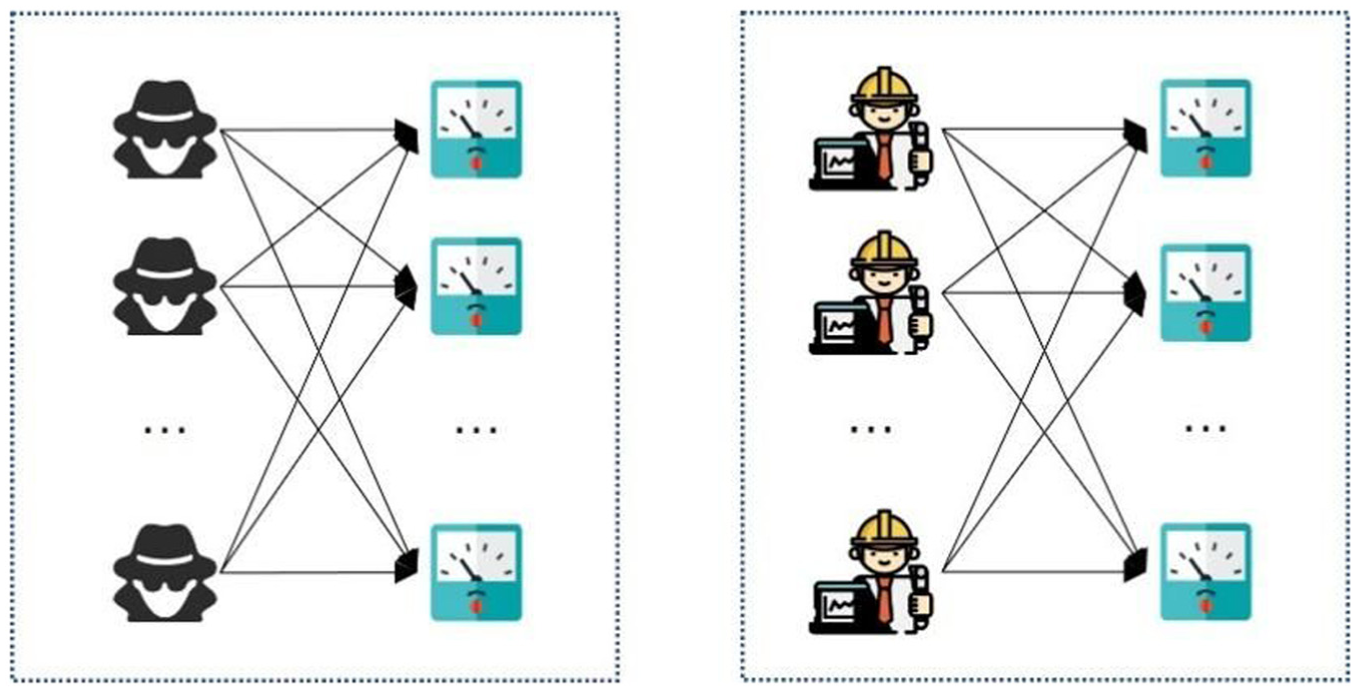
Bipartite graph model.
Applying the Hungarian algorithm facilitates optimal resource matching during the attack and defense process, thereby improving system efficiency and overall performance. By optimizing the matching between participants and smart meters, we can better address the challenges of attacks and defenses, achieving optimal results within the game model. This approach provides robust support for system coordination and optimization, ensuring the effective utilization of resources throughout the attack and defense process.
Edge weight design
Updating posterior probabilities with observed data
In each round of the game, the observed attack and defense behavior data are used to update the posterior probabilities. By defining
Specifically, the posterior probability
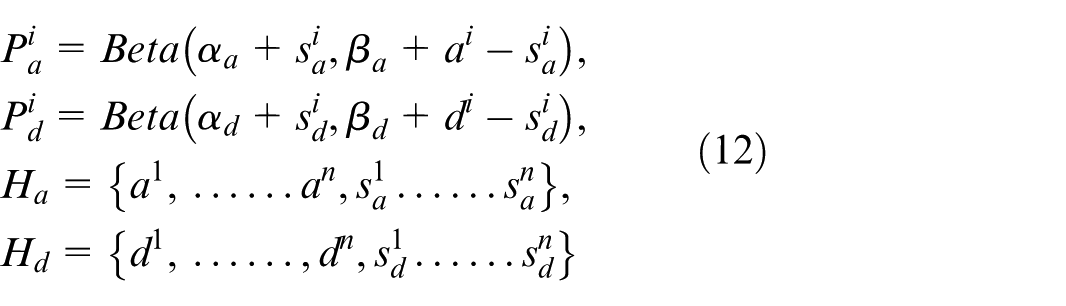
Here,
The advantage of dynamic updating is that it not only relies on static prior probabilities but also allows the probability distributions to be adjusted based on actual observed data, more accurately reflecting the capabilities of both attackers and defenders. This makes the model more adaptive and flexible, better capturing the changes in real-world scenarios.
Weight matrix
To achieve more effective matching, we introduce weight values, assigning weights to the edges between attackers and smart meters, as well as defenders and smart meters. This weight matrix more accurately reflects the preferences of participants in selecting target devices. The weight matrix considers the relationships between attackers and defenders and incorporates various factors from the game process.
In the weight matrix, each element
First, use equation (12) and Appendix 8 to derive the attack cost matrix
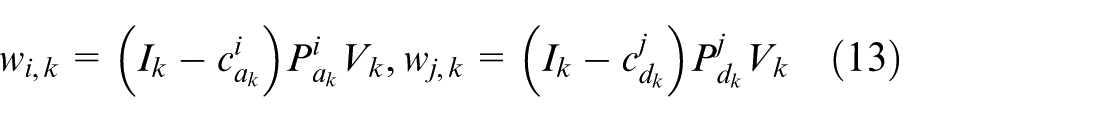
Equation (13) provide the methods for determining
Establishing this weight matrix provides effective input data for the subsequent application of the Hungarian algorithm, making the matching process more precise and better reflecting the strategic choices of the participants.
Multi-to-multi matching optimization
We have optimized the virtual node method in applying the Hungarian algorithm for multi-target attack scenarios. Traditional methods assign virtual nodes the maximum weight to prioritize actual nodes, but this approach fails to represent an attacker’s intentions when targeting multiple smart meters.
Our solution introduces multiple virtual attacker nodes for a single attacker, where each virtual node represents a distinct attack instance, allowing the attacker to target multiple meters simultaneously. If there are fewer attackers than smart meters, we replicate attacker nodes to match the number of smart meters. Similarly, defender nodes are also replicated to enable one defender to protect multiple meters.
The weight of the edges for virtual nodes is now calculated based on equation (13), ensuring accurate representation of attack and defense strategies in multi-target scenarios while preserving the bipartite structure required by the Hungarian algorithm. This optimization enables flexible many-to-many matching between attackers, defenders, and smart meters, improving resource allocation efficiency.
By enhancing the model’s flexibility and applicability, this optimization ensures the Hungarian algorithm performs well in multi-target matching, thus supporting the overall security and resource efficiency of the system.
Analysis of optimal strategies in the game
In this subsection, we will describe in detail the algorithmic process for determining the optimal strategies for both attackers and defenders, including their decision-making processes.
Obtaining attack and defense sequences
To reduce the size of matrix calculations and speed up computation, we propose setting a threshold
Using the Hungarian algorithm, we optimize the calculated weight matrix to obtain the optimal attack and defense sequences:
Here,
By setting the threshold
Generation of optimal strategies
For participants, the core of the optimal strategy is to select attack or defense sequences that achieve the maximum gain with the minimum cost. Our goal is to achieve this, and based on the previous analysis, we propose Algorithm 1 for determining the optimal strategies for attackers and defenders in each round of the game.
Wireless Smart Meter Channel Game Optimal Strategy
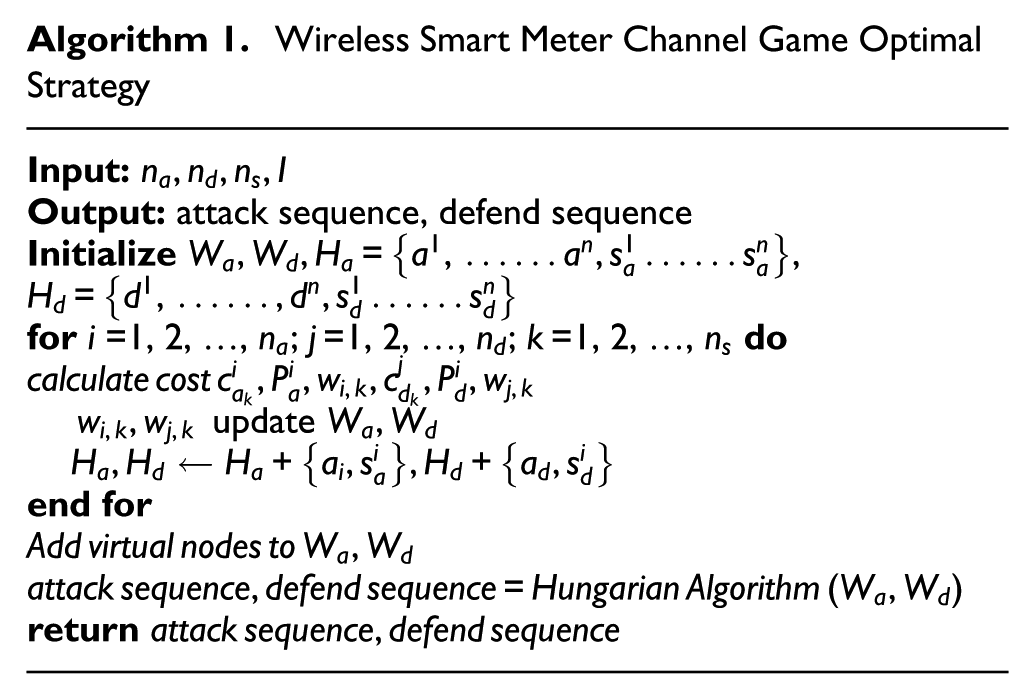
Figure 5 shows the flowchart of the optimal strategy generation algorithm. The specific algorithmic process is as follows: Firstly, input parameters for the current round of the game, including the number of participants and the number of smart meters. Then, iterate over attackers (or defenders) and smart meters to calculate the cost matrix and gain matrix. Based on this data, compute the posterior probability matrix. Using the cost matrix and posterior probability matrix, compute the weight matrix for attackers or defenders regarding smart meters. Inputting the obtained weight matrix into the Hungarian algorithm for optimization, ultimately yielding the optimal attack or defense sequence. This optimal sequence represents the best decisions made by both attackers and defenders in the current round, enhancing the overall efficiency and performance of the system.
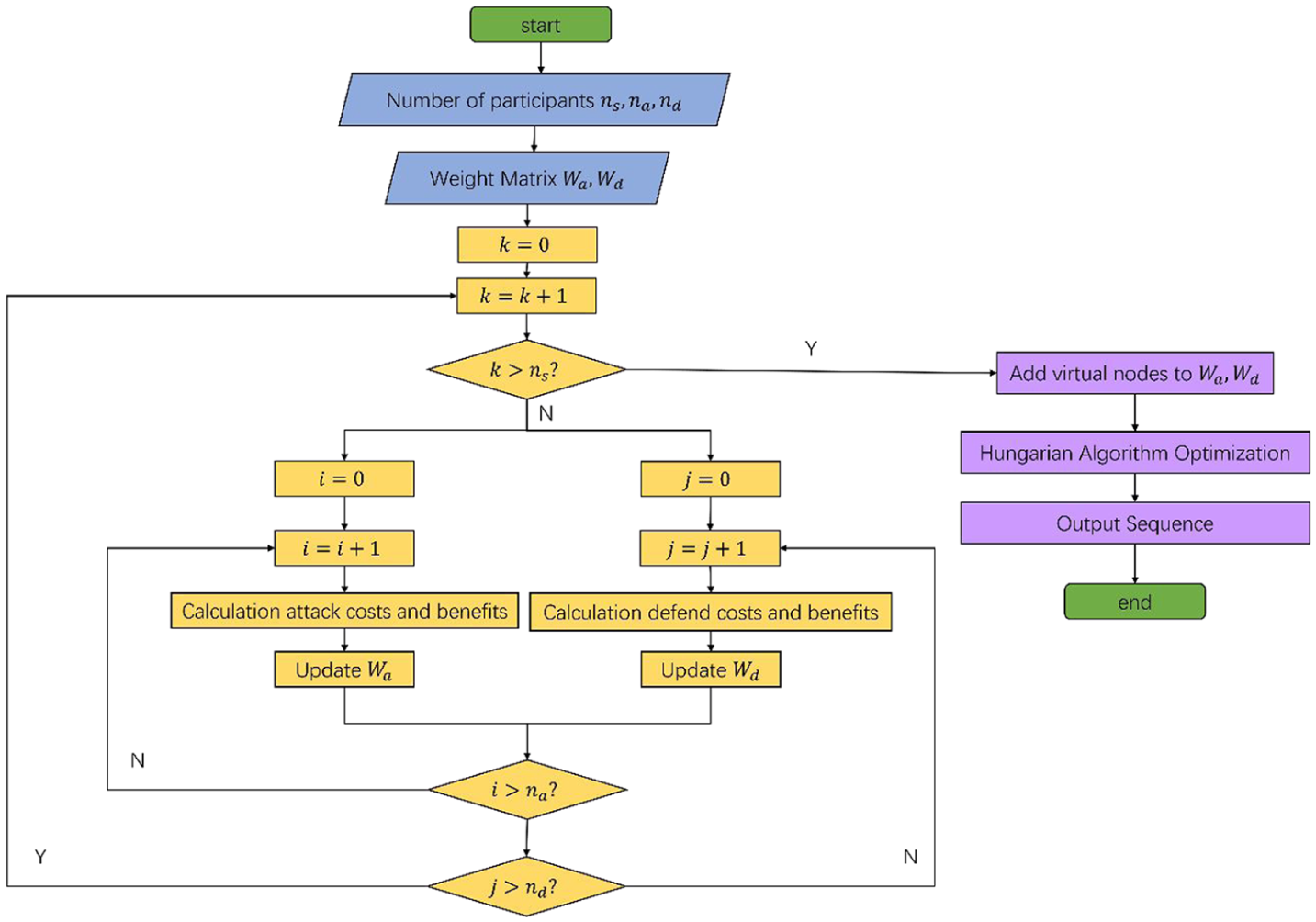
Wireless smart meter channel game optimal strategy flow chart.
Simulation experiments and comparative analysis
In this study, we simulate 2000 smart meters, representing a medium-sized community, with 300 attackers and 300 defenders for a balanced adversarial scenario. This setup considers defense resource limitations and computational complexity. We model node capability differences using uniform and Gaussian distributions to reflect realistic data fluctuations. Our parameter settings follow Chinese national standards (GB/T 19862-2005, DL/T 645-2007), ensuring technical, communication, and security protocols are met. These settings ensure the simulation’s validity and practical applicability.
Analysis of game results under Bayesian equilibrium
Analysis of defense success rate under different strategies
In the Bayesian game model, we set the strategies of both attackers and defenders to Bayesian equilibrium. We compared the defense success rate of this strategy with that of full defense and random defense strategies, as shown in Figure 6.
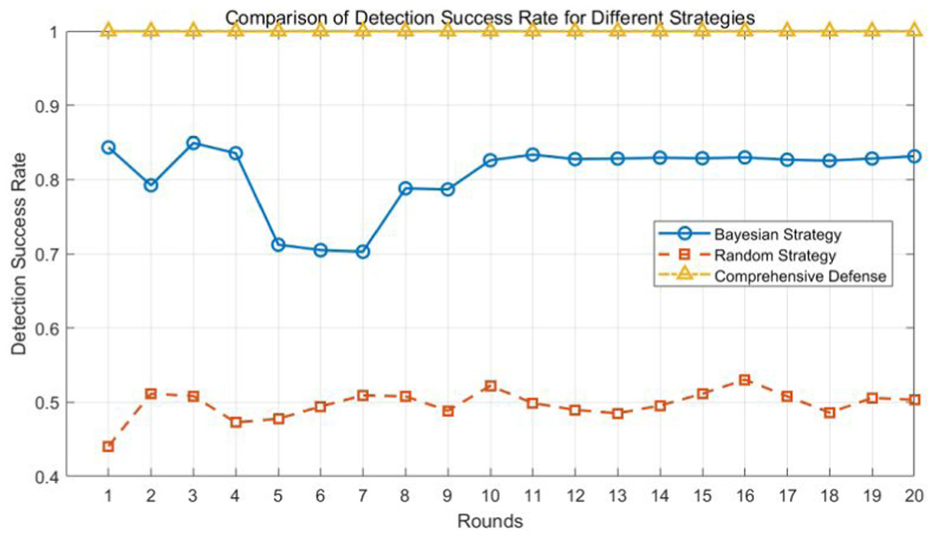
Comparison of defense success rates under different strategies.
Figure 6 presents the comparison of defense success rates under different defense strategies. Our proposed optimal strategy significantly outperforms the random defense strategy. In the long term, the defense success rate stabilizes at around 0.85. Specifically, in the initial stages, the defense success rate is higher as attackers have not fully understood the defense strategy. However, as the game progresses, attackers optimize their attack strategies, causing some fluctuation in the defense success rate, but it remains consistently high.
Analysis of defense costs under different strategies
We compared the defense costs under different strategies, as shown in Figure 7.
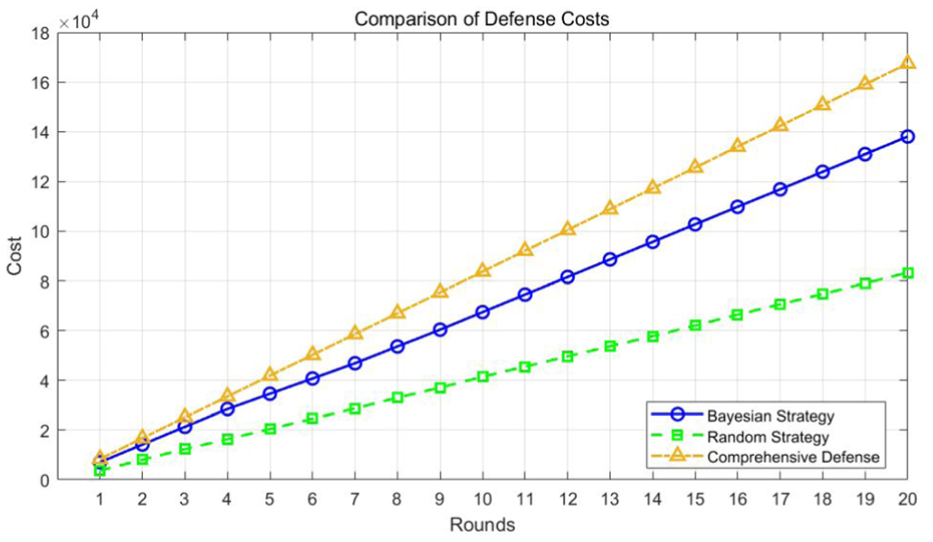
Comparison of defense costs under different strategies.
From the Figure 7, the defense cost required by our proposed strategy is significantly lower than that of the full defense strategy. In the early stages of the game, the cost of our strategy is like that of the random defense strategy. However, in the later stages of the game, due to the increasing number of targets attacked by the attackers, the cost of the Bayesian defense strategy becomes higher than that of the random defense strategy, but remains much lower than the cost of the full defense strategy.
Analysis of defense benefits under the same cost
Previous sections have analyzed the defense success rates and associated costs of different strategies. In practical applications, defense resources are typically limited, making the cost-effectiveness of defense strategies particularly important. To further highlight the superiority of the proposed algorithm, this study compares the benefits of various defense strategies under a fixed cost threshold, thereby demonstrating the differences in effectiveness of different defense methods with identical resource investments.
As illustrated in Figure 8, although the comprehensive defense strategy exhibits strong defensive capabilities, its high costs limit its application under a fixed cost constraint, resulting in defense success benefits that are significantly lower than those of the proposed strategy. In contrast, the random defense strategy, while incurring lower costs than the comprehensive strategy, suffers from the randomness and lack of targeting in its defensive approach, leading to defense success benefits that are also inferior to those of the proposed strategy.
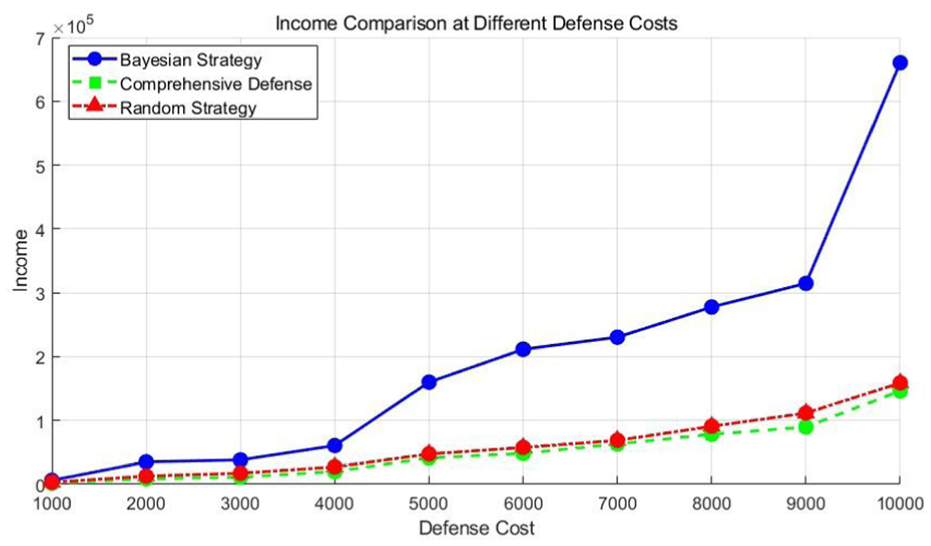
Comparison of the benefits of different strategies at the same cost.
In stark contrast, the Bayesian game strategy achieves considerably higher defense benefits under the same cost conditions. This is primarily because the Bayesian game strategy can dynamically adjust defense decisions based on real-time game information, thereby flexibly optimizing limited defense resources. This approach enhances the success rate of defenses without incurring additional costs.
In summary, under the same cost threshold, the Bayesian game strategy not only effectively increases the defense success rate but also maximizes resource utilization, providing higher defense benefits. These analytical results indicate that the Bayesian game strategy offers an efficient and cost-effective defense option in practical applications, especially in environments with limited defense resources.
The impact of confidence levels on defense success rate
Attackers need only obtain the meter information once to launch an attack. If the attacker successfully monitors in the T1 state, the game proceeds to the second phase, where subsequent attacks are signal interference attacks. This implies that most attacks occur during the T2 phase. Therefore, if the current calculated
We set
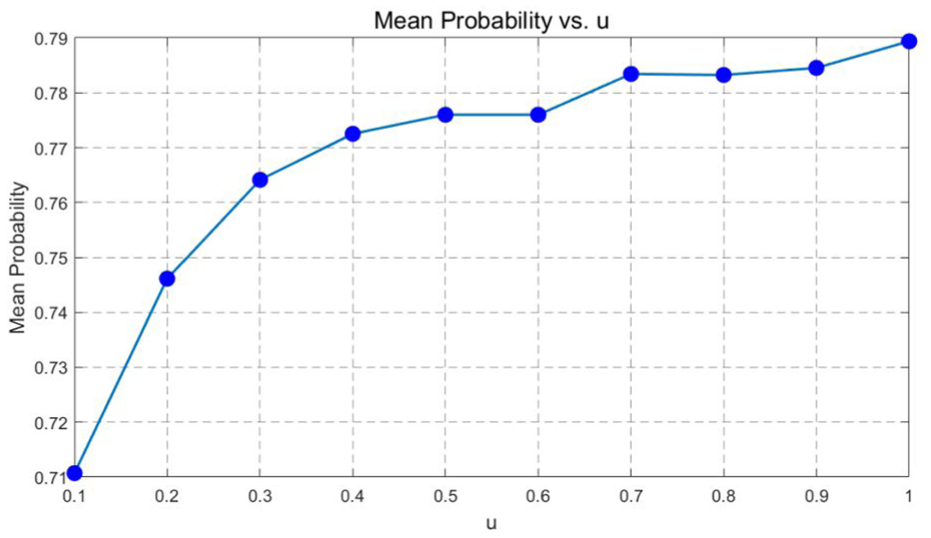
The impact of confidence on defense success rate.
Factors influencing optimal decision making under node ability discrepancy
Impact of interference source distance on power theft costs
In smart metering systems, the distance between the interference source and the electric meter is a crucial factor affecting the cost allocation for power attack. This influence can be studied by configuring different distance settings and interference intensities.
As shown in Figure 10, the authors categorized the distance between the interference source and the electricity meter into several levels and calculated the total cost incurred by the attacker during the game. The results show that as the distance increases, the attacker’s cost decreases. The reason is that for attackers, attacking a meter located farther away is more difficult and requires more resources and effort. Therefore, attackers typically avoid targeting meters that are farther away and tend to focus on meters that are closer, as the attack cost is lower for these meters. This analysis helps us understand that when selecting targets, attackers will exclude meters that are farther away due to the higher attack cost involved. As a result, overall, as the distance increases, the attacker’s cost decreases because meters located at a greater distance are excluded from the attack range.
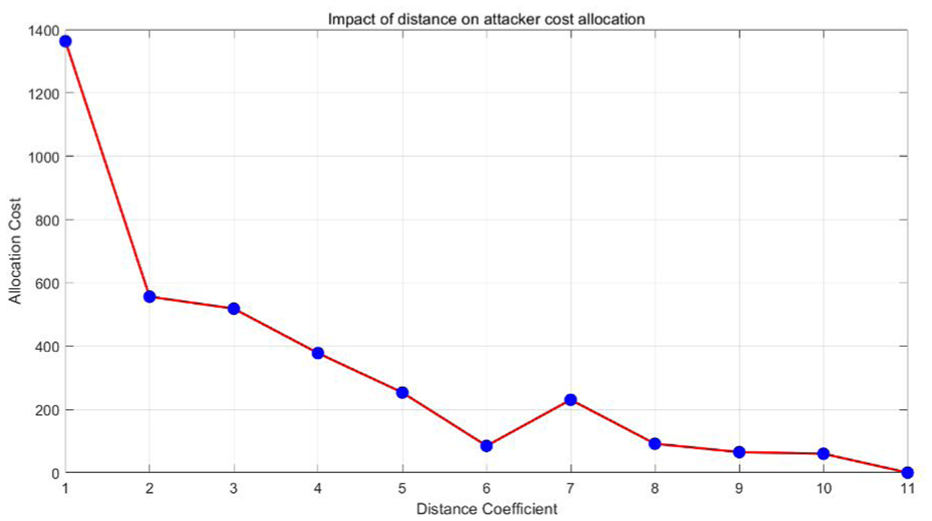
Influence of distance on attacker’s resource allocation.
Sensitivity analysis of node capability based on interference distance
To systematically analyze the influence of node capability differences on optimal resource allocation, we perform a sensitivity analysis by varying the distance between the attacker and smart meters. Specifically, we simulate a range of distances from 5 to 100 m, with increments of 5 m. Using Appendices 4 and 5, we compute the required interference signal strength and the corresponding attack cost at each distance.
As shown in Figure 11, the attack cost increases exponentially as the distance grows, reflecting the path loss characteristics of wireless channels. This trend significantly affects the attacker’s selection strategy. When the distance is short, the required interference power is low, making those meters more attractive targets. As distance increases, attack cost rises sharply, resulting in lower probabilities of selection in the matching process.
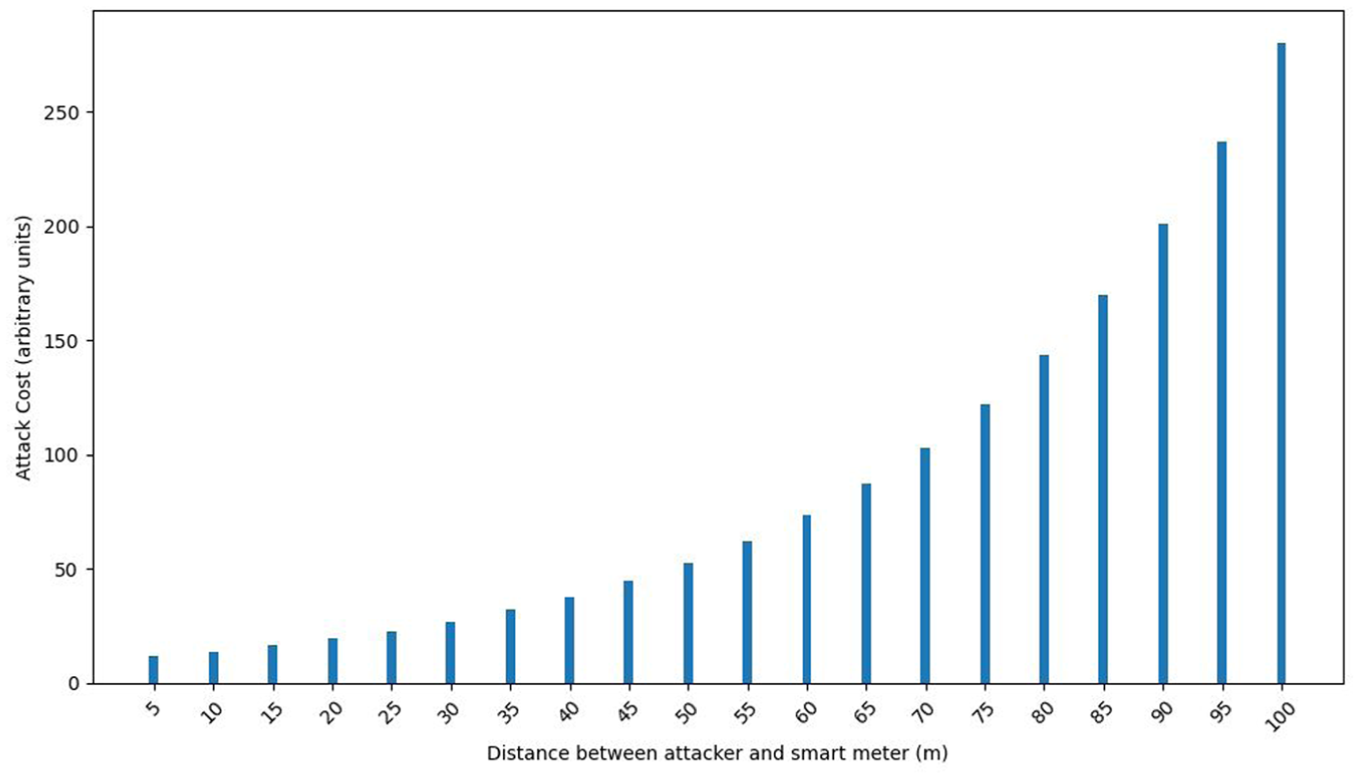
Impact of distance on attack cost.
This sensitivity analysis highlights that the spatial distribution of smart meters plays a critical role in the resource allocation of both attackers and defenders. It further demonstrates the importance of considering physical-layer constraints in designing adaptive security strategies for smart grid systems.
Impact of smart meter value on cost allocation for both parties
In Subsection 3.5, we calculated the value of smart meters using equation (11), which comprehensively considers the power load
As shown in Figure 12, the introduction of smart meter value significantly enhances the defense benefits. This improvement is primarily because, during the game-theoretic process, smart meters with higher value coefficients receive more defensive resources, thereby achieving greater benefits. Specifically, the high value of smart meters reflects their importance within the distribution network, prompting defenders to allocate more resources to these critical meters to ensure their security, thus increasing the overall defense benefits.
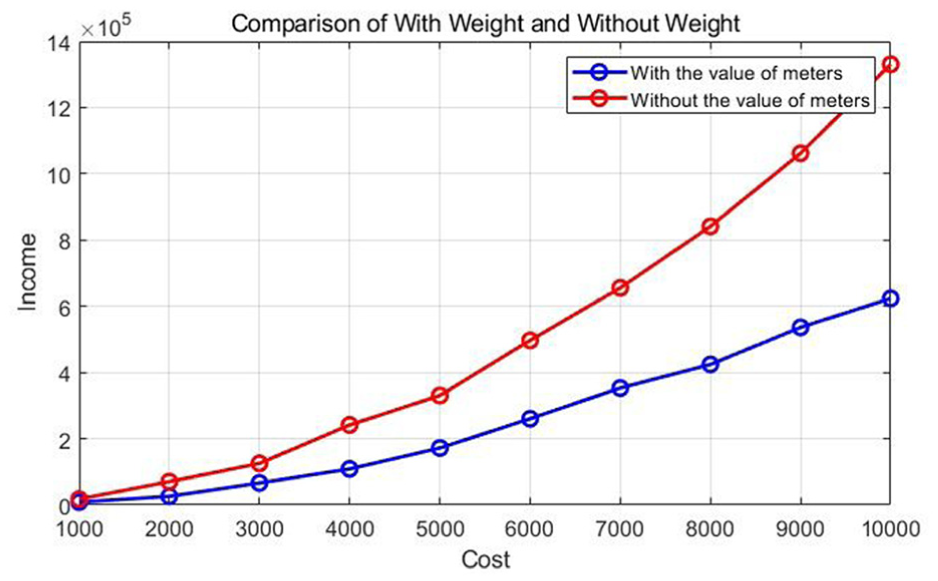
Impact of smart meter value on defense benefits.
To further investigate the influence of the smart meter value coefficient on the cost allocation for both attackers and defenders, we normalized the values of all smart meters. The authors divided them into five equal levels, designated as Level 1 through Level 5. This categorization allows for a comparative analysis of resource investment and cost allocation by both parties across different value levels.
Figure 13 illustrates how the smart meter value coefficient impacts the cost allocation between attackers and defenders. The experimental results show that as the smart meter value increases, the costs for both parties rise significantly. This indicates that high-value smart meters are more attractive targets, leading both attackers and defenders to focus their resources on these critical assets. On the other hand, smart meters with lower value levels receive less resource investment due to their reduced importance.
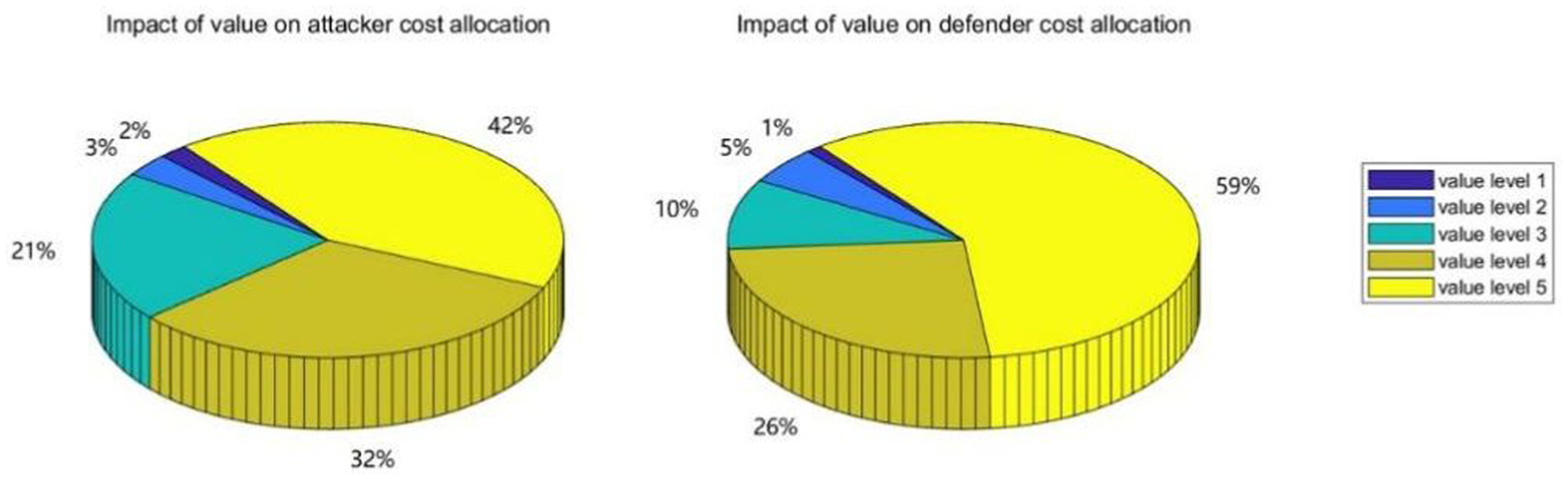
Impact of smart meter value on cost allocation for attackers and defenders.
These findings validate the model’s assumption that the value of smart meters plays a crucial role in regulating the attack-defense game. High-value smart meters become primary targets, influencing resource allocation and cost investment for both attackers and defenders.
By categorizing smart meters into five value levels and analyzing the cost allocations for each, we gain insights into how smart meter value affects strategies. This provides a foundation for more precise attack-defense strategies, optimized resource allocation, and enhanced security in distribution networks. Defenders can allocate resources based on the value levels of meters, while attackers can target high-value meters to maximize benefits and optimize their strategies under resource constraints.
Performance evaluation of Hungarian optimization strategy
Comparison of attacker strategy optimization effects
The authors compared the costs incurred and the pure profits obtained between the random attack strategy, Bayesian attack strategy, and our proposed optimal strategy in each round of the game process.
Figure 14 illustrates the costs borne by attackers in each round across the three strategies. The results show that the proposed strategy has the lowest per-round expenditure cost. Moreover, this strategy reduces the total expenditure cost by half compared to the other two strategies. Furthermore, the attacker’s net profit under different strategies is presented. The strategy optimized by the Hungarian algorithm demonstrates robust profitability, particularly in the latter stages of the game, significantly outperforming both random and traditional Bayesian game strategies.
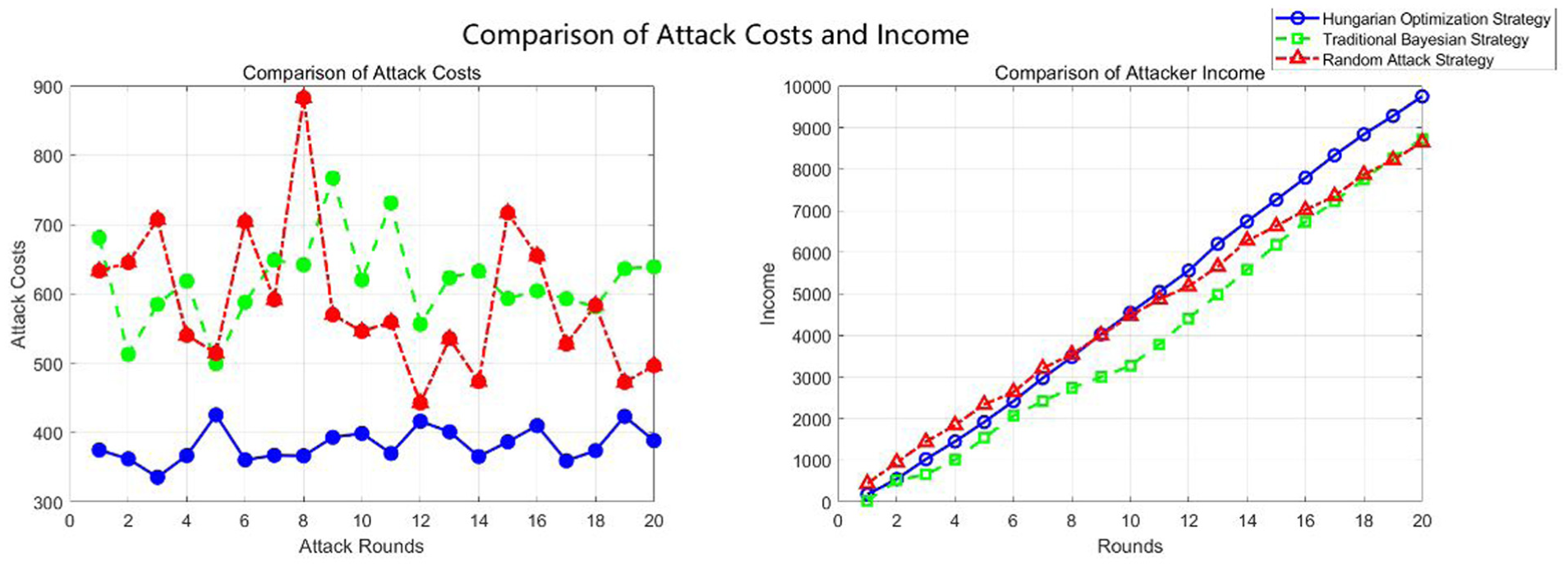
Comparison of attack costs and income for different strategies.
Comparison of defender strategy optimization effects
To compare the effects of defense strategy optimization, the author conducted experiments to compare the defense costs and pure profits of the random defense strategy, Bayesian defense strategy, and the defense strategy proposed in this paper.
In Figure 15, compares the attack costs and returns under different defense strategies. From a cost perspective, the author proposed optimal strategy significantly outperforms both random defense and mixed Bayesian Nash equilibrium strategies. Specifically, the author optimal strategy shows remarkable cost-effectiveness by substantially reducing the economic burden on attackers. Regarding returns, while initially the author strategy yielded slightly lower returns compared to random defense, it demonstrated a pronounced upward trend with increasing game rounds, surpassing the returns of random defense. This indicates the author optimal strategy’s ability to adapt dynamically to changes in the game, adjusting strategies promptly to achieve cost control and optimize returns simultaneously. In this way, the authors not only effectively mitigate attack costs but also ensure sustainable growth in long-term returns, showcasing the significant advantages of their strategy in applied game theory.
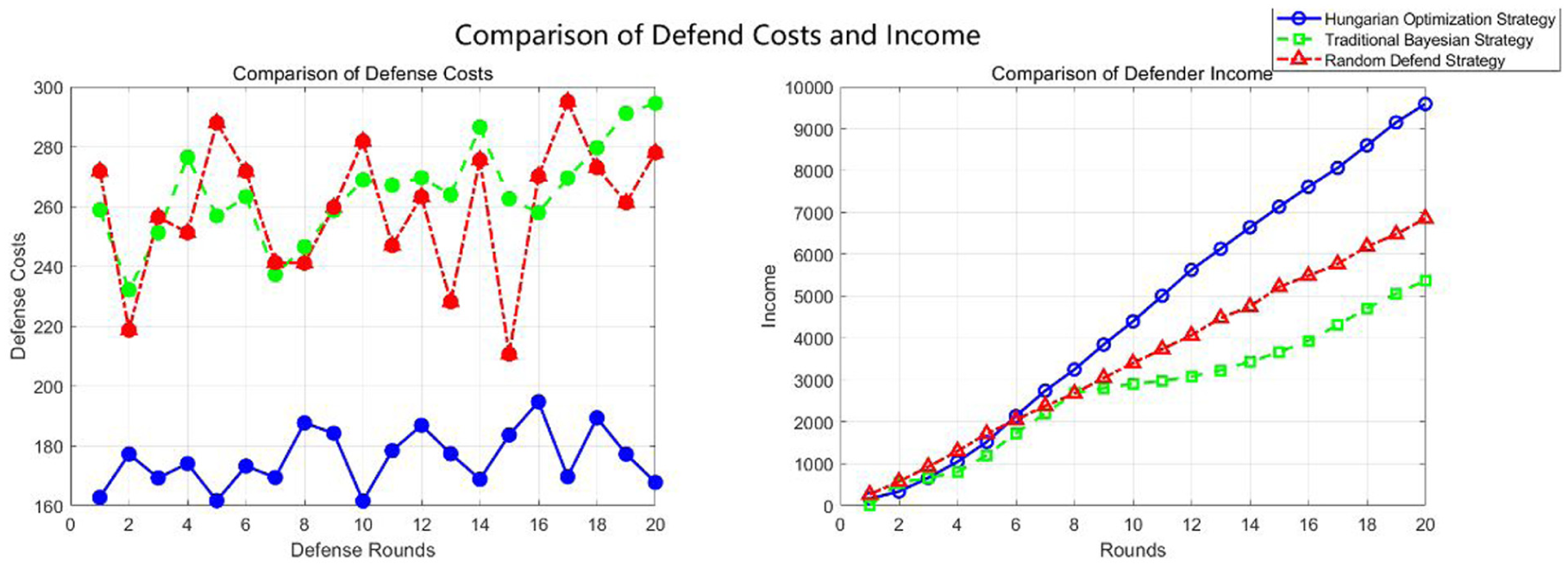
Comparison of defense costs for different strategies.
Comparison with popular defense methods
To further evaluate the effectiveness of our proposed scheme in resource-constrained environments, the authors design a comparative experiment against several popular defense strategies.
XGBoost 48 : A passive defense scheme based on anomaly detection, where the defender uses XGBoost and LSTM models to detect malicious traffic.
Agent-based IDS-IPS 49 : An adaptive defense scheme based on rule configuration, where the defender builds custom rule files and updates them periodically to achieve real-time detection and defense against abnormal behaviors.
Zero-Sum Game 50 : A defense scheme based on static zero-sum game theory, where the defender executes defense strategies according to the Nash equilibrium.
Full Defense 51 : A comprehensive defense scheme in which the defender performs anomaly detection and defense operations on all smart meter nodes in each round, achieving the highest defense coverage.
Under the same dataset and attack settings, the authors compare the defense cost and defense benefit in each round. The results are shown in Figures 15 and 16.
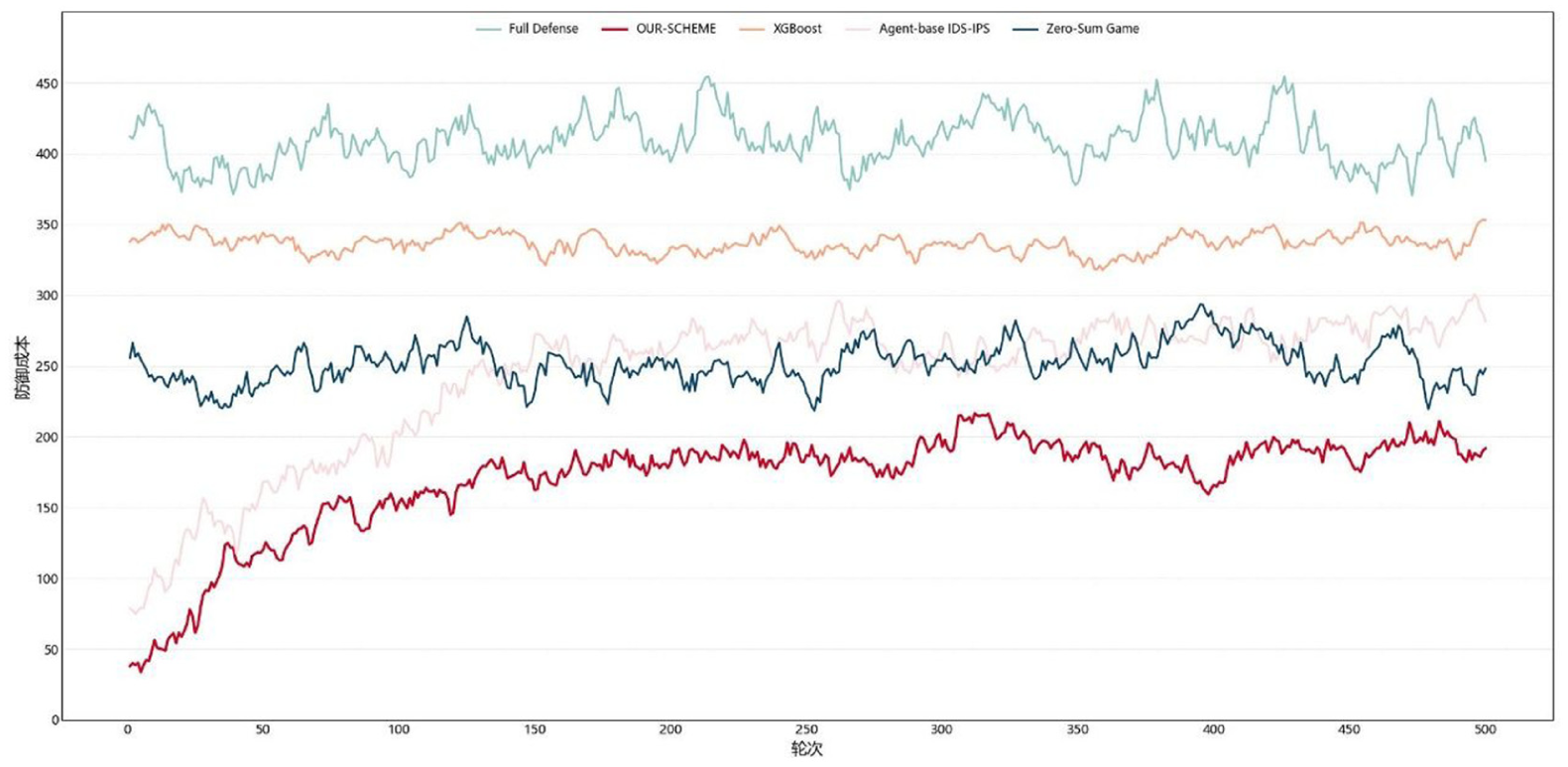
Cost comparison of different defense solutions.
As shown in Figure 16, XGBoost incurs relatively high defense costs (ranging from 323.25 to 356.14) due to its lack of adaptability and vulnerability to false positives. Although the Zero-Sum Game strategy incorporates cost into the Nash equilibrium calculation, it relies on static strategies and lacks dynamic adjustment capability. The Agent-based IDS-IPS scheme uses rule-based updates and starts with a low cost, but the cost gradually increases over time, reaching an average of 286.31. In contrast, the author proposed scheme maintains consistently low resource consumption throughout the entire game process (with an average cost below 232.53), thanks to belief updating and the optimization of resource allocation using the maximum weight matching algorithm.
In terms of defense benefit (Figure 17), XGBoost shows relatively low performance due to frequent misjudgments, with benefits ranging from 913.21 to 1227.75. The Zero-Sum Game offers slightly better results, but is still limited by its static strategy. Agent-based IDS-IPS demonstrates improved performance in the later stages, but still falls short of the ideal outcome achieved by Full Defense. The authors proposed scheme surpasses all comparison methods after round 45 and closely approaches the defense performance of Full Defense in later stages, ultimately reaching a total benefit of 3523.74.
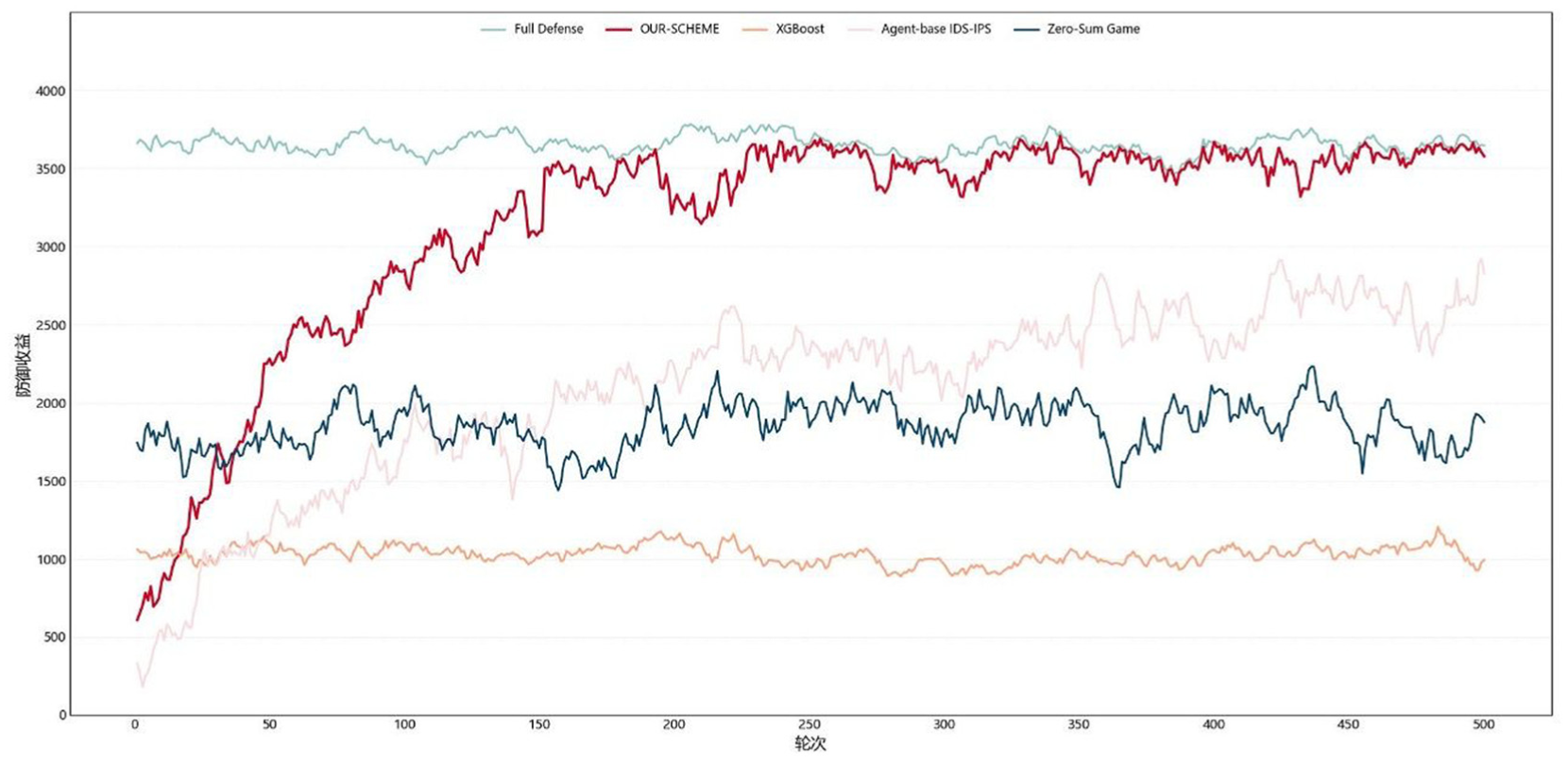
Comparison of benefits of different defense solutions.
In summary, under the context of complex attack behaviors and limited computational resources in smart grid environments, Bayesian game-based defense scheme achieves better performance than traditional data-driven methods. Data-driven approaches often rely on large-scale labeled datasets and static detection thresholds, making them less effective in data-scarce or dynamic scenarios. In contrast, the authors scheme requires no large-scale training, and can perform adaptive defense through belief updating and strategy optimization, ensuring both efficiency and interpretability while enhancing the system’s overall security.
Conclusion and future directions
Limitations
Despite the effectiveness of the proposed Bayesian game model and the Hungarian algorithm optimization in enhancing smart meter system security, several limitations remain:
Adaptive Attacks Not Modeled: The current model assumes static or probabilistic attacker behavior characterized by the Beta distribution. However, in real-world scenarios, attackers may adopt adaptive jamming strategies that evolve based on past outcomes. These dynamic patterns are not fully captured by the current belief update mechanism.
Simplified Network Topology: This study assumes a direct mapping between attackers, defenders, and smart meters. Complex network structures involving multi-hop communication, cooperative attacks, or clustered defenses are not considered, which may affect the model’s generalizability.
Measurement and Estimation Errors: The accuracy of the defender’s strategy relies on precise observations of signal strength, packet loss, and other features. In practical deployments, sensor noise or measurement errors may impact decision-making and belief updates.
Assumed Independence Between Nodes: The model currently treats smart meters as independent targets. In practice, correlation may exist between meters (e.g. geographic proximity or shared infrastructure), which could influence optimal resource allocation strategies.
These limitations suggest opportunities for future research, such as incorporating adaptive learning techniques (e.g. reinforcement learning), modeling richer network interactions, and introducing robust estimation methods under uncertainty.
Future work
This paper proposes a dynamic game theory-based attack-defense model for smart meters to address current protection shortcomings. The main contributions include dynamically modeling the capabilities of attackers and defenders using Bayesian game methods and achieving optimal attack-defense target matching through the Hungarian algorithm. Based on this model, we designed an optimal strategy algorithm to maximize cost-effectiveness and pure profit by optimizing the decisions of attackers and defenders. Simulation experiments validate the effectiveness of the model, showing that the proposed algorithm effectively reduces attack costs and increases overall pure profits.
Future work could focus on the following aspects:
1. Consider the impact of channel uncertainty and communication environment fluctuations on model robustness
This study assumes that wireless channel interference can be modeled and predicted to a certain extent, but in actual scenarios, complex communication environment factors such as channel fading, shielding effects, and non-Gaussian interference may cause model performance to degrade. Therefore, in the future, robust optimization or deep reinforcement learning methods can be introduced to improve robustness and generalization capabilities under uncertain conditions.
2. Expand application to wireless security protection in other key infrastructure fields
Although this study takes smart meters as the starting point, the dynamic Bayesian game model constructed has strong versatility and can be extended to key infrastructures such as electric vehicle charging piles and power Internet of Things devices that also rely on wireless communications in the future to build a unified game-driven security protection framework.
3. Expand the defense resource constraint model to be close to the actual deployment constraints
This paper adopts a one-to-one match between defense resources “node-protection measures” and does not consider multi-dimensional resource constraints such as deployment cost, communication delay, computing resources, and real-time constraints. In the future, multi-objective constraints can be introduced into the optimization model to form a multi-objective combination optimization model or a resource allocation strategy for task scheduling to improve the feasibility of real deployment.
Footnotes
Appendix 2
Appendix 3
Appendix 4
Appendix 5
Appendix 6
Appendix 7
Appendix 8
Appendix 1.
This appendix provides a complete list of parameters used in this article. These definitions can be used as a reference to interpret the meaning of the formulas in this article.

| The cost incurred by the attacker for wireless channel eavesdropping | |
| The value of the information obtained when eavesdropping goes undetected | |
| The defense cost for the defender | |
| The penalty imposed on the attacker upon successful Defense | |
| The cost incurred by the attacker for executing signal interference | |
| The value of the target smart meter | |
| Each participant’s belief or probability distribution regarding the actions of other participants | |
| The defender’s prior belief regarding the game being in Stage T1 | |
| The posterior probability that the defender believes the current game type is T after observing the attacker’s behavior | |
| The probability of the attacker acting given the game type T and the observed historical behavior | |
| The sum of all possible attacker behaviors weighted by their probabilities and the prior probability | |
| . | The impact of the power load borne by the smart meter on its value |
| The weighting coefficient of the power load | |
| The power load borne by the smart meter | |
| Weighting coefficient of the connectivity of key devices | |
| e connectivity between the smart meter and key devices. | |
| The total value of the smart meter | |
| The transmission power | |
| The path loss at the reference distance | |
| The path loss exponent | |
| The distance between the transmitter and receiver | |
| The gains of the transmitter | |
| The gains of the receiver antennas | |
| White Gaussian noise with mean and variance | |
| The signal sent by the malicious interference source, following a normal distribution with mean and variance | |
| The signal strength, antenna gain, distance between the signal transmitter and the smart meter for normal signals | |
| The signal strength, antenna gain, distance between the interference source and the smart meter for the malicious interference signal | |
| The signal strength that the interference source needs to emit | |
| The time for executing the interference attack | |
| The frequency of sending interference signals | |
| The basic energy consumption of the interference source device per unit time | |
| The duration of the device’s continuous operation. | |
| The cost that the attacker needs to pay to attack the smart meter | |
| The interference signal strength required if the attacker wants to launch an attack on the meter | |
| The duration and sending frequency of the interference signal | |
| The unit time basic energy consumption and operation time of the interference source | |
| The energy consumption per unit time for signal strength detection | |
| The energy consumption per unit time for carrier sensing | |
| The energy consumption per unit time for packet loss analysis | |
| The energy consumption per unit time for spectrum analysis. | |
| The basic energy consumption per unit time for device operation | |
| The cost that the defender needs to bear for defending the smart meter | |
| The energy consumption per unit time for signal strength, carrier sensing, packet loss rate, and spectrum analysis measurement by the defender | |
| The basic energy consumption per unit time and running time of the device | |
| Record the number of attempts and successes of attack and defense actions in each round | |
| The posterior probability for attackers | |
| The posterior probability for defenders | |
| The parameters of the prior distributions | |
| Represent the attack and defense actions and their success counts for the smart meter. | |
| The weight of attacker attacking smart meter | |
| The weight of defender defending smart meter | |
| The attack cost matrix | |
| The defense cost matrix | |
| The posterior probability matrices of successful attacks | |
| The posterior probability matrices of successful defenses | |
| The value of the smart meter | |
| The cost incurred by the attacker in attacking the smart meter | |
| The posterior probability of a successful attack by the attacker on the smart meter. | |
| The actions of the participant towards the smart meter |
Consent for Publication
The corresponding author gave consent for the publication of the identifiable details.
Consent to participate
There is no such case.
Ethical considerations
All patients provided written informed consent.
Informed consent/patient consent
All authors provide informed consent.
Author contributions
Yiming Zhao: Writing- Original Draft, Conceptualization. Yulong Zhao: Methodology, Funding acquisition. Changsheng Wan: Writing- Review & Editing. Dong Du: Writing- Review & Editing, Supervision.
Funding
The authors received no financial support for the research, authorship, and/or publication of this article.
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Trial registration number/date
November 2024.
Data availability statement
Data available on request from the authors.
