Abstract
This work proposes the problem of observer-based secure control for discrete-time singular systems subject to denial-of-service (DoS) attacks. The non-periodic DoS attacks that destroy the system’s performance are considered. To estimate the states and deal with the effects of DoS attacks, a new switched observer-based control method is established, which models the closed-loop system as a switched system. Firstly, some sufficient criteria for guaranteeing the exponential admissibility with
Introduction
In practice, many systems can be modeled by differential or algebraic equations. However, some systems, such as economic systems, biological systems and robotics systems,
1
need to be modeled by the above two equations. To study those systems, singular systems have been proposed by scholars. For those systems, the study of singular systems is more difficult because the stability problem is considered, while the regularity and the non-impulsiveness (for continuous systems) or the causality (for discrete systems) are discussed. Over the past few decades, singular systems have received attention due to their extensive applications and many results about singular systems have been reported, such as saturation control,2,3 stability analysis,4,5 security control
6
and sliding mode control (SMC).7–9 The analysis and design issue
2
was studied for singular systems under saturated feedback, where the largest invariant ellipsoid was given by solving optimization problem. The robust
A large amount of existing literature is based on the assumption that the states of the system are fully available. However, this assumption is very difficult to satisfy in practice because of limited control techniques. To conquer this issue, the methods to achieve the stability of the system through the output information of the system are proposed. The methods contain dynamic output feedback (DOF) control,10,11 observer-based output feedback (OBOF) control12–14 and static output feedback (SOF) control.15,16 The DOF control design issue
10
was discussed for singular hybrid systems under input saturation, where the transition rates are partly unknown. Nagamani et al.
14
studied the issue of observer-based SMC for nonlinear systems, where an event-triggered method was adopted to save the network resources. The SOF control problem
15
was proposed for semi-MJSs, where a novel multivariate Lyapunov function was established to discuss the stability of the system. However, the above papers required that the output matrix
Due to the shared nature of communication networks, the transmitted data is vulnerable to hacker attacks. At present, the deception attacks and the DoS attacks are two common categories of network attacks. For the former, it mainly changes the authenticity of the data by injecting false data into it, thereby affecting the judgment of the control center. Moreover, it is difficult to detect because the pattern and time of the attacks are designed by the attackers. For the latter, it mainly cuts off the data transmission, thereby causing system instability. Compared with the deception attacks, the DoS attacks can destroy the system performance without the transmitted information, which is the reason that the DoS attacks receive special attention. To alleviate the impact of the cyber attacks on control systems, many security control methods have been proposed.17–25 The consensus tracking control issue 26 was presented for multiagent systems with deception attacks, where a hierarchical algorithm was established to decompose the multi-agent consensus tracking problem into a single-agent tracking problem. Wang et al. 20 concentrated on the issue of filter design for SMJSs, where a stochastic variable was adopted to describe whether DoS attacks occur. The asynchronous security tolerant control problem 22 was considered for MJSS, where deception attack and DoS attack were cogitated simultaneously. In Zhu et al., 23 Zhang et al., 24 and Zeng et al., 25 the secure control problem was discussed for singular systems subject to DoS attacks. From the existing works, most papers considered the secure control problem for continuous singular systems, few papers discussed the secure control problem for discrete-time singular systems subject to DoS attacks, so the observer-based secure control problem remains a challenge for discrete-time singular systems with nonperiodic DoS attacks.
Summarizing the above discussions, the secure control problem is discussed for discrete-time singular systems by observer control method in this work. The main contributions of this work can be summarized as follows:
Unlike the existing result in Wang et al., 20 modeling DoS attacks with a random variable, the non-periodic DoS attacks that make the communication network unreliable are considered in this paper.
Some conditions for the exponential admissibility with
This work is arranged as follows. In Section II, the preliminaries are introduced. In Section III, the main results are presented. Section IV demonstrates the methodology through two examples. Conclusions are given in Section V.
Problem formulation
Consider the following discrete-time singular systems
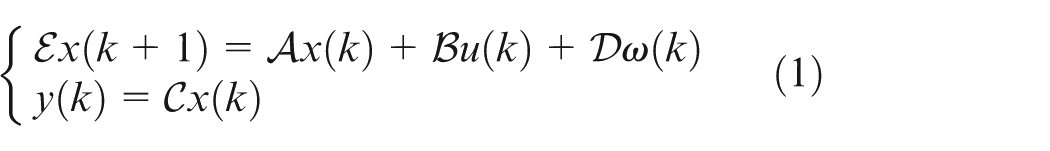
where
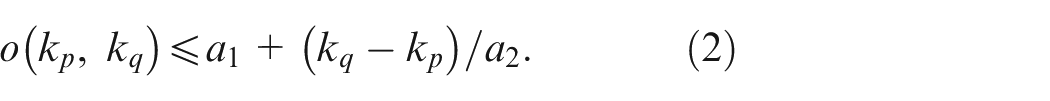
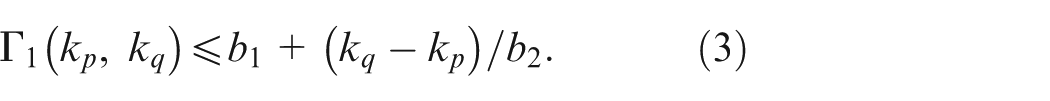
In practice, the transmitted signals are often inevitably attacked because the network transmission channels are open to the public. In this paper, the aperiodic DoS attacks are considered and occur on the sensor-to-observer channel. Assume that
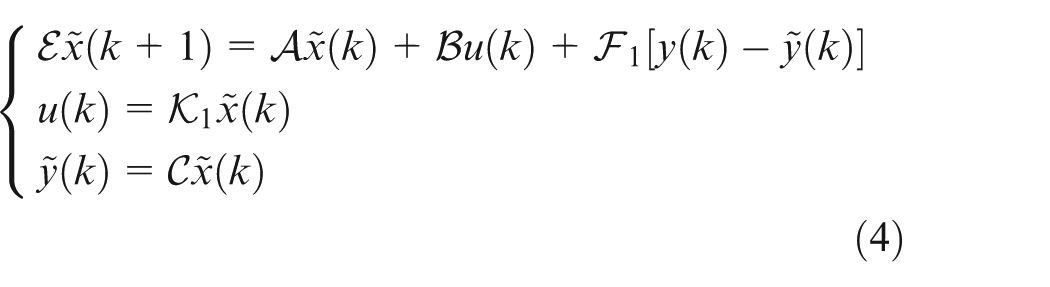
In this paper, in order to estimate the system states, the following observer is established:
for
for
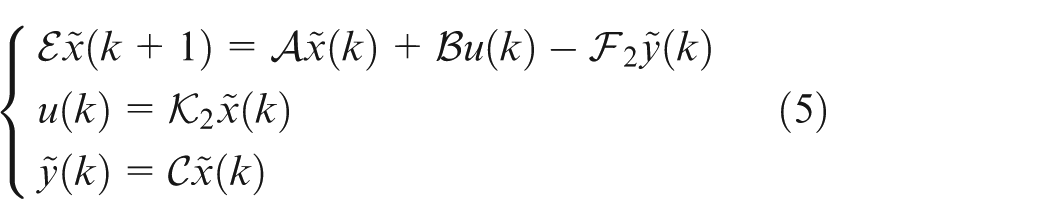
where
Define
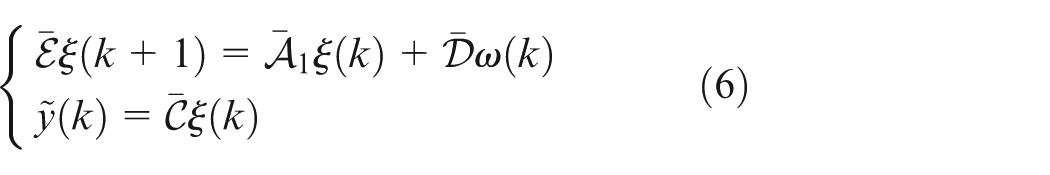
where
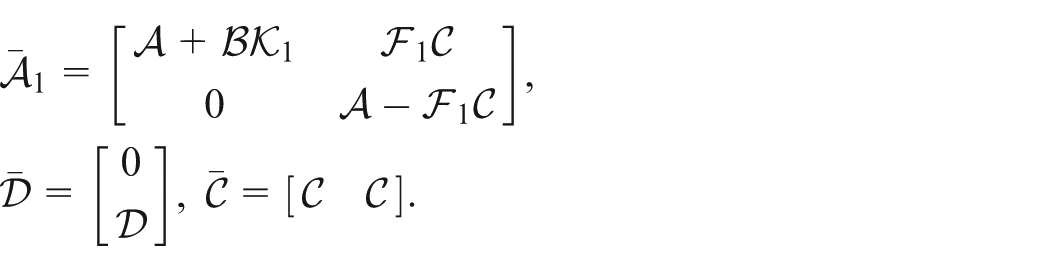
for
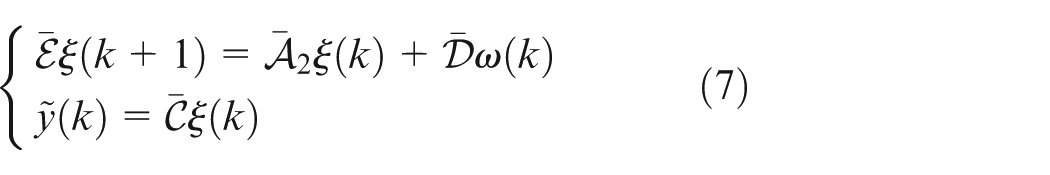
where
then

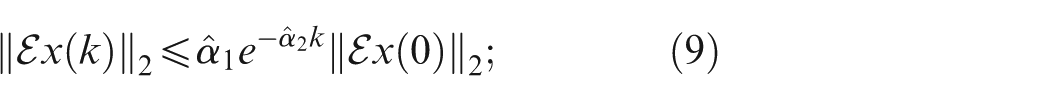
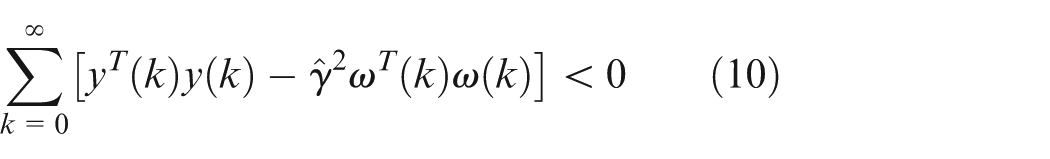
The main objectives of our work are as follows:
(1) the systems (6) and (7) are EA;
(2) under zero initial condition and
where
Main results
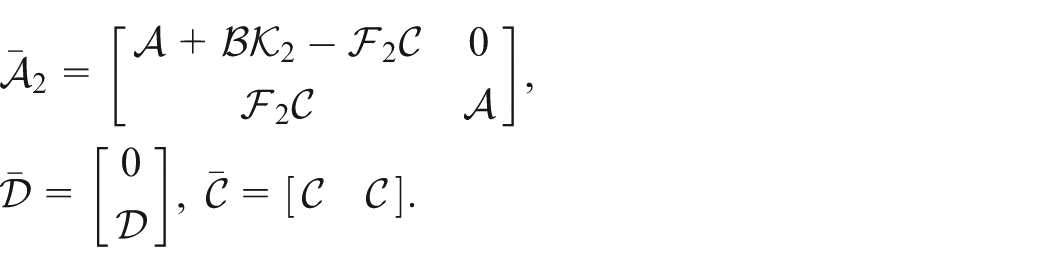
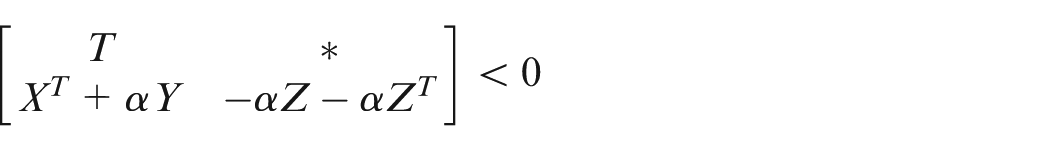
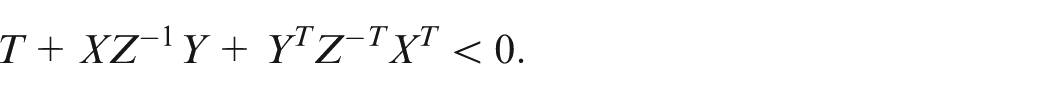
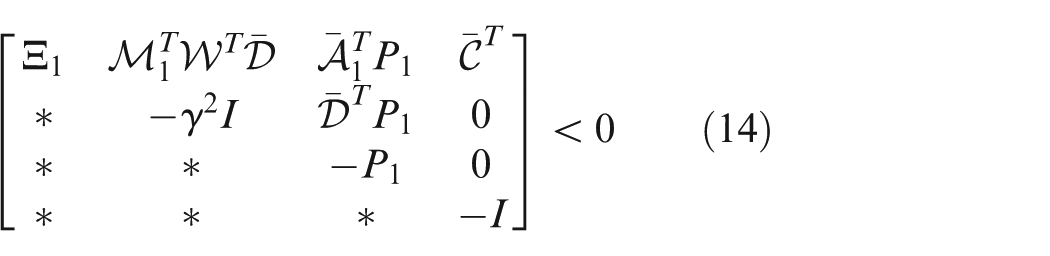
In this section, some sufficient conditions are derived to make sure that the systems (6) and (7) are EA with


where
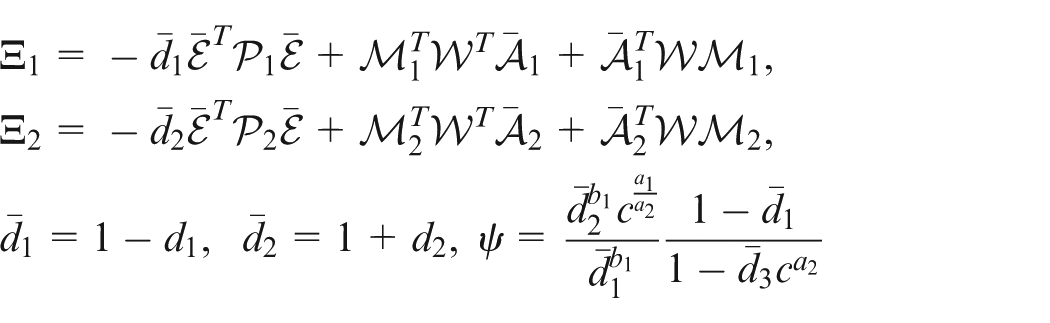
and
Because of rank
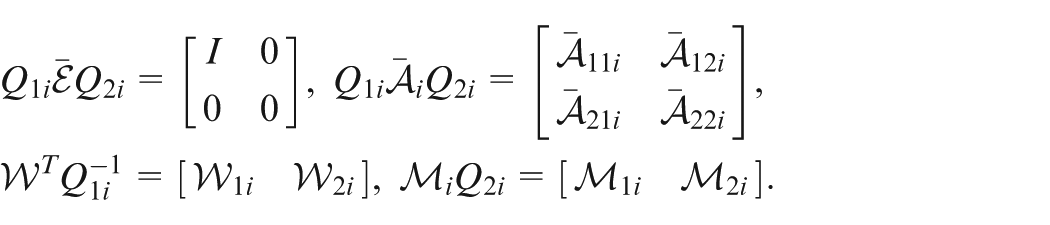
It can be seen from
For
From (14), one has
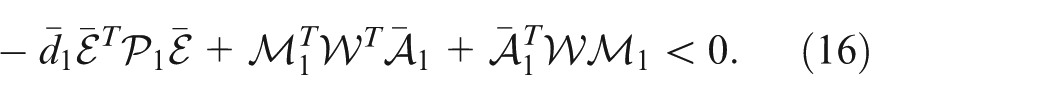
Then, (16) pre- and post-multiplying
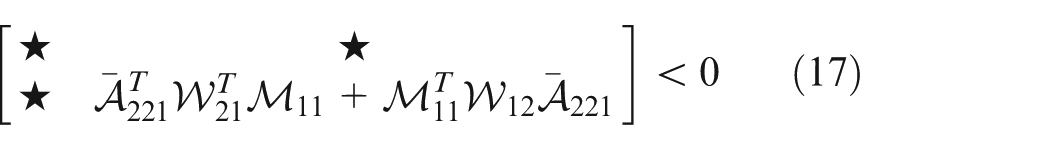
which implies that
For
For

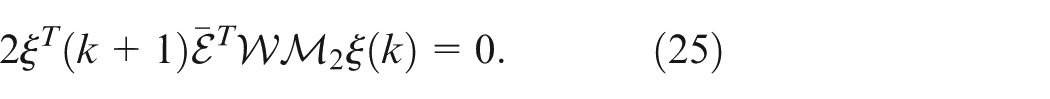
Define
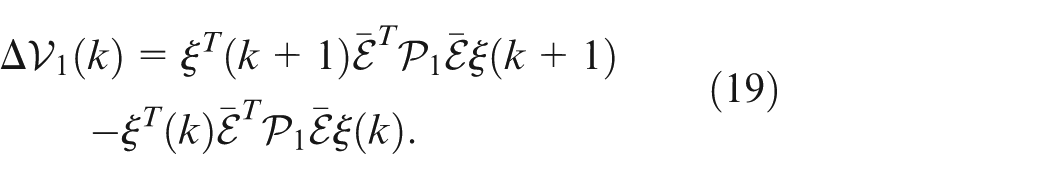
Since
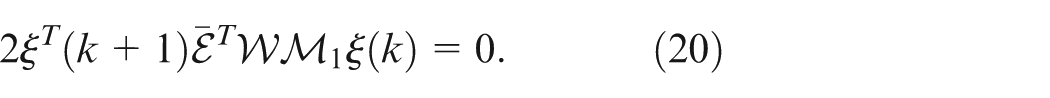
Considering
where
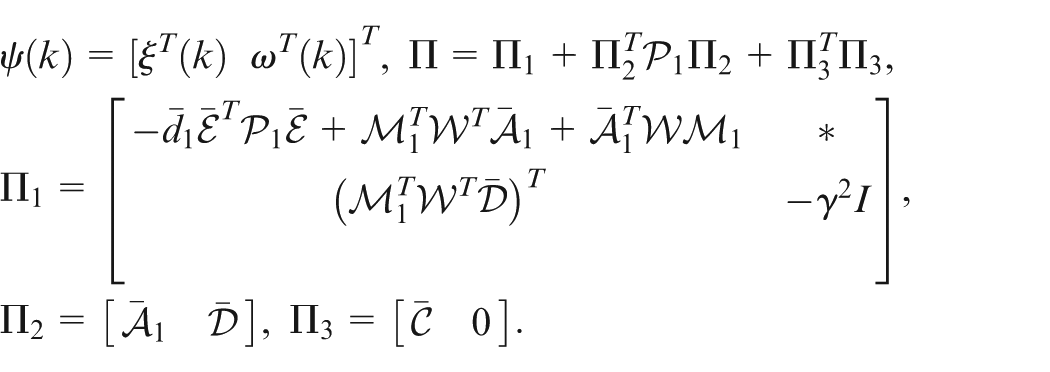
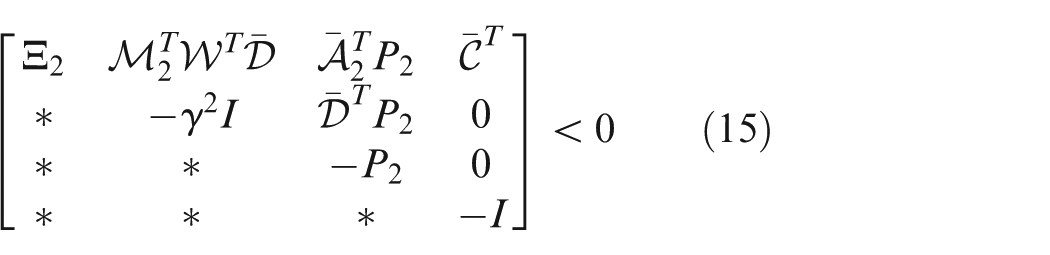
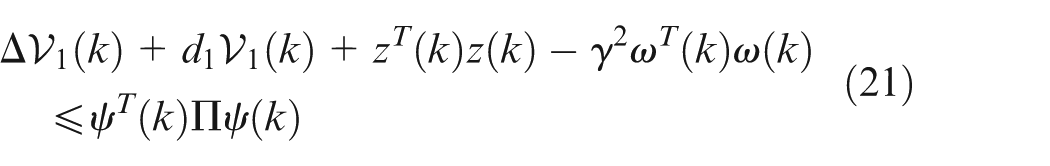
By Schur complement and (14), one has
For

Similar to (18), one can obtain
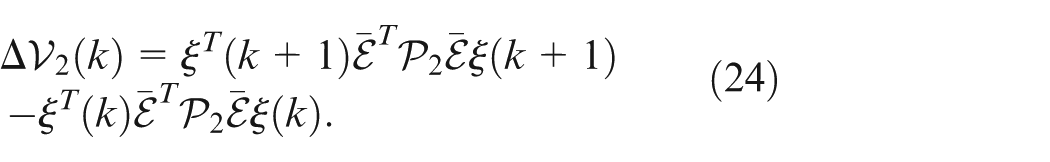
Since
Considering
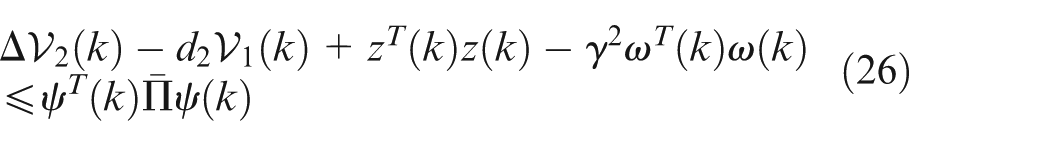
where
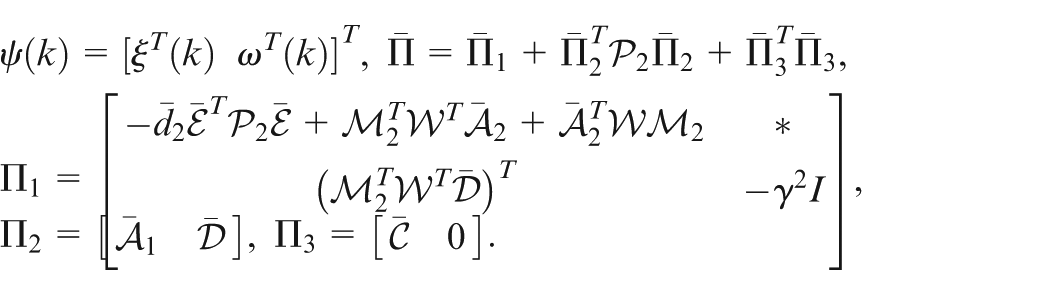
By Schur complement and (15), one has
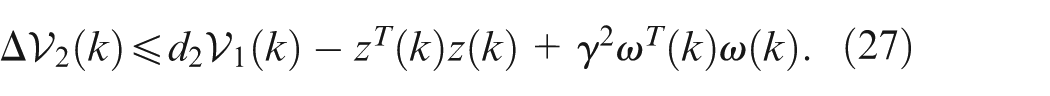
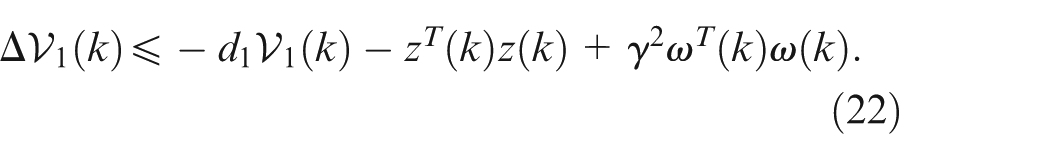
From (22) and (27), one can derive that
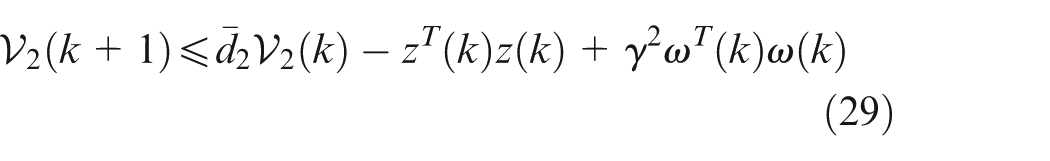
where
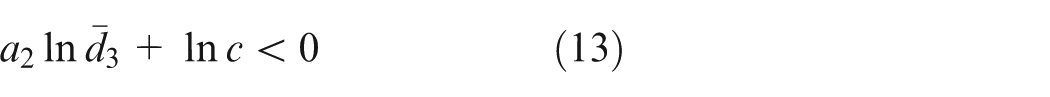
From the definition of Lyapunov functional and (13), we have
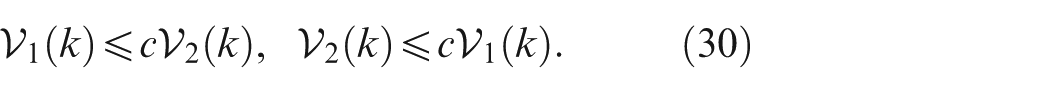
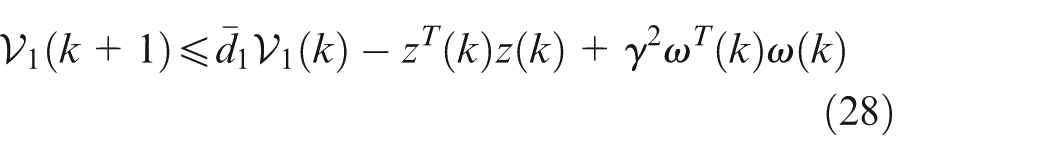
Next, there are two situations to consider, namely,
As to
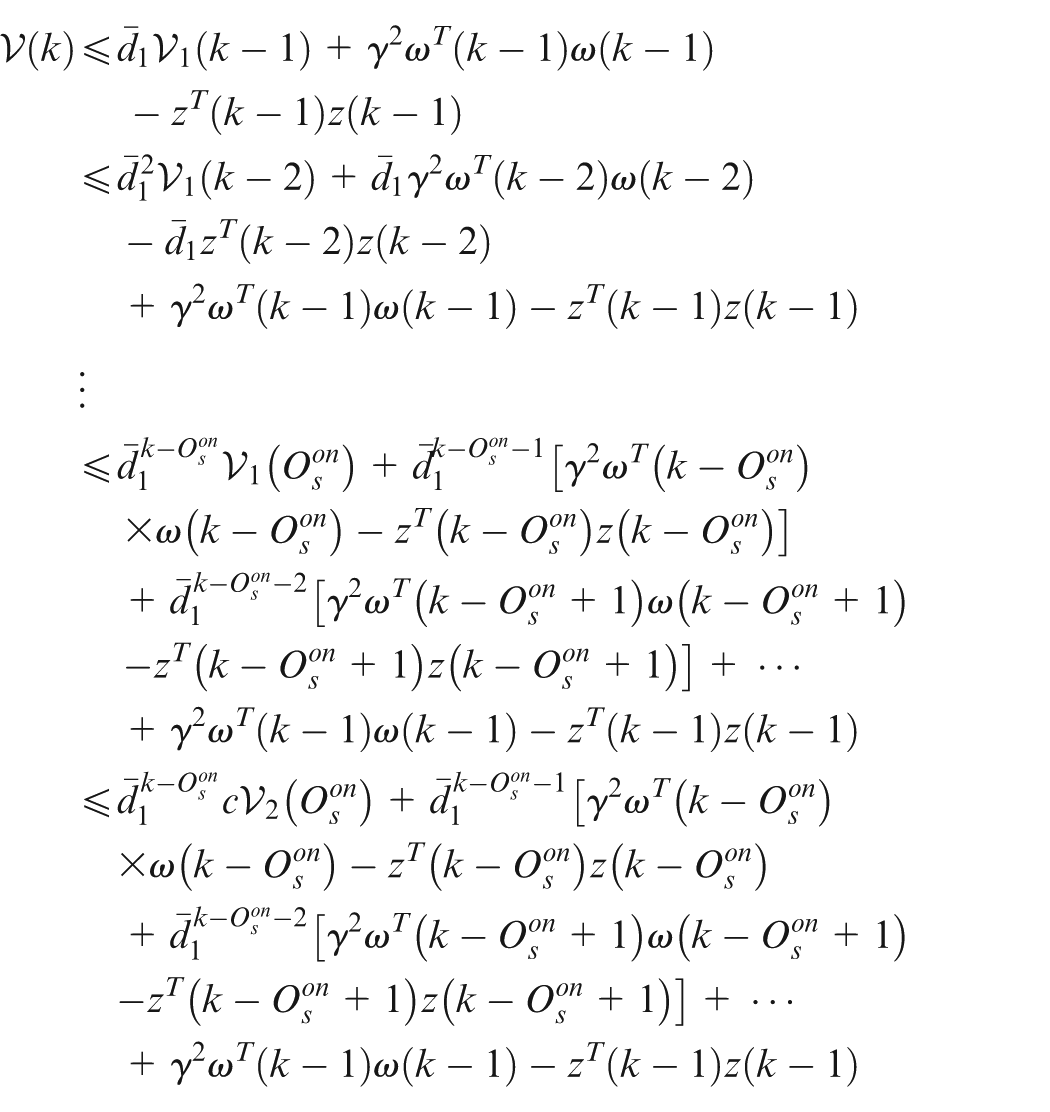
Next, the exponential stability of the systems (6) and (7) are considered.
Let
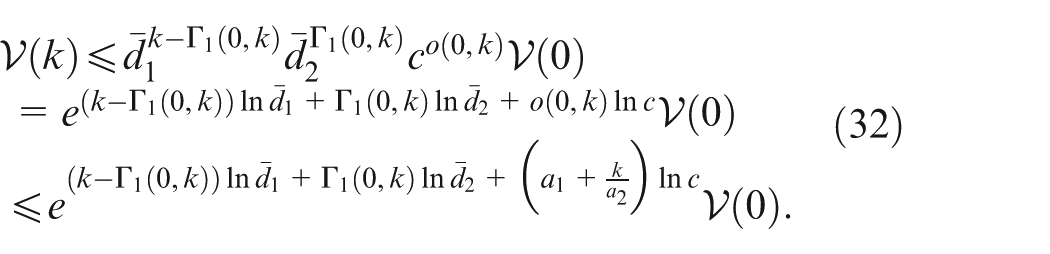
By using Assumption 2, we have
In addition, (14) indicates that
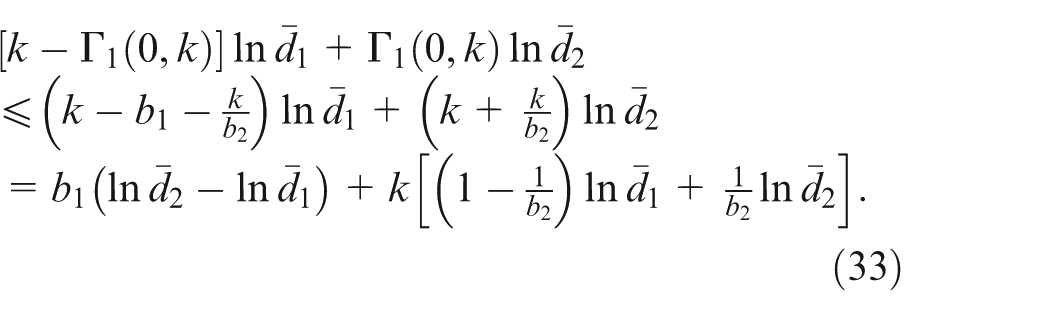
Combining (33) and (34), we get
Substituting (35) into (32), one has
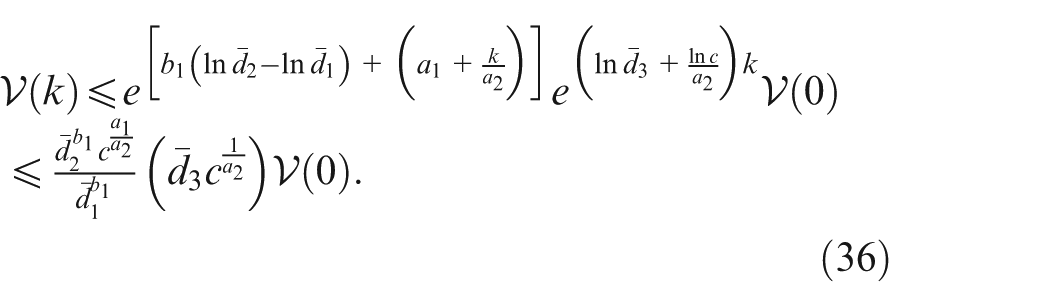
Define
From (36), one can obtain
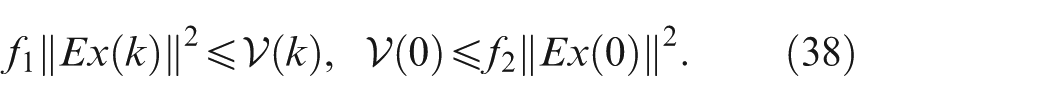
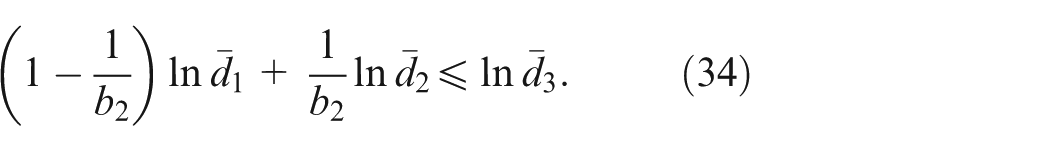
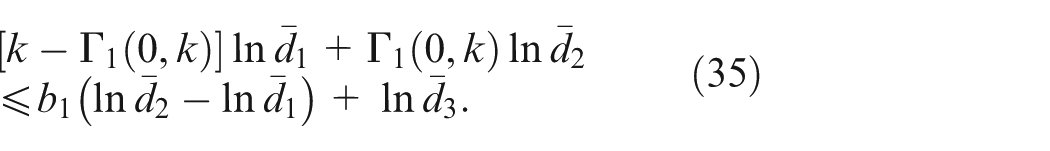
Combining (36) and (38) yields
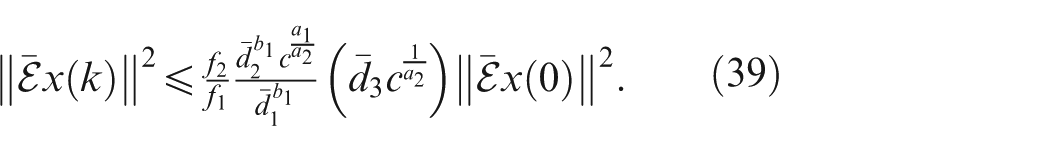
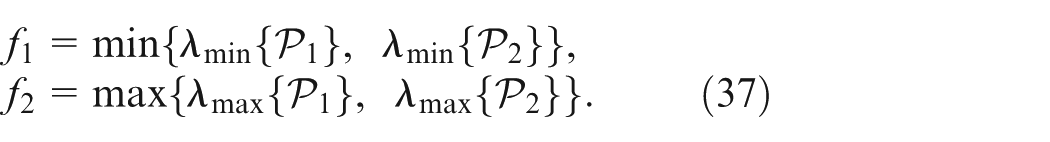
From (15), one can get
Finally,
Since
where
Notice that
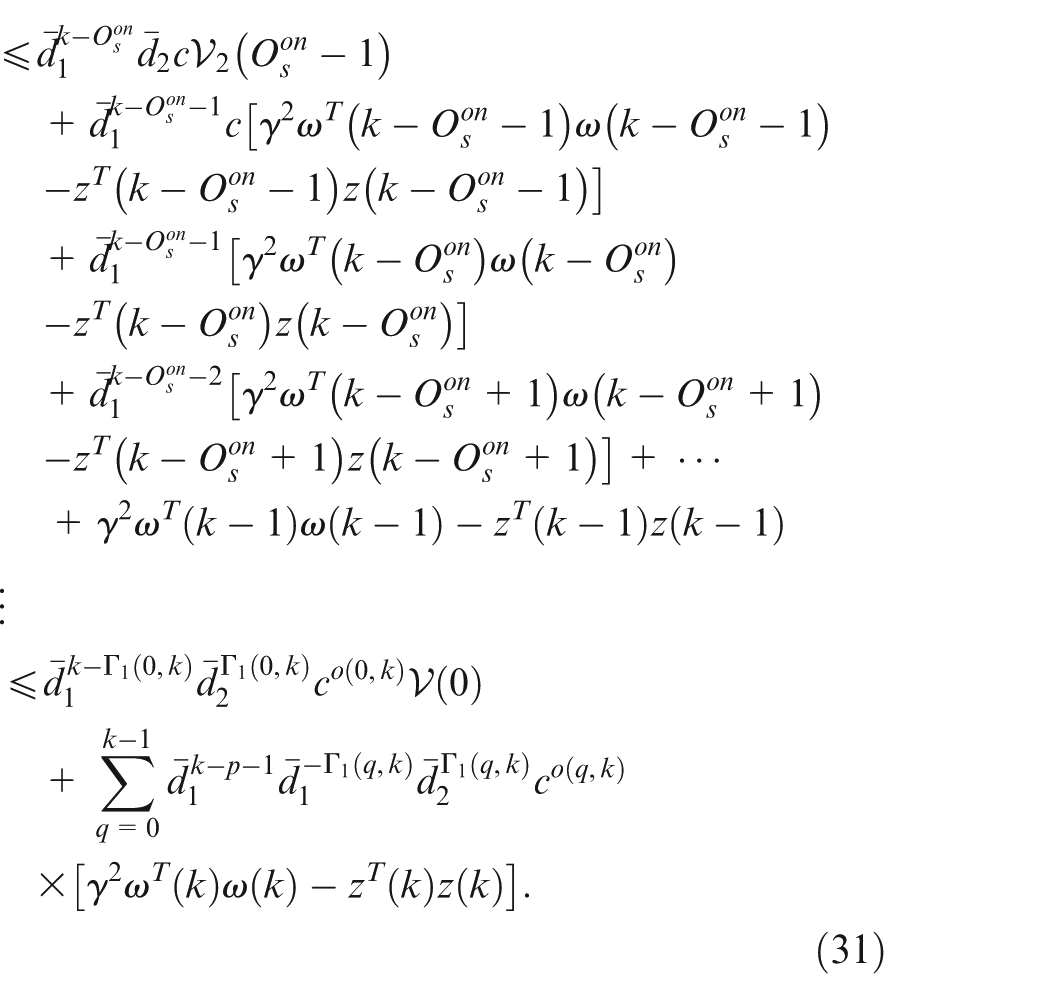
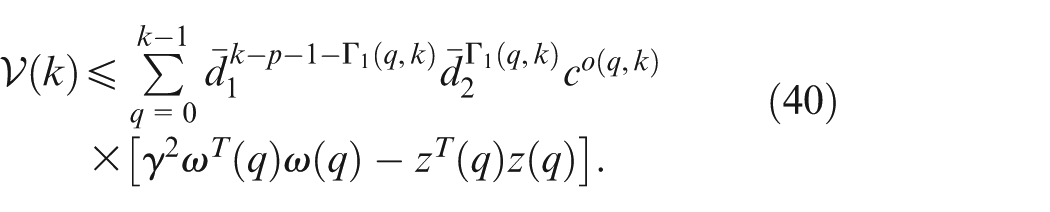
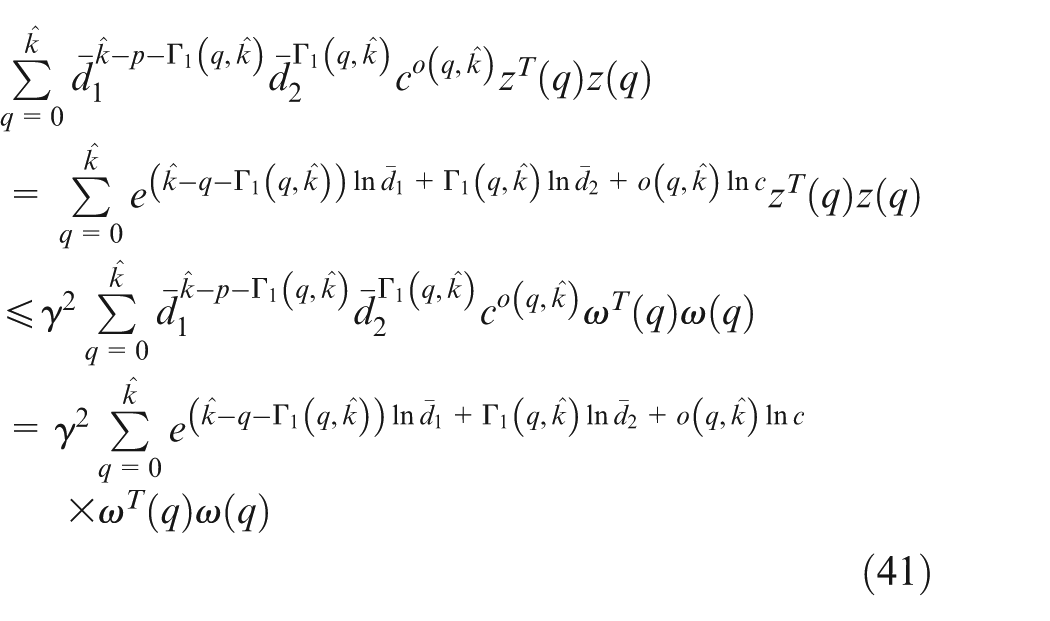
Considering (40), (42) and Assumption 1, one deduces
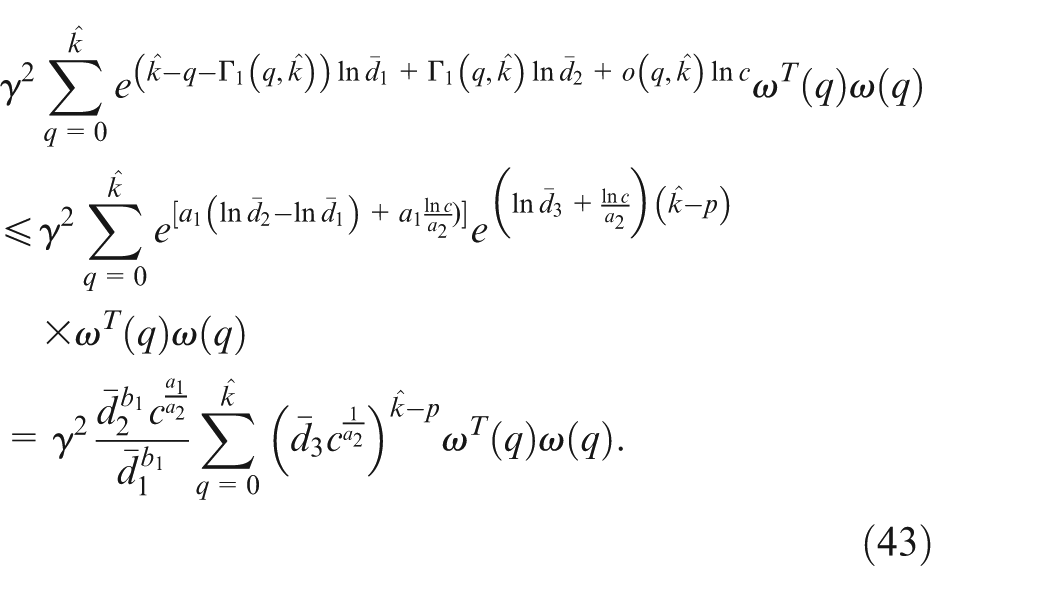
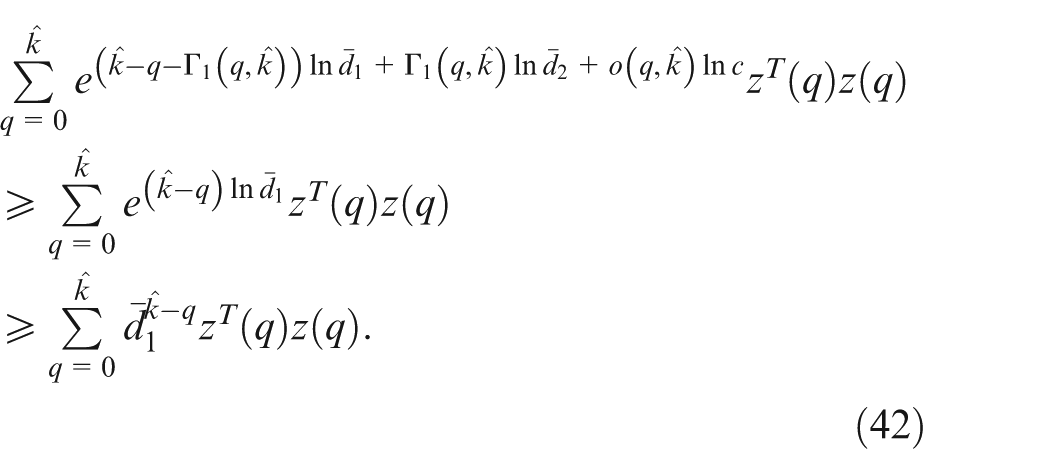
From (41) and (43), it can be derived that
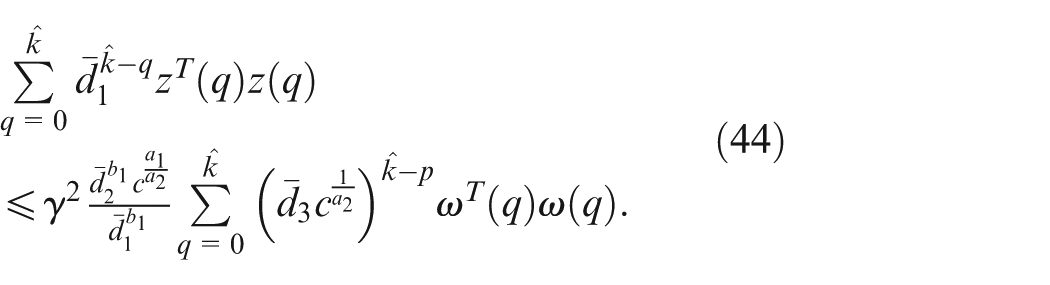
Adding
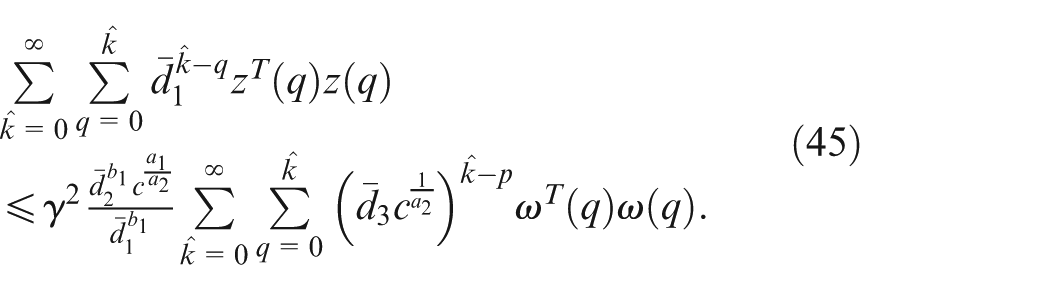
From (45), one has
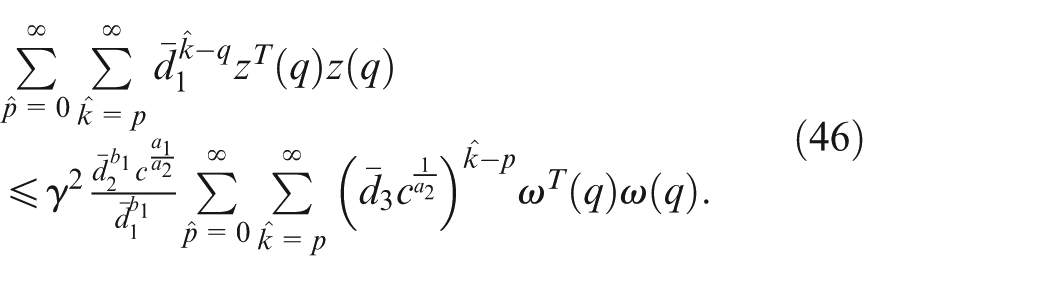
Due to
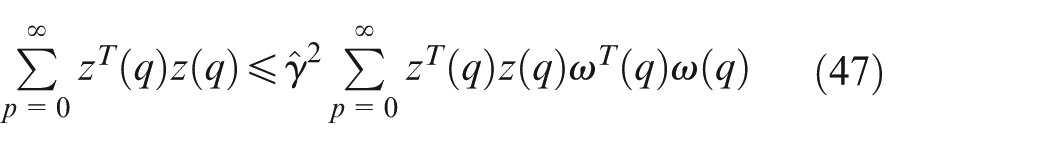
where
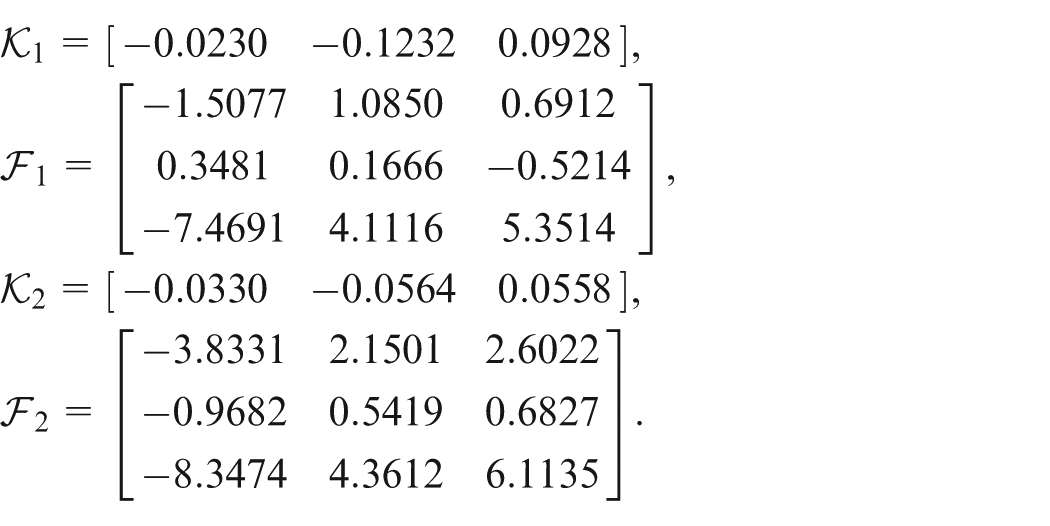
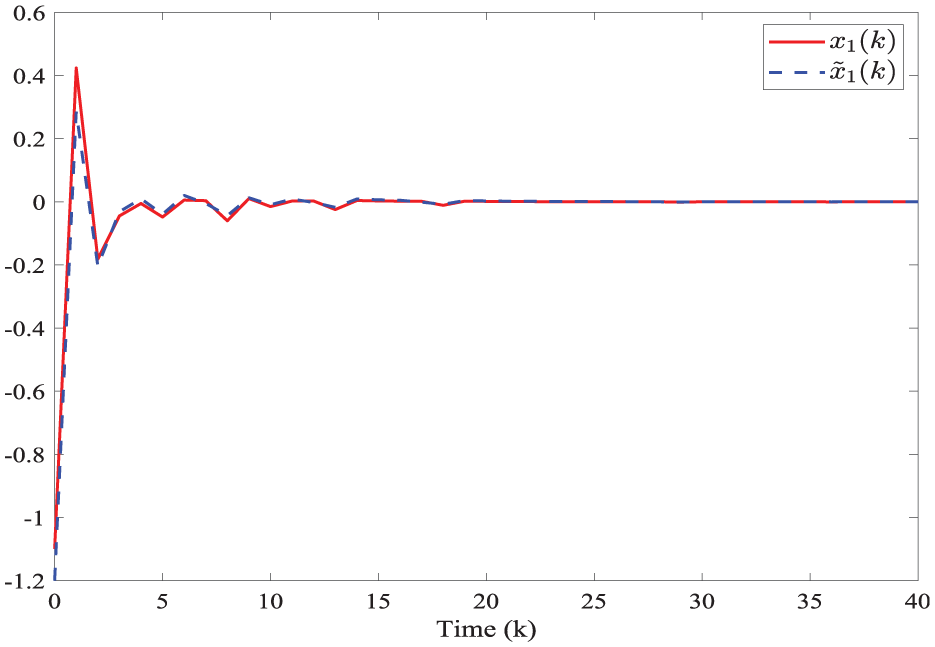
Next, a novel method is developed to obtain the observer gains.


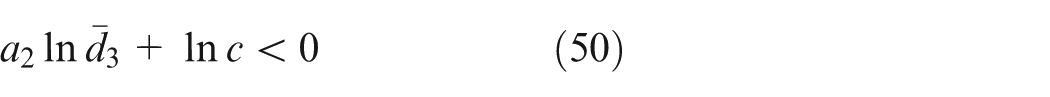
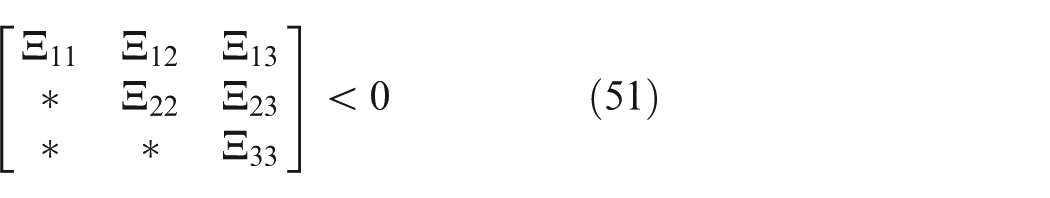
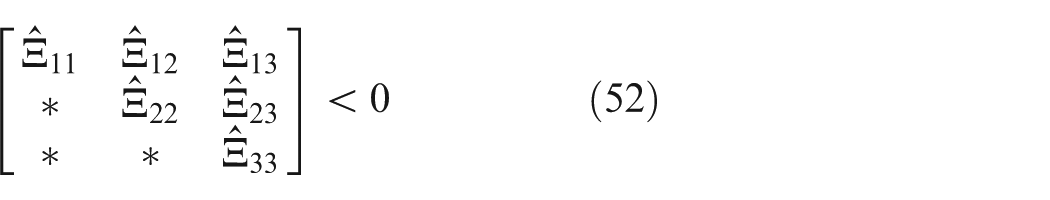
where
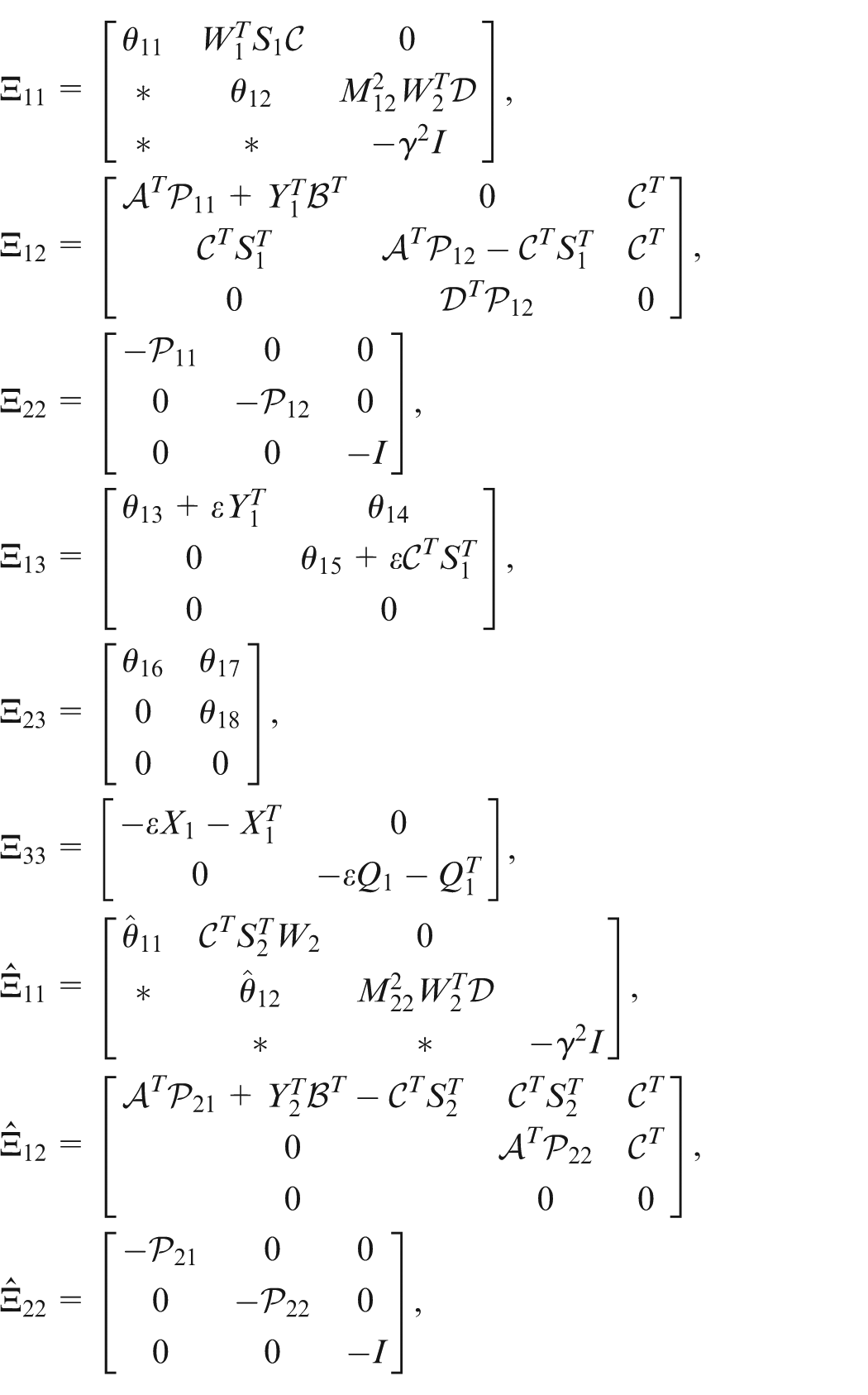
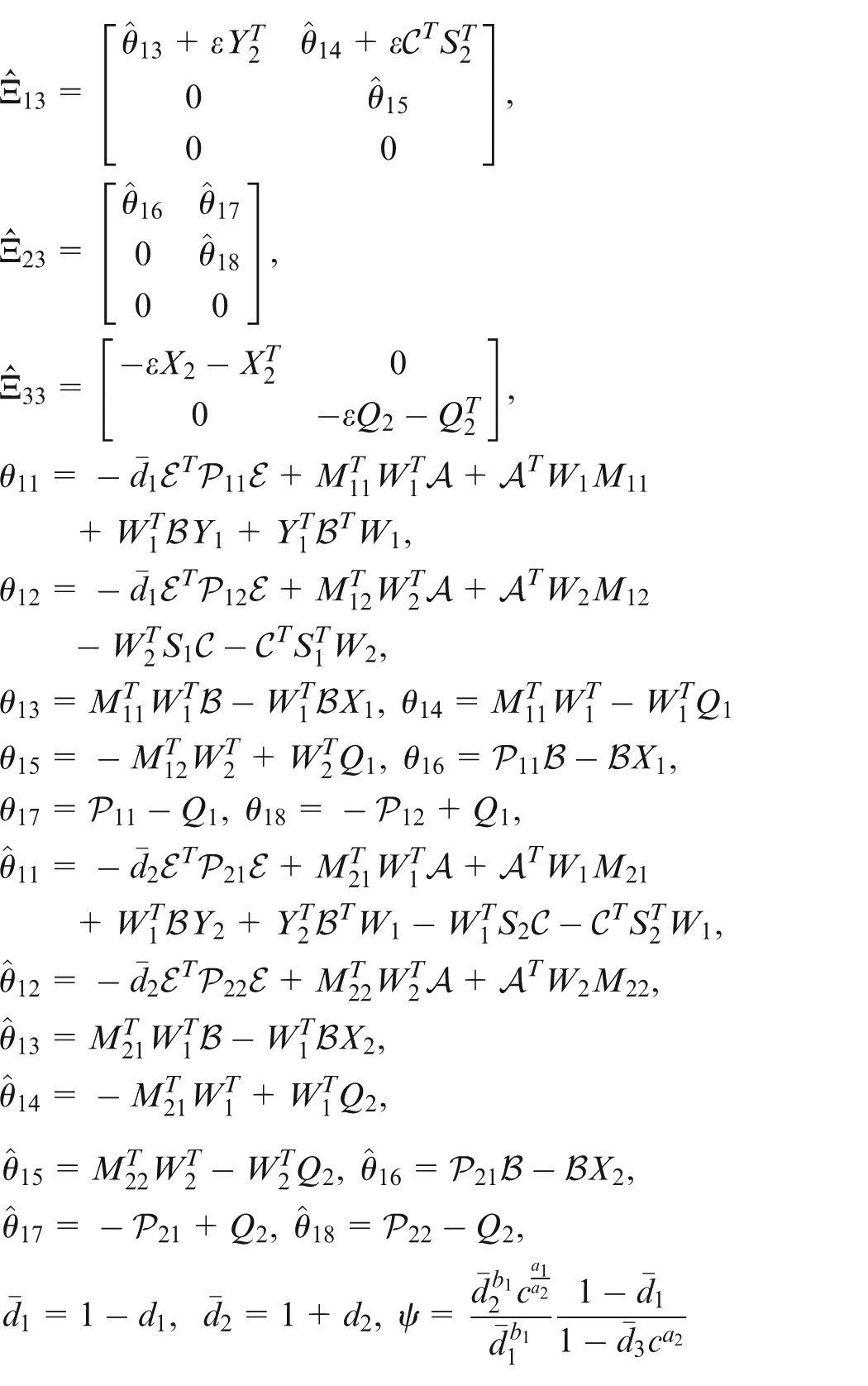
and
Moreover, the observer gains are given as
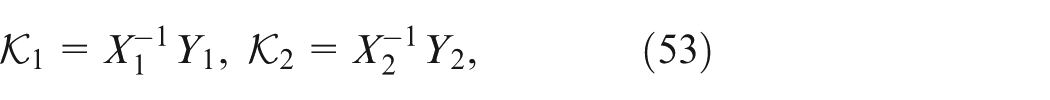
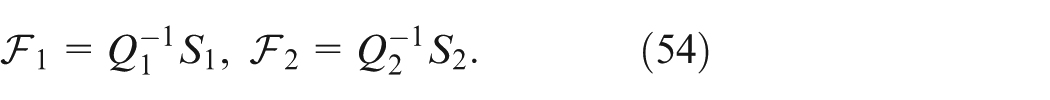

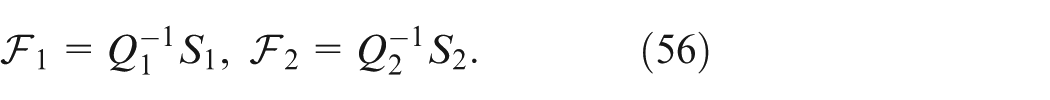




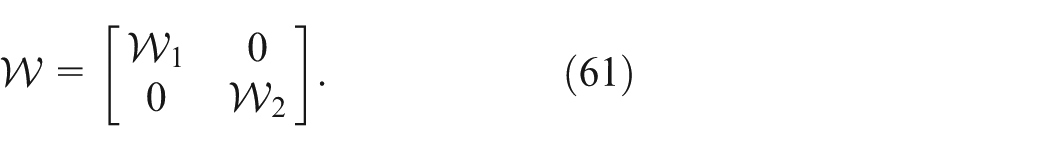
Substituting (55)–(61) into (51) and (52), and applying Lemma 1, we can get (14) and (15). The proof is completed.
Simulation
Two examples are given to illustrate the correctness of the proposed approach.
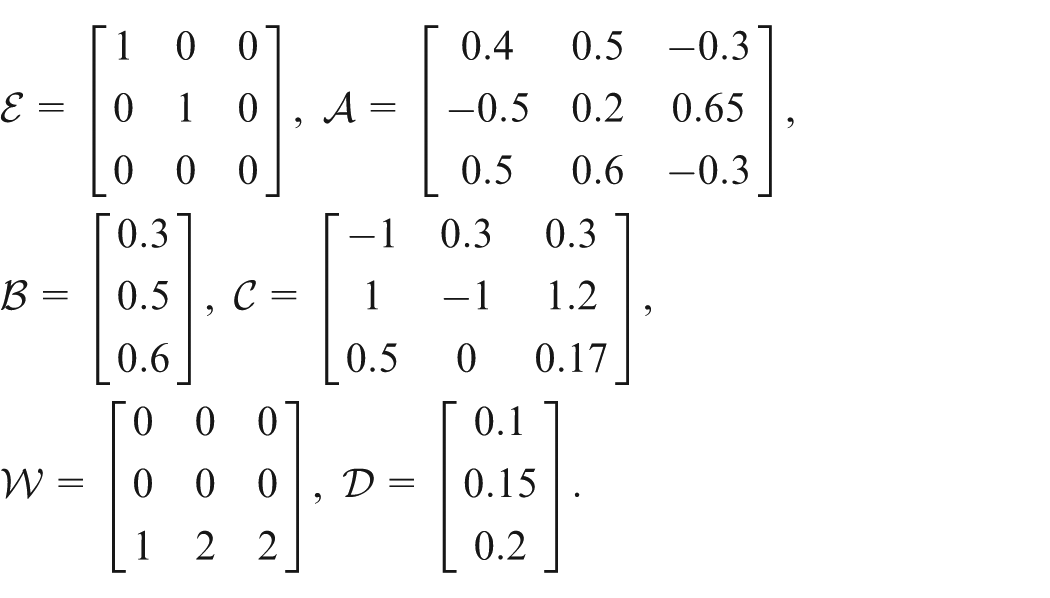
Assume that
Supposes
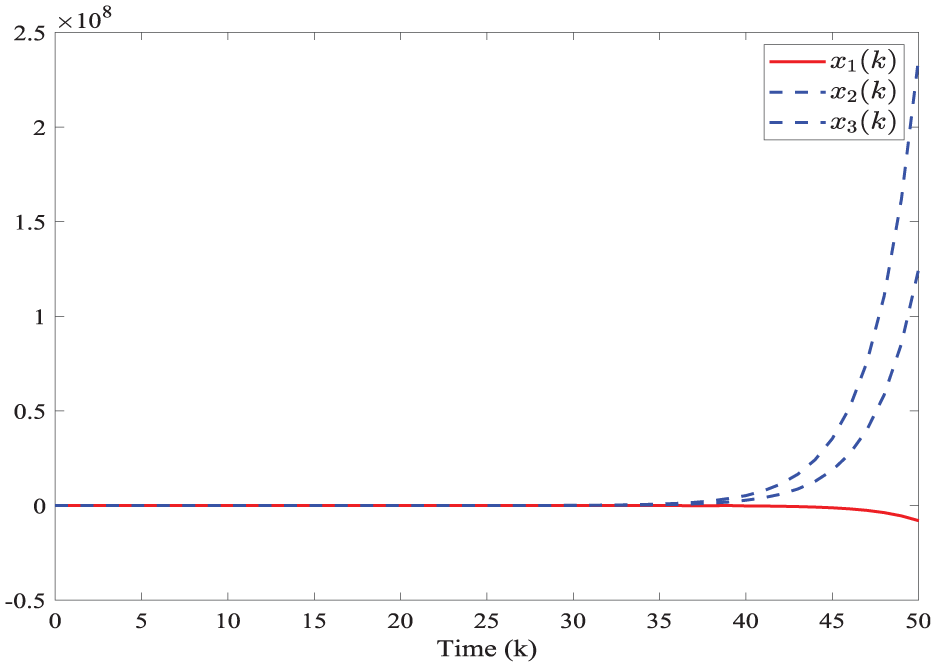
The states of the open-loop system of Example 1.
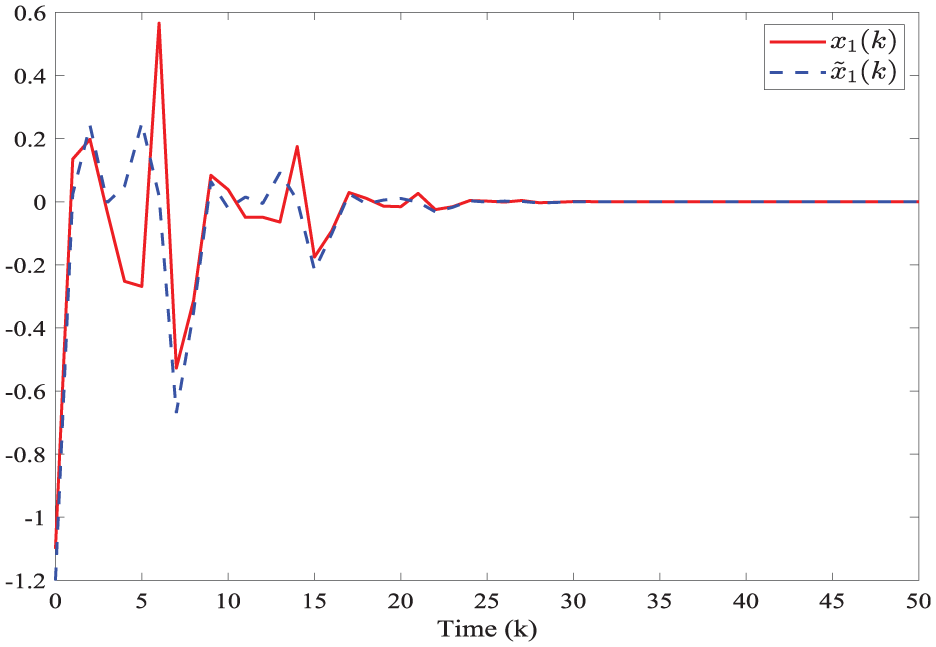
The states of
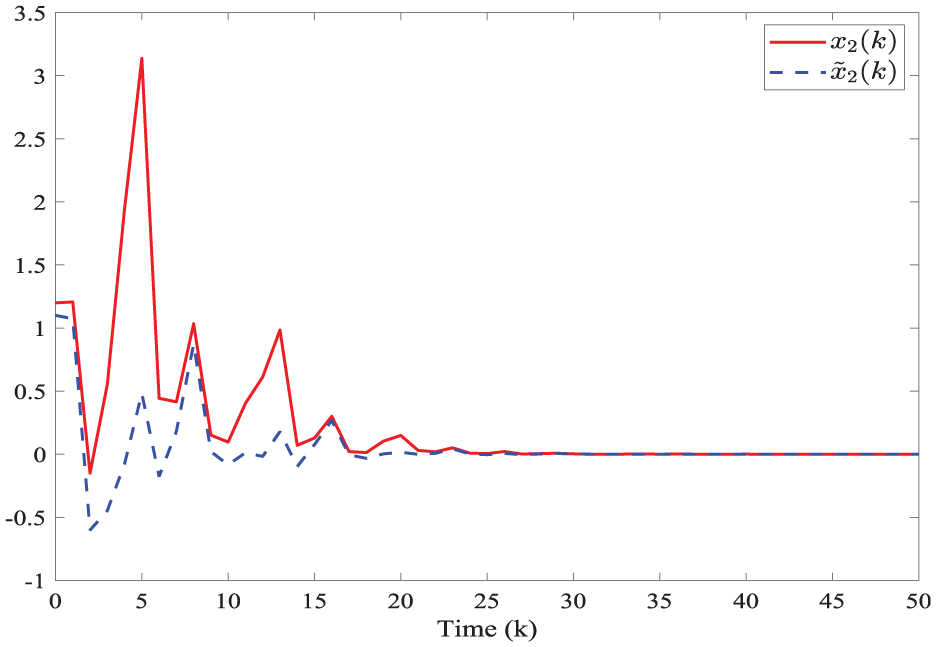
The states of
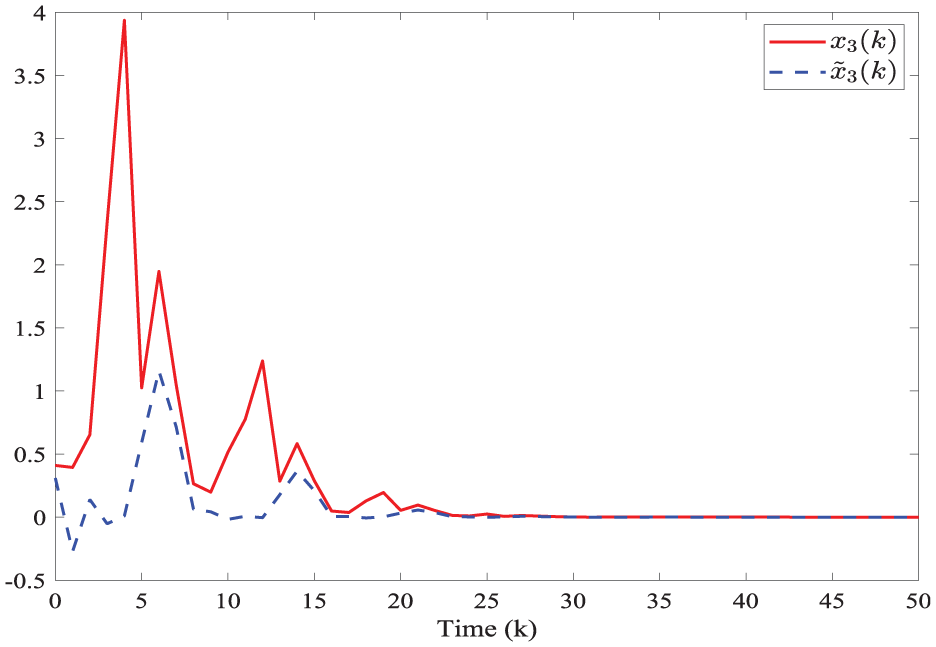
The states of
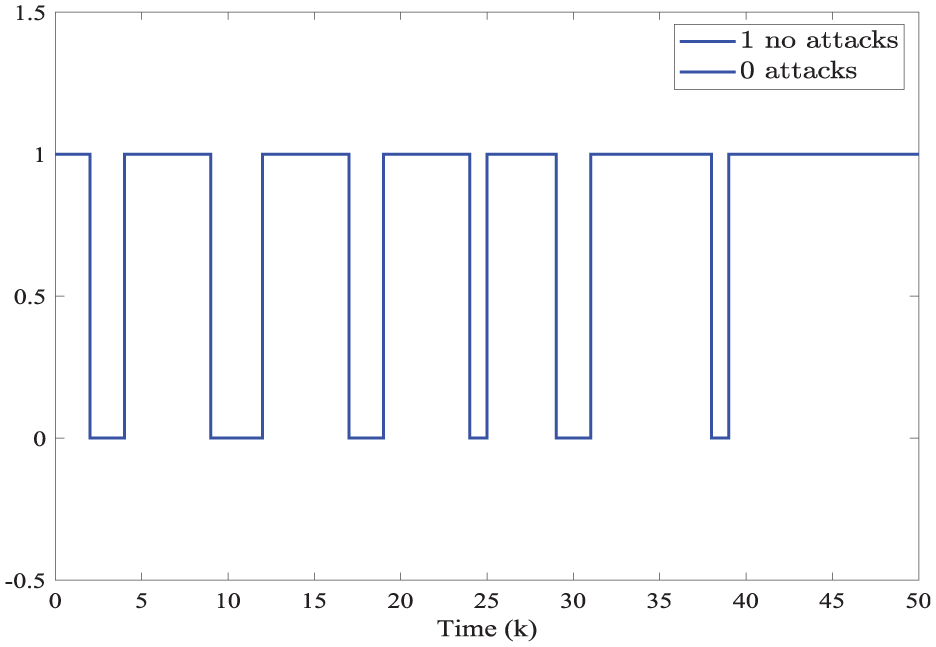
Evaluation of DoS attacks of Example 1.
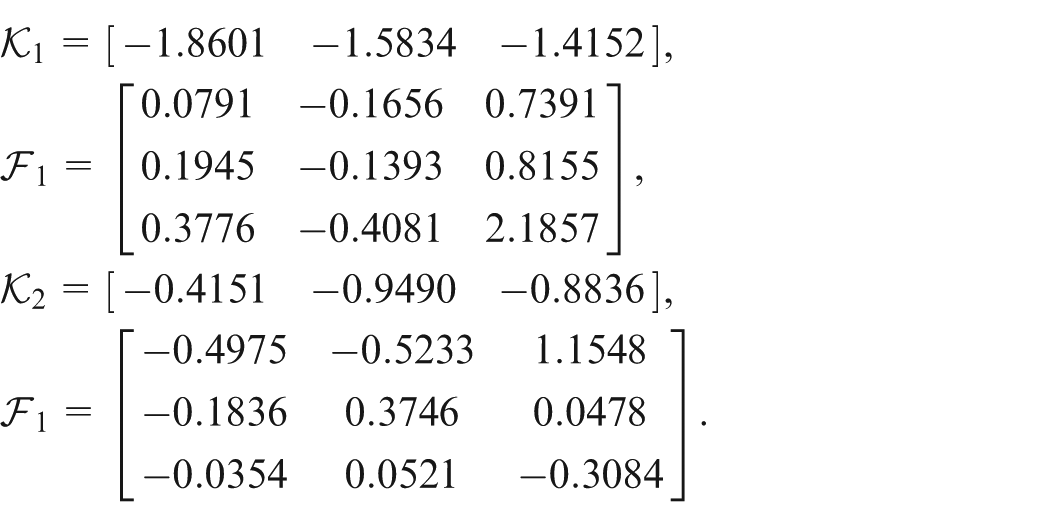
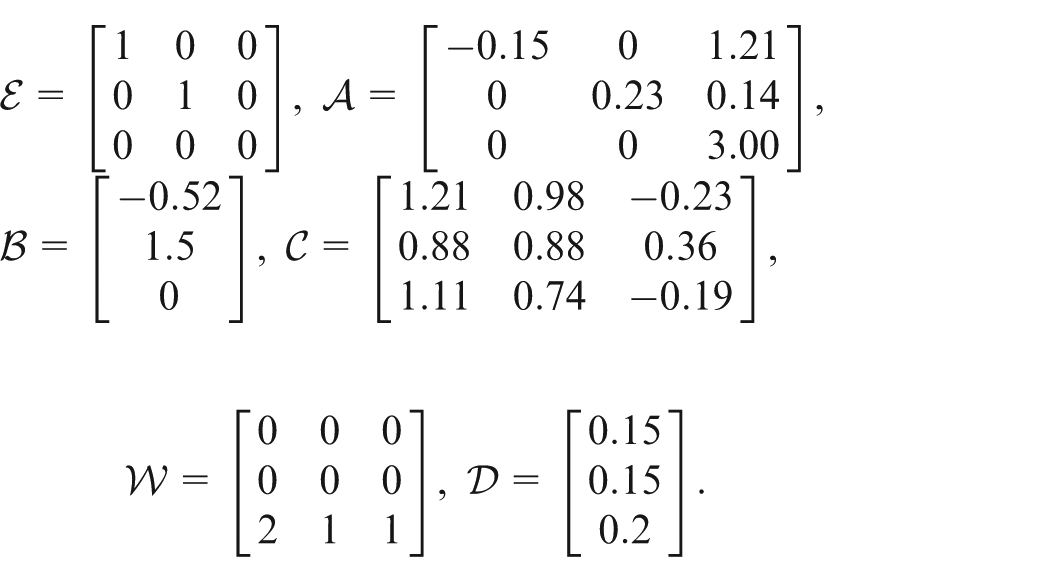
Assume
Supposes
The states of
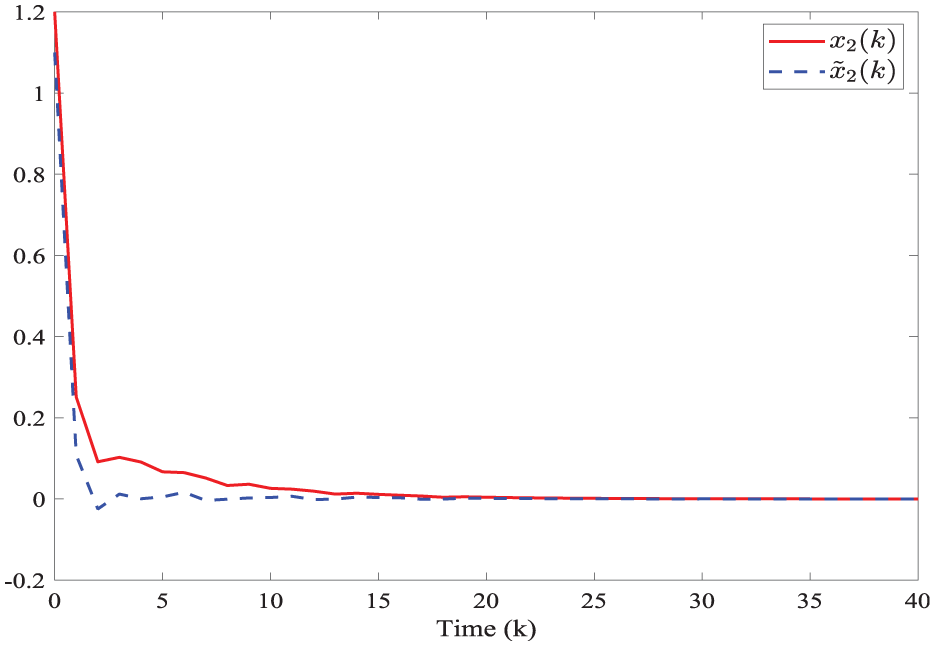
The states of
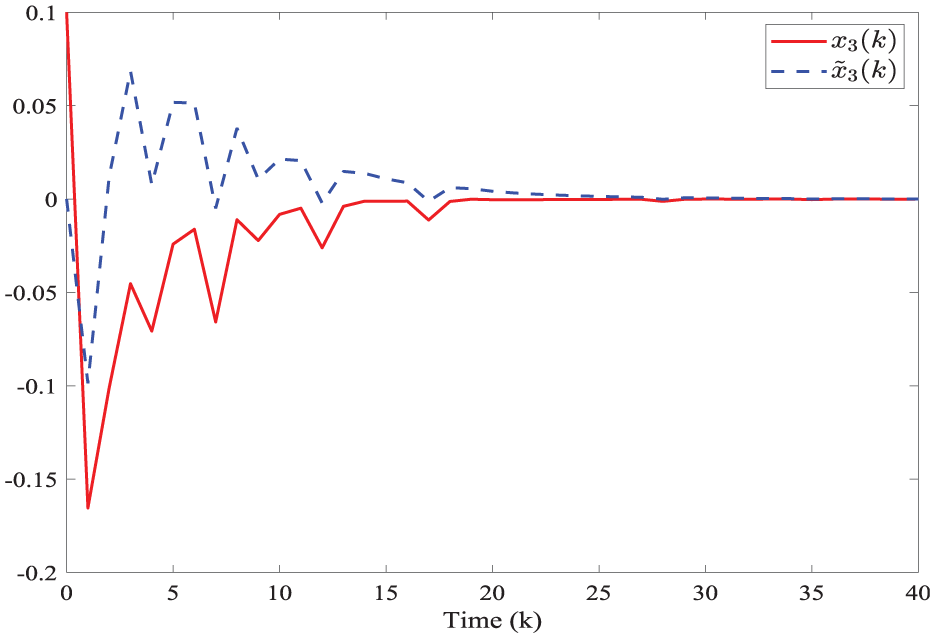
The states of
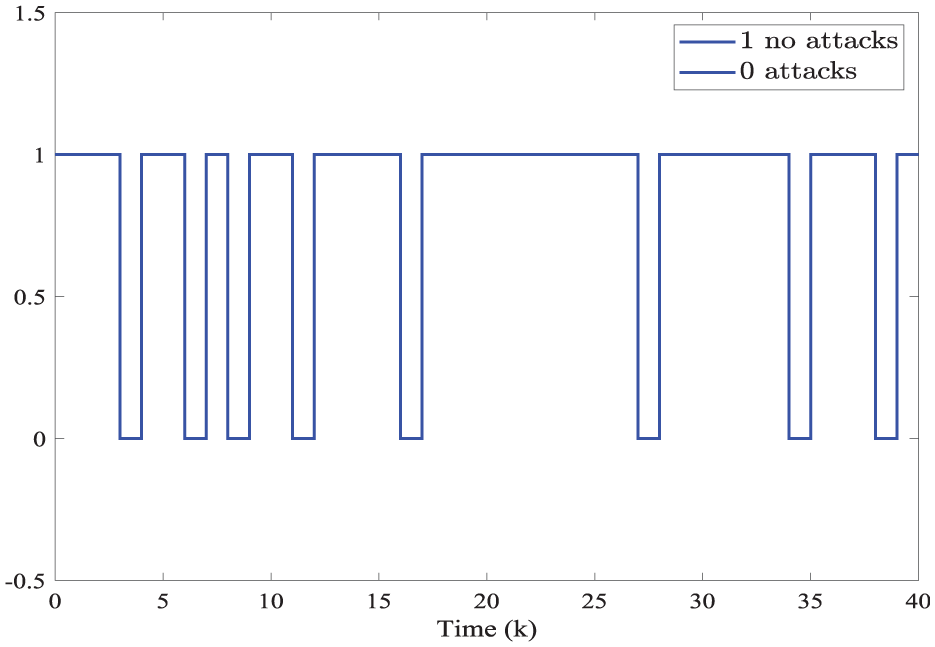
Evaluation of DoS attacks of Example 2.
Conclusions
The problem of observer-based secure controller design has been studied for discrete-time singular systems with DoS attacks in this paper. The non-periodic DoS attacks which make the system unstable are considered. A switched observer-based control method is established to estimate the states. Firstly, some sufficient conditions are given for the corresponding switched systems to be exponentially admissible with
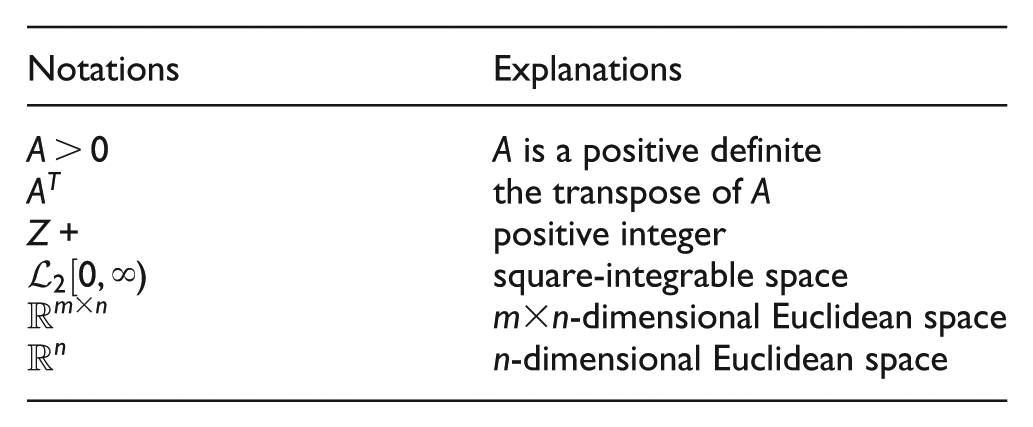
Footnotes
Ethical considerations
This study did not involve human participants, human data, or human tissue.
Funding
The authors disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was supported by Anhui Engineering Research Center of Intelligent Manufacturing of Copper-Based Materials (2024tlxyptZD04), Intelligent Decision Making for Copper Industry Development Anhui Key Laboratory of Philosophy and Social Sciences (2024tlxyptZD09), Anhui Provincial University Research Project (2023AH051659), and Talent Research Initiation Fund Project of Tongling University (2023tlxyrc57).
Declaration of conflicting interests
The authors declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Data availability statement
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.
