Abstract
Due to the significant characteristics of decentralization and tamper resistance of blockchain technology, it helps to solve the problems of timeliness and slow permission control in traditional information sharing. However, most researchers are committed to exploring how to improve the efficiency, reliability, and privacy security of digital twin data. There is a lack of research on issues such as blockchain participants free-riding and not actively participating in information sharing, and how to promote information sharing through incentives. Therefore, this paper designs a distance grouping based practical byzantine fault tolerance consensus algorithm to address the credibility issue of transmitted data, thereby improving the efficiency of negotiation. The feasibility of the algorithm is verified through cases analysis. In addition, for the problem of low subjective willingness of information sharing, this paper designs an information sharing incentive strategy based on blockchain intelligent contracts, establishes digital twin data sharing evolutionary game models with reputation incentives and non-reputation incentives, so as to explore the impact of reputation incentive on evolutionary stability strategies. Finally, simulation analysis is conducted on the evolutionary game model of digital twin data sharing. The impact of several key indicators such as data complementarity, trust, positive incentive coefficient, and data sharing cost on the evolution process of information sharing are considered, and corresponding management insights are obtained.
Introduction
With the rapid advancement of technology such as mobile internet, IoT, cloud computing, big data, artificial intelligence, and blockchain, the global digital economy has rapidly emerged as a vibrant emerging industry. Through digital twin (DT) technology, physical entities can be transformed into simulated virtual models, simulating their behavior in the real world. Through virtual and real feedback, fusion analysis, iterative decision optimization, and other techniques, their performance can be improved and their functional scope expanded. By integrating disciplines such as modeling, data, and intelligence, DTs can act as a bridge between material and information throughout the lifespan of the product, providing timely, efficient, and intelligent services.
DT technology has been widely applied in various industries, especially in intelligent manufacturing. Different levels of DT integration can be used depending on the specific needs of specific industries or applications. Aheleroff et al. (2021) investigated these various levels of integration, and digital twin technology can be applied to various levels of integration depending on industry or application requirements. 1 According to Qi et al., 2 intelligent control of factories, rapid personalized production line configuration, effective monitoring of the entire product lifecycle, intelligent logistics, dynamic scheduling, improved efficiency of robots, ensuring product quality, and maintenance and human-machine interaction of CNC equipment can be achieved by using DT technology. 1
Although these technologies involve different functional applications of DTs, the fundamental element is data. Data transmission plays a crucial role in the functioning of DT. By continuously transmitting data between the physical and digital worlds, DT enable real-time monitoring, analysis, and decision-making, leading to improved system performance, reduced downtime, and lower maintenance costs. As the IoT continues to grow, the importance of DT will only continue to increase, making data transmission a critical aspect of their success.
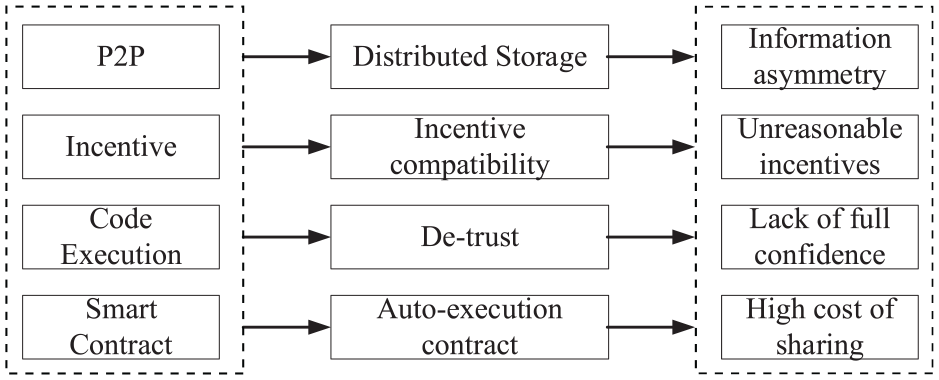
The emergence of blockchain technology provides a new approach to solving the problem of data sharing, as it offers advantages such as decentralization, digital signature technology, automated execution, and regulatory traceability. With the continuous development of blockchain technology, it has been widely applied in various industries, such as organizational management, insurance business, government services, medical information, as shown in Figure 1. Meanwhile, blockchain technology can support various functions such as acquiring, processing, distributing, transferring, parsing, and providing feedback from third parties, thereby greatly enhancing the security and effectiveness of data.
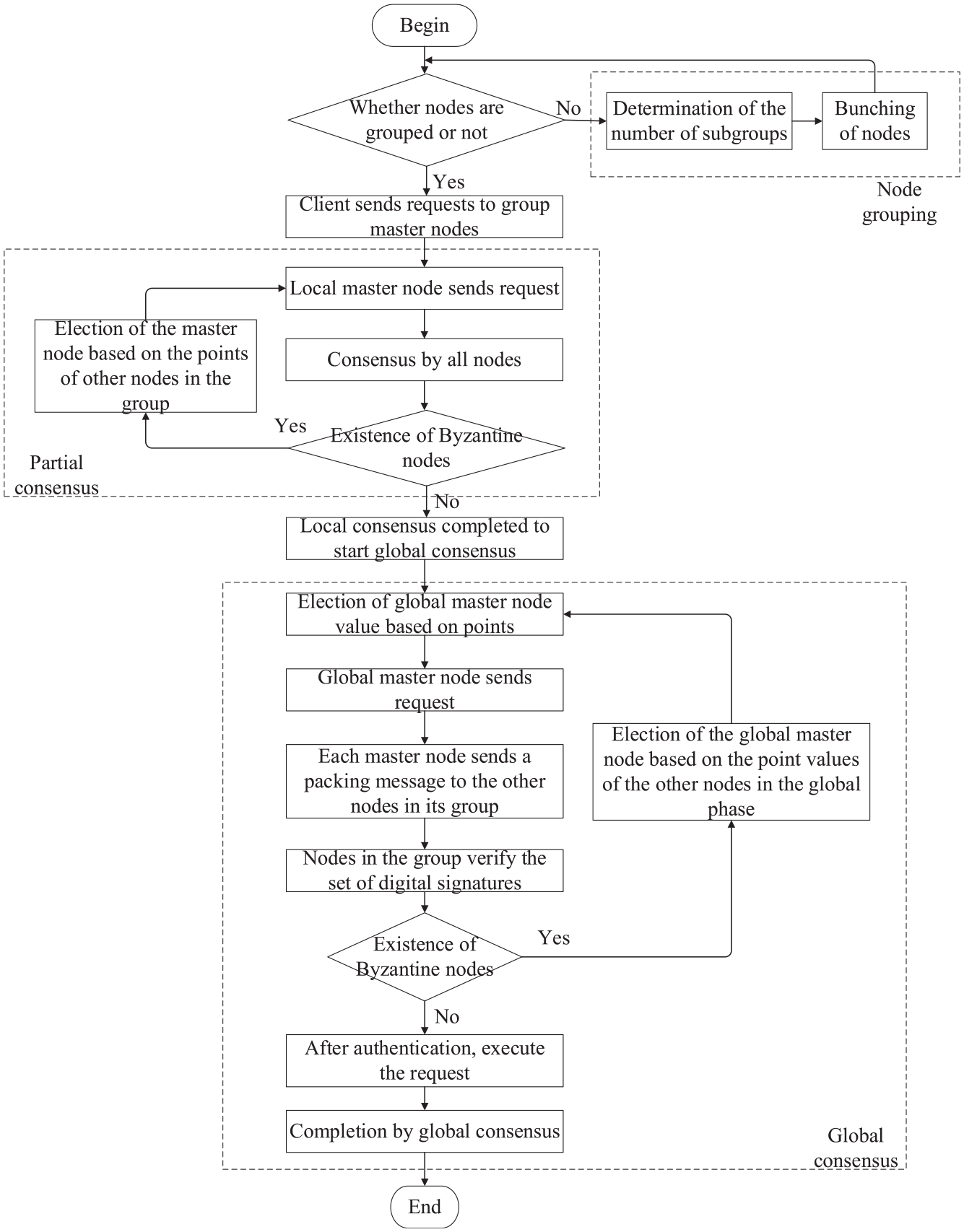
D-PBFT algorithm flow.
Although blockchain technology has made significant progress, it also brings some potential risks, such as participants engaging in selfish behaviors like free-riding. Such behavior not only seriously infringes on the rights and interests of participants but also undermines the information-sharing ecosystem based on blockchain technology, resulting in widespread underperformance of information sharing. Therefore, this paper aims to explore the reliability of DT data sharing and utilize blockchain technology to construct reliable DT data. The contribution of this study mainly lies in consideration of the following aspects:
(1) Improvement of the practical byzantine fault tolerance (PBFT) algorithm by introducing delegated proof-of-stake algorithm, a scoring reward and punishment mechanism, and categorization of nodes based on their distances. It can effectively reduce message complexity, improves consensus efficiency, enhances information security, and avoids privacy issues associated with weak willingness to share among participants when using blockchain technology for DT data sharing.
(2) The correlation between blockchain technology and information sharing is analyzed. Simultaneously, an information sharing incentive model based on blockchain smart contracts was built, taking into account the quantity and quality of information supplied by participants, as well as reputation as an essential indication.
(3) Using evolutionary game theory, a DT data sharing evolutionary model based on blockchain technology is constructed to delve into the dynamic game among participants supported by blockchain technology. In addition, combining evolutionary game theory with system simulation can further explore the information sharing mechanism in the context of DT data, providing a beneficial attempt for the research methodology of information sharing.
The remainder of this paper is structured as follows: A brief review of the related literature is provided in Section 2. Section 3 addresses the security design of trusted data. Incentive strategy for DT data sharing is introduced in Section 4. Section 5 introduces the construction of an evolutionary game model for DT data sharing. A case study is conducted in Section 6 to verify the effectiveness of proposed evolutionary game models. Finally, Section 7 draws some conclusions and suggests some extensions of this work.
Literature review
Information sharing plays a crucial role in today’s digital era, enabling seamless communication and collaboration between individuals, organizations, and systems. This literature review explores three aspects of information sharing: blockchain-based information sharing, information sharing in digital twins, and information sharing based on evolutionary game theory. Each aspect offers unique perspectives and approaches to address information sharing challenges.
Research on information sharing based on blockchain technology
Blockchain technology has emerged as a promising solution for secure and decentralized information sharing in various domains, including healthcare, supply chain management, and finance. A literature review on blockchain-based information sharing reveals that this technology offers several advantages over traditional centralized systems, such as enhanced security, transparency, and immutability.
Researchers have proposed various blockchain architectures and consensus mechanisms to address scalability, privacy, and interoperability issues. Zhang et al. 3 discussed the application of blockchain technology in construction contract management through literature review. In addition, Lim et al. 4 provided a comprehensive overview of the application of blockchain in the supply chain. Meanwhile, Xu and He 5 further determined the optimal application of blockchain in modern logistics information sharing. Considering that blockchain will bring significant changes to resource sharing activities and information service organizations, Xuan et al. 6 proposed a new shared incentive game model that can mobilize participants’ enthusiasm in real-time by leveraging the advantages of blockchain technology, thereby improving overall efficiency. Guggenberger et al. 7 proposed a decentralized information hub model, describing how the company utilizes blockchain technology to promote information sharing and contribute to the supply chain knowledge base. The software connector designed by Longo et al. 8 could interconnection between Ethereum technology and enterprise information systems efficiently. Enterprises could share information with other visible partners, thereby ensuring the security and authenticity of data. 8
Moreover, the integration of blockchain with other emerging technologies, such as Internet of Things (IoT) and artificial intelligence (AI), has opened up new possibilities for smart and autonomous information sharing systems. Blockchain technology has been applied in many fields, Wu et al. 9 explored the application of blockchain technology in on-site assembly of modular construction, and improved the accuracy of information sharing by recognizing information about modules and their assembly through the consensus mechanism of blockchain. Du et al. 10 proposed a new blockchain-based medical information sharing model, which can effectively protect the integrity of information and prevent any form of manipulation.
Research on information sharing in DT
Information sharing is a key aspect of digital twins, as it enables real-time data exchange between the physical and virtual worlds. Through a comprehensive literature review, Chen and Huang 11 found that DT have a positive impact on addressing information asymmetry in the remanufacturing supply chain. Tao et al. 12 first proposed the concept of DT data as a core component of a five-dimensional model.
At present, this field is facing some challenges, such as data quality, consistency, and security. Researchers have proposed various methods to address these challenges, including data preprocessing techniques, data synchronization algorithms, and secure communication protocols. Shen et al. 13 proposed a blockchain-based DT data security sharing framework to address the data sharing issues caused by the lack of data security and trust among device stakeholders. Lee et al. 14 developed and tested a framework that combines traceable data communication, integrated DT, and blockchain. They tested the framework through a case project and found that it enables responsible sharing of project-related information among stakeholders. 14 Putz et al. 15 proposed an owner-centric decentralized sharing model to meet the demand for decentralized sharing of DT data. To address the data sharing challenges of DT data, Huang et al. 16 proposed a product DT management method based on blockchain technology. To address the security issues during the transmission of DT data, Shi et al. 17 proposed a secure and lightweight triple trust architecture to ensure the authenticity of transmitted data and the trustworthiness of identities.
Additionally, the integration of digital twins with other technologies, such as cloud computing and edge computing, has led to the development of more efficient and scalable information sharing systems. Ma et al. 18 proposed a novel edge computing scheme to address the data trust and security issues in edge computing environments, and designed user-defined sensitive data encryption before storing transaction payloads in the blockchain system. Jennath et al. 19 proposed a blockchain-based medical record solution to address the security and privacy issues in existing electronic health systems. Guo et al. 20 developed a distributed trustworthy authentication system that utilizes blockchain technology, edge computing, and Byzantine fault-tolerant consensus algorithms. The system could effectively support security, reliability, convenience, and integrity, and store authentication data in a consortium chain for better tracking of final activities. 20
Research on evolutionary game of information sharing
Information sharing is a common application of evolutionary game theory, as it helps to explain how individuals can achieve mutual benefits by cooperating and sharing information. This approach has been applied to various domains, such as social networks, wireless communications, and energy markets. Researchers have proposed various models and algorithms to analyze the impact of different factors, such as network topology, incentive mechanisms, and reputation systems, on information sharing behavior. Feng et al. 21 constructed a tripartite evolutionary game model for industrial IoT platforms, semiconductor manufacturers, and material suppliers, and analyzed the factors that affect the selection of tripartite information sharing strategies. Cheng et al. 22 constructed an evolutionary game model between small and medium-sized enterprises and leasing companies to mitigate the risk of lease contract breach caused by information asymmetry, and designed incentive mechanisms to encourage tenants and lessors to jointly build a sustainable and trustworthy leasing environment. Shen et al. 23 utilized evolutionary game theory to explore the evolutionary path of port cold chain enterprises participating in information sharing. They also designed an incentive mechanism based on blockchain smart contracts to encourage cold chain logistics enterprises to actively participate in on chain information sharing. 23
Moreover, the integration of evolutionary game theory with other disciplines, such as behavioral economics and sociology, has led to the development of more comprehensive and realistic models of information sharing. Based on the idea of cloud manufacturing, Li et al. 24 constructed a tripartite evolutionary game model consisting of government, remanufacturing enterprises, and recycling enterprises, combining research on the enthusiasm of enterprises for information sharing and its influencing factors with evolutionary game theory and system dynamics. Li 25 conducted in-depth research on enterprise information security investment using evolutionary game theory, analyzing the evolution and influencing factors of information sharing in information security sharing platforms, in order to improve the efficiency of information security sharing platforms. Yu et al. 26 used evolutionary game theory to establish a general game model under symmetric and asymmetric information between retailers and producers based on the benefit matrix, and studied the long-term impact of information sharing on the adoption of organic agriculture. Xing et al. 27 used evolutionary game theory to study the interaction between cold chain logistics enterprises and governments, and discussed the contribution of information sharing to avoid cold chain fractures, in order to provide cold chain transparency, traceability, and fracture proof.
Research gap
Recent years have witnessed a growing interest in the sharing of DT data with the advancement of technology. Many studies have focused on the security, reliability, and efficiency of information sharing in this field. To address these issues, researchers have explored the use of blockchain technology and other related mechanisms, such as establishing a consensus system, to ensure the authenticity and reliability of data. Additionally, policies have been proposed to promote the development of this field. These studies provide important theories and methods regarding information sharing. Moreover, according to the latest research findings, blockchain technology has been widely applied in various domains such as financial services, smart buildings, and healthcare. However, based on the previous summary, the following research gaps still exist.
(1) In recent years, researchers have been dedicated to improving the efficiency, reliability, and privacy security of DT data sharing. However, there is a lack of research on issues such as free-riding behavior and passive participation in blockchain, as well as how to promote information sharing through incentive mechanisms.
(2) Current research has not delved into how participants in DT data make decisions on information sharing through game theory, nor has it analyzed which factors influence these decisions. Additionally, there is no identified method to appropriately adjust the level of incentives to allow different participants to achieve optimal information sharing results under limited trust.
Therefore, this paper designs a distance grouping based PBFT consensus algorithm to address the credibility issue of transmitted data, thereby improving the efficiency of negotiation. In addition, for the problem of low subjective willingness of information sharing, this paper designs an information sharing incentive strategy based on blockchain intelligent contracts, and establishes DT data sharing evolutionary game model with reputation incentives, so as to explore the impact of reputation incentive on evolutionary stability strategies.
Security design of trusted data based on blockchain
Considering that PBFT can provide higher levels of security and reliability compared to crash tolerance, and can handle more nodes without sacrificing performance or reliability, it is highly suitable for use in distributed systems such as blockchain networks. 29 Therefore, in this section, improvements are designed to the existing PBFT algorithm to ensure system security while reducing consensus latency.
Improved PBFT consensus mechanism based on node grouping
Improvement strategies
Based on the analysis of the PBFT algorithm in Appendix A., the following three main improvement strategies are proposed:
(1) To group nodes, the K-means algorithm is introduced, which can group nodes based on their distance from each other. In K-means grouping, Euclidean distance is used as the metric. After grouping, the central node of each group is selected as the initial primary node.
(2) In case of primary node failure, a primary node election process is introduced. According to a reward and punishment system, the punished primary node will be replaced by a new primary node with the highest score.
(3) During the study, it was found that the commit phase of the PBFT algorithm can be removed without affecting the consensus process. The commit phase only serves to collect votes and does not involve agreeing or disagreeing with the message. After the prepare phase is completed, the message has been sufficiently validated by a significant number of legitimate nodes, thus forming a consensus. Therefore, the commit phase can be removed.
Algorithm design
The initial node set provided by the system is represented by the letter
The nearest central distance refers to the sum of distances from an unselected node to each of the already selected nodes. It is represented by the letter
Through the K-means++ clustering algorithm, the initial node set can be divided into several independent groups, each represented by a letter. In each group, there are some nodes closest to them, denoted by
Based on the above Definition, the specific algorithm process is as follows:
If a node has already been grouped, it directly enters the local consensus phase. If a node has not been grouped, it undergoes node grouping. The node grouping is based on the distance between nodes, dividing them into several groups, with the center of each group considered as the initial primary node. The client sends requests to the primary nodes of each group. After the local consensus phase and the global consensus phase, the client receives sufficient correct feedback messages and generates a block.
The local consensus phase and global consensus phase are the stages of achieving consensus within and across groups, respectively. When sending a request, the primary node obtains relevant information from the client and verifies its legitimacy. After the information is audited, the system automatically generates a new piece of information and adds it to the agreed-upon information set. When the list length or waiting time reaches the predetermined maximum value, it can enter the preparation phase.
During the preparation phase, the primary node generates the prepare message using the message list
In the confirmation phase, replica nodes receive prepare messages from other nodes and verify their legitimacy. Once the verification is completed, the replica nodes add the content and verification results of each message to the message list and then generate a confirmation message, which must be signed by the replica nodes.
In the feedback phase, when a node receives a confirmation message from other nodes, it first verifies the legitimacy of the message, including the consistency of digital signatures and view encoding. Then, it statistically processes the confirmation message’s message list and adds the statistical results to the information list. If the length of the agreement on this information exceeds the length of disagreement, it is recorded. Simultaneously, the node generates a feedback message in the format of
The flowchart of the distance grouping based PBFT (D-PBFT) consensus algorithm is shown in Figure 1.
This paper adopts the K-means++ clustering algorithm to group nodes with close distances within a period T. Simultaneously, it allows nodes to undergo minor position changes (small positional changes will not significantly affect consensus latency). According to Selten (1980), 29 when a node has not been grouped yet or is about to join, the system will decide whether to include it in that group based on its distance from the initially grouped primary node.
The node grouping algorithm consists of two main stages: group number determination stage and node grouping stage.
(1) Group number determination stage
Step 1: Randomly select a center from the dataset for the next operation.
Step 2: For the data points
Step 3: Randomly select a new data point as a new center based on a weighted probability distribution, where the probability of selection is proportional to the distance from the already selected centers.
Step 4: Repeat steps 2 and 3 until
(2) Node grouping stage
Step 1: In the
Step 3: After the iteration using steps 1 and 2 for updating, if the values of all cluster centers remain unchanged, stop the iteration; otherwise, continue the iteration.
Furthermore, the D-PBFT consensus algorithm requires periodic re-grouping of nodes since, in practice, over a long period of time, certain nodes’ positions may undergo significant changes, leading to noticeable changes in distances between nodes. Failure to re-group would greatly impact consensus latency.
During re-grouping, the system reconstructs the initial node set and uses the K-means++ clustering algorithm to re-group all nodes. In a specific period, the generated sets of groups and primary nodes are fixed and will only experience minor changes due to operations like primary node replacements, adding new nodes, or removing nodes, but significant changes will not occur.
The
In the primary node replacement policy, when selecting new primary nodes, their scores determine whether they are chosen. Nodes with higher scores have greater security and stability, making them more resistant to attacks. This approach enhances the security of primary node selection and reduces the risk of view changes, thus improving consensus efficiency. Consistently executing the consensus mechanism allows nodes that successfully achieve consensus to receive continuous score rewards. According to Bester and Guth, 31 consensus nodes with higher scores possess stronger security.
To ensure message consistency and accuracy under the same view and message sequence numbers, the traditional PBFT algorithm employs a three-phase protocol. 32 If a node is a Byzantine node, it may adopt different attack strategies, such as tampering with correct messages to make them untrustworthy or sending different messages to achieve its own objectives. With the development of DT technology, some enterprises may attempt to tamper with transaction information, turn customer complaints into positive evaluations, or forge transaction information and create false orders to gain unfair advantages. However, there is little opportunity to use consistency attacks to achieve their goals. Given this premise, the PBFT algorithm’s three-phase protocol has been improved and introduces a two-phase protocol, significantly enhancing the efficiency of the consensus process. The optimized consensus protocol algorithm flow is illustrated in Figure 2, showing significant improvements.
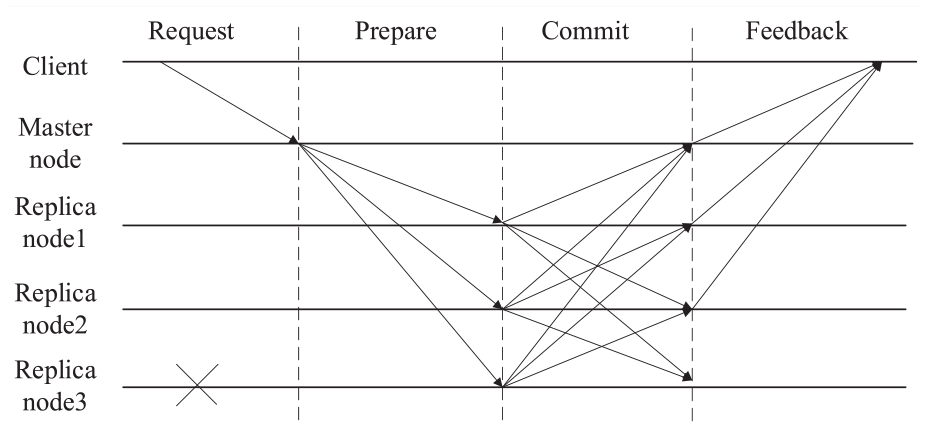
The figure illustrates the schematic diagram of the D-PBFT consensus algorithm flow.
Experimental results and analysis
In this section, the advantages of the D-PBFT algorithm will be further studied and compare it with the PBFT algorithm and the DDBFT algorithm to assess their effectiveness. The DDBFT algorithm is an improved version of the PBFT algorithm, combining the DPOS algorithm with PBFT to enhance PBFT’s dynamism, better meeting practical requirements.
Fault tolerance and security analysis
Fault tolerance analysis
For the PBFT algorithm, assuming there are
The D-PBFT algorithm and the DDBFT algorithm are essentially consistent with the PBFT algorithm. They are all based on the principle of majority rule to solve complex problems. To ensure the accuracy of the consensus cluster, the number of Byzantine nodes should be kept within one-third of the total number of nodes under extreme conditions to guarantee the reliability of the cluster. Even if the initial node set meets the required conditions, it is challenging for the DDBFT algorithm to achieve good fault tolerance because it is subject to strict constraints. The D-PBFT algorithm can group data more precisely based on the distances between nodes, ensuring data security. Furthermore, during the elimination and rotation process, it can effectively remove Byzantine-style nodes, making the final data set more reliable.
Security analysis
During the verification of message legitimacy by Byzantine nodes, they may add unauthorized messages to the message list, whereas non-Byzantine nodes carefully scrutinize messages to ensure their correctness and classify them as unauthorized messages. Replica nodes receive confirmation messages from other nodes but find that f + 1 messages have been detected as incorrect, requiring further corrections. Therefore, replica nodes will generate blocks that do not include the erroneous messages m′. In the feedback phase, the client receives f + 1 blocks without the erroneous messages m′ indicating that f + 1 nodes have reviewed the message m′ but did not approve it. This suggests that the primary node was Byzantine. At this point, the view change protocol will be automatically initiated to adjust the weights of each node in real-time and to reselect a new primary node.
If Byzantine nodes are used as replica nodes, an incorrect consensus may occur during the confirmation process, leading to inaccuracies in the information. Based on the maximum of f errors in consensus, it can be inferred that these incorrect consensus results will not be included in the block and will also be recorded, allowing the identification of replica nodes as Byzantine nodes. On the other hand, replica nodes may forcefully implant incorrect information into blocks. During the feedback process, the client will promptly detect any potentially erroneous blocks and handle them effectively to ensure data accuracy. After achieving consensus, if Byzantine nodes make improper decisions, they are likely to be replaced.
Through in-depth research on the D-PBFT algorithm, it can be concluded that the addition of Byzantine nodes, whether as primary nodes or replica nodes, ensures the secure operation of the system.
Comparative analysis of results
The initial conditions for the experiments were as follows: CPU: AMD Ryzen 7 4800H, 16 GB RAM, operating system: Windows 11 64-bit. Software environment: Python 3.8.8, Simpy 4.0.1. The experimental algorithms used were the PBFT algorithm, the DDBFT algorithm, and the D-PBFT algorithm proposed in this paper. This section analyzes the consensus delay of algorithms.
Consensus latency refers to the time required to achieve consensus from the moment a request is sent by the client within a specific period. A lower consensus latency allows the system to receive messages faster, thereby increasing throughput. Therefore, consensus latency is one of the important metrics for measuring blockchain performance. Its calculation formula is as follows:
In the formula,
In Experiment 1, the number of nodes was adjusted to 90, and the changes in consensus latency during the consensus process were observed using the D-PBFT algorithm.
Figure 3 illustrates the consensus latency variation curve of the D-PBFT algorithm, it can be observed that as the number of consensus rounds increases in the D-PBFT algorithm, the overall consensus latency shows a significant decrease, eventually stabilizing at 540 ms. At the end of a consensus cycle, consensus nodes are eliminated, making the latency throughout the entire consensus process more stable, rather than experiencing drastic fluctuations. When the consensus cycle ends, the new consensus latency will significantly decrease, making the entire process smoother.
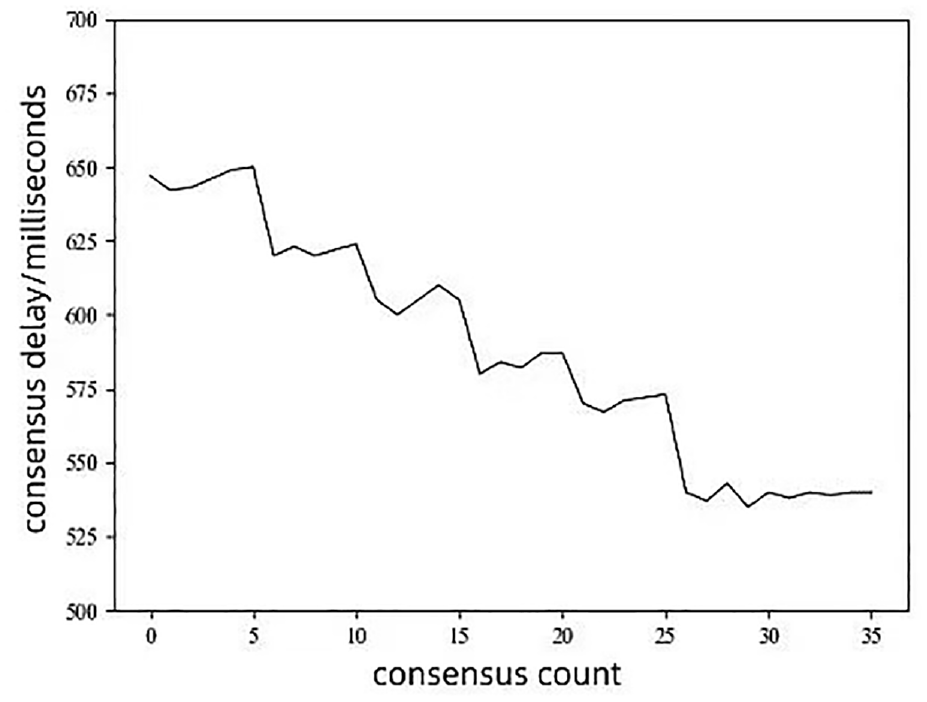
The consensus latency variation curve of the D-PBFT algorithm.
In Experiment 2, the number of nodes was adjusted to 15, 30, 45, 60, 75, and 90, divided into four groups to evaluate the average consensus latency of different algorithms. In the DDBFT algorithm, the primary node is selected through a voting process. The experimental results are shown in Figure 4, where the average consensus latency for each number of nodes on the x-axis is obtained from multiple consensus processes.
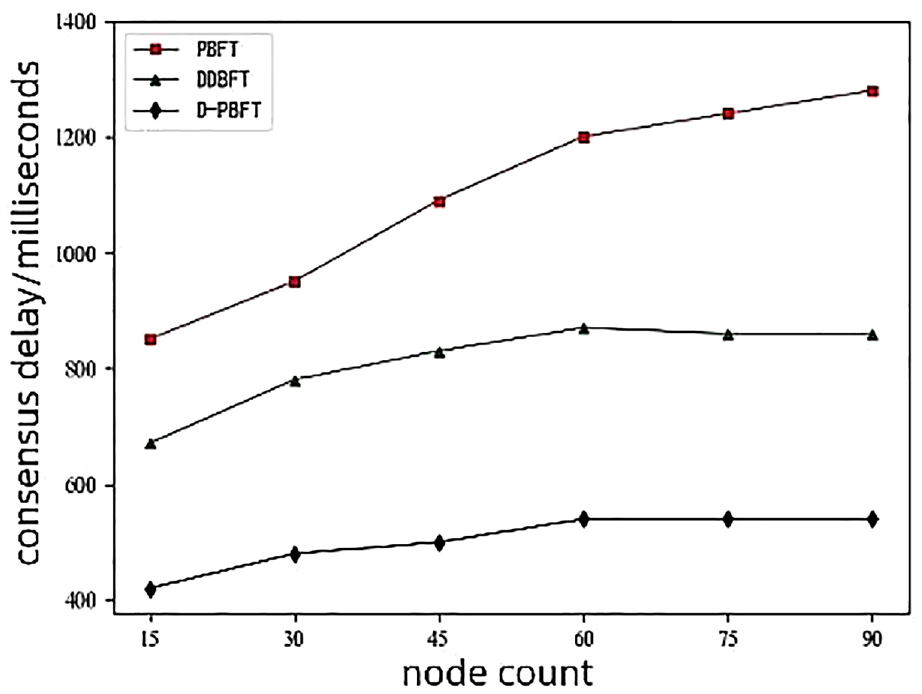
Consensus latency for different algorithms.
Figure 5 shows the comparison of consensus latency for different algorithms. It can be seen that as the number of nodes increases, the consensus time for all three algorithms also increases. Among them, the PBFT algorithm shows a continuous increase in time consumption. On the other hand, the DDBFT and D-PBFT algorithms are able to limit the size of the consensus cluster to within 60 nodes, resulting in no significant change in time consumption. The consensus nodes in the DDBFT algorithm are selected through voting, and their randomness leads to more noticeable data transmission delays, making their latency more apparent compared to the D-PBFT algorithm. After in-depth research, it is found that, regardless of the number of nodes, the D-PBFT algorithm consistently achieves the best consensus performance.
The compatibility between information sharing and blockchain.
Incentive strategy for DT data sharing based on blockchain technology
The core objective of information sharing is to gain benefits through the exchange and sharing of information while ensuring its security, authenticity, timeliness, and value, as well as guaranteeing ownership and value of the information. With the support of blockchain technology, consensus can be reached even among different participants. 34 However, despite the advantages of blockchain technology, there are still many individuals who have not actively joined the blockchain-based information sharing network, which is a noteworthy issue. This section aims to explore the DT data sharing model based on blockchain technology from a systemic perspective and proposes an effective incentive strategy to encourage active participation in information sharing, thereby enhancing the overall level of information sharing.
Coupling analysis of blockchain technology and information sharing
Blockchain technology is an automated, real-time, cross-network data processing method that better controls the access permissions of information, standardizes information, reduces risks in information sharing, and increases the cost of penalties. Through this approach, information sharing can be better managed and supervised, thereby improving the overall efficiency of the system.
Achieving permission control
Permission control of information primarily involves access rights for participating entities. With the advancement of technology, it is increasingly recognized that effective permission management is essential for secure and complete circulation of information, preventing misuse or over-issuance, protecting information integrity, and increasing the value of shared information resources. With the development of blockchain technology, there have been significant changes in information sharing models, as shown in Figure 5. Utilizing smart contracts and strict permission management effectively ensures data security and standardizes data storage and sharing. Through the use of blockchain technology, entirely new rules and systems can be created, and relevant information can be freely imported into the system, enabling intelligent management. By applying cryptographic principles of blockchain technology, user permissions can be more efficiently managed, further enhancing system stability and security, providing robust support for the system’s normal operation. Compared to traditional sharing models, the management capabilities of this technology have been significantly improved.
Achieving information standardization
Standardization is a process of categorizing, formatting, and transforming information into specific categories, formats, and conversion methods. It helps different departments and users at different levels to communicate and share information more conveniently. Information standardization involves not only information representation but also information processing, mainly concerning information processing techniques. However, true information standardization needs to be recognized and applied. Currently, the existence of various information standards makes it difficult for individuals, businesses, and organizations to effectively process large amounts of data and achieve efficient resource sharing.
On one hand, the lack of sound information standards and information sharing mechanisms leads to an unstable operation of the entire information service system, lacking relevant technical support. On the other hand, the absence of unified standards increases the cost of information utilization, severely affecting the effective dissemination and exchange of information. Blockchain technology provides a new approach to unifying information standards, allowing multiple participants to jointly participate in and maintain the formulation and implementation of information standards. 35 By using blockchain technology to build an information sharing system, all participants will be incentivized to work together to ensure the security and accuracy of the information database.
Reducing information sharing risks
Information sharing involves two main risks: first, privacy breaches can have severe consequences for participants, leading to substantial financial losses and exposure to false information; second, information sharing systems are susceptible to malicious attacks, misinterpretation, or the omission of critical data, leading to information theft or loss. Through distributed storage provided by blockchain technology, network attacks can be effectively prevented, reducing sharing costs and enabling automated contract terms, thus ensuring information security and preventing tampering and misuse. Additionally, blockchain technology can trace the source of information and provide verification, thereby preventing the sharing of false information. Therefore, blockchain technology can effectively guarantee the secure interaction and storage of information, greatly enhancing the efficiency and effectiveness of information sharing.
Enhancing incentives and penalties
To address the issue of “free-riders” and discourage deceptive information sharing behaviors, it is crucial to establish a comprehensive system of incentives and penalties to encourage participants to actively engage in information sharing. Blockchain technology offers advantages such as traceability, decentralization, and timestamps, allowing precise recording of participants’ actions. On one hand, breach of contract actions is challenging to tamper with or erase; on the other hand, the wide dissemination of such breaches can cause significant reputational damage, and the parties violating the agreement may incur substantial economic losses. By implementing effective punishment measures on a blockchain-based information sharing platform and appropriately penalizing entities that do not comply with privacy protection, information sharing can be effectively promoted, leading to a win-win situation for both parties.
Incentive strategy for DT data sharing based on blockchain technology
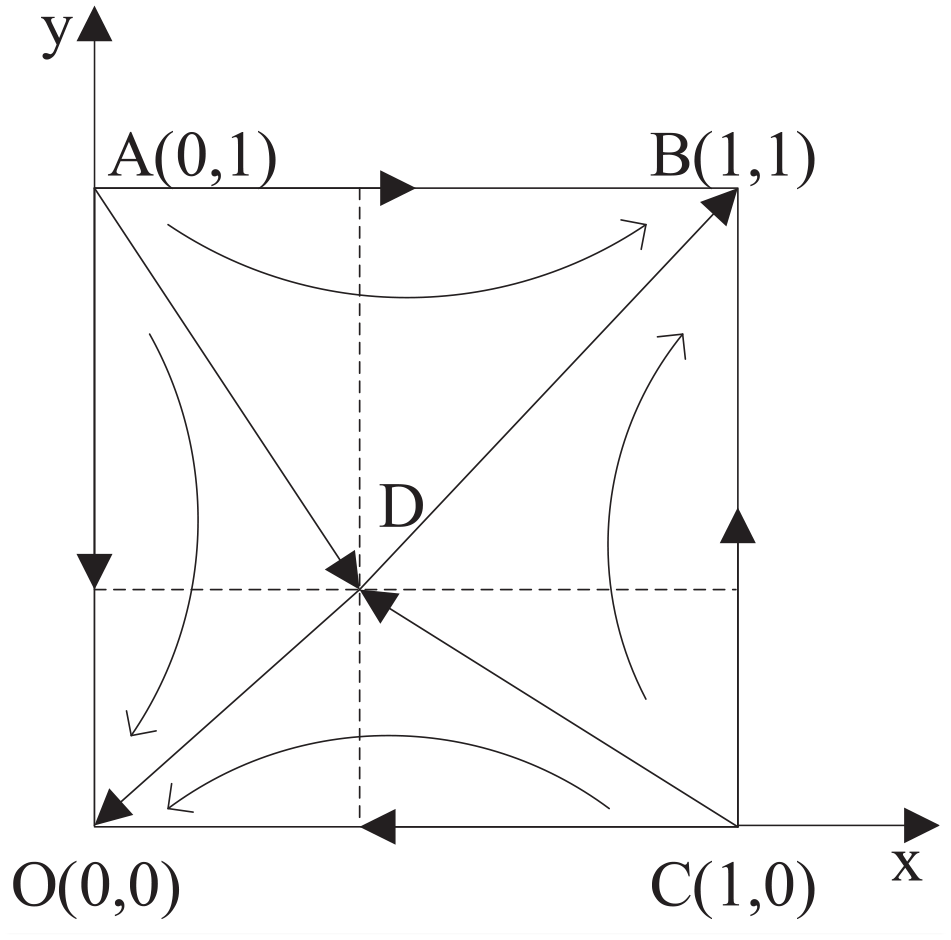
Reputation-based blockchain architecture for DT data sharing
Through the coupling analysis in Section 4.1, it is found that blockchain technology can effectively control information permissions, achieve information standardization, reduce information sharing risks, and increase the strength of penalties for violations. With the advancement of technology, more and more scholars are adopting blockchain technology to realize data sharing and exchange, as shown in Figure 6, where parties can share their own information based on relevant rules and protocols.
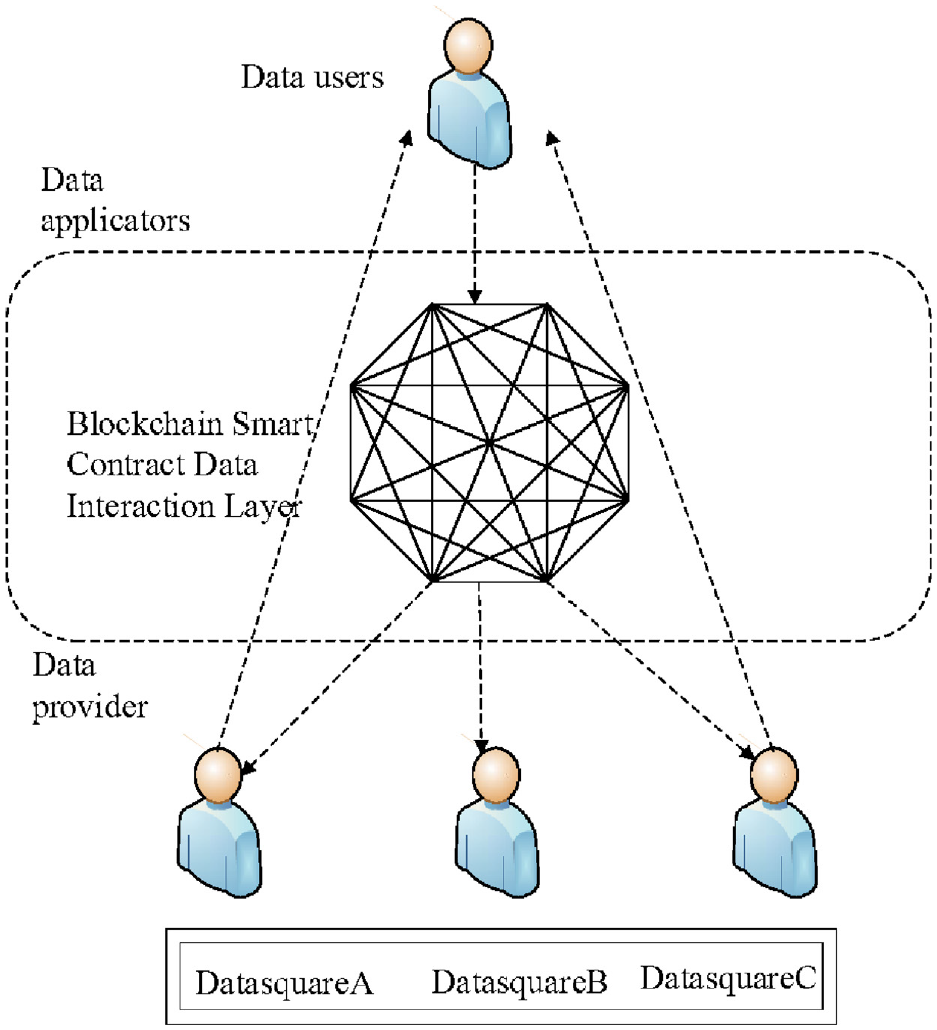
Blockchain-based data sharing architecture.
It can be observed that the blockchain-based DT data sharing model is influenced by various factors, including technological support, cost control, and risk management. Blockchain technology may lead to privacy breaches, making transactions unfair. Moreover, due to the decentralized nature of blockchain technology, effective management may be lacking. Despite the development of blockchain technology, many challenges still exist, such as low enthusiasm among initial participants for information sharing and the impact on the accuracy of some information. Adopting a scientific management approach and establishing a robust incentive mechanism to encourage all parties to participate in information sharing has become a pressing matter.
Traditional incentive methods include monetary rewards, reputation incentives, “tit-for-tat” rewards, and other forms of support. Reputation is a trust relationship established based on repeated games, which can incentivize those who adhere to agreements and act honestly to make the right decisions. Based on Telser, 36 reputation can serve as an effective incentive tool to prevent and reduce opportunistic behaviors.
As early as the 18th century, the significance of reputation was discussed by the economist Adam Smith, but in-depth research on this topic was not conducted. In the 1980s, people began to recognize the value of reputation and incorporated it into the field of economics. Economists such as Milgrom, North, Weingast, Greif, and Kandori combined the theories of new institutional economics and game theory, providing substantial support for the study of reputation theory and laying a vital theoretical foundation for its development. Reputation theory has since evolved into various branches, such as reputation trading theory, reputation information theory, and reputation network theory, which have made significant contributions to the development of reputation theory. However, due to the limited scope of this paper, a detailed explanation of these theories is beyond its capacity, and only the importance of reputation in corporate management is discussed.
Fama 37 and Holmstrom 38 were among the first to view reputation as a potential incentive mechanism. Fama believed that in real life, the “agency problem” (referring to the phenomenon where, due to uncertainty and information asymmetry, agents may deviate from the principal’s objectives, thereby harming the principal’s interests) is not insurmountable. As time goes by, the importance of reputation cannot be ignored, and any fraudulent behavior will face severe penalties. Therefore, in a competitive market, to maintain a good reputation, agents must continuously work to uphold their reputations, even in the absence of clear rewards, they will still adhere to the principle of integrity. 39
Holmstrom further explored the concept proposed by Fama and mathematically proved that reputation can replace explicit incentives in a competitive market. Holmstrom believed that in the early stages of a career, agents are more inclined to work hard as this is the critical period for accumulating reputation. As the agent’s career matures, past efforts and contributions will become symbolic, indicating that the agent is trustworthy. At this point, with this reputation, the agent will be able to receive higher expectations and more substantial returns from the principal.
The rationality of reputation incentives has been widely recognized, but there are also some negative effects. For example, if an agent adopts improper means to pursue short-term benefits, they may not only lose long-term cooperative opportunities but also create a negative impression on others, leading to a decline in the reputation of the entire industry. In this case, it is necessary to introduce punishment measures to protect the principal’s rights and prevent agents with damaged reputations from engaging in illegal activities again.
In conclusion, reputation is a complex concept, encompassing both positive factors and negative effects. Based on this understanding, this paper proposes a reputation-based blockchain transaction architecture, which effectively supports information sharing of DT data, as illustrated in Figure 7.
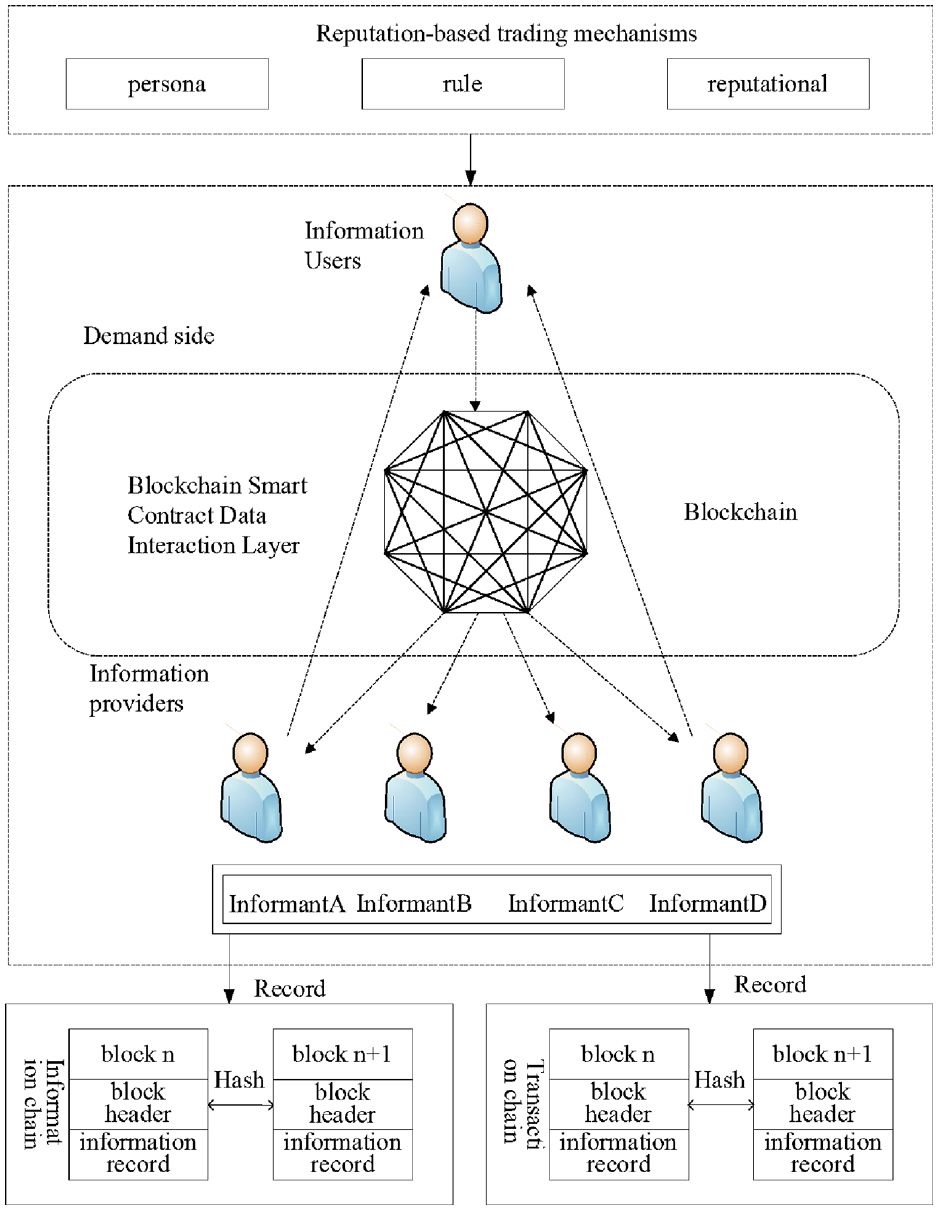
Reputation-based blockchain transaction architecture for DT data sharing.
This paper aims to combine the reputation factor and construct a reputation trading mechanism by comprehensively considering key influencing factors such as the amount and quality of information provided by participating entities. According to Song et al., 40 the reputation-based blockchain smart contract serves as the foundation to achieve automated transactions between participating entities while preserving user control and ownership. It allows information users to publish information requests on the chain, and information providers respond according to the sharing rules. Through a dynamic incentive mechanism, information exchange among all participants is promoted.
During the process of information sharing, participants should fully respect each other’s rights and openly and transparently share relevant information to ensure information security and effectiveness. Blockchain technology can make information sharing among participants more convenient, which can be achieved through three steps: matching transaction partners, creating smart contracts, and executing smart contracts.
Matching transaction partners
In the initialization stage, a blockchain-based decentralized network will be created. Users can obtain a unique identification and key by uploading shared information and register their personal information. Users can decide whether to conduct transactions based on their needs. When information requesters send sharing requests to the blockchain system, these requests will be recorded on the chain and need to provide detailed descriptions, including the required information type, size, etc., for the blockchain system to effectively process and analyze these requests. The system will use an information retrieval mechanism to search for information relevant to the request from the chain and then disseminate this information to other participants in the form of tasks. Through consensus mechanisms, the best transaction partner is selected from numerous information providers to achieve the optimal transaction result.
Creating smart contracts
After determining the transaction partner, the system will create a contract for the successfully matched transaction partner based on their needs. The contract includes terms that both parties must adhere to, as well as corresponding rewards and penalties. Based on consensus, a smart contract is created according to the agreed-upon terms, and its chain code is encapsulated. Each participant must add their private key to the chain code package. Finally, by installing the information sharing chain code package, alignment instantiation is achieved.
Executing smart contracts
When participating entities issue information sharing requests, the chain code will be activated for relevant information exchange. At this point, the smart contract is activated and automatically executed according to the specified rules. With the support of blockchain technology, all transactions are recorded on a shared ledger, and each transaction is signed according to the endorsement policy of the chain code to ensure its reliability and security. Blockchain technology can record and track transactions performed in chronological order. Through the information sharing platform, participants’ credit records are recorded in the blockchain ledger, and these records are updated in real-time based on the participants’ reputation scores. During the information sharing process, all transaction data is divided into blocks and confirmed for authenticity through global dissemination. After rigorous verification, the data is stored in the blockchain system for sharing.
Incentive strategy for DT data sharing based on blockchain smart contracts
Based on the reputation-oriented blockchain architecture for DT data sharing discussed above, this paper proposes an incentive strategy for DT data sharing based on blockchain smart contracts, as illustrated in Figure 8.
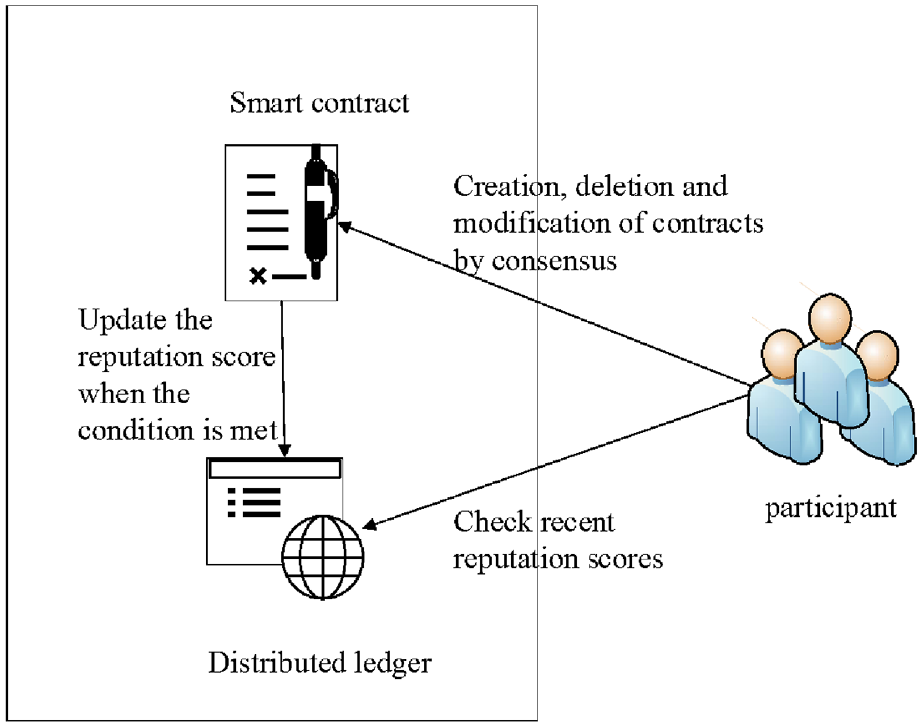
Incentive strategy for DT data sharing based on blockchain smart contracts.
In this paper, the reputation of participants was quantitatively evaluated by comprehensively considering important factors such as the quantity and quality of the information they provided. Specifically:
(1) Leveraging the advantages of blockchain consensus algorithms, the reputation of participants was evaluated based on the size and quality of the information they provided. This process relied on blockchain smart contract technology, achieving distributed and automated reputation management.
(2) Using blockchain technology to quantify reputation allows for better control and management of people’s behavior. Based on historical records, the reliability of each participant is assessed, and corresponding rewards are provided to enhance their reputation.
(3) If the reputation criteria are adopted, the reputation ratings in the distributed accounts will be automatically adjusted by smart contracts. Using blockchain technology, a clear rule framework can be established, and a set of strict standards can be provided to ensure that everyone acts according to these rules. To ensure information security and effectiveness, reputation assessment should be an essential part of rewarding participants.
Quantifying reputation through blockchain technology offers significant advantages:
Firstly, due to the application of blockchain technology, reputation scores can be tracked in real-time and are difficult to tamper with.
Secondly, smart contracts enable automated reputation management, better protecting and enhancing reputation.
Additionally, this quantification method can simulate trust situations in the real world. Through the evaluation of participants’ reputation in blockchain technology, the fairness of information sharing can be improved, and future reputation scores can serve as evaluation criteria.
Reputation scores are an essential incentive factor, used to measure the effectiveness of information sharing transaction matching or smart contract pre-trigger conditions. Through quantitative metrics, the reputation incentives for participating entities can be calculated, thus improving their performance.
This section thoroughly explores the blockchain-based DT data sharing model. Firstly, blockchain smart contracts can provide effective technical support for information sharing. Secondly, the correlation between blockchain technology and information sharing is analyzed. On the basis of considering the influence of reputation, an in-depth analysis of the incentive strategy for information sharing based on blockchain smart contracts is conducted, aiming to achieve better results.
Construction of an evolutionary game model for DT data sharing
This section focuses on the construction of an evolutionary game model for DT data sharing. Firstly, an evolutionary game model considering reputation incentives and a model without reputation incentives were established. Then, the dynamic evolution process of various influencing factors in information sharing is analyzed, and the impact of different incentive levels on participants’ sharing decisions is explored.
Problem description and basic assumptions
Problem description
Due to a lack of willingness among participants to share data, blockchain technology faces potential risks, and effective measures must be taken to regulate these risks. Therefore, it is necessary to devise reasonable incentive mechanisms to actively guide participants and mitigate the externalities caused by imbalanced interests. The influence of external factors has led to a lack of enthusiasm among many entities new to blockchain data sharing, resulting in partial data sharing and deviations in information sharing. This paper aims to use reputation as an effective incentive mechanism to suppress and reduce opportunistic behavior, and quantitatively analyze various factors affecting information sharing and the quantity and quality of information provided by participants.
Evolutionary model assumptions
This study focuses on two enterprises, Enterprise 1 and Enterprise 2, and constructs an evolutionary game model to explore their data sharing behaviors, defining their strategy sets as follows: DT data sharing and No DT data sharing. The meaning of the notations can be found in Appendix B. The following assumptions are made for this evolutionary game model:
H1: The participants in the game are only Enterprise 1 and Enterprise 2. Neither of them has the ability to predict the future, but they can make rational judgments, and their strategy choices are dynamic, affecting each other.
H2: Let
H3: Enterprise 1 and Enterprise 2 consider only the magnitude of benefits resulting from different strategies in their decision-making, without considering other factors.
H4: By analyzing the shared data, enterprises can discover valuable information and achieve direct economic benefits by enhancing their data mining capabilities. This gain is influenced by two factors:
H5: When both parties use shared data for cooperation, they can obtain additional benefits resulting from innovation and data fusion, which are related to the complementarity of DT data and the trust between data-sharing parties. These benefits not only improve efficiency but also help enterprises realize greater business potential. The synergistic benefits of data sharing obtained by both parties are
H6: The cost of sharing DT data can be considered from two aspects: time and material. The time cost refers to the time spent by the data-sharing party in the process of data collection, organization, experimentation, and verification. The material cost refers to the loss incurred by the data-sharing party due to the non-replicability of knowledge.
H7: Positive incentive coefficients encourage both parties to share data, while negative incentive coefficients discourage those who refuse to share data. Implementing effective reward mechanisms and penalties ensure sustainable sharing of DT data. Data sharing may bring various challenges, such as unpredictable risks and data misuse. The data sharing risk losses incurred by both parties are
H8: When both Enterprise 1 and Enterprise 2 choose not to share data, neither party gains any benefits, and their gains are 0.
H9: Considering reputation incentives, enterprises that share data will gain better reputations, and the reputation benefits resulting from the reputation effect are denoted as E.
Construction of the evolutionary game model for DT data sharing without reputation incentives
Payoff matrix for game participants
Based on the assumptions mentioned earlier, in the absence of reputation incentives, Table 1 shows the payoff matrix for the data sharing game between the two parties.
Payoff matrix for data sharing game without reputation incentives.
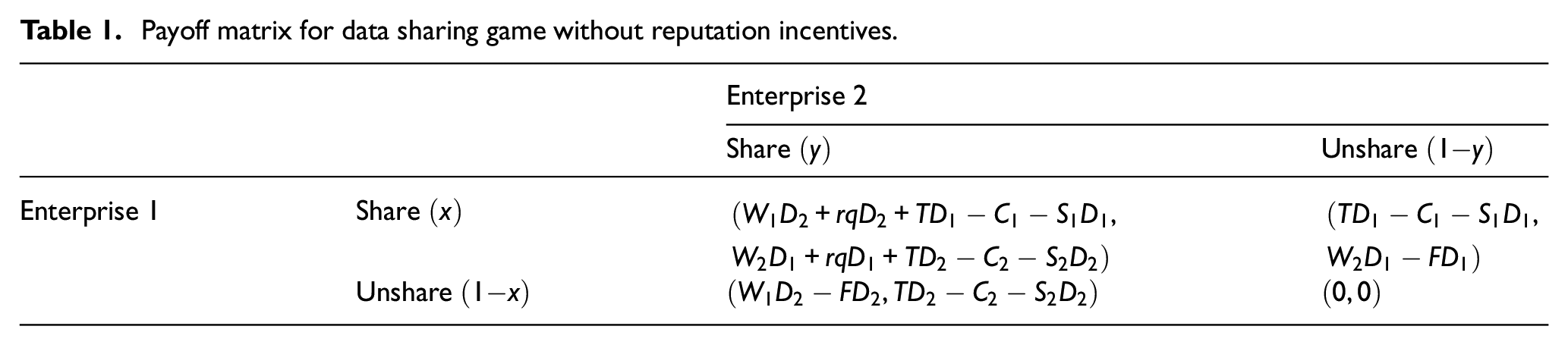
When both parties choose to share data, their payoffs are calculated as Direct Benefits + Synergistic Benefits + Positive Incentives − Data Sharing Costs −Data Sharing Risk Losses.
When both parties choose not to share data, their payoffs are both 0.
When Enterprise 1 shares data, and Enterprise 2 does not share data, Enterprise 1’s payoff is Positive Incentives − Data Sharing Costs − Data Sharing Risk Losses, while Enterprise 2’s payoff is Direct Benefits − Negative Incentives.
When Enterprise 1 does not share data, and Enterprise 2 shares data, Enterprise 1’s payoff is Direct Benefits − Negative Incentives, while Enterprise 2’s payoff is Positive Incentives − Data Sharing Costs −Data Sharing Risk Losses.
Evolutionary stable strategy analysis
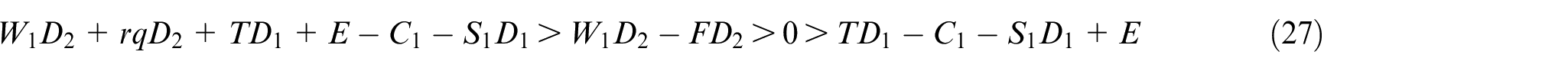
Based on the payoff matrix, it can be inferred that:
When Enterprise 1 chooses to share data, its expected payoff is:
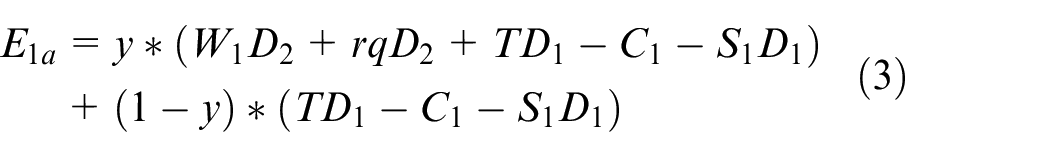
When Enterprise 1 chooses not to share data, its expected payoff is:

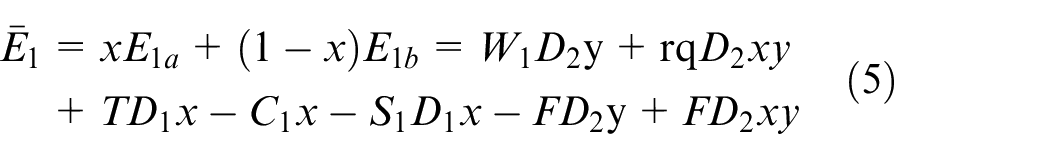
Its average expected payoff is:
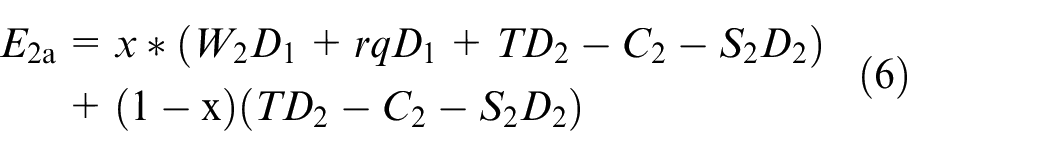
The expected payoff and average payoff for Enterprise 2 are as follows:

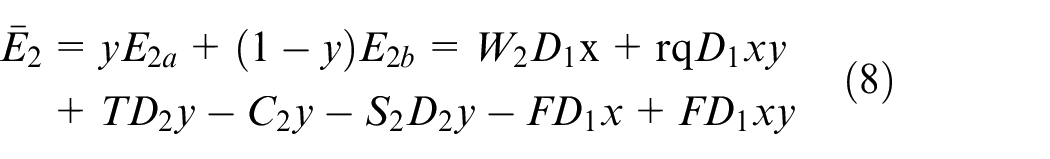
Based on this, the replicator dynamics equations for Enterprise 1 and Enterprise 2 are established as follows:
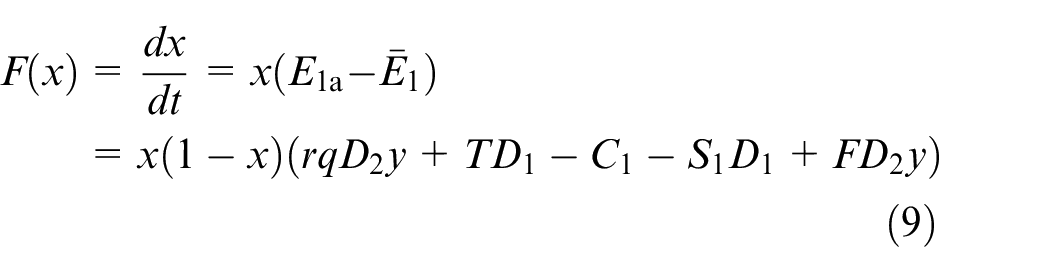
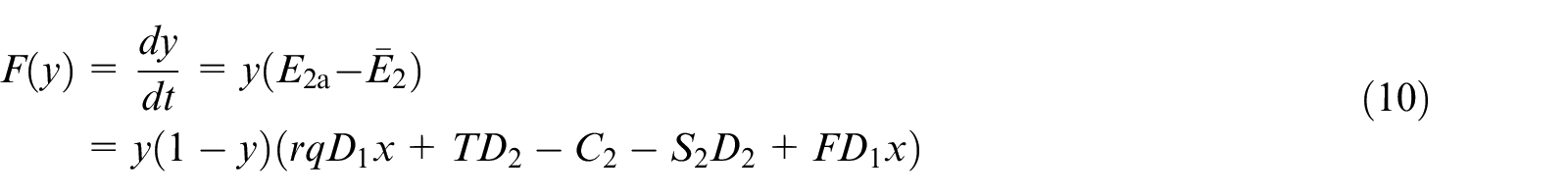
Let
By taking partial derivatives of
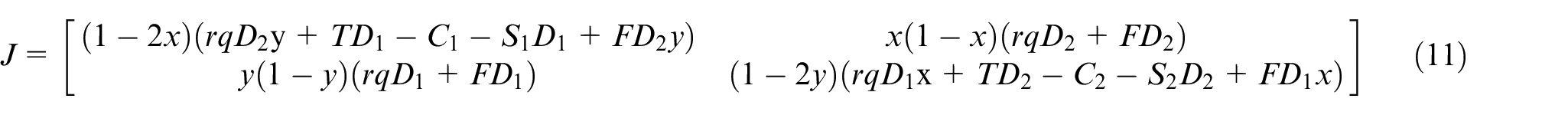
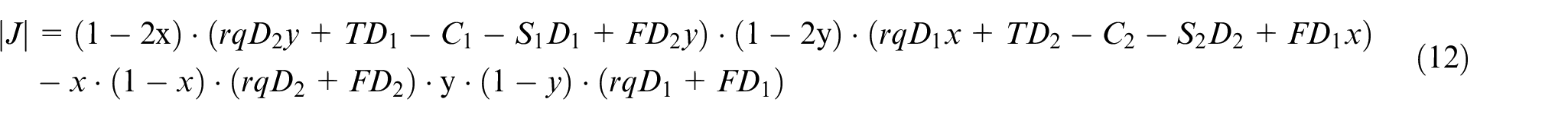
The determinant of the Jacobian matrix is:
By studying the payoff matrix and equilibrium points of the enterprise information sharing game, we can assess the stability of data sharing in the absence or presence of a trust mechanism.
When there is no trust mechanism between enterprises, opportunistic behavior and the misappropriation of others’ achievements may occur if one enterprise does not comply with the data sharing system. In this scenario, even if the cost of not sharing data is minimal or non-existent, the other party may still gain more benefits by not sharing, leading to corresponding losses for the sharing party.
Enterprise 1:
Enterprise 2:
As evident from the above equations, it can be observed that
For point
After substituting the four equilibrium points into the Jacobian determinant, the stability analysis results are obtained as shown in Table 2. If the sign of the Jacobian matrix determinant is greater than 0, and the sign of the trace of the determinant is less than 0, it indicates that the point has good equilibrium stability and can be considered as an evolutionary stable strategy.
Local stability analysis results of data sharing between enterprises without trust mechanism.
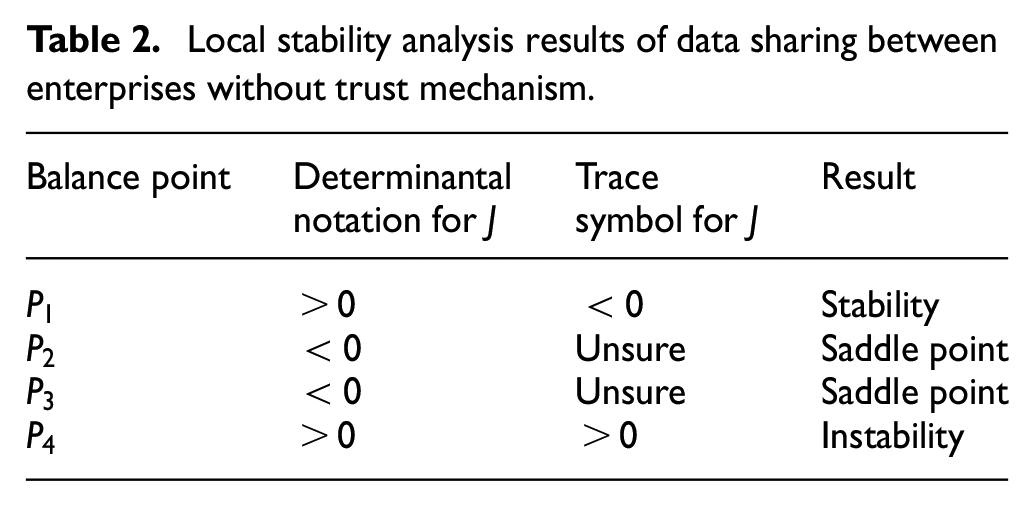
For point
The determinant of matrix
For point
The determinant of matrix
For point
The determinant of matrix
For point
The determinant of matrix
According to Table 2, point
The dynamic evolutionary process of enterprise data sharing is depicted using a phase trajectory diagram in Figure 9. After prolonged interactions, both Enterprise 1 and Enterprise 2 ultimately avoid sharing information as much as possible, indicating that the reputation incentive is ineffective within this range.
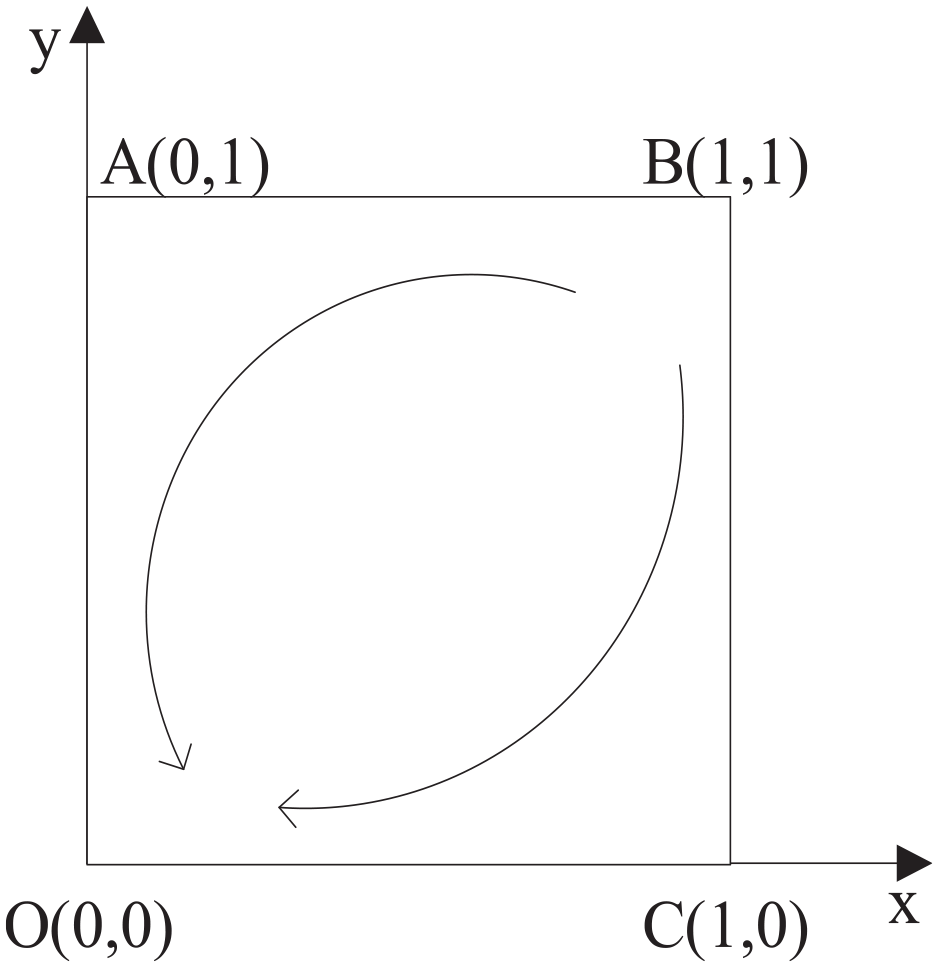
Evolutionary game phase diagram of enterprise data sharing without considering reputation.
Construction of the evolutionary game model for DT data sharing with reputation incentives
Payoff matrices for the game participants
Based on the assumptions stated earlier and considering reputation incentives, the payoff matrices for the participants in the data sharing game are presented in Table 3.
Payoff matrices for data sharing game with reputation incentives.
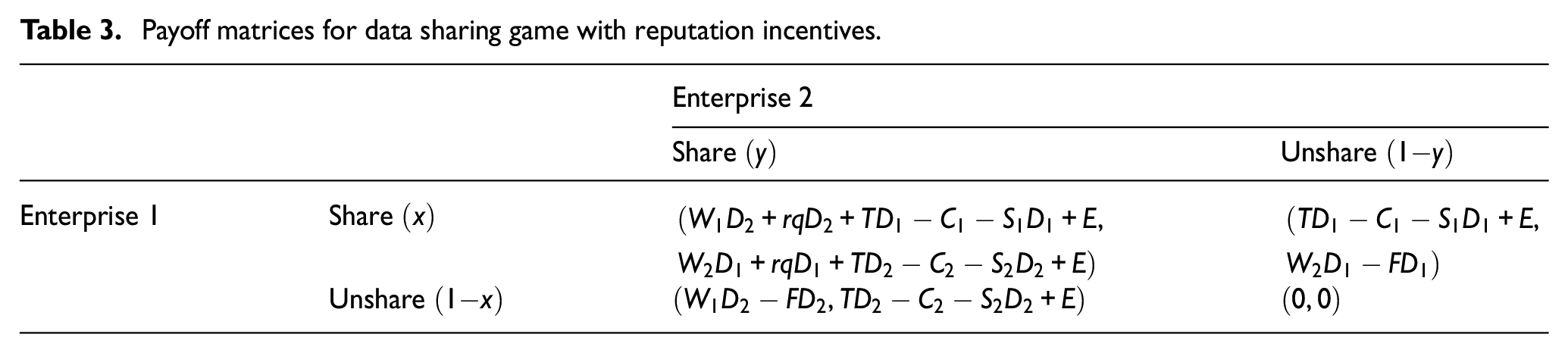
When both parties choose to share data, their respective payoffs include direct benefits, cooperative benefits, positive incentives, reputation benefits, minus data sharing costs, and data sharing risk losses.
When both parties choose not to share data, their payoffs are both 0.
When Enterprise 1 shares data while Enterprise 2 does not share data, Enterprise 1’s payoff consists of positive incentives, reputation benefits, minus data sharing costs, and data sharing risk losses, while Enterprise 2’s payoff is only the direct benefits minus negative incentives.
When Enterprise 1 does not share data while Enterprise 2 shares data, Enterprise 1’s payoff includes only the direct benefits minus negative incentives, and Enterprise 2’s payoff comprises positive incentives, reputation benefits, minus data sharing costs, and data sharing risk losses.
Analysis of evolutionarily stable strategies
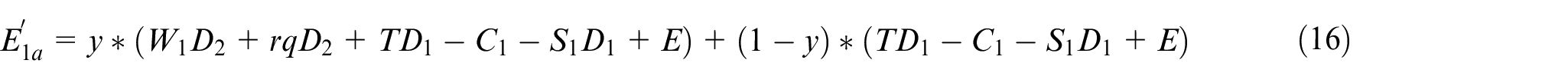
Based on the payoff matrices, it can be observed that:
When Enterprise 1 chooses to share data, its expected payoff is:
When Enterprise 1 chooses not to share data, its expected payoff is:

The average expected payoff is:
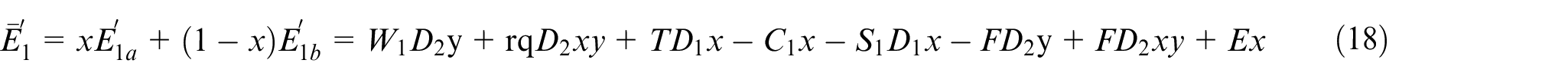
Enterprise 2’s expected payoff and average payoff are as follows:
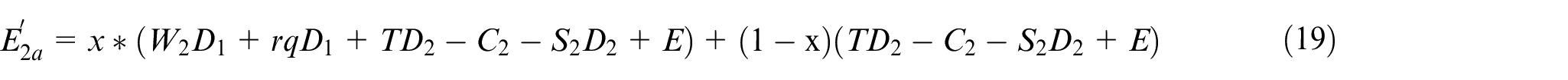

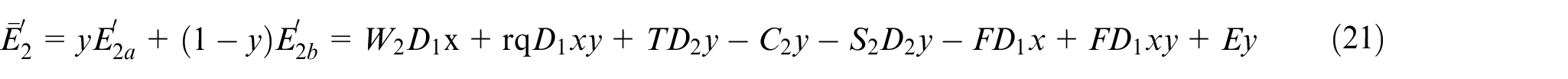
Thus, the replicator dynamic equations for Enterprise 1 and Enterprise 2 are established as:
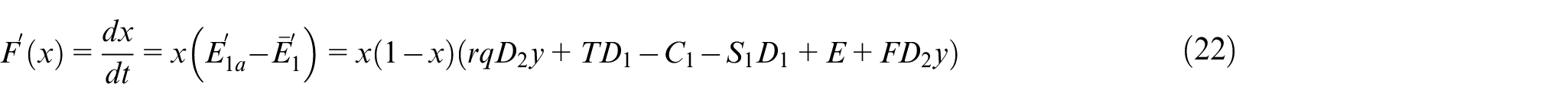
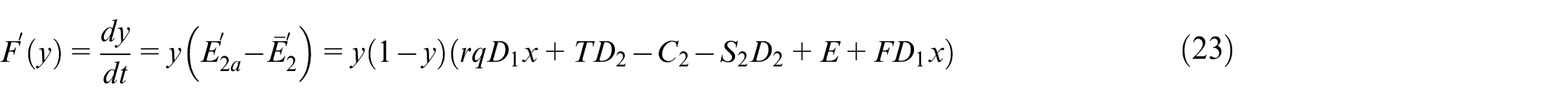
Let
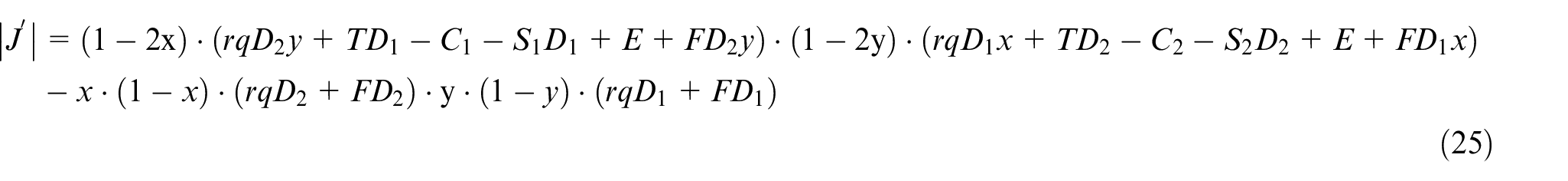
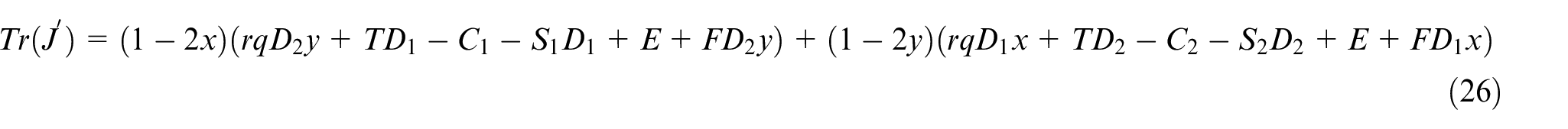
By taking partial derivatives of
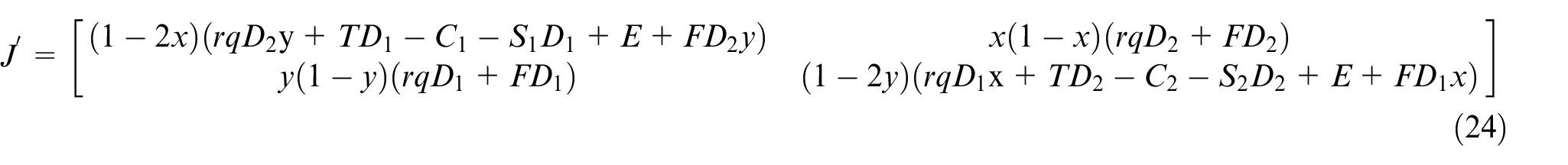
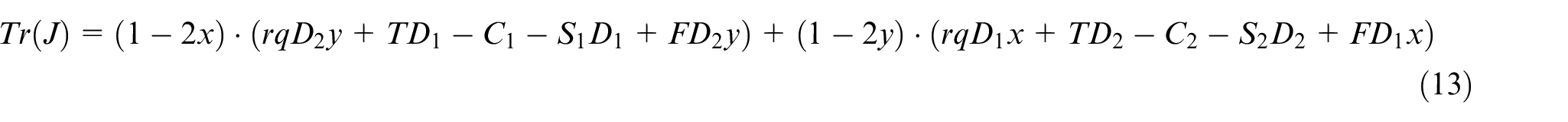
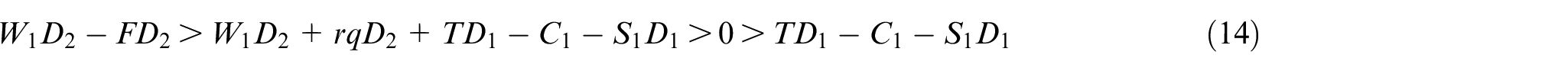
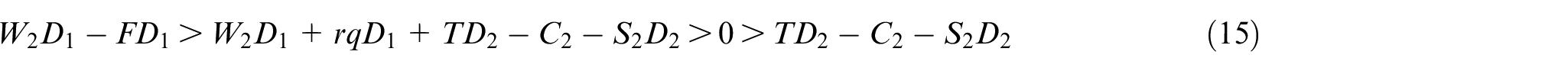
The determinant of the Jacobian matrix is:
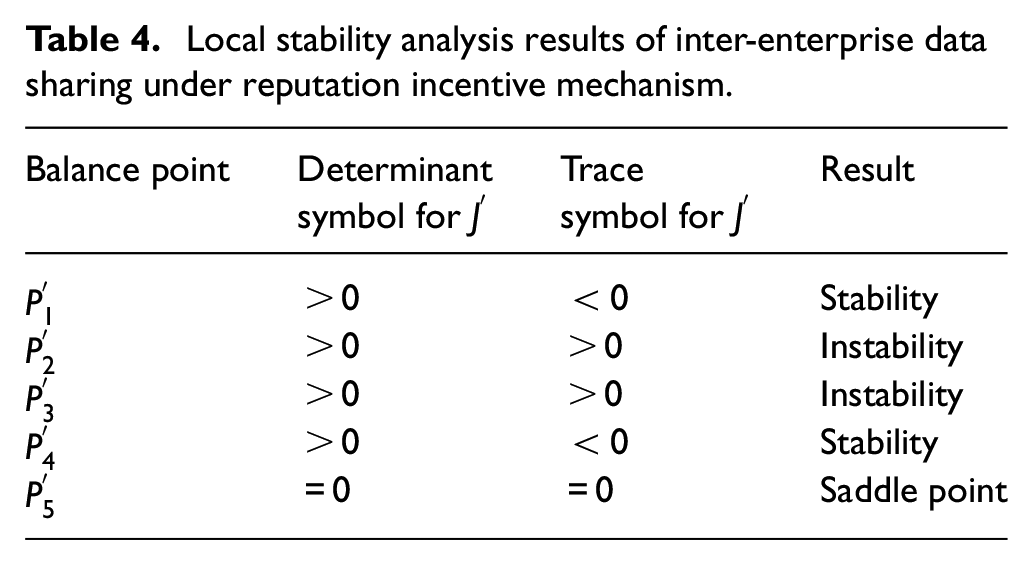
When enterprises establish an effective reputation incentive mechanism, both parties can engage in sharing more actively. This helps in establishing mutual trust and places a greater emphasis on their own reputations, leading to a more proactive assumption of social responsibility. For Enterprise 1, the benefits of sharing outweigh those of not sharing, and the minimum benefit is gained when the counterpart doesn’t share while they do. Thus, it can be deduced that:
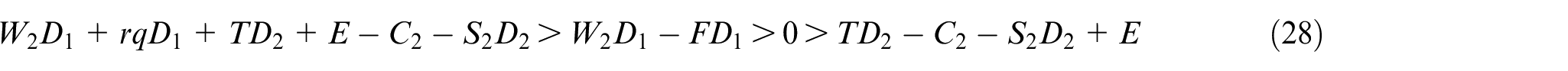
Using the above equations, the five equilibrium points can be substituted to determine whether they are in stable states. The results are presented in Table 4.
Local stability analysis results of inter-enterprise data sharing under reputation incentive mechanism.
Regarding point
Regarding point
Regarding point
Regarding point
Regarding point
As seen from Table 4, points
The dynamic evolution process of enterprise data sharing is depicted through a phase trajectory diagram in Figure 10. When the initial state of enterprise data sharing is in the lower-left region represented by point
Evolutionary phase diagram of enterprise data sharing with reputation consideration.
Due to variations in the data capabilities and technological levels among different enterprises, their ability for data communication and sharing also differs. Strengthening data exchange between enterprises can promote collaboration, greatly enhance synergy, and stimulate greater enthusiasm for data sharing. As the incentive coefficient increases, the positive effects of data sharing, along with a strong reputation, will lead to a broader scope of shared data. When the sum of effective rewards and penalties exceeds the cost of sharing, data sharing becomes more feasible, transforming into a long-term and sustainable strategy. Incentives encompass not only material rewards but also the recognition, trust, and respect from other enterprises.
While other factors remain constant, higher costs of data sharing for enterprises lead to lower likelihood of sharing. With the continuous growth of data volume and emergence of various data types, tasks from screening and organization to transmission demand significant time and effort. To efficiently utilize these resources, enterprises should take measures like establishing a comprehensive data sharing platform for user access. This effectively reduces the complexity of data integration and ensures successful data sharing.
Case study
Case introduction
The application scope of DT technology encompasses two main categories: end users and original equipment manufacturers (OEMs), catering to different needs.
For end-user DTs, the entity designing and applying the DT is the same enterprise. Examples of typical customers for DTs include space agencies, aircraft manufacturers, and metallurgical companies. These customers utilize large-scale equipment such as airplanes, rockets, and blast furnaces. The cost of a complete DT solution can range from millions to billions of dollars. Developing such solutions presents significant research and development challenges for companies. Thus, leveraging DT technology to reduce development costs and enhance equipment reliability and lifespan through virtual models offers a more efficient solution. With technological advancements, many aerospace devices require stringent checks and testing in virtual environments to ensure proper functionality. As new equipment is built and various sensor technologies are employed, real-time feedback through multiple sensors greatly improves equipment performance and contributes to reduced operational costs.
For OEM DTs, the entity constructing and applying the DT comes from different companies. For instance, typical representatives of OEMs include machinery manufacturers from industries like food and beverages, and textiles. The physical entities in DTs are machines such as blow molding machines, injection molding machines, and sewing machines. The application of the “sharing” mode introduces a new approach to propagate DT technology. This enables various companies to share similar equipment, effectively reducing investments. Post-production, each device possesses a unique DT derived from a common “parent,” yet exhibiting distinct characteristics. They accurately record the operational status and parameters of each device under various conditions, providing robust support for maintenance and operation.
As technology advances, the prospects for DT technology are vast. Their high reusability and scalability are expected to lead to significant cost reductions with expanding scales, potentially saving hundreds of dollars or more. The corresponding return on investment could even be measured in “days.” Users can pay fees based on their requirements, and the investment payback period is short, leading to immediate benefits.
Some enterprises have already put this practice into action. Taking the example of Factory J’s DT data sharing, simulations were conducted using actual data to analyze evolutionary game models without and with reputation incentives.
Simulation analysis of evolutionary game for non-reputation-incentivized DT data sharing
Building upon the analysis from the previous section, this section employs MATLAB software to perform numerical simulations on the evolutionary game model of DT data sharing without considering reputation incentives. The results are presented in graphical form, illustrating the evolving behavior of data sharing among companies under various parameters. Assuming for Company 1, the data sharing quantity
(1) Trustworthiness
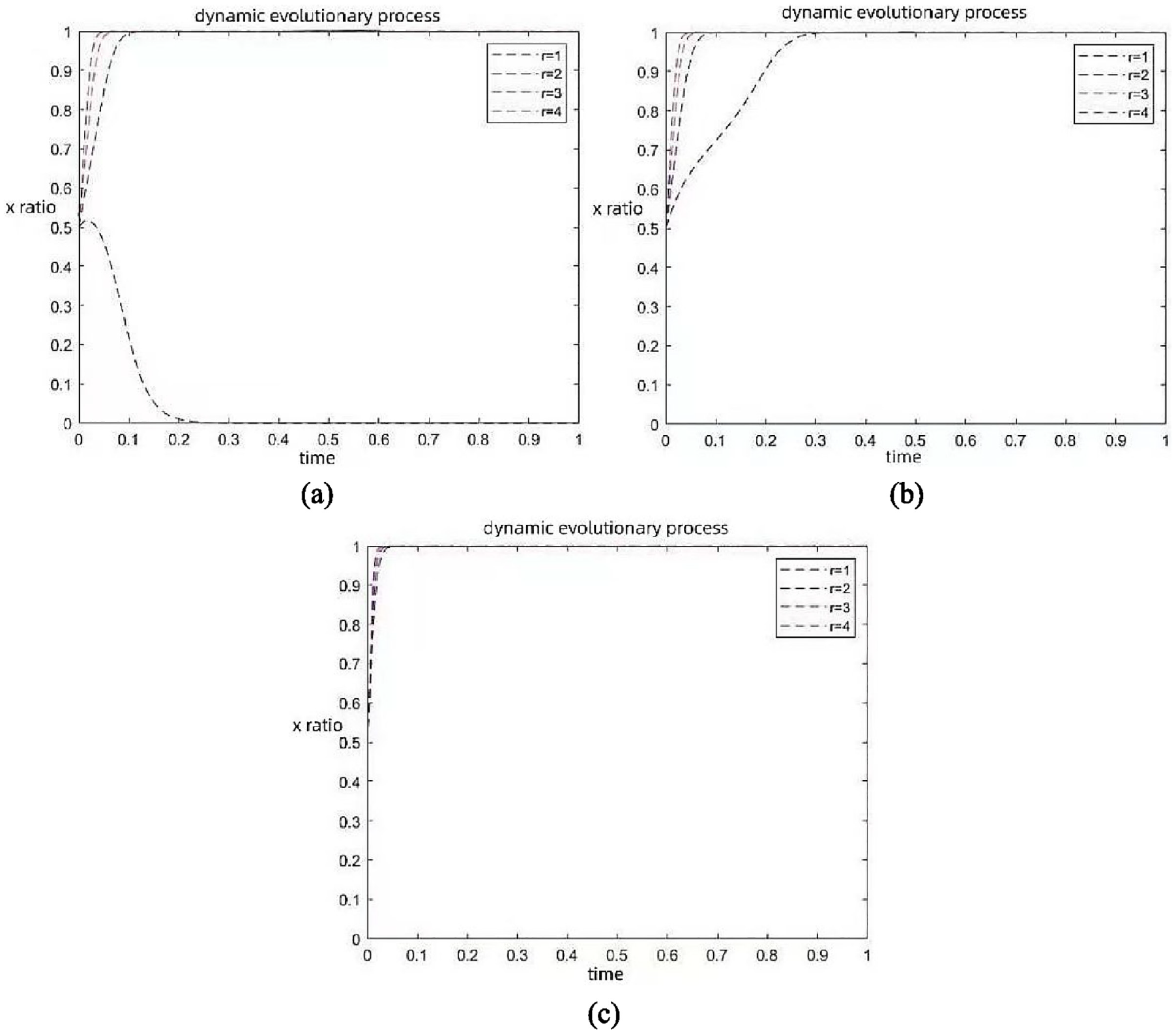
By increasing trustworthiness while keeping other factors stable, the changes in the values of
(2) Data complementarity
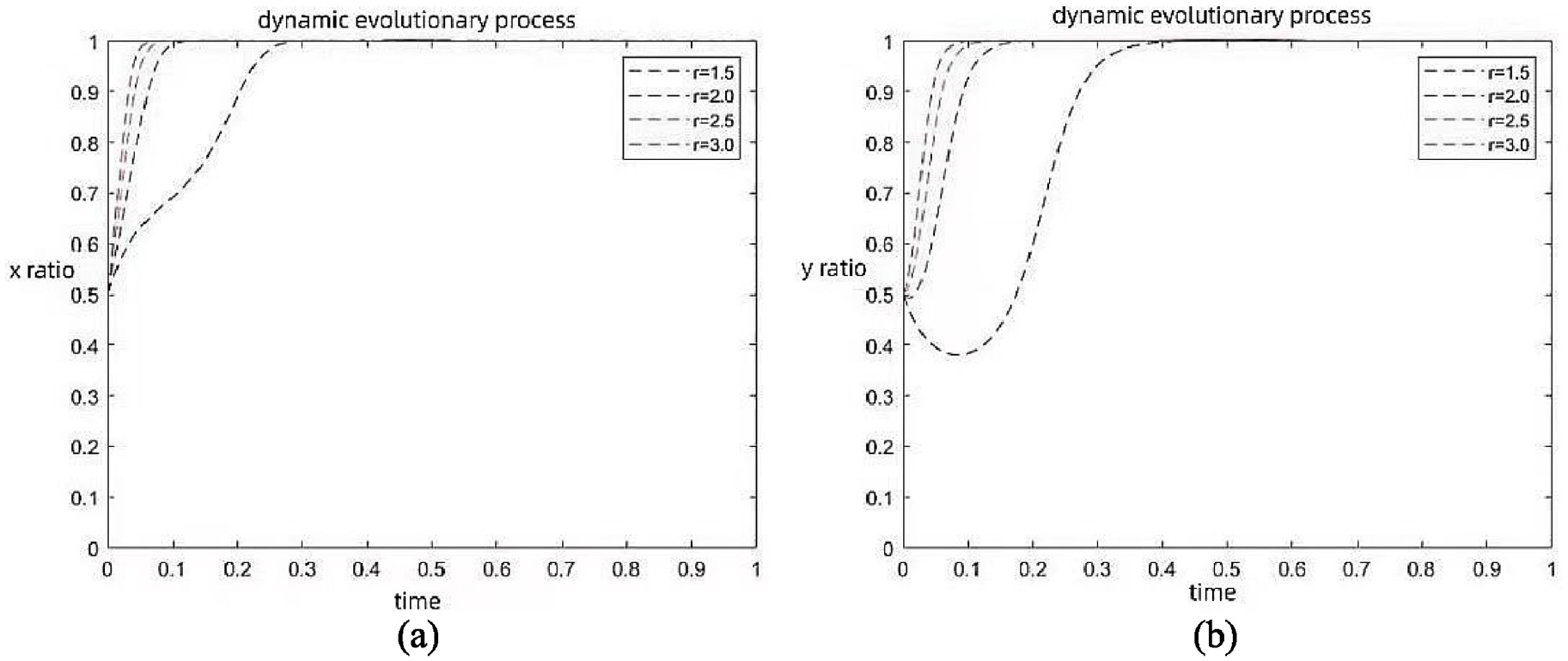
Influence of trustworthiness on evolutionary path of inter-company sharing behavior: (a) company 1’s sharing behavior and (b) company 2’s sharing behavior.
By increasing data complementarity while maintaining other parameters stable, the changes in the values of
(3) Positive incentive coefficient
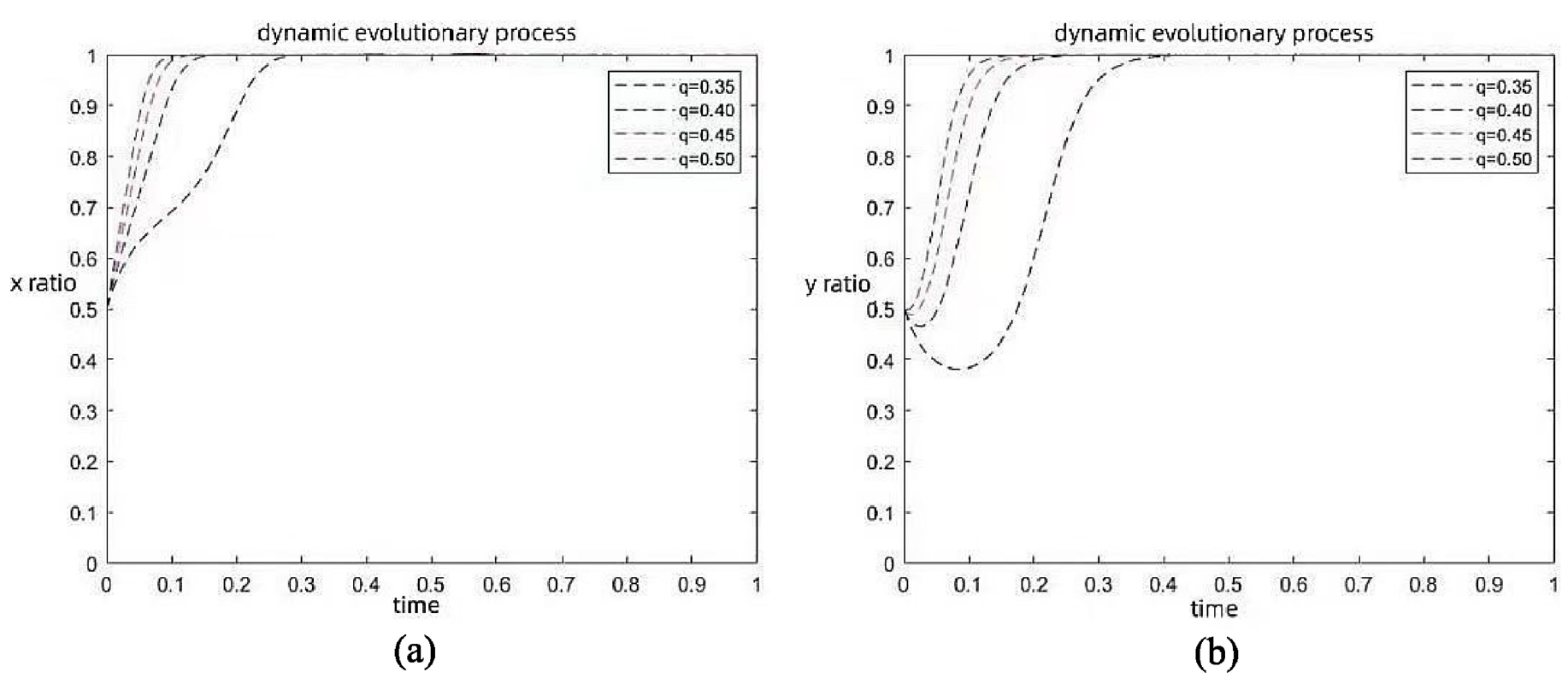
Influence of data complementarity on evolutionary path of inter-company sharing behavior: (a) company 1’s sharing behavior and (b) company 2’s sharing behavior.
By increasing the value of the positive incentive coefficient while keeping other parameters unchanged, the changes in the values of
(4) Data sharing cost
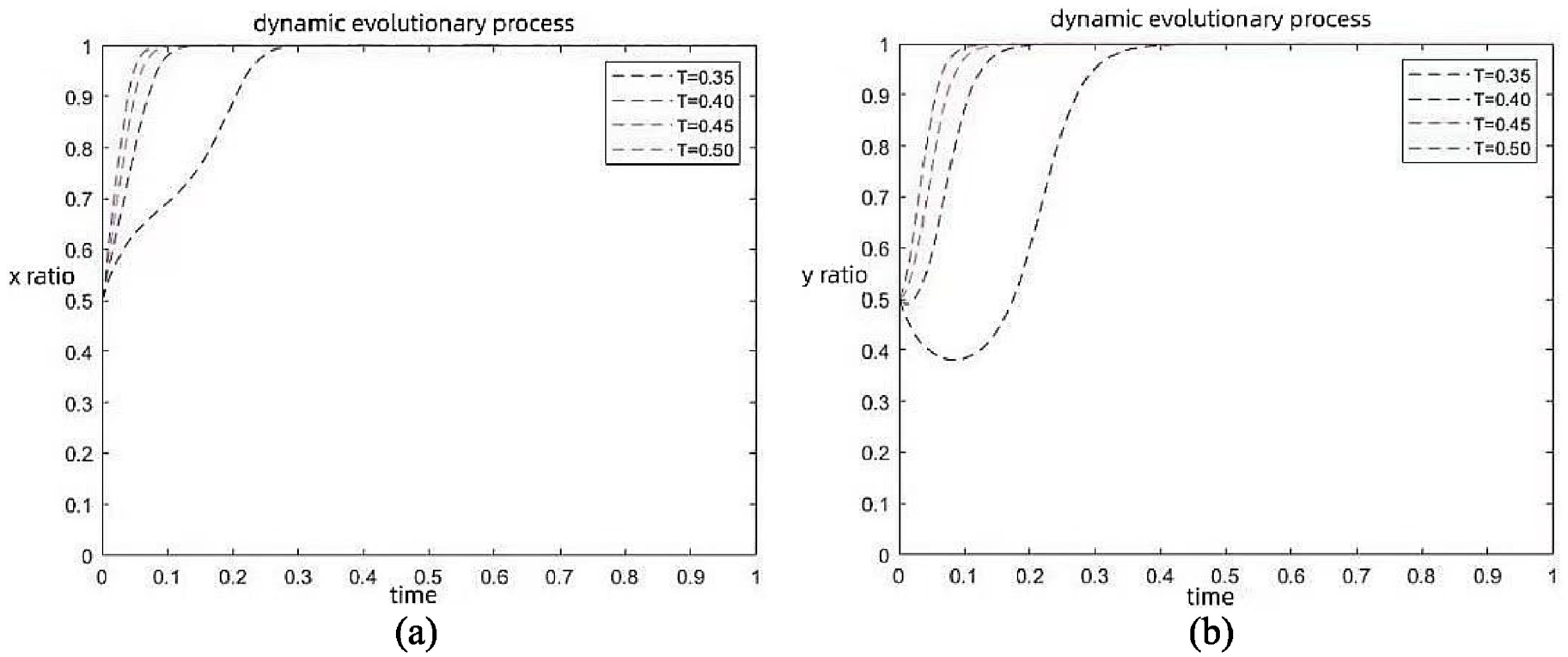
Influence of positive incentive coefficient on evolutionary path of inter-company sharing behavior: (a) company 1’s sharing behavior and (b) company 2’s sharing behavior.
By increasing the cost of data sharing while maintaining other factors stable, the changes in the values of
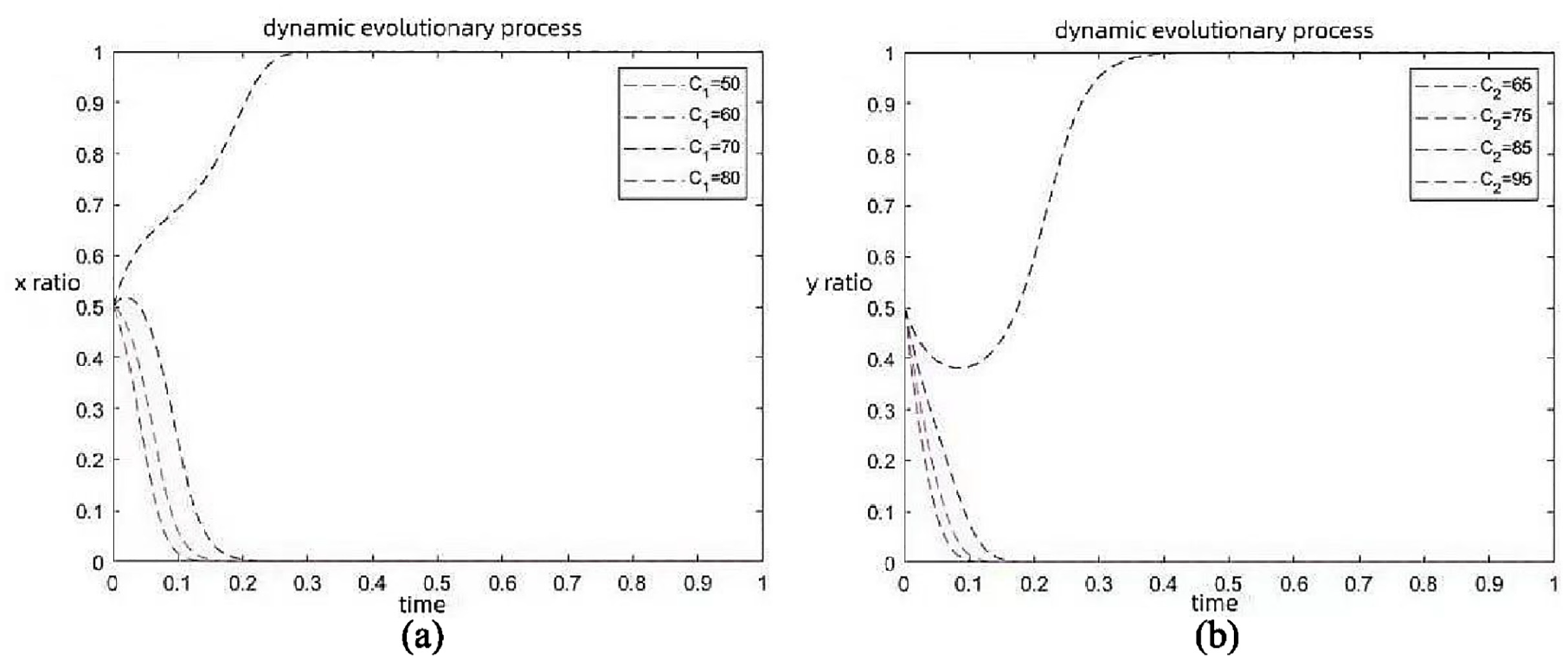
Influence of data sharing cost on evolutionary path of inter-company sharing behavior: (a) company 1’s sharing behavior and (b) company 2’s sharing behavior.
From Figures 11 to 14, it can be observed that an increase in trustworthiness, data complementarity, and positive incentive coefficient leads to changes in the evolutionary path of company sharing behavior. These changes are reflected on the phase diagram, causing the saddle point at point
With the increase in cost, the values of
Simulation analysis of evolutionary game for reputation-incentivized DT data sharing
To investigate the role of reputation incentives in the evolutionary game model of DT data sharing, it is divided into three distinct states: low reputation level, moderate reputation level, and high reputation level. These three states analyze how external factors influence participants’ decisions to adopt an information-sharing strategy. In Case 1, the reputation incentive is set to 1; in Case 2, the reputation incentive is set to 10; in Case 3, the reputation incentive is set to 100. The settings for other parameters should remain consistent with those in the model without considering reputation incentives.
Trustworthiness
According to Figure 15(a), when the reputation incentive is low, the variation in trustworthiness
Evolutionary trajectories of inter-company sharing behavior under different levels of trustworthiness: (a) low reputation incentive, (b) moderate reputation incentive, and (c) high reputation incentive.
Data complementarity
According to Figure 16(a), when the reputation incentive level is low, the variation in data complementarity
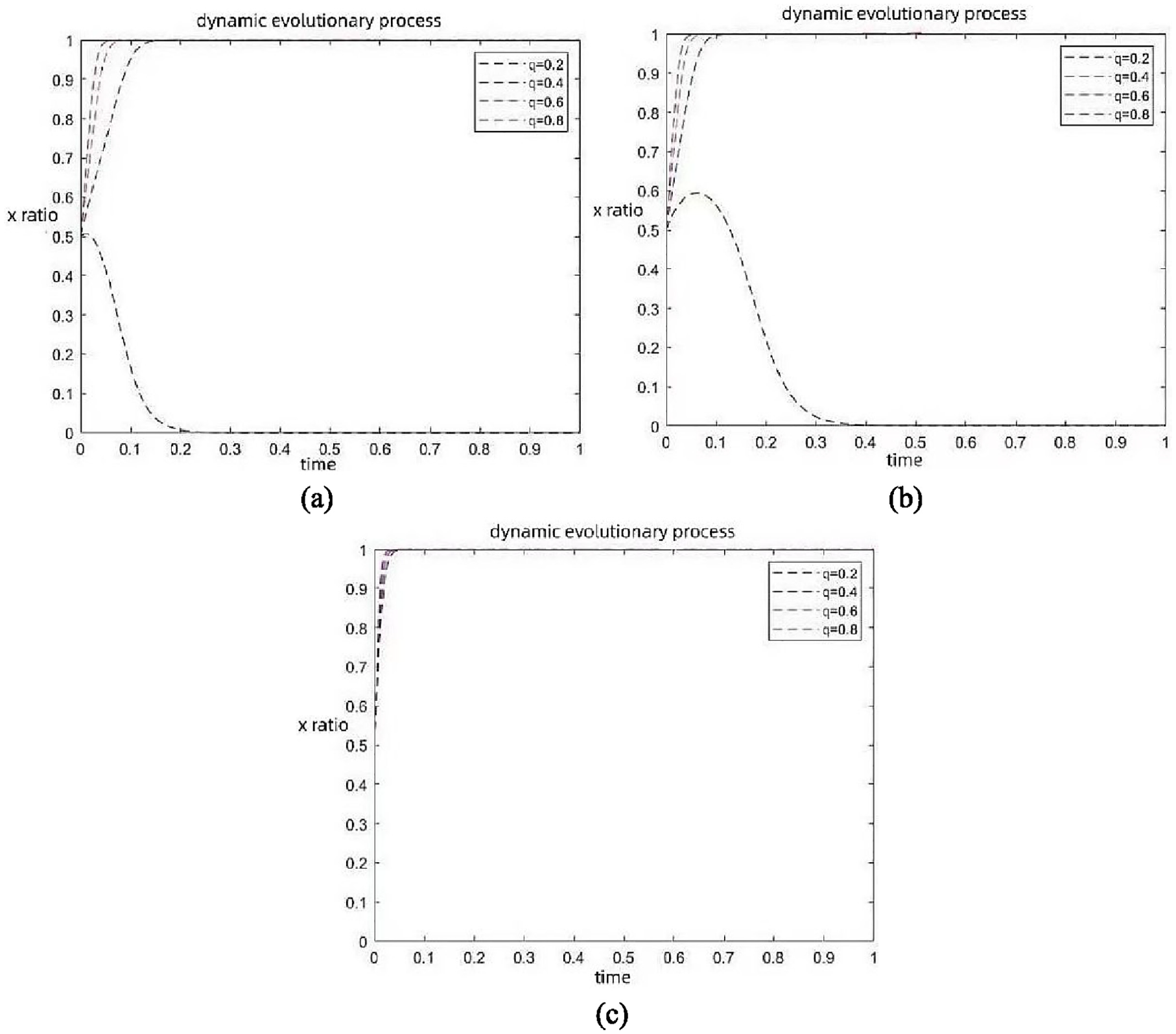
Evolutionary trajectories of inter-company sharing behavior under different levels of data complementarity: (a) low reputation incentive, (b) moderate reputation incentive, and (c) high reputation incentive.
Positive incentive coefficient
According to Figure 17(a), when the reputation incentive level is low, the variation in the positive incentive coefficient
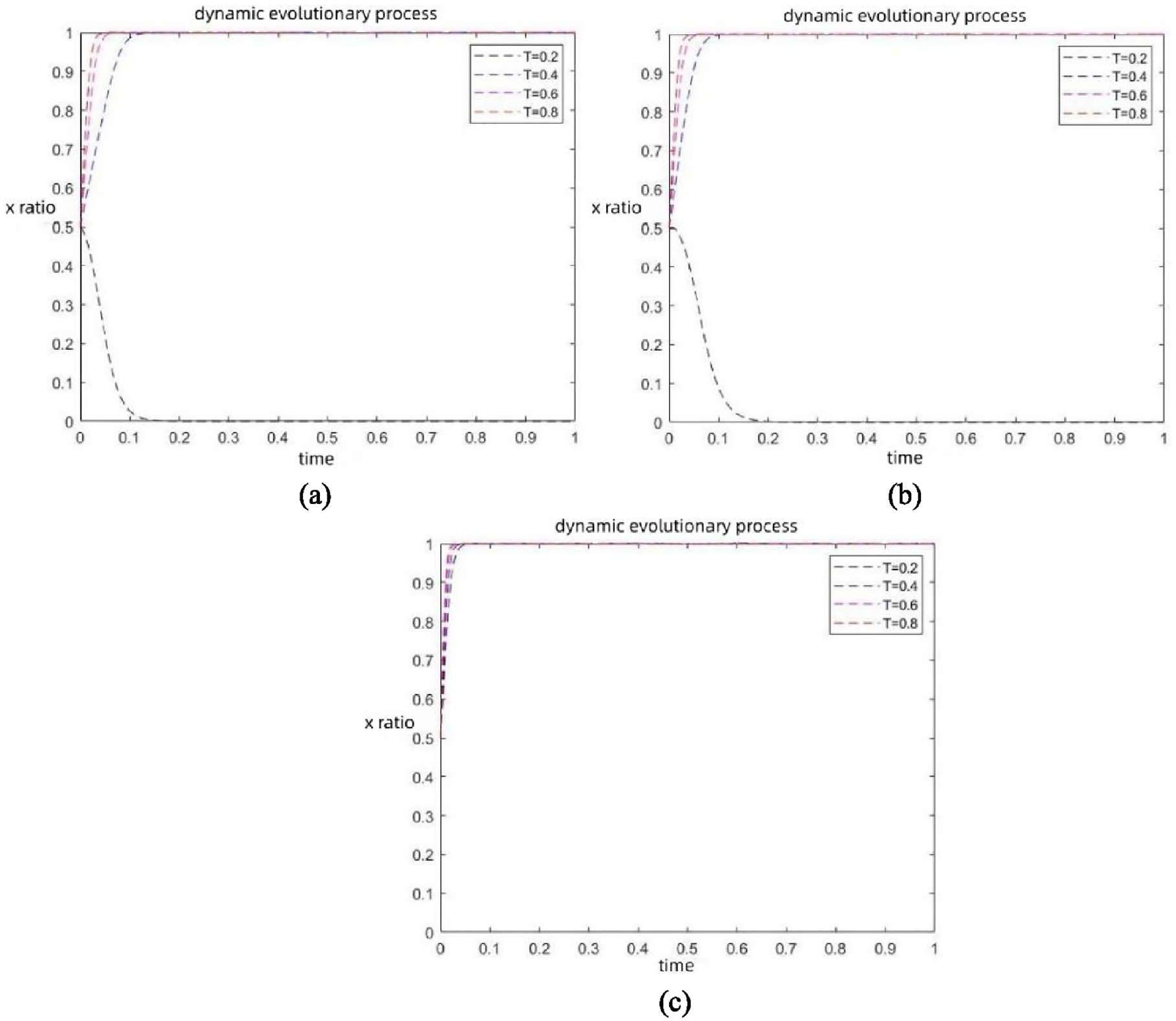
Evolutionary trajectories of inter-company sharing behavior under different levels of positive incentive coefficient: (a) low reputation incentive, (b) moderate reputation incentive, and (c) high reputation incentive.
As depicted in Figure 17(b), when the reputation incentive remains at a reasonable level, changes in the positive incentive coefficient
Data sharing cost
According to Figure 18(a), when the reputation incentive level is low, changes in data sharing cost
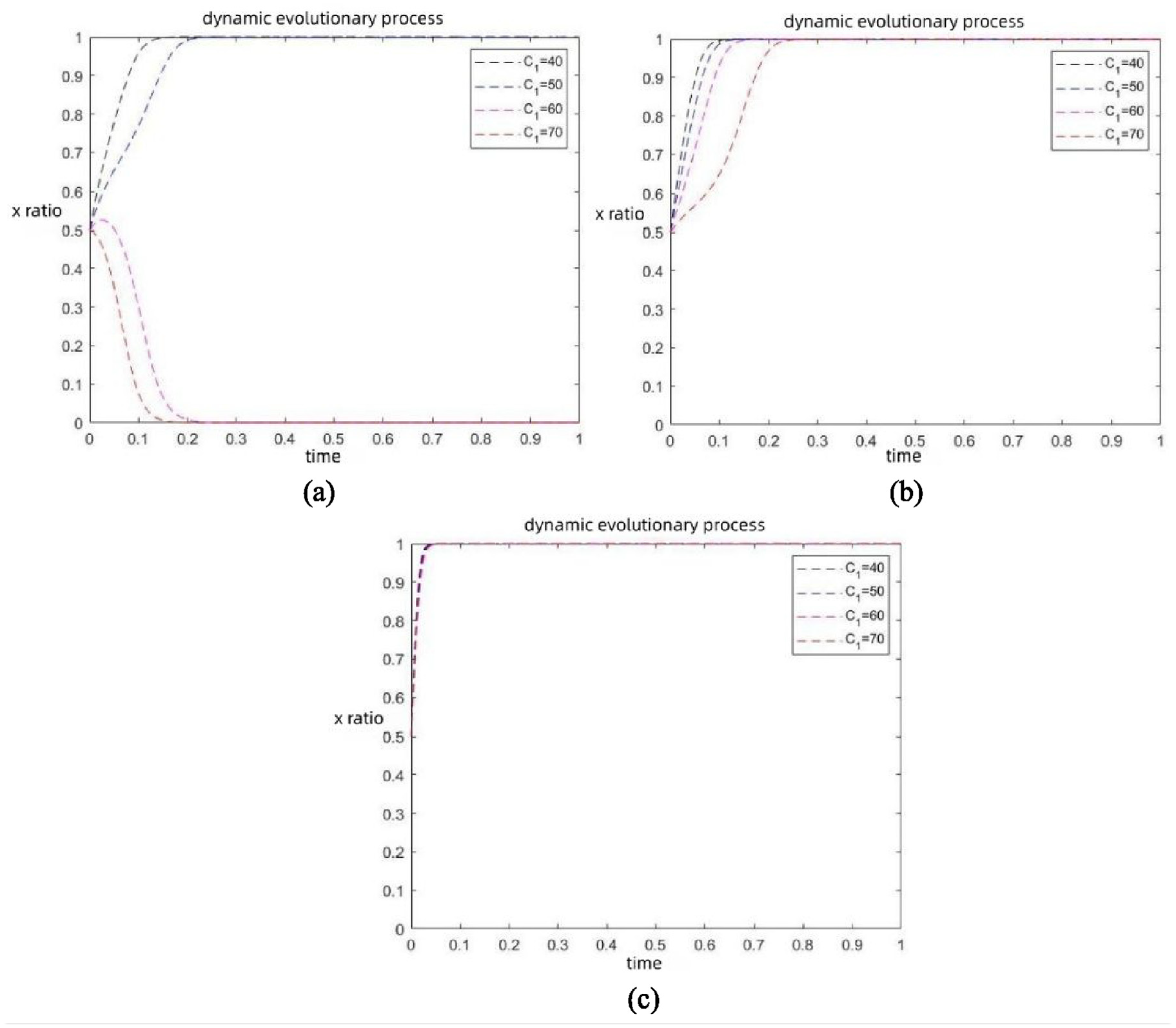
Evolutionary trajectories of inter-firm sharing behavior under different data sharing costs: (a) low reputation incentive, (b) moderate reputation incentive, and (c) high reputation incentive.
After analysis, reducing data sharing costs, enhancing data complementarity, improving positive incentive mechanisms, and establishing trust relationships will contribute to the long-term stable development of data sharing between Company 1 and Company 2. The following conclusions are drawn regarding reputation-incentivized inter-company data sharing:
Companies should enhance their quality and capabilities and improve the collaborative efficiency of DT data. Strengthening the collection, processing, analysis, and application of data can significantly elevate a company’s data management level, thereby better harnessing the maximum value of its data resources. Companies with strong data literacy can more keenly capture and understand data, thus stimulating new data thinking and driving innovation and development of data content. Strengthening communication and collaboration among companies can notably boost collaborative efficiency. When engaging in data sharing, companies should select partners with similar backgrounds and user needs as much as possible to enhance cooperative awareness and facilitate effective data exchange and collaboration. Organizing forums, seminars, and lectures can enhance companies’ understanding of DT data sharing, fostering an atmosphere of mutual respect and trust. Enhancing social oversight promotes mutual trust and cooperation among companies. With the increasing prevalence of “free rider” opportunistic behavior, such as data misuse, misinterpretation, and premature publication of research results, relevant departments, governments, and industry associations should take strong measures to guide and regulate companies, ensuring the effective protection of data rights and establishing a sound enterprise data sharing system.
Conclusion
This paper aims to explore how blockchain technology can incentivize information participants to enhance information sharing levels. Firstly, this paper explores a blockchain-based information sharing model. This model tightly integrates blockchain technology with information sharing, and employs a reputation-based incentive strategy to facilitate communication among participants. It provides a measurable standard for evaluating participants’ contributions, assessing their performance, and offering rewards to encourage better completion of information sharing. By introducing five key factors, namely trustworthiness, data complementarity, positive incentive factors, data sharing costs, and reputation incentives, a comprehensive, objective, and reliable indicator system is constructed to evaluate the development of blockchain smart contract information sharing strategies.
In addition, by applying the concept and methods of evolutionary game theory, a blockchain-based DT data sharing incentive model is established to explore the dynamic changes between different influencing factors. The study find that trustworthiness, data complementarity, and positive incentive coefficients can drive the system toward greater openness. However, data sharing costs also hinder this development. When reputation incentives are low, the system’s evolutionary stable point is O(0,0), with the strategy of participants being {no information sharing, no information sharing}. In such cases, the effect of reputation incentives is limited and fails to achieve the desired outcome. On the other hand, when reputation incentives are high, the system’s evolutionary stable points are O(0,0) and B(1,1), with participants’ strategies being {information sharing, information sharing} and {no information sharing, no information sharing}. The system’s evolutionary stability depends on the combined effects of trustworthiness, data complementarity, positive incentive coefficients, and data sharing costs. In this context, the effectiveness of reputation incentives is influenced by multiple key factors.
Moreover, the experimental results indicate that trustworthiness, data complementarity, and positive incentive coefficients influence the game process and are related to their own thresholds. When trustworthiness, data complementarity, and positive incentive coefficients are below a specific threshold, reputation incentives are ineffective, leading to the system’s evolutionary stable point being O(0,0), with the strategy being {no information sharing, no information sharing}. When these factors excess a specific threshold, reputation incentives become effective, resulting in the system’s evolutionary stable point being B(1,1), with participants’ strategy being {information sharing, information sharing}. Data sharing costs also have a threshold, opposite in effect to other key factors. Analyzing the impact of each indicator on the threshold for information sharing optimization helps to optimize participants’ behavior and implement an effective incentive mechanism.
By applying the conceptual framework of evolutionary game theory, a novel model for incentivizing DT data sharing using blockchain technology is proposed. The paper’s design of a distance grouping-based practical byzantine fault tolerance consensus algorithm and an information sharing incentive strategy based on blockchain smart contracts addresses key challenges related to data credibility and information sharing, which are crucial for the success of the next industrial revolution. 41 Although this paper has deeply investigated information sharing strategies and obtained beneficial results, further exploration can be conducted in the future, such as external factors such as blockchain private key loss, and considering the multiple stakeholders exist within a blockchain system.
Footnotes
Appendix A. The general PBFT consensus mechanism
The PBFT algorithm consists of three different parts: the client, primary node, and replica nodes. The algorithm includes five main phases: the request phase, pre-prepare phase, prepare phase, commit phase, and feedback phase.
Through a detailed analysis of the PBFT process, it can be observed that the existing PBFT algorithm faces the following three issues:
Due to the lack of strict criteria for selecting the primary node, ensuring its accuracy becomes challenging. If multiple elected primary nodes are malicious, it will lead to an extreme consumption of system resources and severely affect the stability, reliability, and security of the system. Additionally, the lack of a robust backup data synchronization mechanism makes the data discrepancies between different nodes more apparent, further impacting the system’s stability and reliability.
The PBFT algorithm lacks a flexible consensus node joining and exiting mechanism, making it ineffective in handling complex environments within the cluster, especially when the number of nodes is large and the frequency of changes is high. This state can severely compromise the system’s reliability. Besides, the PBFT algorithm uses three stages of broadcasting, including single-node broadcasting and two whole-network broadcasts. With the development of P2P technology, especially the last two broadcasts, there is a significant consumption of network bandwidth. If the request volume exceeds the normal range, it can lead to network congestion.
Appendix B
Declaration of conflicting interests
The author declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This research was supported by the National Industry and Technology Major Project of China [grant number QT1451-0415043].
Data availability statement
Data sharing not applicable to this article as no datasets were generated or analyzed during the current study.


