Abstract
This paper concentrates on decentralized variable structure adaptive integral sliding mode control (ISMC) for connected vehicles (CV) against cyber-attacks. First of all, a novel vehicle leader-follower model is established by jointly considering the cyber-attacks which involve replay attack and DoS attack simultaneously. Secondly, a decentralized control scheme is designed on the basis of the variable structure observer and adaptive integral sliding mode technique. The Lyapunov-Razumikhin method is adopted such that the state estimation error of CV system is asymptotically converged to zero, which can overcome the replay attack, DoS attack, and measurement delays, then a corrective signal is designed for the deception attack to eliminate the influence of deception attack on the CV system. Furthermore, the robust asymptotic stability of CV system is guaranteed by exploiting the emerging technique of robust control for time-delay systems. Meanwhile, the string stability of CV is guaranteed, even under the condition of heterogeneous vehicles. Finally, extensive simulations are conducted to verify the theoretical analysis and demonstrate the effectiveness and superiority of the proposed method.
Introduction
With the rapid development of urbanization, the volume of automobiles has increased remarkably, which brings significant convenience to life, but meanwhile unprecedentedly aggravates the issues of road congestion, environmental pollution, traffic accidents, etc. It is imperative to develop Intelligent Transportation Systems (ITS) to manage the vehicle traffic more effectively. Among all the ITS paradigms, the Connected vehicles (CV) system has been attracting wide attention from both academia and industry. CV empowers the vehicles on the road to communicate and cooperate with each other through wireless sensor networks, and drive safely and independently with a small inter-vehicle distance, thus effectively reducing fuel consumption, improving traffic safety and increasing traffic throughput. As a result, CV is becoming one of the most important trends in the research field of ITS.1,2
In the CV control design, there are two issues that need to be specially considered, namely, individual vehicle stability and string stability. The stability of individual vehicle refers to that the relative distance and relative velocity of all adjacent vehicles should be close to the equilibrium state, and it is also the stability condition that most tracking control systems must meet.3–9 String stability is a special problem of CV, which mainly solves the problem of tracking error propagation along the string of vehicles. Up to now, string stability has received significant research attention from different aspects. The readers can refer to Feng et al. 7 to better outline the research work of string stability. For string stability under variable spacing strategy, no inter-vehicle communication is required. On the contrary, this paper focuses on CV control scheme based on constant spacing (CS) policy. A smaller inter-vehicle distance in this scheme means more stringent requirements for string stability. For instance, Wu et al. 8 proposed a pulse control method for an uncertain second-order homogeneous CV system under CS strategy. Wang et al. 9 considered the CV control problem with time delay, obtained the maximum time delay and guaranteed the string stability. A distributed sliding mode control framework was designed which supports multiple information flow topologies to guarantee the string stability. 10
It is worth noting that most of the existing works about CV systems generally assume that the communication networks are secure all the time. However, due to the openness of the wireless network, it is difficult to ensure the security of CV communication based on wireless sensor network. Various cyber-attacks widely exist in the communication network. These malicious attacks on CV may cause personal privacy leakage, significantly reduce cooperative control performance, even lead vehicle out of control and paralyze the entire CV system, leading to major public security problems.11,12 Typical cyber-attacks on CV can be divided into
Up to date, cyber-attacks that corrupt control and measurement signals of CV system can be disguised as disturbances or control behavior, and researchers have studied this from different aspects. For example, Liu et al. 19 suggested the change of communication topology caused by DoS attack, and studied the consensus of multi-agent systems under replay attack and DoS attack. Xiao et al. 20 investigated the distributed adaptive CV control problem for automatic vehicle security based on vehicular ad-hoc networks with intermittent DoS attack. Mousavinejad et al. 21 studied the autonomous platoon control problem under DoS attack, which described the attack as the delay and packet loss, and further designed a resilient controller to guarantee the stability of the system. Biroon et al. 22 developed an observer-based diagnostic algorithm to detect and isolate the replay attack, and the stability of CV can be achieved. Zhao et al. 23 also designed an attack detection framework, which can realize the safe driving by estimation and prediction when the vehicle cannot obtain the complete state information. Debruhl et al. 24 extended the attack detection strategy based on sensor-based proportional differential link and communication feedforward link to real-time switching control strategy in the presence of cyber-attacks. As far as we know, how to design a controller that can effectively suppress the gradual amplification of interference along a string of vehicles with cyber-attacks while ensuring individual stability still remains as an open and challenging problem.
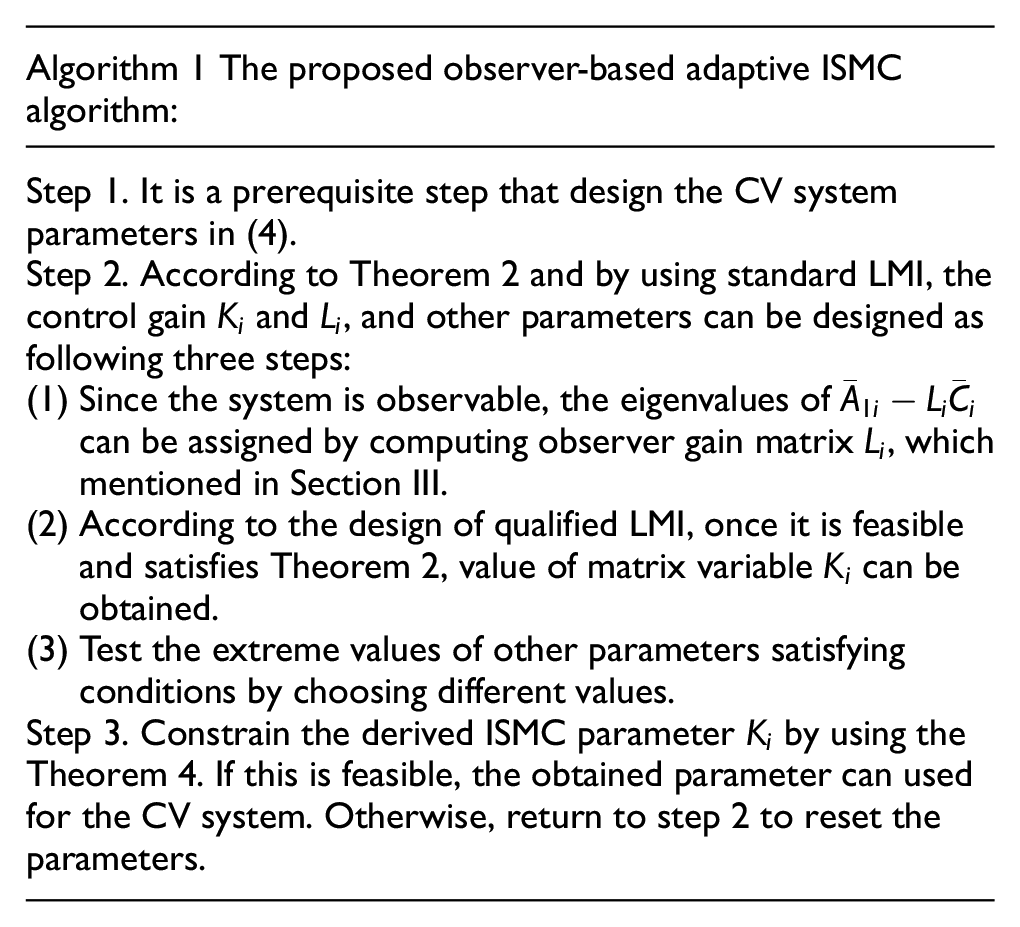
In this research, observer-based adaptive integral sliding mode controller for CVs is designed based on the CS strategy. Furthermore, the corresponding individual stability and string stability in the presence of cyber-attacks are theoretically analyzed. The main contributions of this article are summarized as follows.
A variable structure observer is proposed, and an optional boundary layer observer strategy is provided. The CV state under cyber-attacks combined with measurement delay is estimated. Based on the analysis of system performance, the expression of system state error is derived, and it is proved that the state error of CV is always asymptotically convergent for cyber-attacks.
An adaptive ISMC strategy based on an improved variable structure observer is designed to solve the security problem of CV under cyber-attacks. The uncertainty caused by cyber-attacks is accurately compensated from the initial time, and the asymptotic stability of CV system can be guaranteed according to the conditions derived from Lyapunov-Razumikhin functions.
The rest of this article is arranged as follows. In Section II, the structure of CV system is briefly described, followed by the control model considering cyber-attacks. In Section III, the adaptive ISMC algorithm derived from variable structure observer is proposed for CV system with cyber-attacks and measurement delay. Section IV gives the sufficient conditions for CV control algorithms which achieve individual stability and string stability. Numerical simulation results are provided in Section V. Section VI concludes the paper.
System model and problem formulation
This article studies an CV system composed of
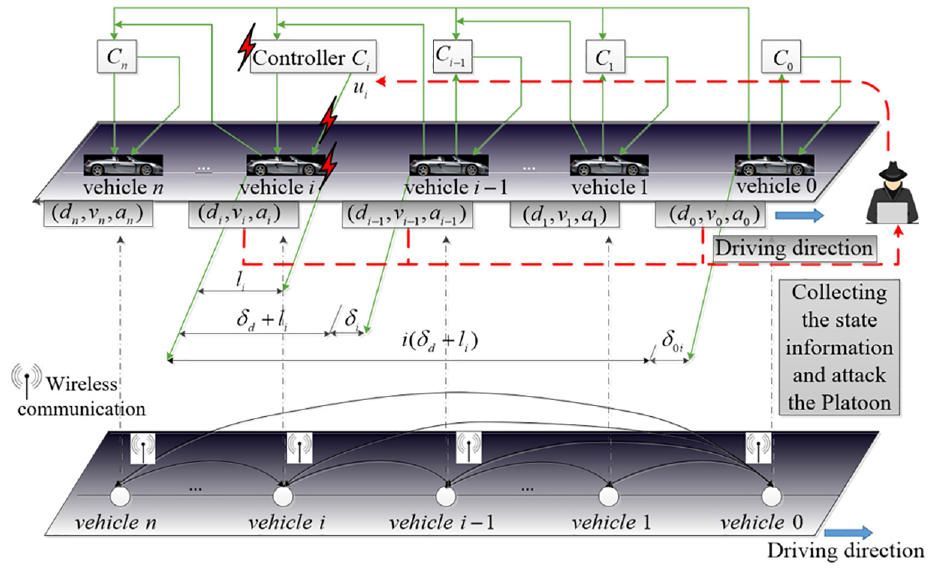
CV system structure.
CV modeling
The tracking error between two adjacent vehicles can be defined as
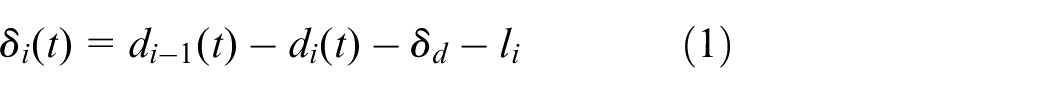
where
The distance error for the
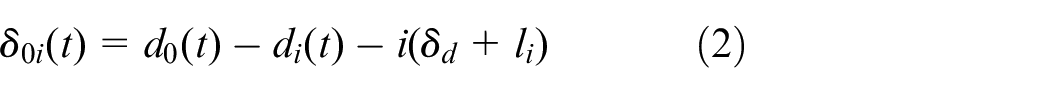
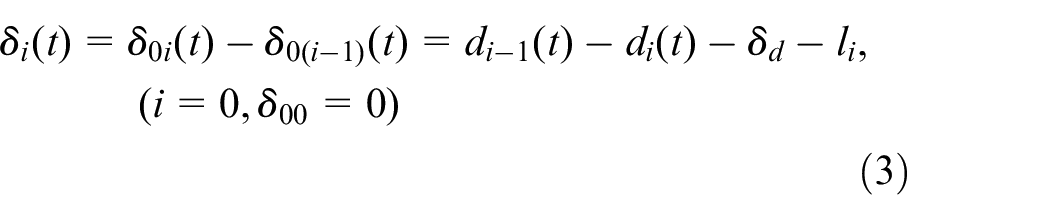
According to (1) and (2), one can get
According to the nonlinear model described in Refs,25–27 the

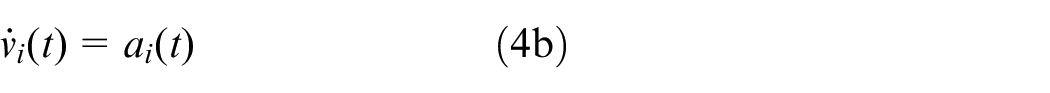

where
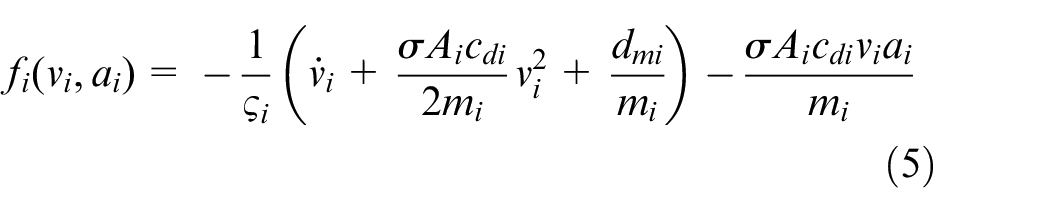
where
After introducing feedback linearization technique
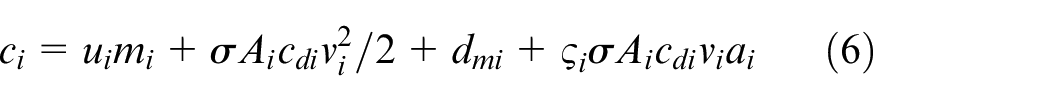
the equation (4c) becomes

where
Define the state variable as
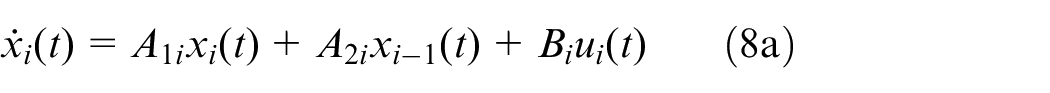
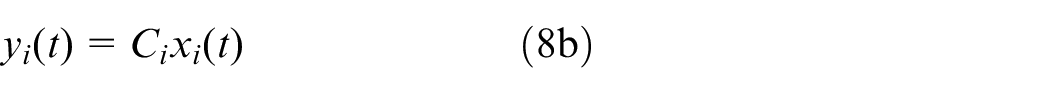
where
The general controller structure for CV is designed as follows

Obviously, the structure of the controller is based on the combination of state variables,
Effect of cyber-attacks
We study the presence of an adversary scenario, which aims to manipulate data transmitted over wireless networks to destroy the stability of CV. The general cyber-attacks including replay attacks, DoS attacks, and deception attacks. In the following, we will analyze what impact each of the attacks will has on the CV.
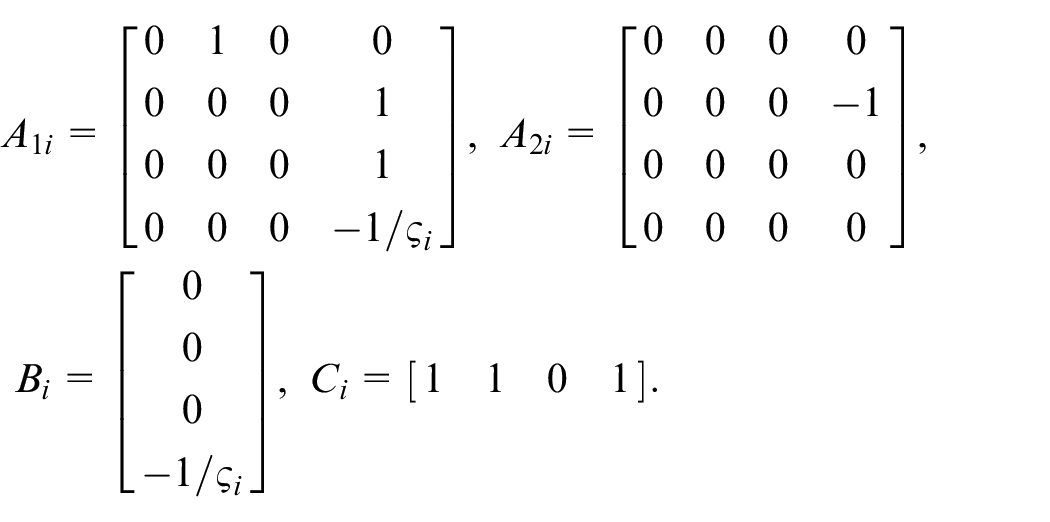
Replay attack
Replay attack refers to a malicious behavior that the attacker can obtain all the control information transmitted in the communication channel during the incubation period, and then repeat the input using the non-current input information, thus becoming a malicious act that interferes with or destroys the normal transmission of information between CV. We consider two common modes of replay attack, as in Ge et al.,
15
namely,
(a) Pseudo-value replay attack and (b) truth-value replay attack.
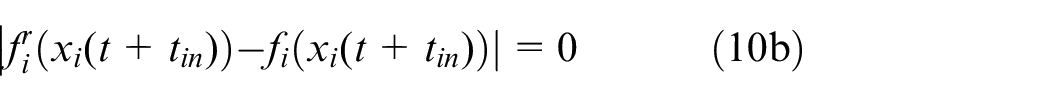
The real-time value at the end of the pseudo-value replay attack is not equal to the attack value, meanwhile the real-time value at the end of the truth-value replay attack is equal to the attack values, which are described as follows
End point of the pseudo-value replay attack satisfies
End point of the truth-value replay attack satisfies
When replay attack occurs, the controller can be transformed into
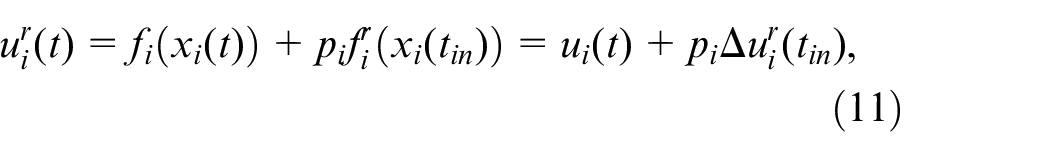
where
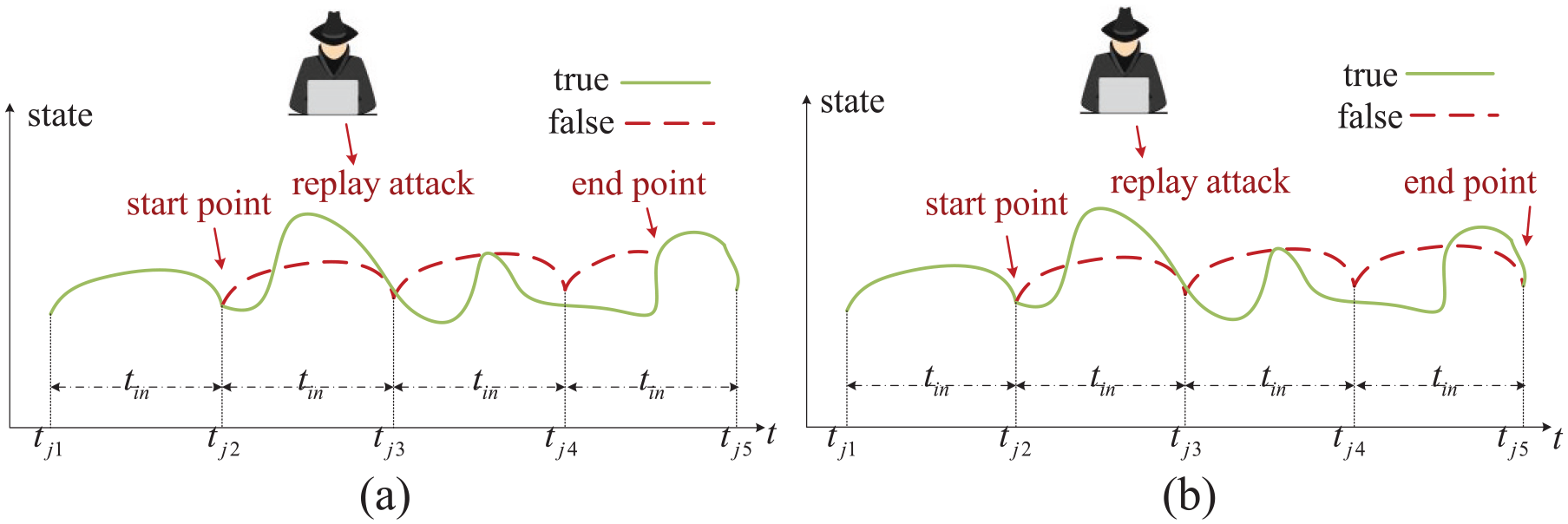
DoS attack
DoS attack is a malicious attack that makes the controller unable to provide services, which is one of the common attacks and destruction for hackers. DoS attack can cause the control loop to be disconnected and the controller cannot get feedback information in time, so that the CV system is out of control, and the final performance becomes bad or even collapses. During DoS attack, there is neither sending nor receiving information in the communication channel.
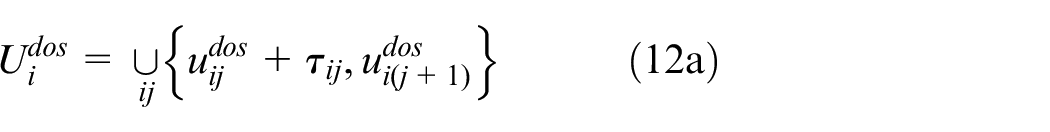
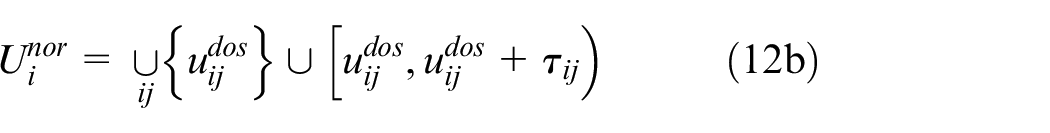
The intermittent DoS attack, as shown in Figure 3, and the DoS interval and Non-DoS interval can be formulated as
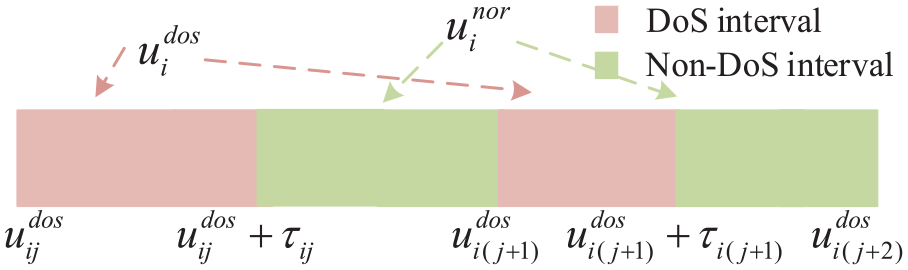
Denial-of service attack.
where
The control signals grabbed by the attacker are described as
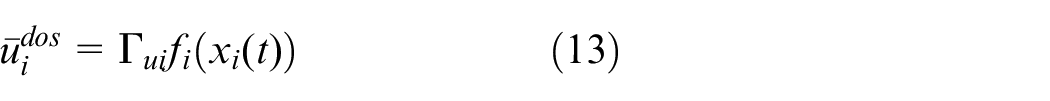
where
However, DoS occurs randomly in most cases. Therefore, the DoS attack model can be modeled as
where
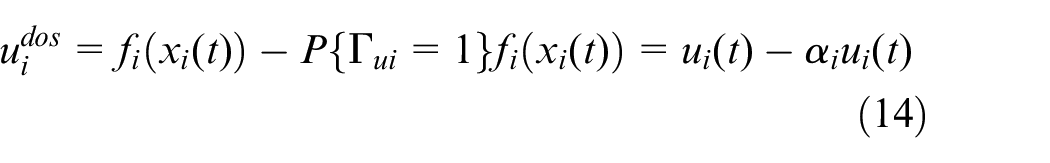
Deception attack
Deception attack means that the attacker monitors the communication information of the system, maliciously and secretly adds the attack signal to the system information, and sends the attack data and real data together through the shared network, thereby reducing and deteriorating the performance of the CV system. Suppose
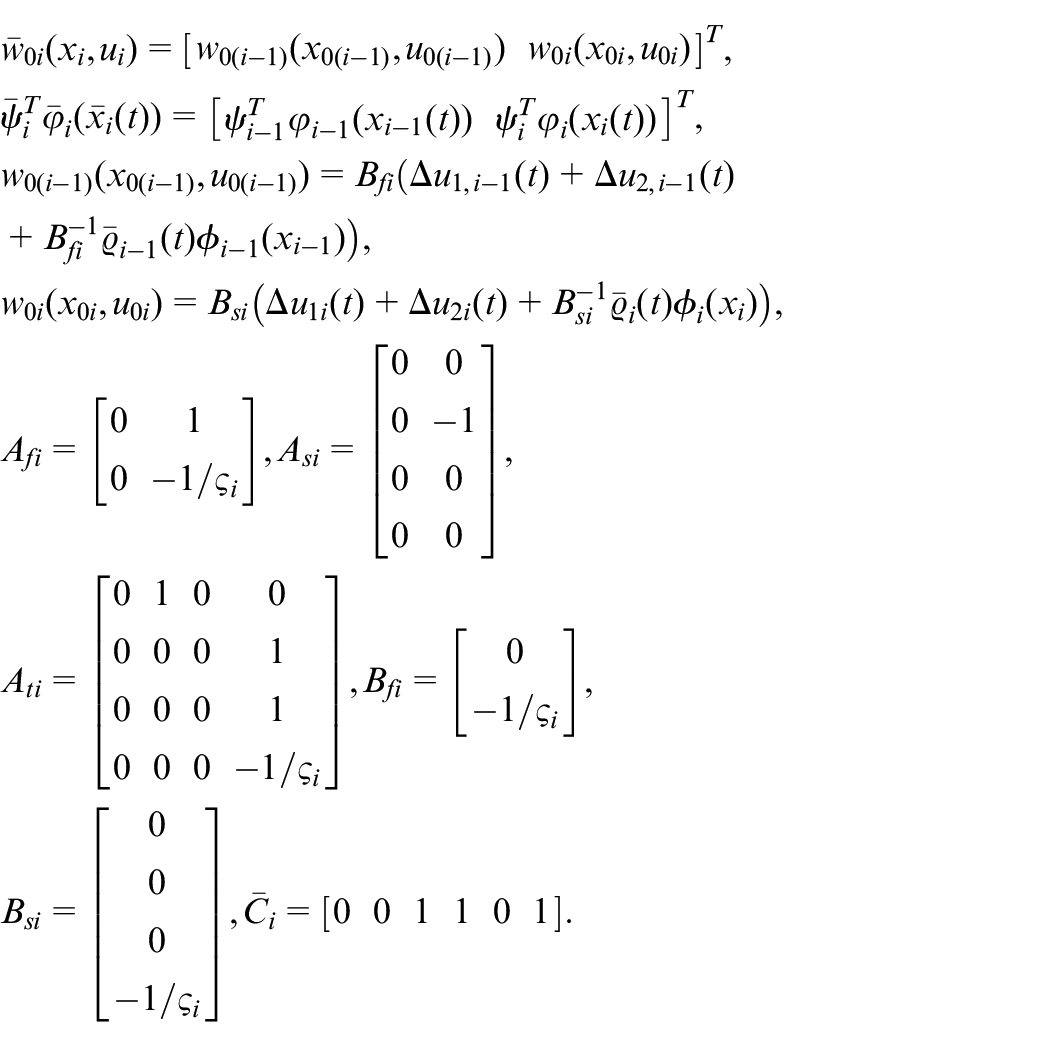
System model transformation
Further considering a more realistic vehicle model with measurement delay, and combined with attack models (11), (14), and (15), CV system (8) can be converted to the following form
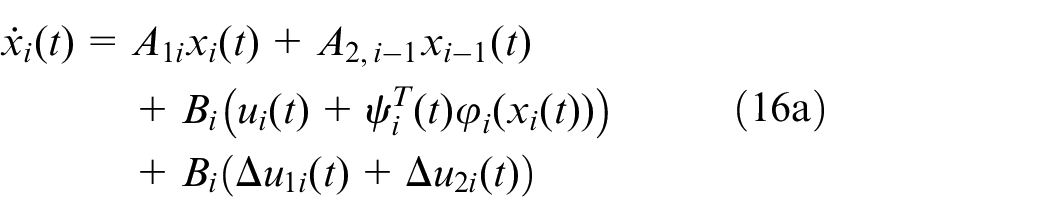

where
The CV in (16) is a coupled system, that is, the state information of the
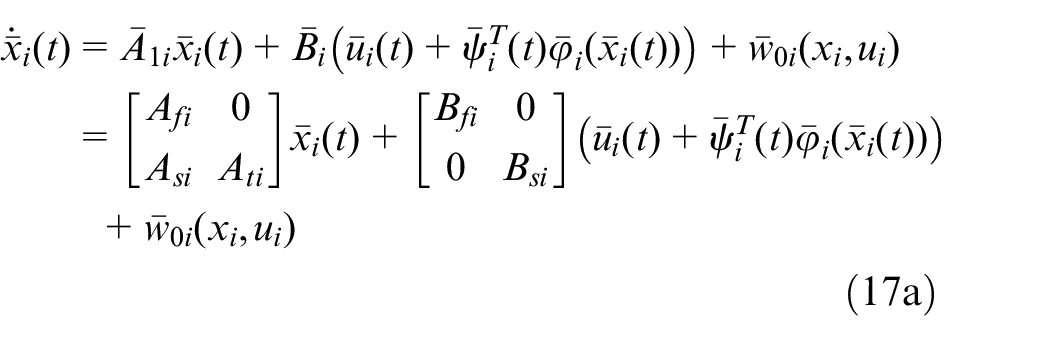
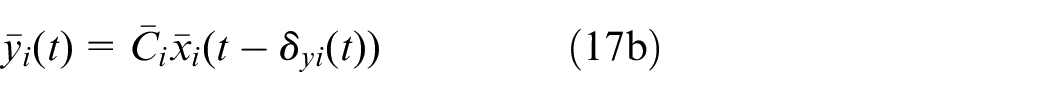
where
The objective
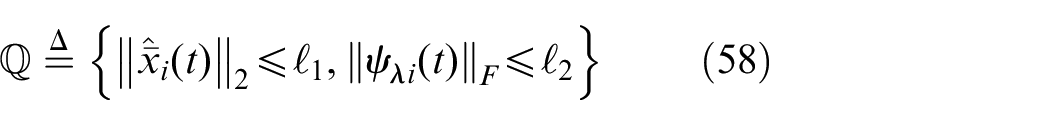
The object of the research is to propose a decentralized adaptive integral sliding mode controller, so that the CV system can satisfy the following requirements.
The CV system satisfies uniform ultimate boundedness under the proposed controller.
String Stability: Spacing error will not propagate and enlarge along the string of vehicles, namely,
Observer design
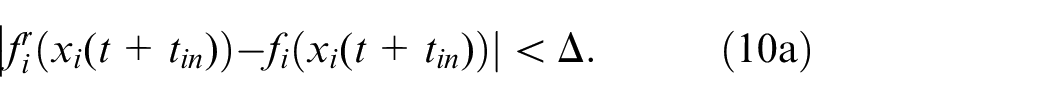
In this section, a variable structure observer is constructed to estimate the vehicle states under cyber-attacks and measurement delays.
Variable structure observer design
Define
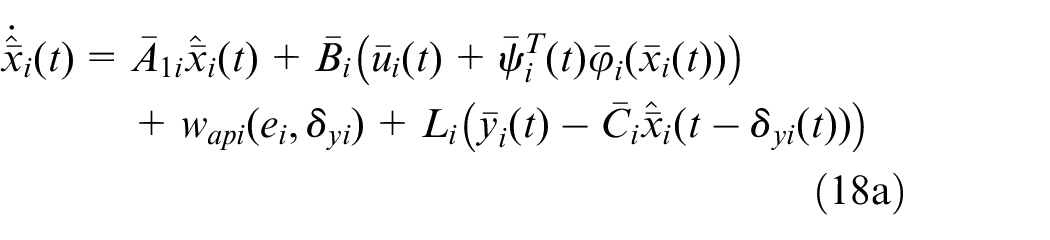
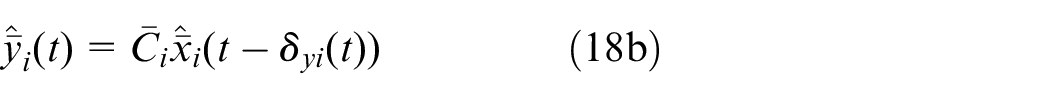
where
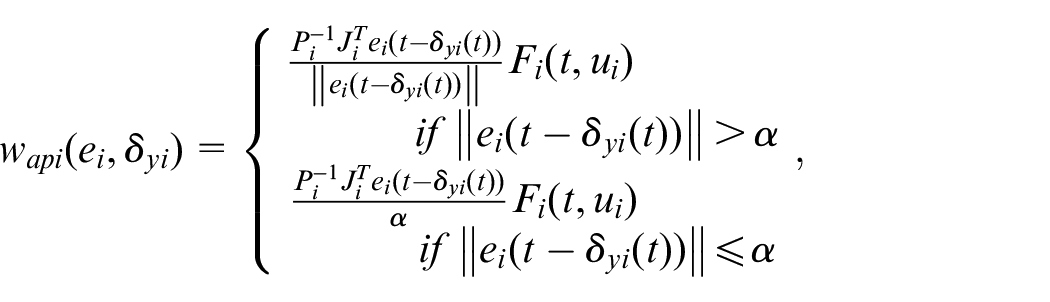
with
where
See Appendix for the proof process.
Next, the convergence properties of the observer (18) are proved as following lemma.
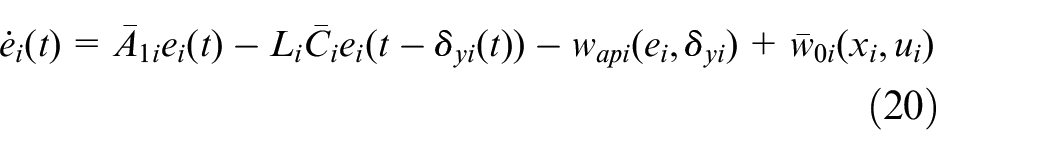
Define
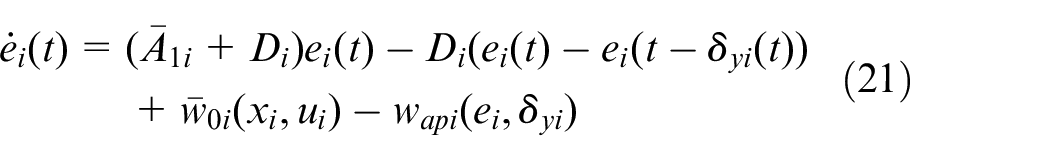
then
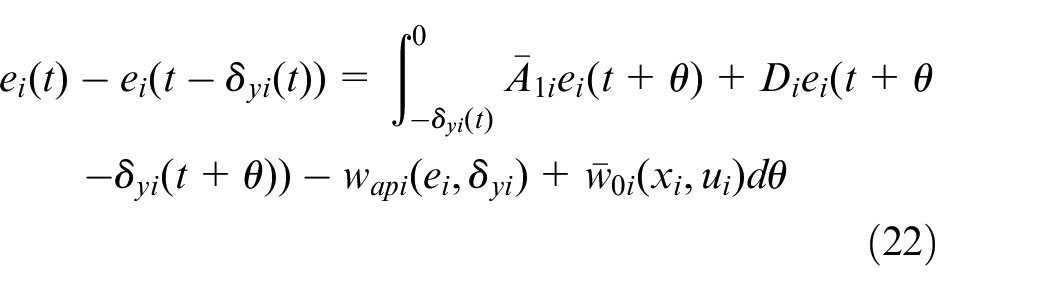
with
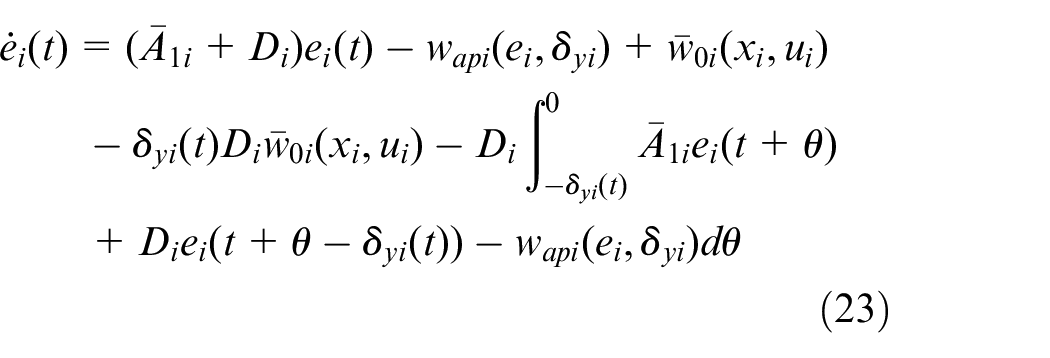
Now define
where
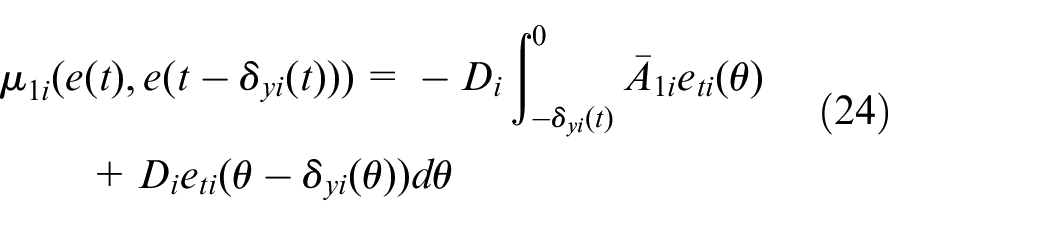
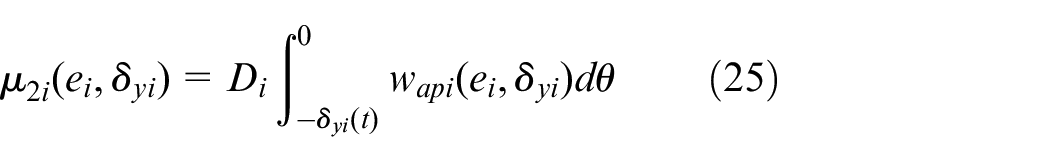
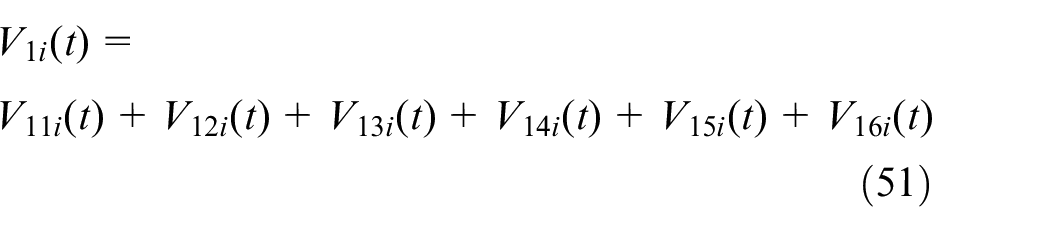
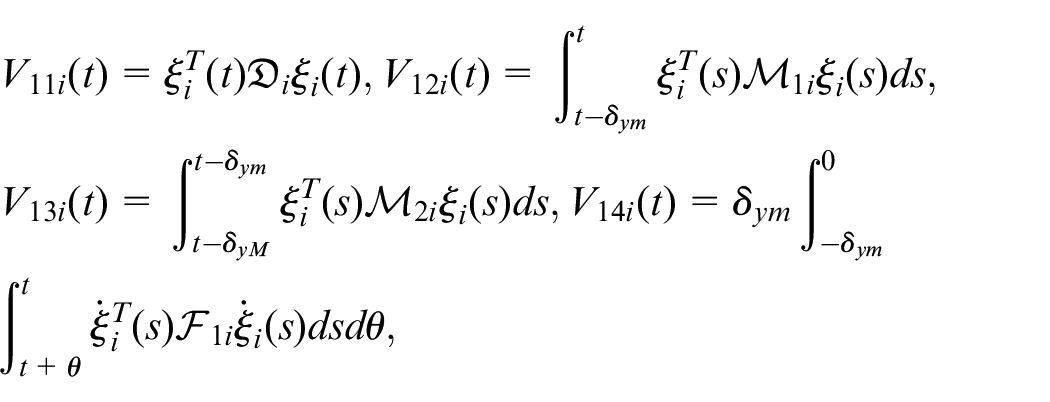
Define the Lyapunov-Razumikhin function candidate as
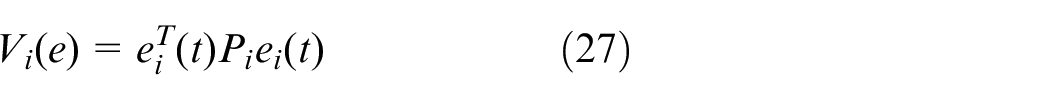
where
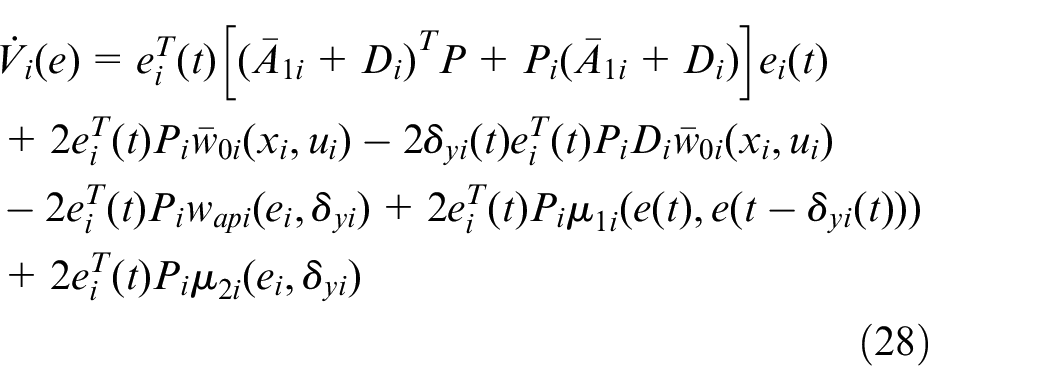
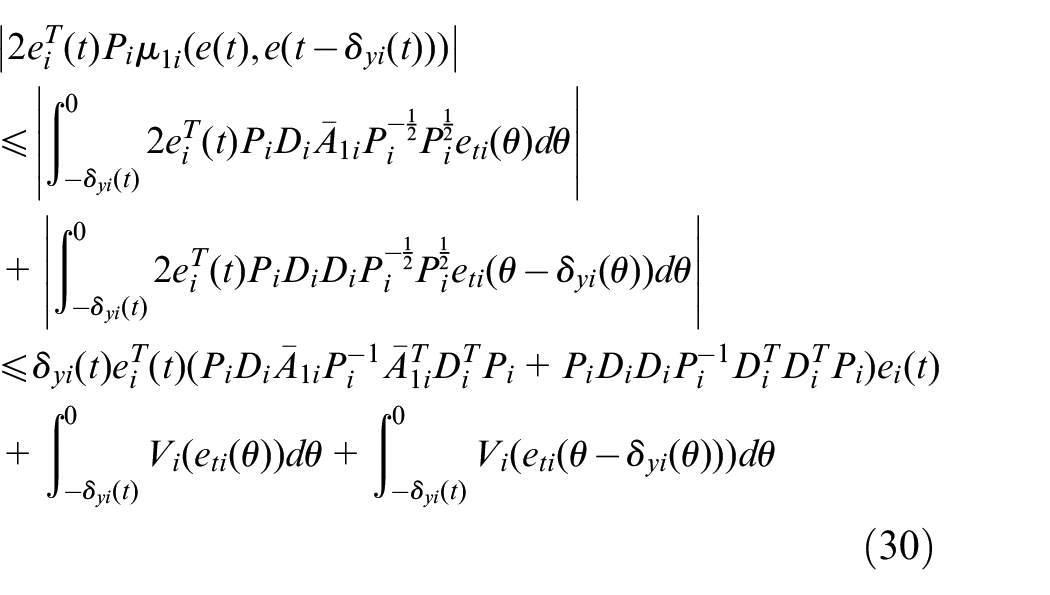
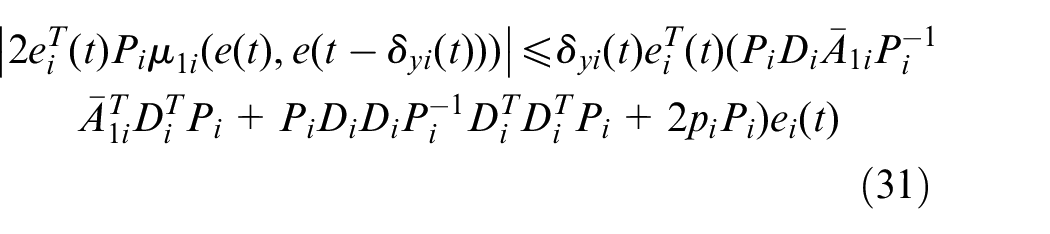
Consider each of these terms separately, namely
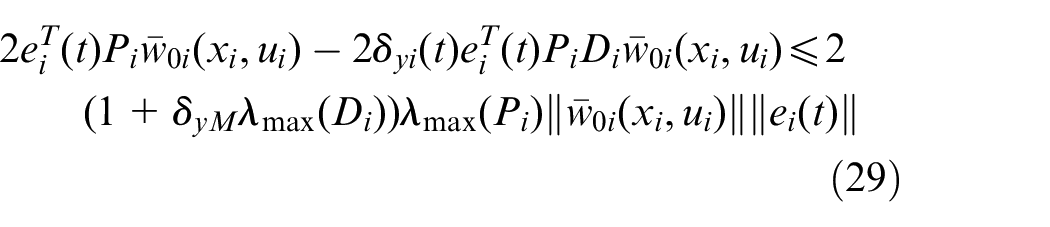
Then the
From Razumikhin theorem
Consider the last part, when
When
So from Lemma 1, we know that
define
Define
Thus, if
When
Define
then
Define
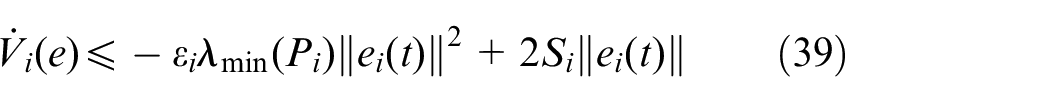
Thus, if
Based on the above analysis, if the estimation error
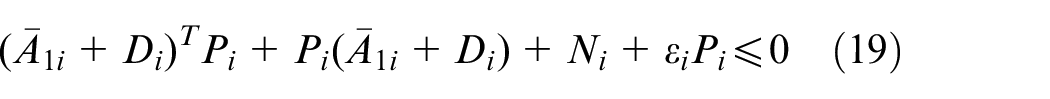
Observer gain design
Since
As a result, the matrix
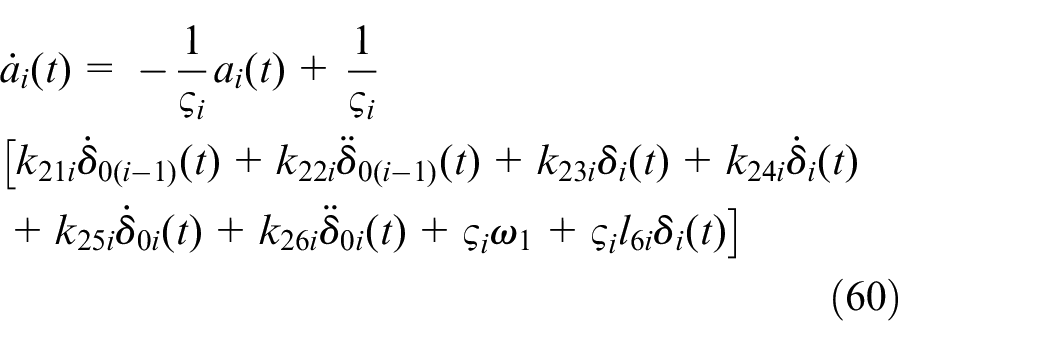
Controller design
Adaptive ISMC design
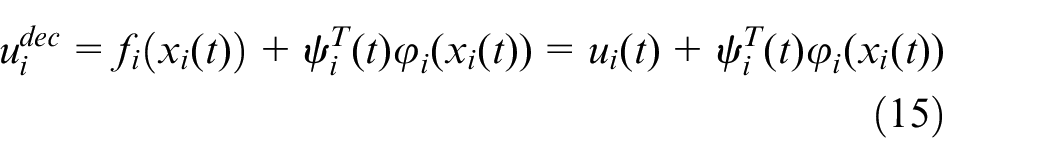
In this section, an equivalent sliding mode controller is designed for the CV system under multiple cyber-attacks, and then a corrective signal is designed for the unprocessed deception attack to eliminate the influence of deception attack on the CV system. The specific design is as follows.
According to the form of variable structure state observer, a new sliding surface can be chosen as:
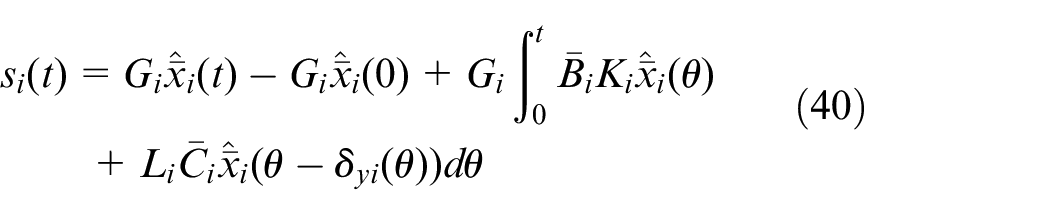
where
By derivation of
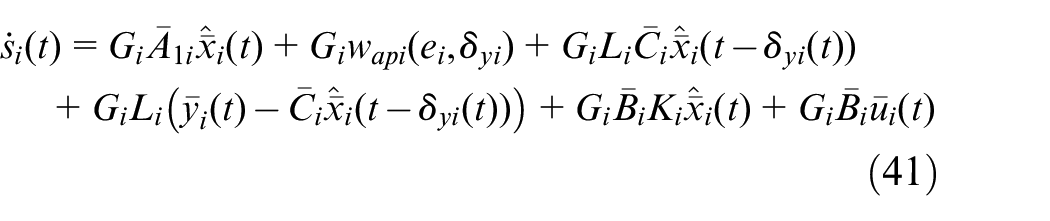
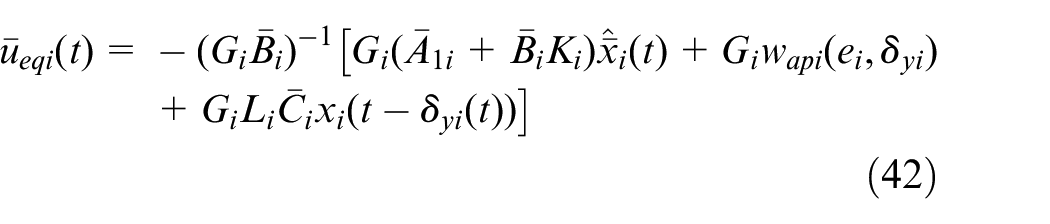
Therefore, equivalent control
In order to achieve the ultimate boundedness of CV system under deception attack, the correction signal is designed as follows:

where
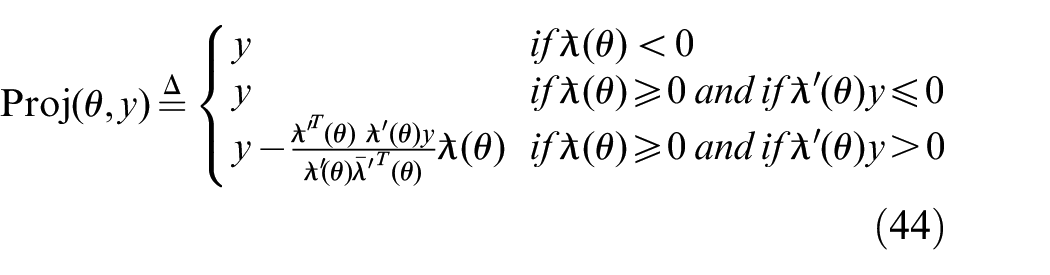
where
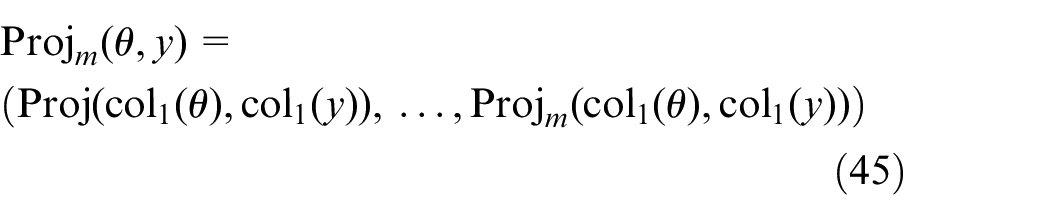
where
At this point, the controller structure changes from (42) to the following form
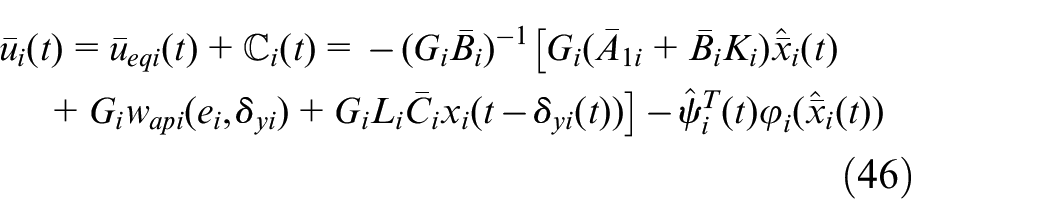
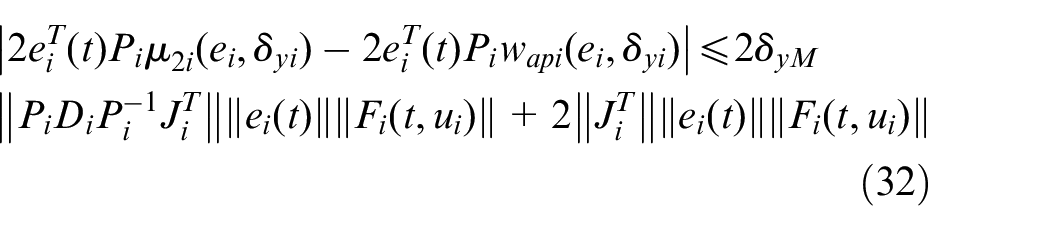
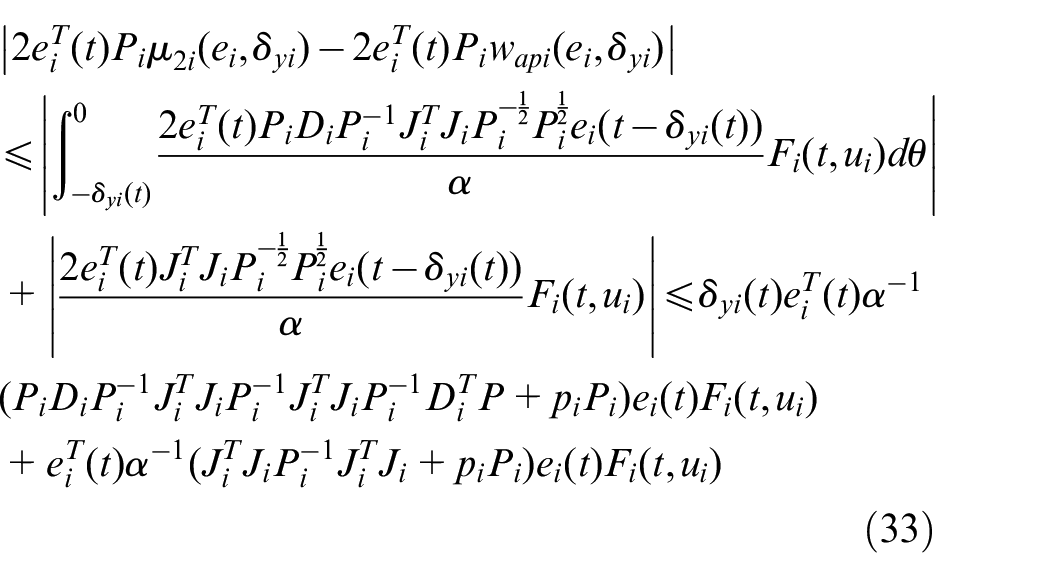
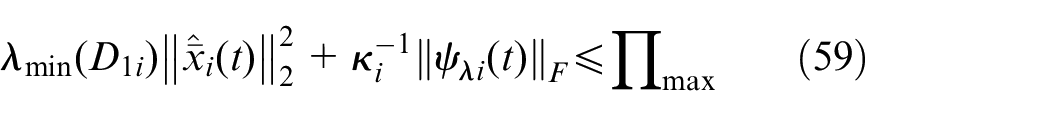
Robust stability analysis
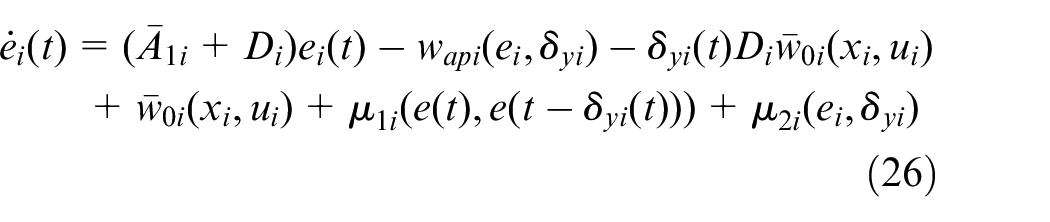
Substituting (46) into (18), one can get
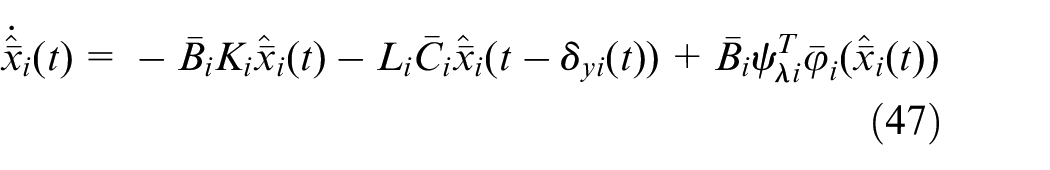
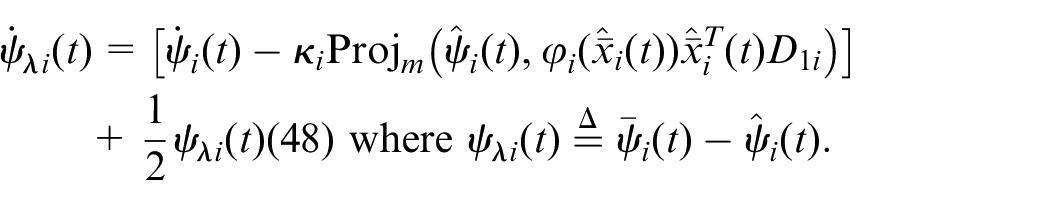
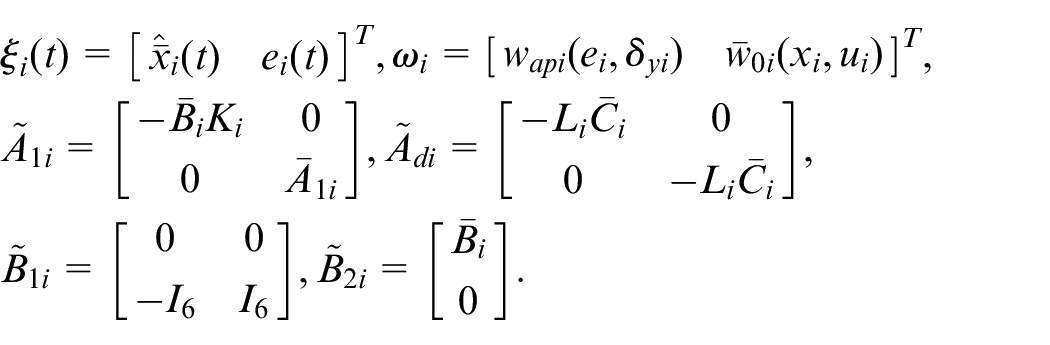
Combining (20) with (47), the augmented equation of CV system can be obtained as
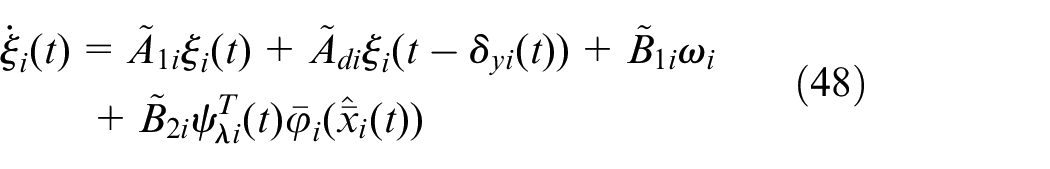
where
The conditions for CV in (48) to be uniformly bounded are given in the following theorem.
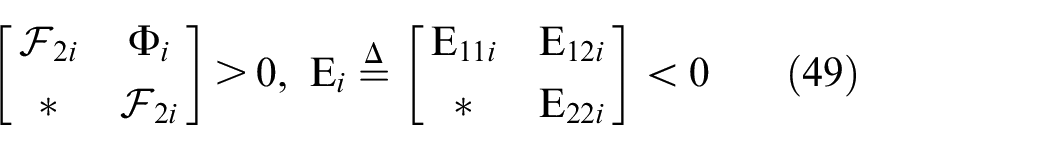
then the CV system (48) under (46) control is uniformly bounded and the ultimate limit satisfies
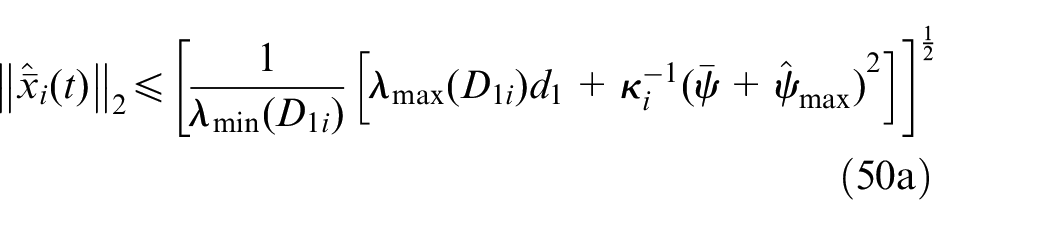
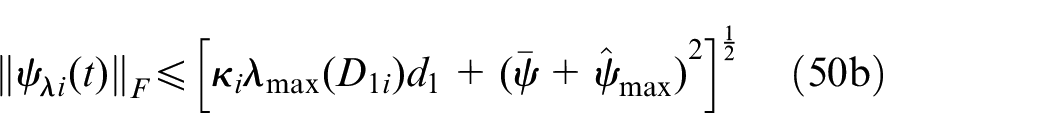
where
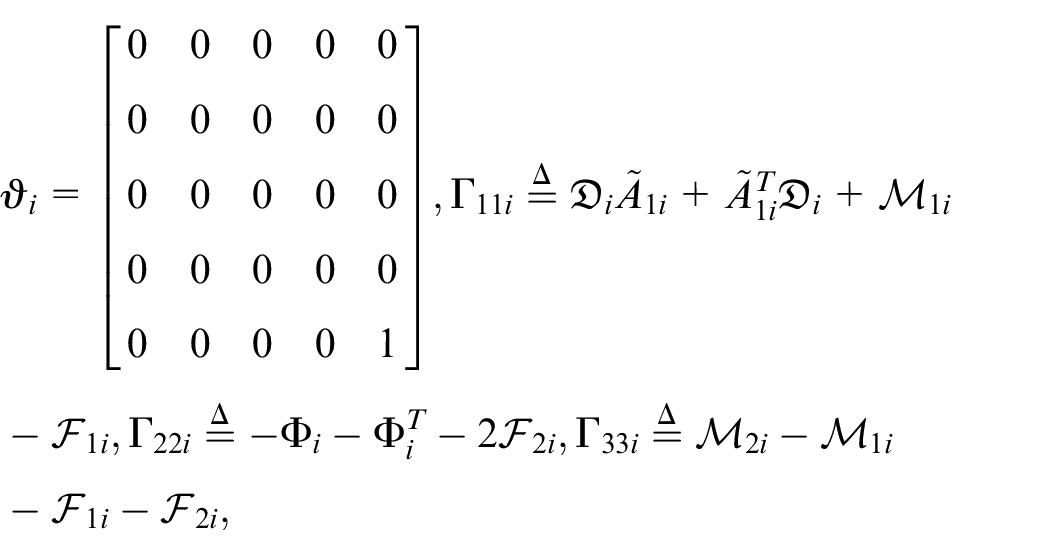
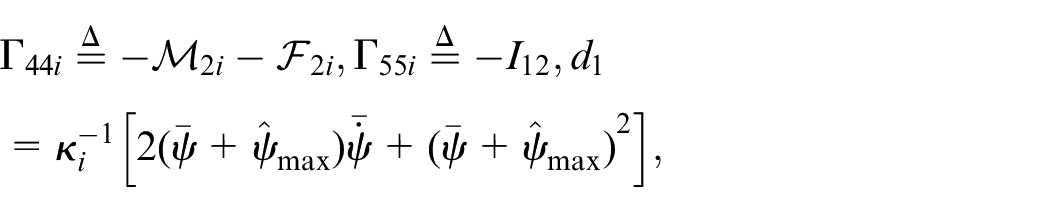
where
where
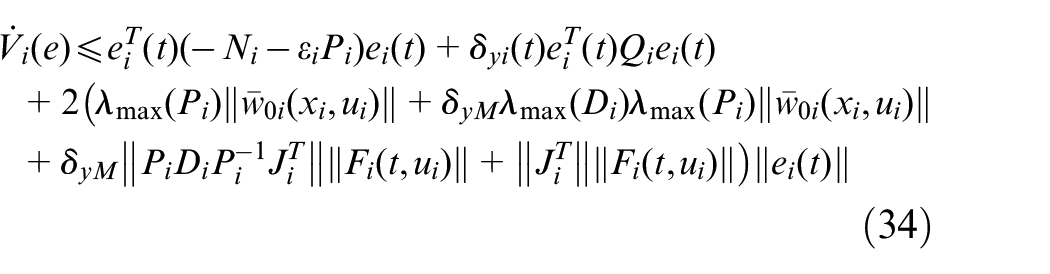
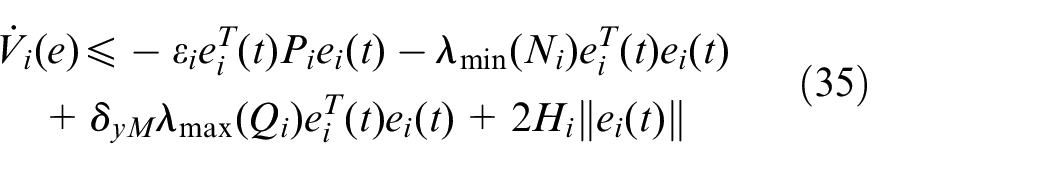
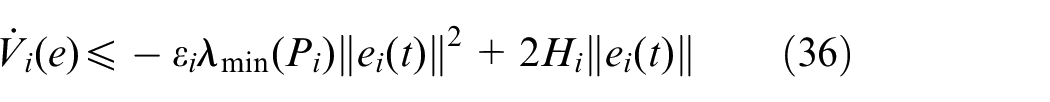
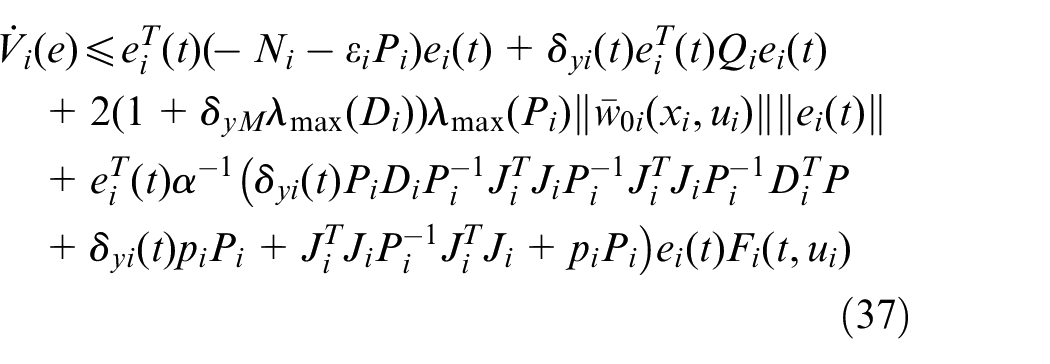
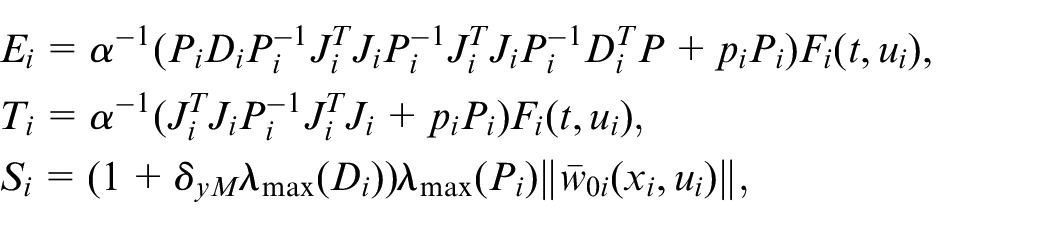
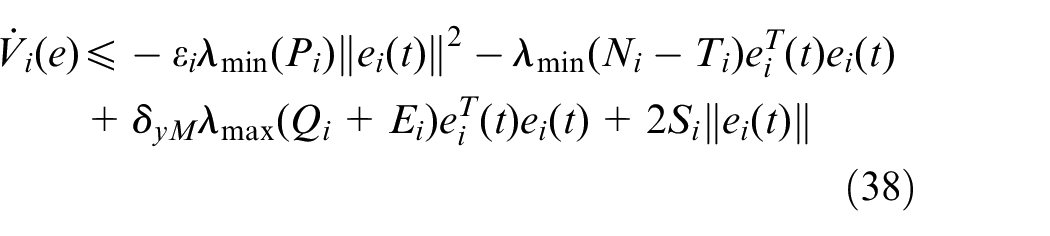
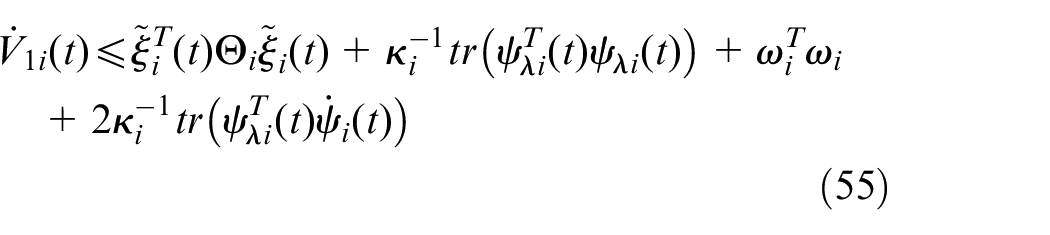
Then the time derivative of
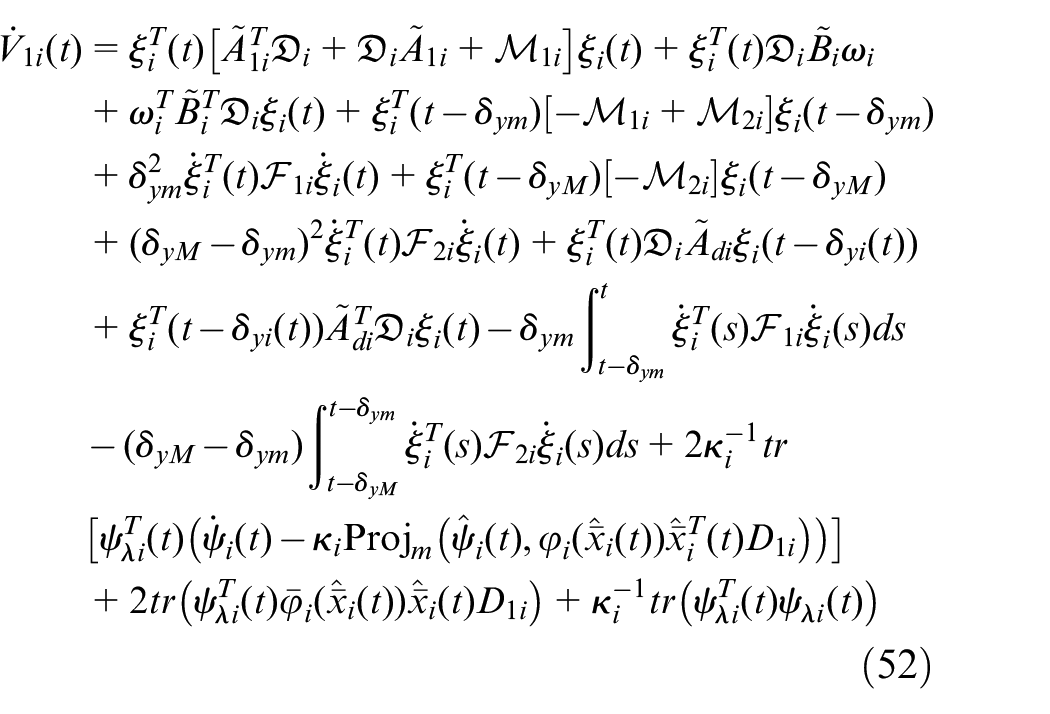
There is also
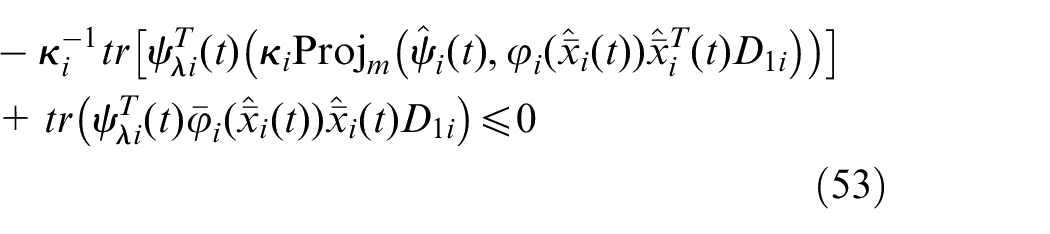
By using Jensen inequality and considering (53), one can get
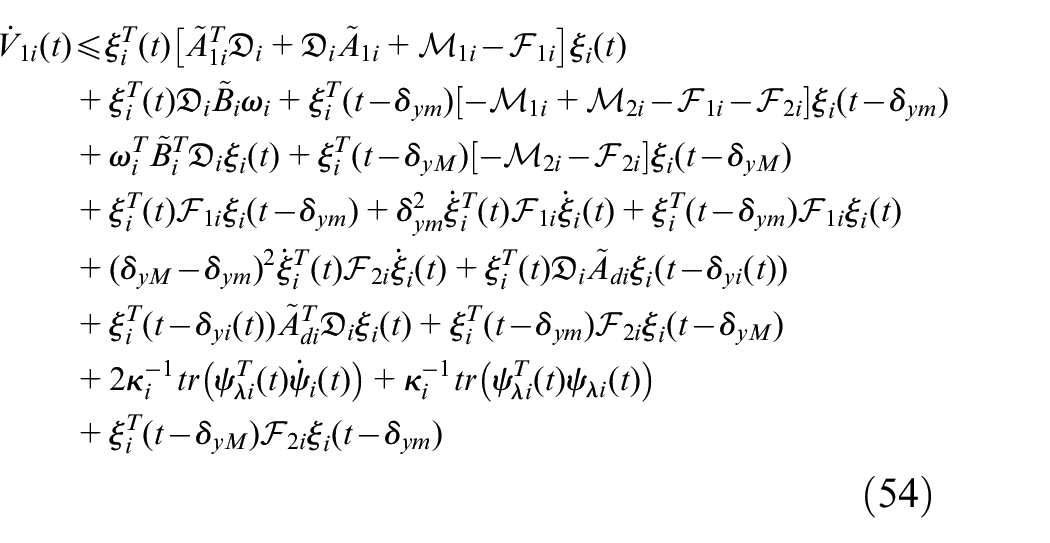
Similarly, we have
where
Transform (55) into the following form:
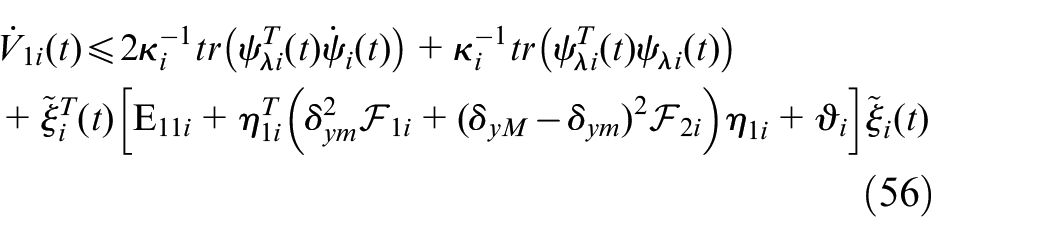
By using Schur complement theorem, if the condition (49) holds, then
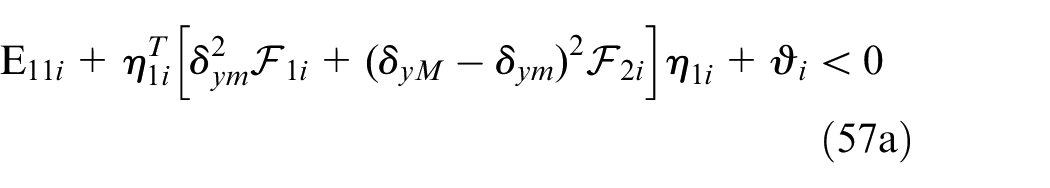
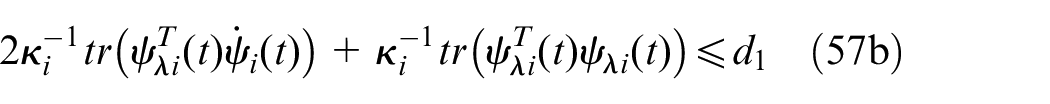
Hence,
where
To show the ultimate bounds for
where
Therefore, if (49) satisfies, then (48) is uniformly bounded.
String stability analysis
Since the correction signal
First, substituting the controller (42) into (7) yields
Then, based on (1) and (56), we have
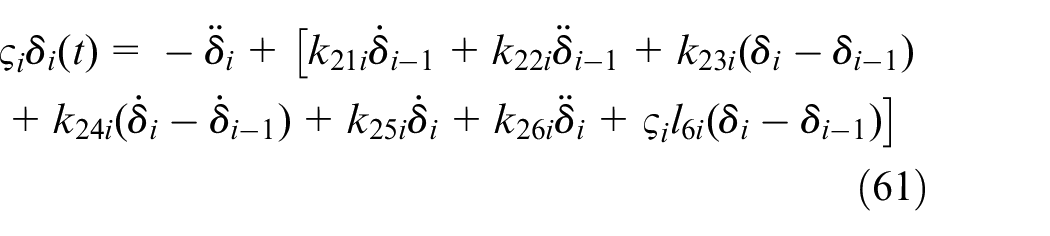
Obviously, the string stability depends on the relationship between adjacent vehicles, and through simple algebraic operations, one can derive
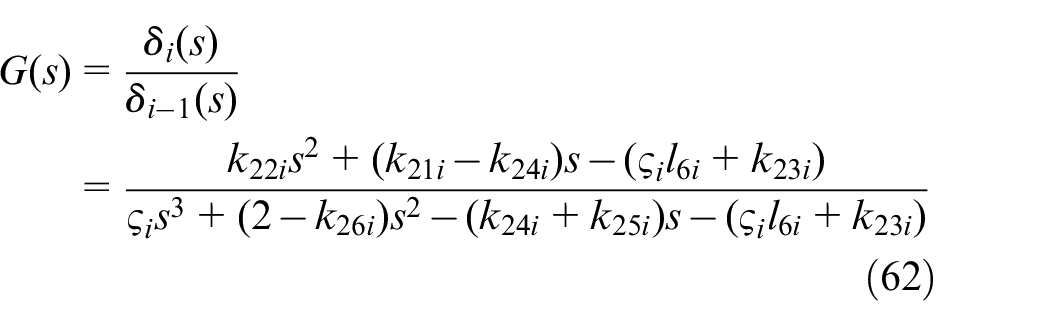
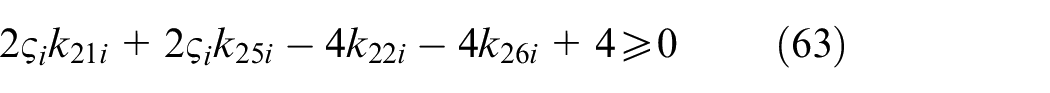
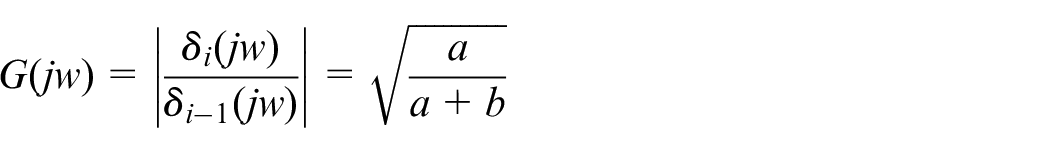
where
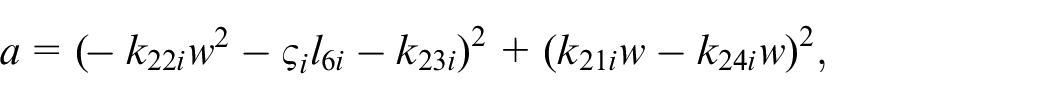
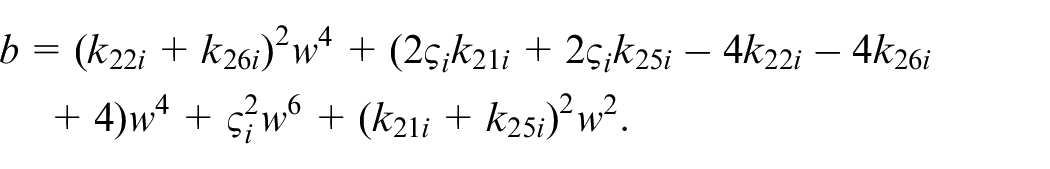
Thus, the results of Theorem 4 are directly used as the gains selection conditions to meet the string stability. This completes the proof.
Simulations
In this section, the designed controller is applied to the CV system composed of five vehicles to verify it’s effectiveness in suppressing attacks under various driving conditions. The virtual simulation experiments are established in MATLAB.
In order to achieve the maximum effect of the replay attack and reduce the probability of being detected, the number of replay attacks against the following vehicle may be different under different road conditions. Therefore, the number of replay attack against the following vehicle is set as
The parameters of vehicle.
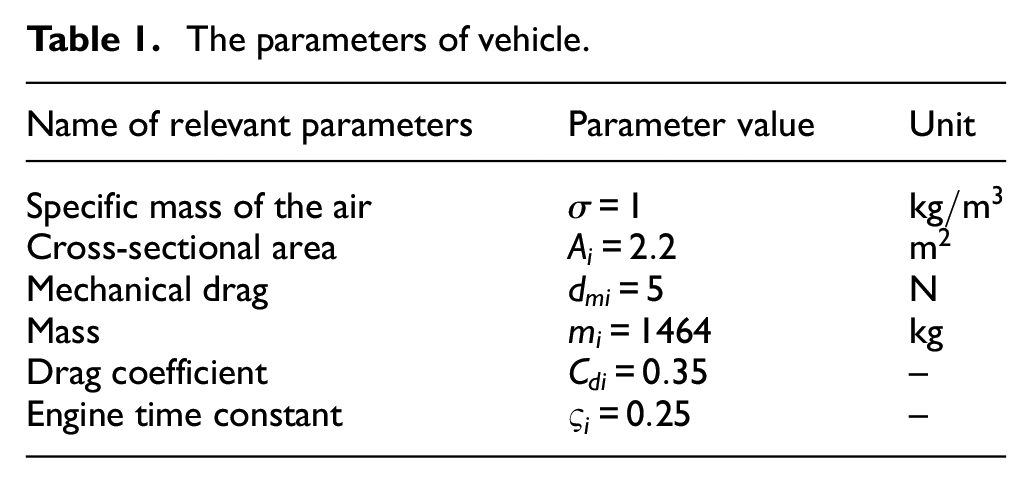
Substituting these parameters into dynamic equations (4c) and (5) yields
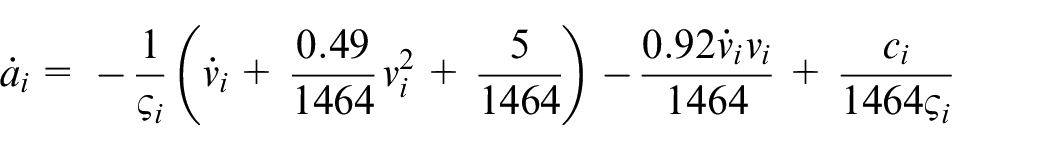
The linearization controller in (6) is given as
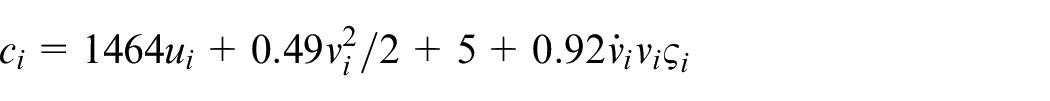
This set of parameters are selected to simulate a CV with smart sensors
The details on how to compute observer gain matrix
Time-varying delay.
In order to well illustrate the effectiveness of the controller designed in this paper, numeral simulation is carried out in the following two scenarios.
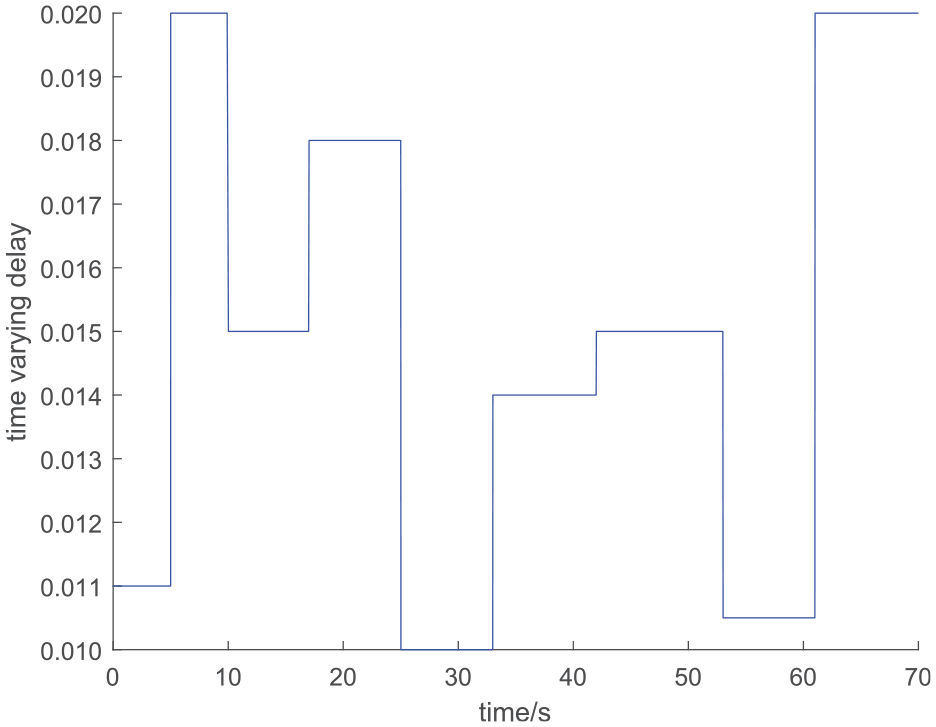
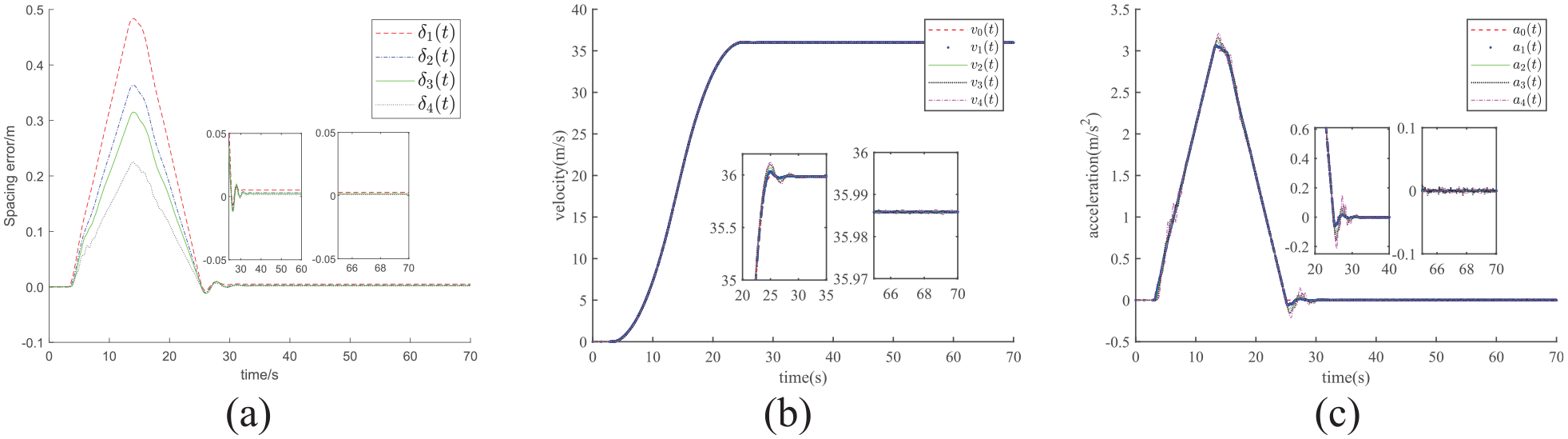
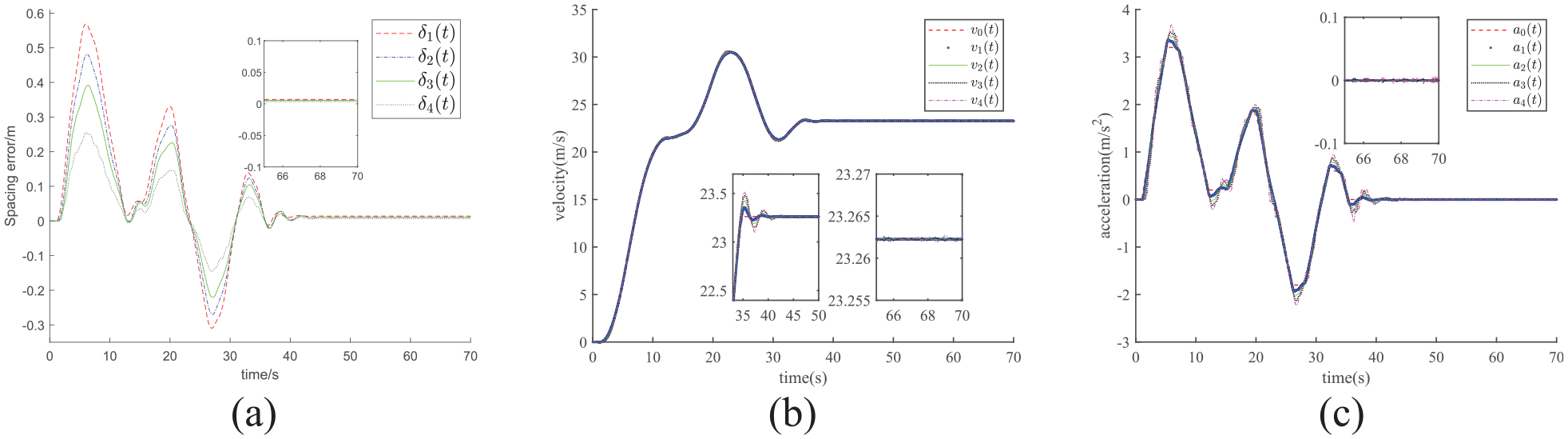
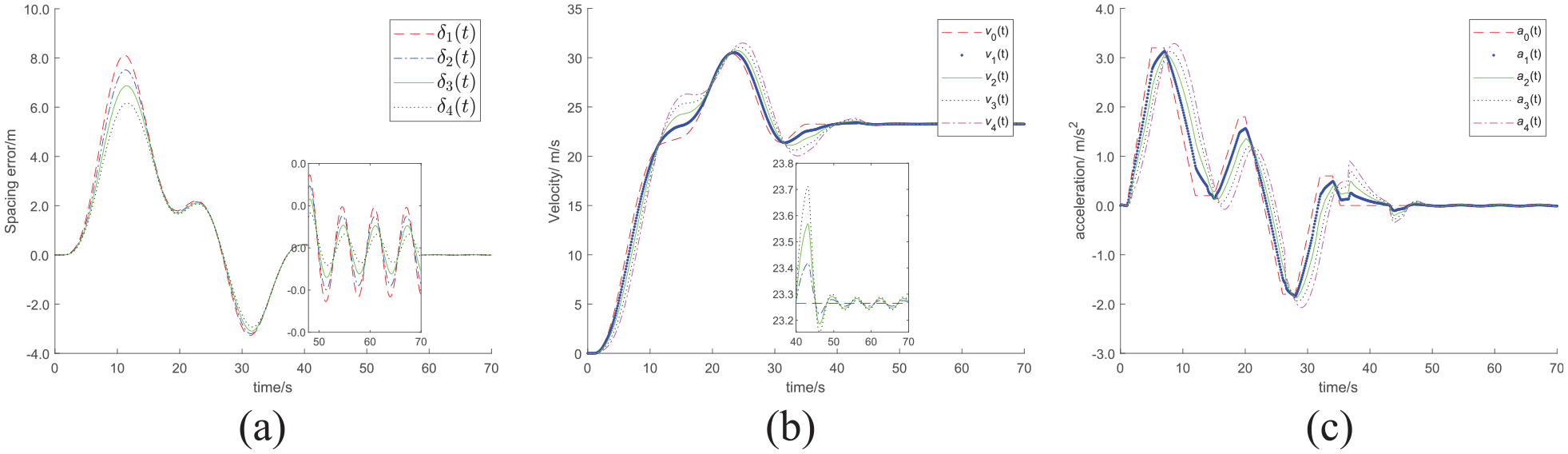
Emergency acceleration of leading vehicle
In this scenario, the leader quickly accelerates from 0 to 36 m/s within 22 s and then maintained a constant speed. The comparison between the proposed controller and the controller in Yue et al. 31 are shown in Figures 5 and 6, respectively. It can be seen from Figures 5 and 6 that the maximum distance errors under the two control methods are 0.49 and 9.71 m, respectively. Although both simulation results satisfy the string stability, the tracking error in Yue et al. 31 is too large, which will lead to vehicle rear-end tracking. The comparison between Figures 5(b), (c) and 6(b), (c) shows that the jitter of velocity and acceleration tracking in Yue et al. 31 is larger than that in this paper, which results in a very poor ride experience in practical applications. Obviously, in this scenario, the performance of the controller designed in this paper is much better than the control method in Yue et al. 31
The control performance of CV under the proposed controller: (a) position error, (b) velocity tracking, and (c) acceleration tracking.
The control performance of CV under the controller in Yue et al. 31 (a) position error, (b) velocity tracking, and (c) acceleration tracking.
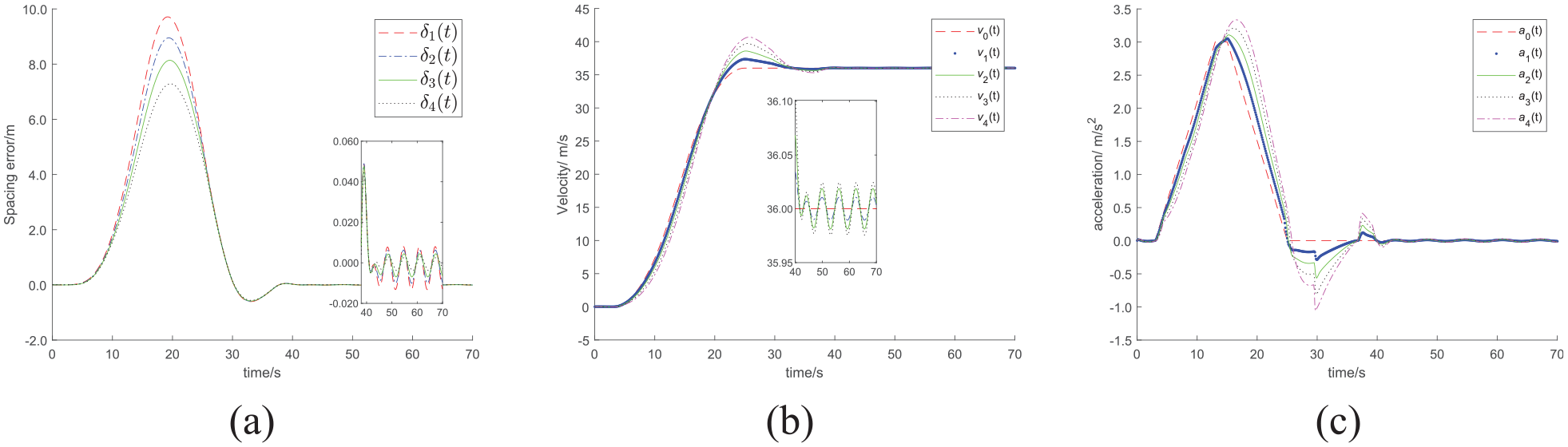
Frequent acceleration and deceleration of leading vehicle
In this scenario, the leading vehicle accelerates from 0 to 21.50 m/s in 11 s, and then accelerates to 30.40 m/s after a short uniform speed of 2.00 s, then slows down to 21.40 m/s in 5 s, and then immediately accelerates to 23.20 m/s and maintains uniform motion.
The maximum spacing error in Figure 7(a) is 0.57 m, but the maximum spacing error in Figure 8(a) is 8.12 m, which is much larger than the safe distance of CV and the inevitable rear-end traffic accident. It can be seen from Figure 7(b) and (c) that even in this complex scenario, the proposed controller in this paper can achieve fast and accurate tracking of velocity and acceleration, while the control effect obtained with the controller in Yue et al. 31 is as good. It can be clearly seen that there is jitter in Figure 8(a) to (c). In addition, the CV system with the proposed controller achieves stability at 41.2 s, while the CV system with the controller in Yue et al. 31 tends to be stable at 49.5 s.
The control performance of CV under the proposed controller: (a) position error, (b) velocity tracking, and (c) acceleration tracking.
The control performance of CV under the controller in Yue et al. 31 (a) position error, (b) velocity tracking, and (c) acceleration tracking.
However, once the attack is too large, the degree of attacks:
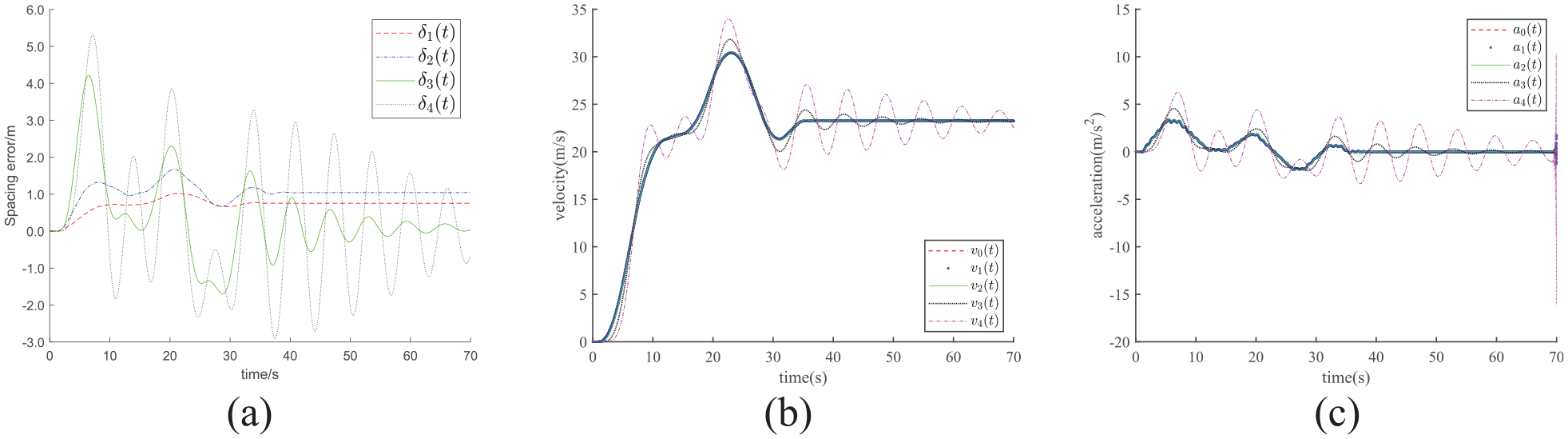
The control performance of CV under the proposed controller: (a) position error, (b) velocity tracking, and (c) acceleration tracking.
Conclusion and future work
In this paper, a novel decentralized CV control scheme based on the variable structure observer and adaptive integral sliding mode technique has been developed with replay attack, DoS attack, and output delay. A corrective signal is designed for the deception attack to eliminate the influence of deception attack on the CV system. By adopting Lyapunov-Razumikhin method, the state estimation error of CV system has been shown to asymptotically converge to zero, which can reduce the negative effect of the replay attack and DoS attack. Furthermore, the robust asymptotic stability of CV system has been guaranteed by using the emerging technique of robust control for time-delay systems. At the same time, the string stability of CV has also been guaranteed, even under the condition of heterogeneous vehicles. The superiority of the proposed scheme has been demonstrated by extensive simulations.
An interesting future topic that merits this research is how to improve the CV performance by considering both longitudinal and lateral control which raise various open problems. One possibility is to apply the method presented in Shao et al.32,33 and Yue et al. 34 to CV control.
Footnotes
Appendix
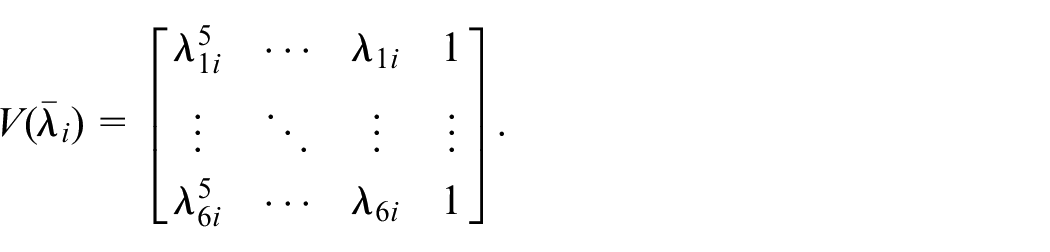
Since
After multiplying the equality (A1) by left
If (A2) satisfies the following conditions, then (19) holds
Introduce the following scalar inequality
Select
Furthermore, by utilizing the conclusions in Ciccarella et al.,
35
namely, if six different eigenvalues take
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This work was funded in part by Dalian High Level Talent Innovation Support Porgram, Grant/Award Number: 2020RQ060; Dalian Science and Technology Innovation Fund, Grant/Award Number: 2019J12GX040; Fundamental Research Funds for the Central Universities, Grant/Award Number: 3132019355
