Abstract
In this study, a co-design method of dual security control and communication is investigated for a nonlinear cyber–physical system (CPS) with an actuator fault and false data injection (FDI) attacks. First, under the discrete event trigger communication scheme, considering the different effects of actuator fault and FDI attacks on a double-end network, a dual security control strategy with active fault-tolerance and active–passive attack-tolerance is proposed. It can accommodate an actuator fault, actively compensate an actuator FDI attack, and passively resist a sensor FDI attack, respectively, thereby establishing a new dual security control framework with fault-tolerance and attack-tolerance. Moreover, the Takagi–Sugeno (T-S) fuzzy model for the nonlinear CPS is established under this framework. Second, by constructing an appropriate Lyapunov–Krasovskii functional and introducing the time-delay theory and the affine Bessel–Legendre inequality, lesser conservative design methods of a robust augmented observer for the estimation of the state, FDI attacks, and fault as well as a dual security controller are obtained. Finally, a classical quadruple-tank model is used to show the validity and feasibility of the proposed method.
Keywords
Introduction
A cyber–physical system (CPS) is a complex system with the highest degree of integration among cyber and physical systems; it realizes real-time perception and control using computational techniques and by communication and control.1,2 Because it is commonly applied in intelligent transportation, smart cities, micro-grids, and other fields, CPS has gained increasing interest and become a prominent topic. 3 Generally, a CPS is prone to risks and can lose stability because of the following reasons: (1) The system operation needs to be accessed and controlled remotely through an open network, and cyber attacks are easy in this scenario, which increases the risks of the system information being destroyed, tampered, or blocked.4,5 (2) The actuator, as the core physical component of a CPS, is highly prone to faults because it needs to operate in a relatively harsh environment for a long time. 6 Therefore, it is significant to study security control for a CPS under the dual threats of cyber attacks and physical faults.7,8
During application, most of the controlled plants are nonlinear. However, modeling a nonlinear system is difficult because of its complexity and particularity and the requirement of high system performance, to solve this problem, the Takagi–Sugeno (T–S) fuzzy model is an effective approach. 9 Its basic concept is to decompose a nonlinear system into a series of linear combinations of local subsystems using IF–THEN rules, and subsequently apply the linear system theory for modeling, analysis, and synthesis. Because of its simple modeling process, it has achieved remarkable results.10–12 There are two aspects of security problems in a nonlinear CPS: physical and cyber security. Physical security refers to the safety and stability maintenance of a CPS when the physical components fail, whereas cyber security refers to the security of the communication network that supports the CPS information perception and interaction.13,14 In view of physical security, fault-tolerant control is an effective method for dealing with component faults, which has advanced in recent years. Passive, active, and active–passive hybrid fault-tolerant methods were respectively adopted in Li and Li, 15 Lan and Patton, 16 and Xu et al. 17 to investigate physical security. However, the above results do not consider the issue of cyber security. Therefore, studying the dual security control problem for a nonlinear CPS based on the T–S fuzzy model is highly challenging, which is one of the motivations of this study.
With the development of CPSs, the security problems of their cyber systems are becoming constantly exposed, and frequent cyber attacks make the control system more vulnerable. In general, cyber attacks on a CPS mainly include denial-of-service (DoS) and false data injection (FDI) attacks. A DoS attack is simple to implement; however, there is no stealth in space and time; therefore, it is easy to detect and prevent.18–20 However, a FDI attack has high concealment and is difficult to detect, resulting in a greater potential threat and higher destructiveness than a DoS attack.21,22 StuxNet virus is a typical example of a FDI attack. 23 For FDI attacks in a CPS, a static output feedback robust control strategy was studied in Su and Ye 24 to achieve stable system operation. In An and Yang, 25 an improved adaptive resilient controller was designed to tolerate attacks passively. In Corradini and Cristofaro, 26 a sliding mode attack-tolerant control strategy was proposed, which effectively realizes a passive defense against FDI attacks. The strategies in Su and Ye, 24 An and Yang, 25 and Corradini and Cristofaro 26 are passive in dealing with FDI attacks, having limited defensive ability, and thus, active defense strategies are more targeted than passive ones. In addition, the above studies only considered cyber attacks in a cyber system. It is well-known that CPS is a combination of physical and cyber systems. Therefore, finding approaches to adopt more active defense strategies to ensure the security of a nonlinear CPS under physical faults and cyber attacks is another research motivation of this study.
In a CPS, the rapidly increasing data generated by its intelligent devices need to be transmitted with limited bandwidth; thus, the inconsistency between the transmission of a large amount of data and the limited communication resources is becoming increasingly important. In the traditional periodic time-triggered communication scheme (PTTCS), the transmission of a large amount of redundant data aggravates the communication burden, and the control strategy design is inappropriately related with the communication. Over the past decade, to solve these problems, a self-triggered communication scheme (STCS), 27 a discrete event-triggered communication scheme (DETCS), 28 and an adaptive event-triggered communication scheme (AETCS)29,30 have been proposed. Among them, the AETCS is novel, and its trigger parameter can change adaptively with respect to the dynamic error of a system. However, once the physical and cyber systems in a CPS are damaged, it is difficult to realize the adaptive coordinates between communication and control under the AETCS. Because the DETCS is simple to implement and can achieve good control performance, it is the most representative trigger scheme. In Lu and Yang, 31 based on the DETCS, a new security observer was designed to estimate a state and an attack. In Li et al., 32 the security consensus problem was considered for multi-agent systems, and an event-triggered control scheme with state dependence was used to update the control input signal. In Gao et al., 33 an event-triggered dynamic output feedback control problem was studied for a discrete Markov jump system, and a dual-event-triggered scheme was implemented asynchronously on the node of a sensor and a controller. The above studies were based on the DETCS, which can effectively save network resources. However, there are few results on the co-design of dual security control and communication for a nonlinear CPS. This is another motivation of this study.
Based on previous investigations, in this study, we aim to co-design dual security control and communication for a nonlinear CPS under the DETCS. The main contributions are summarized as follows:
A new dual security control strategy with active fault-tolerance and active–passive attack-tolerance is proposed, in which an actuator fault and an actuator FDI attack are compensated actively and a sensor FDI attack is defended passively. Furthermore, a dual security control framework is built, which lays the foundation to realize dual security control for an actual CPS with FDI attacks on the dual-end network and an actuator fault.
A robust augmented observer is obtained to accurately estimate the system state, FDI attacks, and actuator fault in real time using the augmented matrix method.
A new T–S fuzzy model of a closed-loop nonlinear CPS is established under the DETCS, which integrates a trigger condition, FDI attacks, and an actuator fault. Subsequently, a co-design method of dual security control and communication with reduced data transmission is established to achieve a balance between dual security control and communication resources.
In the derivation of the robust augmented observer and the dual security controller, an appropriate Lyapunov–Krasovskii function is constructed and the affine Bessel–Legendre inequality is introduced, thereby reducing the conservatism of the system. By an engineering case verification of a quadruple tank, it is shown that the theoretical strategies of this study can effectively resist the adverse effects of FDI attacks and actuator fault and maintain system stability while saving communication resources.
The remainder of this paper is organized as follows. The problem formulation is presented in Section 2. In Sections 3, the design of the robust observer is described. The co-design of dual security control and communication is presented in Section 4. Section 5 discusses the simulation experiments, and the conclusion is presented in Section 6.
Problem formulation
Framework of dual security control
Based on the DETCS, a new dual security framework with an actuator fault and FDI attacks on a double-end network is established, as shown in Figure 1.
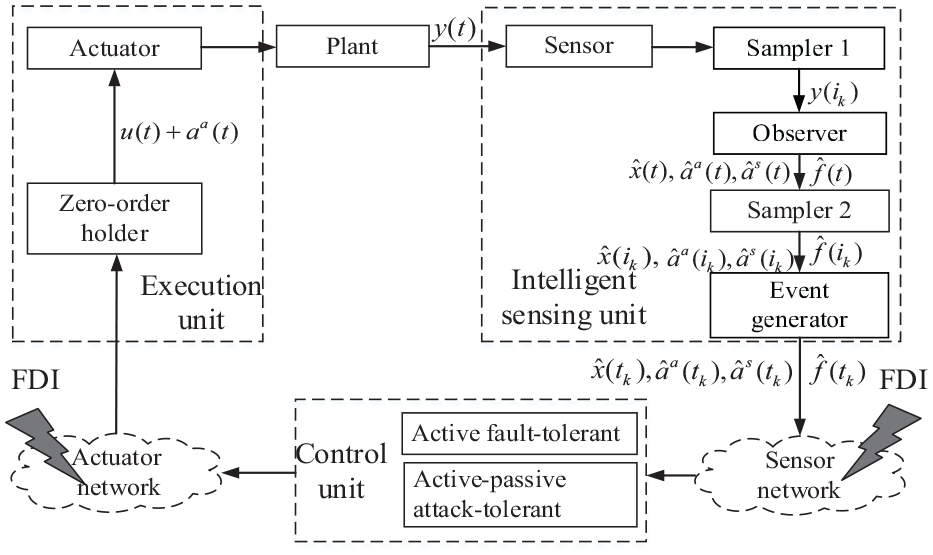
Framework of dual security control.
As shown in Figure 1, the system consists of five parts: a controlled plant, an intelligent sensing unit, a control unit, an execution unit, and a communication network. In this study, an actuator fault and FDI attacks on the actuator and sensor sides are considered simultaneously.
The intelligent sensing unit includes a sensor, samplers, an augmented observer, and an event generator. Among them, the sensor and sampler 1 are used to observe the system output and conduct the sampling at equal periods, and the augmented observer is used to observe the system state, FDI attacks, and an actuator fault. The estimated results are sampled by sampler 2 at equal periods. The event generator is used to determine whether the current sampling value meets the trigger condition. If it does, the sampling value is transmitted to the control unit through the sensor network; otherwise it is discarded. Evidently, the filtered data are transmitted non-uniformly, and the transmission period is longer than the sampling period
The control unit calculates the control quantity with active fault-tolerance and active–passive attack-tolerance on the received data, following which the control data are transmitted to the execution unit. It can be seen that the control action is still conducted in a non-uniform periodic manner.
The execution unit includes a zero-order holder (ZOH) and an actuator. The ZOH holds the data in a non-uniform periodic manner, and it transmits the result to the actuator, which acts on the controlled plant.
System description
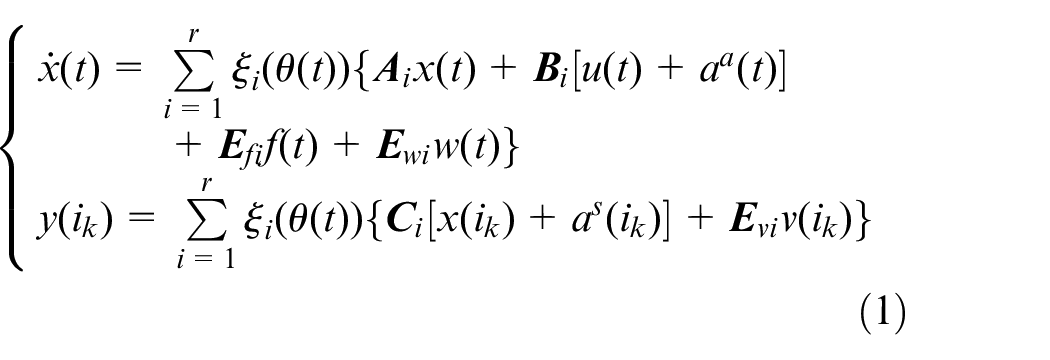
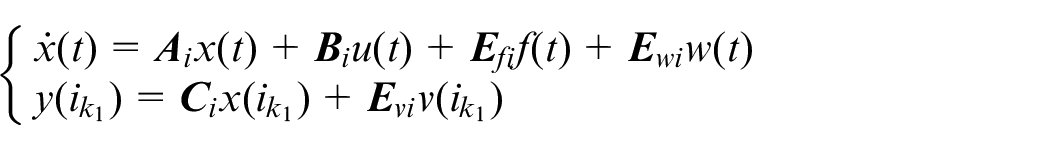
As shown in Figure 1, the plant is continuous, and the operation of the intelligent sensing and control units is completed by the calculation of a digital quantity; therefore, the system is a typical sampling data system. Considering a class of nonlinear controlled plants, the following state equation of the fuzzy system can be obtained by adopting the T–S fuzzy model:
where
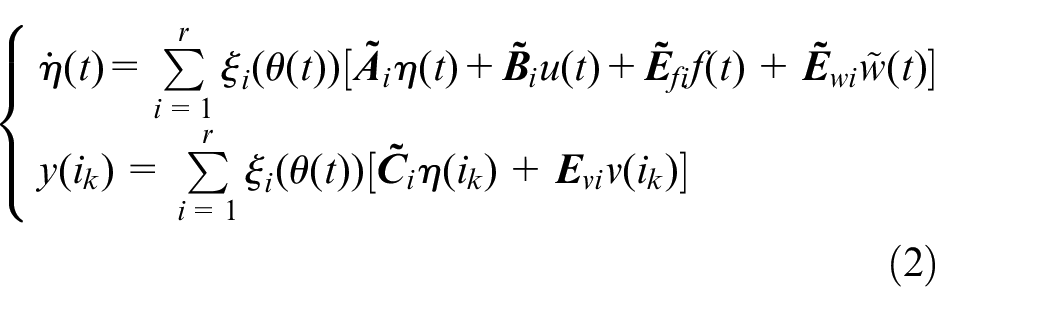
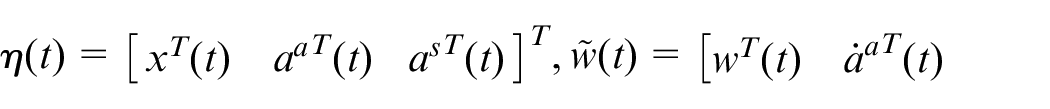
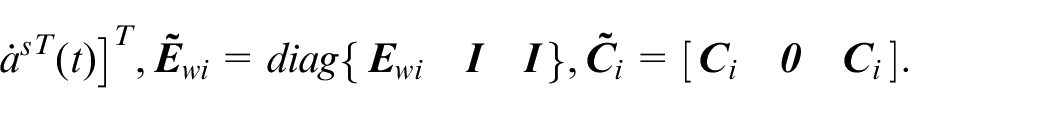
To detect and estimate the FDI attacks and the system state online, system state
where,
Trigger condition of DETCS
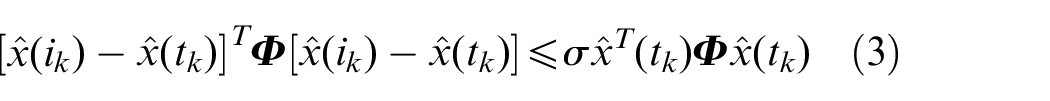
In this study, we adopt the typical DETCS in Peng and Yang 28 to determine whether the current sampling value needs to be transmitted.
where
Analysis of correlated delay interval
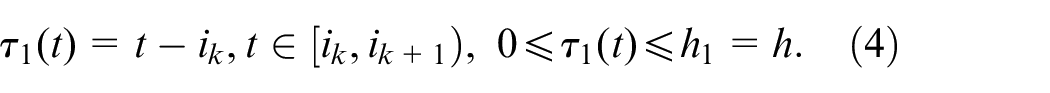
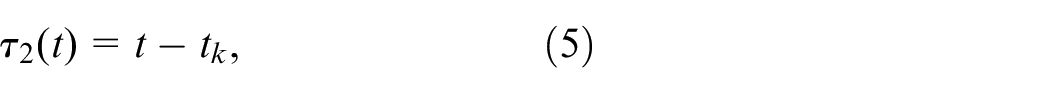
From the above analysis, the estimation of the observer has an equal sampling period, whereas the fault-tolerant/attack-tolerant control is associated with a non-uniform sampling period. Therefore, we treat them as sampling data systems, and subsequently adopt the time-delay theory to deal with these problems.36,37 Similar to the related delay analysis in Li et al., 38 it will not elaborate here.
The time delay function is defined as
where
The upper and lower bounds of the time delay function can be described as follows:
Design of robust H∞ observer for estimation of state, FDI attacks, and actuator fault
Augmented error system
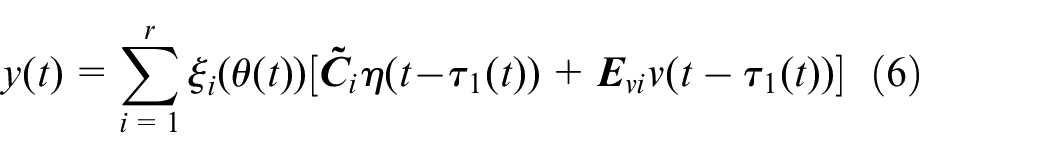
The time delay theory is adopted to analyze the sampling characteristics of the system output in one sampling period; the discrete sampling output equation is held through the ZOH, 39 and the measurement output can be obtained as follows:
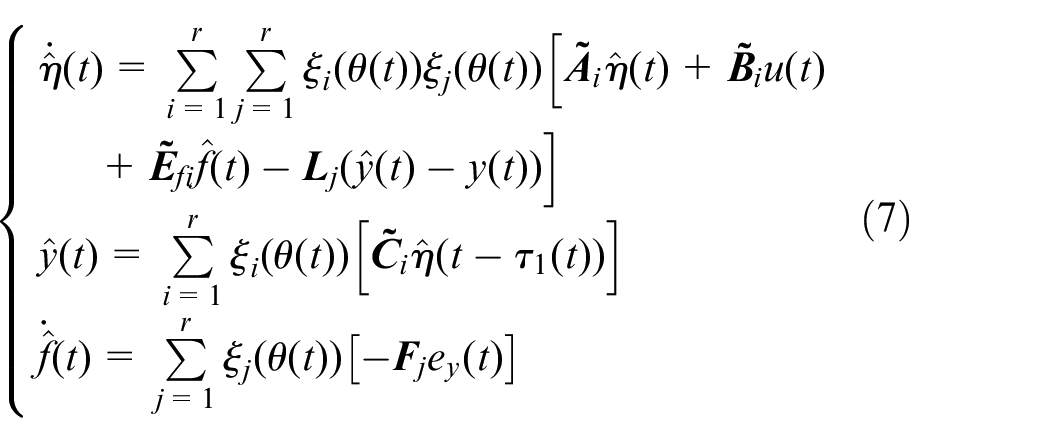
The following observer is constructed to observe the system state, FDI attacks, and the actuator fault:
The following are defined:
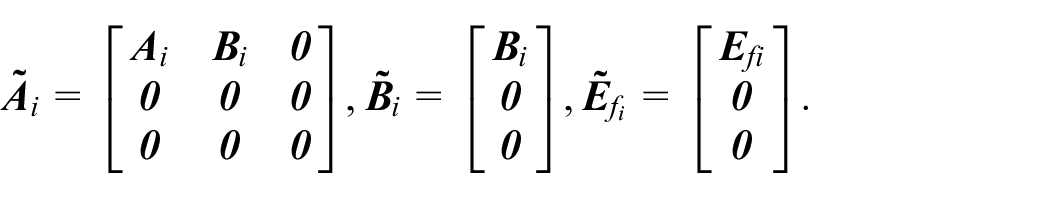
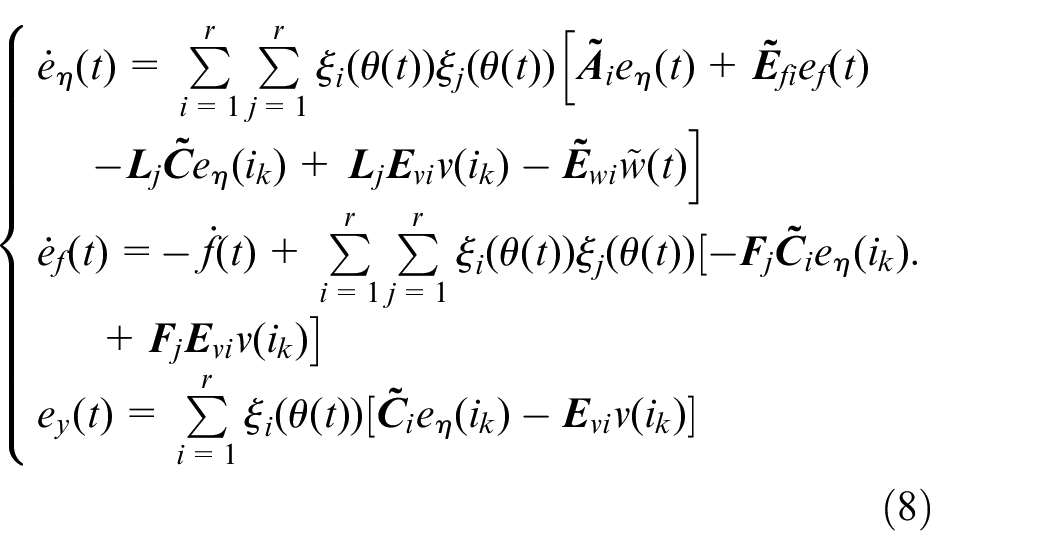
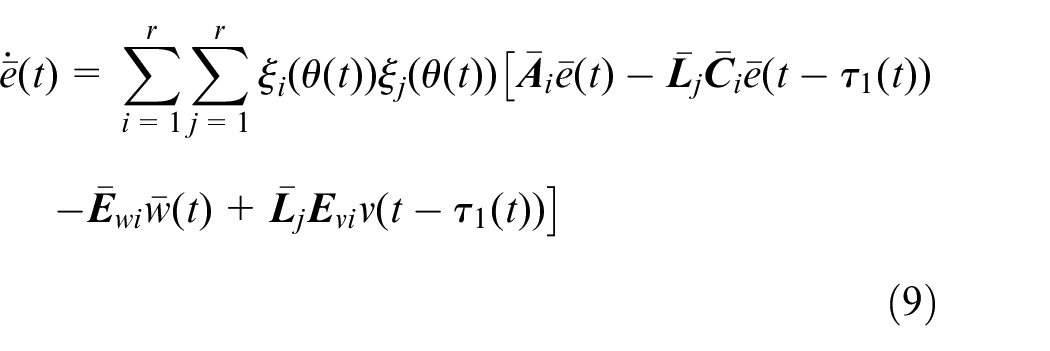
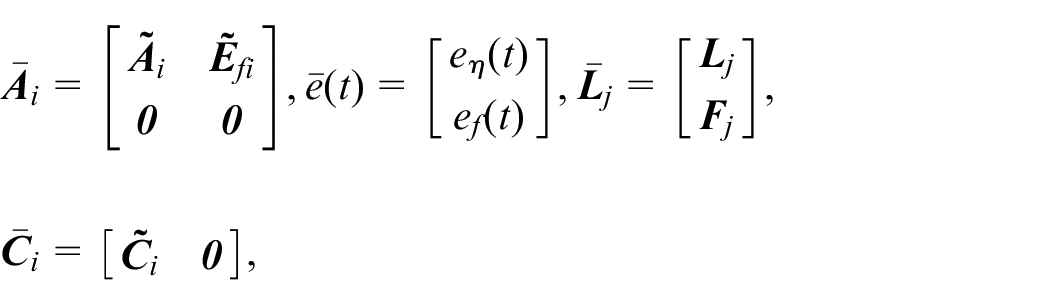
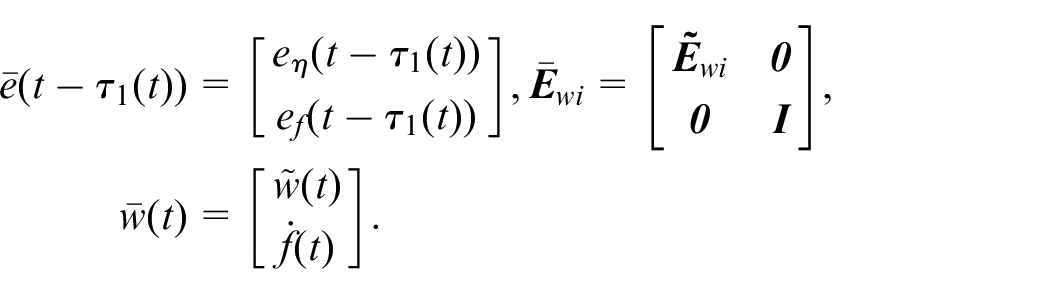
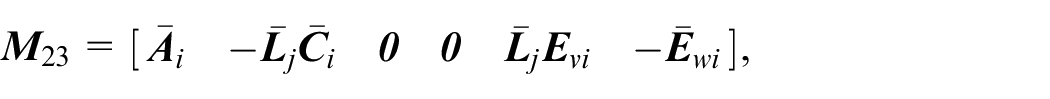
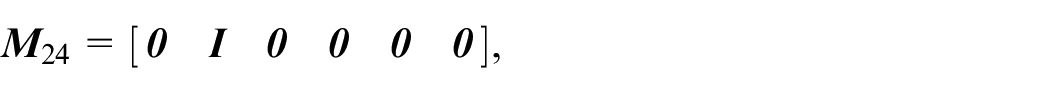
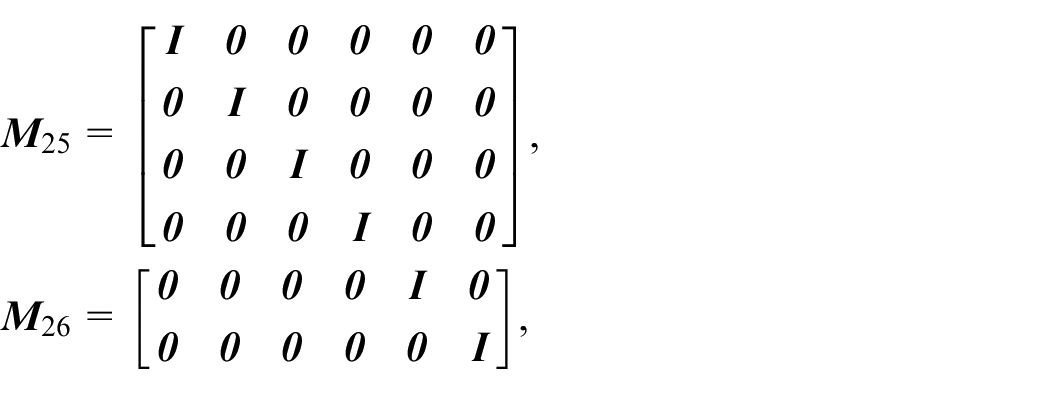
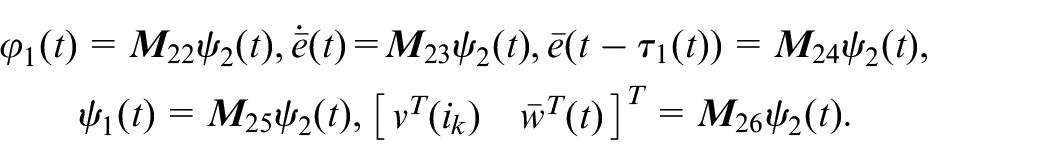
Thus, the augmented error system with the system state, FDI attacks, and actuator fault is as follows:
Where
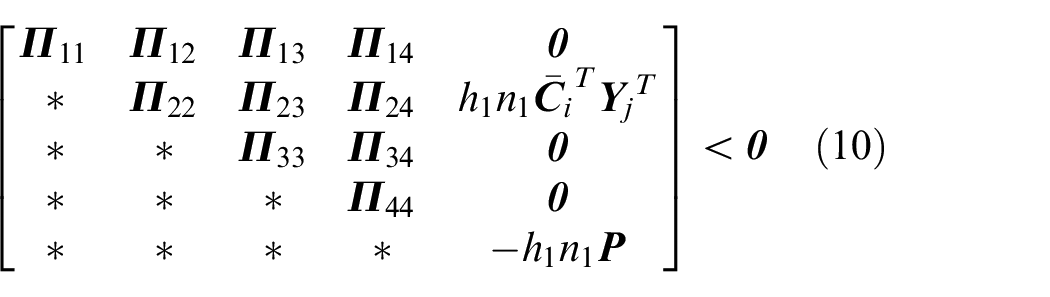
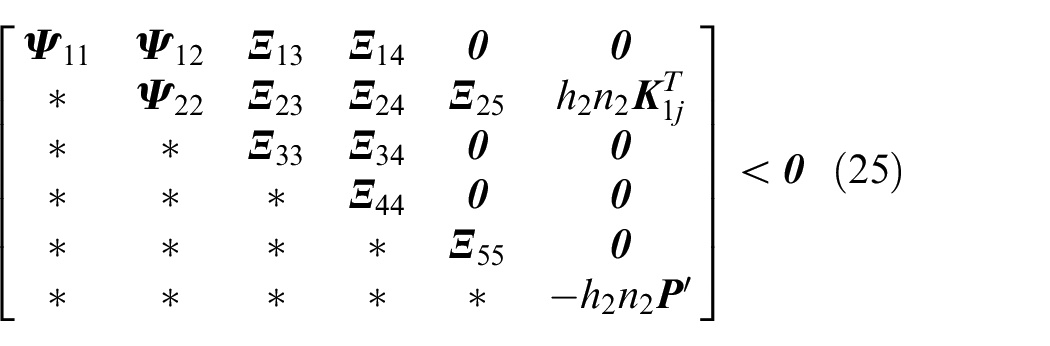
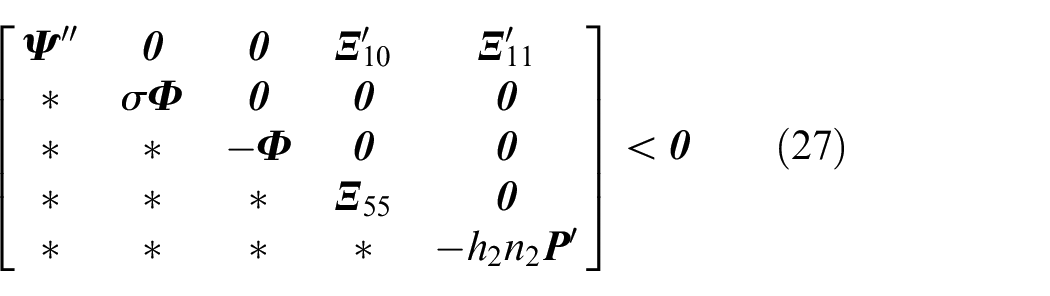
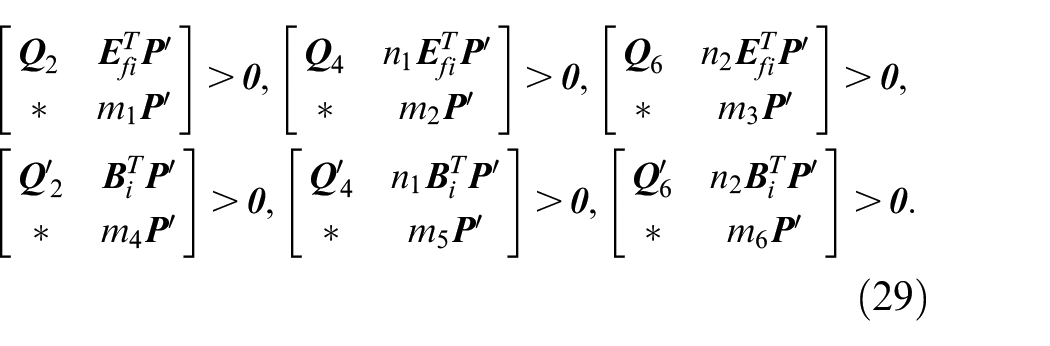
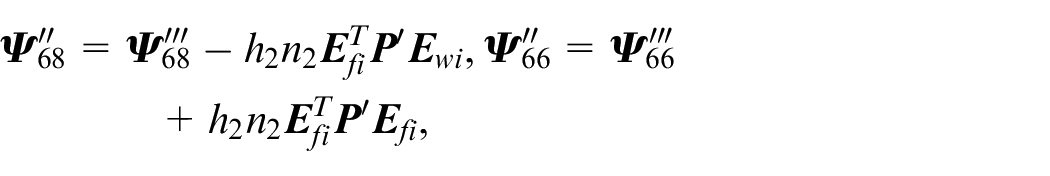
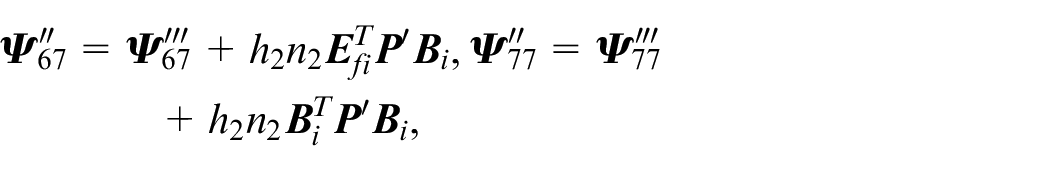
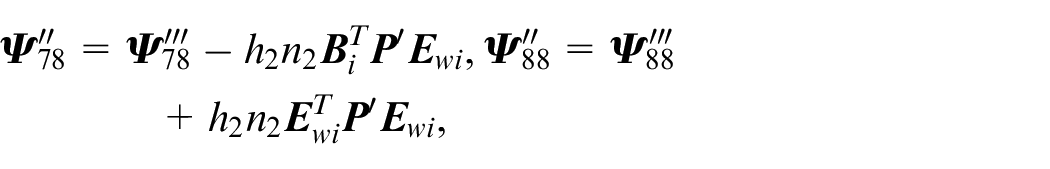
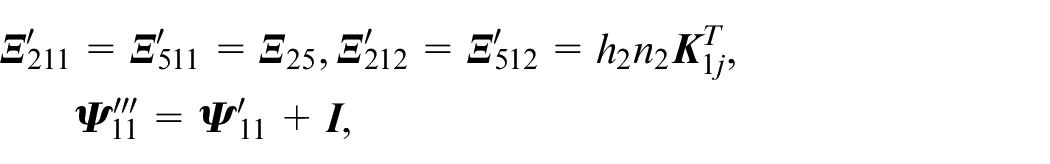
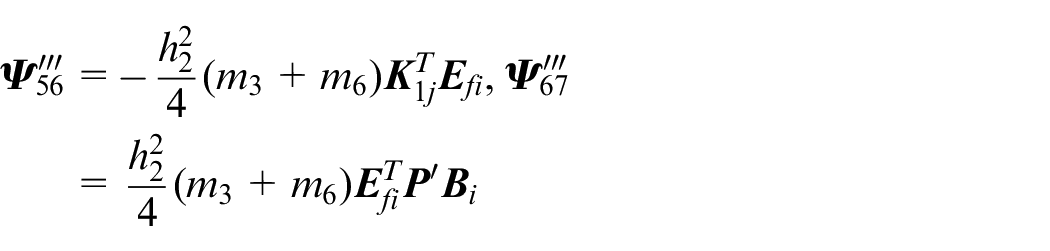
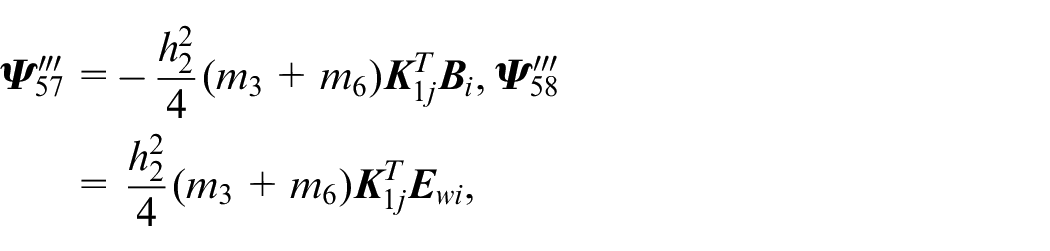
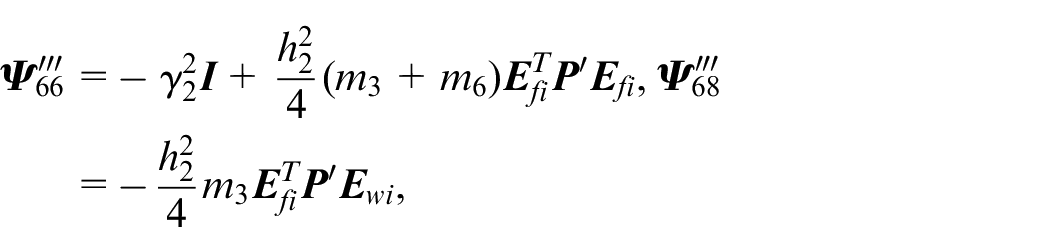
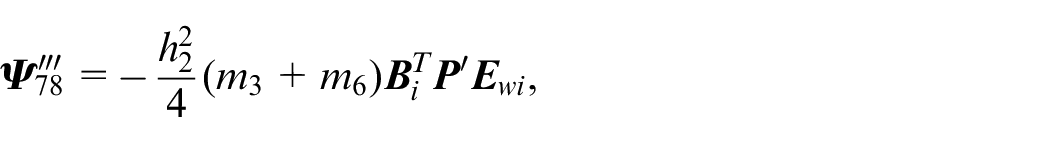
Design of robust
observer
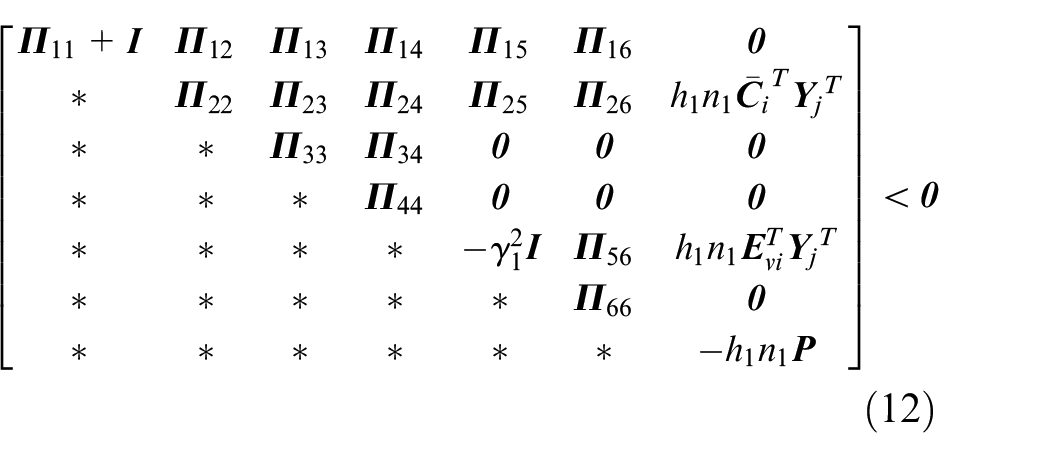
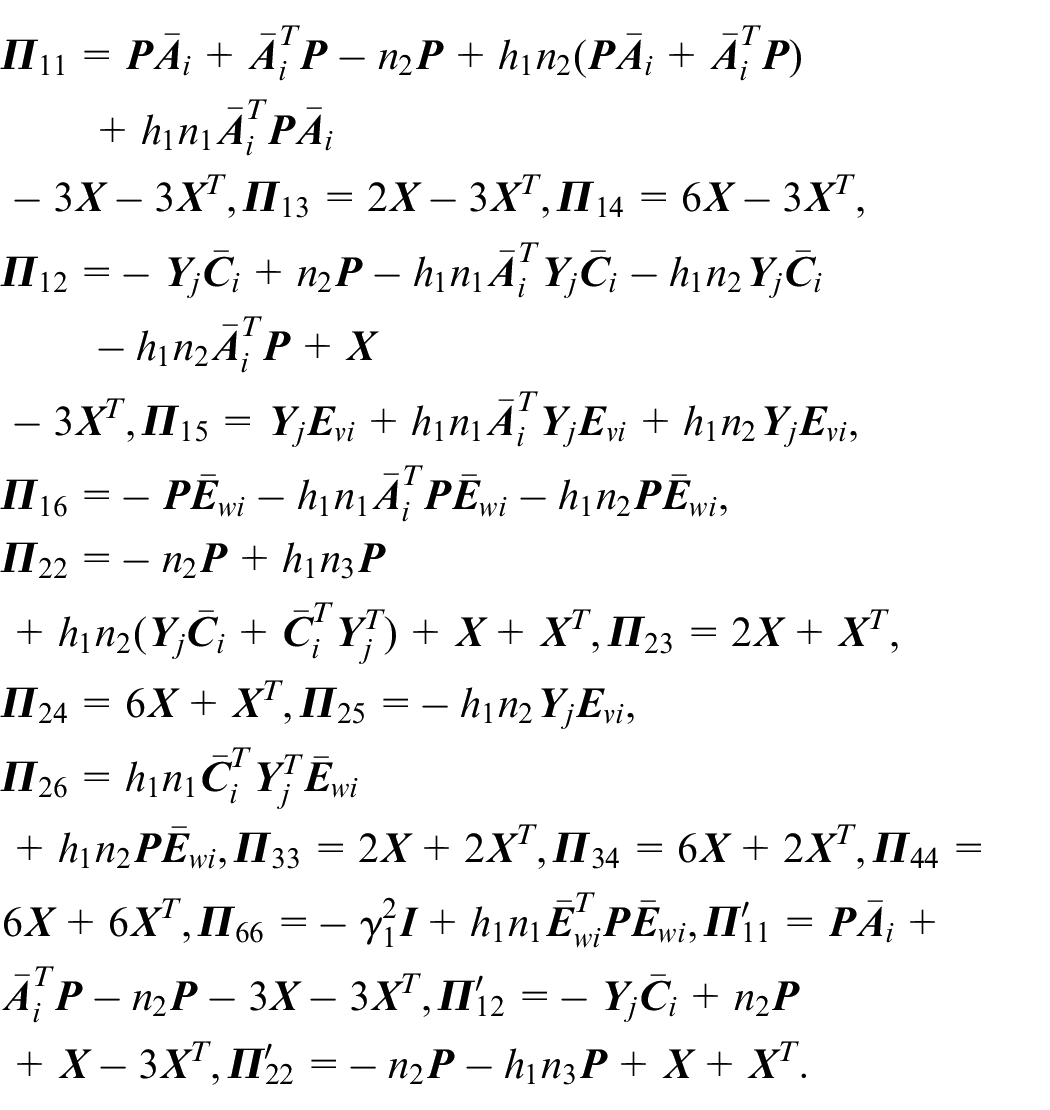
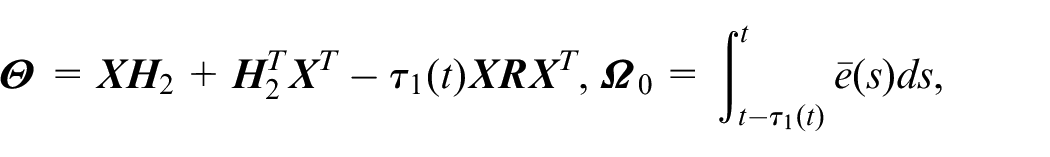
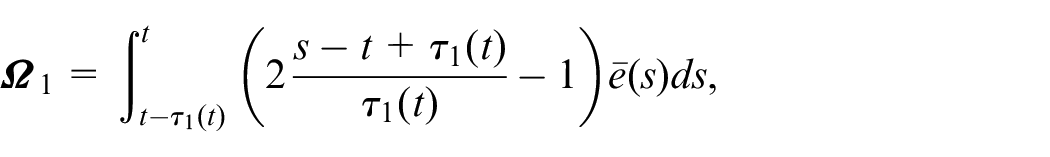
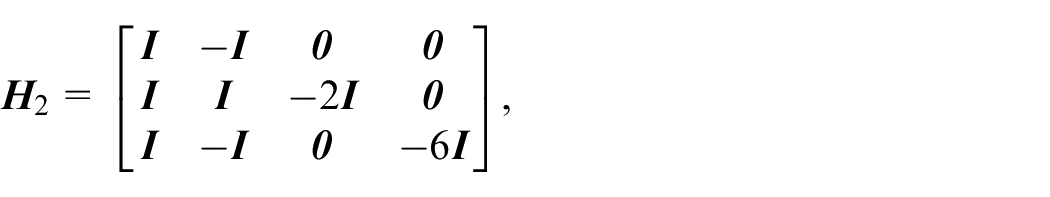
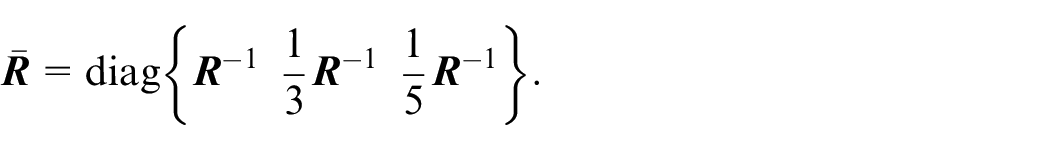
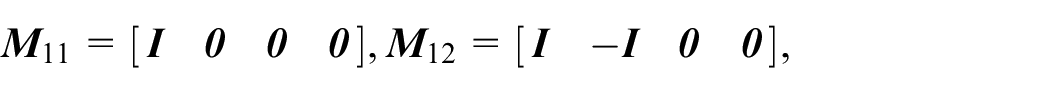
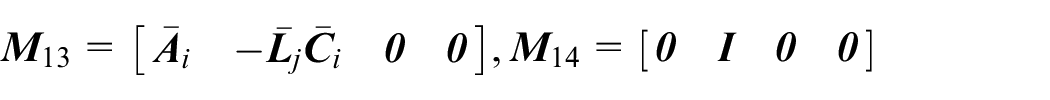
then the error system in equation (9) is asymptotically stable and satisfies the
where
where
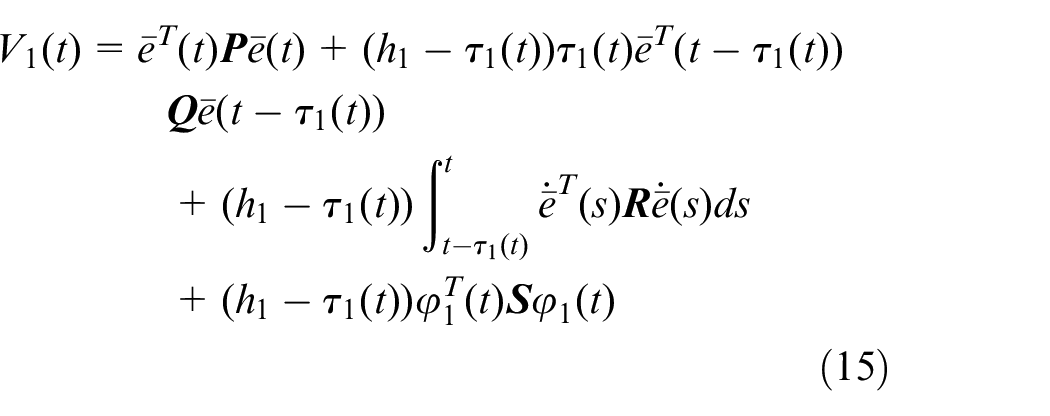
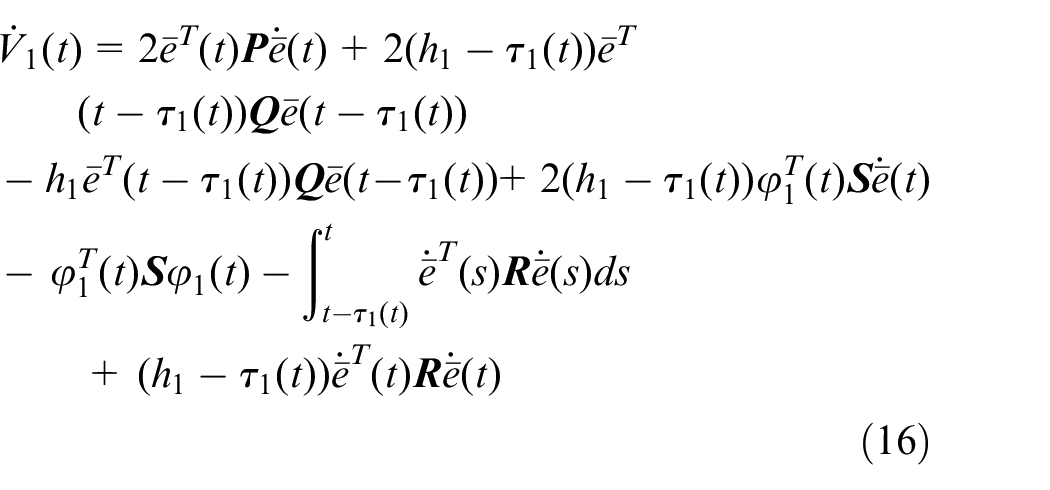
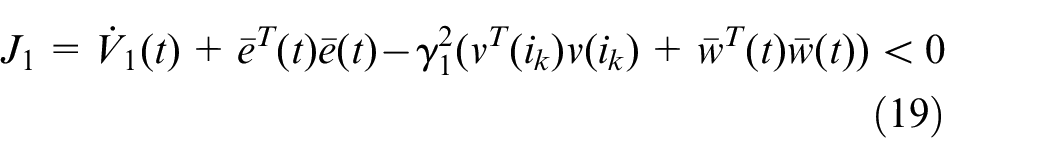
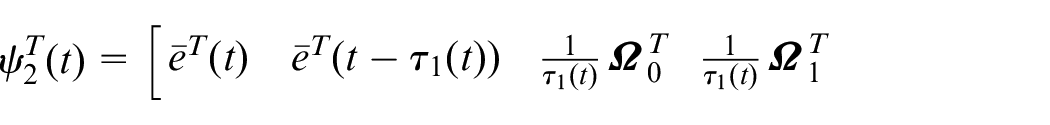
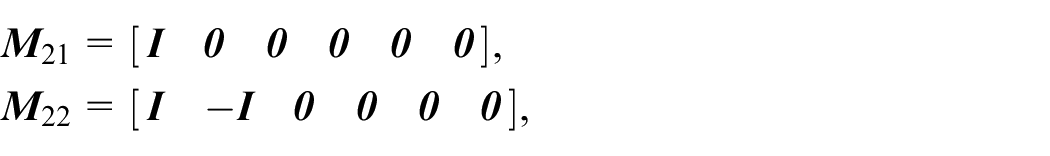
Differentiating along the trajectory of the system in equation (9), we obtain
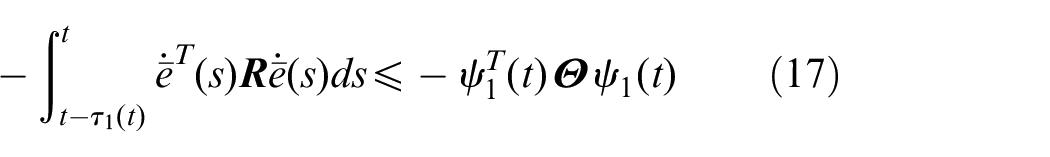
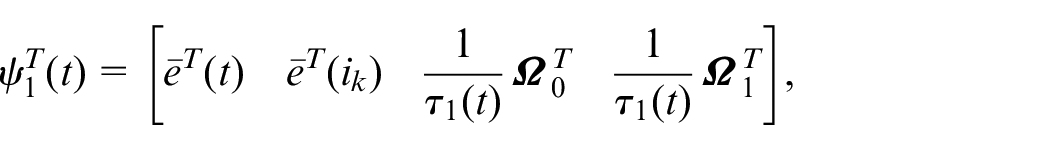
The integral term,
where
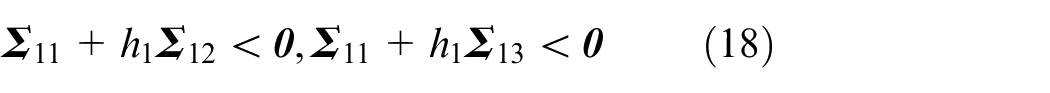
Substituting the inequality in equation (17) into
Thus,
where
If
Under zero initial conditions, when
we define
Furthermore, the following equation can be obtained:
where
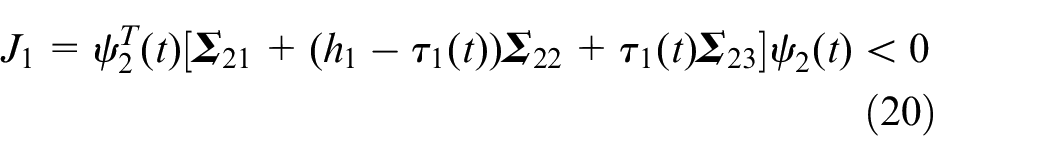
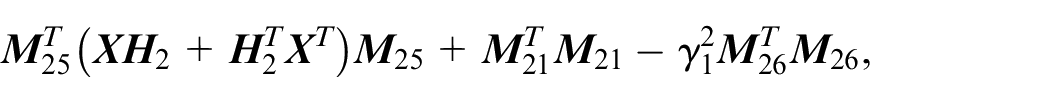
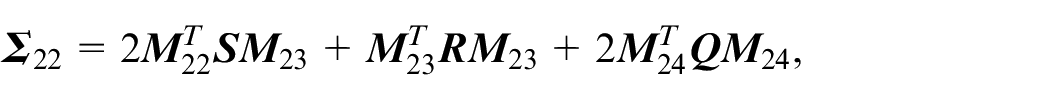
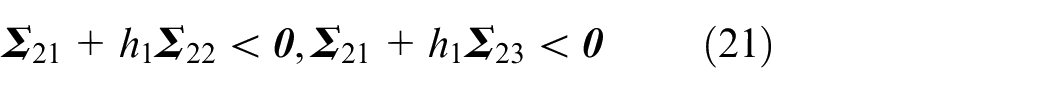
It can be seen from the linear convex combination lemma that
Because the inequalities in equations (18) and (21) are nonlinear, let
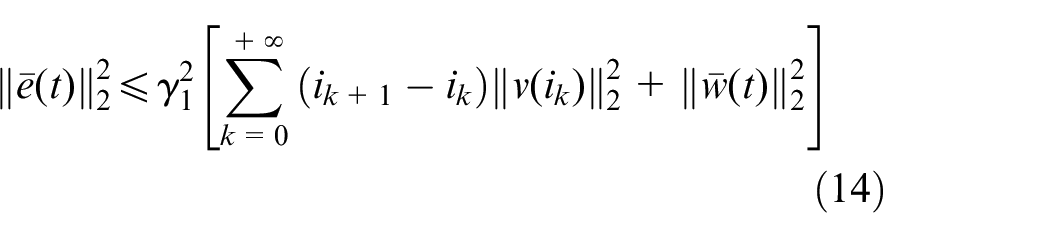
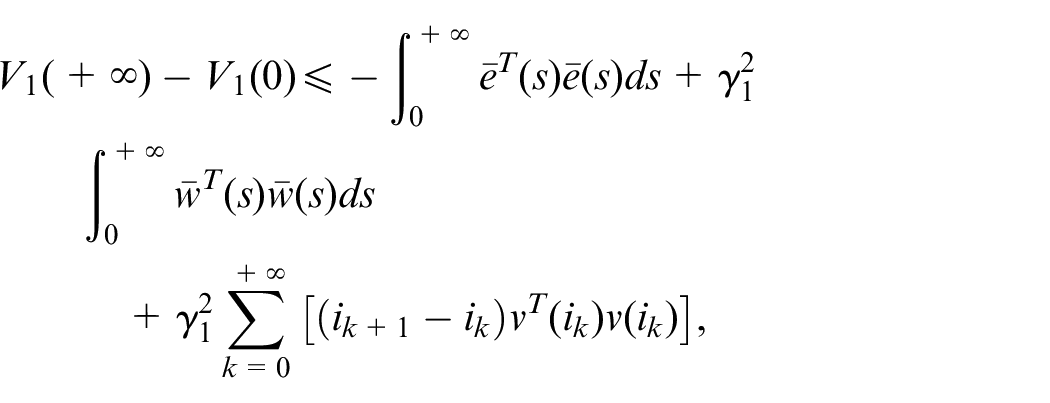
Integrating equation (19) from 0 to
where
Thus,
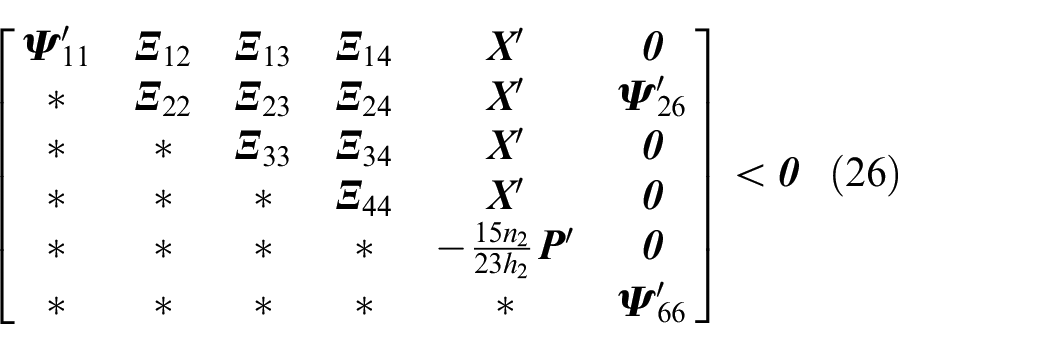
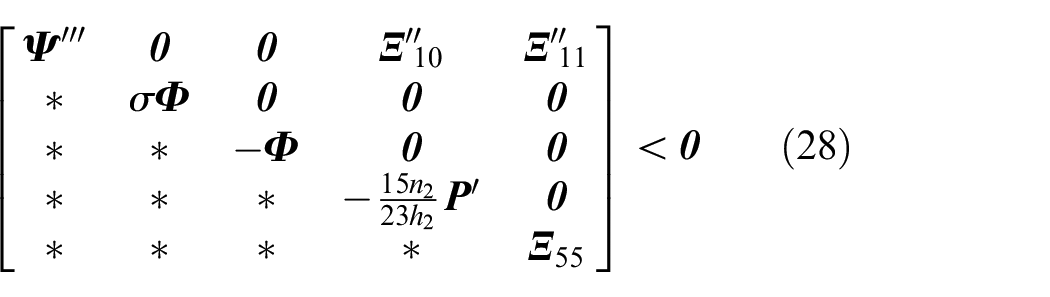
Co-design of robust H∞ dual security control and communication
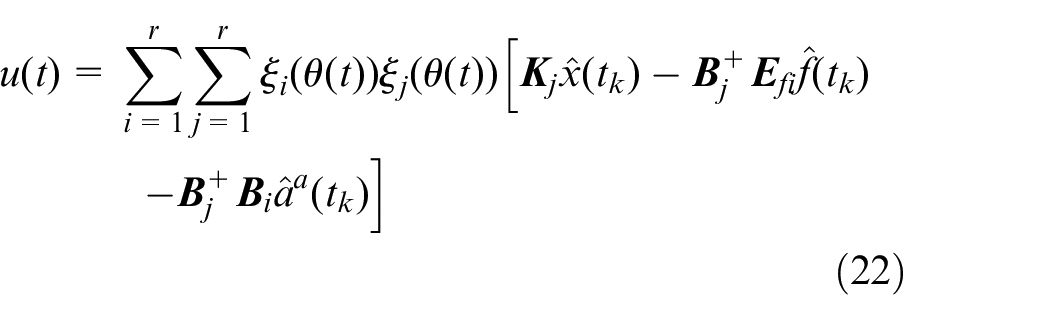
The control input can be updated to apply the following equation:
where
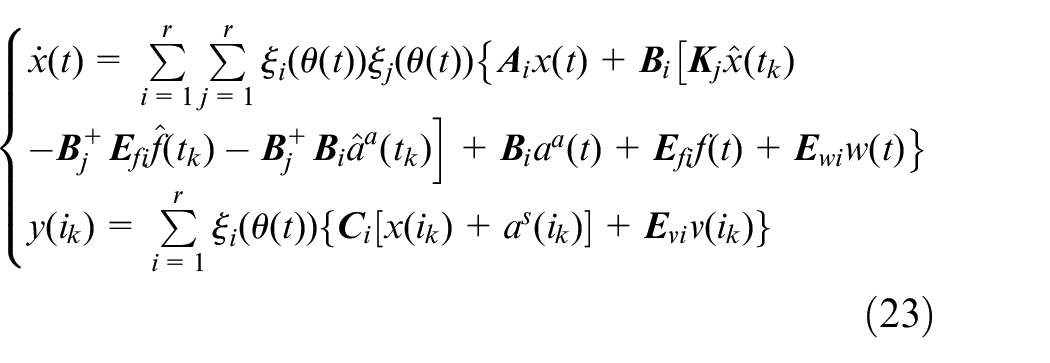
Substituting the control input in equation (22) into the controlled plant model in equation (1), the closed-loop nonlinear CPS model with the actuator fault and the FDI attacks can be obtained as follows:
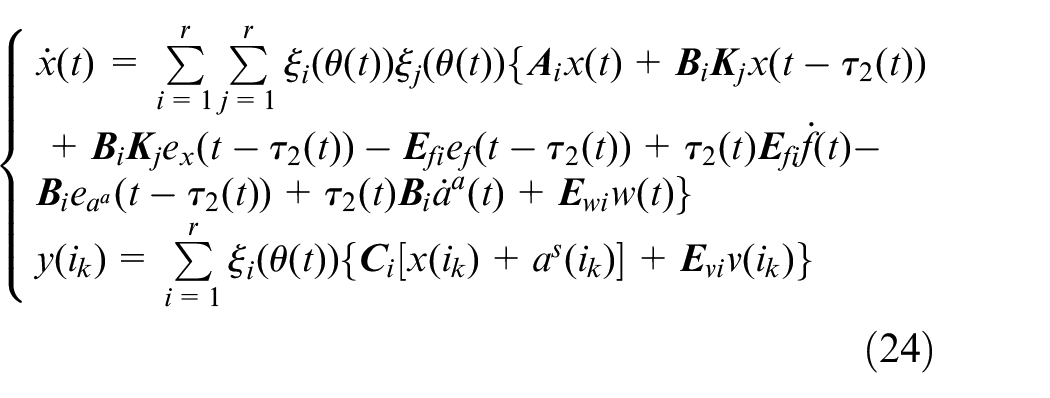
Furthermore, equation (23) can be written as follows:
Design goals
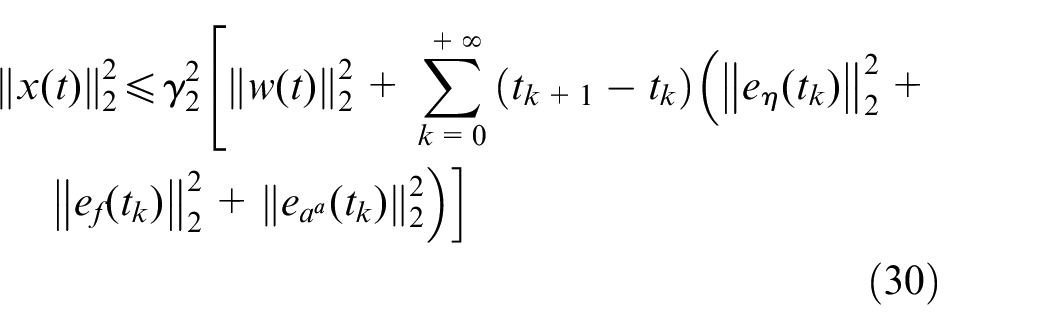
Under the DETCS, for the nonlinear CPS with the actuator fault and the FDI attacks, the co-design goals of fault-tolerance and attack-tolerance and communication are as follows:
In the case of no attack and disturbance, we cooperatively obtain security control matrix
In the case of FDI attacks and disturbances, under zero initial conditions
The nonlinear CPS realizes dual security control; the transmitted data are significantly reduced, saving network resources. Moreover, a trade-off is achieved between the security control performance and the communication resource utilization.
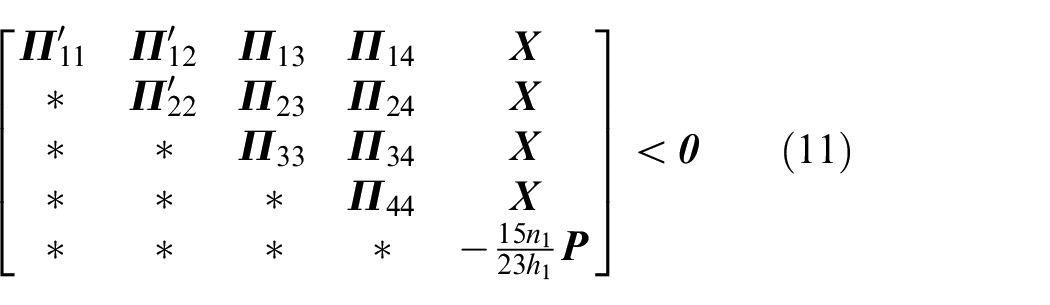
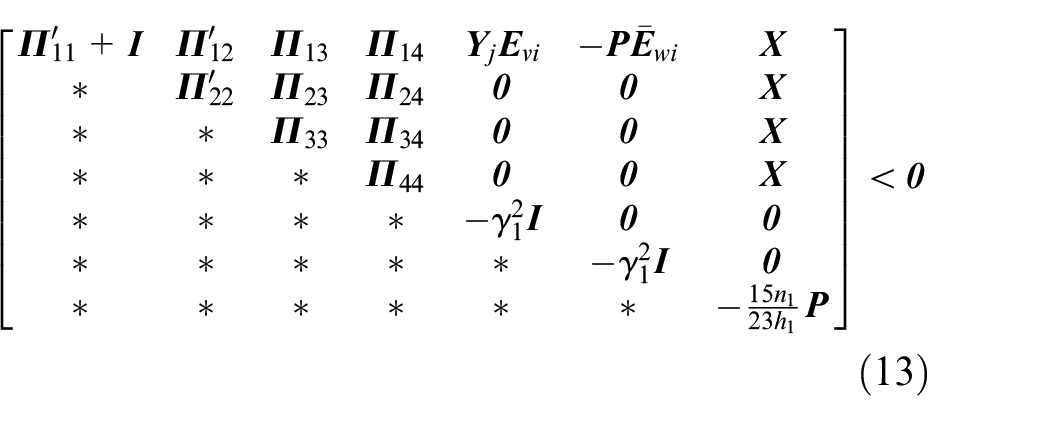
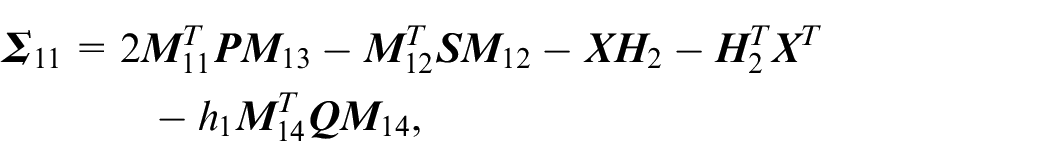
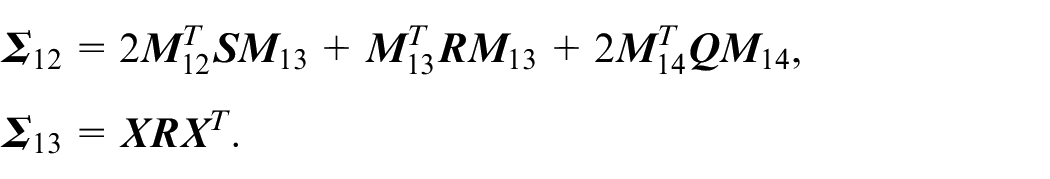
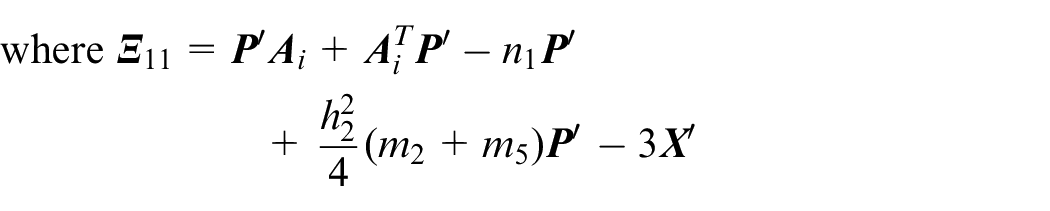
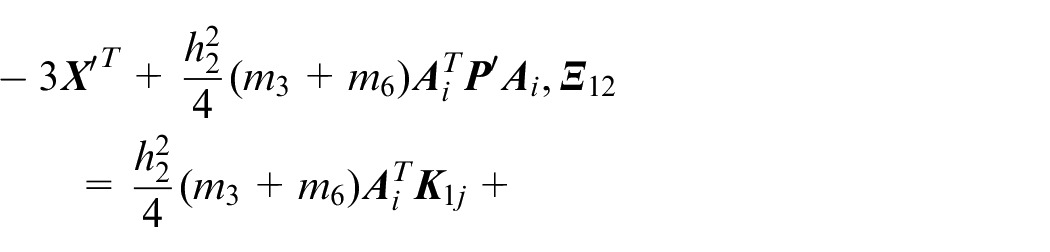
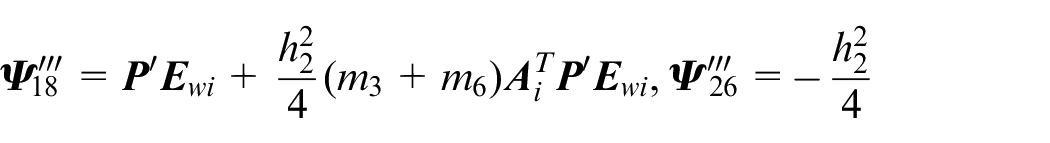
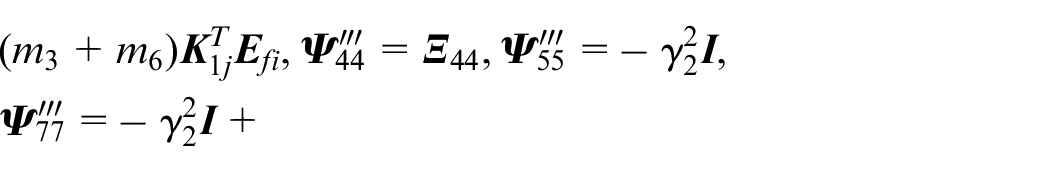
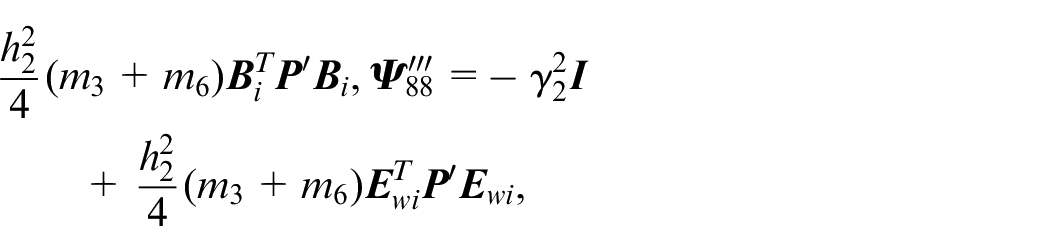
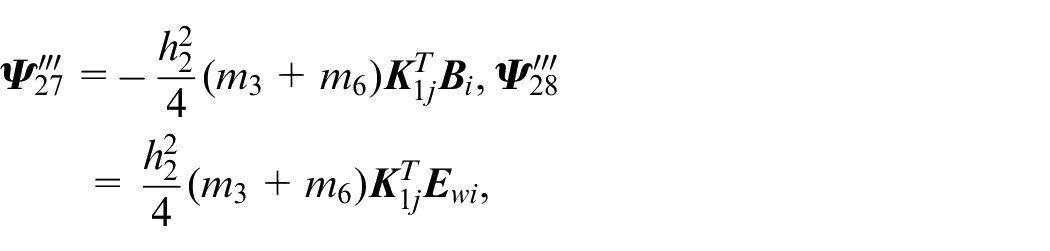
Design of dual security controller
then the system in equation (24) is asymptotically stable, and it meets the
Simulation experiment and results
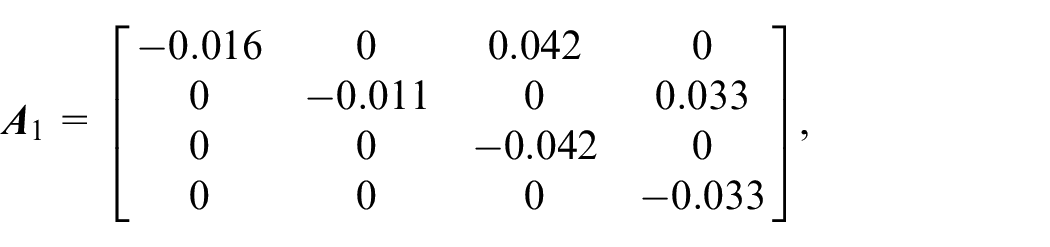
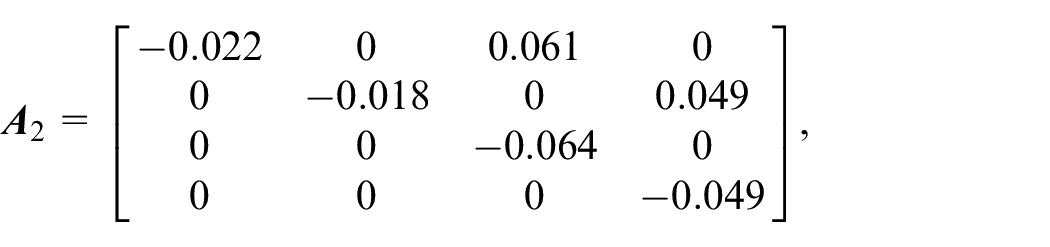
To demonstrate the feasibility and effectiveness of the proposed method in this study, we adopted a classical quadruple-tank model described in Johansson. 42
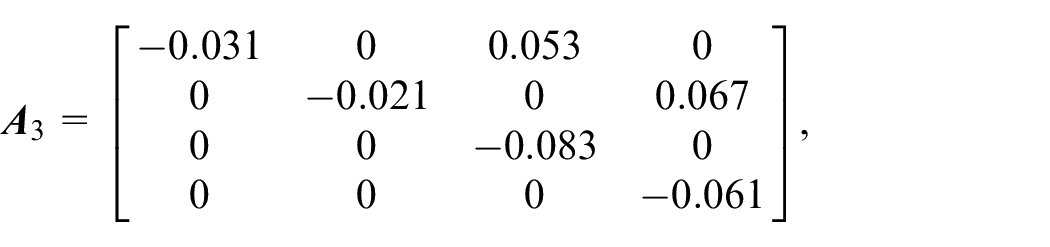
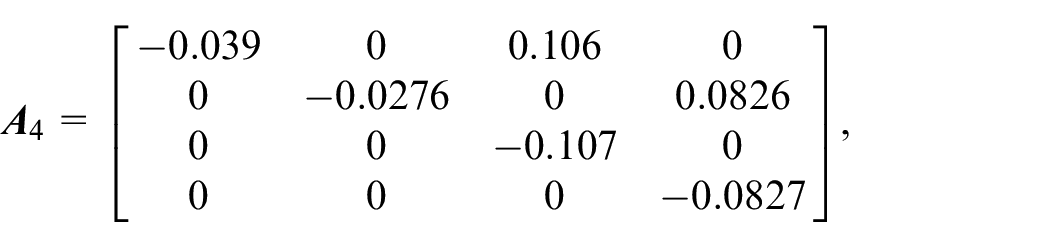
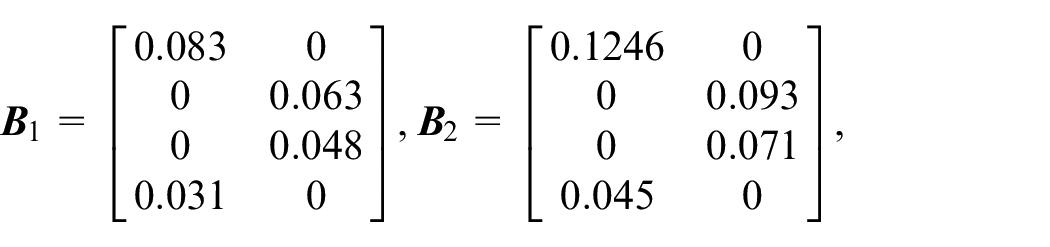
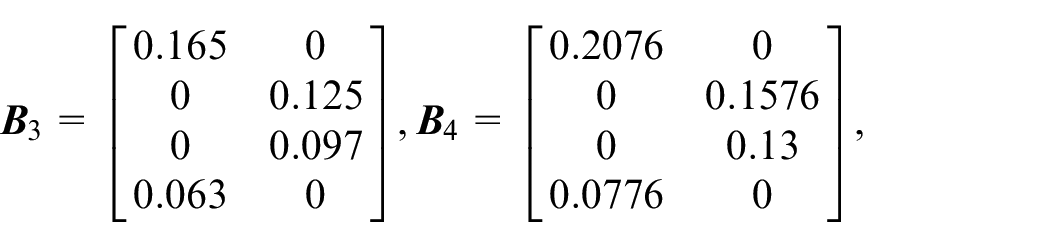
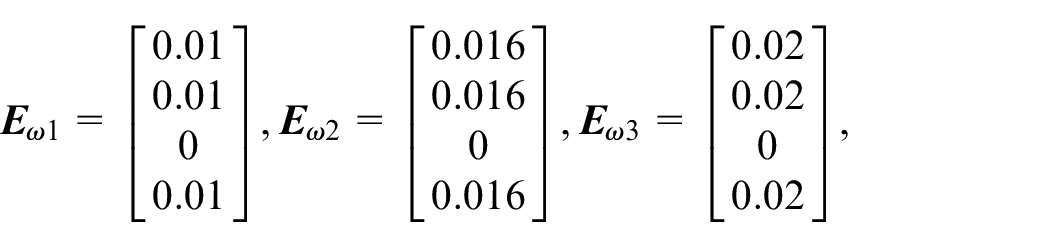
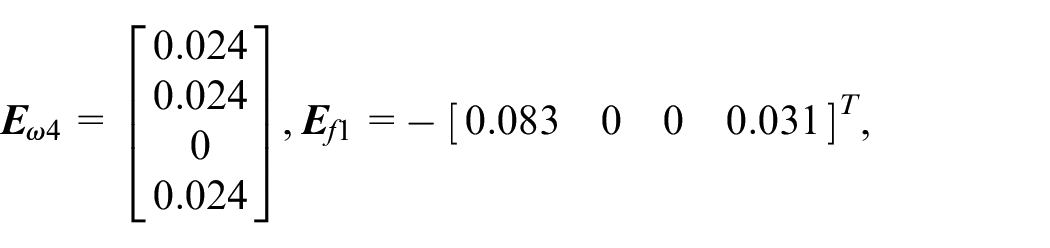
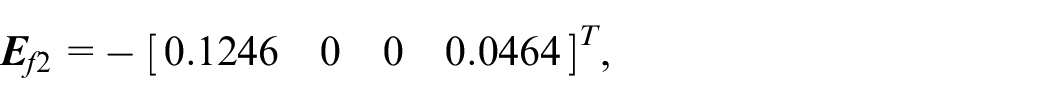
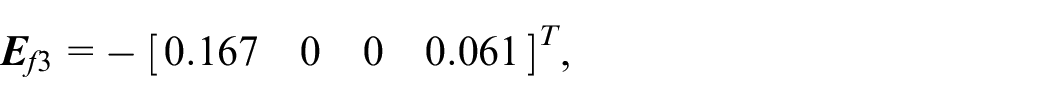
In the simulation,
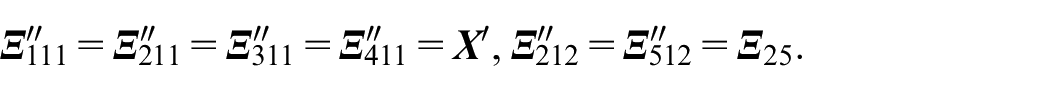
The fuzzy membership function is assumed to be
Rule
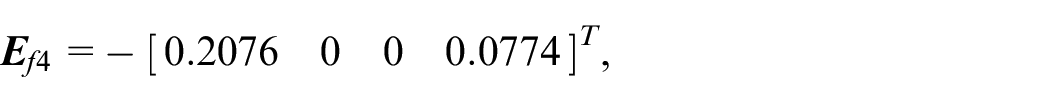
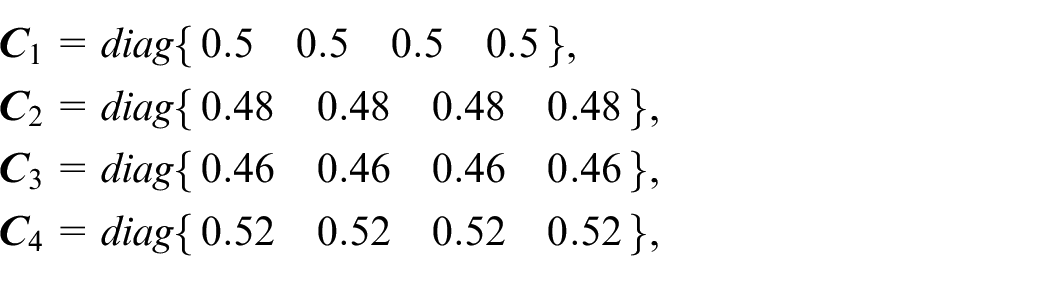
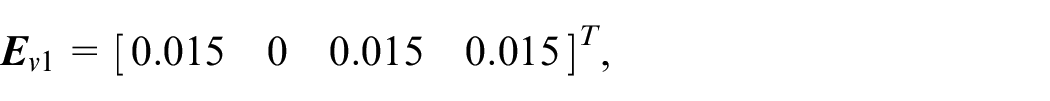
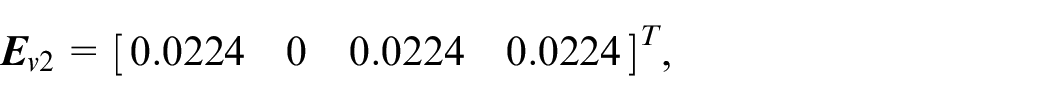
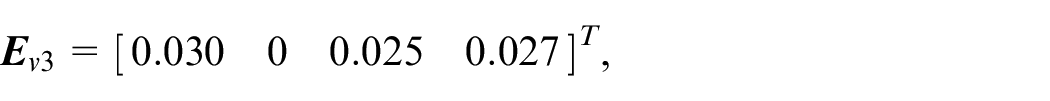
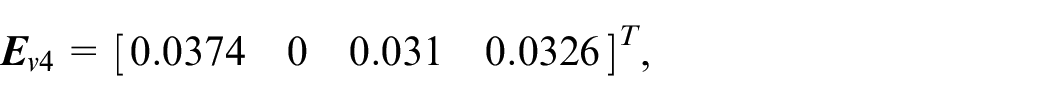
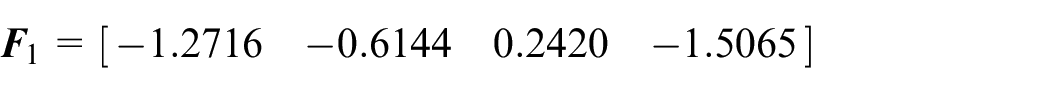
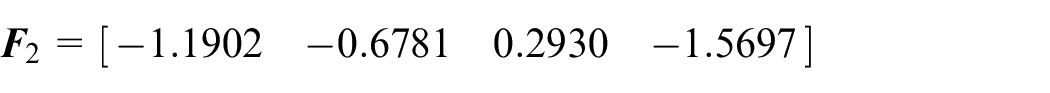
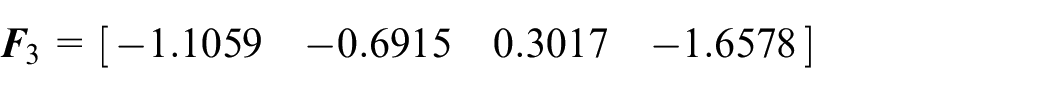
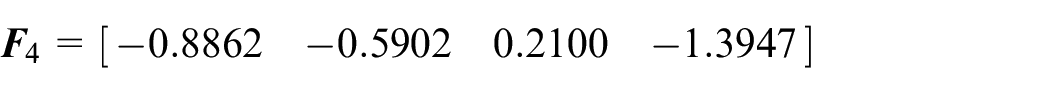
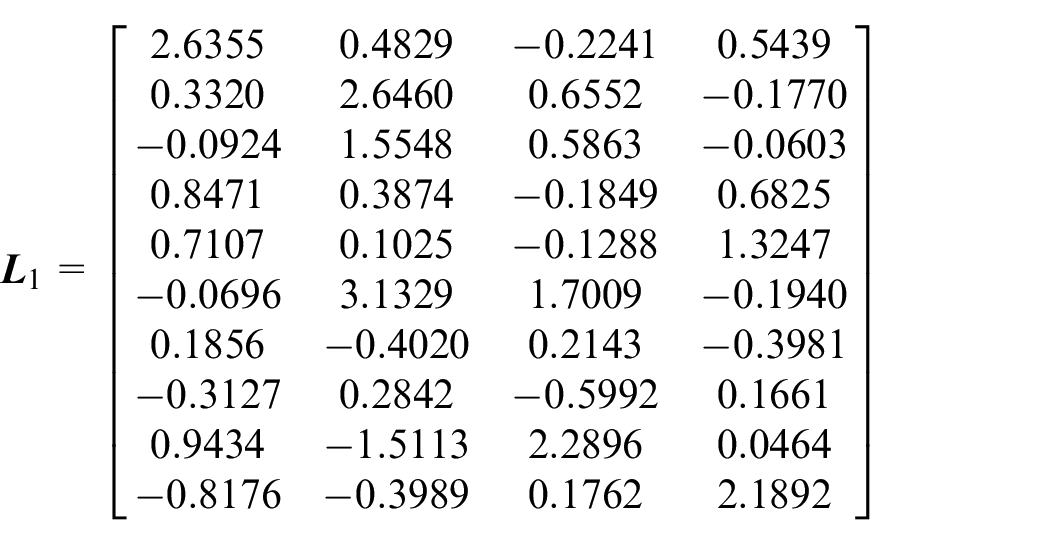
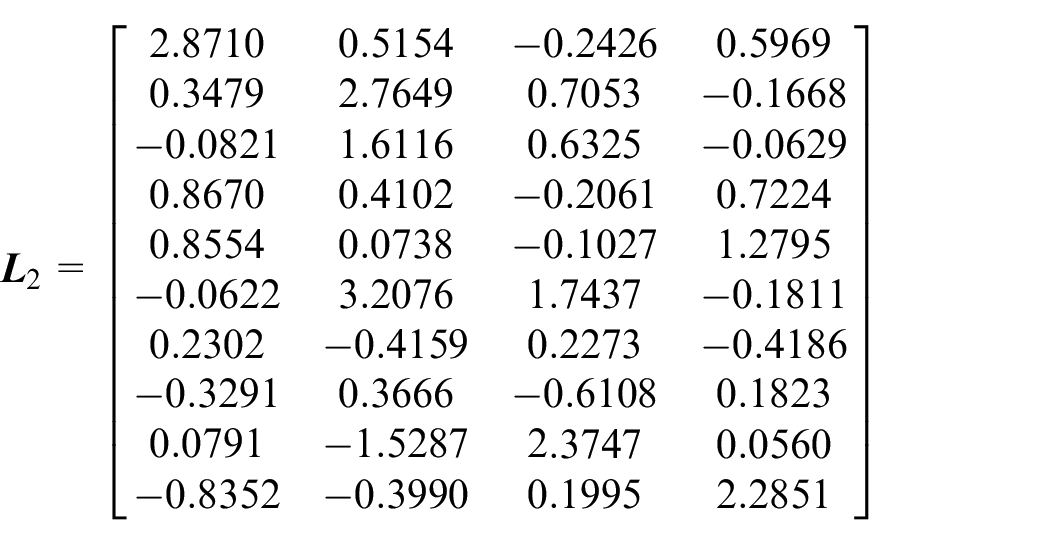
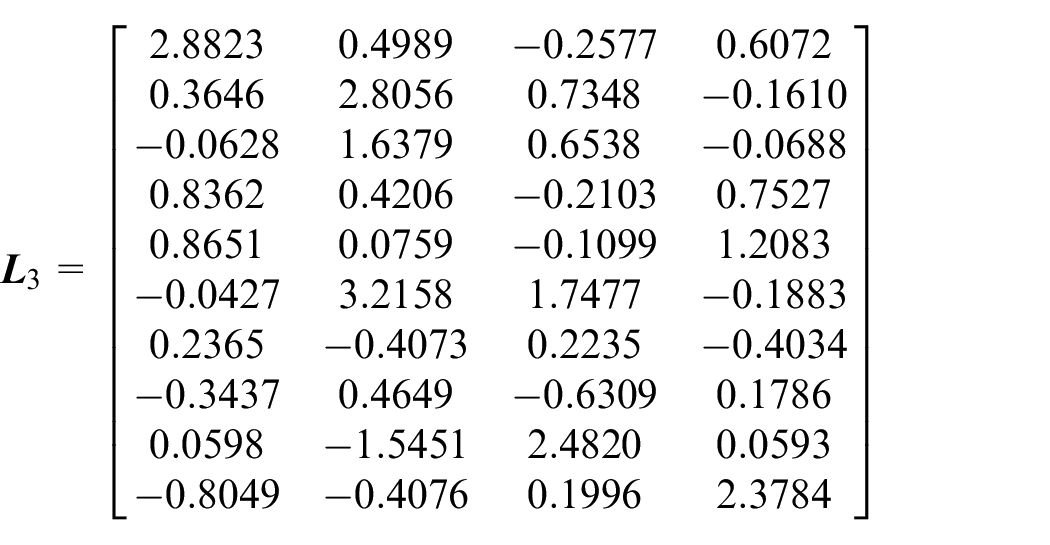
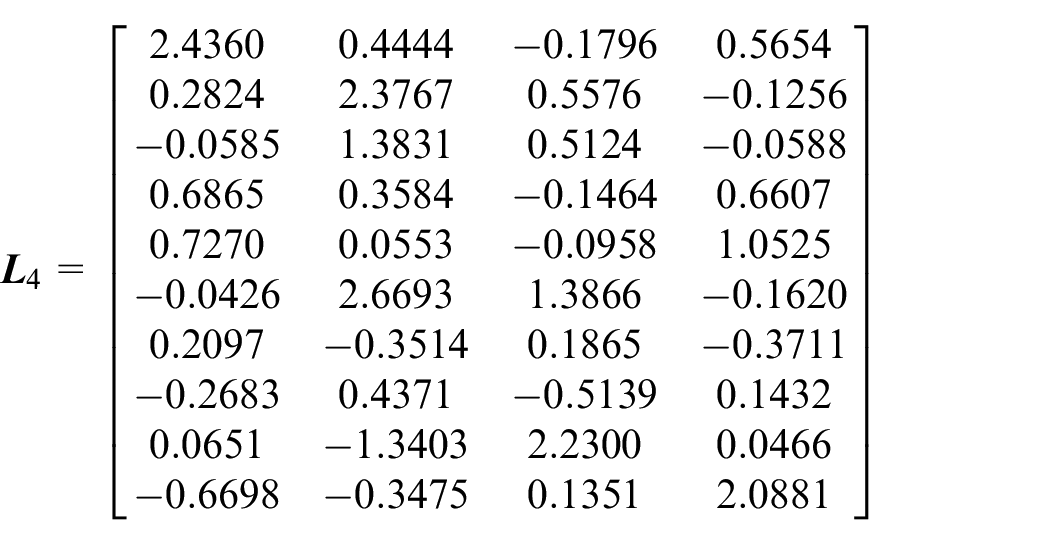
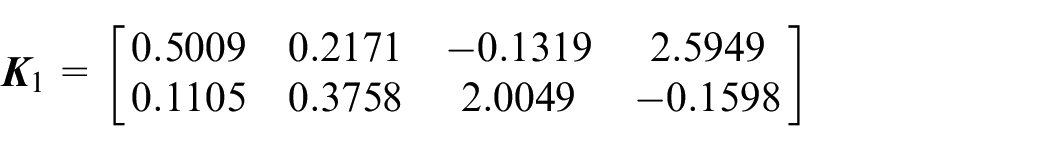
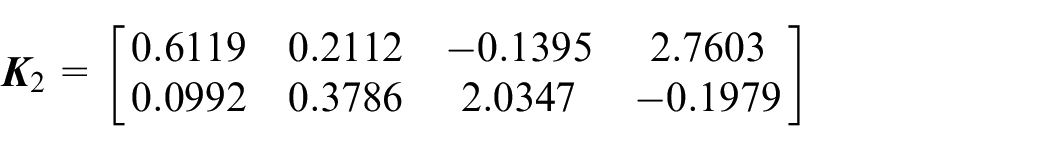
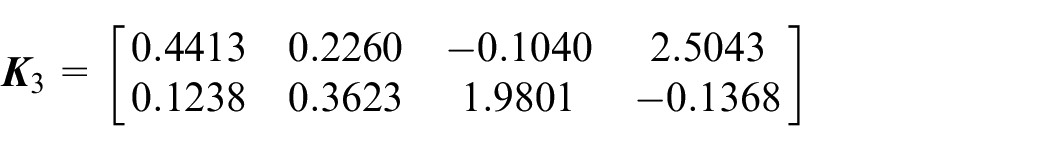
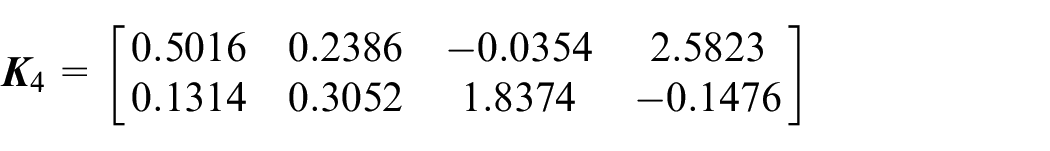
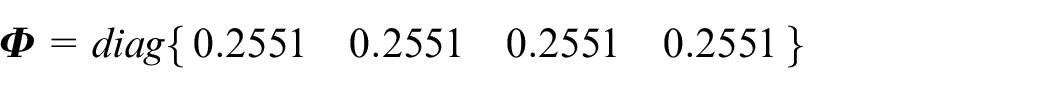
Let
In Theorem 2, let
Estimation of state, actuator fault, and FDI attacks
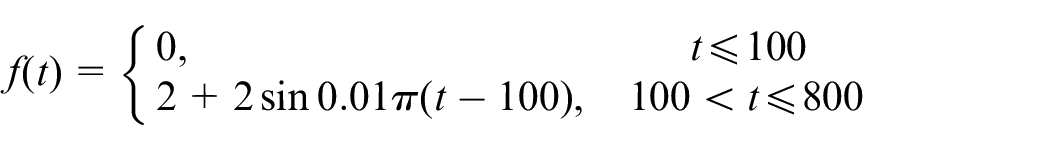
In the simulation, we consider the worst case in which the actuator fault and the FDI attacks occur simultaneously.
Suppose that the fault occurs in the first channel, then the time-varying fault of the system is as follows:
For the actuator FDI attack, we assume that its first channel is constant at zero, and the second channel satisfies the following equation:
For the sensor FDI attack, we assume that each channel satisfies the following equation:
To observe the above system fault and FDI attacks more clearly, the estimations and corresponding errors of the fault and the actuator and sensor FDI attacks are respectively shown in Figures 2 to 9.
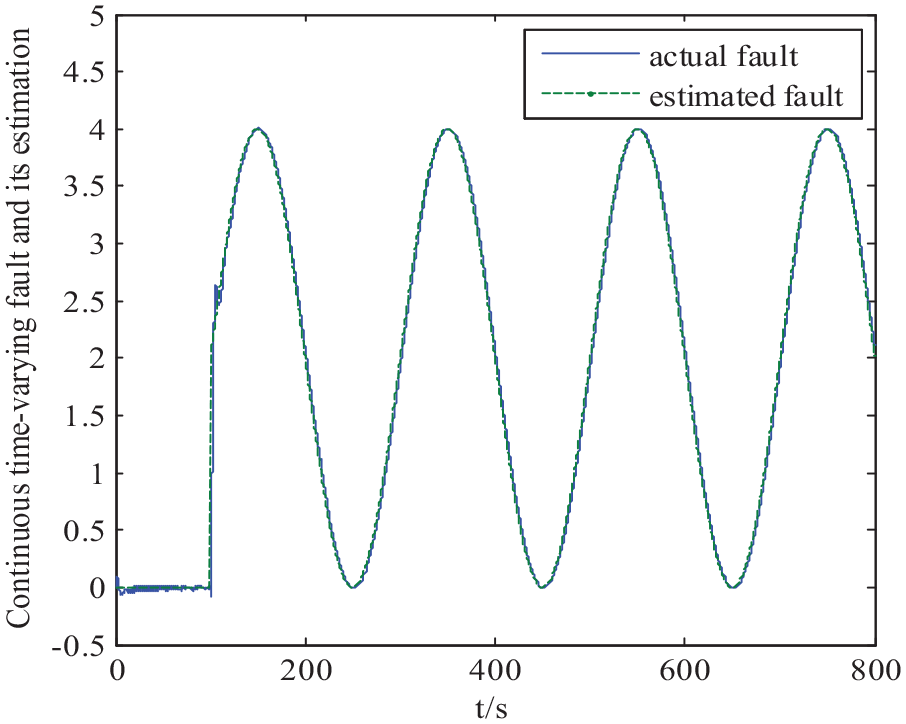
Continuous time-varying fault and its estimation.
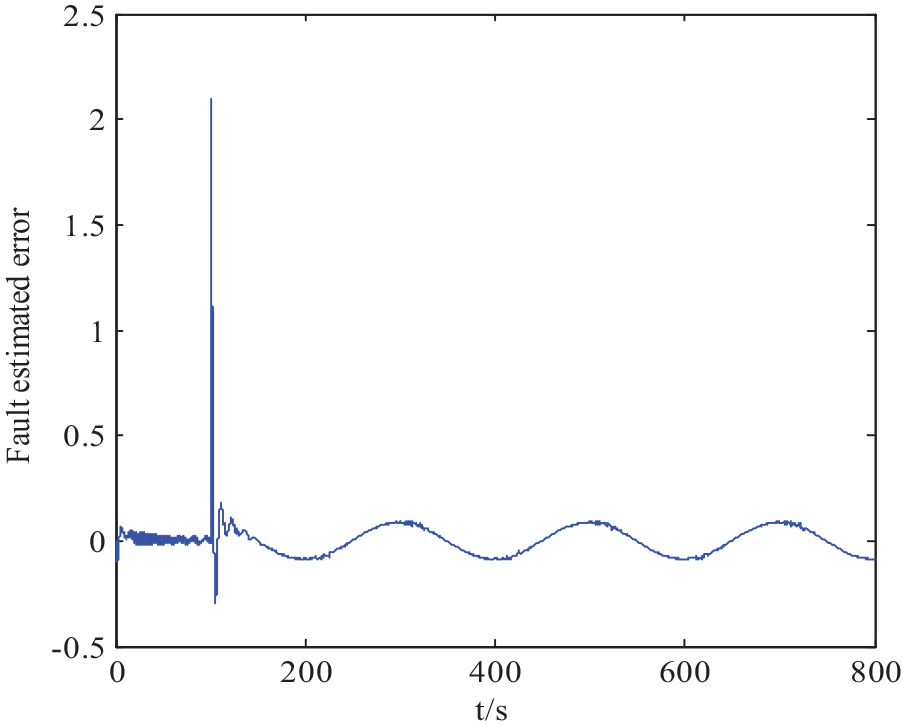
Fault estimation error.
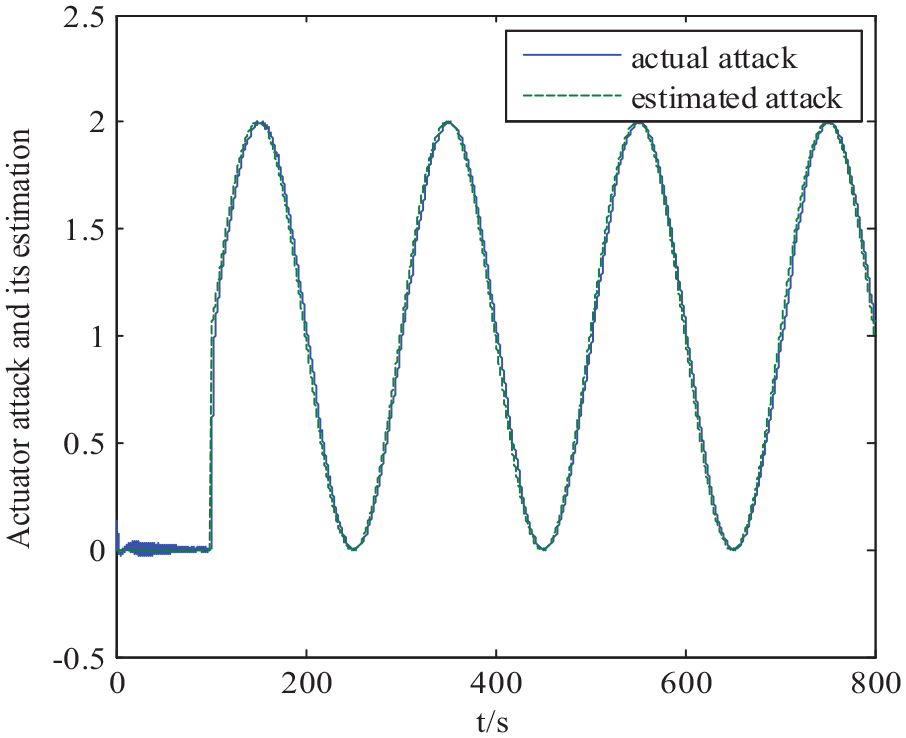
Actuator FDI attack and its estimation.
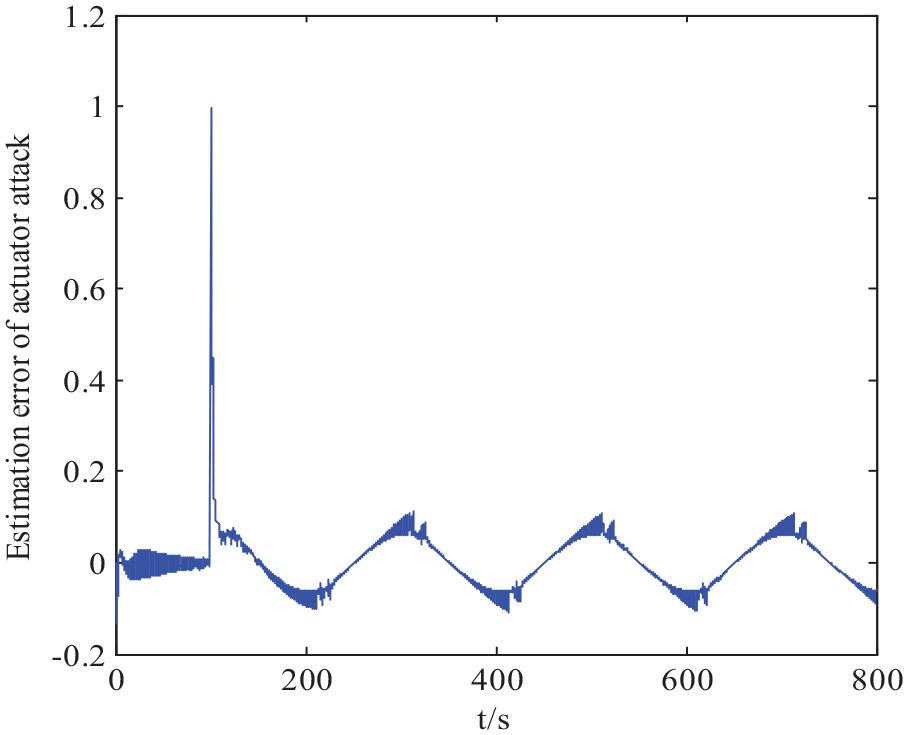
Estimation error of actuator FDI attack.
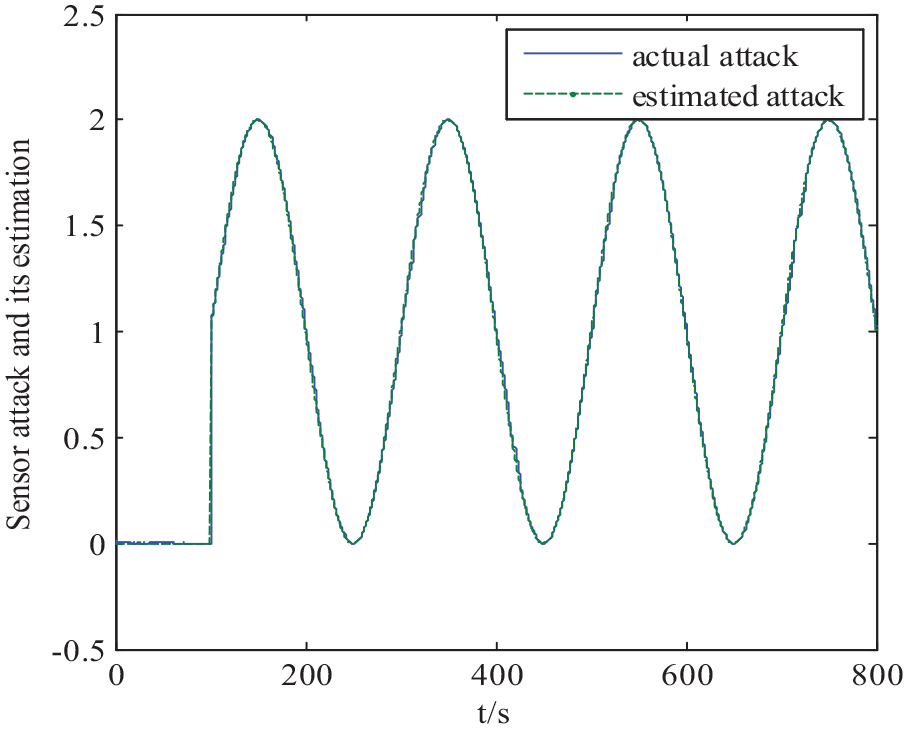
Sensor FDI attack and its estimation.
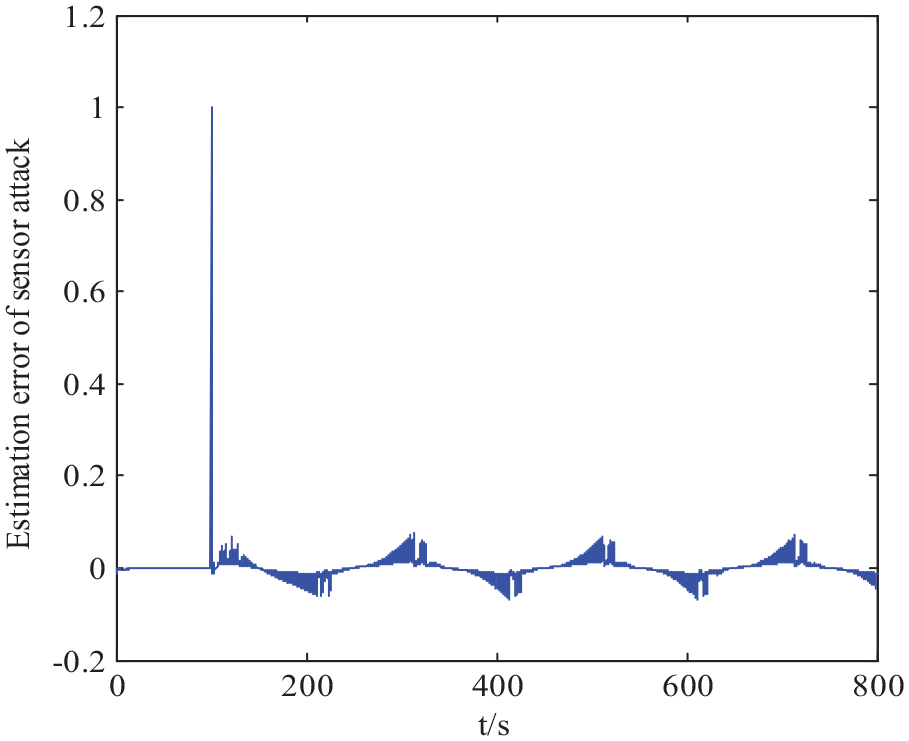
Estimation error of sensor FDI attack.
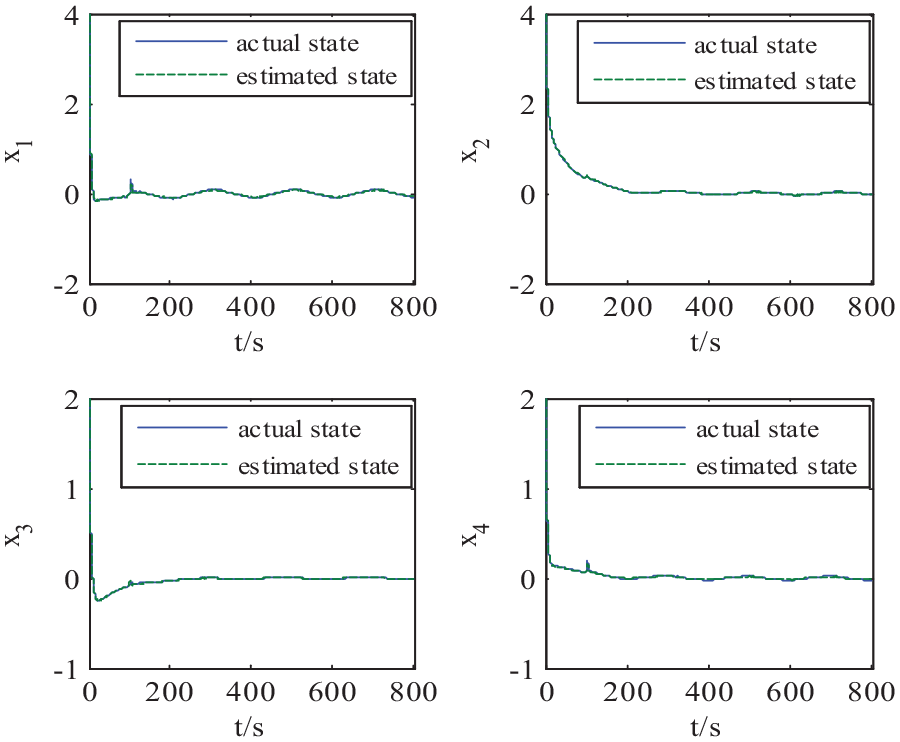
States and their estimations.
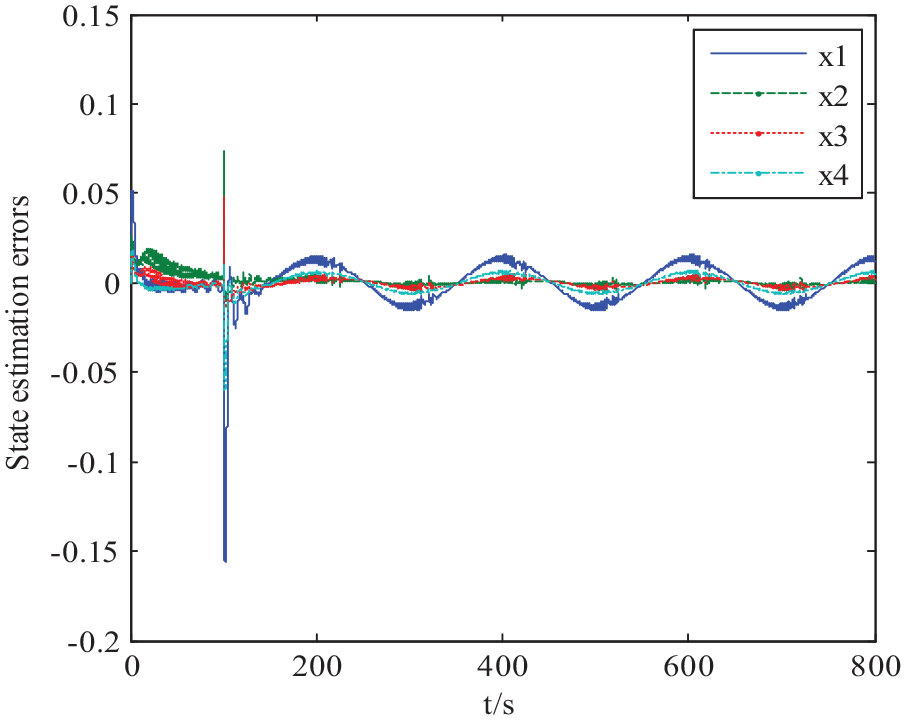
State estimation errors.
It can be seen from Figures 2 to 9 that the estimation errors of the fault, actuator FDI attack, sensor FDI attack, and state have a larger fluctuation at 100s when the FDI attacks and the actuator fault are exerted. The remaining time they are within the normal range. Among them, the fault estimation error does not exceed
Analysis of impact of event-trigger parameters on CPS security and communication resource
To further analyze the influence of the trigger parameter on the CPS security and communication resources, the data transmission amount and the system security state under different trigger parameters are listed in Table 1.
Comparison of data transmission amount and system state under different trigger parameters.
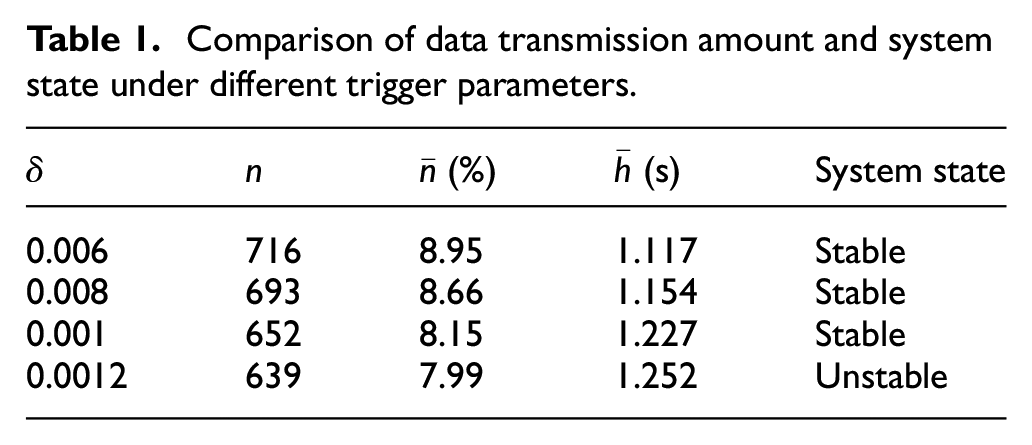
where
It can be seen that with the increase in trigger parameter
Comparison of different control methods
In the following, the active–passive attack tolerance method proposed in this paper and the passive attack tolerance method in Li et al. 38 (to tolerate FDI attacks on double-end network passively and actuator fault actively) are adopted. The output responses with these different attack-tolerance methods are presented in Figure 10(a) and (b). In addition, the data transmission amounts are specified in Table 2.
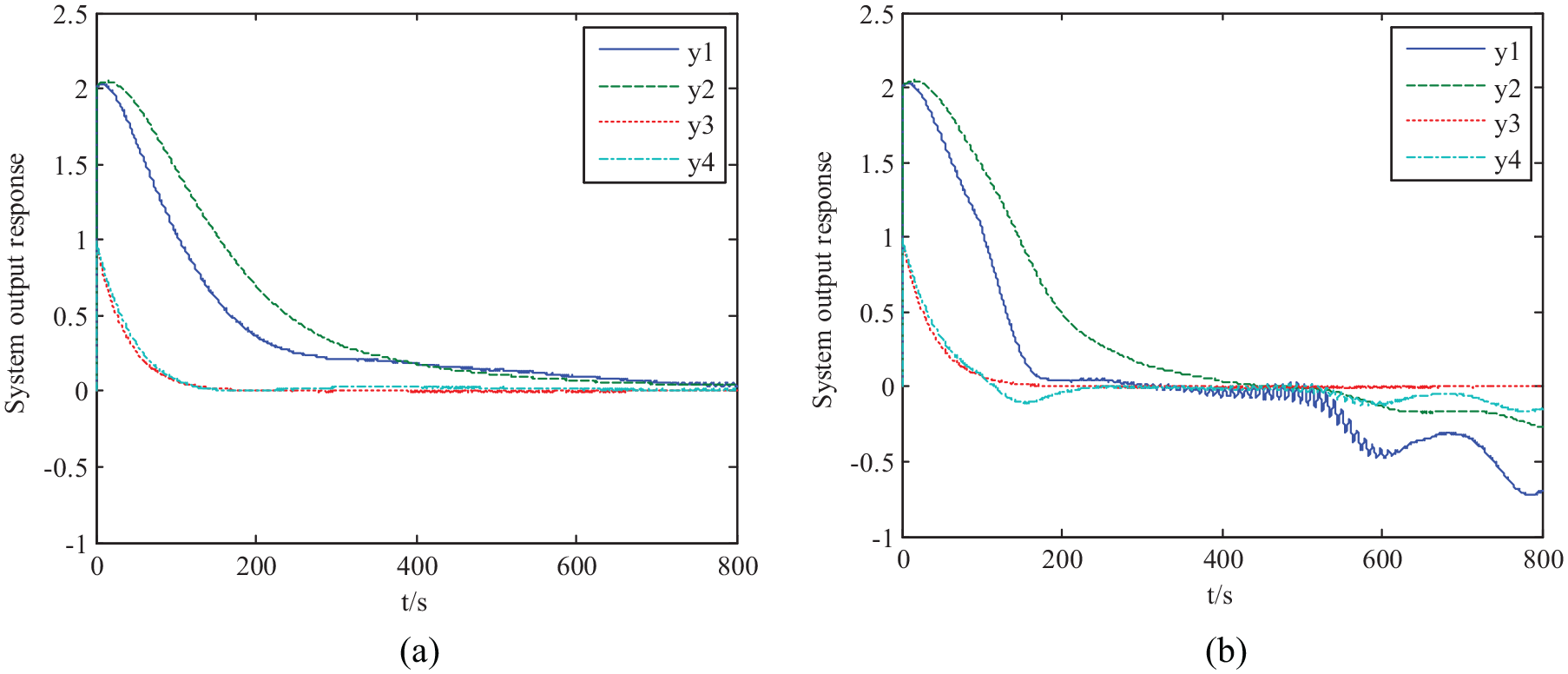
System output responses with different control methods: (a) system output response with active-passive attack-tolerant and (b) system output response with passive attack-tolerant.
Comparison of data transmission amounts with different attack-tolerance methods.
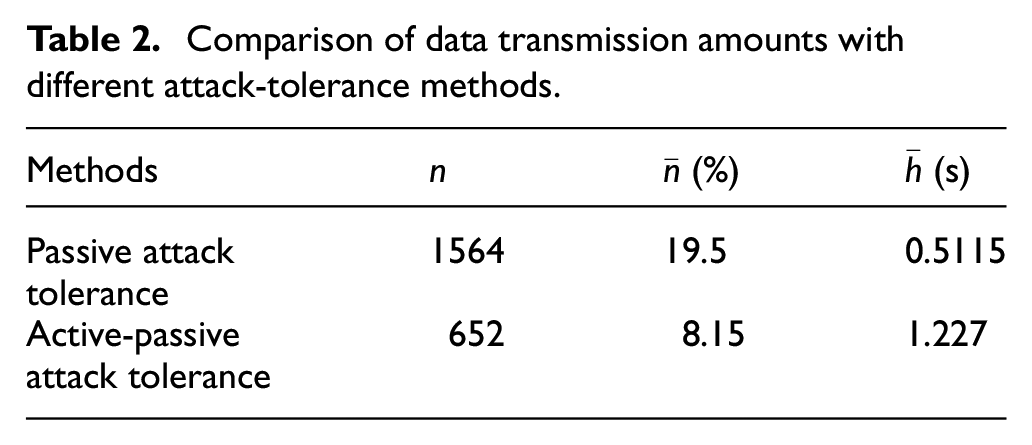
It can be seen that the system output in Figure 10(a) remains stable after 400 s, whereas that in Figure 10(b) becomes divergent after 500 s, which suggests that the method proposed in this paper is more effective in defending FDI attacks than that proposed in Li et al. 38 Table 2 shows that the amount of data transmission is lesser by the method proposed in this paper than that by the other methods. This shows that the former method is also more effective in saving network communication resources than the latter.
The reason is that the method in Li et al. 38 regards FDI attacks on double-end network as types of special disturbances and suppresses them passively in a robust manner. The control strategy proposed in this paper is different; specifically, a highly targeted active compensation is made for the actuator FDI attack according to its estimation, and the passive attack tolerance method is used only for the sensor FDI attack. Therefore, for a highly serious FDI attack, in terms of both the defense ability and the saving of communication resources, the system performance with the method proposed in this paper is better than that by the other method.
Compared to the PTTCS, which needs to transmit 8000 data, the DETCS only transmits 652 data in Table 2, with transmitted data rate of 8.15% and an average transmission period of
Conclusion
Based on the DETCS, this study investigated a co-design method of dual security control and communication for a nonlinear CPS with an actuator fault and FDI attacks. First, a dual security control framework with active fault-tolerance and active–passive attack-tolerance was built, and a T–S fuzzy model of a closed-loop CPS was established, which integrated a trigger condition, the actuator fault, and the FDI attacks. Second, by introducing the appropriate Lyapunov–Krasovskii function, time delay theory, affine Bessel–Legendre inequality, and LMI technique, a robust observer for the estimation of the state, FDI attacks, and fault as well as a dual security controller with active fault-tolerance and active–passive attack-tolerance were obtained. This consequently achieved the co-design goal of dual security control and communication. Finally, a simulation of a quadruple-tank was conducted. It showed that the method proposed in this paper can timely and accurately estimate the system state, actuator fault, and FDI attacks as well as tolerate the fault actively and the FDI attacks actively-passively, simultaneously saving the network communication resources effectively. The proposed results can also provide a theoretical basis for dual security design of a nonlinear CPS in practical engineering. Particularly when a system is subject to FDI attacks and actuator fault simultaneously, the active–passive attack tolerance strategy is expected to be an effective defense method.
However, this study deals with the FDI attack at the sensor-end passively, and the defense capability of passive attack-tolerance is very limited. Therefore, how to establish a more effective defense strategy to actively deal with FDI attacks on a double-end network and further improve the CPS security defense capability will be investigated in the next research study.
Footnotes
Declaration of conflicting interests
The author(s) declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author(s) disclosed receipt of the following financial support for the research, authorship, and/or publication of this article: This study was financially supported by the National Natural Science of China (Grant Nos. 62163022, 61763027), Higher Education Innovation Capacity Improvement Project of Gansu in China (Grant No. 2019B-152), and Youth Science and Technology Fund of Gansu Province (Grant Nos. 21JR1RM339, 21JR7RM192).