Abstract
Pao Fen has emerged as a prominent cyber-enabled money laundering mechanism across East and Southeast Asia, especially within China’s digital financial system. Characterized by rapid, decentralized fund transfers and heavy reliance on personal bank accounts and mobile payment platforms, Pao Fen operations are deeply embedded in digital infrastructures and criminal subcultures. This study presents the first empirically grounded crime script analysis of Pao Fen, drawing on 235 Chinese criminal court cases to deconstruct the laundering process into six procedural stages: Infrastructure Preparation, Activation and Access Setup, Core Laundering Execution, Conversion and Integration, Network Consolidation and Expansion, and Detection and Termination. The analysis identifies core actions, their components, key actors involved, financial crime elements, tools and props used, as well as potential prevention strategies, all of which illustrate the scalable and persistent nature of these laundering networks. Building on these insights, this study introduces the situational interventions for Pao Fen, which applies traditional situational crime prevention approach to the distinct stages of Pao Fen operations to identify targeted disruption points throughout the laundering process. The findings underlie the need for cross-border policy coordination, real-time detection systems, and targeted intervention strategies that reflect the dynamic behaviors and organizational logics of modern laundering operations.
Keywords
Pao Fen as a Money Laundering Modality in Asia: An Introduction
Pao Fen is a Chinese term that originated in the context of money laundering activities in East and Southeast Asia. The Chinese character Pao translates to “running,” while Fen refers to the smallest unit of Chinese currency (RenMinBi and RMB). When combined, Pao Fen literally signifies the rapid transfer and dispersion of small amounts of money. This term did not exist in traditional Chinese vocabulary but has emerged in recent years alongside the rise of cyber-enabled fraud, becoming a specialized term to describe a distinct mode of laundering illicit proceeds.
First appeared in China and then predominantly being active in East and Southeast Asia, Pao Fen operations are primarily conducted by Chinese-speaking participants. Within Chinese criminological scholarship, Pao Fen is defined as a structured laundering technique involving the fragmentation of large sums of illicit funds into smaller transactions to conceal their origin and facilitate their circulation through financial networks (Huang, 2024). Originating within cybercriminal subcultures, the model is decentralized and commission-based, relying on recruited individuals, often called runners, who use personal bank accounts, digital wallets, or cryptocurrency platforms to quickly receive, split, and redistribute illicit funds (Huang, 2024; Ping’an-Helan, 2021; Zhao, 2024). These runners typically earn commissions ranging from 1% to 2% per transaction in exchange for enabling the movement of criminal proceeds (Economic Information Daily, 2021; Qin, 2019; Zhao, 2024). While functionally similar to global money mule operations, Pao Fen is distinguished by its industrial scale, advanced digitization, and deep integration with platform-based infrastructures unique to China’s digital payment environment.
Unlike conventional laundering schemes, Pao Fen operations leverage purpose-built platforms and encrypted communication channels to coordinate laundering tasks. Participants register on these platforms, receive transaction assignments, and complete fund transfers using dynamic QR codes or third-party payment credentials. The platforms act as intermediaries, connecting upstream criminal networks involved in telecom fraud, illegal gambling, or cross-border scams with a large network of downstream participants (known as runners). The technical features of Pao Fen platforms, including real-time order matching, automated commission distribution, and the strategic obfuscation of transaction patterns, significantly enhance the speed, anonymity, and resilience of laundering activities, while concurrently complicating efforts by financial regulators and law enforcement to detect or disrupt illicit fund flows (Huang, 2024; Ministry of Public Security of the People’s Republic of China, 2024; Zhao, 2024; Yang and Liao, 2023).
Although runners in Pao Fen schemes are frequently perceived as minor or low-level actors, their role is functionally indispensable. By enabling the initial placement and complex layering of illegal proceeds, runners serve as gatekeepers to the broader laundering process. Criminological literature generally classifies actors in laundering networks into three categories: core organizers who conceptualize and manage the scheme; professional facilitators who offer technical, legal, or logistical expertise; and recruited participants, who willingly or unwittingly provide access to financial systems (L. Bekkers & Leukfeldt, 2023; Leukfeldt, 2014; Lusthaus et al., 2024). Individuals involved in Pao Fen operations fall within this third category. Their use of legitimate financial channels provides a veil of normalcy, fragmenting transactions across thousands of accounts and complicating forensic tracing.
While often perceived as a low-level activity involving peripheral actors, Pao Fen operations in fact inflict significant harm on both individual participants and broader financial systems. At the individual level, participants with vulnerabilities are drawn in by promises of easy income through seemingly harmless “part-time tasks.” However, involvement in Pao Fen exposes them to serious legal consequences, including criminal prosecution, imprisonment, revocation of banking privileges, and long-term credit damage (Lao, 2023; Ma, 2023; Zhang, 2021). At the systemic level, Pao Fen functions as a highly effective laundering mechanism that facilitates the large-scale movement of illicit funds across borders, thereby enabling the persistence and expansion of cyber-enabled criminal networks. It does so by embedding illegal transactions within routine financial activity, often disguising them as peer-to-peer payments or legitimate e-commerce flows. This integration overwhelms conventional anti-money laundering (AML) controls, exploits regulatory blind spots, and fragments investigative trails, making detection and enforcement particularly difficult (e.g., Yan, 2022). The scale and impact of Pao Fen have drawn growing concern from Chinese authorities. According to Chinese government media reports, in the first three quarters of 2023 alone, 1,718 individuals were indicted for money laundering, and over 62,000 were prosecuted for crimes involving the concealment or disguise of criminal proceeds—an increase of more than 90% year-on-year (CCTV News, 2023; China Daily, 2023). These figures point to the urgency of understanding and addressing Pao Fen as a structurally embedded and technologically enabled threat to financial integrity and legal accountability.
Despite its increasing prevalence and systemic threat, there remains a significant gap in empirical research on the internal structure and procedural mechanisms of Pao Fen. In English-speaking countries, individuals who assist in transferring illicit funds during laundering processes are commonly referred to as money mules (Financial Crimes Enforcement Network, n.d.; United Nations Office on Drugs and Crime, n.d.). An extensive and well-established body of research has explored the phenomenon of money mules, focusing on their operational functions within laundering networks, the demographic characteristics of those most frequently recruited, and the tactics used by criminal actors to target and manipulate these individuals (e.g., Bekkers et al., 2025; Esoimeme, 2021; Europol, 2021; Hong and Lee, 2024; Leukfeldt, 2014; Leukfeldt & Kleemans, 2019; Loggen and Leukfeldt, 2022; Raza et al., 2020; Odinot et al., 2017). The existing literatures in English-language research have significantly deepened understanding of money mules’ operations across diverse regional and socioeconomic contexts but limited scholarly attention has been devoted to Pao Fen, which is active in Asia, especially in China. Current academic knowledge of Pao Fen is drawn almost exclusively from Chinese-language sources (Li et al., 2024; Liu, 2014; Ma, 2023; Zhao, 2024; Zhang and Gu, 2023; Sun, 2022). However, most Chinese-language studies on Pao Fen offer primarily descriptive or conceptual analyses and have not yet to empirically map its operation. Meanwhile, few researchers have applied criminological lens to identify concrete intervention points within the laundering process of Pao Fen. Moreover, English-language scholarship on Pao Fen remains virtually nonexistent, which limits comparative and cross-jurisdictional understanding of its organizational structures, developmental trajectories, and social impacts as a form of transnational crime. Given Pao Fen’s growing role as a critical node in transnational cyber-enabled laundering networks, and its integration with globalized fraud and gambling schemes, there is an urgent need for international scholarly attention. As the practice increasingly transcends national boundaries, effective governance and intervention require coordinated, cross-border criminological research, practices, and policy collaboration.
To deepen the research on laundering crimes, this study uses crime script analysis to analyze judicial cases from China, specifically involving Pao Fen operations. Crime script analysis is a methodological framework that deconstructs complex criminal activities into sequential stages or “scripts,” similar to scenes in a play, to reveal offender decision-making and procedural structures (Cornish, 1994). The analysis identifies key actors and actions at each procedural stage, providing a systematic understanding of how Pao Fen unfolds. The primary research questions guiding this study are: (1) What are the specific stages and routines involved in Pao Fen process? (2) How can this process be disrupted through evidence-based crime prevention strategies? To answer the questions, this study first deconstructs Pao Fen operations into a series of distinct procedural stages. Based on this empirical mapping, the study further proposes the situational intervention preventions for Pao Fen, which applies principles from situational crime prevention framework to identify specific disruption points at each stage of the laundering lifecycle. The framework focuses on strategies to increase offenders’ perceived effort and risk, reduce potential rewards and justifications, and minimize situational triggers. The findings provide detailed insights into specific laundering stages and offender actions that can inform situational crime prevention strategies, such as increasing guardianship over bank account registrations and strengthening verification protocols. These targeted interventions can support international law enforcement and financial intelligence efforts to disrupt the operational flows of cyber-enabled laundering networks.
Applying Situational Crime Prevention on Organized Nature of Pao Fen
Pao Fen networks display a distinctly organized and procedural structure, making them particularly amenable to intervention through the framework of Situational Crime Prevention (SCP). Unlike opportunistic or isolated cybercrimes, Pao Fen operates as a systematic, multi-tiered enterprise involving upstream fund suppliers, midstream platform operators, and downstream runners responsible for fragmented fund transfers. These roles are integrated into stable digital infrastructures and coordinated through hierarchical communication structures, exhibiting features that closely align with criminological definitions of organized crime (Huang, 2024; Wu, 2022; J. Zhang & Gu, 2023).
Originally developed in the 1970s by researchers at the British Home Office (Clarke, 2009), SCP focuses on reducing crime opportunities by targeting specific situational factors surrounding criminal events (Clarke, 1983). From its inception, SCP promoted practical techniques tailored to prevent particular types of offenses by altering the immediate environment in which crimes occur. SCP focuses on reducing criminal opportunities by manipulating situational elements surrounding an offense. It is grounded in rational choice theory and emphasizes that altering the environment, rather than the offender’s disposition, can deter criminal behavior. Over time, the approach has evolved. Clarke (1995) first organized 12 prevention techniques into three broad categories, which were later expanded to 16 techniques across four strategies by Clarke and Homel (1997). A further revision by Cornish and Clarke (2003) refined the framework to its current form, encompassing 25 situational techniques. Notably, Cornish and Clarke (2002) extended SCP to address organized crime by integrating principles from rational choice theory. They introduced the crime script approach to demonstrate how offenders, especially those involved in complex, organized operations, engage in deliberate, goal-oriented decision-making. Rather than acting on impulse, these offenders weigh risks and benefits to optimize their criminal strategies. While SCP has traditionally been applied to volume crimes, scholars have increasingly extended it to organized and cyber-enabled crimes, including those with complex logistical routines (Borrion, 2013; Cornish & Clarke, 2002; Levi & Maguire, 2004). This shift is particularly relevant for analyzing Pao Fen, where laundering tasks follow repeatable patterns and decision points.
There are three core reasons why SCP is especially suitable for analyzing Pao Fen. First, Pao Fen is procedurally complex. It involves multiple actors performing interdependent tasks: criminal networks circulate illicit funds, digital platforms manage semi-anonymous task distribution, and runners execute payment orders. This layered structure mirrors the types of “crime scripts” SCP was designed to dissect and disrupt. Second, Pao Fen is routinized and scalable. It follows standardized, repeatable sequences of laundering activity, including task delegation, fund transfers, identity masking, and commission settlement. Much like workflows in legitimate enterprises, these scripts offer clear entry points for intervention if mapped correctly. Third, the offender population within Pao Fen networks, particularly runners, often consists of economically marginalized individuals with limited awareness of legal risks. This makes the decision-making context crucial. SCP directly addresses such vulnerabilities by proposing targeted techniques that increase perceived risks, reduce rewards, and remove excuses for participation. For example, disrupting recruitment messaging or imposing transaction limits can reshape the cost-benefit calculations that underpin runner compliance.
By treating Pao Fen not as a spontaneous act but as a structured and scriptable offense, SCP offers a powerful analytical and preventative framework. As Cornish and Clarke (2002) explain, organized crimes of this nature represent the highest form of rational offending because they are carefully planned, well-resourced, and deliberately structured to remain concealed. Through crime script modeling, choke points in the laundering process can be identified and matched with situational interventions tailored to each stage.
Building on this foundation, this study develops a series of situational interventions specifically tailored to the Pao Fen operations. These tailored strategies integrate the five strategic dimensions of situational crime prevention, with empirically derived financial crime script stages identified through a systematic analysis of Chinese court judgments. By aligning concrete prevention techniques with each procedural phase, such as implementing stricter bank account verification during infrastructure preparation or enhancing transaction monitoring during core laundering execution, these proposed strategies provide a criminologically grounded and practically actionable framework to disrupt Pao Fen operations at multiple intervention points. Beyond its immediate application, this approach contributes to criminological scholarship by demonstrating how situational crime prevention can be systematically adapted to address complex and technology-enabled forms of organized financial crime.
Data and Analytical Strategy: A Crime Script Analysis on 235 Criminal Cases
A qualitative analysis was conducted in this study using national legal documents manually retrieved from China Judgments Online. This platform, established by the Supreme People’s Court (SPC) of the People’s Republic of China, has been recognized as a legitimate source and widely used in prior academic research (Cai et al., 2018; Gao et al., 2020; Y. Zhang & Huang, 2025). The credibility of the platform and its consistent use in previous scholarship provided a strong foundation for the use of data from this source in the present study.
To collect relevant legal documents, the primary search term “Pao Fen” in Chinese was used, initially yielding 9,159 documents. Because Pao Fen activities predominantly involve criminal conduct, an additional filter narrowed the search to “Criminal Cases” in Chinese. After applying this filter, the final dataset comprised 9,054 cases, covering the period from 2014 to 2025, as China Judgments Online began systematically publishing court decisions in 2014, which is the earliest year available on the platform. However, due to platform display limitations, only the first 600 cases were viewable and accessible. No additional content-based filtering was applied because the aim was to capture a broad and unbiased cross-section of accessible Pao Fen cases. Further filtering could have introduced selection bias by excluding operational variations. Instead, a randomized sampling strategy was employed to ensure transparency and reduce bias, providing each case an equal chance of selection.
It is important to note that while China Judgments Online is the official repository for court decisions in China, not all court decisions are published on the platform. Publication is governed by SPC regulations that exclude certain types of cases, such as those involving state secrets, personal privacy concerns, juvenile defendants, or other sensitive content. Furthermore, the decision to publish is also subject to judicial discretion at the court level, and some cases may be withheld to protect victims or facilitate ongoing investigations. Therefore, the available dataset represents the publicly released subset of national judgments, reflecting both mandated publication requirements and court-level selection mechanisms.
Given the qualitative nature of this study, a purposive sampling strategy was adopted with the goal of obtaining a manageable and information-rich sample that could facilitate an in-depth understanding of the operational processes involved in Pao Fen activities. Qualitative research prioritizes depth over breadth, focusing on detailed examination rather than generalization across a population (Braun & Clarke, 2019). Within this approach, random sampling was used as a practical technique to reduce researcher selection bias when choosing from the available 600 cases. While purposive sampling focuses on information-rich cases, random selection within the accessible pool ensured that diverse types of operational practices were included without introducing subjective selection (Barglowski, 2018; Liamputtong, 2019). To guide sample size determination, a Qualtrics sample size calculator was used, setting a 95% confidence level, a population size of 600 (the viewable cases), and a 5% margin of error. This calculation yielded an ideal sample size of 235 cases, balancing adequate coverage with analytical manageability. Thus, random sampling complemented the qualitative aim by ensuring transparency and diversity within a purposive, in-depth analytical framework.
To achieve this, a randomized sampling strategy was implemented using Microsoft Excel. Because China Judgments Online displays search results with a maximum of 15 cases per page, the 600 accessible cases were distributed across 40 pages. First, an Excel database was constructed by manually recording the page number (1–40) and the position (1–15) of each case listed on each page, creating a structured and comprehensive sampling frame that covered all available cases. A random number generator function in Excel was then applied within each page’s entries to randomly select cases. Specifically, multiple random case numbers were generated per page to ensure that selections were distributed across the entire dataset rather than concentrated within any single page. This randomized procedure ensured that every case within the accessible 600 had an equal and independent chance of being selected, while also maintaining balanced representation across the full set of search results.
After applying the randomization procedures and excluding cases with incomplete or irrelevant information, the final sample comprised 235 criminal cases, aligning with the calculated ideal sample size and providing a robust foundation for in-depth qualitative analysis. Each case was traceable to its original page number and specific position on the judicial website. Following data collection, all case files were imported into NVivo 14 for qualitative analysis. A two-stage thematic inductive approach, following Corbin and Strauss (1990), was used to systematically code and analyze the dataset. For clarity and consistency in the results section, each case will be referenced using the label “case + [number]” (e.g., case 1, case 2, etc.).
Analytical Strategy
To systematically analyze offender behavior in cyber-enabled crime, a crime script analysis approach was employed. Originally developed by Cornish (1994), crime script analysis deconstructs complex criminal activities into sequential scenes, enabling researchers to understand offender decision-making processes and procedural structures (Gilmour, 2014, 2023; Haelterman, 2016; Leclerc, 2017; O’Hara et al., 2020; O’Malley et al., 2023). Building upon this foundation, Snaphaan and van Ruitenburg (2024) introduced financial crime scripting as an extension of traditional crime scripts. Financial crime scripting systematically integrates financial dimensions into crime scripts, including financing sources, payment methods, revenue streams, operational costs, settlement mechanisms, and connections to financial crimes. This integration provides a more comprehensive understanding of profit-driven criminal enterprises by capturing both behavioral and economic flows within illicit operations. In the current study, the principles and components outlined in financial crime scripting are incorporated into the analytical framework to map not only the procedural and behavioral actions within Pao Fen operations but also the underlying financial structures and rationalities sustaining them.
The initial stage of analysis involved open coding of judicial documents (see Gibbs, 2007, p. 45) to identify recurring behavioral patterns, operational strategies, and financial components across cases. This process focused on breaking down the data into discrete scenes and identifying common techniques such as recruiting money mules, disguising financial flows, and coordinating fund distribution. Each recurring idea was treated as a distinct action, decision point, or financial attribute within the broader laundering process and was coded as a node in NVivo. Supporting quotations or case summaries were attached to each node to maintain contextual integrity and traceability.
In the second phase, these coded elements were reorganized to construct a structured financial crime script, following the approach outlined by Snaphaan and van Ruitenburg (2024). This involved systematically describing equivalent actions, roles, financial attributes (such as financing sources, payment methods, revenues, and costs), and props used across each scene. Drawing on Cornish’s (1994) original crime script model, the analysis mapped offender actions sequentially while integrating the financial flows underpinning each stage.
Subsequently, the script was interpreted and organized into a comprehensive table to enhance clarity for both theoretical understanding and practical application, ensuring that the procedural and financial structures of Pao Fen were accurately represented. Due to limited resources, the author reviewed and coded the first 117 cases in detail, covering phases 1 and 2 to construct the core crime script. The findings from these cases were then systematically compared and verified against the remaining 118 cases to ensure consistency and comprehensive coverage across the dataset. Finally, the analysis concluded with the development of targeted intervention strategies, incorporating situational crime prevention principles into the framework to support practical disruption of Pao Fen operations.
With this methodology established and the financial crime scripting framework constructed, the results section delineates the six main phases identified, providing a comprehensive and structured account of the Pao Fen process and its embedded financial dynamics.
Result: Six Primary Phases of the Pao Fen Process and Proposed Prevention Strategies
The crime script analysis revealed that the Pao Fen process consists of six sequential and interlinked phases. First is Infrastructure Preparation, where actors acquire the necessary tools and resources. This is followed by Activation and Access Setup, which involves account activation, credential handovers, and card testing. The third phase is Core Laundering Execution, during which illicit funds are moved, layered, and transferred. Next is Conversion and Integration, where electronic proceeds are transformed into cash or digital assets and profits are distributed. The fifth phase, Network Consolidation and Expansion, is marked by repeat participation, recruitment, and operational adaptation. Finally, Detection and Termination involves law enforcement intervention, arrests, and the partial dismantling of laundering networks.
Table 1 provides an overview of these phases and their sequencing. The results first outline each phase in general terms to build the reader’s understanding, followed by detailed descriptions of sub-actions, illustrative quotes, and visual representations that depict the complexity and adaptability of these laundering scripts. For each phase, targeted prevention strategies based on the situational crime prevention framework are also proposed to address identified operational patterns and vulnerabilities.
Crime Script Analysis of Pao Fen: Scenes, Actions, and Financial Components with Proposed Prevention Strategies.
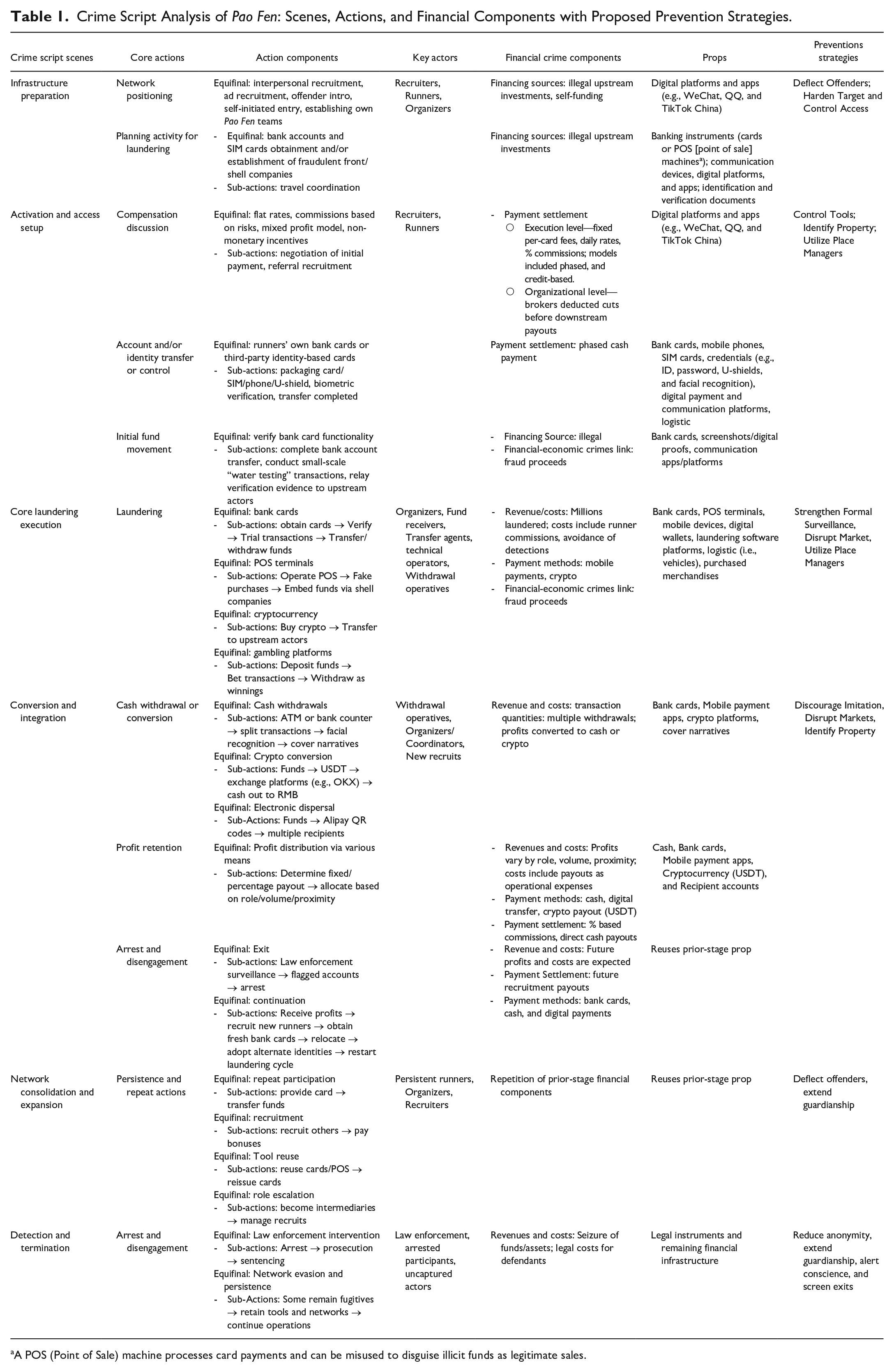
A POS (Point of Sale) machine processes card payments and can be misused to disguise illicit funds as legitimate sales.
Financial Crime Script Analysis of the Six Phases of Pao Fen
Phase 1: Infrastructure Preparation
The preparation stage of Pao Fen operations involves strategic actions by offenders to integrate into laundering networks before actively transferring funds. Key actors include recruiters, self-initiators, and organizers. Recruiters identify and persuade new participants, targeting personal contacts or advertising in public and online spaces. Self-initiators proactively seek out laundering opportunities after learning about card-based schemes through acquaintances or online platforms and independently approach networks to join. Organizers not only recruit but also establish and manage their own Pao Fen teams, coordinating the acquisition of bank cards, mobile devices, verification information, and overall operational logistics to build structured laundering networks.
Phase 1-1: Network Positioning
Pao Fen networks expand through multiple equifinal recruitment pathways, including interpersonal recruitment, advertisement-based recruitment, introductions by existing offenders, self-initiated entry, and the establishment of personal Pao Fen teams. Firstly, Pao Fen operations frequently exploit close interpersonal relationships to expand laundering networks. Offenders often recruit individuals from their immediate social circles, including family members (e.g., cousins, case 11), intimate partners (case 51 and case 75), and close friends (case 56). These trusted relationships reduce suspicion and facilitate cooperation. In case 56, for instance, the defendant recruited her friend by “informing her friend named Weng Moumou (processed in a separate case) about the easy money she earned by lending out her bank card.”
Beyond personal networks, secondly, Pao Fen actors also rely on open advertisement-based recruitment. Several individuals were drawn in after encountering advertisements on social media, forums, and gambling platforms. In case 61, a participant “learned from an online platform that one could profit by lending their bank card for Pao Fen” and responded to a popup advertisement. In case13, an indebted individual saw a “loan offer ad in WeChat Moments” and contacted Gray Wolf Professional Loans, 1 entering a laundering pipeline. A group member in case 8 responded to a WeChat advertisement posted by Sky, 2 while another recruit in case 88 encountered a Baidu Tieba 3 advertisement offering 1.5% commission and free travel for laundering via bank accounts. These open recruitment advertisements were typically financed by recruiters or organizing intermediaries using illegal upstream investments derived from prior fraud proceeds. Such financing models ensured a constant stream of advertisements targeting vulnerable individuals with promises of easy money.
Thirdly, introducing by existing offenders also serve as a common entry route into Pao Fen operations. These introductions often occur through obscured channels, with recruiters using aliases and operating within established laundering networks. In case 105, an individual was introduced to laundering by someone known only by an alias. In case 103, one participant provided multiple bank cards to fugitives, suggesting involvement in a structured, fugitive-run operation. In case 113, a participant submitted both cards and biometric data to a pseudonymous contact within the laundering chain. case 17 illustrates how upper-level controllers relied on intermediaries, including a bank insider, to coordinate recruitment. A similar pattern appears in case 32, where a new recruit was brought in by a prior participant, and in case 5, where communication occurred through an encrypted, Telegram-like messaging platform. Recruiters in these networks similarly relied on financing sourced from upstream illegal proceeds or self-funded commissions, enabling them to maintain recruiter incentives and expand operational reach.
Lastly, a subset of defendants proactively established their own Pao Fen teams, operating semi-independently while serving higher-tier criminal networks. These groups often assigned specific roles and expanded through secondary recruitment. In case 26, two defendants collaborated with “Big Brother” to form a card-running team. In case 24, a defendant directed a layered withdrawal team. In case 111, defendants established two fake liquor stores in Changsha City as POS laundering fronts, appointing staff with fixed salaries. Case 35 illustrates further scaling, where a defendant recruited others who then brought in additional participants, creating a distributed operation across multiple cities. Notably, the financing sources for these self-established teams were often self-funded, with actors using personal capital, prior illicit earnings, or small pooled investments to cover operational setup costs such as rental spaces, front business registration, and recruiter commissions. This self-financing model enabled mid-level offenders to assert operational autonomy, sustain expansion, and attract downstream participants while still remitting a share of illicit proceeds to higher-tier network.
Interestingly, there are also cases where the charged individuals were not part of any known laundering network or organized team, but instead proactively sought out opportunities to engage in Pao Fen activities through online platforms. These individuals did not rely on recruitment or external guidance; rather, they independently navigated cyberspace to locate, connect with, and embed themselves in illicit financial networks. For example, in case 43, one individual accessed multiple illegal online gambling platforms such as “Yingcai,” “Tongbo,” and “Wubai,” which are unlicensed black-market betting sites. This person proceeded to register user accounts and link personal bank cards in order to conduct deposits and withdrawals, providing clear evidence of self-initiated involvement and an active willingness to participate in laundering without coercion or organizational backing. Similarly, in case 77, another individual used the encrypted messaging app Telegram to actively connect with several laundering groups, including those operating under aliases such as “Crab,” “Imperial Dynasty,” and “Saint Seiya.” These groups were affiliated with telecom fraud groups, and the individual’s deliberate engagement with them reflects intentional participation in criminal financial networks without any prior recruitment or structured coordination.
Phase 1-2: Planning Activity for Laundering
Before initiating actual laundering transactions, offenders typically engaged in deliberate, organized, and stepwise preparatory behaviors that formed the structural foundation for their operations. These preparatory activities were often financed through illegal upstream investments, with funds coming from prior fraud proceeds or capital provided by criminal networks to cover essential setup costs such as card procurement, business registration, and initial operational expenses.
A central component of this phase involved the acquisition or distribution of bank accounts and SIM cards, either under the offenders’ own names, via recruited associates, or using forged documents and biometric verifications such as facial recognition. Some individuals directly opened new accounts, while others sourced ready-made cards from underground vendors or existing contacts, fully aware that these instruments would be used for illicit financial flows. For example, in case 110, the defendant “knowingly purchased nine bank cards. . . aware they might be used for illegal activities” and in case 133, another individual “opened multiple bank accounts. . . and handed over the cards and linked mobile phone numbers.”
More complex schemes involved the creation of fraudulent front businesses to simulate legitimate financial activity. These setups were designed to enable high-volume laundering through point-of-sale (POS) devices and commercial account flows. For instance, in case 111, the offender “opened ‘Kuifa Liquor Store’ and ‘Mengfa Liquor Store’ and agreed to launder money by using POS machines to swipe bank cards supplied by downstream collaborators.” Case 155 similarly documented the use of a BBQ restaurant as a front for laundering telecom fraud proceeds, while case 128 revealed that the offender “used false documentation to open a corporate account with Zhongbang Bank and transferred it to the upstream handler for laundering fraud proceeds.”
Across these cases, offenders consistently relied on encrypted communication platforms to organize logistics, receive instructions, and evade detection. Applications such as Telegram, Feiji, and Bat 4 were widely used to maintain secure contact with criminal supervisors and coordinate operations. In case117, participants “installed the ‘Paper Airplane’ app and rented apartments to carry out laundering activities,” while in case 202, the operation’s administrator “coordinated the formation of Telegram groups used for processing gambling-related transactions” from outside the country. Another case in case 118 noted that offenders “advertised within the Bat app to attract recruits. . . who were then brought to Yugan to conduct laundering activities.” 5
Although travel coordination did not occur frequently, when it did, it typically formed a sub-action within the preparatory phase. Offenders first coordinated travel to staging areas, after which they engaged in equifinal preparatory acts such as bank account and SIM card obtainment and/or the establishment of fraudulent front or shell companies. For example, in case 212, a participant “flew to Guangzhou and traveled by train and motorcycle to a mountainous area” where the laundering operation was staged, subsequently participating in bank card operations. Similarly, case 152 recorded that “they were directed to a floating fish farm in Raoping. . . to engage in actual laundering activity.” 6
Phase 2: Activation and Access Setup
The second stage marks the transition from preparation to active engagement in laundering operations. During this phase, recruiters play a crucial role by facilitating compensation discussions between upstream coordinators and prospective participants, negotiating commission rates or fixed fees for their involvement. Once terms are agreed upon, card owners transfer control of their bank accounts or identities to the laundering network, often by providing login credentials, payment passwords, or completing biometric verification as required. Runners may assist in physically delivering bank cards, SIM cards, or identity documents to handlers to enable these transactions. This stage culminates in the initial movement of funds, commonly known as “test transactions,” which are conducted to verify that the bank card or account is functional and properly configured for laundering purposes. These actions collectively confirm the commitment of offenders and the operational readiness of the laundering setup.
Phase 2-1: Compensation Discussion
This subphase marks the formal entry point into laundering operations, where economic incentives are explicitly negotiated and agreed upon between participants and their upstream handlers or recruiters. Payment structures varied considerably depending on the actors’ roles, volume of funds laundered, and level of involvement. Some individuals were promised flat daily rates. For instance, one participant was offered “¥2,000 per day as commission” (~$285 USD; case 10), while others received “¥500 daily per bank card plus full room and board” (~$71 USD; case 221), or rental fees such as “60 to 80 RMB per day per card” (~$9–$11 USD; case 141). In other cases, earnings were tied to transaction volume, with commission rates ranging from 0.2% to 15%. For example, case 112 noted that “recruits were promised 0.2–0.6% per laundering transaction,” while in case 118, an offender “discussed a 15% commission via the Bat app.” Higher rates were often offered for riskier tasks such as physical withdrawals, with some participants receiving “14–16% for cash or scan-based transfers” (case 131).
Organizers and mid-level brokers also profited by taking a cut of the transactions processed through their recruits. In case 76, one participant “paid 6% of the total amount processed by introduced cardholders” to an intermediary, who “then deducted his own share and distributed the remainder.” A similar structure is seen in case 217, where a recruiter was “promised 3 to 4%,” while the cardholders themselves received “5% of the laundered amount.” Other arrangements mimicked multi-tiered pyramid structures, with each actor from recruiter to cardholder receiving a fractional payout. Some individuals negotiated mixed profit models, as in case 122, where “90% of a specified amount was transferred to the upstream as a ‘deposit,’ and 10% was retained as profit.”
These diverse arrangements illustrate the equifinal nature of payment models in laundering operations, encompassing flat rates, commissions based on risks, mixed profit models, and non-monetary incentives. In many instances, commissions served not only as compensation but also as recruitment tools, with participants bringing in others in exchange for referral payments. For example, case 214 details how the defendant was “paid ¥1,000 per card provider he introduced,” (~$143 USD) and in case 205, the defendant was “promised high commissions in exchange for introducing others willing to provide bank cards.” These sub-actions, including negotiation of initial payment and referral recruitment, were often discussed informally through social media platforms such as WeChat, QQ, TikTok, and Telegram-like apps (e.g., Feiji and Bat), and sometimes included non-monetary benefits like “free travel, meals, and lodging” (case 88 and case 38).
Phase 2-2: Account and/or Identity Transfer or Control
Following the commission stage, the laundering process enters a critical operational phase marked by the transfer of control over financial instruments, namely bank accounts, mobile phones, SIM cards, and identity credentials. This phase is distinct from the preparation stage, where offenders acquire, open, or trade accounts and SIMs. While preparation focuses on assembling usable assets, the control transfer phase involves the functional handover and remote enablement of those assets for real-time laundering activities.
Whereas in the preparation stage offenders might gather multiple bank cards under their own or others’ names, often through underground markets or acquaintances, in the control transfer phase, those cards are actively handed over to the laundering network. This handover process reflects equifinality in operational methods, including the utilization of runners’ own bank cards or third-party identity-based cards. For instance, in case 107, a defendant “provided his bank card, phone, and banking credentials to a fraud ring, resulting in over 900,000 RMB in transactions” (~$1,286 USD). In case 129, a recruit “fraudulently obtained a friend’s card and phone, handed them over to the group, and personally assisted in credential setup at the laundering site.”
This whole process also involved phased payment settlements, where actors were compensated upon successful handover of financial instruments. For example, in one case, “[Recruits] provided two bank cards (Bank of China and China Construction Bank) to [runners], who gave [recruits] a few hundred RMB in cash in person” (case 118) as immediate payment for the cards. Similarly, in case 222, “[defendant] contacted his brother-in-law and offered to pay 3,000 yuan (~$429 USD) per month for each lower-limit card and 4,000 yuan (~$571 USD) for higher-limit ones if he could obtain such cards. [Brother-in-law] was also told to collect accompanying phone cards, second-hand phones, and ensure card trial activation.” Such transactions illustrate how financial settlements are embedded within the transfer process itself, serving both as an incentive for card providers and as a validation mechanism to ensure that upstream operators receive functional accounts ready for laundering use.
Cases also reveal escalating levels of compliance and sub-actions within this phase, such as credential setup assistance, packaging of card/SIM/phone/U-shield sets for upstream use and performing biometric verification to finalize transfer completion. Participants not only gave up cards but also “cooperated in facial recognition authentication to validate fund transfers” (e.g., case 120, case 137, case 168, and case 186). For example, in case 168, “[defendant] handed over his mobile phone, four bank cards (from Agricultural Bank of China, Industrial and Commercial Bank of China, Jiujiang Bank, and Postal Savings Bank), PIN codes, and payment passwords to the group. He personally performed facial recognition operations on-site to facilitate illicit transactions, actively assisting in the laundering scheme.” Some actors assumed third-party identities or used borrowed credentials, effectively transferring control over both financial assets and legal identities. For instance, case 236 noted that a charged recruit “provided 19 bank cards, including several under his parents’ names.” Meanwhile, others, like in case 213, “sold accounts complete with SIMs and U-shields,” enabling upstream operators to execute transactions with minimal physical presence.
Phase 2-3: Initial Fund Movement
Once control over bank accounts and associated identity credentials is transferred, the laundering operation proceeds to a trial phase involving small-scale transactions, referred to in both court records and participant testimony as “water testing 7 ” or card verification. The goal of this subphase is to confirm that a bank card is fully functional for the intended laundering purposes. This process is typically involving low-value or split transactions that simulate real use conditions. For example, in case137, investigators noted that “Defendant B conducted bank card verification tests following instructions on WeChat and Telegram apps.” Similarly, case 138 describes a staged operation where the defendant “mailed his bank card, SIM, and ID to a contact, who then used the materials to conduct test transactions before laundering larger amounts.”
In some instances, actors personally performed facial recognition or password input to unlock card functionality, such as in case120, where the defendant “assisted in withdrawing 20,000 RMB in cash after successfully verifying identity credentials.” Other records, like case 214, demonstrate multi-level relay of verification: “Screenshots of online banking logins were passed up the chain to upstream fraudsters, who only initiated transfers after confirming card usability.” Essentially, this step served as both a technical validation and trust-building measure. It reassured upstream operators of the card’s transactional reliability and the user’s compliance, thereby enabling further integration into the laundering network.
These verification transactions were not benign. The financing source for this phase was illegal, as the small test amounts themselves often originated from fraud proceeds. For example, in case 149, it was recorded that “these cards processed a total of 542,010 yuan (~$77430 USD), of which 301,000 yuan (~$43000 USD) was directly linked to telecom fraud.” Similarly, case 107 indicated that the bank card processed “903,475 RMB (~$129,068 USD) in total transactions, of which 544,975 RMB (~$77,854 USD) was traced to fraud victims,” while case 123 noted that “[defendant]’s bank card received a total of 120,366.8 RMB (~$17195.2 USD), including 50,000 RMB (~$7143 USD) defrauded from victim.” Thus, this step not only served as a technical validation and trust-building measure but also formed an integral part of the broader financial-economic crime chain.
Phase 3: Core Laundering Execution
The third phase represents the core laundering stage, where illicit funds are actively processed and concealed through a structured system of specialized actor roles and operational techniques. In this stage, launderers and runners deploy their risk management skills to ensure successful fund transfers while evading detection. Actors are differentiated by their functions as fund receivers, transfer agents, withdrawal operatives, and logistical facilitators, each playing a critical role in sustaining the seamless flow of criminal proceeds. Laundering is executed through methods such as rapid bank transfers, mobile payment systems, and point-of-sale (POS) terminals, with activities coordinated in real-time via encrypted messaging applications.
Phase 3-1: Laundering
The evidence across multiple groups indicates that the primary laundering method utilized by these criminal networks is a coordinated system of Pao Fen operations, functioning as an organized, multi-stage process involving the systematic collection and deployment of bank cards, mobile payment platforms, POS terminals, and sometimes cryptocurrency to transfer and conceal illicit funds. Building upon the infrastructure preparation and activation/transfer stages, this phase involves the actual execution of laundering, where illicit funds are moved, layered, and integrated into the financial system. At the top were organizers and coordinators who planned and supervised operations, as in case 104, where a defendant “acted as organizer and recruiter in a criminal network that facilitated the transfer of fraud proceeds via ‘card runners’,” introducing “multiple individuals to an upstream criminal organization and coordinated the use of their bank cards, phones, and verification information.” Beyond card provision from runners, technical operators authenticated and executed transactions; for example, case 148 documented a defendant who “cooperated in various ways, including facial recognition, SMS verifications, and manual transfers,” and case 117 described a participant who “helped operate software; fund flow: ¥3.37 million,” (~$470,000 USD) while a co-defendant “transferred funds totaling ¥12.28 million” (~$1,710,000 USD) using laundering software like “Paper Airplane.” Field facilitators such as drivers, logistics personnel, and watchers secured physical operations; in case 108, a facilitator “drove others using ride-share vehicles,” while another “was caught on ATM surveillance withdrawing fraudulent proceeds,” and in case 208, two defendants “monitored card holders in hotels to ensure they didn’t abscond,” with one “recording incoming transfers daily.”
At the core of this laundering process is the method of using large-scale recruitment or exploitation of individuals to obtain personal or newly registered bank cards, which are then used to move illicit funds through mobile payment platforms and rapid transfers. These cards are often provided along with linked SIM cards, mobile phones, and access credentials. For example, in case 115 and case 124, defendants knowingly supplied multiple bank cards which were used to channel millions in illicit funds, including confirmed proceeds from telecom fraud. This laundering method also involves systematically verifying cardholder identities through facial recognition and conducting trial transactions before deploying the accounts for fund transfers, as seen in case 127 and case 132. Once fraud proceeds were deposited into these verified accounts, the funds were rapidly moved using mobile payment tools such as WeChat Pay and Alipay. As illustrated in case 104 and case 101, funds were either withdrawn at ATMs or transferred via mobile apps to upstream coordinators. The use of digital wallets enabled swift, low-cost transactions while providing anonymity and operational speed, making them an essential method within the laundering chain.
In parallel, many laundering groups operated or accessed POS terminals, some linked to shell companies, to simulate legitimate commercial transactions and transform illicit funds into seemingly lawful revenue. In case 1 and case 126, POS machines were distributed and activated in private or secluded locations, where team members swiped cards to mimic business activity. A particularly sophisticated variant of this was seen in case 111, where the group swiped funds through liquor stores, falsely purchased Maotai liquor, and later returned the products, effectively converting criminal proceeds into clean money. Similarly, in case 52 and case 47, laundering was channeled through shell companies registered under trade names with accounts set up in provincial banks, thereby embedding illicit cash flows into the formal banking system.
Another key laundering mechanism involved the conversion of criminal proceeds into cryptocurrency, especially USDT (Tether). 8 This method was evident in case 3, case 29, and casec5, where actors received large amounts of cash or used fraudulently obtained funds to purchase digital assets and transfer them to unknown upstream actors, often across borders. The use of USDT provided enhanced anonymity and allowed for easy cross-platform and cross-border movement of value without immediate traceability.
Finally, several laundering operations were directly tied to online gambling platforms, which acted as both the source and destination of illicit funds. In case 117, the gambling site “Cai Shi Jie” was shown to have processed tens of millions of yuan through over 800 bank accounts linked to participants in Pao Fen operations. These platforms used commission-based incentives to attract users and launderers alike, offering a percentage of each transaction to agents or money mules. Other cases, such as case 230, documented how individual actors used personal and family members’ bank accounts to perform Pao Fen transactions that funneled criminal proceeds through gambling sites like Yihao Entertainment and Nangong Entertainment.
Importantly, this body of evidence makes it clear that virtually all of the laundering operations conducted by these groups were rooted in fraudulent schemes targeting individual victims. For example, in case 104, fraud proceeds totaling approximately ¥23,236 (~$3,200 USD) were directly traced to victim losses. In case 102, laundered funds amounting to ¥145,800 (~$20,100 USD) were linked to specific defrauded individuals. The pattern is pervasive: case 107 confirmed that of the ¥903,475 (~$124,000 USD) processed through a single bank card, over ¥544,000 (~$74,700 USD) originated from scam victims. Case 120 documented that one Bank of China card was linked to 13 telecom fraud cases, involving more than ¥1 million (~$137,800 USD) in confirmed victim losses. Similarly, case 152 showed that a single defendant’s accounts processed over ¥793,000 (~$109,300 USD), of which ¥471,635 (~$65,100 USD) were verified as fraud proceeds from at least 15 identifiable victims. These laundering networks processed funds obtained through various types of fraud, including romance scams, investment schemes, fake job offers, and social media impersonation. Each transaction represented money stolen from actual victims in China and, in some cases, from individuals in other countries.
Phase 4: Conversion and Integration
The conversion and integration stage constitutes a critical endpoint in the laundering process, wherein illicit funds are transformed into usable forms and reintegrated into criminal or legitimate financial systems. This stage comprises three interrelated substages. First is cash withdrawal or conversion, in which electronically transferred funds are withdrawn as physical cash or converted into untraceable digital assets such as cryptocurrency. Second is profit retention, involving the allocation and distribution of proceeds to participants according to prearranged payment structures. Third is arrest and disengagement, where runners either face apprehension by law enforcement due to heightened surveillance or, if undetected, prepare to re-enter the laundering cycle. Key actors during this stage include withdrawal operatives, who execute cash-outs and conversions; organizers and coordinators, who oversee profit distribution and operational management; and new recruits, who are mobilized for future laundering activities.
Phase 4-1: Cash Withdrawal or Conversion
After completing the first cycle of laundering, the subsequent stage involves multiple equifinal actions to convert electronically transferred funds into usable forms. Funds are withdrawn as physical cash through ATMs or bank counter services, often split into multiple transactions to avoid detection. In case 102, approximately ¥250,000 (~$34,400 USD) was withdrawn through eight separate transactions before being handed to a superior. Case 177 documents rapid withdrawals totaling ¥191,000 (~$26,300 USD) across multiple bank branches in Xi’an, a major city in northwestern China. In case 203, large cash amounts of ¥195,000 (~$26,800 USD) and ¥190,000 (~$26,100 USD) were withdrawn directly from cards issued by China Construction Bank and the Industrial and Commercial Bank of China, respectively. These withdrawals were sometimes accompanied by facial recognition procedures or by fabricated narratives, such as “buying crayfish,” to reduce suspicion and maintain the appearance of legitimate financial activity. Additional operations in cases 183, 189, and 232 reveal strategic cash-outs at both ATMs and bank counters. In parallel, funds are also converted into untraceable digital assets. In cases 117 and 126, profits were issued in USDT (Tether) and were later converted into Chinese currency (RMB) through cryptocurrency platforms such as the OKX app, 9 one of China’s major digital asset exchanges. A similar laundering pattern appears in case 137, where approximately ¥229,000 (~$31,500 USD) was passed through multiple intermediaries before reaching a handler. Furthermore, some funds are routed electronically to multiple recipients to fragment flows and reduce traceability. In case 102, an additional ¥78,070 (~$10,700 USD) was routed via Alipay QR codes to various recipients.
Phase 4-2: Profit Retention
In the meantime, once the cash is secured, upper-level organizers typically allocate a predetermined share of the profit to each runner. This amount is usually based on a fixed sum or a percentage that was agreed upon during the second stage of the laundering process. These payouts are distributed in a variety of ways, sometimes handed over in cash during face-to-face meetings, or transferred digitally through platforms like WeChat Pay or Alipay. Across the cases, profit margins varied significantly based on role, volume, and proximity to upstream coordinators. For example, case 117 details how one runner earned ¥12,000 (~$1,650 USD) for handling over ¥7.8 million (~$1.07 million USD), while another received ¥18,000 (~$2,480 USD) from ¥3.37 million (~$462,600 USD). At the lower end, case 103 participants received modest profits of around ¥1,800 (~$250 USD). In case 108, one individual received ¥6,500 (~$900 USD) for providing just two cards, while another, with eight cards and over ¥1.3 million (~$178,900 USD) laundered, earned at least ¥2,000 (~$275 USD). Some profits were tied directly to card ownership, as seen in case 113, where one person was paid ¥9,000 (~$1,240 USD) to lend a card. Others, like in case 126, were compensated in cryptocurrency (e.g., USDT), then converted and transferred to relatives’ accounts.
Phase 4-3: Arrest and Disengagement
Importantly, this stage marks a critical turning point for participants in Pao Fen operation. Following the final payout of the first laundering cycle, runners face a diverging path. They may be apprehended by law enforcement, often because of increased surveillance and flagged accounts, or, if undetected, they may continue their involvement by preparing for the next laundering cycle. This preparation typically involves recruiting new runners, obtaining fresh bank cards, relocating to new areas, or adopting alternate identities to evade detection. In effect, they restart the laundering process from the beginning. For more experienced participants, this cycle of cashing out, receiving profits, and re-engaging in the laundering network becomes a continuous loop, carried out with increasingly careful and sophisticated methods to avoid law enforcement scrutiny.
Phase 5: Network Consolidation and Expansion
At the stage of network consolidation and expansion, Pao Fen runners who were not apprehended after the first laundering cycle shifted from single participation to embedded roles within a structured and persistent laundering system. This phase is characterized by repeat participation, where participants provide cards and conduct transfers multiple times. For example, in case 118, one participant initially handed over two bank cards in February 2023 and “again handed over his phone, ID, and three cards” to the laundering team a few days later. These cards received “over 2.88 million RMB (~$397,000 USD), 4.52 million RMB (~$623,000 USD), and 1.73 million RMB (~$238,700 USD) respectively,” demonstrating escalating transactions through repeated engagements (case 118).
Another key action was recruitment, where participants recruited others and paid bonuses to expand the network. In case 118, a co-defendant contacted a laundering group through the Bat app and recruited another participant, promising a “15% commission,” reflecting a structured recruitment and compensation mechanism. Similarly, case 153 shows a layered recruitment model: after being recruited in March 2022, the participant introduced another person and offered him “¥1,500 per referral” (~$207 USD), leading to multiple new recruits who replicated these roles. In case 115, a defendant offered “a ¥300 referral bonus for each new card provider” (~$41 USD) and coordinated recruitment with another participant. Case 127 records an individual receiving “800 RMB and a 250 RMB pack of cigarettes” (~$110 and $34 USD, respectively) for repeatedly introducing another person, while case 90 further illustrates multi-layered recruitment with direct financial rewards for each card or recruit.
This stage also involved tool reuse, with participants reusing cards, POS terminals, and reissuing cards after freezing. In case 126, a participant coordinated the use of “multiple POS terminals shipped nationwide” and borrowed or purchased credit cards from various associates, keeping these tools activated and circulated across laundering cycles. Case 69 shows bank cards passed through multiple hands and used across cities. Even after enforcement actions, participants adapted operations: in case 142, participants “reissued new cards with the same banks” and “again provided them for criminal use.” Case 184 illustrates persistent tool use where cardholders processed over “5.73 million RMB (~$790,800 USD)” across three accounts within months, with “664 deposits and 91 withdrawals,” emphasizing repeated operational flows.
Finally, role escalation occurred as runners became intermediaries managing recruits and operations. In case 124, a participant systematically provided bank cards, including both his own and those obtained from others, supporting ongoing transactions. Between late December 2022 and January 2023, one card processed “over 25 million RMB” (~$3.45 million USD), while another, used by a recruited associate, processed “fraud proceeds from at least 43 victims totaling 2,209,825 RMB” (~$305,000 USD). This participant also introduced additional individuals in March and April 2023, facilitating “over 2.4 million RMB” (~$331,400 USD) and “over 700,000 RMB” (~$96,700 USD) in transactions, demonstrating how runners escalated to managerial roles within a decentralized yet cohesive laundering infrastructure.
Phase 6: Detection and Termination
The final phase of Pao Fen operation, as reflected in the identified legal documents, typically ends with the arrest, prosecution, and sentencing of involved participants. These legal actions formally dismantle certain laundering cells or subgroups, often targeting cardholders, recruiters, and low-level operatives. However, the evidence suggests that this form of exit is incomplete. Many key individuals, including upstream organizers and some repeat offenders, remain uncaptured and are identified in court records as fugitives or unindicted co-conspirators. Their continued evasion emphasizes the decentralized and resilient structure of Pao Fen networks, which can degenerate and regenerate quickly. Remaining actors still possess access to communication tools, financial infrastructure, and recruitment channels, enabling the continued circulation of illicit funds even after partial law enforcement interventions.
The Construction of Situational Interventions for Pao Fen
Building on the detailed analysis of each phase in Pao Fen operations, this study proposes a set of dynamic, context-specific situational interventions that target the specific cues and vulnerabilities present at each stage of the laundering process. These interventions are guided by Cornish and Clarke’s (2003) Situational Crime Prevention (SCP) framework, particularly its focus on reducing opportunities for crime by increasing the perceived effort and risk, reducing the potential rewards, and removing justifications. To apply the situational crime prevention framework to organized laundering, this study develops targeted intervention strategies for Pao Fen operations based on crime script analysis. By systematically examining each stage of the laundering process, the study identifies practical prevention measures aligned with SCP’s strategic dimensions. These strategies translate theoretical insights into concrete actions to disrupt Pao Fen activities, addressing specific opportunities and vulnerabilities within the laundering process.
Preventions on Infrastructure Preparation Stage
The laundering process often begins with offenders leveraging personal trust networks, such as recruiting friends, intimate partners, or relatives who can provide financial tools like bank accounts and SIM cards with little suspicion. Others are drawn in via open-source advertisements on platforms such as WeChat Moments, Baidu Tieba, gambling forums, or pop-up ads that promise easy money. Simultaneously, access to identity-linked tools is facilitated through underground vendors or fabricated documents.
Prevention at this stage involves deflecting offenders by monitoring these platforms for recruitment content and issuing targeted digital awareness campaigns to vulnerable users. Authorities should also harden targets and control access by enhancing KYC protocols, 10 , particularly flagging new accounts opened in bulk or under dubious credentials. Auditing shell company registrations and cracking down on fake storefronts is equally crucial, as these often serve as laundering fronts.
Prevention Toward Activation and Access Setup
As recruits transition into active laundering roles, Pao Fen participants often relinquish full control of their digital and physical instruments, including phones, SIM cards, bank cards, and in many cases, their biometric data. These assets are then used for test transactions, commonly referred to as “water testing,” to validate card functionality and assess participant reliability.
At this stage, the deployment of control tools becomes vital to disrupting laundering operations. Financial institutions should implement technological measures such as anomaly detection systems capable of identifying irregular login locations and device switching behaviors suggestive of test transactions. To further identify property and track high-risk assets, identity protection strategies should include the registration and monitoring of tools such as USB based U shields and preconfigured mobile devices. These tools should be auditable across both banking and telecommunications infrastructures to ensure accountability and traceability. AI driven verification audits can aid in detecting anomalies in device usage and biometric inconsistencies, particularly when access occurs from geographically inaccessible locations. In addition, institutions should use place managers, who oversee specific locations to prevent crime by monitoring activities and enforcing rules, by training frontline personnel such as bank clerks and telecom service agents to recognize signs of proxy behavior during onboarding and identity verification.
Prevention Toward Core Laundering Execution
Laundering execution is the most dynamic stage, where funds are actively laundered through a diverse toolkit: mobile wallets (WeChat Pay and Alipay), shell-company-linked POS terminals, USDT cryptocurrency conversions, and online gambling platforms. Operations are geographically mobile and structurally compartmentalized, meaning that offenders deliberately separate roles across different actors to limit risk exposure.
The deployment of a robust artificial intelligence strategy is vital to effective intervention. Efforts to strengthen formal surveillance should include machine learning algorithms trained on transactional behavior patterns to flag abnormal e-wallet usage, particularly those involving cross-platform or cross-region high-volume transfers within short timeframes. To disrupt markets, AI systems can be leveraged to map interbank transfer chains and uncover circular fund flows between accounts linked to shell companies, thereby exposing laundering infrastructures. Simultaneously, institutions should utilize place managers by requiring payment processors and merchant service providers to monitor and report point-of-sale terminals that exhibit irregular patterns, such as high-value transactions at unusual hours or sales inconsistent with the registered business type.
Prevention Toward Conversion and Integration
Once money has been cycled through digital or pseudo-commercial platforms, it must be extracted. Offenders typically accomplish this through ATM withdrawals, in-person handoffs, or digital disbursements via Alipay and WeChat. Cryptocurrency is often used to obscure the final trail, with funds converted into USDT and routed to trusted third parties such as relatives. This stage also marks the redistribution of profits and the recruitment of new actors, thereby completing the feedback loop.
Effective countermeasures should include identity protection protocols that identify property, such as requiring biometric authentication for high-frequency ATM withdrawals and monitoring repeated transfers to unverified or non–Know Your Customer compliant wallets. At the same time, authorities should disrupt markets by targeting the resale of “cleaned” goods used in fabricated transaction laundering schemes, including high-end luxury liquor. Restricting access to known cryptocurrency off-ramp services can further limit opportunities for illicit fund conversion. To discourage imitation, enforcement agencies should publicize failed second stage laundering attempts and impose clearly visible penalties to demonstrate consequences and deter replication. Artificial intelligence can enhance these strategies by profiling cash-out patterns, detecting overlapping payout behaviors, and assigning dynamic risk scores to mule accounts likely to be reactivated in future laundering cycles.
Prevention Toward Network Consolidation and Expansion
Persistent laundering networks are sustained through the repeated use of tools such as point-of-sale terminals, phone numbers, and bank accounts, along with recurring behaviors and pyramid-like recruitment structures that offer incentives for each new runner recruited. Offenders who evade apprehension often re-enter subsequent laundering cycles, using encrypted communication platforms to reorganize quickly and covertly. In this context, efforts to extend guardianship can be advanced through artificial intelligence–driven network analysis, which links otherwise unrelated accounts, terminals, and devices by detecting shared usage histories or overlapping identifiers such as IP addresses and device fingerprints. This enhanced surveillance capacity allows for the identification of layered recruitment structures and the early detection of repeat involvement. To deflect offenders, financial institutions should adopt control measures that restrict the issuance of financial instruments across multiple regions, particularly targeting individuals previously flagged through investigations or identified by high-risk behavioral indicators.
Prevention Toward Detection and Termination
During the exit phase, authorities should reduce anonymity by issuing nationwide digital wanted notices linked to biometric data, thereby limiting offenders’ ability to operate under false identities. Simultaneously, they should screen exits by seizing tools previously used in laundering activities such as devices, cards, or accounts, and blacklisting them to prevent future re-registration or misuse. To alert conscience, law enforcement can provide structured incentives for voluntary disclosure, such as sentence reductions in exchange for full cooperation, which may motivate internal actors to come forward and expose the broader network. These efforts should also extend guardianship through the use of artificial intelligence assisted suspect mapping and cross case linkage analysis, which can uncover complex organizational structures and recurring offender patterns that may otherwise remain hidden.
Discussion: New Criminological Insights into Laundering Networks from Pao Fen Case Analysis
Pao Fen has emerged as a pervasive and deeply embedded cyber-enabled money laundering practice across China, as well as in other East and Southeast Asian countries, reflecting a national-level challenge in the control of financial crime. Despite the severity and visibility of this issue, as evidenced by recurring law enforcement operations and media coverage in Chinese provinces such as Guangdong, Guangxi, Henan, Jiangxi, and Shanxi (see, e.g., Guangdong Provincial Public Security Department, 2024; Wang & Tian, 2024; Xinhua News, 2024), there remains a notable absence of comprehensive, centralized datasets documenting the scale, actor typologies, and operational patterns of Pao Fen participants. Current academic research in this space is limited and tends to rely on high-level summaries, descriptive statistics, or official reports, without much rigorous empirical engagement (e.g., Pei & Jiao, 2024; Yan, 2022; Zhao, 2024). Particularly lacking are English-language studies that systematically analyze the internal dynamics, tools, and behaviors that constitute the laundering process.
This study addresses that gap by offering the first empirically grounded operational model of Pao Fen, derived from a unique dataset of Chinese judicial case records. Through detailed analysis of 235 cases, this study identified six-phase operations in Pao Fen comprising: Infrastructure Preparation, Activation and Access Setup, Core Laundering Execution, Conversion and Integration, Network Consolidation and Expansion, and Detection and Termination. These stages reflect the transformation of laundering from individual experimentation into institutionalized, cyclical criminal routines. Based on this operational logic, this study develops targeted strategies for disrupting Pao Fen by applying situational crime prevention principles to each stage of the process.
Among the findings, one of the most critical insights is the identification of self-initiated offender trajectories within Pao Fen. In contrast to the dominant narrative presented in much of Western scholarship, which often depicts money laundering participants as individuals who are recruited either willingly or under coercion by hierarchical criminal organizations (Abdul Rani et al., 2024; Leukfeldt & Kleemans, 2019; Raza et al., 2020), this study uncovers a distinct subset of actors who proactively and voluntarily entered laundering networks. These individuals did not wait to be approached or manipulated. Instead, they actively sought out opportunities to engage in laundering activities by leveraging digital platforms such as Baidu Tieba, WeChat Moments, and encrypted communication tools such as Telegram and Bat. These offenders demonstrated a high level of autonomy as they independently navigated the entire process, from identifying potential laundering schemes to acquiring the necessary digital tools, understanding operational protocols, and participating in fund transfers. In doing so, they bypassed traditional recruitment structures, treating laundering as a self-driven opportunity rather than a coerced act. This finding challenges the conventional framework and points to the existence of voluntary, self-directed offenders. Recognizing this offender type has important implications for both criminological lens and law enforcement strategies. It clarifies how individuals may self-select into criminal economies online and highlights the ways in which digital environments facilitate both recruitment and voluntary entry into illicit financial systems.
A second key insight lies in the identification of persistent and repeatable behaviors among Pao Fen participants, revealing a structured and evolving criminal network. The analysis in this study shows that laundering activities are not isolated or opportunistic events but instead routinized and cyclical processes, often carried out by the same actors across multiple laundering cycles. These individuals frequently reuse or reacquire similar tools, including previously frozen bank accounts, reissued bank cards, POS terminals, and cryptocurrency wallets, demonstrating a high level of operational continuity and adaptability. Beyond tool reuse, the findings also reveal patterns of internal recruitment and hierarchical progression within laundering networks. Experienced participants do not merely continue their own operations, instead they often recruit and mentor new participants, expanding the network and solidifying their roles as mid-level coordinators or team leads. In some cases, individuals who began as basic fund runners progressed to more strategic roles, such as managing Telegram groups, providing technical onboarding, or distributing illicit profits, indicating a form of promotion and role specialization. This pattern of behavioral persistence and internal advancement suggests that Pao Fen operations function with quasi-organizational structures, allowing them to regenerate and scale even after law enforcement interventions. Traditional deterrence efforts, such as freezing individual accounts or disrupting a single laundering chain, are insufficient in the face of such systemic resilience. To address this, a more dynamic framework needs to be proposed to prevent this type of criminal behaviors such as the current proposed framework to longitudinal monitor offender behaviors, including AI-driven detection of repeated tool usage, role evolution, and recruitment behaviors, to more effectively disrupt these adaptive laundering networks.
A third major contribution of this study is the recognition that Pao Fen activities are not static or isolated events, but rather dynamic, adaptive, and continuously evolving operations. Effectively countering them requires ongoing threat profiling and intervention strategies that are both flexible and technologically sophisticated. This conclusion is supported by several key features observed in Pao Fen operations. First, runners frequently employ deliberate risk avoidance strategies, including geographic relocation and structured transaction patterns. Second, laundering behaviors are persistent and repeatable, often carried out across multiple operational cycles. Third, although the organizational structure is relatively loose, it maintains a functional hierarchy that allows actors to shift roles and expand activity as needed. Finally, participants display a high level of digital fluency, as seen in their use of encrypted communication platforms, virtual currencies, and remote-access tools to maintain operational secrecy and scalability. In response to these complexities, integrating AI-based surveillance and intervention mechanisms within this stage-based situational interventions constitutes a valuable application of situational crime prevention principles to complex laundering network. Traditional situational crime prevention strategies, such as increasing guardianship and limiting access to crime opportunities, remain relevant for disrupting Pao Fen operations. Their effectiveness can be further strengthened through the integration of artificial intelligence tools capable of real-time anomaly detection, behavioral pattern analysis, and mapping of decentralized laundering networks. This integration allows for proactive interventions that target specific laundering stages and behaviors, rather than relying solely on post-incident enforcement. Given the adaptive and dispersed structure of Pao Fen networks, implementing AI-informed situational crime prevention represents a practical advancement to better align interventions with offenders’ operational realities.
Limitations and Future Directions
While this study offers critical insights into the operational dynamics of Pao Fen networks, it is important to acknowledge the limitations in the work that point to the need for further research in this area. First, the study is subject to sampling bias and limited generalizability. Due to technical constraints associated with the judicial document search engine, only the first 600 court cases were accessible and analyzed. As a result, the crime script developed from this dataset reflects a limited subset of Pao Fen cases and may not fully capture the diversity of laundering scenarios occurring across China, as well as other regions in Asia and beyond. For instance, the study does not include cases involving cross-border laundering through cryptocurrency mixing services or laundering strategies embedded in newer digital platforms. Therefore, while the findings offer valuable insight into prevalent laundering patterns, they may not represent the full range of laundering behaviors, especially those involving advanced or evolving technological methods.
Second, the data exhibited significant variability in richness and detail. Although court documents provide more structured and credible information compared to media reports, they remain constrained by legal procedural focus. Most documents are limited to formal charges, legal reasoning, and sentencing outcomes, and often omit deeper insights into offenders’ psychological motivations, internal decision-making processes, or the organizational structures of laundering networks. Additionally, there is often a lack of standardization in how case details are recorded across jurisdictions, resulting in inconsistencies and gaps in the evidentiary base. These omissions restrict our ability to explore offender intent or understand how informal norms and trust operate within laundering networks.
Third, the sample is inherently biased toward apprehended offenders. This means the analysis is based solely on individuals who have been identified, charged, and prosecuted, potentially excluding an important subset of offenders who remain undetected or deliberately operate under the radar using more advanced risk management and anonymization techniques. These individuals may exhibit significantly different laundering behaviors, including the use of crypto tumblers, cross-jurisdictional shell firms, or sophisticated bot-operated laundering chains. Consequently, the current study likely underestimates the technological and procedural diversity that characterizes the full landscape of Pao Fen operations.
In light of these limitations, future research would benefit from incorporating a broader and more diverse range of data sources to more fully capture the complexity and evolving nature of Pao Fen operations. Moving beyond court documents to include qualitative interviews with offenders, digital ethnographies of laundering communities, and computational modeling of laundering flows could offer richer insights into their decision-making processes, operational logics, and technological adaptations. These expanded approaches can not only strengthen the generalizability and depth of crime scripts but also create opportunities to empirically test the effectiveness of the strategies proposed in this study. For example, applying these proposed strategies in controlled simulations or partnering with financial institutions and enforcement agencies to assess real-world implementation could help evaluate its utility in detecting, disrupting, and deterring laundering behaviors.
As the first empirical effort that systematically unpacked Pao Fen launder operations and translated those insights into an actionable intervention framework, this study can provide a foundational step toward more informed, data-driven strategies for combating cyber-enabled financial crime. Future research should build on this foundation to refine, validate, and adapt intervention tools in response to the continuously evolving laundering landscape.
Footnotes
Declaration of Conflicting Interests
The author declared no potential conflicts of interest with respect to the research, authorship, and/or publication of this article.
Funding
The author received no financial support for the research, authorship, and/or publication of this article.
