Abstract
Sink location protection is critical to the viability of sensor networks as the central point of failure. Most existing work related to sink location protection focuses on local traffic analysis attack. In this paper, we study the sink location protection problem under a more powerful type of attack, the global traffic analysis attack. In order to hide the sink location, a protocol based on packet sending rate adjustment (SRA) is proposed. By controlling the packet sending rate of each node according to the current number of source nodes, SRA conceals the real traffic volume generated by source nodes and hence disguises the location of the sink. For further reducing the communication cost, we propose a light weight SRA protocol (L-SRA), which protects the sink location while significantly decreasing the communication cost. Performance of both SRA and L-SRA has been validated by theoretical analysis and simulation results.
1. Introduction
Wireless sensor networks (WSNs), which feature information sensing, data processing, and wireless communication, have been widely used in military and civilization sectors [1, 2]. A typical WSN is composed of hundreds of sensor nodes and one sink. Once a sensor node detects an abnormal event, it acts as the source node (or source) and sends several event (or real) packets periodically to the sink. Then, the sink collects these packets and sends them to the network manager. Such many-to-one communication pattern makes the sink the central point of failure [3, 4]. An attacker could destroy the sink physically after tracing and locating it and hence paralyze the whole sensor network. Therefore, preserving the sink location is of great importance, and sink damage can cause the whole network to become useless.
Two types of sink location attacks can be used to determine the location of the sink, the global traffic analysis attack (GTA) [5–9] and the local traffic analysis attack (LTA) [10–14]. Existing sink location protection protocols mostly consider the local traffic analysis attack. The schemes against the local attack [10–14] become ineffective in the presence of a global attacker, since a global attacker attempts to locate the sink by identifying the region exhibiting a high traffic sending rate. For example, the global attacker can deduce the location of the sink by monitoring the high volume of transmissions caused by the appearance of a new source (or several new sources). We thus focus on the privacy preserving techniques that defend against a global attacker.
There are several solutions proposed to defend against global attackers [5–9]. However, some of them generated high traffic volumes around the sink [5, 6, 9]. Consequently, the sink cannot be well concealed. Some other solutions are based on several restrict assumptions which were not suitable to most applications [7]. A simple solution proposed by [8] tried to control the packet sending rate of each node in such a way that every node sent packets at the same rate. However, if sensor nodes send packets at a low rate, the real packets must be delayed seriously. On the contrary, if sensor nodes send packets at a high rate, the communication cost is high. To address above problems, in this paper, we propose a sink location protection protocol based on packet sending rate adjustment (SRA) under the global attack. SRA sets the packet sending rate of each node according to the current number of sources in WSNs. (Note that the packet sending rate of each node is the sum of the event packet sending rate and the fake packet sending rate.) With uniform packet sending rate across the entire sensor network, SRA can defend against global attack effectively without incurring extra forwarding latency (the latency from event packet receiving to event packet forwarding by a node). Based on SRA, we further find that the communication cost can be significantly reduced if the packet sending rate is set according to the maximum traffic of the network. So we continue to propose a light weight SRA protocol (L-SRA), which protects the sink location successfully while decreasing the communication cost significantly. Particularly, L-SRA does not increase forwarding latency. Performance of SRA and L-SRA has been validated by analysis and simulation results.
The rest of the paper is organized as follows. Section 2 introduces the related work. We then present our network and attack models in Section 3. Sections 4 and 5 propose our new protocols, SRA and L-SRA, respectively, for sink location protection against the global attack. The performance analysis of our scheme is given in Section 6. Section 7 presents the performance evaluation through simulations. Finally, we conclude the paper with future work in Section 8.
2. Related Work
A variety of approaches have been used to protect the sink location, such as fake message injection, randomization of forwarding delay, and the use of fake sinks in order to hide the real sinks' positions [8]. Generally, existing related work can be classified into sink location protection against a local eavesdropper (LTA) [10–14] and sink location protection against a global eavesdropper (GTA) [5–9].
In order to defend against the local eavesdropper, Deng et al. [10] introduced a technique to protect sink location by changing the ID field from time to time. In [11], it was shown that, by carrying out rate monitoring and time correlation attacks, an attacker can trace sinks. To mitigate these two kinds of attacks, Deng et al. presented four schemes including the multiple-parent routing scheme, the controlled random walk scheme, the random fake path scheme, and the hot spots scheme [11]. In [12], fake packets and redundant hops are considered to misguide the local attacker when real packets are sent to the sink. In order to balance between the packet delivery latency and the sink's location privacy, Li et al. [13] proposed an intelligent fake packet injection scheme based on the random walk. Ebrahimi and Younis [14] protected the sink's location by improving the traffic volumes in low-traffic-activity areas. So the local attacker will be distracted to these areas other than the sink. However, these techniques cannot resist passive traffic analysis attacks under a global attacker. A global eavesdropper can easily defeat these schemes. For example, the global eavesdropper only has to find the area with a high number of transmissions to locate the sink.
For a motivated attacker, eavesdropping on the whole network is a fast and effective way to locate the sink. In [6], fake sinks were designed to confuse a global attacker. Although fake sinks can protect the sink from local attacker, it is not effective in the case of a global attacker. This is because global traffic analysis can identify all fake and real sinks according to the high traffic volume compared with other areas. Acharya and Younis [5] consider the attackers with both local and global views. Since nodes near the sink send more packets than other nodes, the global attacker attempts to find the area with high traffic volume and then locate the sink. BAR was proposed to hide the sink location by making the sink selectively transmit packets to random sensor nodes in its vicinity. Relaying these packets away from the sink can confuse a local attacker. However, BAR is efficient to defend against a global attacker. This is because all these packets will definitely travel through the nodes near the sink and then form a higher traffic volume near the sink. Thus, the global attacker can locate the sink by traffic analysis. Ying et al. [7] introduced a concealing sink location (CSL) protocol. Each node in CSL generated the same traffic volume as the sink's neighboring nodes by transmitting a number of fake packets. Thus CSL can defend against traffic analysis attack launched by a global attacker. However, the design of CSL protocol is based on the following restrict assumptions. (a) The sink is located at the center sensor network. (b) Sensors are deployed within a circular area. (c) The deployment is done according to a uniform distribution. Such restrict assumptions do not apply to many real WSN deployments. Mehta et al. [9] introduced fake sinks and backbone flooding to defend against global eavesdropper. In the scheme using fake sinks, each source redundantly sent packets to several fake and real sink nodes. In the backbone flooding scheme, each source sent packets to one of the backbone nodes which then flooded these packets to other backbone nodes. The sink is a neighbor of a backbone node which can overhear the flooding. However, in both schemes, all traffics will meet at either dummy backbone nodes (near the real sink) or the real sink. A simple solution proposed by [8] tried to control the packet sending rate of each node in such a way that every node sent packets at the same rate. However, how to choose an appropriate value for the packet sending rate has not been solved yet.
3. System Model
3.1. Network Model
We assume N evenly distributed sensor nodes and one sink in the whole network. The sink node and other sensor nodes have the same appearance. The sink constructs the network topology (e.g., build the broadcast tree) by one-time broadcast over the entire network [9]. After that, sensor nodes can send packets hop by hop to the sink by parent node of each node [9]. For example, given a node u, its parent set
3.2. Attack Model
Different from sensor nodes, the attackers have faster computational ability and more storage space and can communicate with each other in a larger range. Several attackers are deployed in the network to launch collusion attack. Specifically, their attacking abilities are listed as follows:
Passive Traffic Monitoring: the attacker is able to eavesdrop the packet transmissions in a range but is unable to decipher packets. Ability of Collusion: Several attackers monitor their local traffic separately for a period of time and then move close to share their information. At last, they can infer and obtain the whole network traffic pattern.
4. Packet Sending Rate Adjustment Protocol
In order to defend against the global traffic attacker, we propose an efficient sink location protection protocol based on packet sending rate adjustment (SRA). SRA first investigates what value should be assigned to the packet sending rate of each node so that low communication cost and low forwarding latency can be achieved (e.g., in an extreme case, if all event packets are transmitted by one node, the node cannot transmit all these event packets immediately unless its packet sending rate is high enough). Then, SRA creates a uniform packet sending rate, thus preventing the attackers with a global monitoring ability from tracing the sink with extra low forwarding latency. Specifically, the procedures of SRA include network initialization phase and packet sending rate setting phase.
4.1. Network Initialization
In this phase, each node, say u, initializes a list
4.2. Packet Sending Rate Setting Based on Number of Sources
SRA protects the sink location against global traffic analysis attack by creating a uniform packet sending rate. One important related question is how large the packet sending rate should be. The high or low packet sending rate can result in high communication cost or forwarding latency. Figure 1 shows an example, where three sources (

Event packets forwarding at node
Theorem 1.
If there are m sources, for any sensor, say u, in order to forward the event packets immediately while incurring low communication cost,
Proof.
Given m sources and the fact that the event packet sending rate of each source is R, if u must transmit event packets from
According to Theorem 1, in order to set an appropriate packet sending rate for different subinterval, the sink must obtain the number of sources during the subinterval. As source nodes appear and disappear randomly, once a node, say u, becomes a source, the sink divides (
Step 1 ((
) computation).
The sink computes the time interval, known as (
Once a source, say u, appears, u starts a broadcast
Step 2 (subintervals division).
If a new source u is the only source during (
tag1 = FALSE, tag2 = FALSE; Insert tag1 = TRUE; tag2 = TRUE;
Insert
Insert

Subinterval divivison for a new source.
In Algorithm 1, before u appears, the subintervals and the number of sources are recorded in queues If If For If
Step 3 (uniform packet sending rate creation).
After obtaining the subintervals in Step 2, SRA sets the packet sending rate of each node according to the number of sources at each subinterval. For example, if there are
The sink broadcasts
For instance, Figure 4 shows how SRA adjusts the packet sending rate of each node when four sources including

Duration of event packet sending.

Subinterval division for four sources.
5. Lightweight Packet Sending Rate Adjustment Protocol
In SRA, the packet sending rate of each node for the current subinterval is set to
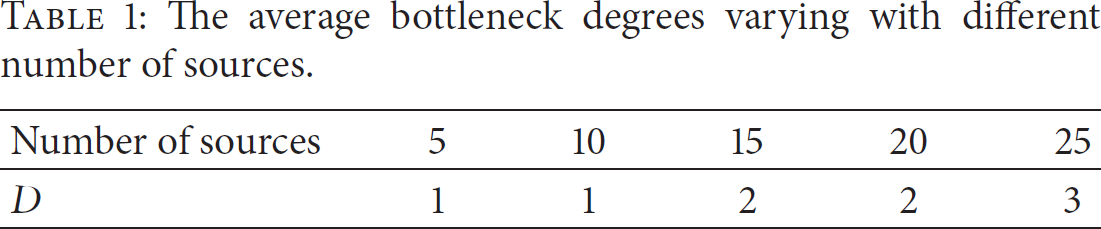
The average bottleneck degrees varying with different number of sources.

The traffic of the bottleneck node.
Definition 2.
Definition 3.
Definition 4.
Definition 5.
In view of the above discussion, we further propose a Light weight SRA protocol, entitled L-SRA, which attempts to further reduce the communication cost of the network and balance the real traffic while achieving the sink location security requirement.
5.1. Overview of L-SRA
When a new source u appears, L-SRA first partitions (
L-SRA includes four major steps: (
Theorem 6.
The more uniform the real traffic is, the less the bottleneck degree for a subinterval σ is.
Proof.
We use entropy to measure the randomness of real traffic. Entropy is a mathematical measure of information uncertainty. Entropy of a random variable X with a probability function 
Suppose that the numbers of event packets transmitted by node v and all nodes in the network are 
Obviously, a higher value of
5.2. Subintervals Division
L-SRA first divides (
//
5.3. Path Construction for Traffic Balance
Here, L-SRA finds shortest path from u to the sink while balancing real traffic distribution. For
add c to v = the node whose traffic degree is minimum from c's parent set;
// increase the traffic degree of each node on the path for sub-interval // update the bottleneck degree for sub-interval
Specifically, the path construction process is as follows. Source u is first selected as the current node; L-SRA then chooses the next node from u's parent set whose traffic degree is minimum during
5.4. Packet Sending Rate Adjustment
In this step, different from SRA, the sink broadcasts not only
6. Performance Analysis
The performance of SRA and L-SRA will be analyzed from the following three aspects.
6.1. Security Performance
A global attacker can ascertain which nodes send packets, their sending rate, and the number of packets. Then the attacker can infer the location of a sink, because the neighbors of the sink node tend to send more packets than other nodes. Our SRA and SRA-L make every node send the same number of encrypted events or fake packets at a constant rate. Therefore, the global attacker cannot determine the sink from the number and rate of packets.
Specifically, we define and use the entropy of the network traffic
Security Performance for SRA. SRA includes two phases: network initialization phase and the packet sending rate setting phase. Without loss of generality, we just analyze the security performance for the latter here because the former is one time and thus the sink is considered to be safe.
In the packet sending rate setting phase, network traffic appears in the following three conditions according to Section 4.2:
The source broadcasts the packet The sink broadcasts the packet Each node sends packets with the same rate. The entropy of the network traffic is
Security Performance for L-SRA. Similar to SRA, the network traffic in L-SRA appears in three conditions. Different from SRA, in L-SRA, the sink broadcasts two packets, one being
6.2. Communication Cost
The communication cost of SRA and L-SRA for a subinterval, say σ, is the total number of packets transmitted for the three conditions described in Section 6.1. There are S sources and
The communication cost of SRA for subinterval σ resulted by two broadcasts and sending packets with the same rate, say
For L-SRA, extra communication cost is added due to the broadcast of the shortest path compared with SRA. And the packet sending rate is different for L-SRA and SRA. Specifically, each node sends packets at the rate of
6.3. End-to-End Latency
We use the number of hops that an event packet takes from the source to the sink on average to measure the end-to-end latency. Take note that the computation time that the sink needs is very short and hence has not been considered for two reasons: firstly, we assume that the sink has powerful computational ability; secondly, the computation process is simple for SRA and L-SRA and hence the computation time can be ignored.
The end-to-end latency for SRA and L-SRA includes the latency incurred by packet transmission and broadcasts from the source and sink. The packet transmission takes
7. Simulation Results
We evaluate the performance of SRA and L-SRA in view of communication cost and end-to-end latency in this section. There are several solutions proposed to defend against the global attackers [5–9]. However, some of them generated high traffic volumes around the sink [5, 6, 9]. So the sink cannot be well concealed. Some of them are based on several restrict assumptions which were not suitable to most applications [7]. The solution proposed by [8] tried to hide the sink location by balancing the traffic distribution without introducing strict assumptions. Thus, we compare our SRA and L-SRA with the “Baseline” scheme proposed by [8]. All the simulations have been performed based on OMNET++. The sink is placed randomly. Each source sends 5 event packets to the sink at the rate of
Figure 6 shows how the communication cost changes as the average number of neighbors, say m, increases for SRA, L-SRA, and “Baseline.” The parameters are set as follows:

End-to-end latency under different protocols.
Next, in order to investigate how S and

End-to-end latency under different protocols.

End-to-end latency under different protocols.
We can observe in Figure 7 that L-SRA performs significantly better than the other two. The communication cost for SRA is generally lower than “Baseline.” Nevertheless, when the value of
As expected, L-SRA performs best and SRA performs better than “Baseline” as shown in Figure 8. Besides, we further observe that the communication cost of both SRA and “Baseline” grows quickly, while that of L-SRA grows slowly as S increases. This is because in most cases the bottleneck degree not only is far less than S but also increases less with the growth of S. Therefore, L-SRA can reduce its communication cost significantly. Take note that when
Next, we examine the end-to-end latency of real packets for different

Communication cost comparison among different protocols.
Figure 10 shows the end-to-end latency with different network scale N for L-SRA, SRA, and “Baseline.” It is observed that the end-to-end latency of them all increases with the increasing of N. This is because the latency which resulted by broadcast (initiated from the source or sink) increases with the growth of

End-to-end latency under different protocols.
8. Conclusion
In order to defend against the global traffic attack, we first propose a sink location protection protocol based on packet sending rate adjustment (SRA). By controlling the packet sending rate of each node dynamically, SRA hides the location of the sink successfully. For further communication cost reduction, we then propose a light weight SRA protocol (L-SRA), which protects the sink location while reducing the communication cost obviously. Future work will focus on sink location protection against the global attacks in mobile sensor networks.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Authors' Contribution
Juan Chen, Zhengkui Lin, Yan Liu, and Ying Hu contributed equally to this work. Xiaojiang Du provided the preliminary idea. Juan Chen improved the idea and finally wrote the paper. Zhengkui Lin gave the theory analysis. Ying Hu and Yan Liu designed and performed the simulation.
Acknowledgments
This research is supported in part by the Natural Science Foundation of China under Grants nos. 61300188, 61301131, 61301132, and 61203082, by Liaoning Province Science and Technology Plan Program no. 2011402003, by National Key Technology R&D Program no. 2012BAF09B01, and by the US National Science Foundation under Grant no. 1065444.