Abstract
Software Defined Network (SDN) architecture has been widely used in various application domains. Aiming at the authentication and security issues of SDN architecture in autonomous decentralized system (ADS) applications, securing the mutual trust among the autonomous controllers, we combine trusted technology and SDN architecture, and we introduce an authentication protocol based on SDN architecture without any trusted third party between trusted domains in autonomous systems. By applying BAN predicate logic and AVISPA security analysis tool of network interaction protocol, we can guarantee protocol security and provide complete safety tests. Our work fills the gap of mutual trust between different trusted domains and provides security foundation for interaction between different trusted domains.
1. Introduction
Autonomous decentralized systems (ADS) have been extended and applied to a variety of domains [1–6]. The main extension in ADS is to implement the dynamic management and to optimize the allocation of virtualized computing, storage, device controllers, and cyber resources. The current major platforms are mature in management and optimization of traditional computing and storage resources. However, the dynamic management and the allocation of ADS devices as cyber resources are a new problem which has not been studied thoroughly. The problem is mainly from network architecture design. The traditional TCP/IP architecture cannot meet the increasing demands, especially the virtualized network and ADS services. Thus, ADS needs new network architecture and techniques with flexibility, robustness, security, and credibility to solve the problem.
In the next generation network architecture design, many experts and scholars have completed a series of remarkable research work. Specifically, OpenFlow [7], introduced by Nick McKeown, gave researchers a way to run experimental protocols in the networks. Based on Software Defined Network (SDN) and OpenFlow protocol, researchers implemented network management and security functions mainly in the aspects of control, traffic forwarding, and load balancing. But the security issue in OpenFlow design should be thoroughly concerned, especially the security interaction function between different controllers' nodes. The problem of security certification issues between the different single controllers limits the interaction range of a SDN architecture, which is only used in a single domain with a single controller, such as the Data Center.
In order to solve secure interaction issues, experts and scholars have completed a series of research work. Reference [7] proposed the SANE network architecture in which logic controllers could provide secure authentication for device access and loading strategy. Moreover, [8] further extended SANE network architecture with data forwarding strategy by using core controller method. The improved architecture implemented with data forwarding function, in a certain extent, could solve the security threats between controller layer and data forwarding layer.
Reference [9] implemented a new network architecture GENI and recognized that a large number of malicious attacks and flood attacks can be easily spread through logic control layers and data forwarding layers and lead to corresponding secure issues, for instance, DDoS attack.
Reference [10] evaluated the weakness of OpenFlow protocol. The author thought OpenFlow had an accurate secure certification method between controllers and switches, but this method did not provide security mechanisms under transport layer.
Based on SDN architecture, [11] did a comprehensive analysis for evaluating NOX, POX, Ryu, and Beacon [12–15] controllers in compatibility, reliability, security, and processing capacity. Focusing on the aspect of security, the authors pointed out that the reason to most controllers' security problems was forged stream message length, protocol version, or wrong type of message flow.
Besides, in [16], the authors analyzed the entire SDN security issues and pointed out that the new network architecture with a rapid response and antithreatening security mechanism was needed to be reestablished, especially in the differences of security threats between controllers and traditional network.
Based on the above issues, one of the key features of ADS is to allow content-based message broadcasting. In order to ensure the real-time system, message package could not be encrypted. The receiver node does not check whether the source address is valid or not, and whether the message package has been tampered or not. It means that an attacker can set up the entire attack in essentially one operation. While the security for ADS is drawing attention, it is an indisputable fact that there is a lack of effective methods to support those frameworks. The contributions of our paper are as follows:
Our paper introduces a new architecture to increase the probability of guaranteeing the credibility for future network architecture by applying the ideas of trusted network to ADS. The new architecture with trusted function modules can measure sensitive information and provide a security interaction function between different SDN domains. Based on the new architecture with trusted function modules, we propose a trusted domain authentication protocol that protects controllers' credibility among entire network architecture when communicating with a nontrusted third party. Trusted function modules, such as Trusted Measurement Module (TMM) and TCG Software Stack (TSS), could provide a set of services to ensure authentication protocol's security, for example, encryption, decryption, digital sign, or key management. The protocol gets trust certifications among different trusted domains and provides secure base in domain session. We demonstrate security of our trusted domain authentication protocol by BAN logic and AVISPA security analysis system and perform a comparative analysis of our trusted domain authentication protocol against some prevalent protocols, namely, IKEv2 [17], IDAKE-MA, and SKAP [18], in performance analysis. We believe that the protocol performance, including calculating consumption and storage consumption, is an index which can give us obviously evidence to prove advantage of our protocol.
This paper is organized as follows. Section 2 introduces a SDN trusted domain network architecture and describes our trusted domain authentication protocol. In Section 3, we demonstrate security of our protocol by the BAN logic [19]. In Section 4, we analyze security of our protocol with different malicious test scenarios by AVISPA security analysis system [20]. Section 5 performs an analysis between our protocol and some authentication protocols.
2. Security Authentication Protocol for ADS Applications
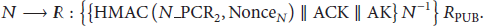
As shown in Figure 1, we propose a SDN trusted domain network architecture which combines SDN and trusted computing. This architecture contains a single controller and a number of network devices. For solving the trust certification problem among trusted domains, we design some modules in SDN controller. TMM, based on TSS [21], is used to measure the sensitive information of SDN controller and connect network devices. Sensitive information includes controller platform hardware information, controller platform OS information, controller software information, and trusted function modules information. Controller Flow Rule (CFR) is trusted policy, including SDN data forwarding strategy and trusted measurement strategy, which was measured by TMM. Controller Communication Module (CCM) ensures controller authentication process between individual trusted domains.
SDN trusted domain network architecture.
In SDN trusted domain network architecture, we propose a domain secure certificated protocol between SDN trusted domains, and, in particular, our protocol can be utilized on nontrusted third party circumstance. From the viewpoint of the trusted chain [22], we can implement a consistency test of measuring information integrity about controller hardware, operating system, controller software, and CCM for trusted negotiation. After finishing trusted negotiation, we can adopt the method of multilevel authentication to guarantee security. More specific, controller authentication can be divided into two parts, controller platform authentication and controller software authentication, which protects the release of sensitive information and prevents unauthorized users from capturing sensitive information. The combination of sensitive information and random numbers, based on the strong protection of sensitive information, ensures that sensitive information is not being hijacked and not subject to replay attacks by unauthorized users, thereby avoiding the security of sensitive information by refusing the connection of those illegal or security risks.
2.1. Protocol Certification Process Overview
Before we design our security certification protocol, we present the three major aspects of our protocol certification process.
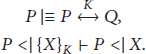
First, in accordance with the trust chain transfer rules in trusted computing, the TMM is based on TSS and will follow the orders by measuring sensitive information of SDN controller hardware, operating system, CCM, and storing measurement results into RTS (Root Trusted Storage) of the PCR register.
Second, the controller platform certification: when implementing different trusted domain controller authentication, authentication requester sends the HMAC calculation results of hardware information, operating system, and random numbers to the receiver, respectively, and expects the identical HMAC result with the receivers. If the controller platform's HMAC result of the receiver is consistent with that of the requester, then we complete the certification process of controller platform.
Finally, the controller software certification: in terms of implementing the trusted authentication of sensitive information in controller software, the requester sends HMAC calculation results, including controller software metrics, core controller module metrics, and random numbers, to the receiver. As shown in the controller platform certification in Figure 1, the receiver will compare the controller software HMAC results with that of the requester. If their results are consistent, we complete the certification of the controller software.
2.2. Specific Certification Process
First, we define the related symbols used in the certification process:
R: authentication requester, N: authentication receiver, AK: session key, ACK: authentication successful symbol,
Figure 2 shows the specific certification process. More details will be introduced in following two subsections.

Trusted domain authentication process.
2.2.1. Controller Platform Certification Process
Controller platform certification process consists of the following steps.
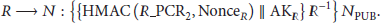
Step 1 (R (the requesting controller) sends an authentication request to N (the receiving controller)).
First, R creates a digital signature for its own controller platform identity information
Step 2 (N receives the authorized information from R).
First, N receives the encrypted message including R's ID and
Step 3 (R receives the authorized information from N).
First, R receives the verification feedback from N, which is encrypted by the public key of R, indicating that there is a trusted negotiation between R and N. Second,
Step 4 (N receives the HMAC sensitive information of the controller platform operating system
PCR2 and key random numbers of R, AKR).
First, N receives
2.2.2. Controller Software Certification Process
In this subsection, we continue to explain the steps in certification process. These steps are related to the controller software certification process.
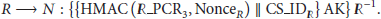
Step 5 (R receives the sensitive information HMAC value from the receiving controller platform operating system).
First, R receives the operating system sensitive information from the receiving controller platform and implements a credible verification, as shown in Step 2, with the operating system measurement result
Step 6 (N receives the controller software verification request from R).
First, N decrypts the information by R's public key, proving the existing base of the trust negotiation between R and N. Then, using the decryption of the sensitive information HMAC value of the controller software, N implements a credible verification as shown in Step 2. If the credible verification passes, N will proceed a negotiated registration using the controller software information
Step 7 (R receives the verification information from N).
First, as shown in Step 6, using the sensitive information HMAC value of the controller software, the receiving controller implements a credible verification as shown in Step 2. Then, if the credible verification passes, R will implement a negotiated registration using the controller software information of N. R encrypts the sensitive information HMAC value of
Step 8.
First, receiving controller software application modules HMAC value of R, N implements a credible verification as shown in Step 2. Then, if the credible verification passes, N will encrypt the sensitive information HMAC value of
3. BAN Logic Security Analysis
According to the BAN logic security analysis, this section analyzes whether our authentication protocol is secure or not.
3.1. BAN Logic Security Analysis
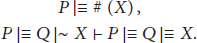
BAN predicate logic is composed of 10 basic syntax and semantic clauses:
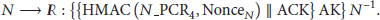
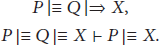
3.2. BAN Logic Inference Rules
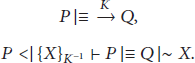
This section describes the four main specific rules of BAN logic to provide a theoretical basis for SDN trusted domains security authentication protocol. ⊢ is primitive symbol, such as
(1) Message Meaning Rule
Theorem 1.
Consider
Explanation. If P believes that Q's public key is K, and P has received the message
(2) Temporary Value Validation Rules
Theorem 2.
Consider
Explanation. If P believes that message X is fresh, and P believes that Q has sent message X, we can infer that P believes that Q believes the message X.
(3) Jurisdiction Rules
Theorem 3.
Consider
Explanation. If P believes that Q has jurisdiction for message X, and P believes that Q believes message X, we can infer that P believes the message X.
(4) Receive Messages Rules
Theorem 4.
Consider
Theorem 5.
Consider
Theorem 6.
Consider
Explanation. The above theorem states that if a subject has received a formula, and the main part knows the relevant secret key, we can infer that the body has received part of the formula.
(5) Belief Rules
Theorem 7.
Consider
Explanation. If P believes that Q has sent a
3.3. SDN Trusted Domain Security Authentication Protocol's Formal Presentation
In this section, we formalize SDN trusted domain security authentication protocol:
3.4. BAN Logic Security Goals
For security requirements of SDN trusted domains security authentication protocol, this paper sets up multiple security goals:
R believes that N is credible to believe ACK.
3.5. BAN Logic Initialization Assumptions
In order to verify the authentication protocol compliance with BAN logic, we make the initialization assumptions of BAN logic:
3.6. BAN Logic Secure Analysis
This section will use the BAN predicate logic inference to verify the authentication protocol's security goals, which is based on the BAN logic initialization assumptions of Section 3.5.
(1) Inference 1: From Step 1
(2) Inference 2: From Step 2
Same as inference 1, we can get the conclusions
(3) Inference 3: From Step 3
From Theorem 3, we can infer
(4) Inference 4: From Step 4
Same as inference 3, we can get the conclusions
(5) Inference 5: From Steps 5 and 6
Same as inference 1, we can get the conclusions
(6) Inference 6: From Step 8
Same as inference 1, we can get the conclusions
From the above BAN predicate logic inference, we can get that the conclusions conform to the BAN logic security goals which are defined in Section 3.4. Obviously, PCR, random numbers, and session key are important to the authentication protocol. From the BAN predicate logic inference, we have proved that sensitive information can meet the demands of network security.
4. Protocol Security Testing
This section will use the Dolev-Yao (DY) attack model [23] for actual security testing. The DY attack model could have the following variety of knowledge:
Attackers are familiar with encryption, decryption, hashing, and other cryptographic operations, and they have the public key and private key of themselves. Attackers hold the network identity and public key of each subject. Attackers have basic password analysis ability.
Attackers could perform a variety of attacks, such as replay attack.
4.1. Security Goals
The DY attack model can control the entire network and catch the data for tampering attack and replay attack. For ensuring the protocol security, the authentication protocol must be detected by DY attack model. To this end, this paper sets up multiple security objections [24] for the DY attack model:
Random number, Controller platform ID/controller software ID is confidential during transmission. Controller software authentication session key is confidential. Successful certification logo (ACK) is completed.
4.1.1. Security Goals Formalization
In response to these security goals, this paper will test the safety of the authentication protocol using AVISPA network analysis tool. For testing protocol security, the AVISPA network interaction protocol security analysis system makes a formalized definition about test method of protocol security goals. Description is shown below.
(1) Information Confidential Test
Secret (E, id, S). This is a statement which means that subject S shares information E, and this secret is named an unchanged id which will be used in the goals definition.
(2) Information Verification Test
Witness (A, B, id, E). This is a weak authentication attribute, which means that A declares that A has sent a message E to B, and this statement is named an unchanged id which will be used in the goals definition.
Request (B, A, id, E). This is a strong authentication attribute, which means that B declares that B has received a message E from A, and this statement is named an unchanged id which will be used in the goals definition.
WRequest (B, A, id, E). This is a weak authentication attribute, which is similar to Request (B, A, id, E), but it does not verify replay attacks.
4.1.2. Modeling and Simulating Security Goals
In this section we will use HLPSL to build security goals modeling, which is based on formal definition of security objectives.
For testing the security goals in Section 4.1.1, the authentication requesting platform needs to verify PCR, random numbers, and platform id of the authentication received platform. The HLPSL code appears as shown in Box 1. Obviously, the authentication receiving platform also needs to verify PCR, random numbers, and platform id of the authentication requesting platform. The HLPSL code appears as shown in Box 2.
Role sdnTNap_Init(A,B : agent, Kab :symmetric_key, H :hash_func, Ap_Start, Ap_Init, Ap_aSuccess : text, SND,RCV: channel(dy) ) played_by A init State :=0 transition ∧request(A,B,b_a_K1ab,K1ab') ∧request(A,B,b_a_SIGKpubKb,SIGKpubKb') ∧secret(K1ab',k1ab,{A,B}) ∧request(A,B,b_a_bNonce,BNonce') ∧request(A,B,bpcr1,H(BPcr1'.BNonce')) ∧request(A,B,bpcr2,H(BPcr2'.BNonce')) ∧request(A,B,bpcr3,H(BPcr3'.BNonce')) ∧request(A,B,bpcr4,H(BPcr4'.BNonce')) end role
Box 1
role sdnTNap_reply(A,B : agent, Kab : symmetric_key, H : hash_func, Ap_Start,Ap_Init,Ap_aSuccess,Ap_bSuccess : text, SND,RCV: channel(dy) ) played_by B init State :=1 transition ∧request(B,A,a_b_SIGKpubKa,SIGKpubKa') ∧request(B,A,a_b_aNonce,ANonce') ∧request(B,A,apcr1,H(APcr1'.ANonce')) ∧request(B,A,apcr2,H(APcr2'.ANonce')) ∧request(B,A,apcr3,H(APcr3'.ANonce')) ∧request(B,A,apcr4,H(APcr4'.ANonce')) 15.State = 15∧RCV(Ap_aSuccess') = |> State':=17∧SND(Ap_bSuccess) end role
Box 2
4.2. Security Test
4.2.1. Test Scenarios
For the security goals, this paper sets up three test scenarios to verify whether the protocol satisfies the security goals or not. As shown in Table 1, in Scenario 1, we implemented a single session with all the roles played by legitimate agents. In Scenario 2 and Scenario 3 we tested the situations, in which the intruder would impersonate each of the legitimate agents: the authentication requesting controller platform (Scenario 2) and the authentication receiving controller platform (Scenario 3).
Scenario description of security test.

4.2.2. Test Results
As shown in Boxes 3 and 4, the authentication protocol passed OFMC security test and ATSE security test, and the authentication protocol is not attacked by DY model, so we can conclude that the authentication protocol is secure.
% OFMC % Version of 2006/02/13 SUMMARY SAFE DETAILS BOUNDED_NUMBER_OF_SESSIONS PROTOCOL D:∖…∖NPLAB∖temp∖130476350162500000.if GOAL as_specified BACKEND OFMC COMMENTS STATISTICS parseTime: 0.00s searchTime: 0.04s visitedNodes: 1 nodes depth: 0 plies
TYPED_MODEL PROTOCOL D:∖…∖NPLAB∖temp∖130476352862187500.if GOAL As Specified BACKEND CL-AtSe STATISTICS Analysed : 4 states Reachable : 0 states Translation: 0.14 seconds Computation: 0.00 seconds
From the summary details of Boxes 3 and 4, we can see that our authentication protocol is tested by CL-AtSe model and OFMC system, based on constraint logic, and our protocol was analyzed by 4 states. So, the conclusion of our test is quite convincing.
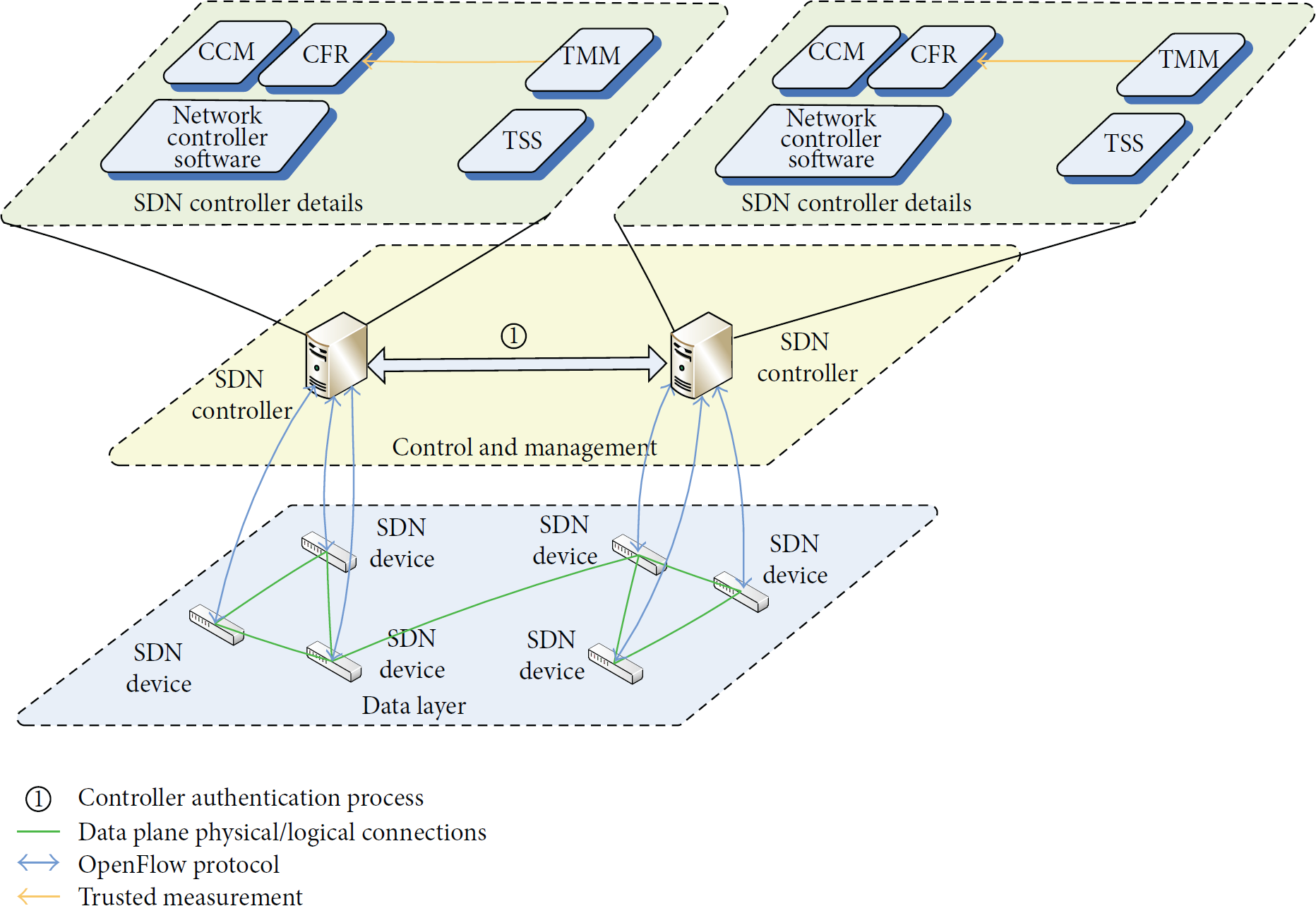
5. Performance Analysis
5.1. Calculation Consumption
This section uses the authentication response time defined in [25] to evaluate the calculation overhead of the protocol. The authentication response time (T) is mainly composed of three parts: the authentication requesting platform computing time (
Thus, we define the authentication requesting platform computing time including operation overhead of HMAC, digital sign, and encryption and decryption.
Similarly, we define the authentication receiving platform computing time including operation overhead of HMAC, digital sign, and encryption and decryption.
In particular, we consider that the ideal transport network excludes the impact of network latency.
According to the above definition, the calculation overhead of authentication protocol is mainly composed of HMAC, digital sign, message encryption and decryption, and the network transmission. As shown in Table 2, we make a detailed comparison between IKEv2, IDAKE-MA [26], and SKAP in this paper.
Comparison in the performance of protocols.
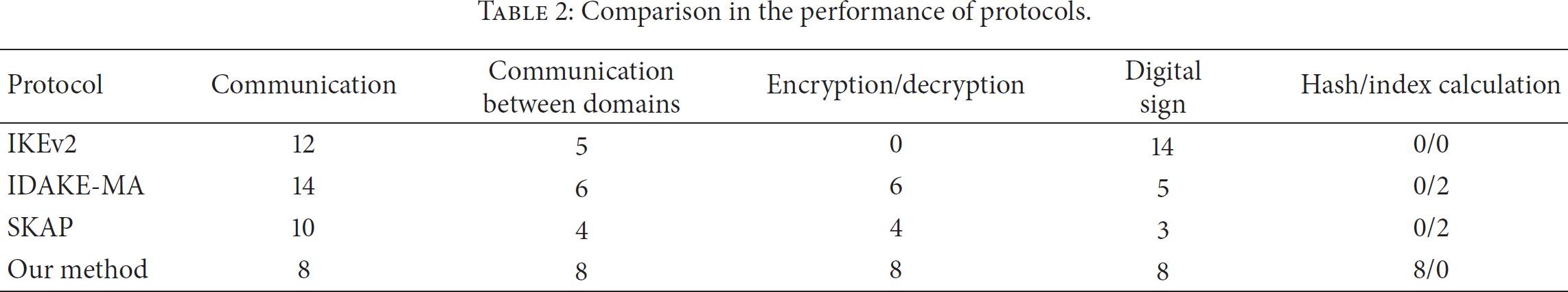
It can be seen in Table 2 that the authentication protocol of this paper has higher calculation consumption compared with other domain protocols. In particular, we propose a no third party certification method. So our approach has advantages in communication frequency, which effectively reduces the total number of communications and network overhead. Furthermore, the authentication protocol is based on trusted computing, which effectively protects the credibility of network domains, and the trusted authentication protocol could make more advantages in security. Last but not the least, the authentication protocol does not have index calculation. Compared with other protocols in Table 2, our approach could significantly improve computational efficiency and reduce the cost of computing.
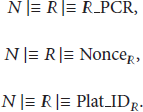
5.2. Storage Consumption
For the authentication protocol of this paper, we assume that the average frequency of the requester connecting to the receiver under random conditions is 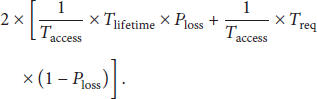
Assuming the time of the latency timer is two times that of the response message time, we can further simplify that the storage average amount of the receiver is
According to the above formula, on the one hand, if
On the other hand, as shown in Figure 3, if

The storage consumption of our method.
So far we assumed that the

The storage consumption of SKAP.

The storage consumption of IDAKE-MA.

The storage consumption of IKEv2.
6. Conclusion
In this paper, we introduced and demonstrated a security authentication protocol of SDN trusted domain in ADS applications and designed the trusted domain network architecture to solve the credential problem of SDN architecture. The trust negotiation concept with nontrusted third party is a prerequisite for communication between different SDN trusted domains in ADS applications.
The main contributions are as follows:
In the paper we considered replay attacks and intermediator attacks. In the future, we plan to consider other attacker behavior models including opportunistic collusion attacks, random attacks, and insidious attacks to further demonstrate superiority of our protocol.
Footnotes
Competing Interests
The authors declare that they have no competing interests.
Acknowledgments
This research was supported by Funding Project for Beijing Key Laboratory of Trusted Computing, National Engineering Laboratory for Critical Technologies of Information Security Classified Protection, Open Research Fund of Beijing Key Laboratory of Trusted Computing, and 2015 Intelligent Manufacturing Special Project: The Comprehensive Standardized Test. The paper is also supported by a Beijing Natural Science Foundation project (no. 4162006).