Abstract
Ciphertext-Policy Attribute-Based Proxy Reencryption (CP-ABPRE) has found many practical applications in the real world, because it extends the traditional Proxy Reencryption (PRE) and allows a semitrusted proxy to transform a ciphertext under an access policy to the one with the same plaintext under another access policy. The existing CP-ABPRE schemes were proven secure only in the selective security model, a limited model, which is an unnatural constraint on the attacker. The scheme proved in this model can only be called selectively secure one. However, from a security perspective, the adaptively secure CP-ABPRE scheme is more desirable. In this paper, an adaptively secure CP-ABPRE scheme is proposed, which is based on Waters’ dual system encryption technology. The proposed scheme is constructed in composite order bilinear groups and proven secure under the complexity assumptions of the subgroup decision problem for 3 primes (3P-SDP). Analyses show that our proposal provides higher computational efficiency compared with the existing schemes.
1. Introduction
With the development of Internet and open distributed networks, the Attribute-Based Encryption (ABE) scheme [1] has drawn great attention of researchers in recent years. Unlike the Public Key Encryption mechanism, ABE scheme takes attributes as the public key and associates the ciphertext and user's secret key with attributes, so that it provides more flexible access control mechanism over encrypted data. This dramatically reduces the cost of network bandwidth and sending node's operation in fine-grained access control of data sharing. Therefore, ABE has a broad prospect in the large-scale distributed applications to support one-to-many communication mode. Traditional ABE has two variants according to the form of access policy: Key-Policy ABE (KP-ABE) and Ciphertext-Policy ABE (CP-ABE) [2]. In a KP-ABE system, ciphertexts are associated with attribute sets and secret keys are associated with access policies. However, CP-ABE is complementary, and the sender could specify access control policy, so, compared with KP-ABE schemes, CP-ABE schemes are more suitable for the realistic scenes.
As the research and application of the ABE go ahead, Proxy Reencryption (PRE) [3] has been introduced into ABE schemes. Considering such a scenario, in the email forwarding, Alice is going on vacation and wishes the others like Bob could still read the message in her encrypted emails. With an Attribute-Based Proxy Reencryption (ABPRE) system, in which a proxy is allowed to transform a ciphertext under a specified access policy into the one under another access policy, she could meet her intentions without giving her secret key to either the mail server or Bob. So ABPRE schemes [4] are needed in most of practical network applications, especially Ciphertext-Policy ABPRE (CP-ABPRE) schemes [5], which have more flexible access control policy than Key-Policy ABPRE (KP-ABPRE) schemes [4]. Generally speaking, an ABPRE scheme has an authority, a sender, a user called a delegator who needs to delegate his/her decryption ability to someone else, a proxy who helps the delegator to generate a reencrypted ciphertext, and some receivers as participants. Recently, due to their widespread use in the realistic scenes, widespread attention was paid to ABPRE schemes by researchers and some excellent ABPRE schemes have been proposed [6–12].
However, most of existing ABPRE schemes [6–12] were proven secure only in the selective security model [13], in which an adversary must firstly choose an attack target before the public parameters are published. This restriction on an attacker was not natural, which causes attackers to behave differently from the way in a real environment. And most of existing schemes [11–15] demanded a number of paring operations, which indeed costs much in the communications. Therefore, motivated by these concerns, an efficient and adaptively secure CP-ABPRE scheme is proposed in our paper. Our scheme overcomes the restriction on an attacker in a selective security model and could be better applied to the open distributed networks. In the meantime, our proposal supports any monotone access formulas and costs less computational overhead compared with the existing schemes.
The rest of this paper is organized as follows. In the next section, we shall briefly review related works in the field of ABE. In Section 3, some preliminaries including complexity assumptions, access structures, and CP-ABPRE model are provided. Then, the concrete CP-ABPRE scheme is given in Section 4. In Section 5, we analyze the correctness and security of our scheme and compare our scheme with existing schemes in terms of access structure, security, and computations efficiency. Finally, the conclusion is drawn in Section 6.
2. Related Works
In 2005, Sahai and Waters [16] proposed a new type of IBE [17] called Fuzzy IBE (FIBE) which regards identities as a set of descriptive attributes. It is often regarded as the first concept of ABE [1, 18]. ABE can be categorized as either KP-ABE or CP-ABE, and the latter is more flexible and more suitable for the realistic scenes [2]. In 2007, Cheung and Newport [19] used AND gates on positive and negative to express attributes in order to achieve their CP-ABE scheme's access policy and proved the security under the DBDH assumption. And then Nishide et al. [20] designed a new CP-ABE scheme with AND gates on multivalue attributes as its access policy. To realize fine-grained access control strategy, Bethencourt et al. [21] used the Access Tree in their scheme. In order to design CP-ABE schemes with flexible strategy under the DBDH assumption, Goyal et al. [22] and Liang et al. [23] adopted Bounded Access Tree, respectively. Later, Ibraim et al. [24] used the general Access Tree to eliminate the boundary constraints in the literature [22, 23]. In 2011, Waters [25] used Linear Secret Sharing Scheme (LSSS) access structure under q-PBDHE assumption to construct a CP-ABE scheme.
However, unfortunately, the security of those CP-ABE schemes that we mentioned above was proven in a weaker security model, called the selective-policy security model which derived from the selective-ID security model for constructing an IBE scheme without the random oracle model [26]. In the selective security model, the adversary must firstly declare which policy he wishes to be challenged on before the public parameters are published. This restriction on the attacker is not natural, which causes attacker to behave differently from the real environment [13]. Considering the restrictions of the selective security model, researchers expected that the ABE scheme should be designed and proven secure under the adaptive security model. So, in order to overcome the drawbacks of the selectively secure ABE schemes, Lewko et al. [13] proposed an adaptively (or fully) secure ABE scheme by using the dual system encryption technique [27] which is a common method for proving an adaptively secure scheme in IBE or ABE. Later, Lewko and Waters [28] provided a new methodology which can transform the selectively secure schemes to adaptively secure ones and presented a CP-ABE scheme that is proven fully secure. In 2014, Garg et al. [29] constructed the first fully secure ABE scheme that can handle access control policies expressible as polynomial-size circuits. Afterwards, some excellent adaptively secure ABE schemes were proposed [3, 30, 31].
Recently, in the field of cryptography, the concept of PRE has been proposed to make data sharing more efficient. Introduced by Mambo and Okamoto [32] and first defined by Blaze et al. [33], PRE can support the delegation of decryption rights, which is never considered in extending the traditional Public Key Encryption (PKE). In PRE, a semitrusted proxy is enabled to transform a ciphertext encrypted under one's public key into a new ciphertext intended for others with the plaintext unchanged. The decryption proxy, however, can learn nothing about the secret key or the plaintext. Due to these characteristics, PRE has many practical applications. For example, Xu et al. [34] built an encrypted cloud email system with PRE, which allows a user to send an encrypted email to multiple receivers, store his encrypted emails in an email server, and review his history. In addition, it can also be used in secure distributed files systems, cloud storage, on-line Electronic Medical Record (EMR), and so on [4, 5, 35–39].
To date, PRE has been extended to adapt different cryptographic systems. The ABPRE is one of the extensions in which a user is able to empower designated users to decrypt reencrypted ciphertext by deploying attributes. In 2008, Guo et al. [40] proposed the first ABPRE scheme and it is also the first KP-ABPRE scheme. In 2009, Liang et al. [6] proposed the first CP-ABPRE scheme, in which the proxy is enabled to transform a given ciphertext under a specified access policy into the one under another access policy. But, unfortunately, only AND gates on positive and negative attributes are supported by their access policy. In 2010, Luo et al. [7] proposed a new CP-ABPRE scheme which supports AND gates on multivalue and negative attributes. Compared with [6], it has a new property named reencryption control which means that the user can decide which ciphertext can be reencrypted later during the encryption process. Later, Seo and Kim [8] presented another CP-ABPRE scheme which only needs a constant number of bilinear pairing operations. So the computation cost and ciphertext length are reduced significantly compared to previous schemes [7, 27]. In 2013, Li [9] presented a new CP-ABPRE scheme in which the ciphertext policy is matrix access policy based on LSSS matrix access structure. In 2014, Chung et al. [10] analyzed these CP-ABPRE schemes [6–8, 33] and made comparisons of them by some criteria. The aforementioned CP-ABPRE schemes, however, are only CPA-secure. To tackle this problem, Liang et al. [11], for the first time, proposed a new single-hop unidirectional CP-ABPRE scheme supporting any monotonic access formulas. Despite being constructed in the random oracle model, it is proved to be CCA-secure. In 2015, Kawai [12] proposed a flexible CP-ABPRE scheme in which the reencryption key generation can be outsourced in Attribute-Based Encryption and proved their scheme is secure in the selective security model.
All these CP-ABPRE schemes mentioned above, unfortunately, were only proven to be selectively secure [13], which is just discussed above. A CP-ABPRE system with selective security, which limits an adversary to choose an attack target before playing a security game, might not scale well in practice as well. This is because a realistic adversary is able to adaptively choose his attack target when attacking a cryptosystem. Therefore, an adaptively secure CP-ABPRE scheme is extremely desirable in most practical network applications. In 2014, Liang et al. [14], for the first time, formalized the notion of adaptive security for CP-ABPRE systems and proposed a new CP-ABPRE scheme, which is proven adaptively secure in the standard model, but their scheme demands a number of paring operations that imply huge computational overheads. In 2015, Backes et al. [15] presented an Inner-Product Proxy Reencryption scheme. Although their scheme can easily be converted into an Attribute-Based Proxy Reencryption scheme, the ciphertext is only associated with AND gates access structure, which does not conform to the flexible access policy. Motivated by these concerns, in this paper, we propose an efficient and adaptively secure CP-ABPRE scheme which supports any monotone access formulas.
Our contributions can be briefly outlined as follows. (1) A new scheme is proposed and it overcomes the restriction on the attacker in a selective security model in the existing schemes [6–9, 11] and is proved to be adaptively secure. (2) Our proposal supports any monotone access formulas including what the AND gate access structure supports. (3) Our scheme costs less computational overhead compared with the corresponding scheme [14]. (4) We try to construct our scheme in composite order groups and use three assumptions to prove its security.
3. Preliminaries
3.1. Composite Order Bilinear Groups
Composite order bilinear groups were introduced by Boneh et al. [41]. First, let G and
Then, let
3.2. Complexity Assumptions
We now present three assumptions of the subgroup decision problem for 3 primes (3P-SDP) [13]. First, we let G and
Assumption 1.
We randomly choose element g as the generator of
Definition 2.
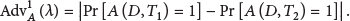
Assumption 1 holds if there is no polynomial time algorithm A which has a nonnegligible advantage
Assumption 3.
We randomly choose elements
Definition 4.
Assumption 3 holds if there is no polynomial time algorithm A which has a nonnegligible advantage
Assumption 5.
We randomly choose elements
Definition 6.
Assumption 5 holds if there is no polynomial time algorithm A which has a nonnegligible advantage
3.3. Access Structures
In this paper, the role of the participants is taken by the attributes. As shown in [42], any monotone access structure can be represented by a Linear Secret Sharing Scheme.
Definition 7 (Linear Secret Sharing Schemes (LSSS)).
Let Π denote a secret sharing scheme over a participant collection P. One says that Π is called linear over the shares distributed for each participant can form a vector over for Π there always exists a share-generating matrix M, which has l rows and n columns. Now, function ρ is defined and used to each party. That is, the party labeling row i can be denoted as
The linear reconstruction property can be defined as follows. Suppose that Π is an LSSS for access structure A. Let
3.4. CP-ABPRE
3.4.1. Algorithm Model
Generally speaking, a CP-ABPRE scheme is composed of 6 fundamental algorithms and it has an authority, a sender, a user that we call a delegator who needs to delegate his/her decryption ability to someone else, a proxy who helps the delegator to generate a reencrypted ciphertext, and some receivers as participants. The 6 algorithms are shown as follows.
3.4.2. Security Model
The adaptive security definition for a CP-ABPRE scheme is described by a security game between a challenger B and an adversary A, which is shown as follows.
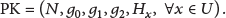
Setup. B runs the Setup algorithm to create a new system and then sends A the public key PK.
Phase 1. A makes the following queries.
(i) Secret Key Extract Queries. B runs the KeyGen algorithm after A submitting sets of attribute
(ii) Reencryption Key Extract Queries. A submits sets of attribute
Challenge. A chooses two messages
Phase 2. Phase 1 is repeated. Note that there is a restriction that no sets of attributes
Guess. A outputs a guess result
In the above game, the advantage of A is defined as
Definition 8.
A Ciphertext-Policy Attribute-Based Proxy Reencryption scheme is adaptively secure (or fully secure) if the advantage of any polynomial time adversary is negligible in above game.
3.4.3. Master Secret Security
Master secret security is an important property for unidirectional PRE defined by Ateniese et al. [43]. Roughly speaking, even if the dishonest proxy colludes with the receiver who can decrypt the reencrypted ciphertext, it is still impossible for them to get any information on delegator's secret key and the plaintext [44].
Definition 9.
The master secret security of a CP-ABPRE scheme can be defined based on the following master secret security game.
Setup. The challenger B runs the Setup algorithm to create a new system and then sends the adversary A the public key (PK).
Queries. A makes the following queries.
(i)
(ii)
Output. A outputs the secret key
In the above game, the advantage of A is defined as
Lemma 10.
For a CP-ABPRE scheme, the plaintext security implies the master secret security. That is to say, for a CP-ABPRE scheme, if there is an adversary A who can break its master secret security defined above, then there also exists an adversary
In Section 5, we will prove that there is no polynomial time adversary who can break the CP-ABPRE scheme with a nonnegligible advantage. So Lemma 10 is obvious.
4. The Proposed CP-ABPRE Scheme
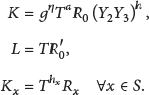
In this section, we shall introduce our adaptively secure CP-ABPRE scheme. Before this, in order to facilitate understanding, notations used throughout the paper are summarized in Notations.
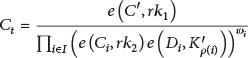
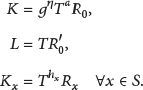
Our adaptively secure CP-ABPRE scheme is constructed in composite order linear groups of order
(1)
(2)
(3)
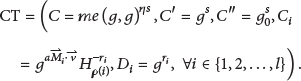
The ciphertext is generated as
(4)
(5)
(6)
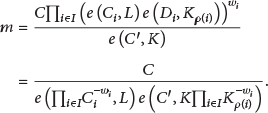
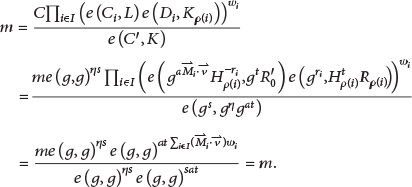
The message m can be recovered as
(7) Decrypt Then compute the message m by
5. Analyses and Proof
5.1. Correctness Analyses
The correctness of the scheme is based on the bilinear character of pairing
Then, the correctness of the decryption algorithm for the reencrypted ciphertext is shown as follows:
Both the original ciphertext decryption and the reencrypted ciphertext decryption processes in Section 4 are correct because the message m can be recovered correctly. Hence, our CP-ABPRE scheme is also correct.
5.2. Security Proof
Dual system encryption [27] is considered as a common and powerful tool to transform a selectively secure scheme into an adaptively secure one [13, 45, 46]. In a dual system encryption scheme, both keys and ciphertexts have two forms: normal and semifunctional [13]. A normal key can be used to decrypt normal or semifunctional ciphertexts, while a semifunctional key can only be used to decrypt normal ciphertexts. Notably, the semifunctional keys and ciphertexts are only used in security proof. To prove the security of our CP-ABPRE scheme, we firstly define the semifunctional keys and ciphertexts as follows.
Let
Semifunctional Ciphertexts. We firstly use the Enc algorithm to generate normal ciphertext and choose element
Semifunctional Key. We use KeyGen algorithm to generate normal secret key. And then we choose random exponents
A semifunctional key of type 1 is
A semifunctional key of type 2 (in type 1
We should note that there will be an extra factor
Our proof of security relies on Assumptions 1, 3, and 5 defined in Section 3. The security proof is obtained via a hybrid argument over a sequence of games defined bellow. Let Q be the maximum number of key queries that the adversary makes, and a series of games are defined as follows,
In the latter part of this section, we will prove that the above games are indistinguishable under the composite assumption.
Lemma 11.
Assume that there is a polynomial time adversary A such that
Proof.
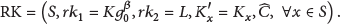
We establish a polynomial time algorithm B which receives
Setup. B chooses random exponents
Phase 1. B responds to whatever A's key requests by using the KeyGen algorithm to make normal keys, since it has the MSK.
Challenge. A provides two messages
Phase 2. Repeat Phase 1.
Guess. A outputs its guess result
If
Hence, if A can distinguish
Lemma 12.
Assume that there is a polynomial time adversary A such that
Proof.
B receives
Setup. B chooses random exponents
Phase 1. This phase can be divided into three parts. To form the first To generate the normal keys of queries greater than k, B needs to run the KeyGen algorithm since it has the master secret key (MSK). To answer the kth query, set
If
Challenge. A provides two messages
Actually, if the kth key can be used to decrypt the challenge ciphertext, then
For
Thus, if
Hence, if the adversary A has a nonnegligible advantage ε to distinguish
Lemma 13.
Suppose that there is a polynomial time adversary A such that
Proof.
B receives
Phase 1. The first (
Phase 2. Phase 1 is repeated.
Hence, if
Lemma 14.
Assume that there is a polynomial time adversary A such that
Proof.
The proof is similar to those of Lemmas 11–13. B receives
Setup. B chooses random values
Phase 1. To form semifunctional keys of type 2, B responds to each A's key query by randomly choosing elements
Challenge. A submits two messages
Phase 2. Repeat Phase 1.
Guess. A outputs its guess result
If
Hence, if A can distinguish
Theorem 15.
If Assumptions 1, 3, and 5 hold, our CP-ABPRE scheme is adaptively secure.
Proof.
If Assumptions 1, 3, and 5 hold, we have proved that the real CP-ABPRE security game
5.3. Analyses and Discussions
5.3.1. Security Analysis
The reencryption control, which allows the encryptor to decide whether the ciphertext can be reencrypted, was first put forward by Luo et al. in [7]. In our CP-ABPRE scheme, we can see that the element
5.3.2. Performance Analyses
In this part, we will make some comparisons of different CP-ABPRE schemes, and the results are summarized in Tables 1–3. A comparison of access expression and some properties is given in Table 1. In addition, we shall compare the performance and efficiency of our proposal with the existing ones in Tables 2 and 3. We use
Property comparisons.

DBDH: Decisional Bilinear Diffie-Hellman, CTDH: Complex Triple Diffie-Hellman, ADBDH: Augment Decisional Bilinear Diffie-Hellman, 3P-SDP: subgroup decision problem for 3 primes, and DPBDHE: Decisional q-Parallel Bilinear Diffie-Hellman Exponent.
Performance comparisons (I).

Performance comparisons (II).

From Tables 1–3, we can draw the following conclusions. Liang et al. [6], Luo et al. [7], Seo and Kim [8], and Backes et al. [15], respectively, proposed their schemes based on the CP-ABE in which the ciphertext is associated with AND gates access structure. However, the access policy in these four schemes is not flexible enough; it can only support AND operation on attributes. The ciphertext policy realized in Li's [9], Liang et al.'s [11, 14], and our scheme is LSSS matrix access structure which supports any monotonic access formula including what the AND gate access structure supports. Different from Li's [9] and Liang et al.'s [11] schemes, our scheme is adaptively secure. And, what is more, our scheme needs only a constant number of paring operations in Reencryption and Decryption phase when compared with Liang et al.'s scheme [14]. That is, our scheme greatly reduces the computational overhead.
From the above analysis, we can conclude that our scheme is more efficient and secure than previous CP-ABPRE schemes.
6. Conclusions
CP-ABPRE employs the PRE technology in the ABE cryptographic setting and could be applicable to many real world applications, such as email forwarding. The existing CP-ABPRE systems, however, were proven secure only in the selective security model which causes attacker to behave differently from real environment. So an efficient and adaptively secure Attribute-Based Proxy Reencryption scheme is proposed in this paper. By using the dual system encryption, the proposed scheme can be proven to be adaptively secure rather than selectively secure which is much less practical. Meantime, our scheme supports any monotone access formulas including what the AND gate access structure supports. And compared with the existing schemes, our scheme needs only a constant number of paring operations in Reencryption and Decryption phase, which greatly reduces the computational overhead.
Footnotes
Notations
Competing Interests
The authors declare that there are no competing interests regarding the publication of this paper.
Acknowledgments
This work was supported by Natural Science Foundation of China under Grant no. 61103178, Natural Science Basic Research Plan in Shaanxi Province of China under Grants nos. 2015JM6294 and 2016JM6002, and the Fundamental Research Funds for the Central Universities under Grant no. 3102015JSJ0003.