Abstract
How to improve both security and energy efficiency is one of the most prominent issues in wireless sensor networks (WSNs). In this paper, we present a trusted and energy efficient approach for cluster-based WSNs. The approach offers (i) trusted hardware module design; (ii) energy-efficient clustering algorithm; and (iii) network operation. In the cluster-based WSNs, every cluster head is equipped with a designed trusted hardware module (TM) to improve security. Then, for improving the energy efficiency of the network, a trusted hardware based energy efficient clustering (TEEC) algorithm is proposed to select appropriate cluster heads. In the network operation, we use TEEC algorithm to perform clustering and apply TMs to achieve security functions. The analysis shows that our approach does well in resisting the attacks such as data confidentiality attack, data integrity attack, and compromise node attack. In addition, experimental results show that the TEEC algorithm makes more balanced clusters with the variance value of loads around 50% and prolongs the life cycle of the network at least 10% compared to traditional methods.
1. Introduction
Wireless sensor networks (WSNs) have been applied to a variety of applications, such as healthcare, smart home, agriculture, and military. A wireless sensor network is a network system comprised of spatially distributed devices using wireless sensor nodes to collaboratively collect, process, and transmit physical or environmental conditions [1].
Security is very important especially when WSNs are used to collect some sensitive and important information. However, due to dynamic topology and openness of wireless channels, sensor nodes are vulnerable to various attacks such as eavesdropping attack, tamper attack, replay attack, and compromise attack. Most researches in security issue are based on software. But software-based methods [2–18] are easy to be attacked when there are some compromised nodes. To solve this problem, trusted computing [19] has been adopted to detect the attacked nodes in WSNs. The main idea of trusted computing is to establish a trusted root to ensure integrity and security of the system. If a node is compromised, the trusted root of the node is also tampered. So the trusted root can be used to measure the integrity of nodes so that the compromised node can be detected. However, trusted computing based methods [20,21] just adopt the traditional Trusted Platform Modules (TPMs) [22–25] to finish some security functions without designing their own trusted computing modules. Traditional TPMs are mainly applied in computer platform other than wireless sensor networks. TPMs have a complex Trusted Computing Group (TCG) software stack and numerous different password mechanisms, which increase the complexity of computation. Thus, a new trusted computing module with a lighter logical structure and optimized functions should be designed to apply in wireless sensor networks.
At the same time, the sensor nodes have limited energy for computing, storage, and communication. Clustering algorithms can improve energy efficiency because they partition sensor nodes into a number of clusters and enable cluster heads to discard redundant and uncorrelated data [26]. Traditional clustering algorithms [27–32] are energy efficient, but they choose different nodes as the cluster heads in different rounds. However, based on the assumption in [21], in TPM approach the cluster-head should be fixed. Therefore, traditional clustering algorithms are not suitable.
So in this paper, we propose a trusted and energy efficient approach for cluster-based WSNs. We first design a trusted hardware module TM (Trusted Module), which adopts the trusted computing idea. Then, we present a clustering algorithm TEEC (Trusted hardware based Energy Efficient Clustering), which has two steps: initial clustering and final clustering. The contributions of our work are as follows:
This approach adopts the hierarchical network architecture, which solves the scalability problem. The introduction of powerful high-end cluster heads simplifies the management of low-end sensor nodes. The approach also has a trusted hardware based energy efficient clustering algorithm TEEC. Simulation results show that when compared with traditional clustering algorithms, its clusters have more balanced number of nodes because the value of the variance of loads is very small. It also prolongs the life cycle at least 10% compared to traditional algorithms. The network operation in this paper applies our designed TM to do node authentication, key establishment, and data transmission. The analysis shows that our approach guarantees information confidentiality, strong and flexible key establishment and management, nodes authentication, and replay protection and resists node compromise.
The remainder of the paper is structured as follows. Section2 introduces the previous work of other experts and shows the advantages of our proposed approach. Section3 describes the trusted network architecture and energy consumption model. Section4 introduces the proposed trusted and energy efficient approach, which contains the trusted hardware module design, the clustering algorithm, and the network operation. Section5 shows the security analysis and the simulation results. Section6 presents the conclusions.
2. Related Work
Security is one of the most critical challenges in WSNs. Numerous efforts have been dedicated to security techniques, which include software-based security technique and hardware-based security technique [20,21,33,34].
The software-based security technique consists of intrusion detection [2–4], secure routing [5–10], key establishment, and management [11–18]. Coppolino et al. [2] have proposed a special intrusion detection system called IDS (Intrusion Detection System), which detects malicious activities accurately and ultimately make a strong protection. Shashikala and Kavitha [10] have summarized some secure routing solutions, described the basic principles of these cases, and then analyzed their advantages and disadvantages. Castillejo et al. [15] have proposed a trustworthy domain model, which is used to deploy security services. The model can not only accept and control sensor nodes in a domain, but also define different effective security policies. Perrig et al. [16] have proposed a suite of security protocols called SPINS (Security Protocols for Sensor Networks), which has two security building blocks: SNEP (Secure Network Encryption Protocol) and
The hardware-based security technique is a good way to guarantee the security of wireless sensor networks. Yang et al. [21] have introduced a hardware-based trusted computing technology into WSNs and proposed a heterogeneous network architecture. In the architecture, a WSN is partitioned into clusters and each cluster head is equipped with a trusted hardware module. This architecture solves the scalability problem and amortizes the workload of security enforcement, but the method lacks some detailed descriptions about the trusted hardware module design. In addition, the method has not considered adopting efficient clustering algorithms to choose appropriate nodes as cluster heads for improving energy efficiency.
Energy conservation is another important topic in WSNs. Clustering algorithms are the key techniques to improve energy efficiency. Heinzelman et al. [28] have proposed a clustering hierarchy protocol called LEACH (Low-Energy Adaptive Clustering Hierarchy), which selects the cluster heads randomly in each round and balances the load of network. The DEEC (Distributed Energy-Efficient Clustering) protocol [30] selects the cluster heads by a probability, which is based on the ratio between the residual energy and the average energy. Nodes with higher residual energy have more chances to be the cluster heads. Then the energy efficiency of the network is improved. Gupta and Jana [26] have presented a genetic algorithm based clustering approach called GACR (Genetic Algorithm based Clustering and Routing), which is also applied in heterogeneous WSNs. The clustering is based on residual energy of the cluster head and distance from sensor nodes to their corresponding cluster head. These traditional clustering algorithms are energy efficient. However, they are not suitable for the hardware-based WSNs, where the hardware modules are only embedded into the cluster heads. Once the heads are determined, the network will never change its cluster heads in the network life cycle.
3. Preliminaries
In this section, we introduce the trusted WSN architecture and some hypotheses. Then the energy consumption model which is used in our work is described.
3.1. Trusted Network Architecture
We adopt the clustering structure [21] as the network architecture. There is a base station and multiple clusters in a wireless sensor network. The base station has strong data processing and communication capabilities, and it is responsible for monitoring and managing the entire wireless sensor network. The base station needs to communicate with the cluster heads and at the same time act as the gateway to exchange information with external networks.
Each cluster contains a head node and several member nodes. The cluster head node is responsible for managing and controlling its cluster. It collects information from the cluster members and does data aggregation and then transmits the processed data to the base station. In this paper, the cluster head is equipped with a TM, which is introduced in the next section.
Here are some hypotheses about the wireless sensor networks of this paper:
The base station is at the center of the network and has a constant supply of energy. Because the base station needs to finish the complex calculation and data communication, it requires enough supply of energy to guarantee the normal operation of the network. Cluster head nodes are equipped with permanent energy supply. Cluster heads need to do data communication and data aggregation. In addition, the cluster head which is equipped with a TM also requires extra energy to improve network security. The coordinates of all nodes in the network are known and fixed. All cluster member nodes have limited and equal initial energy.
3.2. Energy Consumption Model
Wireless sensor network life cycle depends on the residual energy of each node. So energy plays an important role in the construction and operation of the network. In this paper, all the cluster member nodes have limited energy, which will be consumed when the nodes send or receive data. The first-order radio model [28] is used as the energy consumption model. The amount of energy consumption in transmitting 
Here 
The node consumes the following amount of energy in receiving 
In this paper, network operation is divided into rounds. In each round, the cluster member nodes need to consume energy when communicating with the cluster head nodes. The amount of energy consumption
Network life cycle can be defined as the time until the first node dies or the time until the last node dies or until a desired percentage of nodes die [32]. We use life cycle in terms of round from the beginning of the network operation until any one cluster member node depletes its energy.
4. Trusted and Energy Efficient Approach
In this section, we present a trusted and energy efficient approach for cluster-based WSNs. The structure of the proposed approach is shown in Figure1. First, we design a TM (Trusted Module), which is applied to improve the security of the network. The detailed design of TM is shown in Section4.1. However, TM needs to consume extra energy. So we just choose the cluster heads to install the TMs. Second, we propose a clustering algorithm named TEEC (see Section4.2), which is used to select appropriate nodes as the cluster heads for improving the energy efficiency of the network. Then, we describe the network operation, which shows how the network runs from nodes deployment to nodes death. The network operation contains the following steps: clustering, TM-based CHs authentication, TM-based CMs authentication, and TM-based key establishment, data collection, and transmission. The detailed process of network operation is shown in Steps 1–5 of Section4.3.

Structure of proposed approach.
4.1. Trusted Module Design and Functions
In this section, we first introduce the logical structure design of TM. Then, we apply the TM to authenticate the identity of a CH (cluster head node) and the identity of a CM (cluster member node).
4.1.1. TM Design
Traditional Trusted Platform Modules (TPMs) are not suitable for wireless sensor networks. The reason is mainly manifested in the following aspect. A wireless sensor network has hundreds of nodes. The sensor node needs low cost and simple coprocessor. However, traditional TPMs have a complex TCG software stack and numerous different password mechanisms, which increase the complexity of computation. Aimed at actual characteristics of wireless sensor networks, we design a trusted hardware module named TM, which adopts the trusted computing idea. The module has a specific logical structure, as shown in Figure2.
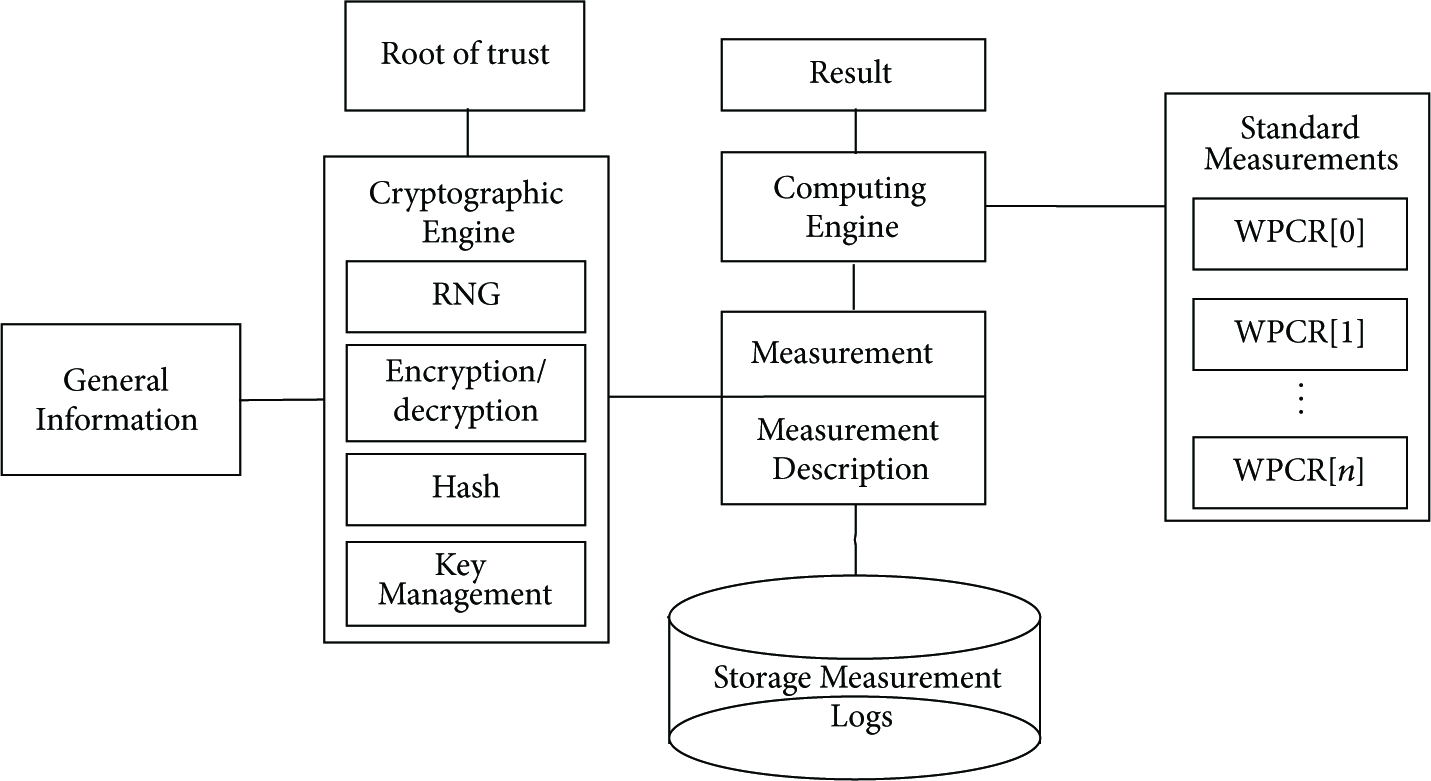
Logical structure design of TM.
The logical structure of TM contains the following components.
4.1.2. TM-Based CH Authentication
We adopt integrity measurement to finish cluster head authentication. Traditional TPMs use platform configuration registers (PCRs) to realize integrity measurement. TPM measures the platform from BIOS program, OS loader, and operating system to applications and records the measurements. Then it determines the security of the system through comparing the calculated PCRs with the standard PCRs. The PCR values are calculated as follows:

Here
In the cluster head authentication part of our method, we only measure the operating system [37] and store cluster head's standard measurement value in 
Here 
The current measurement value is transferred to TM's
4.1.3. TM-Based CM Authentication
We apply the efficient signature in the cluster member authentication part. The signature is described below: let
Step 1.
The node CM generates a random number
Step 2.
Once the message is received from CM, the CH sends this message to its TM's
Step 3.
The TM generates two random numbers r (
Step 4.
The node CM decrypts the received message and gets
Step 5.
The
The authentication flow is shown in Figure3. All the messages need to be encrypted. And

Message flow of cluster member authentication.
After each cluster member authentication, the
4.2. Clustering Algorithm
The wireless sensor network is divided into multiple clusters. Each cluster head is equipped with a TM. Selecting appropriate nodes as cluster heads and making clustering efficiently can prolong network life cycle. We propose a trusted hardware based energy efficient clustering (TEEC) algorithm. The algorithm contains two steps: initial clustering and final clustering.
4.2.1. Initial Clustering
Choosing the nearest nodes from base station as cluster heads is the simplest clustering method. We name this method NEAREST. However, the selected heads are all gathered near base station. Some nodes far from base station will spend a lot of energy when sending messages to cluster heads. Choosing random nodes as cluster heads is another clustering method, which is named RAND.
In this paper, cluster heads have continuous energy supply. The long distance from cluster heads to base station will increase a lot of costs. So we need to select appropriate threshold for this distance

Initial clustering.
4.2.2. Final Clustering
Choosing optimal nodes from initial cluster heads is our target. The selection needs to be on the basis of three aspects. First, the total distance from member nodes to heads is short. Second, cluster heads are decentralized. Third, the number of the member nodes in each cluster is balanced. So we designed the TEEC algorithm, which includes the following steps.
Step 1.
Set the wireless sensor network to be a square which is
Step 2.
Create
Step 3.
The number of all nodes in the network is 
Step 4.
Set the values of all the ordinary nodes' rows to ∞:

Step 5.
Calculate the minimum value in the ordinary nodes columns. The minimum value row represents the nearest initial cluster head
Step 6.
Set the minimum number of each cluster to
Step 7.
The network is divided into
Step 8.
The 
4.3. Network Operation
The network operation shows how the wireless sensor network runs from nodes deployment to nodes death. It uses TEEC algorithm to perform clustering and applies TMs to achieve security functions. During the network operation, time is divided into multiple rounds as shown in Figure5. Each round consists of a set-up phase and a steady-state phase. At the set-up phase, the nodes need to be authenticated and assigned session keys. The steady-state phase has several frames and its time is much longer than the set-up phase. In this phase, the nodes are responsible for collecting and transmitting data.

Network operation.
Before nodes deployment, the BS (base station) has known the geographical location information of each node. The steps of network operation are shown as follows.
Step 1 (
).
Before network deployment, the base station determines the clusters by running the proposed trusted hardware based energy efficient clustering (TEEC) algorithm. Equip each computed cluster head with a trusted hardware module (TM). At the moment, the network goes to the set-up phase of first round.
Step 2 (TM-based CHs authentication).
Each TM verifies the security of its cluster head through the cluster head authentication method (see Section4.1.2). If a TM detects an untrusted cluster head, it will power off its cluster head. Then the trusted cluster heads each broadcast their identity.
Step 3 (TM-based CMs authentication).
If a cluster member node receives the broadcast message from its assigned cluster head, it will send a request to its head and finish CM authentication. Otherwise, it will send a request to its nearest cluster head and do CM authentication. If a cluster head treats a cluster member as an untrusted node, it will remove the cluster member from its cluster. The detailed process of CM authentication is shown in Section4.1.3.
Step 4 (TM-based key establishment).
First round is
Other rounds are
After authentication of CHs and CMs, secret session keys need to be established. The
Step 5 (data collection and transmission).
Consider
Cluster member nodes collect information and send encrypted data to the cluster heads. Each TM's
5. Approach Evaluation
In this section, we first analyze the security of the wireless sensor network using our approach. Then we simulate the proposed TEEC algorithm and compare it with other traditional clustering algorithms about the network life cycle.
5.1. Security Analysis
We assume that an attacker is active from the beginning of the network. The wireless channels can be attacked by many attacks, which include eavesdropping, forging, replying and modifying messages. Further, the adversary can deploy malicious nodes into the network terrain. The malicious nodes can disrupt the network functionality. Besides, the adversary can capture a node and access the secret information in the node. Based on the attacks, we analyze the proposed approach.
Suppose the session key between a member node and its cluster head is
Cluster head authentication adopts integrity measurement through TM. It measures the operating system and stores cluster head's standard measurement value in
5.2. Simulation Results for TEEC
Since we have analyzed the security of our proposed approach, we also need to evaluate its energy efficiency. We simulate the TEEC algorithm and compare it with different clustering algorithms for evaluating its energy efficiency.
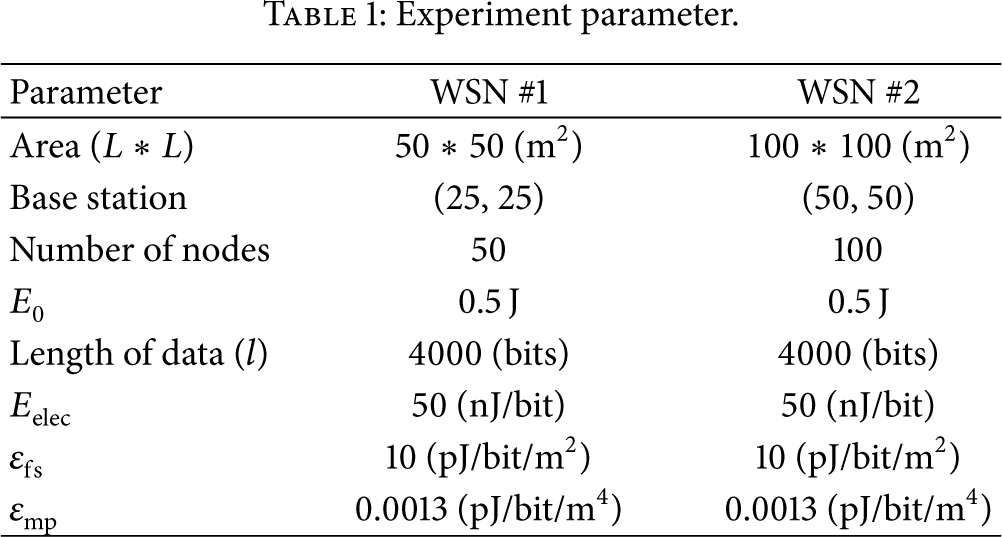
5.2.1. Simulation Settings
We use MATLAB R2014a and C programming language to simulate TEEC with the same parameters (the amount of the driving the electronics' energy consumption
Experiment parameter.
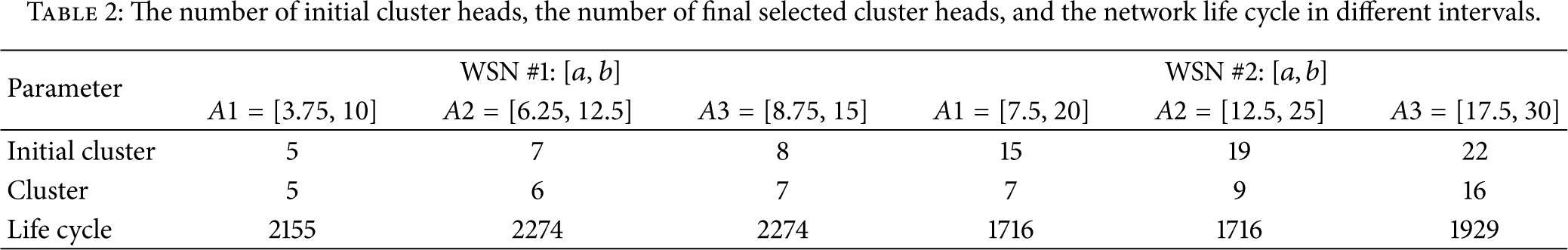
5.2.2. Simulation Results for Different Parameter Intervals of TEEC
In the initial clustering stage of TEEC algorithm, there are two variables: basic distance
The number of initial cluster heads, the number of final selected cluster heads, and the network life cycle in different intervals.
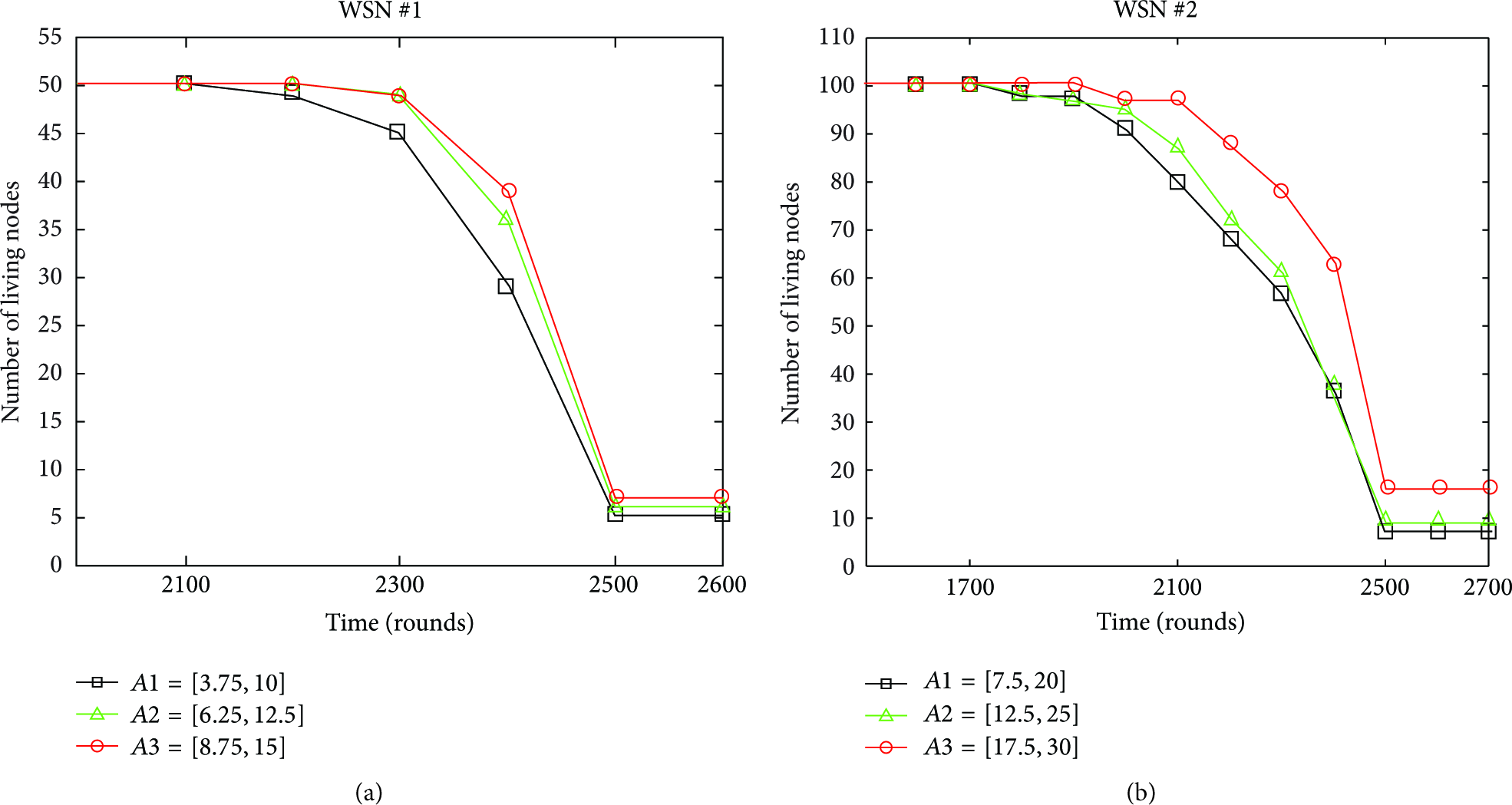
Comparison of the number of living nodes in different intervals.
5.2.3. Simulation Results for Different Trusted Hardware Based Clustering Algorithms
Form Table3 and Figure7, we can find that NEAREST is worst because it has the shortest life cycle and the least number of living nodes before about 2500th round. As for TEEC and RAND, the simulation result of TEEC is better. The detailed reasons are as follows. First, it has longer life cycle than RAND in WSN #1 from Table3 and has more number of living nodes than RAND from about 2100th round to 2500th round in Figure7(a). In WSN #2, although TEEC has slightly shorter life cycle, it always has more number of living nodes from about 1800th round to 2500th round in Figure7(b). Second, TEEC has much less “variance” than RAND in Table3. The “variance” is calculated to measure the balance of load. It is the variance of an array, which contains the number of nodes in each cluster. So TEEC with lower number of “variances” are more balanced than RAND.
The selected interval [
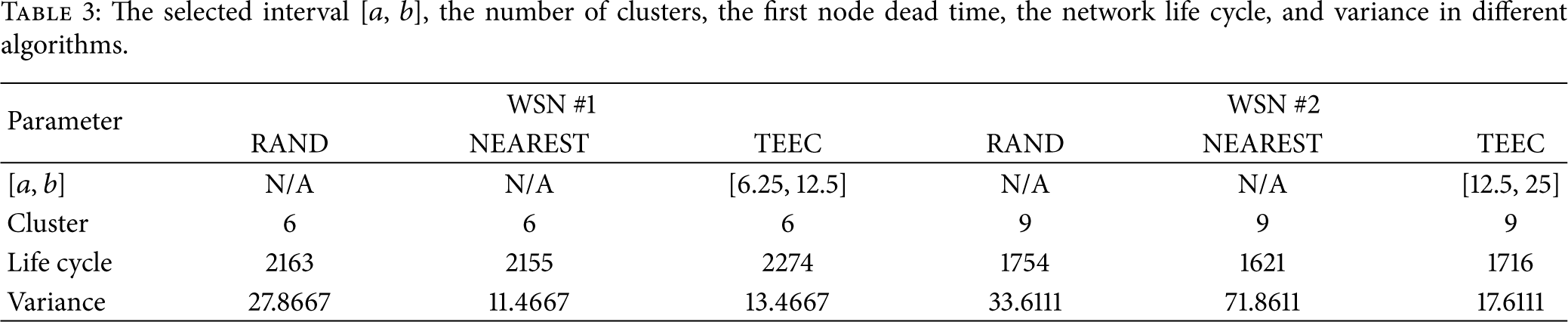

Comparison of the number of living nodes in three different trusted hardware based clustering algorithms.
5.2.4. Simulation Results for Different Clustering Algorithms
The proposed approach uses the clustering network topology and deploys the designed TM in the selected cluster heads. However, both of the TM and security operation need to consume energy. An efficient clustering algorithm can reduce energy consumption and prolong network life cycle. So we design the trusted hardware based energy efficient clustering (TEEC) algorithm when cluster heads are equipped with TMs. In order to validate TEEC algorithm, the experiments compare our proposed TEEC algorithm with the traditional clustering algorithms LEACH, DEEC, and GACR. Table4 and Figure8 illustrate the comparison results. First, as shown in Table4, the life cycle of TEEC is longest. Second, from Figure8, we can find that the number of living nodes of TEEC is always highest before 2400th round. So our proposed algorithm is competitive when compared with others.
The selected interval [
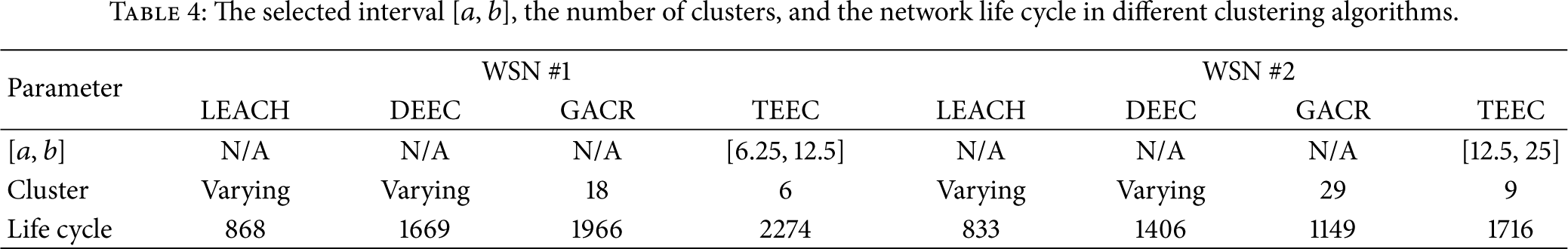

Comparison of the number of living nodes in different clustering algorithms.
5.3. Discussions about Proposed Approach
This paper is our first step to apply a trusted hardware module TM in wireless sensor networks. And we choose the relative small-scale networks as the research object. These kinds of networks have research value for the following reasons: (1) some important applications in the society are suitable to be implemented by small-scale WSNs such as health-monitoring systems or social surveillance. These applications are very vulnerable to security-attacks, for example, forging. Therefore, our TM based approach can assure the reliability of sensor nodes. (2) In large-scale wireless sensor networks, some nodes are too far from the sink node and in most of the applications the environment is extremely harsh. Thus, it is difficult to employ the TMs in the sensor nodes. Even if the TMs are employed in some remote sensor nodes, the security mechanisms need to consume extra energy.
6. Conclusion
The sensor nodes in wireless sensor networks have limited computation, storage, and communication abilities. Traditional security mechanisms are not suitable to protect the network. The proposed approach uses the trusted computing theory and hierarchical topology structure and deploys the designed TMs in the cluster head nodes to improve network security. At the same time, we put forward a trusted hardware based energy efficient clustering (TEEC) algorithm. This algorithm divides the network into several clusters. The nodes do data communication through the clustering structure, thus improving the energy efficiency of the network. Therefore, the proposed approach improves the network security and energy efficiency at the same time.
In our future work, we will extend the trusted hardware module in the large-scale wireless sensor networks. Although it is difficult to employ TM in large-scale networks, where most WSNs are large scale, it is necessary to apply TM in these networks. For this kind of network, the messages sent from member nodes need to be transferred by several cluster heads so that the messages can get to the sink node. However, our proposed approach is not suitable for this situation; we need to propose new clustering routing protocols. If the network is large scale, the cluster heads cannot have sufficient energy supply. In the new clustering routing protocols, the energy of cluster heads also needs to be considered. We plan to employ fuzzy clustering or genetic algorithm to compute the next hop of sensor nodes. And the objective function contains the remaining energy of all sensor nodes and the distance between sensor nodes.
Footnotes
Competing Interests
The authors declare no conflict of interests.
Authors' Contributions
Tianshu Wang conceived and designed the experiments. Xichen Yang performed experiments. Tianshu Wang, Gongxuan Zhang, Xichen Yang, and Ahmadreza Vajdi wrote and reviewed the paper. Tianshu Wang, Gongxuan Zhang, Xichen Yang, and Ahmadreza Vajdi approved the final version of the paper.
Acknowledgments
This paper has been supported by the National Natural Science Foundation funded Project no. 61272420.
