Abstract
Intruders detection is one of the very important applications in Wireless Sensor Networks (WSNs). Sometimes detecting intruders is not sufficient; distinguishing whether an intruder is legal or illegal is necessary. Since k-barrier coverage is widely used in detecting intruders, a barrier construction algorithm is needed, which can not only detect an intruder but also judge an illegal intruder. An intruder is defined as illegal if and only if it crosses straightly through the monitored region from the special side to another side. On the contrary, it is a legal intruder. To detect an intruder and distinguish whether the intruder is legal or illegal, a strong k-barrier coverage algorithm is proposed. The strong k-barrier coverage is a local barrier constructing algorithm and can detect any intruder crossing the k-barrier with a full probability. The strong k-barrier coverage detects all intruders penetrating the annular region for k times. What is more, the proposed strong k-barrier algorithm can provide a reliable judgement on whether an intruder is legal or illegal, and the constructed k-barrier coverage is different from the traditional one-way barrier coverage using binary barriers that are intersected but not overlapped. Some simulation tests show that the proposed algorithm can construct strong k-barrier coverage very well.
1. Introduction
Wireless Sensor Networks (WSNs) have been studied for years, which have many important applications for their particular capabilities in monitoring environment, such as in a battlefield or in an international border; all these circumstances need a comprehensive monitoring. Barriers in WSNs for intruders detection have been studied a lot, which can assure that all intruders crossing a belt annular can be detected. In some applications, only one direction crossing the region is illegal. For example, people can leave a theater without their movie tickets being detected, whereas they are not allowed to see a movie without tickets. In the above applications, it is not appropriate to use the traditional barrier coverage models since they cannot distinguish the legal and illegal intrusion behaviors.
In most previous works, researchers only considered whether or not WSNs can form barrier coverage or whether WSNs provide k-barrier coverage. The theoretical basis of designing barriers of WSNs is studied in [1]. In one barrier coverage, intruders may cross the barrier from the gap without being detected. Since one barrier coverage cannot meet the requirements of intrusion detection in many applications, high degree of coverage must be taken into account, and the reasons of requiring k-barrier rather than 1 barrier are discussed in [1]. A weekly k-barrier coverage has been studied in many literatures, such as [2]. For some applications of WSNs, weekly k-barrier coverage is not enough; thus the strong k-barrier coverage is needed, for example, a WSN with a really high detecting probability. Detecting intruders with highly probability relies on a strong barrier coverage.
In the study of barrier coverage, construction algorithms for barrier have been researched much. Generally speaking, there are two kinds of research directions, local barrier construction and the global barrier construction algorithms. Though global barrier coverage, such as the one in [3], which requires much fewer sensors than full coverage, is a befitting model of coverage for intrusion detection, it also has limitations. Then a local barrier coverage algorithm is studied intensively in [4–7].
Our contributions in this paper are as follows: We find that traditional one-barrier coverage model is not suitable for some applications of WSNs in intruders detection, especially in one-way intruders detection. Comparing the previously binary barriers models, we consider using a k- (more than 2) barrier model to achieve the one-way intruders detection, which does not need to satisfy the conditions in binary barrier model. We propose a k-barrier coverage algorithm, which can easily construct k barriers in monitored areas; then we use the formed k-barrier coverage model to realize the goal of one-way intruders detection without satisfying the limitations of binary barriers coverage.
The remainder of the paper is organized as follows. Section 2 introduces the related work. Then the system model, the barrier construction algorithm, and the barrier mending model are presented in Section 3. Section 4 shows an important application of our model. The simulation results are presented in Section 5. Finally, conclusion of this paper is presented in Section 6.
2. Related Work
The authors in [1] research the mathematical conditions of building a weak barrier coverage in randomly deployment WSNs and devise a centralized algorithm to determine whether a region is k-barrier covered. In literatures [8–11], the authors study barrier coverage intensively. The authors in the literature [12] suppose the situation of one barrier, and they study an energy-efficient border intrusion detection algorithm, with measuring and guaranteeing the coverage quality of WSNs.
In [2], the authors introduce a weak k-barrier coverage problem by at least k sensors in a belt region and propose a simple algorithm to determine whether a belt region is weakly k-barrier covered. The strong barrier coverage of WSNs is introduced in [9], which is a model with a really high probability to detect intruders. The authors in [13] describe the worst- and best-case coverage calculation for homogeneous isotropic of WSNs, in which they combine the Voronoi diagram and graph search algorithm. In literatures [14, 15], the authors present a fundamental geometric data structure of the Voronoi diagram, which present us with a preliminary knowledge of the Voronoi diagram. Sometimes it is not sufficient for weak k-barrier coverage. In the literatures [16–18], the strong barrier coverage has been researched deeply. And the authors propose the minimum and maximum exposure path algorithms, respectively. The minimal exposure path is thought to be the worst-case coverage of WSNs, which is a weak barrier coverage. On the contrary, the maximum exposure is best-case coverage of WSNs.
The authors in [4–7] consider that the sensors cannot locally determine whether the sensor deployment provides global barrier coverage. So the authors present a localized sleep-wake-up algorithm for maximizing the network lifetime. Barriers in the above literatures are all presented in one-dimensional space. In the literatures [19, 20], a k-barrier scheduling for the intruder detection in 2-dimensional space is introduced. The authors propose a distributed scheme whose target is providing low detection delay and low energy. Considering that the detection delay and low energy at the same time are a challenge, it is essential to consider them in multidimensional space. Besides, a new concept of one-way barrier coverage with wireless sensors has been introduced in [21–23], and the authors propose the concept of one-way barrier and establish a necessary condition for WSNs to provide a one-way barrier coverage, which requires that WSNs report illegal intruders but ignore the legal ones. However, the two barriers, which are intersected but not overlapped, are limited in binary barriers.
Motivated by works of the above literatures, we propose to use k-barrier coverage of WSNs to replace the previous binary barriers to achieve the one-way detection while achieving the same goal in the literatures [21–23]. A strong k-barrier coverage algorithm is proposed, which is a local barrier algorithm and can detect any intruders crossing the k-barrier with a full probability, assuring that all intruders penetrating the annular region can be detected k times. Furthermore, the proposed k-barrier model can make a reliable judgement on whether an intruder is legal or illegal, which is different from the traditional one-way barrier coverage. When compared with the algorithm proposed in [24] and another sensor deployment, the number of sensors is much less.
3. System Model
3.1. Network Model
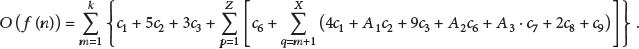
This paper assumes that sensors are deployed in an annular region to detect intruders which try to cross straightly through the monitored region and to report the illegal intruders. An illegal intruder is an intruder crossing through the monitored area from the special side to the other side. If not, it is a legal intruder on opposite moving direction. In this section, we give some basic definitions for the annular region. The annular region is a special case of a belt region whose two left and right boundaries coincide with each other while its two upper and lower boundaries are parallel, as shown in Figure 1. In addition, some definitions about k-barrier coverage are given. In Figure 1, we can see that it is combined with two concentric rings, with the radius of outer ring being

The initial wireless sensor network; sensors are distributed as the Gaussian distribution.
The sensors are deployed following the Gaussian deployment, and the total number of sensors is N. Each sensor has an identical sensing radius
Definition 1 (annular belt region).
A region bounded with two up and down parallel curves and two overlapping right and left boundary curves is called an annular belt region.
Definition 2 (barrier).
A barrier is a sensor group with sensing area overlap to form a belt coverage region starting from the left boundary to the right. There might be more than one barrier in belt region.
Definition 3 (k-barrier coverage).
A circular region is referred to as k-barrier coverage if and only if any intruders crossing through the region can be detected k times by the WSNs.
Definition 4 (traditional 2-barrier coverage model).
It is a model with two barriers whose lower boundary of one barrier and upper boundary of the other barrier overlap.
Definition 5 (global and local barriers).
Global barrier means that sensors can know a global knowledge of WSNs to build a barrier; on the contrary, local barrier is defined as a barrier; the constructing sensors of the barrier only know a local background of WSNs.
Definition 6 (strong barrier coverage and weak barrier coverage).
A weak barrier has at least one gas and a strong barrier has no gap, so that no intruders can cross the monitored area without being detected no matter what crossing paths intruders would choose, but there is at least one safety path that intruders could cross the monitored area without being detected.
Definition 7 (alarm line).
An alarm line is the bottom line (or curve) of the innermost barrier, which will report an alarm when an intruder crosses the alarm line from the other barriers to the inner of region but does not report any alarm whenever an intruder crosses the line from the inner region to the outer region.
Definition 8 (one-way barrier coverage).
A circular region over which sensors are deployed is defined as one-way barrier covered if and only if whenever an intruder crosses the monitored region from the outer ring to the inner ring, and at least one sensor reports an alarm; otherwise, there is not any.
In this paper, we consider a belt region with its two approximate vertical boundaries being overlapped, that is, a circular region in Figure 1. The network model shown in Figure 2 describes the loop dividing, and the monitored area S is divided into k equal concentric loops, which can be expressed as
The loop dividing figure, where the blue lines are the dividing line, and the black lines are the two borders, and k is preset in our opinion, and
3.2. Strong k-Barrier Construction Algorithm
In this section, we propose an algorithm to achieve k-barrier coverage, which needs much less sensors in building barriers. As mentioned the part of network model, the monitored area is a circular area, which is divided into k equal parts. In addition, the way of building every barrier is identical in each part. The construction of one barrier is introduced as follows, such as the innermost circular loop, and others do the same.
There are two steps in the barrier construction algorithm. The first step is to assign some basic information to sensors and let them know the information of their neighbors' locations. Then the other step is to find the remaining sensors used in building a barrier.
3.2.1. Information Assignment
In this step, we divide the S into k equal parts, and, in every part, a barrier is going to be designed, as shown in Figure 2. Since the total number of sensors is N, we suppose that the number of sensors in the innermost ring is n, and the number of other circular rings increases according to the circumference of each ring. Suppose that circumference of the innermost ring is
3.2.2. Barrier Construction Algorithm
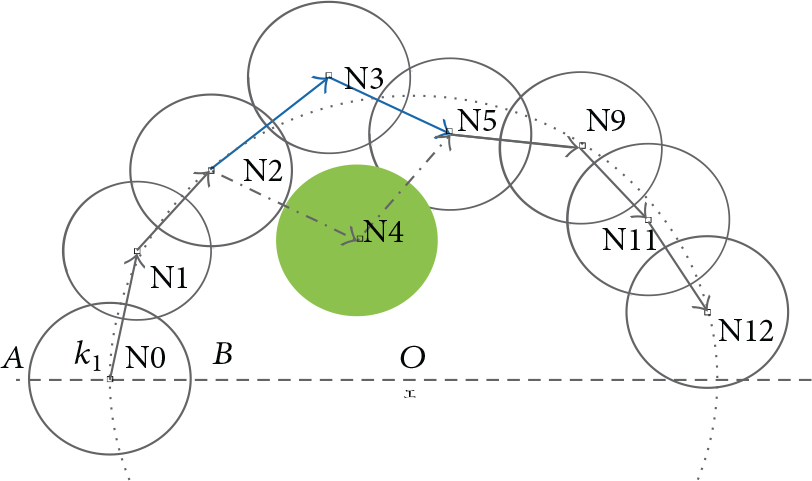
The last step is specific to constructing the barrier. Firstly, we randomly find a starting sensor and search the next satisfying sensor in turn. In order to simplify the operation, we do the search along the clockwise. Equation (6) describes the distance limitation of two adjoining sensors, but it cannot help us find the ideal candidate sensor. Then at least one more condition is really needed, which is the angular restriction. Noting that, we consider the polar coordinates of sensors. The specific expression of a sensor
When finding the next sensor, it is not necessary to search it in global scope because we have to construct k strong barriers, which has no gap between two adjoining sensors. To satisfy the distance limitation, that is, (6), it must be in the polar angle

Graph of the next sensor in the maximum polar angle.
In the triangle
In our k-barrier coverage algorithm, we can calculate the minimal amount of nodes that can be used to create a k-barrier deployment. It is a variable changing with the perimeter of ideal barriers and the sensing radius of sensor nodes. Let us take
The computational complexity of the proposed algorithm is marked as
of sensors deployed following the Gaussian deployment in the radius; discrete number; k = the barrier number.
search the next satisfying sensor, break, fail to find sensor
turn to next step successfully find the next sensor
go back to repeat to find the next valid sensor; the minimal number succeed in building a barrier, break;
go back to step before two steps;
3.3. Barrier Mending Model
3.3.1. Energy Model
After running for a certain time, nodes failure may be an unavoidable problem by running out of energy or by some physical damage. In previous works, most of them consider the remaining energy of an individual sensor, which can be a good way to decide whether a barrier needs to be mended. As one sensor fails, the barrier will be destroyed. In this paper, we consider a strong k-barrier coverage, which should detect all intruders permeating the monitored area almost being detected k times. Once a hole appears in a barrier, intruders may pass through the barrier without being detected. Gap is the crack without any barrier detecting an intruder's incursion.
To maintain the monitoring quality, a barrier mending model is required. We can get the remaining energy (described as
Then we can get relationship between network lifetime and coverage ratio. Assuming that T is the work time of network, we can get the relationship as follows:
Once the remaining energy of a sensor is equal to zero, it means that the sensor is dead. Two neighboring sensors around the sensor in the same barrier can detect its failure. The two neighboring sensors can transmit information to each other. The previous sensor before the dead one in the barrier has to find another sensor to replace the dead one. At the same time, the replacement sensor connecting with the latter sensor of the dead sensor in the barrier mending model must satisfy some requirements. In other words, the new barrier can monitor one line of the field and no intruders can pass through the line without being detected. In other words, the new barrier can monitor one line of the field and no intruder can pass through the line without being detected. There are some limitations needing to be satisfied. The limitations are the Euclidean distance between the dead sensor and the replacement sensor and the distance between the replacement sensor and the latter sensor. These distances all must be shorter than two times the sensing range, whereas the Euclidean distance between the dead sensor and the latter sensor should be shorter than the communication range
An example of barrier reconstruction.
Since the remaining energy of each sensor can be calculated according to (10), there is
The procedure of finding a replacement sensor should satisfy the following rules.
Rule 1.
The previous sensor should select the replacement one among the nearest neighborhoods in its ring, while they are free to use.
Rule 2.
If such a suitable sensor is not found, we can borrow a suitable replacement one to form the other rings.
Rule 3.
If no sensor can be found based on the above two rules, the current barrier cannot be mended; then we release the remaining sensors, which become redundant sensors and are free to help other barriers in case some sensors fail.
3.3.2. A Barrier Health System
The remaining energy of the dying
Suppose that the speed of data transmission is equal, marked as v. Then the time of data transmission between the dying node and its neighbor nodes is
The remaining energy of the dying node is at least
And an actual protocol that can be used to send the alerts to the base station is in reference [6]. In [6], nodes in a cooperative node group will be considered as opponents to each other; therefore, each node will maintain a Q-value which reflects the payoff that would have been received if that node selects one action and the other nodes jointly selected the other action. After that, the node with the highest total payoff will be elected to forward the data packet to the next cooperative node group towards the sink node.
4. Practical Application
This part presents the application of our WSNs in one-way intruders detection. By using the barrier construction algorithm proposed in this paper, a k-barrier coverage can be finally achieved as an ideal situation, as shown in Figure 5. Since the sensors in our network are distributed following the Gaussian distribution when

Application of one-way barrier in detecting different intruders. s1 and s2 are the trajectories of crossing straight through the monitored area and s3 is the trajectories of incompletely crossing line.
Previous works using barriers to provide one-way barrier coverage have been studied a lot. A new coverage model called one-way barrier was firstly proposed in [6]. It proposed the concept of neighboring barriers and designed different protocols to provide one-way barrier coverage for different sensor models based on neighboring barriers. In addition, a one-way barrier coverage has been proposed in [19], and the single intruder has been considered in [19]. But when used to detect multiple intruders, it is not so effective.
In this section, the model is used to detect the illegal and legal intrusion. We also need to set an alarm line like in [6, 7, 19]. But there is little different between the alarm line in this paper and in literatures [6, 7, 19] because the barriers in [6, 7, 19] are two neighboring barriers which have a continuous overlapping region. There are two special barriers. However, in our WSNs, the above limitations are not necessary conditions. This is an improvement we have made. Our detection system is shown in Figure 5. In the monitored area, it has formed k-barrier coverage being described by the black rings with arrows. This situation is the ideal situation and the direction of arrows is the direction of building barriers. In fact, it does not matter how k-barrier coverage is constructed by using our algorithm; k has to be more than two. When k is equal to two, our algorithm is just the neighboring barriers proposed in [6, 7, 19]. That is to say, it is a special situation of our model.
4.1. One Intruder
Obviously, WSNs with only one barrier cannot furnish one-way barrier coverage. As mentioned before, two barriers can provide one-direction barrier coverage, but it must follows some special assumptions, such as the limitations mentioned in literatures [21–23]. This paper concentrates on using k-barrier coverage to achieve the same goal. Here we suppose that there is only one intruder crossing the annual region. As shown in Figure 5, there are three possible paths that one intruder may follow. For example, the three red dotted lines with arrows are some possible invasion paths of the intruders in Figure 5, described as s1, s2, and s3, respectively.
We assume that intruders penetrating straightly through the circular monitored area from outside to inner region are illegal intruders, which need to be detected. In practical situation the circular monitoring area is like an isolation belt, and only the intruders thoroughly penetrating the area from outside to inside need to be broadcast, such as s1. On the contrary, intruders not thoroughly penetrating the monitoring area or penetrating the area from the inside to outside are thought to be legal, like the paths s2 and s3 in Figure 5. In order to distinguish the illegal intruders, we quote the notion of alarm line in literature [6]. And the alarm line in [6] is a little different from to the one in this paper. An alarm line here is a line or curve along the belt with the following property: the network reports an alarm whenever an intruder crosses the alarm line from outside to inside, but it does not report any alarm when an intruder crosses the line from inside to outside. The bottom line of the innermost barrier of WSNs is chosen as the alarm line.
Here we take k-barrier as an example. When an intruder thoroughly penetrates the monitoring area and enters into the protected region, the intruder will be detected k times and will trigger the alarm line. It is illegal that the intruder is detected k times at first and then triggers the alarm line. On the contrary, it is legal. For example, the path s1 in Figure 5 is illegal, and the path s3 is legal, which will not report any alarm. When the alarm is reported, we can easily distinguish the illegal one. Since some intruders are not going to enter the inner region of our monitored area, such as the path s3 shown in Figure 5, an intruder enters into the monitoring area and is detected several times being less than the maximum number of barriers constructed in our model, but does not trigger the alarm line; then the intruder is also thought to be legal. It is obvious to see that our model can effectively detect the illegal intruders, and it does not require two neighboring barriers, and it can be used more widely. Above all, there are some common situations most likely happened in our monitored area.
4.2. Multiple Intruders
When considering more than one intruder at the same time, our k-barrier coverage can provide one-way barrier coverage if the intruders cross straight through the region satisfying some constrains. AS shown in Figures 6(a), 6(b), and 6(c), there are three possible penetrating paths of intruders.

Three kinds of invasion ways.
When intruders cross the circular area along the same direction, such as in Figures 6(a) and 6(b), intruders a and b either penetrate the circular rings from the outer boundary to the inner boundary or from the inner boundary to the outer boundary. In this case, intruders are detected
5. Extended Application
In previous sections, we studied k-barrier coverage of WSNs in a circular area; here we are talking about its extended application used in more generalized environment, for example, with rectangular area. As seen in Figures 7(a) and 7(b), the length is 100 m, and width is 80 m. In Figure 7(a), the rectangular area has been divided into four width parts equally, and sensors are deployed in the middle line of each part following Gaussian deployment (

Extended application in rectangular area.
When sensors are deployed randomly in monitored area, there are risks of sensors being deployed in some place with high density; on the country, some places are with very few sensors. Since the strong k-barriers mean that no intruders can penetrate the monitored area without being detected, no gaps are allowed in barriers. To make sure of building strong k-barriers in WSNs with sensors randomly deployed, we should deploy more than enough sensors in monitored area.
The minimal amount of nodes in each barrier calculated according to formula (10) is
6. Performance Evaluation
6.1. Simulation Methodology
The simulation results are obtained in MATLAB. The objectives of the evaluation are threefold: (1) testing the feasibility and effectiveness of our algorithm in constructing k-barrier coverage; (2) testing our sensor network in detecting whether an intruder is legal or illegal; and (3) studying the performance of our algorithm under different system parameters, such as different sensing radii of sensors, different barrier constructing models, and different sensor distributions.
In the simulations, deploy 640 nodes in an annular region. The distribution of sensors follows the Gaussian distribution and radius of the annual region ranges from 20 m to 100 m. The sensing radii of all sensors are identical. Intruders try to cross the region from one ring to the other ring. Here the annular region is divided into four parts with equal width. Without loss of generality, we assume that the intruders' always move from any of the two edges of the annular region. We study different influence of sensor sensing radius in constructing our barriers. Then we study the impact of system parameters and intruders characteristics. The sensing range is set as 8 m and the communication range is set as 16 m. The number of k is assumed to be 4 in advance. Since the sensors are deployed as the Gaussian deployment, the real value of k may not exactly be 4. The number of sensors in each part of the four annular regions is 64, 128, 192, 256, respectively, which are calculated according to the perimeter of each ring.
6.2. Construction of the WSNs
To test the feasibility and effectiveness of our algorithm, Figure 8 shows the initial Gaussian deployment diagram, and we take

Initial Gaussian deployment of sensors with
Figure 9 shows the simulation results of our algorithm. We take

k-barrier constructing model with
In the innermost circular ring of Figure 9(a), there is an incomplete dotted line, which does not construct a complete barrier, and the incomplete barrier is enlarged in Figure 9(b). It shows that the barrier cannot find a next suitable sensor under our constraints. Such a barrier is not needed, then we will dissolve it. And the sensors in the incomplete barrier can go to sleep until they are waken up.
6.3. Impact of Sensing Radius
To evaluate the impact of sensing radius on the performance of our barrier constructing algorithm, we set the initial numbers of sensors as 56, 104, 152, 208 from the innermost annular ring to the outermost one, and sensors are deployed following the Gaussian deployment in every annular ring. In addition, if we can build one barrier, the number of sensors is enough. The sensing radii of sensors are set to be 8 m and 10 m for each evaluation, respectively. Different sensing radii are shown in Figure 10. In Figure 10, we can see that the larger the sensing radius is, the less the sensors are needed to build a barrier in the same situation. For example, when

Number of sensors constructing k-barrier with
6.4. Comparison with Another Model
As the purpose of our k-barrier coverage in WSNs is to detect intruder invasion, we can compare it with [21], which uses a two-neighbor barrier coverage to detect one-way intruders. We construct such a two-neighbor barrier coverage using our k-barrier coverage algorithm. As shown in Figure 11(a), in Figure 11(b), it is a 2-barrier coverage constructed by our k-barrier coverage algorithm, where

Relevant comparison with our k-barrier coverage.
6.5. Impact of Sensor Distribution
To evaluate the impact of sensor distribution on the performance of our algorithm, we adopt the Gaussian development model in Figure 8 and calculate the number of sensors needed to build a barrier in Figure 9(a). Here we discuss another sensor distribution, which is the Uniform distribution, and compare the sensor number used in building barriers with the Gaussian deployment model. The reason why we choose the Uniform distribution is that it is widely used in past researches. The result is shown in Figures 11(a), 11(b), and 11(c). Figure 12(a) shows the Uniform distribution generated in MATLAB, and we can see that sensors are deployed randomly and with no rules in the monitored region. To compare the influence of sensor distribution with Gaussian distribution, the number of sensors distributed in every single annular region is the same as the number in Figure 8.
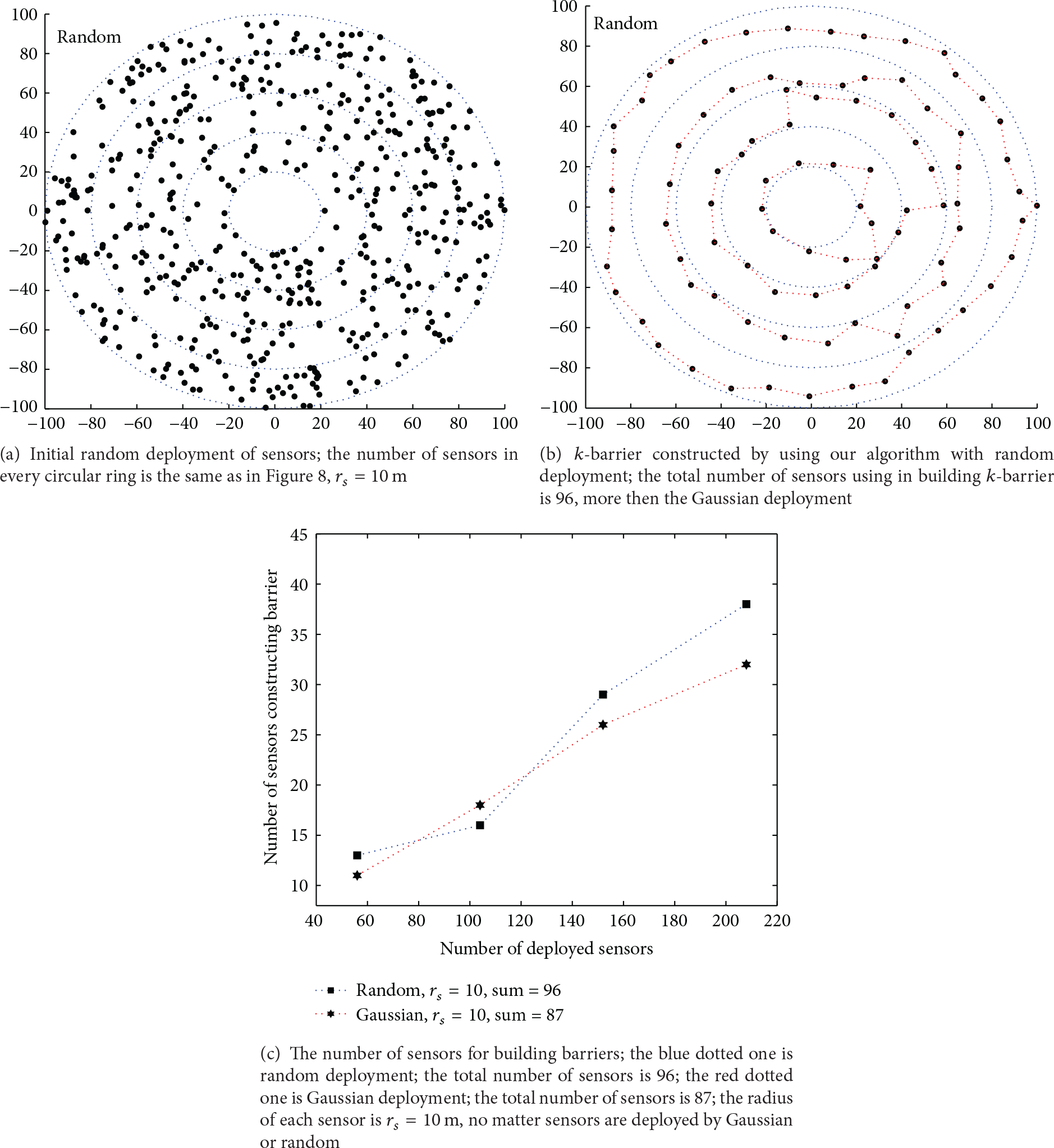
Comparing our sensor distribution with random deployment.
To build the barriers by using the algorithm proposed in our paper, it is obvious that more sensors are required. Figure 12(b) is a simulation result, and there are also four barriers in the annular region. The sensing radius, the range of our annular region, and the simulation times are the same as the previous Figure 9. Comparing Figure 12(b) with Figure 9(b), it is easy to see that it takes more sensors to build barriers. In Figure 12(b), it shows 4 barriers constructed by using sensors with the Uniform distribution. Figure 12(c) shows the contrast figure of the Gaussian distribution and Uniform distribution, which plots the number of sensors in every barrier. In Figure 13, we can see more about the relationship between randomly deployed sensor redundancy and the number of strong k-barrier coverage. Since sensors are deployed following random deployment, it is more hard to construct barriers than Gaussian deployment. In our k-barrier coverage algorithm, we can calculate the minimal amount of nodes that can be used to build a k-barrier deployment according to formula (10).
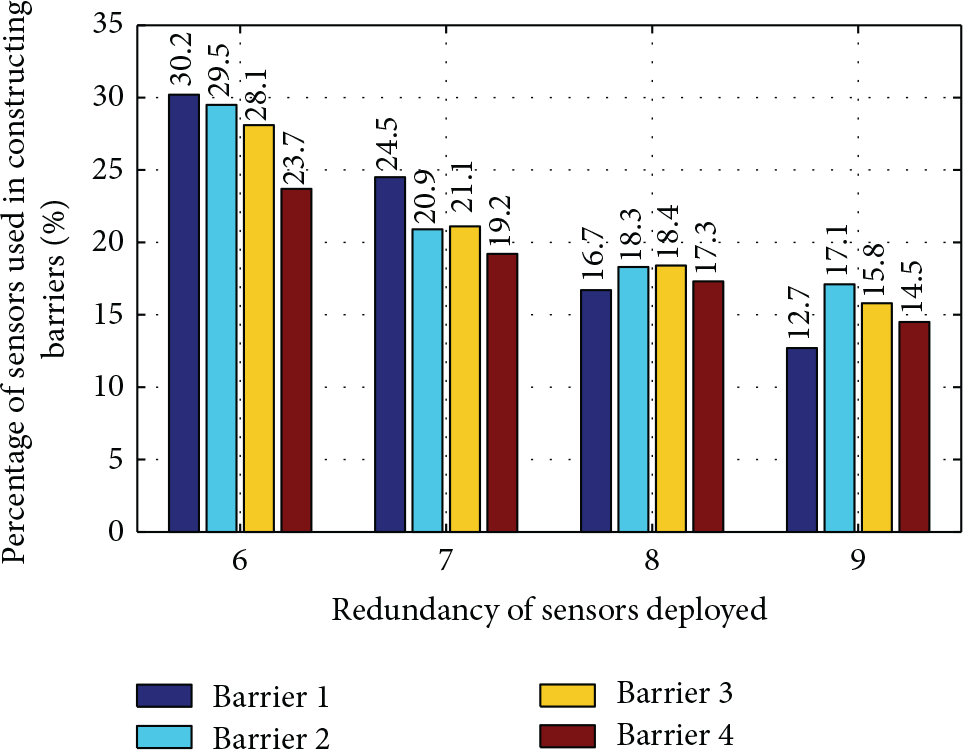
The relationship between the percentage of nodes utilization and nodes redundancy.
The degree of redundancy changes from six times to nine times the minimal amount of sensor nodes in every barrier. As can be seen in Figure 13, the higher the redundancy, the lower the utilization rate of the nodes. It means that the number of sensor nodes used in building barriers is inverse to the nodes redundancy. When the degree is lower than six, it is very difficult to complete k-barrier coverage.
6.6. Impact of Delta Value (i.e., σ)
In this part, we evaluate the impact of parameter σ on the performance of our algorithm. As seen in simulations, σ varies from 1 to 8. The results are shown in Figures 14(a) and 14(b). After 20-time simulations, we note that the number of sensors used in building barriers is related to the delta value σ. When σ is getting bigger, the performance is getting worse. And when σ is big enough, the Gaussian distribution tends to be Uniform distribution. In Figure 14(a), it is shown that there are almost four overlapped lines, and when σ is equal to 1, 2, 3, 4, respectively, the number of sensors used in building barriers is nearly equal. As shown in Figure 14(b), the total number of the sensors used to build the barriers is different. It is shown that when
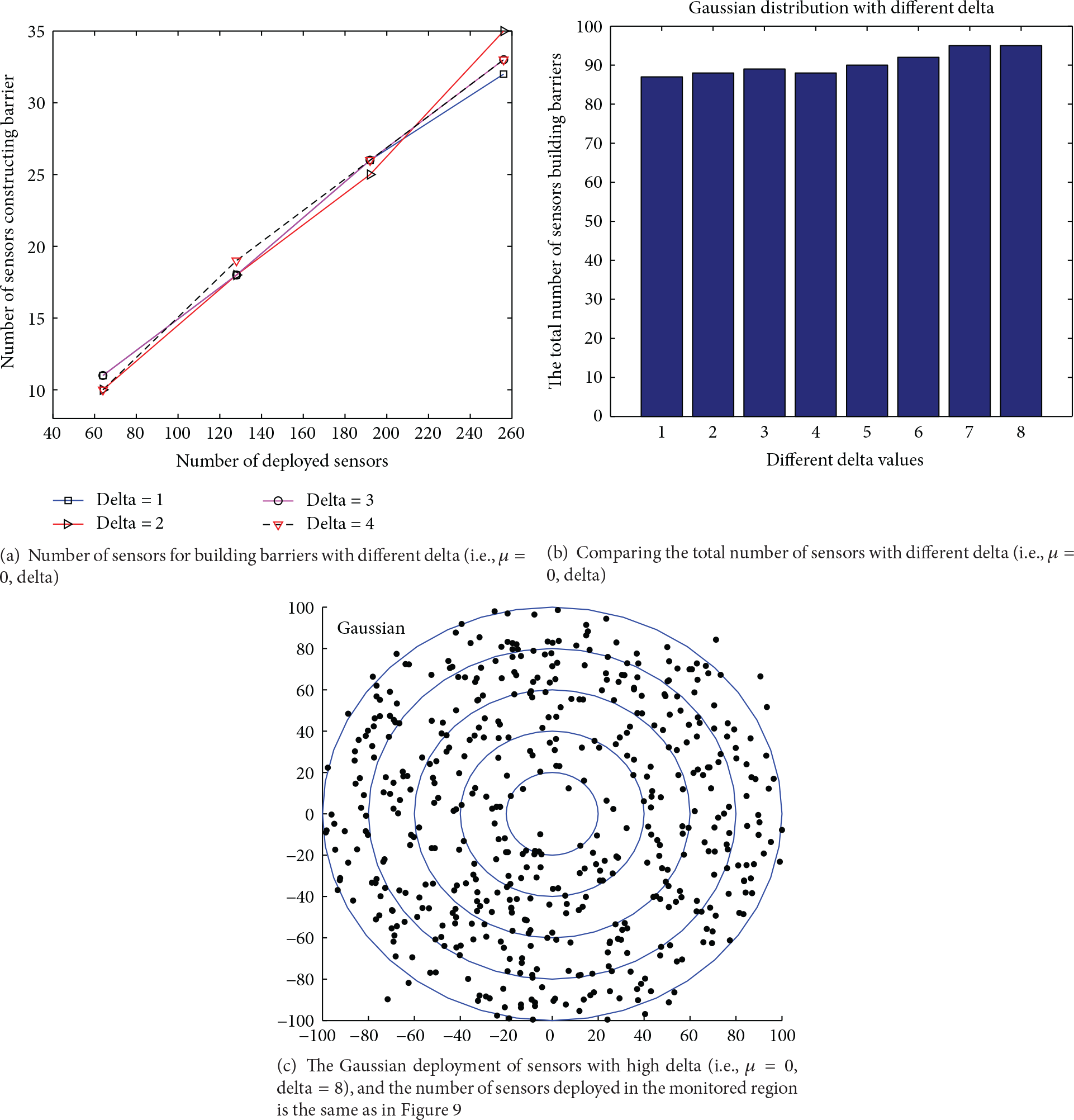
Comparing with different delta (i.e.,
7. Conclusion
In this paper, we propose a barrier constructing algorithm in WSNs for intruder detection, which constructs k-barrier in a circular area, and apply our algorithm in one-way intruders detecting. When an intruder is detected k times at first, and it is broadcasted at last, it is an illegal intruder. On the contrary, if it is broadcasted at first, then it will be detected at least one time; it is a legal intruder. The goal of detecting whether an intruder is legal or illegal is achieved well. On one hand, the simulation results prove that our protocol can build k-barrier very well. On the other hand, the simulation results prove that the total number of sensors used in building k-barrier is small. Therefore the Gaussian distribution with low σ is a good choice.
Footnotes
Competing Interests
The authors declare that they have no competing interests.
Acknowledgments
This work was supported in part by the Program for Science and Technology Innovative Research Team for Young Scholars in Sichuan Province, China (Grant no. 2014TD0006), National Natural Science Foundation of China (Grant no. 61001086), the Fundamental Research Funds for the Central Universities (Grant no. ZYGX2011X004), the Overseas Academic Training Funds, University of Electronic Science and Technology of China (OATF, UESTC) (Grant no. 201506075013), and the Program for Science and Technology Support in Sichuan Province (Grant nos. 2014GZ0100 and 2016GZ0088).