Abstract
We present a decentralized medium access control protocol for cognitive radio wireless sensor networks. The proposed protocol allows secondary wireless sensors nodes to recognize spectrum opportunities and transmits data based on the licensed users’ arrival prediction on the channel. It estimates the number of active cognitive wireless sensor nodes and it also adjusts the sleep cycle in order to conserve energy. The proposed protocol does not need a dedicated common control channel to negotiate for the data channels. We evaluate delay, energy consumption, and goodput, which are the three important qualities of service parameters through simulation. The simulation results show that the proposed approach achieves higher energy conservation with a small cost of delay and adequate aggregated goodput.
1. Introduction
Cognitive radio wireless sensor network (CR-WSN) is a collection of wireless mobile sensor devices called cognitive radio wireless sensors (CRWS) [1]. These sensors have cognition capability with limited broadcast range and resources. A network of these devices collaborates for researches, industrial, and consumer applications such as environmental monitoring, surveillance, agriculture, and wildlife monitoring. When CR-WSNs are deployed in an ad hoc fashion, CRWS nodes may be inactive for long periods and whenever something is detected, they have to be activated immediately. These characteristics of CR-WSNs and applications motivate a medium access control (MAC) protocol that is different from traditional CR-MAC protocols.
The MAC protocols for CR-WSNs are similar to multichannel MAC protocol for wireless sensor networks (WSNs). However, they have two additional and very important responsibilities which are (a) to protect incumbent licensed users (also called primary user (PU)) of the channels from the cognitive users’ interference and (b) to conserve energy. Limited amount of energy in wireless sensor networks has always been a key topic [2]. Most of the existing MAC protocols for cognitive radio networks (CRNs) [3, 4] do not consider energy conservation as their first priority and so they are unsuitable for wireless sensor environment.
Moreover, most of the existing MAC protocols for CRNs [4] and CR-WSNs [1] need an additional global dedicated common control channel (CCC) and this may not be available in some practical cost-sensitive applications. It may saturate as the number of users increases and it is wasteful of channel resource.
Although many articles reported in the literature argue that CCC is required for CR-WSN, they really do not give proper suggestion for how to get the channel. Some argue to use ISM band and others argue to lease, rent, or acquire license band. In reality, both ideas are not quite practical in many CR-WSN scenarios. Allocating a channel only for control packets is waste of resource and against the norm of cognitive radio. Using ISM band for CCC is not suitable in terms of protecting right of PUs.
In this paper, we present a distributed MAC protocol for CR-WSNs. In the proposed protocol, secondary wireless sensor (SWS) nodes divide the time of licensed channels into default slots. The control transceivers of all the SWS nodes are rendezvous in the channel's default time. Each SWS node senses the channel and maintains a channel status table. They rank the channels according to the possible arrival of incumbents on the channel and prepare the preferred channel list. SWS nodes negotiate for the data channels in the default time. After negotiation, they tune their data transceivers in to the selected data channels and start communication. In order to conserve energy, SWS nodes estimate the number of active nodes and they increase or decrease sleep time accordingly. If there is no data to send or receive then the data transceiver goes into the sleep state.
The following presents the main contributions of this paper.
(a) Channel Selection Algorithm. A novel channel selection algorithm is proposed based on exponentially weighted moving average filter model. This model predicts arrivals of incumbent licensed users in a particular channel and selects a channel that is less prone to the claim of the incumbent user.
(b) Energy Conservation. Although every SWS node is equipped with two transceivers, control transceiver of the SWS node enters into the doze state if incumbent licensed user is detected in the channel. It also enters into the doze state according to the density of SWS nodes. Therefore, in the proposed approach, the SWS nodes efficiently conserve energy.
(c) Analysis of the Channel Access Delay. The channel access delay is analyzed and the correctness of the analysis is verified by the simulation.
(d) Incumbent Protection. This paper addresses efficient spectrum utilization and protection of licensed users with little or no tolerable damage. In the proposed approach, several strategies are carried out to protect the rights of the incumbents. Cooperative sensing, that is, nodes that share the sensing information and maintain knowledge of the channels’ status in the entire networks, is used. Further, the proposed protocol takes care of the traditional hidden node problem, exposed node problem, and multiple channels hidden node problem.
We organize the rest of this paper as follows. We review related work in Section 2. We discuss the system model and assumptions in Section 3 and detail the proposed protocol in Section 4. We discuss the simulation results and performance evaluations in Section 5. Finally, we conclude the work in Section 6.
2. Related Work
An efficient MAC protocol design is one of the most challenging issues in CR-WSNs. Although a number of MAC protocols for cognitive radio networks are available in literature, they are not designed specifically for the CR-WSNs. Therefore, there are many areas where the improvements are desirable and possible.
Dynamic channel assignment (DCA) [5] -based MAC protocol [6] employs a default control channel while other channels may be used for data transmission. It assumes that each cognitive radio is equipped with two transceivers out of which one constantly monitors the common channel. This allows it to avoid the multichannel hidden terminal problem. The other transceiver is located on the data channel. RTS/CTS packets are exchanged in the control channel and they are used for negotiating the data channels for the data/acknowledgement (ACK) transmission. Any node that wishes to begin a transmission must ensure that the channel it wants to use is idle. If no channel is available, then a node that wants to transfer packets must wait for an idle channel through the observation of CCC and it must wait for a random back-off time to access the channel again.
Most of the existing MAC protocols for CRNs are based on the global CCC. As we mentioned in Section 1, CCC may get saturated [7] and it can become a victim of DoS attack [8]. Moreover, allocating one channel just for the control packet exchange is a wastage of resource for channels’ constrain (802.11b kind of) networks. To solve the problem due to CCC, a synchronized MAC (SYN-MAC) [9] proposes nondedicated and nonglobal CCC-based MAC protocol for CRNs. This protocol enables the cognitive users to exchange negotiation packets in the data channels such that no CCC is required. In this protocol, time is divided into slots and each slot is dedicated to one channel in order to control message exchange. All cognitive users in a network are synchronized and switch to a channel in the predefined time slots. A node beacons in all its available channels at the beginning of the corresponding time slots. After nodes receive a message, the nodes exchange information regarding their channel sets. After a network is initialized, nodes are synchronized and at the beginning of each slot, the control radio of every node tunes to the respective channel. When a cognitive user wants to send data to the receiver, the cognitive user selects a common channel between them. Then, the cognitive user sends a control message to the receiver at the beginning of the time slot. After the control message exchange, data transfer starts.
Although SYN-MAC does not require CCC, it blindly selects a channel from the available channels set after the network initialization stage. This is not always the best way. Moreover, energy conservation is not considered as a major task.
The proposed approach is similar to SYN-MAC. However, it is different compared to SYN-MAC in many ways. SYN-MAC randomly selects a channel from the available channels set. This may not be efficient because the channel is selected blindly from the available channels sets. This may be more prone to be reclaimed by incumbent licensed users. In the worst case, incumbent licensed users may reclaim the channel just after channel selection. Once incumbent licensed users reclaim the channel, cognitive users have to wait for the next available control slot. Moreover, as energy conservation is not considered in this protocol, it may not be suitable for direct usage in CRWS’ network environment. The sensing in the system level and the incumbents’ protection is also not clearly defined.
Xu and Tan [10] proposed a MAC protocol for single-hop CRNs (MCR-CRN). This protocol divides time into control information window (CIW) and data window (DW). In CIW, nodes sense channel and exchange the status of the channels. After CIA, this protocol works similar to the way 802.11 DCF works. A secondary user informs PUs’ activity to another, but how they know and inform the PUs’ activity in different channel is not clear. It is also not clear how multiple channels are utilized.
Shah and Akan [11] reported the performance of the CSMA-based MAC protocol with CCC for CR-WSNs. In this protocol, the two performance metrics were derived based on the fact that the SUs can exploit the cognitive radio to simultaneously access distinct traffic channels in the common interference region. Gao et al. [12] extended their previous work [13], where they proposed an adaptive modulation technique for CR-WSNs, by allowing each user to choose multiple subcarriers for data transmission. This is a distributed energy efficient spectrum access approach (DEES-MAC) in CR-WSNs. Considering that new users in the network can choose the same subcarriers in the same time slot independently and cochannel interference can occur, this scheme allows multiple new users to share the same subcarriers provided their respective signal-to-interference and noise ratio (SINR) is acceptable.
3. System Model and Assumptions
3.1. Cognitive Radio Wireless Sensor
We consider CRWS devices as intelligent devices with a cognition capacity to observe, orient, plan, learn, decide, and act as mentioned in [1]. These devices can form dynamic spectrum access networks by utilizing the white spaces in the licensed bands. These CRWS are capable of dynamically switching and working in multiple types of frequencies. Each CRWS device is equipped with two half-duplex transceivers. (a) Control transceiver—it is used to control message exchange and snoop neighbors’ activities. (b) Data transceiver—it is meant for data transfer. This transceiver enters into the doze state if there is no data to send or receive.
We consider that there are two noncooperative types of network users—the incumbent licensed users are also called as primary users and SWS are also called as secondary users. The primary users are the incumbent license holders of a frequency band. For communication, SWSs opportunistically use the free spectrum that is not used by the incumbent licensed users.
3.2. Channel
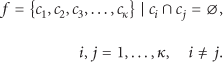
Assume that there are κ nonoverlapping incumbent license channels which are conditionally and opportunistically accessible by the SWS nodes. Here, channel denotes a continuum of frequencies in free space with frequency range that is equal to the maximum and the minimum frequency range which are defined for that channel. We define that the channels are the frequency spectrum (f) divided into mutually exclusive subintervals of equal length.
Set of channels,
3.3. Synchronization
We assume that all the SWS nodes are in the vicinity range and they can listen and decode each other's communication signals clearly. When a SWS node wakes up, it waits for a certain predefined time in a randomly selected channel. If it does not hear of any activity from any SWS node, then it considers itself as the first SWS node in the network. Then, SWS node divides time into κ equal slots of fixed duration, “
Channels with their default timeslots.
The control transceiver of the SWS node hops into all the channels. It senses and sends a beacon into all the channels at the corresponding time slots, if it does not sense incumbent licensed user's signal on the channel. After beaconing, it broadcasts the available channels list to other SWS nodes in the network. The SWS nodes respond sending their available channel set to the broadcasted request. SWS nodes record their own and neighbors’ channel information in the channel status table. If a channel is already occupied by the incumbent licensed user, then the SWS node skips that channel. After sending a beacon in all the channels, SWS nodes know the default slot for the channel and the available channel sets of the neighbor SWS nodes.
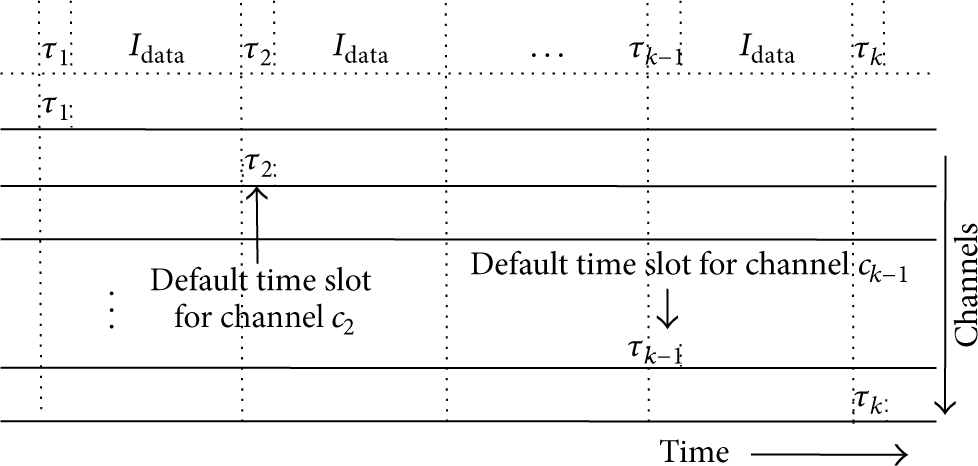
All the SWS nodes in the network tune their control transceiver in the channel's default slot. As in Figure 2, at the beginning of each default slot, SWS nodes compete to send a beacon that carries their local time. This is similar to the timer synchronization function (TSF), in the IEEE 802.11 power saving mode [14]. Following the TSF, a SWS node only updates its time, if the time carried in a received beacon frame is faster than its own local time. When a SWS node receives a beacon frame, it drops its own beacon frame.
Channel negotiation in the default timeslot.
In general, two kinds of solutions can be used for synchronization, in-band solution and out-of-band solution. If the network is large and complex, then global positioning system (GPS) can be used for the synchronization, as an out-of-band solution. If the out-of-band solution is used, then there is no synchronization overhead due to the proposed scheme. There are several solutions in the literature for synchronization [15, 16]. This is a different area of research and so it is out of scope of this paper.
This protocol requires tight time synchronization and does not work if any node fails to synchronize. This is the limitation of this protocol.
3.4. Sensing
The detection or sensing of the incumbent licensed users’ activities on the channel is an important task in CR-WSNs. When the SWS nodes try to access the white spaces opportunistically, they have to ensure that they do not interfere with the incumbent license users’ activities. At the system level, the proposed protocol follows two kinds of sensing as in IEEE 802.22 [17]—(i) fast sensing and (ii) fine sensing.
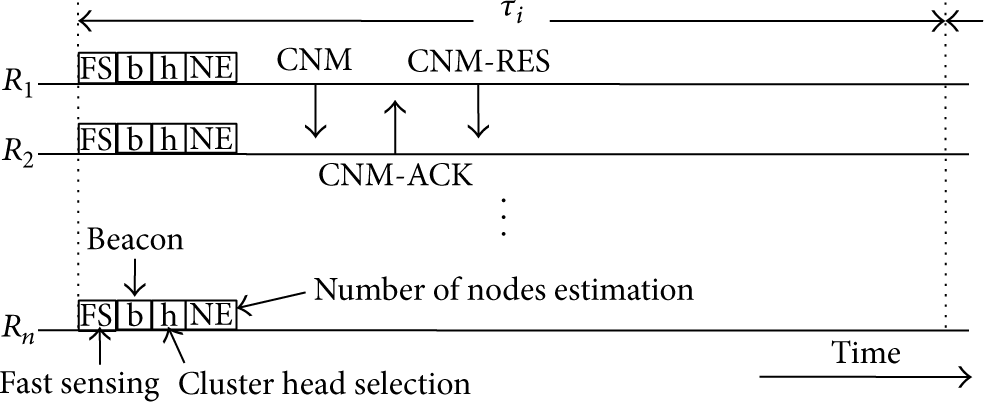
Fast sensing takes very small time. In this, the energy detector computes the energy of the received signal samples and compares it with the predefined threshold level in order to determine the presence or absence of the signal from the incumbents. Fast sensing gives three results: (a) channel is busy; (b) channel is idle, and (c) uncertain. These sensing results are used to decide if the subsequent fine sensing stage is needed. Power consumption is assumed to be the same as that of the idle state as it is a kind of limited sensing. As in Figure 3,

Incumbent licensed user's maximum tolerable time and fast and fine sensing scheduling.
Fast sensing takes very less time and so accuracy is low. Fine sensing is performed to decrease a false alarm and increase the QoS. The duration for this is much larger compared to fast sensing. This is a tradeoff to improve the sensing accuracy at the cost of time. Fine sensing gives two results: (a) channel is busy or (b) channel is idle.
Power consumption for fine sensing is assumed to be equal to that of the receiving state. After the beginning of each
From a logical perspective, the proposed approach uses cooperative sensing to learn network-wide spectral opportunities.
3.5. Channel Status Table
As we mentioned earlier, each SWS node maintains channel status table (CST) by sensing the licensed spectrum and overhearing from the neighbors’ communication. Table 1 is an example of CST. In Table 1, if incumbent licensed user is active in the channel, then it is marked as 1; if the channel is idle then it is marked as 0, and if the SWS node is not sure about the status of the channel then it is marked as 2. How the records on CST are used is described in Section 4.1.
Channel status table.

3.6. Incumbents’ Data Channels Uses Model
We consider that the occupancy of the available data channels follow discrete-time Markov process of two states, that is, ON/OFF. If an incumbent license user is active on the channel then it is the the ON state or the busy state. Therefore, SWS nodes cannot use the timeslot. If the incumbent license user is not active on the channel then it is the OFF state or the idle state and it is available to use by SWS nodes.
4. Protocol Description
In the proposed protocol, the SWS nodes “fast sense” the channels and record the results in the CST. Then, the SWS nodes sort and make a preferred channel list (PCL) of the available channels according to the availability of the channels using exponentially weighted moving average filter as in (2). The same channel can be in different ranks in different SWS nodes as per the geographical location and time. SWS nodes select the highest ranked common channel between the sender and receiver for data communication. Then, the data transceiver of the sender SWS node and the receiver SWS node hop into the negotiated channel and start a data transfer. The detailed channel negotiation, data transfer, and control transceiver sleep cycle are given in the following subsections.
4.1. Channel Negotiation
After gaining the knowledge of the default slot of the channels, all the SWS nodes tune their control transceiver into the channel's default slot. A SWS node that has buffered packets in the outgoing queue waits until the medium becomes idle. After the medium is idle for a DIFS period, the SWS node randomly sets its backoff timer to uniform (
This process is shown in Figure 2. After sensing, if no incumbent licensed user's activity is found then the contention winner SWS node (
We use exponentially weighted moving average filter for incumbent licensed user's arrival prediction in a particular channel. We used exponentially weighted moving average filter model, because this model decreases weight exponentially, unlike other weighted moving average time series models. If the incumbent user occupied the channel in the last time slot, it is more likely to be still there on that channel. This model is more suitable in our approach, because it is always better to select a channel that has no recent history of incumbent user's activity. The lower the value of the predicted status for the next slot (
where
4.2. Data Transfer
After the communication pairs select a common channel for data transfer by examining the incumbent licensed user's arrival probability on the channel for the next
4.3. Control Transceiver's Sleep Cycle
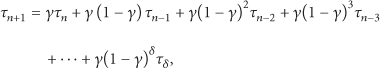
As in Figure 2, the control transceiver of the SWS node does fast sensing at the beginning of the default time. If no incumbent licensed user is detected then, it sends a beacon for synchronization. Then, a SWS node that has residual battery power more than the threshold (σ), waits for a random time and sends a signal. This claims a cluster head to its vicinity for a number of SWS estimation. Other SWS nodes suppress their cluster head-claiming message after they receive the message from the neighbor. After this, SWS nodes estimate the number of active SWS nodes based on the inverse function of probability

where
5. Performance Evaluation
We extended ns-2 [21] for multiradio, multichannel and opportunistic spectrum access environment and simulated the proposed protocol. We evaluated it by analysis and simulation. We simulated the proposed protocol in 4 nodes to 55 nodes scenarios. The SWS nodes are confined in a
We selected DCA-based [6], SYN-MAC [9], MCR-CRN [10], CSMA-based [11], and DEES-MAC [12] protocols to compare with the proposed approach. CSMA-based and DEES-MAC protocols are CCC-based protocols and proposed for CR-WSNs. SYN-MAC and MCR-CRN protocols are non-CCC-based protocols and particularly not designed for CR-WSNs. DCA-based, SYN-MAC, and MCR-CRN protocols are proposed for CRNs. For all the protocols, we assumed that CCC is not free from incumbent licensed users’ intervention. Incumbent licensed users can reclaim any channel any time including CCC. All the simulations were carried out in four channels including control channel scenario. We compared the channel access delay, per packet delay, power consumption, and aggregated goodput with varying number of PUs and SWSs.
Figure 4 shows, per packet delay in different offered loads when the number of active PUs is five, SWS nodes is 16 and four channels scenario. We evaluated CSMA-based, DEES-MAC, MCR-CRN, SYN-MAC, DCA-based MAC and the proposed approaches in a low offered load scenario of 25 packets per second to moderate offered load scenario of 200 packets per second.

Per packet delay in different offered loads when the number of active PUs is five.
In DCA-based protocol, SWS nodes have to negotiate for the data channel before sending each packet. Therefore, DCA-based protocol has moderate delay when offered load is small and highest delay among all the simulated protocols when the offered load is high.
MCR-CRN assumes that once channel is sensed in CIW; the channel is entirely free for the SWS to utilize until SWS nodes sense channel and negotiate again. We found it somewhat difficult to simulate this protocol and compare with the proposed protocol without modification. We modified it as whenever PU appears on the channel, SWS nodes move to another channel according to the predefined hopping sequence and resume their transmission. If the channel is not free in sensing period, then the SWS nodes wait for next beacon interval and sense for the PUs signal and negotiate for the channel.
Simulation results show that MCR-CRN has average delay in low offered load and highest delay, after DCA-based protocol, in moderate offered load. In the proposed approach, SWS nodes have to wait for a cluster head selection and the number of active nodes estimation before the channel negotiation. Therefore, it has a slightly greater delay. However, the differences among most of the approaches are not much in the entire offered load.
Figure 5 shows the average consumed power for different offered loads in 10 SWS nodes scenario. There is a big difference between average consumed power by the DEES-MAC and DCA-based MAC protocols. However, the proposed protocol shows moderate power consumption. Although in the proposed approach SWS nodes are equipped with two transceivers, control transceivers of the SWS nodes enter into the doze state if incumbent licensed user is detected in the channel. Control transceivers also enter into the doze state according to the SWS nodes’ density. Therefore, the SWS nodes efficiently conserve energy.
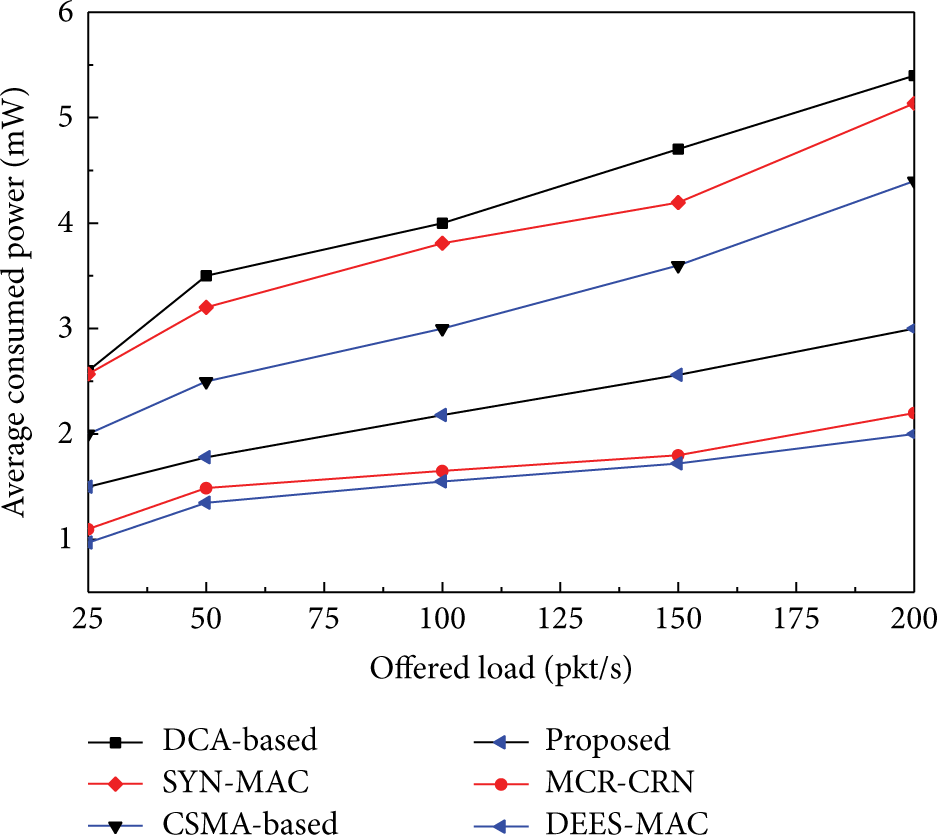
Average consumed power in different offered loads when the number of active PUs is five.
The results show that DCA-based protocol consumes more energy followed by SYN-MAC, CSMA-based, the proposed protocol, MCR-CRN, and DEES-MAC. DEES-MAC consumes least energy because of its power allocation algorithm for each SWS to minimize the energy consumption per bit over all channels in the given scenario.
Figure 6 shows the aggregated goodput of the network in Figure 6(a) 12 SWS nodes and Figure 6(b) 32 SWS nodes scenarios. The proposed protocol has a satisfactory aggregated goodput and it is better than SYN-MAC and DCA-based protocols in all the scenarios.
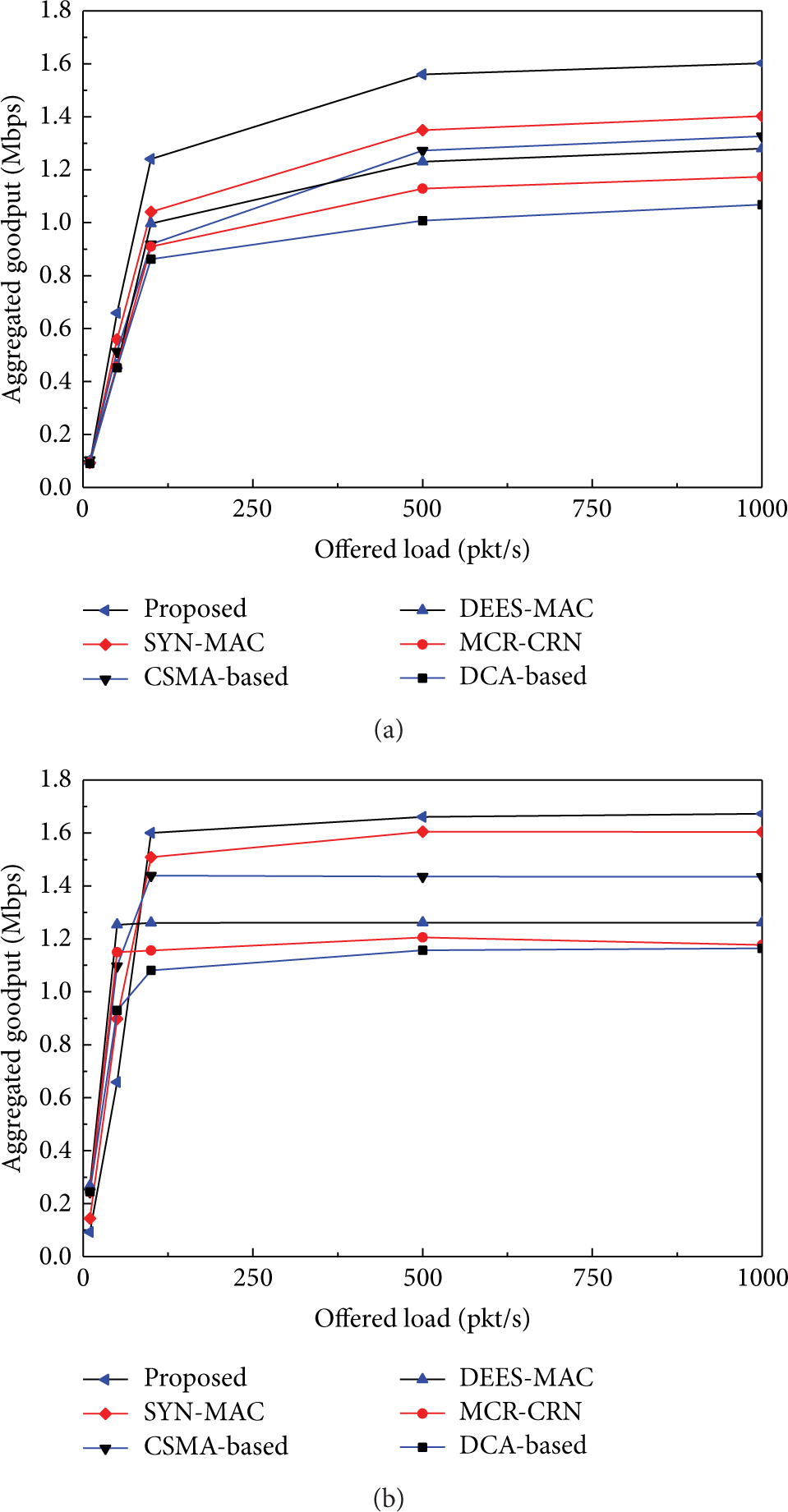
Aggregated goodput in various offered loads when the number of active PUs is five. (a) 12 SWS nodes scenario. (b) 32 SWS nodes scenario.
DCA based protocol achieves better goodput only in a low traffic load. It is because DCA based protocols negotiate for data channels before sending each data packet. Therefore, it suffers from CCC bottleneck problem or early CCC saturation problem in higher offered load and it cannot perform well. In Figure 6(b), when SWS nodes are 32, aggregated goodput of the SYN-MAC is close to the proposed approach when offered load is low, but in higher offered load the proposed protocol outperforms SYN-MAC. The reason is that unlike the proposed protocol in SYN-MAC, SWS nodes select channel randomly without considering the behavior of PUs on the channel; therefore it is more prone to encounter PUs than the proposed protocol.
Figure 7 shows the aggregated goodput in various offered loads when the number of active PUs is 15 and the number of SWS nodes is 12 and 32. When the number of SWS nodes is 12, the proposed protocol achieves higher goodput than any other non-CCC-based protocol and most of CCC-based protocol except CSMA-based protocol in all offered loads.

Aggregated goodput in various offered loads when the number of active PUs is 15. (a) 12 SWS nodes scenario. (b) 32 SWS nodes scenario.
When the number of SWS nodes is 32, the proposed protocol achieves moderately higher goodput in all offered loads. In the proposed protocol, PUs arrive more frequently on the channels when the number of active PUs is large, therefore SWS nodes may need to wait for entire BI. In the worst case it may be several BIs. Therefore, it has moderate aggregated goodput. Nevertheless, the proposed protocol outperforms DCA-based, SYN-MAC, and MCR-CRN. This is due to the channel selection strategies in the proposed protocol, which is less prone to be reclaimed by incumbent licensed users. Frequent channel switching is unnecessary, until incumbent licensed users activities are found on the channel.
Joshi et al. [22] analyzed channel access delay in CR-MAC protocol for ad hoc CR-WSNs without a CCC. The analysis is for the similar CR-MAC protocol. We evaluate the accuracy of the proposed protocol comparing the channel access delay by analysis and simulation results using (17) of [22] as follows:

where

As discussed in Section 1, MAC protocols for CRNs are not suitable for CR-WSNs, but we could not find de facto standard MAC protocol for CR-WSNs to compare with the proposed protocol.
Figure 8 shows an evaluation of the proposed model and simulation results when the number of channel is four, maximum retry limit is three, minimum CW size is 32,

Comparison of the channel access delay by analysis and simulation with varying number of PUs.
Figure 8 shows the delay due to number of PUs while number of active PUs is constant to five. Here the active PUs means PUs having packet to send. For the analysis, collision probability is calculated from the simulation result and shown in Figure 9. The figure shows that the channel access delay increases as the number of PUs increases.

Collision probability when the number of active PUs is 15.
From the results it is clear that when the number of active PU is small, channel access delay is reasonable even if there is no dedicated CCC for control packet exchange. However, when the number of active PU is more, then it is better to use dedicated CCC.
Figure 9 shows the collision probability of the control packets when the number of PUs is fixed to 15 nodes and number of SWS nodes is varied from 5 nodes to 50 nodes. These results are from simulation based on the above parameters.
Above results show that the proposed protocol achieves higher energy conservation with a small cost of delay and adequate aggregated goodput. The results also show that in the densely populated networks, CCC-based protocol performs better; however, in the sparsely populated networks, CCC-less protocols have similar or better performance. As, energy conservation is very important in a wireless sensor network, the proposed protocol's achievement is satisfactory. Further, we considered that in CCC-based MAC protocol, the CCC is not free from PUs’ arrival. Therefore, the goodput in CCC-based MAC protocol is less, but in general, CCC is considered as free from PUs’ intervention.
6. Conclusions
We presented a decentralized MAC protocol for CR-WSNs. In the proposed approach, cooperative sensing is used to learn the network wide spectral opportunities. The incumbent licensed users’ activities observation in a particular channel helps in the selection of the most reliable channel for data transmission. This method predicts incumbent licensed users’ arrival. Hence, it helps in the protection of incumbent licensed users. SWS nodes perform fast and fine sensing in the incumbent's maximum tolerable time. This ensures the incumbents’ right to use the licensed channel without interference from the opportunistic users. By estimating the active SWS nodes, the sleep cycle adjustments can be made to conserve energy.
Although, we did not find promising de facto standard CCC-less MAC protocol for cognitive radio sensor networks to compare with the proposed protocol, we compared the proposed protocol with CCC-based MAC protocols for CR-WSNs, CCC-based protocols for CRNs, and CCC-less protocols for CRNs.
The analysis and simulation results suggest that if the number of active PUs is less, MAC protocol without CCC works fine. However, if the number of PUs is more, then using CCC-based MAC protocol is better. Further, this protocol needs tight time-synchronization and the limitation of this protocol is that it may be not suitable for large scale networks.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This research was supported by Basic Science Research Program through the National Research Foundation of Korea (NRF) funded by the Ministry of Science, ICT & Future Planning (NRF-2012R1A1B4000536).