Abstract
Physical layer security, whose aim is to maximize the secrecy rate of a source while keeping eavesdroppers ignorant of data transmitted, is extremely suitable for Wireless Sensor Networks (WSNs). We therefore, by developing the classical wire-tap channel, construct an approach to compute the secrecy rate between a sensor node and its responsible cluster head in the clustered WSNs. A noncooperative secrecy rate game towards WSNs is formulated to solve contradictions between maximizing the secrecy rate of a sensor node and minimizing power consumed for data transmission. Using evolutionary game theory, we set up a selection dynamics upon which a power level can be adaptively selected by a sensor node. Thus, the objective of secrecy rate adaptation for maximizing the fitness of member sensor nodes is achieved. We also prove the game is stable; that is, there exist evolutionarily stable strategies (ESSs) that explain which strategies will be selected by a sensor node in the end. Moreover, a corresponding algorithm of secrecy rate adaptation is given. Numerical experiments show our proposed approach can adaptively adjust the secrecy rate of a sensor node, which provides a novel way to guarantee the confidentiality of WSNs.
1. Introduction
Providing security for Wireless Sensor Networks (WSNs) is challenging, due to the characteristics of wireless communications, limited resources of sensor nodes, dense and enormous networks, as well as the unattended environments where sensor nodes are prone to physical attacks. A large number of security approaches [1] such as cryptography, attack detection, and secure routing have been proposed to defend various threats and vulnerabilities in WSNs. Different to these traditional methods, physical layer (PHY) security [2, 3] using the physical properties of the radio channel to help provide secure wireless communications is currently attracting considerable attention. This approach is extremely suitable for WSNs since it achieves security through taking advantage of the fundamental ability of the physical layer, not adding extra components.
The main idea of PHY security is to maximize the rate of reliable information from a source to a destination, while keeping eavesdroppers ignorant of data transmitted. This rate is referred to as secrecy rate and its maximum reliable value for a channel is known as secrecy capacity. Wyner [4] in his pioneering work introduced a wire-tap channel and showed that perfect secrecy could be attained even without the application of shared secrets. Since its inception, secrecy capacity has been fundamentally developed in other channels including Gaussian wire-tap channel [5], broadcast channel [6], relay channel [7], multiple-access channel [8], interference channel [9], multiple-input single-output (MISO) channel [10], multiple-input multiple-output (MIMO) channel [11], and feedback channel [12].
Along with the foundation of secrecy capacity in various channels, a recent trend of long-standing interest has emerged in how to improve PHY security under the same surroundings. These include methods such as cooperation relays [13], joint relay and jammer selection [14], channel frequency selectivity [15], and game theory [16–26]. In practice, during the process of transmitting data, the transmission power is a key factor that influences the secrecy rate of a source. From a noncooperative perspective, each sensor node, due to its selfishness, attempts to increase its transmission power for maximizing its secrecy rate in response to actions of the other sensor nodes. In this manner, it will however cause more and more interference to the other nodes and consume its own energy extraordinarily. These interactions among sensor nodes naturally result in applications of game theory.
As an efficient method to solve problems of optimal strategies, game theory provides a rich set of mathematical tools for investigating the multiperson strategic decision-making, which has been broadly employed in WSNs security [27–33]. It is generally assumed that players in the classical game theory have complete information about the game and about behaviors of opponents and must act completely rationally. Distinguishable to these assumptions, evolutionary game theory (EGT) to be borrowed in this paper imagines that conditioned players who are randomly drawn from a large population play the game repeatedly. Moreover, over time players have the opportunity to optimize their individual utilities by reacting to simple observations from their opponents. This nature satisfies the requirement for the current large-scale wireless networks with characteristics of self-organization, self-configuration, and self-optimization. Thus, many researchers are currently engaged in developing EGT based schemes [34, 35]. Typical examples exist in evaluating an incentive protocol [36], adjusting multiple-access control and power control [37], maximizing TCP throughout [38], learning for an optimal strategy [39], coevolving rational strategies [40], implementing network selection [41], sensing the spectrum collaboratively [42], selecting dynamic service [43], enforcing cooperation among network nodes [44], promoting the selfish nodes to cooperate with each other [45], and so forth.
Up to now, there are some papers on combining secrecy capacity with game theory in different environments. The work in [19] formulates a noncooperative game between a source and a jammer relay for achieving the optimal secrecy rate of the source. Also, a noncooperative game between wireless users and a malicious node is introduced in [20], where the wireless users, through choosing a relay station, are to maximize a utility function considering their mutual interference and security of the chosen path whereas the malicious node is to reduce the overall network's secrecy capacity. From the perspective of information theory, the work in [22] provides a mathematical formulation for the noncooperative zero-sum game existed in the two-user MISO Gaussian interference channel with confidential messages. In [23] the authors model a two-person zero-sum game with the ergodic MIMO secrecy rate as the payoff function, in order to examine the trade-offs for the legitimate transmitter and the adversary. Since cooperation, on the contrary, is capable of improving PHY security, the work in [21] introduces friendly jammers to interfere with the eavesdropper to increase the secrecy rate of a source. A Stackelberg game is investigated to reflect interactions between the source that pays jammers for their interference and jammers who charge the source with a certain price for the jamming. Different from [21], a Stackelberg game [18] between primary users and secondary users in cognitive radio networks is modeled to maximize transmission rates of secondary users. Consequently, primary users’ secrecy rates are improved with the help of trustworthy secondary users. Besides, typical examples of the Stackelberg game exist in analyzing the cooperation between the primary and secondary transmitters in cognitive radio channels [24] and formulating the sources and the friendly jammers in a two-way relay system as a power control scheme to achieve the optimized secrecy rate of the sources [25]. Moreover, a nontransferable coalitional game [17], as one of cooperative games, is applied to achieve secrecy rate gains from cooperation in the presence of a cost for information exchange. The work in [26] formulates the relay selection in a two-stage decode-and-forward cooperative network as a coalitional game with transferable utility, which decreases the computation complexity in solving the distributed relay selection problem. In addition, the cooperative Kalai-Smorodinsky bargaining game [16] is adopted, for transmitters with the MIMO channel, to find an operating point that balances network performance and fairness. This point allows transmitters to adjust their precoders appropriately and thus improves the overall secrecy capacity of the network.
To the best of our knowledge, this paper is the first work to focus on exploring secrecy rate adaptation in WSNs with the idea of EGT. We first extend the classical secrecy rate equation to fit for the WSNs. We are thus able to understand what parameters will influence the secrecy rate in WSNs. Then, we solve the decision-making problem among sensor nodes for maximizing their utilities through a noncooperative secrecy rate game. The replicator dynamics is applied to illustrate the evolution process how sensor nodes select adaptively their power level strategies and achieve their adaptation of secrecy rate.
Compared with the related works mentioned herein, there are some distinctions in this paper. We concentrate clearly on the secrecy rate between a sensor node and its responsible cluster head in the clustered WSNs, while many other channels are considered in [4–12, 46–48]. We employ EGT to disclose the dynamics of secrecy rate adaptation for sensor nodes, while EGT is applied to other fields [34, 36–44, 49]. Our eventual objective is to maximize the fitness of sensor nodes while several current works [16–21] make use of various games to improve PHY security for different surroundings. Therefore, our contributions lie mainly in the following aspects:
considering the interference environment, we construct an approach to compute the secrecy rate between a sensor node and its responsible cluster head by developing the classical wire-tap channel [4, 5], which is suitable for the clustered WSNs;
we formulate a noncooperative secrecy rate game towards WSNs, which is able to reflect interactions among sensor nodes and the cost of energy consumed for transmitting data. Solving the game will help sensor nodes, by maximizing their utilities, to select their power level strategies correctly;
we attain, from the view of EGT, a selection dynamics that promotes sensor nodes to seek a power level strategy with higher fitness, as well as ESSs for the game to describe which power level strategies will be adopted by mutants in the end. The secrecy rate adaptation for sensor nodes is thus achieved.
The rest of this paper is organized as follows. In Section 2, we discuss the network surroundings to be studied and compute the secrecy rate between a sensor node and its responsible cluster head in the clustered WSNs. In Section 3, a noncooperative secrecy rate game towards WSNs is set up. Moreover, secrecy rate dynamics and ESSs for the game are explored. In addition, an algorithm is introduced to describe how to adjust adaptively secrecy rate of sensor nodes. In Section 4, by performing numerical experiments in an example of the secrecy rate game, we illustrate the influence of a cost parameter, as well as the corresponding ESSs. Moreover, the process of secrecy rate adaptation for sensor nodes is disclosed. Finally, a conclusion is provided in Section 5.
2. System Model
2.1. Interference among Sensor Nodes
Multiple-access channels based WSNs are under consideration in this paper. It is well known that multiaccess interference is a significant factor to reduce the performance of such networks. Lack of coordination among sensor nodes will lead to a great number of interfering power from their neighbors, even if each sensor node transmits signals at the lowest required power to its destination.
To attain the number of interferers for a particular sensor node, we use the assumptions as follows. We assume the WSNs are composed of static and identical sensor nodes that are uniformly scattered with node density ρ on a 2D grid. Each of sensor nodes is equipped with an omnidirectional transmitting and receiving antenna of the same gain and operates in a half-duplex way; that is, receiving and transmitting simultaneously are not allowed. The receiving and interfering ranges rely on the transmission powers of a source and the other sensor nodes in the same zone. Let
For a given sensor node, we now describe the number of its interferers. We employ Poisson distribution, due to its mathematical tractability, to estimate approximately the distribution of sensor nodes. In general, the maximum number of interferers should be computed in terms of the mean value and several times of standard deviation
2.2. Secrecy Rate in Clustered WSNs
The topology to be studied, as depicted in Figure 1, is based on the clustered structure due to its popularity. By using clustering, all sensor nodes are grouped into different clusters. Each cluster has a coordinator, referred to as cluster head, and a number of other sensor nodes as members, called member sensor nodes. This clustering leads to a two-tier hierarchy, where cluster heads construct the higher tier while member sensor nodes form the lower tier. In this hierarchy, a time-slotted data transmission scheme is adopted. In the first time slot, data captured by member sensor nodes in the same cluster are transmitted to the responsible cluster head, then in the second time slot the cluster head aggregates the data received and sends them to the base station through other cluster heads. Note that, for simplicity, our work is focused on the secrecy rate between a member sensor node and its responsible cluster head in the first time slot.
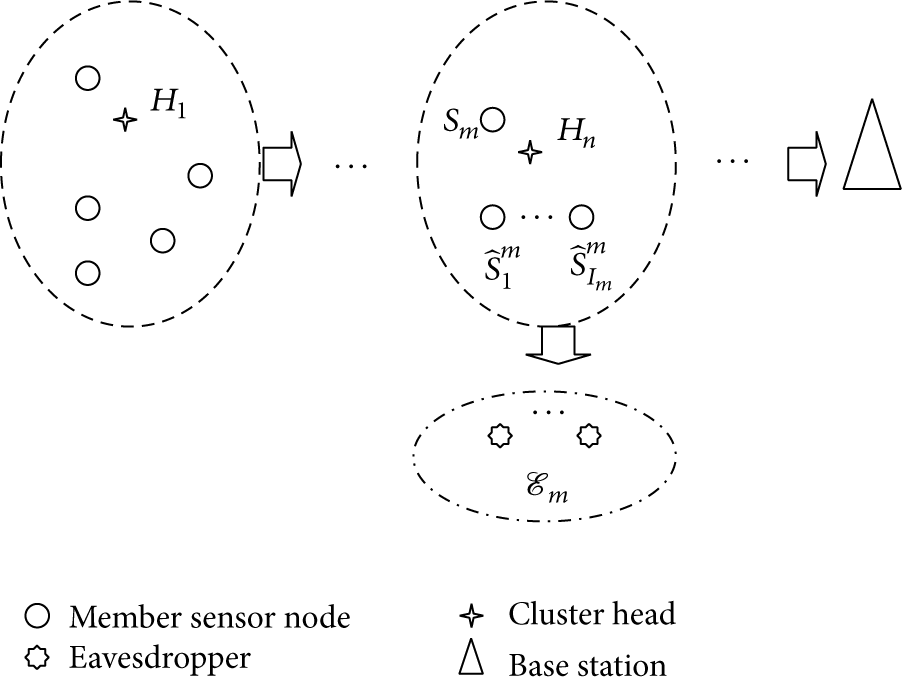
Network model.
Let
Due to the broadcast nature of channels, a cluster head endures a collision of signals from some member sensor nodes that are transmitting their data simultaneously. We treat these signals from member sensor nodes other than the target source as additive interference and compute the number of these interferers according to (1). For any member sensor node
where
Similarly, the channel capacity from member sensor node
where
where
3. Joint Secrecy Rate and EGT
3.1. A Compendium of EGT
Briefly, EGT is mainly concerned about a dynamic environment where players are continually interacting with others and adapting their strategies based on their expected payoffs they attain. In EGT, the concept of population consisting of a group of individuals (i.e., players) is introduced, and expected payoffs are replaced by fitness of individuals. An individual in an evolutionary game is able to observe the actions of other individuals, learn from these observations, and slowly adjust its strategy to attain the solution in the end. In this manner, we are able to understand the dynamics of interactions among individuals in a population.
In fact, the evolutionary process is determined by two noticeable elements: a mutation mechanism to provide mutants and a selection mechanism to promote some mutants with higher fitness over others [52]. While the mutation mechanism is described by evolutionary stable strategy (ESS), the selection mechanism is highlighted by replicator dynamics. The concept of ESS is to require that the final equilibrium must be capable of repelling all invaders; that is, if a strategy is evolutionarily stable, then it must keep such a quality that almost all individuals in the same population follow this strategy and mutants hardly invade successfully. This ESS is in fact a refinement of Nash equilibrium. On the other hand, the replicator dynamics is able to explain and predict the changeable trend towards population shares associated with different pure or mixed strategies. It selects individuals in a fitness proportional fashion. Thus, subpopulations with better fitness than the average will grow, while those with worse fitness than the average will be reduced in their numbers.
3.2. Secrecy Rate Game towards WSNs
Definition 1.
The secrecy rate game towards WSNs that is symmetric consists of a 3-tuple
In the secrecy rate game towards WSNs, we consider all member sensor nodes form a population and regard them as individuals. These individuals are intelligent agents who, during interactions with others, are able to self-adjust their strategies according to their current fitness. Their objectives are to adapt their secrecy rates by maximizing individual fitness.
Due to the interference among sensor nodes, an optimal power must be allocated to all member sensor nodes. From (4), the secrecy rate of member sensor node
where
3.3. Dynamics Analysis on Secrecy Rates of Member Sensor Nodes
We now explore the secrecy rate dynamics of member sensor nodes using the replicator dynamics. To begin with, all member sensor nodes, for transmitting data, select randomly one of available power levels. Each member sensor node, from the view of noncooperative game theory, expects to maximize its own fitness. It therefore adjusts periodically its power level (i.e., its secrecy rate is adjusted) and compares the corresponding fitness with the average fitness of the whole WSNs. If a higher value is attained, the member sensor node changes its current power level (i.e., its current secrecy rate is changed) to a new one; otherwise, it keeps its current strategy unchanged. Letting
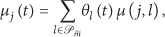
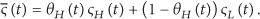
The state of the WSNs at time t, denoted by
where
Correspondingly, we define the expected secrecy rate of member sensor node
where
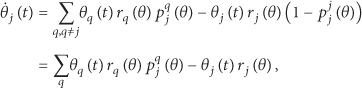
To make use of the idea of the replicator dynamics, we require the rate at which member sensor nodes change their strategies. This rate is determined by the performance of current strategies of member sensor nodes and by the population state. Let
while the inflow to the power level strategy j is
which constructs the replicator dynamics determining which power level strategies will be adaptively selected by a member sensor node.
For a member sensor node, whether or not to switch its power level is based on the corresponding fitness. Among the notations above, we suppose that j and q denote the power level strategies adopted by the original individuals and a small group of mutants, respectively. Then, the reviewing member sensor nodes change to the mutant strategy if and only if the fitness difference observed is positive; that is,
In fact, the choice probabilities in (13) result from individual differences in preferences across member sensor nodes and not from observation errors made by member sensor nodes with identical preferences. To isolate the effect of choice probabilities, for simplicity, we assume that all review rates are constantly equal to one; that is,
Substituting (13) and (14) into (12), we can, for member sensor nodes, get the selection dynamics as
This selection dynamics, determining the selection probability of a power level strategy, will be used to adapt the decision of a member sensor node and is at the same time affected by decisions of the other member sensor nodes.
3.4. Convergence and Stability Analysis on Secrecy Rate Game towards WSNs
Lemma 2.
If a power level strategy j is strictly dominant, then
Proof.
The case that a power level strategy is strictly dominant means member sensor nodes with this strategy, irrespective of which strategy any of other member sensor nodes chooses, can gain a strictly higher fitness than with any of other strategies. This will result in increasing the corresponding fraction in the population. Member sensor nodes employing a strictly dominant strategy will then occupy the whole population over time. Lemma 2 therefore follows.
From Lemma 2, we can attain that member sensor nodes whose strategies are strictly dominated will vanish eventually from the population; that is, if a power level strategy j is strictly dominated, then
Theorem 3.
The WSNs population state
Proof.
It is obvious that member sensor nodes employing different power level strategies will attain different fitness under the same WSNs surroundings. This fact means only one power level strategy, correspondingly, is endowed with the highest fitness among all strategies. Ranking all fitness values in descending order, we express the relationship of these fitness as
as equilibrium. Theorem 3 therefore follows.
Theorem 4.
The equilibrium of the secrecy rate game towards WSNs is evolutionarily stable.
Proof.
Following Theorem 3, we can, for the secrecy rate game towards WSNs, attain equilibrium as
can be changed into
where
denotes the corresponding downsized population state, which has equilibrium as
We now illustrate, in order to justify the equilibrium is evolutionarily stable, that eigenvalues of the Jacobian matrix of the downsized population state all have negative real part. Here an element of the Jacobian matrix that is a
The Jacobian matrix denoted by
In (21)
From Theorem
3.5. Secrecy Rate Adaptation Algorithm
The algorithm of secrecy rate adaptation for WSNs is in fact to describe the process how member sensor nodes select adaptively their power level strategies. During this iterative process, periodically, a member sensor node observes its fitness in an entirely distributed mode and evaluates its current fitness with the average fitness of the whole WSNs. If the difference is larger than a predefined maximum bound, then the member sensor node selects a new power level strategy according to the selection dynamics from (15). This interactive process goes on until the ESS of the secrecy rate game towards WSNs is achieved. All member sensor nodes thus find a satisfactory solution to secrecy rate adaptation, and no member sensor nodes can benefit by switching their current power level strategies while the other ones keep their strategies unchanged. From now on, we can show the algorithm as follows.
Algorithm 1.
Initialize all coefficients including W, I, select a power level strategy j with the selection probability compute the fitness compute the expected secrecy rate DO WHILE .T. // τ means a predefined minimum bound; IF EXIT; ENDIF // IF get select a new power level strategy j with the new selection probability compute the fitness compute the expected secrecy rate ENDIF; ENDDO; RETURN the array of
4. Experiments
Since member sensor nodes are generally constrained in limited computation, memory, and battery life, we simplify the number of power level strategies to introduce an example of the secrecy rate game towards WSNs. We consider that a member sensor node
where
Obviously, for the example of the secrecy rate game towards WSNs, we can get (a)
Next, we initialize all coefficients required in the example of the secrecy rate game towards WSNs for performing numerical experiments. According to IEEE 802.15.4 physical layer specifications, we let
4.1. Effect of α
The ESSs of the secrecy rate game towards WSNs are dependent on the cost parameter α. As depicted in Figure 2, utilities of all strategy profiles are decreasing linearly with different speeds while α is increasing gradually. This fact means the influence of a power level strategy becomes larger than that of secrecy rate on the utility of a member sensor node. We can see lines of
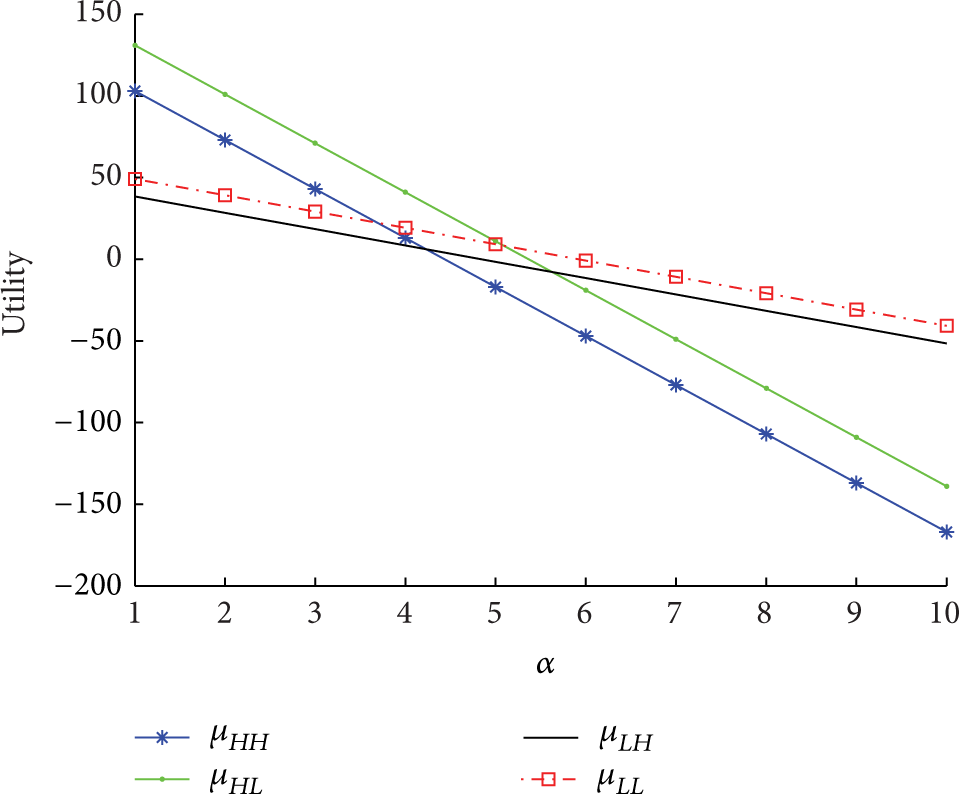
Effect of α on ESSs of the example of the secrecy game towards WSNs.
4.2. ESSs for the Example of the Secrecy Rate Game towards WSNs
To illustrate the evolution of member sensor nodes selecting different power level strategies, the probability distribution function φ in (15) should be first defined. According to the idea [52] through linearizing the function φ, we suppose
where
where γ is in fact a parameter that will influence the convergence speed of ESS. Let γ be 0.5 (in practice, γ may be an arbitrary real number); we attain different ESSs of the example of the secrecy rate game under different cost parameter values 3, 4.5, and 6, which are illustrated in Figures 3, 4, and 5, respectively. Note that these cost parameter values determine three different ESSs. As illustrated in Section 4.1,



A mixed ESS (0.6841, 0.3159) exists when
In Figure 3, when the initial value of (25) is 0.005, that is, if only 0.5% member sensor nodes select the high power level strategy
In Figure 4, even if 99.5% member sensor nodes select
In Figure 5, all curves of member sensor nodes selecting
4.3. Secrecy Rate Adaptation
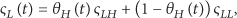
Our mechanism of secrecy rate adaptation in WSNs is realized when member sensor nodes select adaptively their power level strategies for maximizing their fitness. For convenience, let
From (8), we can attain that the average fitness of the whole WSNs is
Similarly, we denote the expected secrecy rate of a member sensor node adopting
and the average secrecy rate of the whole WSNs,
Here
We are now able to, under different cost values 3, 4.5, and 6, show changeable trends of fitness depicted in Figures 6, 7, and 8, as well as expected secrecy rates in Figures 9, 10, and 11, respectively. In Figures 6 and 9 where

Different fitness when

Different fitness when

Different fitness when

Different expected secrecy rates when

Different expected secrecy rates when

Different expected secrecy rates when
5. Conclusion
We have demonstrated the evolution process of secrecy rate adaptation for sensor nodes in the clustered WSNs. For this aim, the classical wiretap channel has been extended to fit for the clustered WSNs and the corresponding equation to compute secrecy rate has been attained. The secrecy rate game we have constructed is able to reflect the interactions among member sensor nodes. With EGT, we have attained a selection dynamics to determine how member sensor nodes for maximizing their fitness will select their power level strategies. We have also proved the stability of the secrecy rate game to illustrate which power level strategy will be adopted in the end. The results from experiments for an example of the secrecy rate game towards WSNs have verified all ESSs and have revealed the process of expected secrecy rate adaptation for member sensor nodes. As a result, this disclosure of secrecy rate adaptation will be beneficial to employ PHY security to guarantee the secrecy of transmission in WSNs.
Footnotes
Notations
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work was supported by National Natural Science Foundation of China under Grant no. 61272034, by Zhejiang Provincial Natural Science Foundation of China under Grants LY13F030012 and LY13F020035, and by Science Foundation of Shaoxing University under Grant no. 20145021.