Abstract
Barrier coverage is a fundamental problem for lots of applications in wireless sensor networks. In reality, sensor nodes' true locations may not be known to us considering that not every sensor node is equipped with a GPS. The measured locations of sensor nodes obtained by applying node localization algorithm often have errors, which makes it difficult to form a line-based barrier with mobile sensor nodes. In this paper, we study how to efficiently schedule mobile sensor nodes to form a barrier when sensor nodes suffer from location errors. We explore the relationship between the existence of uncovered hole and location errors and find that the lengths of uncovered holes are decided by the cumulative location errors. We also propose a method in frequency domain to efficiently calculate the distributions of the cumulative location errors. The possibility of the existence of uncovered holes can be derived by analyzing the step responses of the cumulative location errors. Extensive experimental results demonstrate the effectiveness of the proposed algorithm.
1. Introduction
Wireless sensor networks (WSNs) [1–6] have been widely used in a variety of application scenarios. In WSNs, the quality of sensing [7–10], which is often referred to as coverage, is a fundamental concern. Barrier coverage deploys sensor nodes in a long, narrow region of interest (ROI) which carries out detecting the targets when they penetrate into the region. It finds significant application in WSNs. For example, in the application of border surveillance, we are able to detect unauthorized intrusions by deploying sensor nodes along the boundary of interest.
The first and most important aspect to form a barrier is how to design sensor nodes deployment. When the sensor nodes are placed to the expected locations, the quality of barrier coverage is guaranteed. However, in actual applications, most cases of the ROI are in harsh environment, which make it difficult to obtain the expected locations and deploy the nodes there. Sensor nodes are deployed randomly in most practical cases; for example, they can be dropped from aircraft [11]. To this end, the sensor nodes are not deployed to the expected locations initially, and they could not form a barrier. Fortunately, thanks to recent advances in mobility-assistant technology, sensor nodes have the ability to move around to carry out tasks [12, 13]. Hence, a barrier coverage could be formed by controlling the senor mobility.
Firstly, each mobile sensor node obtains its location before moving to the expected locations. Therefore, the problem of achieving barrier coverage is covert to the localization problem of mobile nodes. Equipping GPS receivers on each node to get the accurate location information is too cost-expensive. Hence, in practical use, only several nodes are equipped with GPS receivers. The other nodes are located by integrating the relative locations to their neighboring nodes using localization algorithms. In the past years, lots of localization algorithms have been proposed, such as Time of Arrival (TOA) [14], Time Difference of Arrival (TDOA) [15, 16], Angle of Arrival (AOA) [17, 18], and Received Signal Strength Indicator (RSSI) [19–21]. However, the location results provided by these algorithms have low accuracy and in most cases with location errors. Due to location errors, mobile nodes' measured locations are different from their actual locations. Thus, they cannot stop and be deployed at the expected locations in real applications. To guarantee the quality of barrier coverage, barrier formation should be adaptive to the location errors. However, little literature considers the effects of location errors.
Moreover, the location errors of the localization algorithms are diverse and may follow a random distribution. Traditional methods always analyze the worst cases, that is, the lower and upper bounds. However, worst case analysis is always conservative and hard to capture the higher-order location error characteristics. For example, node A is equipped with a GPS receiver; node B is located relative to node A, and the location error follows a uniform distribution:
In this paper, we investigate how to efficiently schedule mobile sensor nodes to form a barrier when sensor nodes suffer from undetermined location errors. Firstly, we investigate how the uncovered holes are generated by the location errors and find that the lengths of uncovered holes are decided by the cumulative location errors. Then we analyze how to calculate the distributions of cumulative location errors. Since each location error follows a distribution, convoluting the distributions of individual location errors to get the distribution of the cumulative location error is inefficient. Its computational cost is extremely high when the network is large. In this paper, we calculate the location errors in the frequency domain. Convolution is converted to multiplication and the computation complexity is heavily reduced. Third, after the cumulative location errors are obtained in frequency domain, we analyze the characteristics of their step responses (e.g., probability distribution functions). Then, the probability of uncovered holes existing could be easily obtained from the step responses. Finally, when the possibilities are high, we reduce the possibilities by deploying more nodes, equipping more GPSs, or improving sensing range to guarantee the quality of barrier coverage adaptively.
To the best of our knowledge, our work is the first applying frequency analysis on studying barrier coverage problem when nodes have location errors. The major intellectual contributions of this paper are summarized as follows:
We theoretically analyze the relationships between the lengths of the uncovered holes and the location errors. The mathematical expressions of calculating the uncovered holes' length from the cumulative location errors are given. When each location error follows a distribution, we give an efficient method to calculate the distribution of the cumulative location error in frequency domain. We propose a method of analyzing the step response of the cumulative location error to get the probability of the uncovered hole existing. We study some cases to show how to use our framework and guarantee the quality of barrier coverage adaptively.
The rest of this paper is organized as follows. Section 2 surveys the related work and Section 3 analyzes the barrier coverage when location errors exist. We give theoretical expressions of calculating the uncovered hole length in Section 4. Then in Section 5 we calculate the cumulative location errors in frequency domain and get the probabilities of the uncovered holes existing. Section 6 gives examples of using our framework and corresponding evaluation and Section 7 provides conclusions.
2. Related Work
Barrier coverage is a fundamental problem for lots of applications in wireless sensor networks and has been widely researched. Kumar et al. [22] firstly defined the notion of k-barrier coverage and introduced weak and strong coverage in a belt region. Liu et al. [23] proposed a solution for strong barrier coverage when sensor nodes are randomly deployed according to a Poisson point distribution process. Li et al. [24] investigated the weak k-barrier coverage problem and derive a lower bound for the probability of weak k-barrier coverage. Since most cases of the ROI are in harsh environment and difficult for human being to reach, Saipulla et al. [11] investigated barrier coverage with airdropped wireless sensors under line-based deployments and give a lower bound for the existence of barrier coverage. In [25], He et al. showed the suboptimality of line-based deployment when the length of shortest line segment is larger than that of shortest path and for the first time quantified the need of curve-based deployment; then they introduced a concept of distance-continuous curve and provided an algorithm to obtain the optimal sensor deployment when the deployment curve is distance continuous. Chen et al. [26, 27] proposed the methods of scheduling sensors energy efficiently while guaranteeing the detection probability of any intrusion across the region based on probabilistic sensing model, which is a more actual sensing model.
Due to recent technological advances, nodes have the ability to move around to carry out tasks. Barrier coverage in mobile sensor network is a hot research area. He et al. [28] guaranteed that each point along the barrier line is monitored periodically by mobile sensors by using a periodic monitoring scheduling algorithm. Saipulla et al. [29] presented a method which could construct the maximum number of barriers under the constraints of sensor mobility. Shen et al. [30] found that barrier coverage could be achieved with fewer mobile sensors than stationary sensors when applying random deployment. Wang et al. [31] proposed a method of using minimum number of mobile sensor nodes to improve barrier coverage when the stationary nodes are not forming a barrier after initial deployment. He et al. [32] designed a periodic monitoring scheduling algorithm in which each point along the barrier line is monitored periodically by mobile sensors and propose a coordinated sensor patrolling algorithm to further improve the barrier coverage, where each sensor's current movement strategy is derived from the information of intruder arrivals in the past.
Using mobility-assistant nodes in randomly deployment barrier coverage can achieve higher quality sensing performance if they could move to the designed locations. However, due to high equipment cost, not all mobile nodes are equipped with GPS receivers. We locate them using typical localization algorithms. However, location errors exist which will significantly affect the quality of coverage. Thus, in this paper, we investigate how to efficiently schedule mobile sensor nodes to form a barrier when sensor nodes obtain locations with errors.
3. Barrier Coverage When Location Errors Exist
Mobile wireless sensor networks usually consist of large number of mobile sensor nodes. We denote
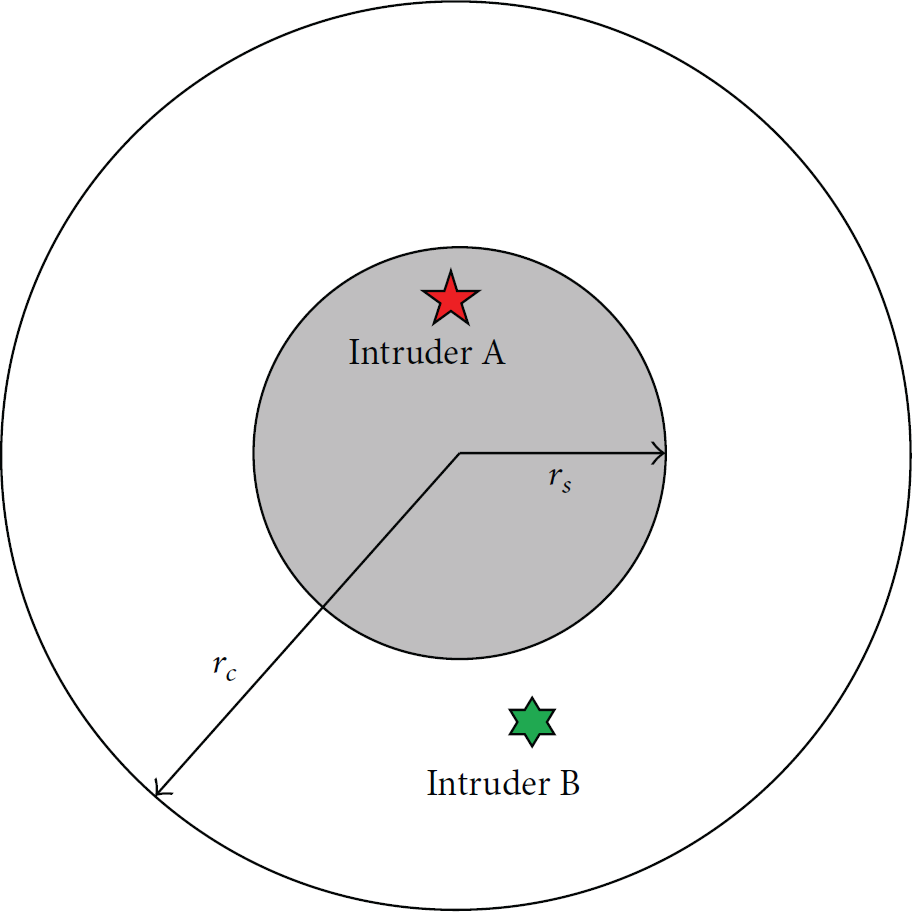
Sensing range and communication range of sensor node.
We construct the model of the region of interest (ROI) with a closed line interval
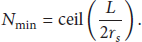
Considering the limitation of the sensing range and communication range of the nodes, the minimum number of nodes we need to form a barrier to cover L is
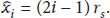
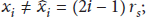
As shown in Figure 2(a), we deploy

An example of line-based barrier coverage: (a) nodes are deployed in the expected location; minimum number of nodes is used to form a barrier; (b) when location error exists, the barrier has uncovered holes on it.
However, in practical scenario, the ROI is probably in a harsh environment, and sensor nodes are usually deployed randomly. In such case, the sensor nodes are not deployed in the expected location initially, and the barrier cannot be formed. Fortunately, with mobility-assistant technology, the mobile nodes can move to the designed locations to form a barrier. However, it is too expensive to equip each node with a GPS receiver. In a typical network, only several nodes are equipped with a GPS receiver, which act as the beacon nodes. Then, we can use localization algorithms to locate other nodes that are neighboring these beacon nodes. When these locations are obtained, they also become beacon nodes to the other neighboring nodes. With such method, all the nodes' locations can be obtained.
Actually, there is localization error in practical process. Take example of node
In wireless sensor networks, none of the existing localization algorithms can obtain perfectly accurate location; that is, the location errors exist actually. Hence, we get
Definition 1.
The one-hop location error
While there is location error, mobile nodes cannot move to the optimized locations. We take an example to demonstrate the impact of the location errors. As shown in Figure 2(b), we utilize
4. Models of the Uncovered Holes
In the above section, we show that due to the existence of the location errors the nodes cannot move to the expected locations. Hence, this situation incurs uncovered holes on the barrier. The uncovered holes could be classified into three categories: (1) the uncovered hole between two neighboring nodes where one node is located based on the other node; (2) the uncovered hole between two neighboring nodes where the two nodes are not located based on one another; (3) the uncovered holes between the leftmost (or rightmost) node and the left (or right) endpoints of L. We define them as the first, second, and third type of uncovered hole, respectively, in the following description. We will give detailed analysis of these three types of uncovered holes in this section.
4.1. The First Type of the Uncovered Hole
The first type of uncovered hole is shown as in Figure 3. There are two neighboring nodes, nodes

Node
Theorem 2.
For two neighboring nodes, nodes
Proof.
The interval between nodes
4.2. The Second Type of the Uncovered Hole
The second type of uncovered hole is shown as in Figure 4. There are two neighboring nodes, nodes

Theorem 3.
For two neighboring nodes, nodes
Proof.
Since the interval between nodes
Similarly, for
As shown in Figure 4(a), when
4.3. The Third Type of the Uncovered Hole
The third type of uncovered hole is shown as in Figure 5. Node

The uncovered hole between the leftmost (rightmost) node and the left (right) endpoint of L: (a) uncovered holes do not exist; (b) uncovered holes exist.
Theorem 4.
The length of the uncovered hole between the leftmost node
Proof.
For the uncovered hole between the leftmost node and the left endpoint of L, since the leftmost node is set to be deployed at
As shown in Figure 5(a), when
Similarly, we can prove
We have introduced the three types of uncovered holes. From Theorems 2, 3, and 4, we find the following:
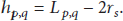
The uncovered holes are decided by the neighboring nodes' interval D, the sensing range The first type of uncovered hole is decided by the one-hop location error. The second and third types of uncovered holes are decided by the cumulative location errors. Thus, as the network scale gets larger, they can be much more complicated to analyze than the first type of uncovered hole. In an actual network, the three types of uncovered holes are not separated. For example, when
5. Analysis of Coverage in Frequency Domain
We have introduced the uncovered holes in aforementioned section and find that the uncovered holes are determined by the node location errors. For practical consideration, the location errors are usually not fixed. Each one-hop location error follows a random distribution which can be obtained by theoretical analysis or from numerous experiments. The cumulative location error follows a superimposed distribution, and the probability density function equals the convolution of the probability density functions of the individual one-hop location errors.
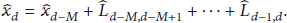
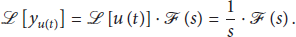
Let
We define
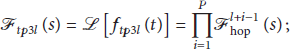
Thus, we need to convolute the one-hop location error distributions to get the distributions of the cumulative location errors. When the distributions of the cumulative location errors, that is,
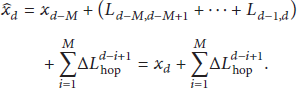
Let
By using Laplace Transform and converting distributions to the frequency domain, we calculate the cumulative location errors for different types of uncovered holes as
Let
Let
Based on the step responses, it is feasible to analyze the uncovered holes.
For the first type of uncovered hole, its length is
Similarly, the probability of the second type of uncovered hole existing is
We have developed the theoretical framework to model and analyze the uncovered holes. The procedures are shown in Algorithm 5.
Algorithm 5.
The theoretical framework to model and analyze the uncovered holes is as follows:
Obtain individual one-hop location error distributions of the network and convert them into frequency domain using Laplace Transform. Calculate the distributions of the cumulative location errors in frequency domain by multiplications. Analyze the step responses to get the probability of having uncovered holes on the barrier.
6. Evaluation
In previous sections, we have introduced our framework of analyzing the uncovered holes. In this section, we give some examples to show how to use the framework. The parameters of the simulations are summarized in Table 1.
System constants and simulation parameters.

The length of the region of interest L is 2000 m and the sensing range
However, as shown in Figure 6(a), due to high cost, only node 

The example systems: (a) we deploy 21 nodes, and only node
To use the proposed framework, we first use Laplace Transform to covert 
Then we calculate the cumulative location errors for different cases of uncovered holes. Obviously, there may exist some first type of uncovered holes and a third type of uncovered hole (at the right endpoint of L) on the barrier. By (29) and (32), we have

The step response of
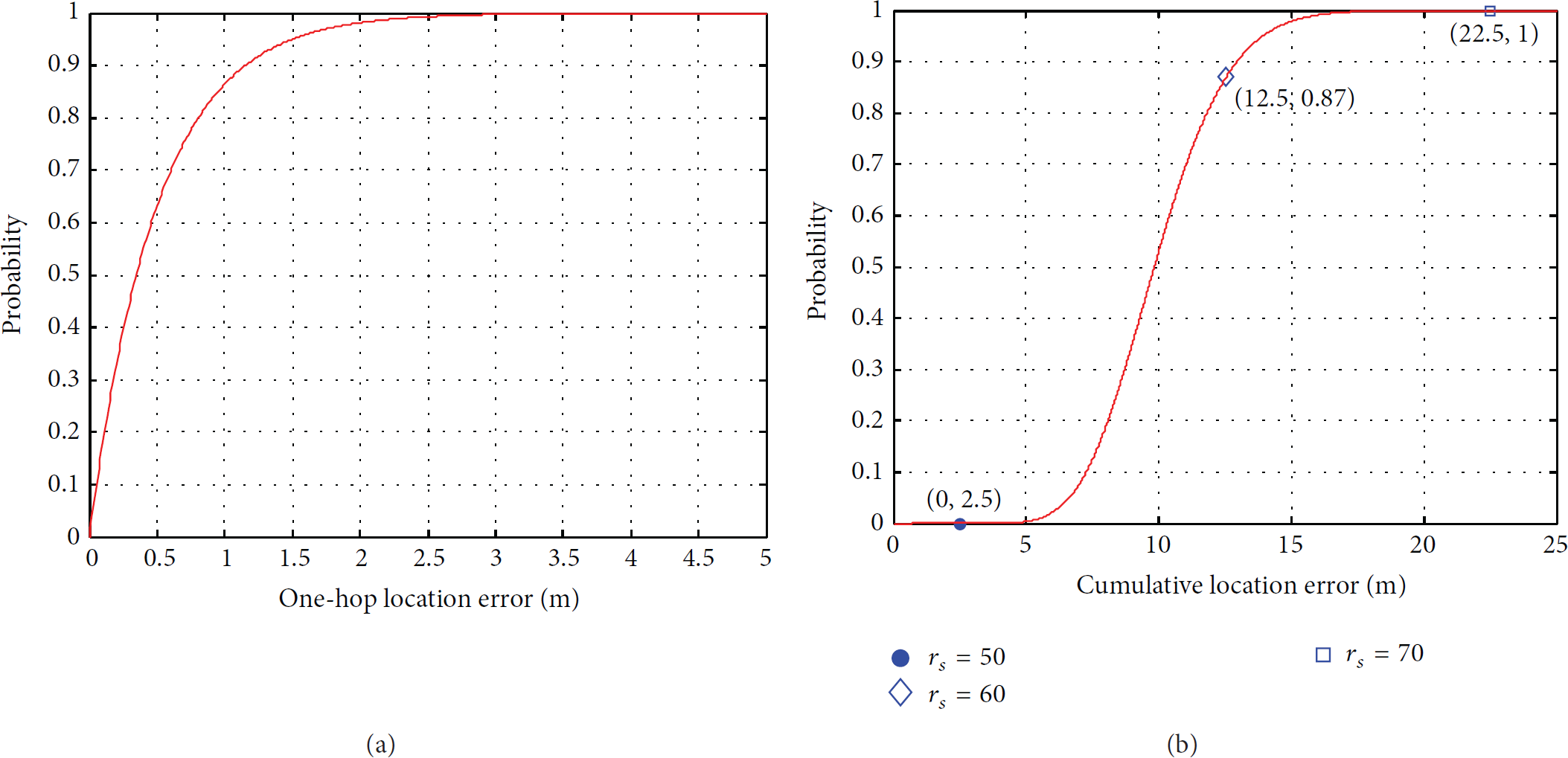
The step responses: (a) step response of
We have obtained the probability of an uncovered hole existing at the right endpoint which is
6.1. Enlarge Sensing Range
We enlarge the sensing range here. Enlarging the sensing range does not affect the location errors. Thus, the step responses of
Using (35) and (38), we find the following: (a) when
Thus, when the sensing range is enlarged to 70 m, there is no uncovered hole on the barrier. However, in many applications, the sensing range is fixed. In these situations, enlarging the node's sensing ability is not practical.
6.2. Deploy More Nodes
As shown in Figure 6(b), we add more sensor nodes into the network. Obviously, the probability of having the first type of uncovered hole is not affected, which is
We add 
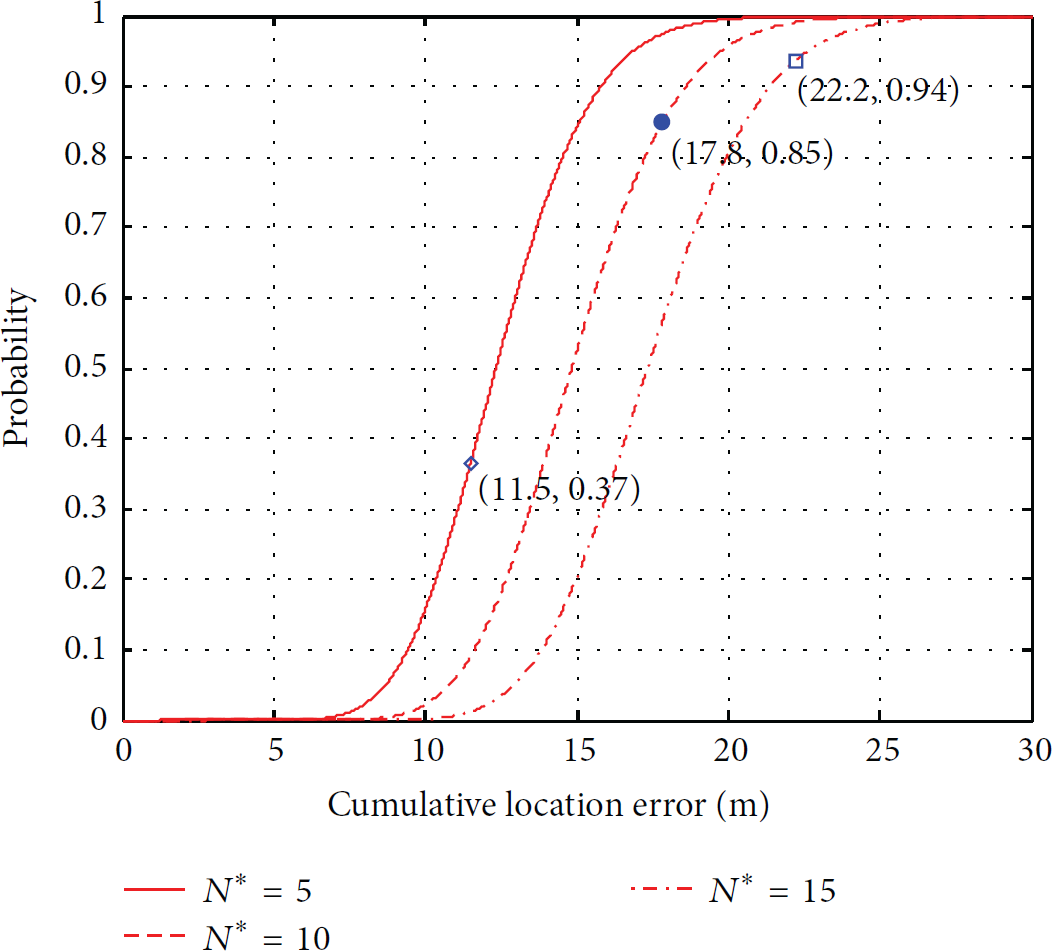
The step response of
When
When
When
Obviously, we can see that the probability of having uncovered holes is reduced by deploying more nodes.
6.3. Equip More GPSs
As shown in Figure 6(c), more nodes are equipped with a GPS receiver. Obviously, the probability of the first type of uncovered hole existing is still

The step responses: (a) step response of
When we equip one more GPS receiver (on
When we equip two more GPS receivers (on
When we equip three more GPS receivers (on
Thus, the probability of having uncovered holes is reduced by equipping more GPS receivers.
In general, we have shown how to use our framework by the examples and get the probabilities of the uncovered holes existence. When the probabilities cannot meet our requirement, we adaptively enlarge the node's sensing ability (sensing range), deploy more nodes, or equip more GPS receivers to achieve high quality barrier coverage.
7. Conclusions
In this paper, we study how to efficiently schedule mobile sensor nodes to form a barrier when sensor nodes suffer from location errors. We find that when location errors exist, there may exist uncovered holes on the barrier and the quality of sensing cannot be guaranteed. We give the theoretical relationship between the length of the uncovered holes and the cumulative location errors. To get the cumulative location errors efficiently, we propose a method which calculates them in the frequency domain. We analyze the step responses to get the probabilities of having uncovered holes on the barrier. To guarantee the quality of sensing, we adaptively enlarge the node's sensing ability (sensing range), deploy more nodes, or equip more GPS receivers to reduce the probability of uncovered hole existing. In the future work, we will consider the constraints of the actual systems, like the cost constraints, the battery constraints, and the constraints of the probability of uncovered hole existence, and optimize the systems performance.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
Project is supported by the National Natural Science Foundation of China (nos. 61273079 and 61502352), Key Laboratory of Wireless Sensor Network and Communication of Chinese Academy of Sciences (no. WSNC2014001), the Open Research Project of the State Key Lab of Industrial Control Technology, Zhejiang University (nos. ICT1541 and ICT1555), the Natural Science Foundation of Hubei Province, China (no. 2015CFB203), and the Natural Science Foundation of Jiangsu Province, China (no. BK20150383).