Abstract
Routing in mobile social networks is a challenging task due to the characteristic of intermittent connectivity, especially when the nodes behave selfishly in real world. Selfish behaviors of node always influence its altruism to provide forwarding service for others and degrade network performance strongly. In this paper, to address the selfishness problem in MSNs, we propose a service-based selfish routing protocol, SSR. When making forwarding decision, SSR employ user altruism and the amount of service that the relay nodes provide. User altruism is determined by the social selfishness and the individual selfishness. The services include pairwise services and social services, which is also considered as the incentives to stimulate node to be more cooperative. The more services the node provides, the more chance the node has to be served. The node with higher altruism and fewer services is the preferred relay node. Simulation results show SSR achieves better performance when the user altruism is low and demonstrate the effectiveness of the service-based scheme.
1. Introduction
The portal devices such as smart phone, laptop, and tablet computer have been very popular in the world with the rapid development of the technologies of wireless communication and integrated circuit. These devices with the wireless capabilities such as Bluetooth, WiFi, or 3G are often carried by people and cooperate with each other to form an ad hoc network for exchanging and sharing data. Social behavior analysis has been introduced to resolve the routing issues when nodes are attached to the human or vehicles and could achieve better performance by using social relationship in real life environment. Hui et al. [1] named the network pocket switched networks (PSNs), a typical type of delay tolerant networks (DTNs) [2]. Because there have been some inherent social features in the network, it is also called mobile social networks (MSNs).
Some institutes try to find social properties of the mobile social networks in the real world based on the data set collected from the portable devices attached to human, for example, Reality Mining [3], Infocom’05 [4], and Infocom’06 [5]. And there have been lots of routing strategies for mobile social networks, such as LABEL [6], BUBBLE [7], and SimBet [8] which all employ the social network properties to help message forwarding. However, in the previous routing techniques, there is a common assumption that all nodes in the network are unselfish and cooperative. That is, each node is willing to receive and relay the packets sent by other nodes. Unfortunately, in the real world, most people are selfish and there would be some selfish nodes dominated by rational human. For example, the node would be reluctant to deliver the packet for others because of the limited resources (energy, buffer, bandwidth, etc.).
Obviously, node selfishness affects node behaviors and degrades the network performance. To stimulate selfish nodes to forward packets, many incentive protocols such as reputation-based, credit-based, and TFT-based for ad hoc network have been proposed [9–12]. The goal of these incentives is to handle the individual selfishness, assuming that the status of nodes is equal. However, in a real social network, the social relations or social ties of nodes are different and a node is more willing to relay packets for those who have social relations or social ties with it. Li et al. [13] call it social selfishness. They propose a social selfishness aware routing (SSAR) algorithm to allow user selfishness and provide better routing performance in an efficient way. However, SSAR quantifies the node's willingness to evaluate its forwarding capability based on the social ties, which is not enough to reflect the real willingness of the node to relay the packets. Besides social ties, the residual resources of the node also have impacts on user's willingness to relay the packets. For example, a node has strong social relation with other nodes but its resources are scarce (e.g., very low energy of the battery). Though it is very willing to serve for other nodes, it cannot do it because it lacks the resources.
In this paper, we propose service-based selfish routing protocol for mobile social networks, which consider the user altruism to relay packets and the amount of service of node. The main contributions of the paper are as follows. Classify user altruism into social altruism and individual altruism. Social altruism is decided by the social selfishness, while individual altruism is determined by the current resources of the node. Propose a service-based incentive scheme, in which the service made by the node is considered as the incentive to the node. Different from other works, it quantifies the services of the node based on its altruism. The services of the node include the pairwise services between the two given nodes and their services for the whole network. Propose a routing protocol based on the amount of services of the relay node and demonstrate the effectiveness of the protocol via simulation.
The remainder of this paper is organized as follows. Section 2 discusses the related works. Section 3 presents the system model and describes the problems. Section 4 gives the detailed design. Section 5 introduces simulations and discusses the results. The last section concludes the paper.
2. Related Works
2.1. Routing in Social Network
Hui and Crowcroft have proposed a routing algorithm called LABEL [6] which takes advantage of communities for routing messages. LABEL partitions nodes into communities based on only affiliation information. Then each node in the network has a label telling others about its affiliation. A node only chooses to forward messages to destinations or to the next-hop nodes belonging to the same group (same label) as the destinations. LABEL significantly improves forwarding efficiency over oblivious forwarding using their data set, but it lacks a mechanism to move messages away from the source when the destinations are socially far away.
BUBBLE [7] combines knowledge of the community structure with knowledge of node centrality to make forwarding decisions. Centrality in BUBBLE is equivalent to popularity in real life, which is defined as how frequently a node interacts with other nodes. People have different popularities in the real life so that nodes have different centralities in the network. Moreover, people belong to small communities like in LABEL. When two nodes encounter, the node forwards the message up to the node with higher centrality (more popular node) in the community until it reaches the same level of centrality as the destination node. Then, the message can be forwarded to the destination community at the same ranking (centrality) level.
SimBet presented in [8] makes routing decisions by centrality and similarity of nodes. Centrality means popularity as in BUBBLE. More specifically, the centrality value captures how often a node connects nodes that are themselves not directly connected. Similarity is calculated based on the number of common neighbors of each node. SimBet routing exchanges the preestimated centrality and locally determined similarity of each node in order to make a forwarding decision. The forwarding decision is taken based on the similarity utility function (SimUtil) and betweenness utility function (BetUtil). When nodes contact with each other, the node selects the relay node with higher SimBet utility for a given destination.
In [14], Fabbri and Verdone propose a sociability-based DTN routing, which is based on the idea that nodes with high degrees of sociability (frequency encountering many different nodes) are good forwarding candidates. They defined the sociability indicator metric to evaluate the forwarding ability of a node. The routing strategy forwards packets to the most sociable nodes only.
In [15], authors propose a fuzzy-assisted social-based routing (FAST) protocol that takes the advantage of social behavior of humans on the road to make optimal and secure routing decision. FAST uses prior global knowledge of real-time vehicular traffic for packet routing from the source to the destination. In FAST, fuzzy inference system leverages friendship mechanism to make critical decisions at intersections which is based on prior global knowledge of real-time vehicular traffic information.
2.2. Handle Selfishness
Since selfish behavior of the node degrades the performance of routing protocol, many incentive mechanisms have been studied to stimulate individual selfish node to be cooperative. The incentive strategies can be classified into three categories: reputation-based, credit-based, and TFT-based approach.
In reputation-based schemes, forwarding services are provided to nodes depending on their reputation. When a node provides services for other nodes, it gets good reputation. Nodes with good reputations can receive services from other nodes. On the contrary, misbehaving nodes get bad reputations and will be denied participation in the network. The fear of detection and punishment motivates nodes to cooperate. Mei and Stefa [9] proposed a reputation-based incentive scheme (Give2Get) for DTN routing, which can detect misbehaving nodes and remove them from network routing. They proved that their proposed scheme achieves Nash equilibria.
The credit-based schemes introduce some form of credit or virtual currency to regulate the packet-forwarding relationships among different nodes. Nodes earn virtual currency by forwarding packets for others. These credits can be used to obtain forwarding service from any node in the network. For every forwarding request, the virtual bank charges the sender an extra amount of virtual currency, and the intermediate nodes redeem their rewards at the bank after successful delivery. SMART (secure multilayer credit-based incentive) scheme [10] uses credits to provide incentives to selfish nodes. Such scheme adopts a novel layer concatenation technique to withstand cheating actions of selfish nodes. MobiCent [11] assumes that each mobile device is capable of operating in two modes: a long-range low-bandwidth radio to maintain an always-on connection and a short-range high-bandwidth link to opportunistically exchange a large amount of data with peers in its vicinity. MobiCent provides a credit-based algorithmic mechanism design approach to address selfish attacks.
In TFT-based schemes, every node forwards as many messages for a neighbor as the neighbor forwards for it. In this way, a node autonomously lowers services to a neighbor if it detects that the neighbor is misbehaving. Shevade et al. in [12] proposed the use of pairwise tit-for-tat (TFT) as a simple and robust incentive mechanism for DTN routing. This incentive-aware routing protocol allows selfish nodes to maximize their own performances without any significant degradation of system-wide performance. Rather than attempting to detect misbehavior, it focuses on detecting good behaviors by using TFT.
Li et al. [13] introduce the social selfishness problem into DTNs and proposes a routing algorithm SSAR following the philosophy of design for user. SSAR allows user selfishness and improves performance by considering user willingness, resource constraints, and contact opportunity when selecting relays. User willingness is quantified by the social relations among nodes, which is used to evaluate its forwarding capability.
Based on the regularity of human behavior, authors propose a hot-area-based selfish routing protocol (HASR) tailored for mobile social networks. Data transmission is based on the active degree of the node, which is calculated by the weight of hot areas that nodes will visit, when there are no selfish nodes. When nodes behave selfishly, routing decision is made by the contribution index that indicates the contributions to data transmissions of the network made by nodes. Moreover, they present a social contribution-based routing protocol for selfish vehicular network in [16]. When making forwarding decision, the protocol considers both the delivery probability to the destination and the social contributions of the relay node.
Guan et al. [17] study the impact of individual and social selfish behaviors in DTNs. Based on analysis, it is concluded that social selfishness leads the internal threats in DTNs. The main reason of internal threats is that some nodes have less social relations and difficulty to participate in the forwarding process. When these nodes cannot afford the forwarding cost, they will be isolated by the network and become malicious node. To avoid the internal threats, authors measure the social wealth distribution of the DTNs by using Gini coefficient and design the taxation strategy to redistribute the social wealth.
3. System Models and Problem Statement
In this section, we first define the user altruism and then formalize the network model. Finally, the problem is stated and analyzed.
3.1. User Altruism
User altruism means the user willingness to relay packets for other nodes and is related to the user selfishness. As mentioned before, the user selfishness could be classified into social selfishness and individual selfishness. Correspondently, there are also social altruism and individual altruism. Social altruism between two nodes depends on their social relation. The stronger their social relation is, the larger their social altruism is and the more chance the two nodes forward packets for each other. Let SA denote the social altruism.
However, social altruism to relay the packets for others just reflects the social relations among nodes. It may not reflect the real willingness of an individual rational entity. To differentiate from the social altruism, we introduce individual altruism, denoted by IA. The current resources of node would affect the individual altruism. If a node has limited resources such as low energy or low buffer, it is not willing to relay packets for others, even if its social altruism is high. The more the resources of the node, the larger the IA.
3.2. Network Model
We model the mobile social network as a directed contact graph
As for individual altruism, it is determined by the residual resources of node. The residual resources of node change over time with the consumption of the resources so that the IA is variable. IA could be calculated by the current resources of nodes. Without loss of generosity, we compute IA based on the residual energy of node; that is, IA is equal to the percentage of the residual energy.
Moreover, we assume that nodes are honest and trust each other. There are no malicious nodes in the network and nodes never drop packets intentionally. We do not consider the buffer issue in this paper for the handheld nodes gradually have more and more storage size and the bandwidth is high enough to allow the exchange of all messages between nodes at encounter times. These assumptions are reasonable because capabilities of today's handheld node are stronger and are also used commonly in some studies [18].
3.3. Problem Statement
In mobile social networks, selfish behaviors of node pose great challenges for data forwarding. Both social selfishness and individual selfishness have impacts on routing decision. SSAR [13] allows social selfishness and improves performance by considering user willingness and contact probability when selecting the relay nodes. User willingness is used to calculate its forwarding capability. However, user willingness is only quantified by the social relations among nodes. It does not reflect the real willingness of nodes, which should consider the individual altruism. The IA should be taken into account to evaluate relaying capability, combining with social altruism SA.
On the other hand, incentive is an effective method to stimulate selfish nodes to cooperate with each other. The existing incentive methods such as reputation-based and credit-based need infrastructure (e.g., trust authority or virtual bank), which is not scalable and requires higher investment. In our opinions, when two nodes i and j meet each other, the reason node i relaying packets for node j is how much services that node j provided for it or for the network. More services mean more contributions. In the rest of this paper, service and contribution are used interchangeably. The more services (or contributions) node j provides, the more probability node i relays packets for it. It sounds like TFT-based method. Different from TFT-based method, the services the node provides include pairwise services and social services, which are the services provided for the whole network. For any two given nodes, when they serve each other, they make pairwise services. Traditional TFT-based method just considers pairwise contributions when relaying packets, but it is unfair to those who serve more for other nodes. For example, node j has relayed many packets from other nodes except node i; then node i will refuse to relay packets from node j according to pairwise principle. So, the social services also should be considered to make forwarding decision. Moreover, the pairwise services of traditional TFT method are evaluated by the amount of data exchanged between two nodes. But in social selfish network, user selfishness to forwarding packets is different from each other. To stimulate the node with lower altruism to be cooperative, it should get more rewards if it relays packets from others. The lower the altruism, the more the rewards. For those with higher altruism, especially social altruism, they will get less reward than those with lower altruism. Because they have stronger social relations among the network, they have more chance to serve for other nodes and get enough rewards. So, the services of the node should be calculated based on its altruism.
4. Detailed Design
In this section, we present the details of SSR protocol. At first, we define some notations to make the presentation clear: ψ: the set of nodes that node i provides forwarding service.
4.1. Altruism to Forwarding
In selfish mobile social network, the altruism of the node to relaying packets for other nodes is essential to make routing decision. The altruism is determined by the social altruism and the individual altruism. Social altruism depends on the social relations among nodes. The stronger the social altruism between two nodes is, the larger the probability the two nodes encounter and the more the willingness to provide forwarding services for each other is. Then a node should forward packets to the relay node with higher social altruism for the destination node. However, the capability of relaying packets is also constrained by the individual altruism. If the individual selfishness of a node is lower, it will be reluctant to relay packets though it has stronger social relations with destination node. For example, a node has high social altruism to forwarding packets for the destination node, but its energy of battery is not enough to support, to provide forwarding service. And it has to refuse to relay packet due to the large individual altruism. The altruism of node i to relay packet to node j is
When a node encounters several nodes, it will choose the nodes with higher altruism to relay packets to the destination node as the next hop.
4.2. Incentive Schemes
To stimulate selfish node to behave more unselfish, incentives are effective method. Intuitively, the more service the node provides, the more contributions it makes and the more rewards it should achieve. The rewards that the node gets are proportional to the amount of its service. For simplicity, let the rewards be the amount of service that the node provides. Usually, when a node relays one packet from other node, it provides 1 unit service for the other node. But in socially selfish network, the node that has small social strength to forward packet should get more incentives if it provides forwarding services successfully in order to stimulate it to be more cooperative. Define the amount of service that node i provides after it relays a packet from node j as
If node i relays a packet from node j, then node i provides
4.3. Contribution Index
To indicate which one serves more than the other for a pair of nodes, define
However, the services a node provides are not only for a given node; it will relay packets for all the nodes in the network if possible. On the other side, node i also consumes services provided by the nodes. Define
And let the serving index of node i for the network be
Then we design a contribution index for node i to evaluate the forwarding capability to node j as
Contribution index has twofold implications:
Contribution index is used to evaluate the capability to relay packets. It is natural that the node with smaller contribution index is the preferred candidate for providing relay service. The node with smaller contribution index has to provide service for others so that it could get more rewards to increase its contribution index.
4.4. Packet Forwarding
Packets forwarding in SSR is based on the altruism to relay packets for the destination and the contribution index of the relay nodes. The node with higher altruism and smaller contribution index will be the candidate for relaying packet. The pseudocode of packet forwarding carried out by each node is presented in Algorithm 1.
(1) (2) Broadcast destinations of packets in the buffer (3) Get summary vectors from neighbors (4) (5) buffer of node i (6) (7) calculate (8) (9) (10) (11) (12) choose node j, with the highest (13) send packets that destination is node k to node j (14) (15)
When node i encounters some neighbors, it firstly broadcasts the information of the packets such as the destination of the packets. The neighbor j computes its willingness to relay the packet to the destination node k, that is,
5. Performance Evaluation
In this section, we evaluate the performance of the proposed SSR protocol using a Java based simulator. For comparison, we also implement SSAR [13] and SimBet [8] protocols.
5.1. Simulation Setups
The simulation is based on two real traces referred to as Infocom’05 [4] and Infocom’06 [5]. In these traces, there were 41 and 78 participants carrying small devices to log contacts of the mobile devices for 3 days in Conference Infocom 2005 and 2006, respectively. Infocom’05 trace logs more than 20 thousand contacts with each other and average contacts for two given nodes are about 4.5 per day and Infocom’06 trace logs about 190 thousand contacts with 6.5 average contacts per pair per day. Each contact includes the two contact entities, the begin-time, and the end-time. We use the contacts to perform trace-driven simulations. In simulation, we assume that if any two nodes have contact history, they have social relation with each other. The more they contact, the stronger social relation is and the higher social altruism could be.
In the simulation, each node generates 2 packets per hour and selects a destination node randomly. The packet has a certain TTL. Once TTL expires, the packet will be dropped. To demonstrate the impact of individual willingness caused by the limited energy, we design a simple scheme for energy consumption, though it is not practical. According to the study of [19], a typical handheld node (i.e., smart phone) usually exhausts its energy in 21 hours if it is in regular usage pattern (i.e., calling and messaging). We assume the energy decreases linearly with a loss rate 1 mAh per minute and it will consume 0.01 mAh when sending or receiving the packet. The initial energy of node is randomly selected from 1200 to 1600 mAh. The threshold
5.2. Simulation Results
For fair comparison, we extend SSAR and SimBet with individual altruism IA. For SSAR, when calculating packet priority, it should be multiplied by IA. For SimBet, the node should relay the packet with the probability of IA.
Firstly, we investigate the impact of individual altruism determined by the residual energy of node on data delivery ratio. We assign each node with an initial energy randomly selected from 1200, 1300, 1400, 1500, and 1600 mAh and each node consumes 1 mAh per minute. When the energy of the nodes is less than

The impact of individual altruism caused by the residual energy.
As seen from Figure 1, data delivery ratio of all algorithms increases first and then decreases when it reaches a certain value. This is because more and more energy consumption leads to lower individual altruism, decreasing the probability to relay packets. Moreover, SSAR outperforms SSR at the beginning. After a period of time, the delivery ratio of SSAR drops more quickly than that of SSR. The reason is that when the energy of node is high, the nodes in SSAR relay packets with high probability and deliver more packets. As time elapses, the residual energy is lower and lower, and the probability to relay packets decreases. When the residual energy is less than
Figure 2 shows the percentage of nodes providing relaying services to other nodes. The percentage of relay node increases because there are more and more nodes participating in packets relaying. More nodes in SSR join in forwarding for the incentives stimulate nodes to be more cooperative and the node with less contribution has to relay packets so that its packets could be relayed by other nodes. On the other hand, the nodes with larger social altruism (stronger social relation for SSAR or higher centrality for SimBet) are the preferred next hop to relay packets and the nodes with weak social relations or lower centrality are not easy to be a relay node. That is to say, the incentive scheme of SSR is effective to stimulate the node to be more cooperative.
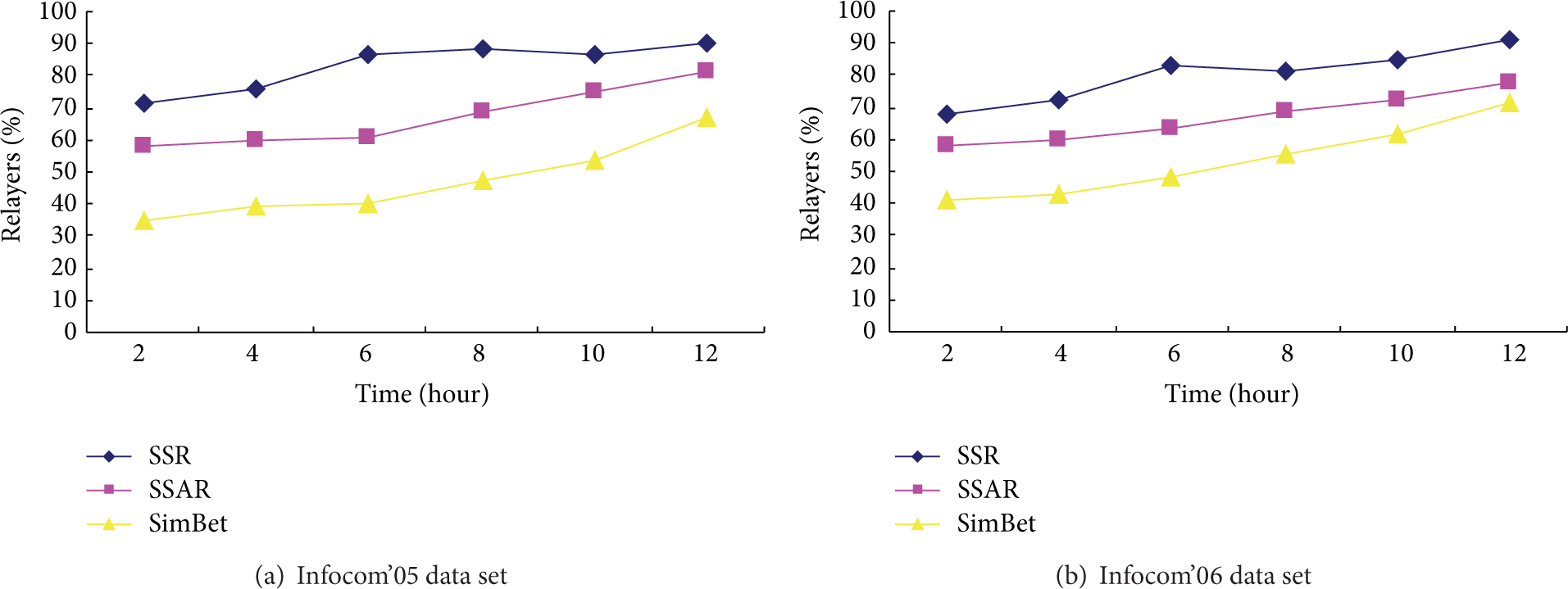
The percentage of nodes participating relaying service.
6. Conclusions
In this paper, we have proposed a service-based data forwarding scheme. Firstly, we classify user altruism to relay packets into social altruism and individual altruism. Then we introduce service-based incentive scheme, in which the contributions the node makes are considered as the incentives to the node. The service consists of pairwise service between two given nodes and social service for the entire system. Making forwarding decision is based on the altruism to forwarding the packets and the contributions of the relay node. The node with higher altruism and lower contributions is a preferred candidate for packet relaying. Simulation results show that SSR performs better than SSAR and SimBet when the altruism of node is low and demonstrate the effectiveness of incentive scheme of SSR.
Footnotes
Conflict of Interests
The authors declare that they have no conflict of interests about the paper.
Acknowledgments
This work is supported in part by National Science and Technology Support Program of China (2012BAI22B05), National Science Foundation of China under Grants nos. 61103226, 61103227, 61170256, 61173172, and 61370151, and the Fundamental Research Funds for the Central Universities under Grant no. ZYGX2013J067.