Abstract
With the rapid development in wireless communications and cloud computing technologies, clients (users) often use handheld mobile devices to access remote servers via open network channels. To provide authentication and confidentiality between clients and servers, a large number of ID-based authentication and key exchange (ID-AKE) protocols have been proposed for mobile client-server environments. However, most of the existing ID-AKE protocols adopt the precomputation technique so that they become vulnerable to the ephemeral-secret-leakage (ESL) attacks, in the sense that an adversary could use the ephemeral secrets to reveal the private keys of clients from the corresponding exchange messages. In the paper, we propose a new ESL-secure ID-AKE protocol for mobile client-server environments. We formally prove that the proposed protocol satisfies the security requirements of both mutual authentication and key exchange while resisting the ESL attacks. When compared with previously proposed ID-AKE protocols, our protocol has higher security and retains computational performance, since it requires no bilinear pairing operation for mobile clients. Finally, we mention the possibility of adopting our protocol as an authentication method of the extensible authentication protocol (EAP) for wireless networks.
1. Introduction
A key exchange protocol allows two parties to construct a session key. A symmetric encryption scheme with the session key is used to achieve confidentiality between the two parties. However, key exchange protocols without authentication are not secure against impersonation and intruder-in-the-middle attacks. An authentication and key exchange (AKE) protocol is a key exchange protocol under which the established session key of two parties remains secret to other parties. Several famous AKE protocols [1–3] based on the traditional public-key systems [4, 5] have been proposed to provide confidentiality and mutual authentication.
In 1985, Shamir [6] proposed an identity- (ID-) based public-key system that eliminates the certificate management in conventional public-key systems. In an ID-based public-key system, a user's public key is derived from the user's identity information, such as name, social security number, and e-mail address. However, Shamir's system is not practical. In 2001, Boneh and Franklin [7] followed Shamir's idea to propose a practical ID-based encryption scheme based on the Weil pairing. Afterwards, the ID-based cryptography received significant attention. A large number of ID-based cryptographic schemes and protocols have appeared in the literatures, such as ID-based encryption schemes [8–11], ID-based signature schemes [12–14], ID-based group key exchange protocols [15–18], and ID-based AKE protocols [19–23].
1.1. Motivation
With rapid growth of wireless communications, clients usually employ mobile devices (e.g., smart card) to obtain services from remote servers via open network channels. In a mobile client-server environment, these mobile devices are generally resource-constrained because they possess only low-power energy and limited computing capability. In this case, cryptographic operations with expensive computations would become heavy load for mobile devices. Hence, it is a critical issue to diminish the computational load of mobile devices in AKE or ID-based AKE protocols.
To overcome the resource-constrained situation on the client side, several AKE protocols [24–26] for mobile devices have been proposed for conventional public-key systems. Also, based on Boneh and Franklin's ID-based public-key setting, a number of ID-based AKE protocols for mobile devices [27–33] have been proposed to focus on the computation issue for mobile devices. These protocols above adopted an imbalanced computation technique to reduce the client's computational cost by shifting computational burden to a powerful server.
On the other hand, the offline precomputation technique is employed to lighten the online computational load of mobile devices. In the offline precomputation phase, ephemeral secrets (or random values) are required to generate some values in advance. In the meantime, the ephemeral secrets and these precomputed values are stored in the memory of mobile devices for the usage in the online phase. As a result, a new type of attacks would occur, called ephemeral-secret-leakage (ESL) attacks [34–36], in the sense that an adversary can reveal the private keys of clients from those precomputed values or the corresponding exchange messages if the ephemeral secrets are compromised. To our knowledge, the existing ID-based AKE protocols [27–33] did not address the ESL attacks at all. In the paper, we will construct an ID-based AKE protocol which is resistant to the ESL attacks under mobile client-server environments.
1.2. Related Work
In 2002, Smart [19] proposed the first ID-based AKE (ID-AKE) protocol based on the Weil pairing. However, Shim [20] pointed out that Smart's protocol does not offer forward secrecy. Shim also presented a new ID-AKE protocol with the optimal number of Weil pairing operations. Afterwards, several ID-AKE protocols [21–23] were proposed to improve performance and achieve more security properties. However, the protocols mentioned above require bilinear pairing operations on both ends and are consequently not suited for low-power computing devices.
In 2005, Choi et al. [27] proposed an ID-AKE protocol for mobile client-server environments. They adopted an imbalanced computation technique which shifts the client's computational burden to a powerful server. In 2010, Wu and Tseng [28, 29] also proposed two efficient ID-AKE protocols which do not require any bilinear pairing operations on the client side under mobile client-server environments. Their protocols are proved to be secure against ID attack, impersonation attack, and passive attack and offer mutual authentication, implicit key confirmation, and partial forward secrecy. In 2012, He [30] presented a new ID-AKE protocol to improve the performance of Wu and Tseng's protocol on client side. In addition, Islam and Biswas [31] and He et al. [32], independently, proposed ID-AKE protocols based on elliptic curve cryptography (ECC) without using bilinear pairings. Chuang and Tseng [33] proposed a generalized ID-based AKA protocol for mobile multiserver environments which is suitable for both general users with a long validity period and anonymous users with a short validity period. Chuang and Tseng's protocol is secure against all known attacks and provides forward secrecy. Indeed, all the mentioned ID-AKE protocols [27–33] adopted the precomputation technique to reduce the computational load of the mobile client. In such a case, as mentioned earlier, those ID-AKE protocols would be vulnerable to ESL attacks under mobile client-server environments.
In 2007, LaMacchia et al. [34] presented a strong security model for AKE protocols, which is concerned with the ESL attacks. They proposed a concrete AKE protocol resistant to ESL attacks. In their protocol, the leakage of ephemeral secrets would not damage the security of session keys and private keys of parties. In 2011, Ni et al. [35] proposed a strongly secure ID-AKE protocol which captures all basic security properties including the ESL resistance. Although Ni et al.'s protocol requires six bilinear pairing operations, one can employ the precomputation technique to reduce the computation cost if it knows the identity of the other party in communication beforehand. However, they did not address the scenarios for applications to mobile client-server environments. In 2014, Islam [36] also proposed a provably secure ID-AKE protocol resistant to ESL attack. Islam's protocol still requires two bilinear pairing operations for a client.
1.3. Contribution and Organization
In the paper, we propose a new ID-AKE protocol resistant to ESL attacks in mobile client-server environments, called ESL-secure ID-AKE protocol. In the proposed protocol, we also adopt the techniques of imbalanced computation and offline precomputation to reduce the computational cost required by a mobile client. Indeed, our protocol requires no bilinear pairing for mobile clients. Our protocol employs Tseng et al.'s ESL-secure signature scheme [37] to achieve the client-to-server authentication. Also, the offline precomputation is carried out prior to the execution of our protocol to achieve better performance. As compared with previously proposed protocols, our protocol is secure against the ESL attacks while retaining the computational performance. For security analysis, we first formalize the adversary's capabilities by redefining the adversarial model of ESL-secure ID-AKE protocols in mobile client-server environments. Under the computational Diffie-Hellman (CDH) assumption [7, 12], we demonstrate that our protocol is provably secure in the random oracle model [38, 39]. Finally, we discuss the relationship between our protocol and the extensible authentication protocol (EAP) for wireless networks [40–43]. It turns out that our ESL-secure ID-AKE protocol can be viewed as an authentication method of the EAP framework [40, 41].
The remainder of this paper is organized as follows. In Section 2, mathematical assumptions are presented. An adversarial model of the ESL-secure ID-AKE protocols is presented in Section 3. The proposed ESL-secure ID-AKE protocol is presented in Section 4. In Section 5, we give security analysis of the proposed protocol. Performance comparisons and discussions are given in Section 6. Finally, conclusions are drawn in Section 7.
2. Preliminaries
In this section, we compendiously introduce the concept of bilinear pairings, the related mathematical assumptions, and the notations used throughout this paper.
2.1. Bilinear Pairings
Let bilinearity: for all nondegeneracy: for some computability: given
Note that condition (1) implies that
2.2. Security Assumptions
Let Computational Diffie-Hellman (CDH) problem: given
Definition 1.
The CDH assumption in
2.3. Notations
For convenience, the system parameters, notations, and functions used throughout this paper are defined as follows:
P: a generator of the group s: the system private key s randomly chosen from
3. Adversarial Model
Based on the security models in [34, 35], we present an adversarial model of ESL-secure ID-AKE protocols for mobile client-server environments. In 2007, LaMacchia et al. [34] presented a strong security model of AKE protocols, which addresses the ephemeral-secret-leakage (ESL) attacks. Based on LaMacchia et al.'s model, Ni et al. [35] defined the security model of strongly secure ID-AKE protocols (or named ESL-secure ID-AKE protocols) by adding the key extract query. Their model is a modification of LaMacchia et al.'s model altered from the conventional PKI-based setting to the ID-based setting.
In the following, we first describe an adversary's capabilities of ESL-secure ID-AKE protocols for mobile client-server environments. In our adversarial model, we assume that an adversary
Hash Queries Extract (ID): upon receiving such a query, the oracle Send Reveal Ephemeral-secret-leakage ( Corrupt ( Test (
Here, we present the adversarial model of ESL-secure ID-AKE protocols. The reader is referred to [34–36] for detailed descriptions.
Definition 2 (partnership).
One says that
Definition 3 (freshness).
An oracle no Corrupt query can be issued before the query Send
Definition 4 (ESL-secure ID-AKE security).
An ESL-secure ID-AKE protocol for mobile multiserver environments offers existential unforgeability and possesses the secrecy of session key against adaptive chosen ID attacks if no PPT adversary The adversary Every user is assigned a private key via the key extract phase after the system setup phase accomplishes. No Reveal ( The adversary The adversary
Definition 5 (advantage).
Let Succ denote the event that
Definition 6 (partial forward secrecy).
An ESL-secure ID-AKE protocol
Definition 7 (implicit key authentication).
An ESL-secure ID-AKE protocol provides implicit key authentication if every client is assured that no other clients can learn its session keys with the server.
4. Our Protocol
In this section, we present our concrete ESL-secure ID-AKE protocol for mobile client-server environments. Our protocol consists of three phases, namely, the system setup phase, the key extract phase, and the mutual authentication and key agreement phase.
4.1. System Setup Phase
Our system consists of a powerful server S and some mobile clients. These clients refer to users with handheld devices. A client has access to the server through open channels, such as the Internet or wireless networks. The powerful server S is responsible for generating and distributing private keys to clients while providing services or applications. The server S is also responsible for generating the system parameters.
In the phase, the server S first generates two cyclic groups randomly select a system private key compute the system public key choose six cryptographic hash functions publish public parameters and functions as
4.2. Key Extract Phase
In the key extract phase, a client submits its identity The client submits its identity Upon receiving a client's identity Set

The key extract phase.
4.3. Mutual Authentication and Key Exchange Phase
Suppose that a client with identity The client with identity
Random select an ephemeral secret Compute Compute Send Upon receiving
Compute Check whether the equality Acquire a nonce N. Compute Finally, send Upon receiving
Compute Check whether the equality Compute Compute a session key The client sends Upon receiving
Check whether the equality Compute a session key
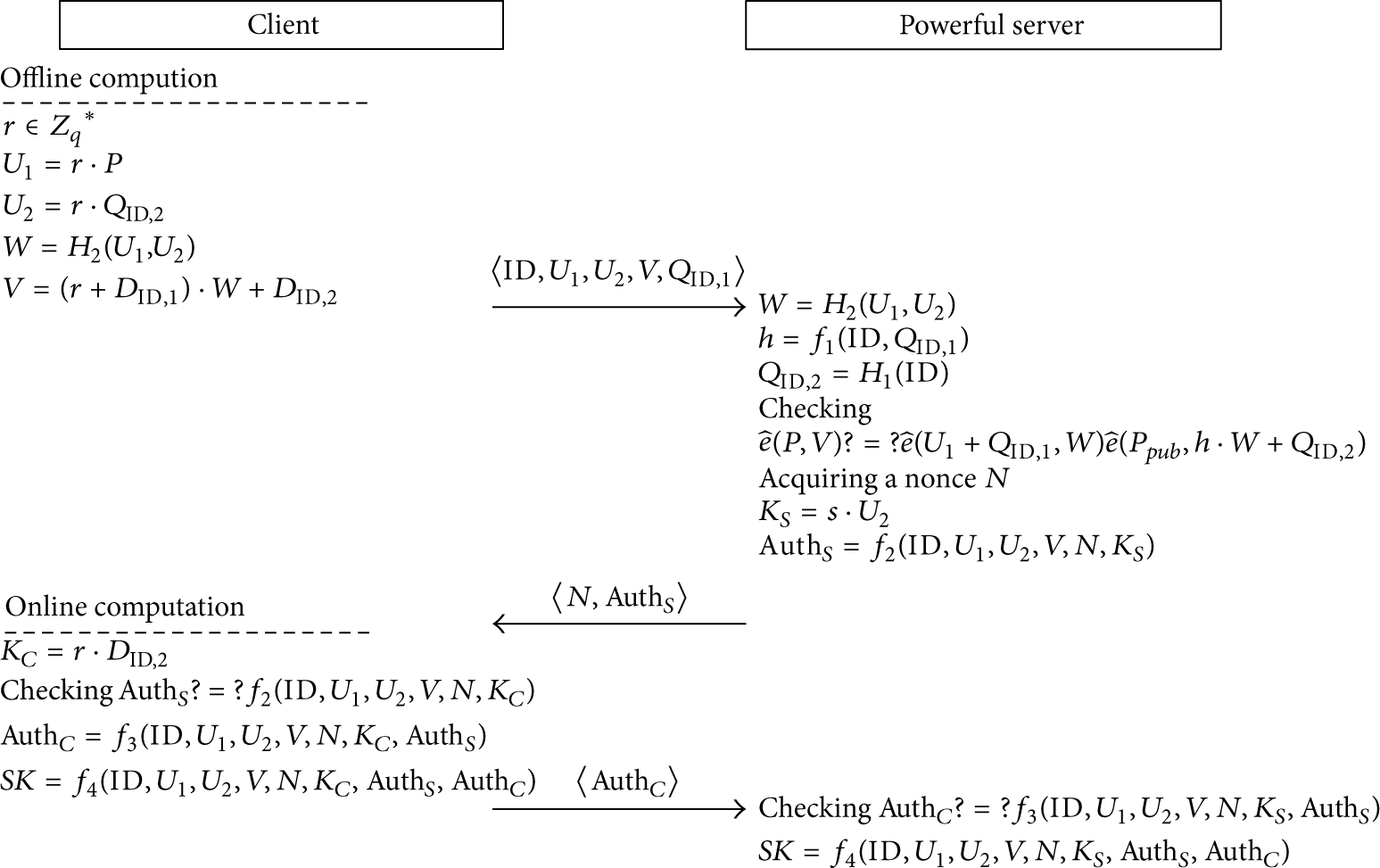
The mutual authentication and key exchange phase.
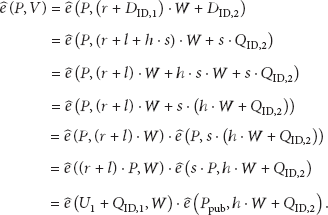
In the following, we present the correctness of the equality in Step (2)(b):
On the other hand, we have
5. Security Analysis
In this section, we present the security analysis of our proposed protocol in the random oracle model [38, 39]. In the following, five theorems are given to prove that the proposed protocol achieves the security requirements of ESL-secure ID-AKE protocols for mobile client-server environments. These security requirements include client-to-server authentication, server-to-client authentication, key agreement, implicit key confirmation, and partial forward secrecy. In Theorems 8 and 10, we show that the proposed protocol provides the client-to-server and server-to-client authentications under ID, impersonation, and ephemeral-secret-leakage attacks, respectively. Hence, the proposed protocol offers mutual authentication. In Theorem 9, we will show that the proposed protocol provides secure key agreement under known-session-key attacks. Furthermore, the implicit key confirmation and partial forward secrecy are achieved by Theorems 11 and 12, respectively.
5.1. Client-to-Server Authentication
First, we prove that an adversary cannot impersonate a legitimate client to communicate with the server under the CDH assumption. We establish this by the methods similar to those in [24, 28], in which a Simulation
Theorem 8.
Assume that a probabilistic polynomial-time (PPT) adversary
Proof.
We assume that there is a probabilistic polynomial-time algorithm
Next, we would like to construct an algorithm Initialization: at first, Simulation Extract (ID); upon receiving such a query and Ephemeral-secret-leakage ( Send queries: there are four cases.
When When Upon receiving the Send When
By the responses to those queries above,
5.2. Key Agreement
In the following, we prove that the proposed protocol provides key agreement under the CDH assumption. Simulation
Theorem 9.
Assume that a PPT adversary
Proof.
Firstly, we know that the adversary
Without loss of generality, we denote by the symbols Test
In the following simulation, we employ the algorithm Initialization: at first, Extract (ID): it is the same as in the proof of Theorem 8. Reveal ( Ephemeral-secret-leakage ( Corrupt ( Test (
In the simulation above, Simulation
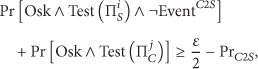
Note that, if ε is nonnegligible, the probability
5.3. Server-to-Client Authentication
In the following theorem, we prove that an adversary cannot impersonate the server S to communicate with the client C under the CDH assumption.
Theorem 10.
If a PPT adversary
Proof.
Here, we employ an algorithm
Let the symbol
Case 1. The adversary
Case 2. The values
Case 3.
Next, we discuss the probability for each of the three cases. It is obvious that the probability of Case 1 is less than
Hence, by assuming that
5.4. Implicit Key Confirmation
Theorem 11.
Under the CDH assumption, our proposed protocol offers implicit key confirmation in the random oracle model.
Proof.
We say that an ID-AKE protocol provides implicit key confirmation if the protocol assures that the server/client can compute a session key which no others can produce. By Theorems 8 and 10, the client and the server can authenticate each other in the random oracle model under the CDH assumption. In Theorem 9, we have proved that an adversary cannot compute the session key. Therefore, our proposed protocol provides implicit key confirmation.
5.5. Partial Forward Secrecy
Theorem 12.
Under the CDH assumption, our proposed protocol offers partial forward secrecy in the random oracle model.
Proof.
If the adversary
6. Performance Comparisons and Discussions
For convenience, the following notations are used to analyze the performance:
By the simulation results in [44, 45],
Computational costs (in seconds) required for pairing-based operations.

In the following, we analyze the computational cost of the proposed protocol. In our protocol, the client side requires
In Table 2, we demonstrate the comparisons among Ni et al.'s protocol [35], Chuang and Tseng's protocol [33], Islam's protocol [36], and ours in terms of the computational cost, communicational cost, and ESL security. As mentioned in Section 1, both the proposed protocols of Ni et al. and Islam fulfill all basic security properties including ESL resistance, while Chuang and Tseng's protocol cannot withstand ESL attacks. In Section 5, we have demonstrated that our protocol also fulfills all basic security properties including ESL resistance. Moreover, Chuang and Tseng's protocol and ours only require
Comparisons between some recently proposed protocols and ours.

In the following, let us discuss the relationship between our protocol and the extensible authentication protocol (EAP) for wireless networks [40–43]. Typically, the EAP standard or framework [40, 41] is viewed as an authentication framework independent of the underlying authentication technology. Under the EAP framework, many authentication protocols have been proposed, and each of them has various advantages and weaknesses. As in [42], our ESL-secure ID-AKE protocol might be viewed as an authentication method of the EAP framework, without relying on PKI (public key infrastructure). In such a case, there is no need for the management of certificates and the deployment of certification authority (CA).
Most EAP authentication protocols lack identity protection or user anonymity. In this paper, we focus on optimizing the authentication process but do not address the issue of user anonymity. Indeed, as mentioned in Section 1.2, Chuang and Tseng's ID-AKA protocol [33] is suitable for general users (with a long validity period) and anonymous users (with a short validity period) as well. Generally, ID-based or certificate-based authentication protocols must rely on other techniques (e.g., Universal Subscriber Identity Module of cellular networks) to provide user anonymity [42]. In addition, the reader can refer to [43] for the privacy protection issue of authentication protocols in the EAP framework.
7. Conclusions
In the paper, we proposed an efficient ESL-secure ID-AKE protocol for mobile client-server environments. Under the CDH assumption, our protocol is provably secure to provide mutual authentication, key agreement, implicit key confirmation, partial forward secrecy, and resistance to the ESL attacks in the random oracle model. We adopt the imbalanced computation to reduce the computational cost required by a mobile client. In addition, a mobile client may perform offline precomputation to reduce the online computational cost. When compared with previously proposed ID-AKE protocols for mobile client-server environments, our protocol has higher security and better computational performance.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
This research was partially supported by the Ministry of Science and Technology, Taiwan, under Contract no. MOST103-2221-E-018-022-MY2.