Abstract
Information security has been received more and more attention for next-generation wireless sensor networks. In this paper, we consider the problem of resource management based on security satisfaction ratio with fairness-aware in two-way relay networks. Multiple source nodes exchange information with the help of relay node in the presence of an eavesdropper, and diverse security requirements are taken into account with coexistence of security users and normal users. The joint problem of power allocation, and subchannel pairing and allocation aims to maximize the security satisfaction ratio for legitimate users subject to limited power and subchannel constraints. We model the security resource management problem as a mixed integer programming problem, which is decomposed into three subproblems, distributed power allocation, distributed subchannel allocation, and distributed subchannel pairing, and then solved it in constraint particle swarm optimization (CPSO), binary CPSO (B_CPSO), and classic Hungarian algorithm (CHA) method, respectively. Moreover, a suboptimal subchannel pairing algorithm is proposed to reduce the computational complexity compared with the CHA. Simulations are conducted to evaluate the effectiveness of the proposed algorithms.
1. Introduction
1.1. Background
Small cell (such as relay and femtocell) is a promising technology in fifth generation (5G) mobile communications [1]. Classical one-way relay channel consists of one sender, one receiver, and one assisting relay. Recently, there has been increasing attention from the research community paid to studying the two-way (bidirectional) relay channel, where two senders exchange information via one assisting relay at the same time. Compared with the traditional one-way relay, two-way relay provides improved spectral/power efficiency for information exchange between two source nodes [2, 3]. Therefore, the research of two-way relay has received much interest in recent years. The basic idea of two-way relay is to exchange information through one or more assisting relay nodes (RNs) based on the idea of network coding. The relay can be categorized into the following two types depending on its forwarding protocol [4]: (1) amplify and forward (AF): RN receives signal from source node and then amplifies the signal and forwards it to the terminal node. AF relays are beneficial due to their simpleness and short delays; (2) Decode and forward (DF): DF relays receive and encode useful signal and then forward a new signal. Such relays are beneficial in interference-limited systems because this type of relays does not amplify noise and interference. Recently, information security has drawn much more attention due to broadcast feature of wireless channels [5, 6], and two-way relay is more vulnerable to eavesdropping due to its transfer character. Therefore, more and more scholars study how to improve the security of two-way relay.
1.2. Related Works
Recently, there are a few literatures focusing on the two-way relay security. In [7], the authors consider the case where the transmit messages and the feedback signals are subject to eavesdropping in two-way relay networks, and the question of how much the feedback signal impacts the secrecy capacity is investigated by studying two fundamental models. In [8], the authors study the bidirectional broadcast channel with confidential messages, and the simulations show that a strong secrecy capacity region is established in two-way relay networks. In [9], secrecy capacity is analyzed in a Gaussian two-way relay wiretap channel, and a jamming strategy is introduced to maximize the achievable secrecy rate regions. In [10], the security of the three-phase two-way relaying system with an eavesdropper is investigated. A cooperative jamming and power allocation scheme is proposed to enhance the system secrecy capacity. In [11], the authors study the secrecy capacity maximization based on power allocation in DF two-way relay systems with the presence of an eavesdropper. But the water-filling-like power allocation [12] is too complex for small cell as relay to complete. These literatures improve the relay security in a certain extent, and secrecy capacity as security model is widely used. However, to the best of our knowledge, users’ responses to information security in two-way relay networks has not been studied in the current literatures. As we know, secrecy capacity is just an objective measurement of information security, which cannot well reflect the users’ actual feelings to information security. Therefore, new security evaluation criteria from the perspective of users should be studied in two-way relay networks.
1.3. Our Contribution
In this paper, we present a novel problem of resource management based on security satisfaction ratio with fairness-aware in two-way relay networks. Our contribution can be summarized as follows: (1) we introduce a novel security satisfaction ratio model, which is utilized as objection function to analyse the information security problem through resource optimization. Compared with secrecy capacity, security satisfaction ratio can well reflect the users’ actual feelings to security. (2) Diverse information security requirements are considered for different legitimate users in this paper. Furthermore, the fairness of users is also guaranteed. (3) Constrained particle swarm optimization (CPSO) algorithm, binary CPSO (B_CPSO) algorithm, and classic Hungarian algorithm (CHA) are jointed to solve this security resource optimization problem. (4) A suboptimal subchannel pairing algorithm is proposed to reduce the computational complexity of subchannel pairing compared with CHA. Performance of the proposed algorithms is verified by simulations.
1.4. Organization
The remainder of this paper is structured as follows. The system model and target problem are presented in Section 2. Section 3 provides the joint resource allocation based on security satisfaction ratio with fairness-aware (JRASSFA) algorithm. Performance of the proposed algorithms is described in Section 4. Finally, Section 5 gives the conclusions.
2. System Model
2.1. System Model
A two-way relay OFDMA system consists of one RN, K pairs of mobile users (PMUs), and one eavesdropper (E) in this paper. As shown in Figure 1, PMUs transmit information with the help of a RN, while eavesdropper tries to eavesdrop the exchange information of PMUs. In this scenario, legal users attempt to acquire maximum security information. The relay node works in a half-duplex mode and uses AF protocol. The process of AF two-way relay transmission is divided into two phases: multiple access phase (MA) and broadcast (BC) phase. In MA phase, PMUs transmit signals to RN synchronously and then RN amplifies the received signals and broadcasts them to PMUs in BC phase. In order to avoid interuser interference, each subchannel can only be occupied by no more than one PMU. We set B as the bandwidth of each subchannel and N is the number of subchannels. PMU k consists of

Security transmission model.
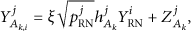
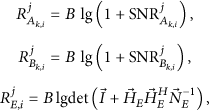
We assume that subchannel i is allocated to
We denote the received signal of eavesdropper E in the MA phase by
In the BC phase, we denote the received signal at
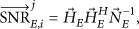
We assume that each PMU has perfect capability of self-interference cancelation in the BC phase. Based on (1), (3), and (4), the SNRs (signal-noise ratios) of
The composite received signal in MA and BC phases at eavesdropper E can be given by
The SNR of the eavesdropper can be written as follows:
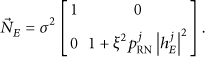
Based on Shannon capacity formula, the capacities of users
Definition 1 (secrecy capacity).
It is the capacity difference between the legitimate information exchange between the terminals and the information leakage to the eavesdropper.
Then the secrecy capacity for a PMU (
2.2. Secrecy Ratio and Security Satisfaction Ratio
Secrecy ratio reflects the users’ security extent, which means that users can get higher information security guarantee under higher secrecy ratio.
Definition 2 (secrecy ratio).
Secrecy capacity accounts for the proportion of the total capacity. It can be described as follows:
Definition 3 (security satisfaction ratio).
It is defined as the users’ satisfaction extent to their own information security in the process of transmission.
In two-way relay security OFDMA system, information security is threatening each user. Thus, we need to find a criterion to evaluate the information security extent from the perspective of users, and the security satisfaction ratio (SSR) of users is a good criterion to evaluate users’ information security extent. In this paper, secrecy ratio (
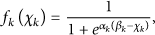
Sigmoid function is one of the monotone functions which satisfy the above characteristics [13–15], and it has been widely used to solve the resource allocation problem in wireless networks. In [13, 15], Sigmoid function based noncooperative access control algorithm is proposed in CDMA and IEEE 802.11e networks, respectively. The Sigmoid function is defined as follows [14]:
Thus, the SSR function of PMU k is defined as follows based on Sigmoid function:

SSR function of users.
2.3. User Type and Fairness Model
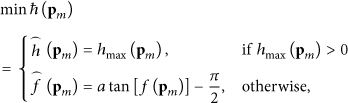
Diverse security requirements are taken into account with coexistence of security users and normal users in this two-way relay system. In this paper, users are divided into three types: VIP (very important person), IP (important person), and NP (normal person). In order to guarantee the security requirement for different users, security tolerability is defined as follows:
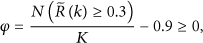
Fairness is also important in wireless communication systems since all users expect to have better experience whether they are VIPs or not. Plenty of data transmission rate is the assurance of communication quality, especially for NPs, who focus on transmission rate more than information security. Therefore, we should not only pursue SSR maximization, but also consider the users’ capacity requirement. In [16], the authors assess the user's capacity by the normalized cumulative distribution function (CDF), which is widely used in 3GPP2 and IEEE802.16j. Therefore, in this paper, we use CDF as fairness index to assess the fairness of system. The normalized capacity
The fairness criterion can be given by
2.4. Problem Formulation
In this subsection, a subchannel assignment variable and a subchannel pairing variable are defined by
We consider a two-way relay network with K PMUs and N subchannels. Hence, the total security satisfaction ratio U of PMUs can be defined as
3. JRASSFA Scheduling Algorithm
JRASSFA scheduling algorithm consists of three subalgorithms: powering allocation based on CPSO algorithm, subchannel allocation based on B_CPSO algorithm, and subchannel pairing algorithm. These three subalgorithms are joint to optimize (21), aiming to maximize the SSR by appropriate power allocation, subchannel allocation, and subchannel pairing. Moreover, in this section, two subchannel pairing algorithms are presented: CHA algorithm and suboptimal subchannel pairing algorithm.
3.1. Powering Allocation Based on CPSO Algorithm
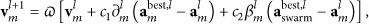
In this section, we first introduce particle swarm optimization (PSO) algorithm. PSO is a swarm intelligence algorithm that models social behavior to guide swarms of particles towards the most promising regions of the search space and has been proved to be efficient in solving engineering problems. The basic idea of PSO algorithm is to find an optimal solution by sharing information among individuals in the group. The standard form for PSO can be given in [17]
In 2010, Kim et al. proposed a simple and efficient constrained PSO (CPSO) for engineering optimization problems containing various constraints and mixed integer-discrete-continuous type of design variables [18]. CPSO is constrained PSO algorithm which is used to solve the problem subject to constrained conditions. In this paper, we will use CPSO algorithm to solve our power allocation problem in the case of given
Next, we will rewrite (23) according to power allocation variable
In order to understand easily, Figure 3 shows the search process under CPSO, which could be described as follows: in the initial stages of iteration, all the particles in nonfeasible region are trying to move to a feasible region which satisfy the constraint conditions and then find the optimal solution which is satisfied with both the objective function and the constraint conditions in the feasible region.

Change graph of objective function.
The brief power allocation algorithm is given in Algorithm 1.
(1) (2) (3) Denote the particle swarm as respectively initialized as for each particle, where (4) Initialize subchannel assignment variable and subchannel pairing variable (5) Initialize each personal optima (6) Initialize global optima (7) (8) while (9) Update (10) for (11) if (12) then (13) end for (14) (15) if (16) then (17) end while (18) (19) Output the best position
3.2. Subchannel Allocation Based on B_CPSO Algorithm
Because the value of subchannel assignment variable
First we rewrite velocity part of (23) according to subchannel allocation variable
(1) (2) (3) Denote the particle swarm as respectively initialized as (4) Initialize subchannel assignment variable and power allocation variable (5) Initialize each personal optima (6) Initialize global optima (7) (8) while (9) Update (10) for (11) if (12) then (13) end for (14) (15) if (16) then (17) end while (18) (19) Output the best position
3.3. Subchannel Pairing Based on CHA Algorithm
The remaining problem is the subchannel pairing, which can be formulated as
3.4. Suboptimal Subchannel Pairing Algorithm
The previous subsection presents a subchannel pairing algorithm based on CHA, the complexity of which may will be high with large values of K and N. In this subsection, we propose a suboptimal subchannel algorithm to reduce the computational complexity by decomposing the subchannel pairing into two phases: MA phase and BC phase.
Subchannel pairing for given power allocation and subchannel allocation: subchannel pairing for PMU k in the MA phase is in accordance with
In the BC phase, subchannel j can be selected as
4. Simulation Result
We consider one relay with multiusers and one eavesdropper in this simulation. The legitimate users are uniformly located on a circle centered at the RN and with radius of 50 meters. The eavesdropper is assumed to locate at a distance of

Average SSR versus distance.
4.1. Average SSR versus Eavesdropper Distance
Figure 4 illustrates the average SSR of JRASSFA using CHA (JRASSFA_C), JRASSFA using suboptimal subchannel pairing (JRASSFA_S), and equal power allocation (EPA) [22] algorithms for different security preference parameters, assuming that the eavesdropper exists between 100 m and 450 m from the RN. We can see that the average SSR of PMUs increases when the eavesdropper is far away from the RN, particularly when the eavesdropper is far away from relay node at a distance within 250 m. There are two reasons that can explain this result: (1) the farther the distance between eavesdroppers and relay nodes, the worse the SINR eavesdropper received and thus the less the communication information the eavesdropper eavesdrop, so the security satisfaction ratio of users increases; (2) the path loss is a major factor deteriorating the received signal of the eavesdropper within 250 m in the simulation, so the average SSR of PMUs increases rapidly at a distance within 250 m. Moreover, smaller
4.2. Secrecy Ratio versus Individual PMU
Figure 5 shows the effectiveness of our proposed algorithm in security requirement guarantee in the case of

Secrecy ratio versus PMU k.
4.3. CDF versus Normalized Capacity
Figure 6 shows the fairness performance of JRASSFA_C, JRASSFA_S, and proportional fair (PF) algorithm [23]. From this simulation, we can find that the ratio of PMUs whose normalized capacity is larger than 0.3 is

CDF versus normalized capacity.
4.4. Average SSR versus Total Transmit Power of RN
Figure 7 shows the better performance of the proposed JRASSFA_C and JRASSFA_S in terms of the average SSR versus
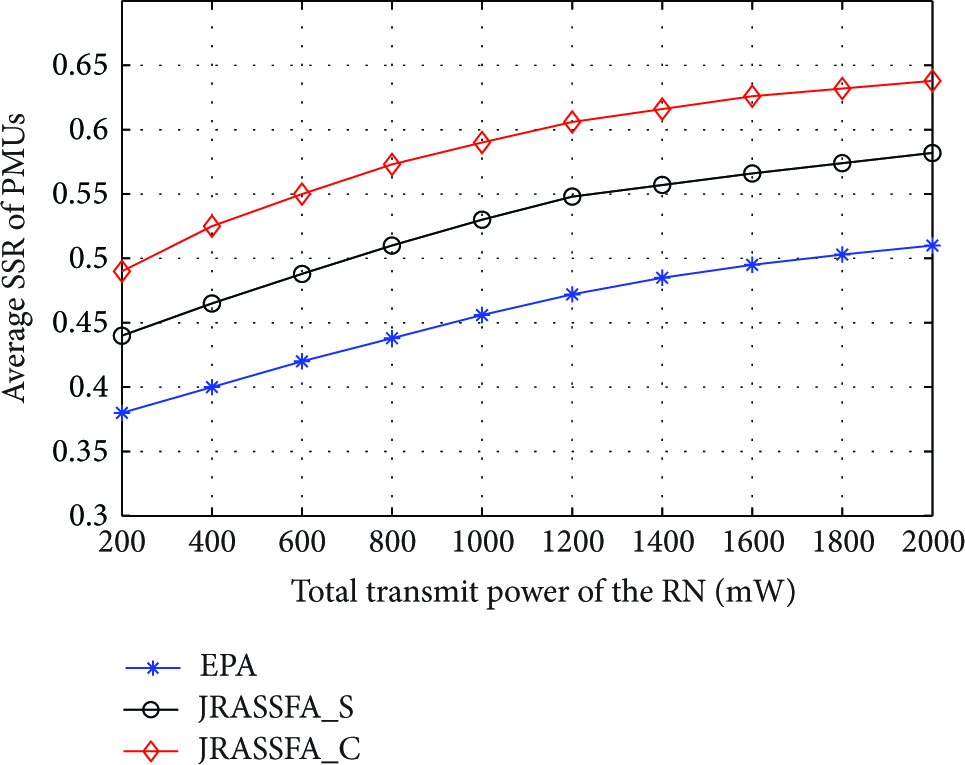
Average SSR versus total transmit power of RN.
4.5. Average SSR versus Total Transmit Power of User
Figure 8 depicts the average SSR versus the total transmit power of user and we can see that the SSR increases with the increased transmit power of user. The reason for this result is that the increased transmit power of user leads to larger SNR than eavesdropper. Thus it will cause increase in the SSR. Moreover, our proposed JRASSFA_C and JRASSFA_S provide the better performance compared to the EPA algorithm. Still, the JRASSFA_C outperforms the JRASSFA_S. However, we can get a tradeoff between algorithm complexity and SSR performance due to the fact that the JRASSFA_S has lower complexity.

Average SSR versus total transmit power of user.
5. Conclusions
In this paper, we have investigated the joint resource management for orthogonal frequency division multiple access (OFDMA) security two-way relay networks in next-generation wireless sensor networks. A novel security satisfaction ratio model is introduced as the objection function to evaluate the information security of users. Meanwhile, in order to guarantee diverse information security requirements and fairness for different users, secrecy ratio and CDF are also presented in this paper. We model this security resource optimization problem as a mixed integer programming problem and then solve it in constraint particle swarm optimization (CPSO), binary CPSO (B_CPSO), and classic Hungarian algorithm (CHA) method, respectively. Moreover, a suboptimal subchannel pairing algorithm is presented to reduce the computational complexity of subchannel pairing CHA algorithm.
Simulation results indicate that JRASSFA_C and JRASSFA_S provide better security performance than the other two algorithms. However, a number of open problems still remain. Indeed, the expected value of secrecy ratio is different among different users, but in this paper we only consider the same expected value among different users in order to simplify the analysis. In addition, how to improve the secrecy ratio in order to satisfy users’ security tolerability and, furthermore, to avoid the interruption of transmission under the total power constraint should be further studied in the future.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This research is supported by the 863 Project no. 2014AA01A701, the Three Links and Two Platforms of Beijing Education Network and Information Center, and the WLAN Schievement Transformation Based on SDN of Beijing Municipal Commission of Science and Technology, National Natural Science Foundation of China (61271179, 61101109).