Abstract
Wireless sensor networks (WSNs) provide network services through the cooperation of sensor nodes, while the basis of cooperation depends on the trust relationships among the nodes. In this paper, we construct an evolutionary game-based trust strategy model among the nodes in WSNs, and we subsequently introduce a strategy adjustment mechanism into the process of game evolution to make up for the deficiency that the replicator dynamic model cannot reflect the requirement of individual strategy adjustments. Afterward, we derive theorems and inferences in terms of the evolutionary stable state through dynamic analyses, providing a theoretical basis for WSN trust management. Furthermore, we verify the theorems and inferences with different parameter values, especially the trust incentive and the upper limit of data retransmission after packets are lost, and both of them are closely related to the evolutionary stable state. The experiments demonstrated that, under certain conditions, the involved nodes can finally reach a stable state of the system by constantly adjusting their trust strategy. At the same time, the speed of evolution of our strategy adjustment mechanism in achieving the stable state is much faster than that of the usual replicator dynamic evolution method.
1. Introduction
Recently, WSNs have developed from a promising research area to a useful technology that is applicable to real-world scenarios. Akyildiz et al. [1] have classified the applications of WSNs as military applications, environmental applications, health applications, home applications, and other commercial applications. In the near future, WSNs that are comprised of small-size, low-power sensor nodes will become an integral part of our lives.
Similar to any computer-related environment, security in WSNs is considered to be nonfunctional but an essential requirement that keeps the complex system available and reliable [2]. In recent years, in addition to the traditional cryptography-based network security technology, trust-based security mechanisms have gradually attracted more attention from academia and industry. The concept of
Game theory as a mathematical theory tool focuses mainly on the competitive and cooperative relationship of the participants, and it has been widely used in the field of WSN security. In [8], Shen et al. summarized the current research of different types of games in WSN security. Among various methods of game theory, the evolution game takes the changing trend of the overall population as the research object, where sensor nodes of WSNs are viewed as an individual, and all of the sensor nodes are an overall population. After the continuous evolution of a population, a trust management system guides the individual nodes to make trust decisions that maximize their utilities, and the rate of individuals who choose the strategy that has a higher gain will increase. Conversely, the rate of individuals who choose a strategy that has a lower gain will correspondingly decrease. Thus, the rate of individuals who choose their corresponding strategies remains stable, and the population will finally reach a game equilibrium state. Therefore, it is meaningful for us to study the trust decision model and the evolutionary process of WSNs using evolutionary game theory.
In this paper, we analyze the data retransmission behavior after packets are lost in the communication process of WSNs. Based on this approach, we set up the trust strategy game model, which reflects the gains and losses of the involved nodes. Additionally, we use a new dynamic evolution method that is based on strategy adjustment, to derive and further prove the related theorems and inferences in terms that involve how to use the trust strategy game model for the system to reach a stable state. In the end, we verify the theorems and inferences that are derived following the simulated experiments, and we show the advantage of our dynamic evolution method based on strategy adjustment through a comparison with the usual replicator dynamic evolution method. These research results could provide a theoretic foundation for a trust mechanism in WSNs.
The main contributions of this paper are summarized as follows.
Considering the sensor nodes' data retransmission after packets are lost, we build a trust strategy game model and we introduce a trust incentive mechanism to promote nodes to choose the trust strategy. Accounting for the strategy choice process of individuals, we propose a dynamic evolution method that is based on strategy adjustment and we prove theorems and inferences in terms that involve how to use the trust strategy game model for the system to reach a stable state, through theoretical analyses and experimental verification. The experiments prove that, under certain conditions, the speed of our dynamic evolution method, based on strategy adjustment, reaches a stable state much faster than that of the usual replicator dynamic evolution method.
The remainder of this paper is organized as follows. In Section 2, we overview related research and focus on the difference between our work and other related studies. In Section 3, we set up the trust strategy game model. In Section 4, we propose a new dynamic evolution method that is based on strategy adjustment. In Section 5, we analyze the evolution process that follows from our dynamic evolution method and we derive and prove the related theorems and inferences about the evolved stable state. In Section 6, the simulation results confirm the conclusions and the advantage of the proposed evolution method is illustrated. Finally, the conclusions are provided in Section 7.
2. Related Work
The process of maintaining security using a trust mechanism in wireless networks can be observed as a process of strategy interaction. The trust decision of a node could affect the trust decision (trust or distrust) of the other nodes and the network state (security or insecurity), where the decision-making process can be explained and analyzed by game theory. Thus, there are many scholars who have studied trust and cooperation of wireless networks using different types of game theory, such as the noncooperation game [9–11], cooperation game [12], Bayesian game [13], and evolutionary game [14–24]. The various branches of game theory have corresponding applications in research on trust for security in wireless networks.
Mejia et al. [11] proposed a trust model that is based on a noncooperative game that uses a bacterial-like algorithm to allow the nodes to quickly learn the appropriate cooperation behavior. Based on cooperative game theory, Palomar et al. [12] proposed a new technique for handling security issues in mobile wireless sensor networks. They defined a game between sensor nodes and concentrated on three fundamental factors: cooperation, reputation, and quality of security, and they proposed a method for calculating the trust degree of nodes based on the amount of cooperation. In [13], Agah et al. developed a model that is based on Bayesian game theory, which is capable of formally explaining the characteristics of ad hoc networks. They further described a simple strategy that enforces cooperation among nodes.
Among the methods of game theory, the evolutionary game becomes a new type of effective method for trust and cooperation of nodes in wireless networks because an evolutionary game has the characteristic of limited rationality. Thus, the dynamic evolutionary game method has been widely used [15–18]. Dong et al. [19] provided a model for the optimization and stability of Internetware systems and improved their credibility with the Wright-Fisher process, which makes the whole system steady for a long time. Komathy et al. [20] analyzed the selfishness of neighboring nodes in MANET and followed a dynamic evolution with a fixed strategy or a random strategy. Finally, their system could reach a cooperation level of the nodes that increased to 100%. Seredynski and Bouvry [21] addressed the problem of node cooperation in the network using an evolution game that considered the impact of the network size and node type on the cooperation among the nodes. The authors analyzed the specific case in which a reputation system is not present in the network and investigated whether cooperation is dependent on the information type that is used by the trust systems of the network participants.
In the evolutionary game trust model, some work introduced incentives to encourage the nodes to cooperate. Shen et al. [22] introduced incentives for the trust decision problem, for example, a node that obtained additional income by selecting a trust strategy. These authors also studied the dynamic evolution process of trust strategy choice of nodes and derived conditions for the evolutionary stable strategy. Chen et al. [23] built a dynamic incentive mechanism to adapt to WSNs based on evolutionary game theory, which enables the selfish nodes to cooperate with one another, to ensure normal network services. Wang et al. [24] proposed an evolutionary game-based trust cooperative simulation model for large-scale MANETs. They constructed a trust-preferential expected action space that effectively confined malicious members to obtaining illegal payoffs. Finally, through evolutionary analysis of a game model, they deduced the convergence condition between the optimum strategy and a trust-preferential strategy.
Thus far, the basic evolutionary game thoughts have been mostly derived from the research results of Taylor and Jonker [25]. Currently, in evolutionary game theory, the replicator dynamic equation is a dynamic evolution equation with a selection mechanism. The establishment of a replicator dynamic equation is an important symbol-adjusting process of a group behavior. This approach can better reflect and predict the evolution results, but its limitation is obvious. The replicator dynamic studies only the changing trend of the overall group rather than the strategy choice process of individuals. In this paper, we learn the evolutionary dynamics based on the rethinking mechanism from [26] for the strategy choice, and we propose a strategy adjustment mechanism that is based on dynamic evolution. This mechanism designs the choice process of individual strategies, and an individual is likely to change its current strategy at each game. The individual will imitate the opponent's strategy as its new strategy, and the probability of the new choice strategy depends on the rate of individuals taking this strategy currently. This method accounts for the process of an individual's strategy choice based on dynamic evolution in such a way as to make up for the deficiency of the replicator dynamic model.
Compared to [22–24], our work is distinguishable in terms of the type of factors in the game and the process of the dynamics. Our ideas derive partly from the trust strategy model [22]; however, considering the data retransmission after the packets are lost, we build a different trust strategy game model and we propose a strategic adjustment mechanism that is introduced into the process of game evolution. As a result, we obtain different theorems compared to [22]. Furthermore, our work focuses centrally on the incentive mechanism for trust decisions of sensor nodes in WSNs, while Chen et al. [23] studied the incentive mechanism for selfish nodes and Wang et al. [24] studied the situation of large-scale MANETs. Overall, our work is different from the related studies described above, and the theorems and inferences on the evolution stable state could provide a theoretic foundation for trust mechanisms of sensor nodes in WSNs.
3. Node Trust Game Model of WSNs
3.1. Network Model
3.1.1. Strategy Description
WSNs adopt mainly the packet retransmission mode; in other words, the data are sent from a source node to the target node by forwarding from other nodes. Each node has two strategy choices:
To describe this process clearly, we introduce five symbols, as shown in Table 1.
Symbol descriptions.

3.1.2. Data Retransmission after Packets Are Lost
Packet loss during the network forwarding process is caused mainly by a network that has unreliable factors, such as weather and the energy of the nodes. In other words, the more unreliable a network is, the more serious the packet loss situation is.
Assume that all of the nodes in the network have the same unreliable factors, and, then, any node will have the same probability of successfully sending the data packet at any one time. Note that the probability is q. When a data packet transmission fails, the nodes tend to retransmit the packet until it forwards the data packet successfully. In general, the system will set a retransmission upper limit and stop retransmitting once the number of times for resending exceeds the upper limit. N represents the upper limit.
Obviously, the total number of retransmitting data packets obeys a geometrical distribution, when the packet retransmission is successful. Because the successful probability of sending the data packet at any one time is q, the successful transmission probability within the retransmission upper limit N is 

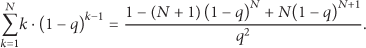


3.2. Trust Game Model
When the WSN nodes interact with one another, each node can choose either the strategy
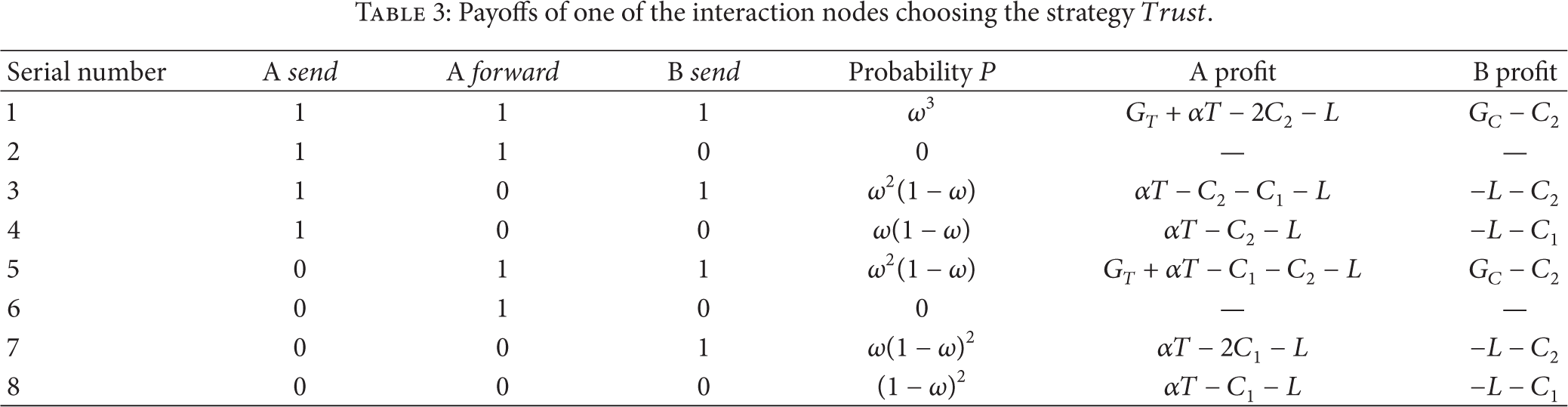
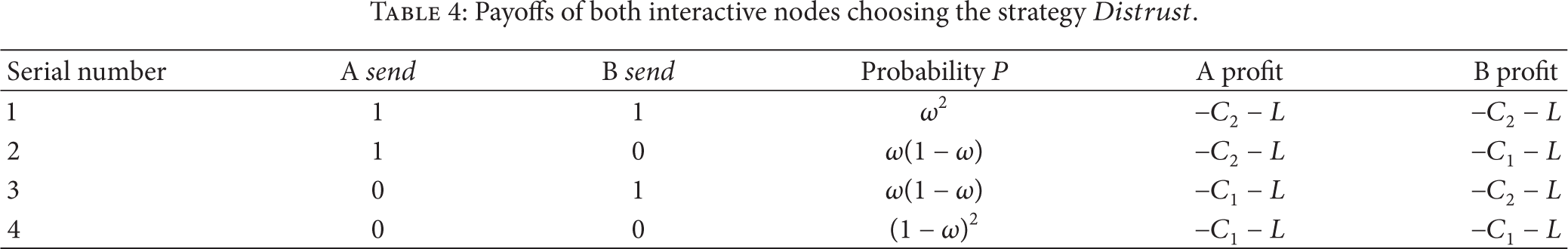
For Tables 2, 3, 4, and 5, we give an explanation of each symbol: P represents the probability that each event occurs, 1 and 0 means success and failure, respectively, and “—” means an impossible event in real life, regardless of its payoffs.
Payoffs of both interaction nodes choosing the strategy

Payoffs of one of the interaction nodes choosing the strategy
Payoffs of both interactive nodes choosing the strategy
Matrix of payoffs.

3.2.1. Both Interaction Nodes Choose the Strategy Trust
When two nodes A and B interact, each node has two actions, namely, send and forward. In addition to, due to the unreliable factors in the network, each action has two possible results, either success or failure. As shown in Table 2, there are 16 different events in all. This table shows the probability of each event occurring and the gains of the nodes.
We can see that, in Table 2, when two interactive nodes both choose the strategy
3.2.2. One of the Interacting Nodes Chooses the Strategy Trust
When two nodes A and B interact, and, in that interaction, A chooses the strategy
3.2.3. Both Interactive Nodes Choose the Strategy Distrust
If both of the two interactive nodes A and B choose the strategy
According to Table 4, when both of the two interactive nodes choose the strategy
Definition 1.
The WSNs node trust game is a 4-tuple W is a population that is composed of a very large number of individuals (sensor nodes in WSNs); N is the set of individuals who are in the same population W; S is the set of strategies, and U is a payoff matrix that is formed from the utilities of the game between the two individuals, and its value is shown in Table 5.
4. Strategy Adjustment Based on the Evolutionary Game
In this section, we introduce the dynamic evolution method for adjusting the strategies, to make up for the deficiency in the replicator dynamic. During the process of evolution, each individual in the game constantly adjusts the current strategy in such a way as to enable the individual to modify its current strategy with a certain probability.
Let
Therefore, after a game 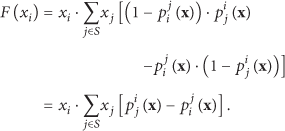
Based on the analysis above, we use a probabilistic method to quantify the strategy adjustment.
Definition 2 (see [26]).
In the WSNs node trust game, when the nodes that choose the pure strategy i play games with the nodes that choose the pure strategy j, the probability
In Definition 2,
5. Trust Game Model Analysis
5.1. Evolution Dynamics Analysis
Because the stable state
According to Definitions 1 and 2 and (6), the dynamic equation for the individual proportion of choosing the strategy Trust is derived as follows:

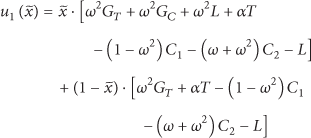
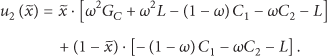
Theorem 3.
If
Theorem 4.
If
Proof.
To prove that
Because
Taking the derivative of 

According to Definition 2, it is easy to know that
When
When
Under the conditions of Theorem 3, only the Nash equilibrium can be used to choose a trust strategy for both sides; this equilibrium is strictly a dominant and stable evolution. In other words, regardless of what strategy node B will choose, the total income for node A choosing the Trust strategy is always greater than that of choosing the Distrust strategy. Regardless of what the initial state is for all of the nodes, the network will eventually reach a stable state in which all of the nodes choose a Trust strategy through evolution.
Under the conditions of Theorem 4, only the Nash equilibrium can be used to choose a Distrust strategy for both sides; this equilibrium is strictly a dominant and stable evolution. In other words, regardless of what strategy node B chooses, the total income for node A choosing the Distrust strategy is always greater than that of choosing the Trust strategy. Regardless of what the initial state is for all of the nodes, the network will eventually reach a stable state in which all of the nodes choose a Distrust strategy through evolution.
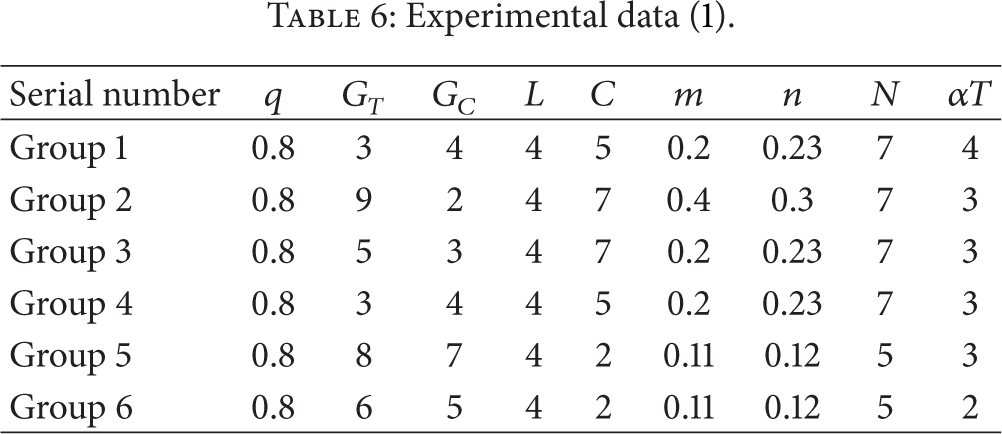
5.2. Trust Model Analysis
To ensure the security and stability of the WSNs and to improve the mutual trust among the nodes, we can adjust the controllable parameters in the WSNs’ trust mechanisms to satisfy the conditions of Theorem 3 and avoid the conditions of Theorem 4. After we take 
From (13), we know that
Inference 1.
Improving the trust incentive
Proof.
If the trust incentive
Inference 2.
When
Proof.
When
Inference 3.
When
Proof.
When 

5.3. Comparison with Replicator Dynamics
Replicator dynamics are one of the dynamic evolution methods in evolutionary game theory; the replicator dynamic equation is described as follows:


We put (8) and (9) into (16). It is easy to obtain the game model of Definition 1, according to which the replicator dynamic equation allows the system to dynamically evolve; the dynamic equation in which the individuals choose the strategy 
Compared with (10) and (18), (10) is the same as (18) when
Comparing (10) and (18), the dynamic equation expresses the speed of the dynamic evolution. There are three cases. (1) The evolution speed of (10) is faster than that of (18) when
Overall, we can derive that the convergence speed to the steady state is much faster in the evolution method than in the replicator dynamic as long as
6. Simulation Experiments
The experimental environment is Matlab 7. The experimental content is divided into three parts.
The first part is the verification of the evolution stable experiment, including the verification of Theorems 3 and 4 and Inference 2. The second part is to study the factors that have an effect on the evolutionary stable speed, including the verification to Inferences 1 and 3. The third part is the experiments that compare the dynamic evolution method based on strategy adjustment and replicator dynamics.
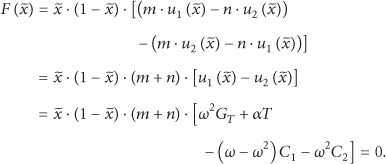
6.1. Experiment on the Evolutionary Stability
The experiment verifies the conclusions about the evolutionary stable state which are drawn by Theorems 3 and 4 and Inference 2.
We set the parameters of the first group and second group to meet the conditions of Theorem 3, the third group and fourth group to meet the conditions of Theorem 4, and the fifth group and sixth group to meet the conditions of Inference 2. The results of the trust evolution of the WSN nodes were observed under the 6 groups of parameters. The experiment data settings are shown in Table 6. The experimental results are shown in Figures 1–3.
Experimental data (1).
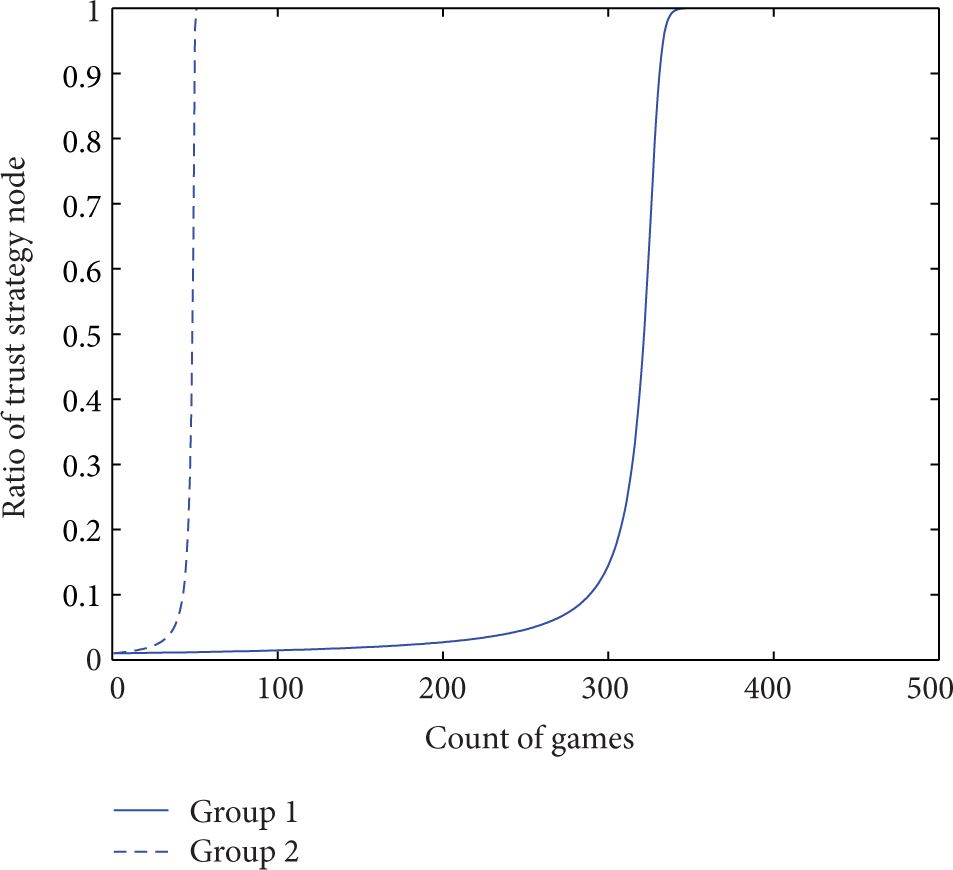
Trust evolution curve (1).
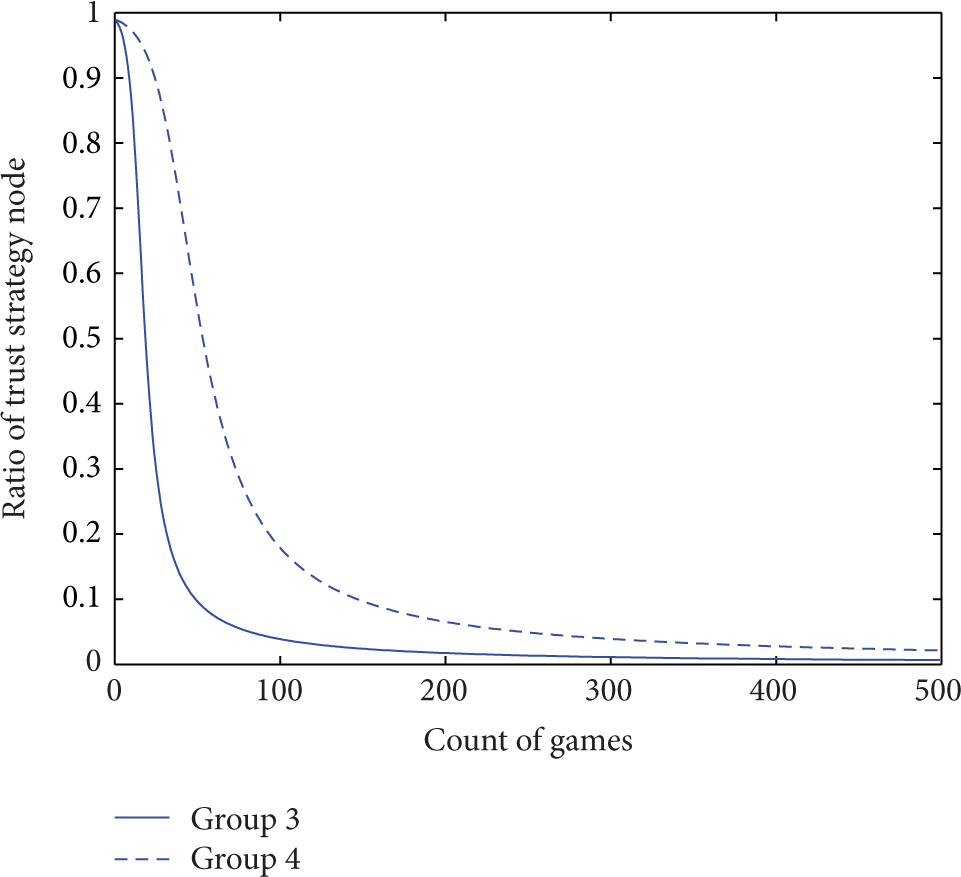
Trust evolution curve (2).

Trust evolution curve (3).
In Figure 1, the solid curve and dotted curve correspond to the first group and second group of the experimental data in Table 6, respectively. We can verify that the experimental data values from the first group and second group meet the conditions of Theorem 3 and Definition 2, respectively. As seen from Figure 1, when the initial value of the dynamic equation (10) of the sensor nodes trust evolution is 0.01, that is, when the rate of the sensor nodes choosing strategy
In Figure 2, the solid curve and dotted curve correspond to the third group and fourth group of the experimental data in Table 6, respectively. We can verify that the experimental data values from the third group and fourth group meet the conditions of Theorem 4 and Definition 2, respectively. As seen from Figure 2, when the initial value of the dynamic equation (10) of the sensor nodes trust evolution is 0.99, that is, when the rate of the sensor nodes choosing strategy
In Figure 3, the solid curve and dotted curve correspond to the fifth group and sixth group of the experimental data in Table 6, respectively. We can verify that the experimental data values from the fifth group and sixth group meet the conditions of Inference 2 and Definition 2, respectively. As seen from Figure 3, when the initial value of the dynamic equation (10) of the sensor nodes trust evolution is 0.01, that is, when the rate at which the sensor nodes choose the strategy
6.2. Verification Experiments on the Effect of Convergence Speed
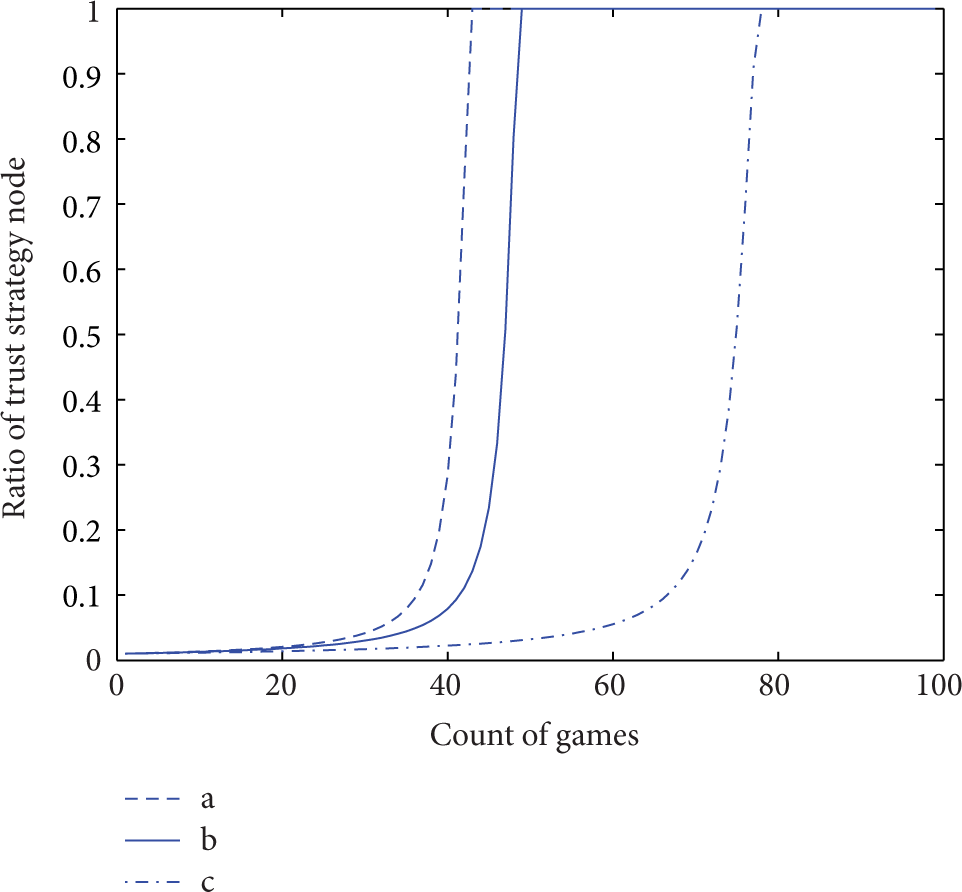
In this section, we explore the two important influencing factors on the evolutionary stable state: the trust incentives
Experimental data (2).
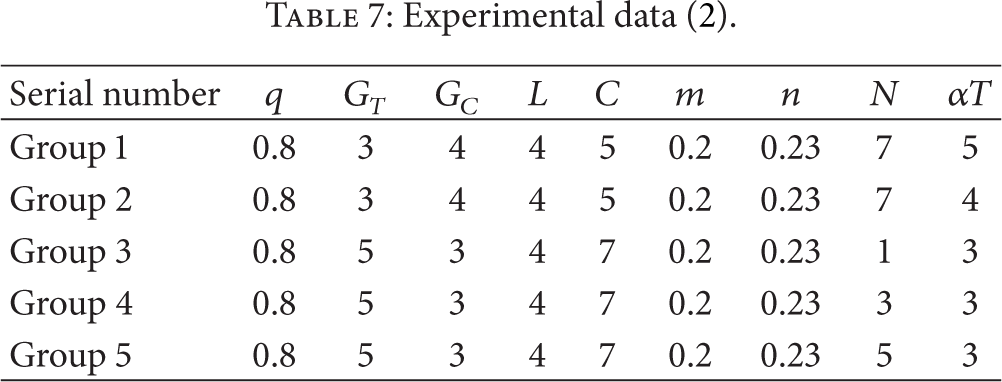
Trust evolution curve in terms of
Trust evolution curve in terms of N.
Figure 4 gives the effect of the trust incentives on the trust evolution. The solid curve and dotted curve correspond to the experimental data of the first group (
Obviously, the speed of the curve of
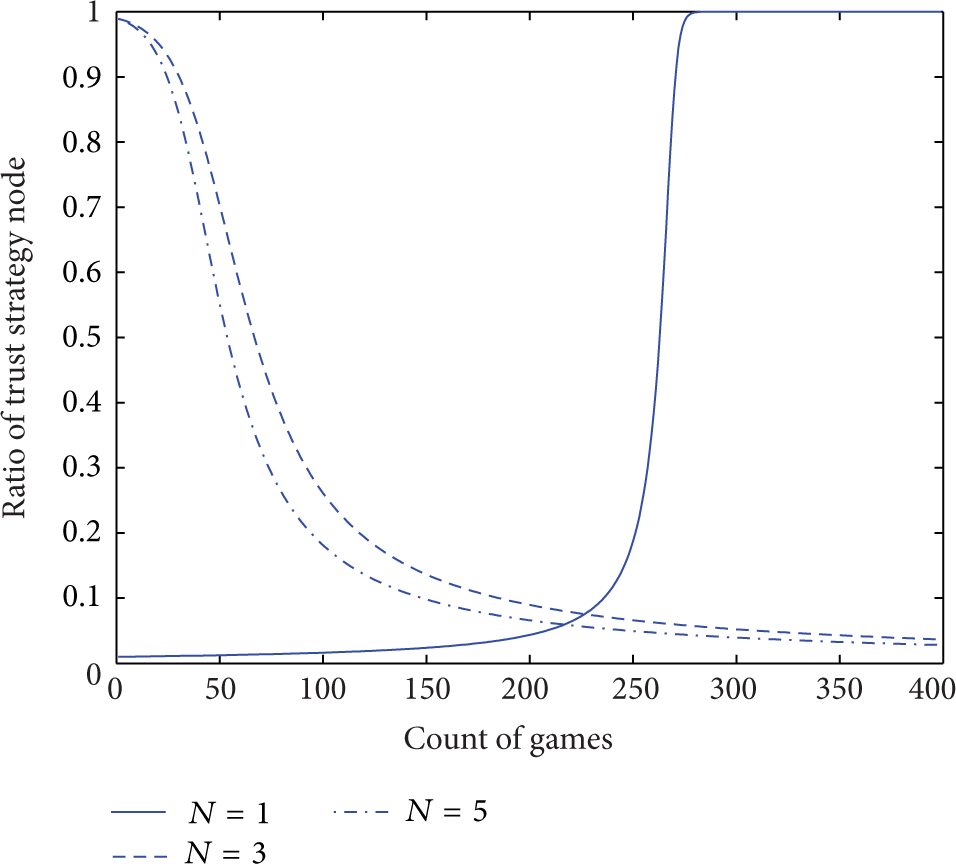
The following experiment is verified by the effect of the upper limit retransmission N. In Figure 5, the curves correspond to the experimental data of the last three groups in Table 7; the data in the three groups varies the value of N and maintains the values of the other parameters.
The experimental data of the last two groups correspond to the trust evolution curve of
In Figure 5, the solid curve of
Comparing the experimental results of the three groups of data under the same conditions, we know that if the upper limit retransmission N is smaller, the conditions of Theorem 3 are easily met and the steady state at
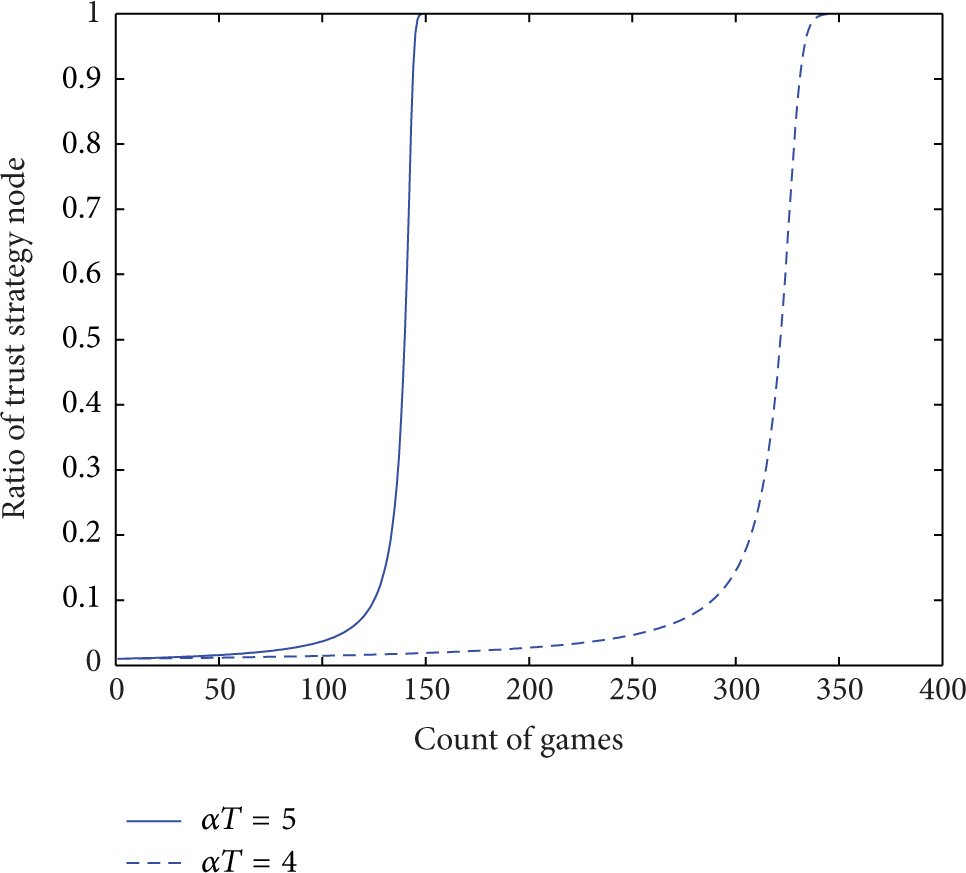
6.3. Experimental Comparison with the Replicator Dynamic
In this section, we set the same initial values and compare our dynamic evolution based on strategy adjustment following the dynamic equation (10) and the replicator dynamic method according to the replicator dynamic equation (18). Then, we analyze the effect of the convergence speed toward the steady state using the two different evolution methods.
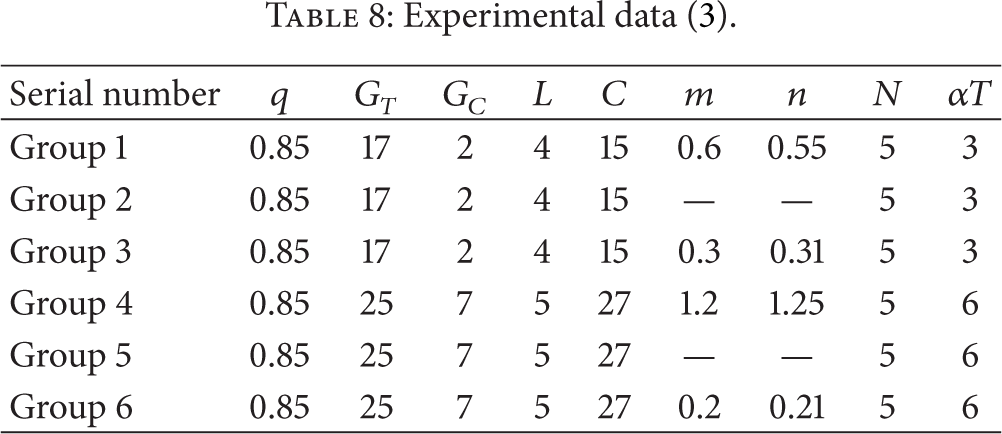
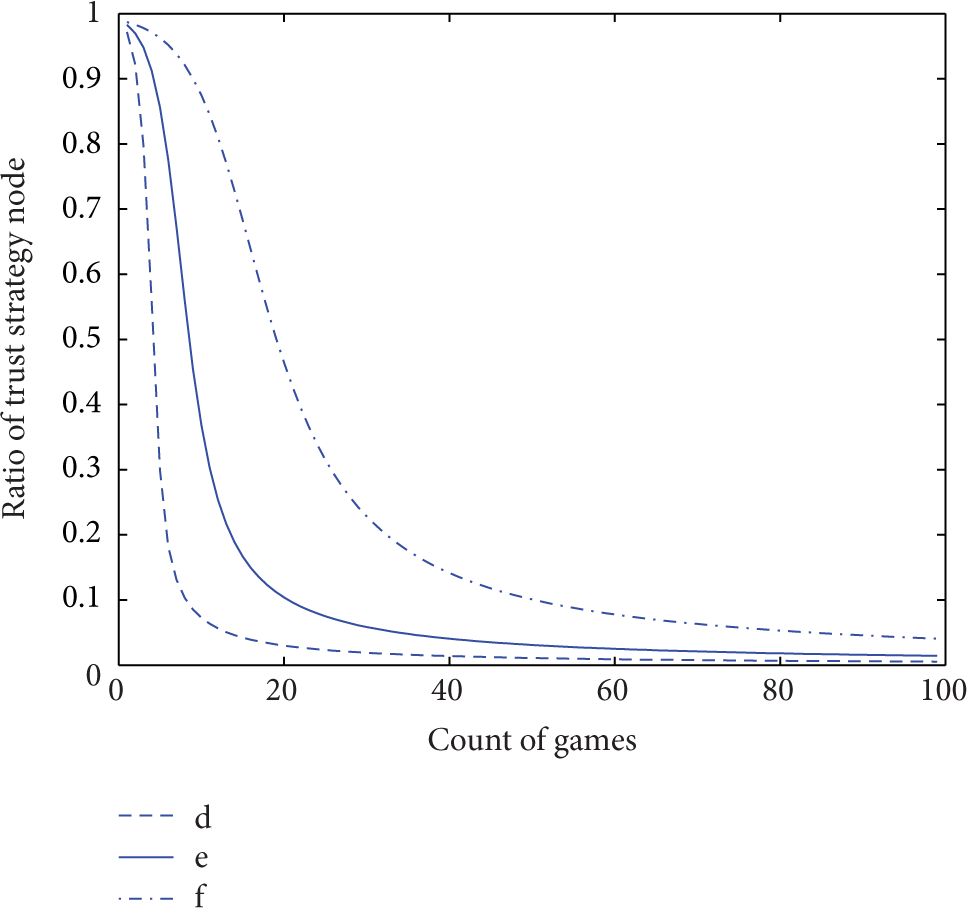
The experimental data are shown in Table 8: the first, third, fourth, and sixth groups of data for our method of dynamic evolution are based on strategy adjustment, and the second and fifth groups of data are based on the replicator dynamics. Through the previous analysis of Section 5.3, the replicator dynamics are a special case of our dynamic evolution method and are based on strategy adjustment, and the replicator dynamic evolution equation (18) is unrelated to the values of m and n; thus, we ignore the values of m and n. The experimental results are shown in Figures 6 and 7, respectively.
Experimental data (3).
Trust evolution curve compared with the replicator dynamic (1).
Trust evolution curve compared with the replicator dynamic (2).
In Figure 6, the curves a, b, and c correspond to the experimental data in the first, second, and third groups of Table 8, respectively. They meet the conditions of Theorem 3. Moreover, the data of the first and third groups satisfy the conditions of Definition 2, which implies that these three curves will finally reach the evolutionary stable state at
In Figure 6, curve b is the trust evolution curve, which meets the condition
In Figure 7, curve e is the trust evolution curve, which meets the condition
7. Conclusions
A WSN's trust management is an important aspect of WSN security. In this paper, we study WSN node trust decisions and trust evolution problems using evolutionary game theory. Based on the interaction cooperation of the sensor nodes, we consider the data retransmission after packets are lost and the trust incentive mechanism and we build an evolutionary game model that is closer to the reality of WSNs. Moreover, we propose an evolution method that is based on a dynamic adjustment strategy, to make up for the deficiency of the replicator dynamic method, which cannot show the trust decision process of the individuals. Through the analysis of dynamic evolution, we draw the conditions of reaching a steady state and analyze the factors that affect the convergence speed, and, finally, we compare the evolution speed of our method with that of the replicator dynamics. Last, the conclusions are proved effectively and feasibly by several experiments.
The results of this paper reveal the evolution dynamics rules of trust decision-making and trust evolution of WSNs; we could further calculate the trust values of the sensor nodes based on this evolution method-based strategy adjustment in subsequent work, and the trust management model that we propose provides a theoretical basis for the security of WSNs.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
This work was supported by the National Natural Science Foundation of China under Grant no. 61272034.
