Abstract
To protect users’ private locations in location-based services, various location anonymization techniques have been proposed. The most commonly used technique is spatial cloaking, which organizes users’ exact locations into cloaked regions (CRs). This satisfies the K-anonymity requirement; that is, the querier is not distinguishable among K users within the CR. However, the practicality of cloaking techniques is limited due to the lack of privacy-preserving query processing capacity, for example, providing answers to the user's spatial queries based on knowledge of the user's cloaked location rather than the exact location. This paper proposes a cloaking system model called anonymity of motion vectors (AMV) that provides anonymity for spatial queries. The proposed AMV minimizes the CR of a mobile user using motion vectors. In addition, the AMV creates a ranged search area that includes the nearest neighbor (NN) objects to the querier who issued a CR-based query. The effectiveness of the proposed AMV is demonstrated in simulated experiments.
1. Introduction
With advances in mobile communication technology and the widespread use of GPS-enabled mobile devices, location-based services (LBS) are growing rapidly. In LBS, mobile users issue spatial queries to LBS providers to obtain information based on their geographical locations [1–4]. Typical LBS applications include road navigation, area-specific weather forecasts, map information, automotive traffic monitoring, location-based SNS, and nearest point of interest (POI) queries [5–7].
Because LBS is provided for users based on their locations, users must report their location information to an LBS provider. Although LBS provides valuable services to users, revealing one's private locations to potentially untrustworthy LBS providers poses privacy concerns [8, 9]. Knowledge of a person's location can be used by an adversary to physically locate and identify the person. In fact, there are many real-life scenarios in which perpetrators abuse technologies to gain access to private location information about victims [10]. In an effort to preserve the privacy of LBS users, a number of location anonymization techniques have been studied. In particular, spatial cloaking that blurs a user's exact location into the cloaked regions (CRs) such that the CR satisfies the user-specified K-anonymity requirement has been widely used [11–23].
Several researchers have presented the concept of a location anonymizer, a trusted third party that acts as a middle layer between the user and the LBS server [6]. The anonymizer blurs the users’ exact locations into CRs using existing location anonymization algorithms and sends the CRs, rather than the exact user location, to the LBS server. This mechanism enables the users to obtain the desired LBS without revealing their exact locations to the LBS server. The K-anonymity requirement given by the querier ensures that the CR is K-anonymous (e.g., the querier is indistinguishable among K users within the CR), thus reducing the probability of the querier's location being exposed to untrustworthy parties to 1/K. Because the LBS server does not know the querier's exact location, it can only return a set of candidate answers to the CR-based query.
This paper proposes a cloaking system model called anonymity of motion vectors (AMV), which provides anonymity for spatial queries. The proposed AMV can address user queries based on the user's cloaked location information from the location anonymizer. The AMV minimizes the CR by predicting user movements based on the motion vector. The proposed method can be applicable in both outdoor and indoor environments. For example, a client in the car moves along the road and a cloaked region (CR) can be created based on the client's moving speeds and directions. In indoor environments, the movement range of a client is generally restricted due to various obstacles like walls and doors. This might make the motion vectors produced by the proposed AMV invalid. Nevertheless, the AMV can achieve effective query processing by adjusting the update intervals of the vector according to the size of the indoor space (i.e., the movement range of the client). The main features of the AMV can be summarized as follows:
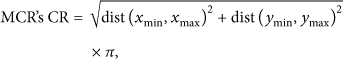
Client movements are considered when generating a CR that satisfies the user-specified K-anonymity level. The user location update cost of the anonymizer can be reduced by allowing the anonymizer to not check the user location from time t to Compared with the previous cloaking model (distributed grid based continuous cloaking (DGCC) (refer to Figure 1) [23], minimum cycle region (MCR) [24], which produces circular CRs (refer to Figure 2)), the AMV generates a smaller CR, thus lowering the query processing time.

An example of the CR creation (4-anonymity).
CRs satisfying 4-anonymity (the previous MCR).
The major notations used throughout this paper are as shown in Notations.
The rest of this paper is organized as follows. Section 2 highlights related works. Section 3 describes the proposed AMV model and depicts the creation of CRs using the previous MCR and proposed AMV. Section 4 describes the creation of
2. Related Work
To address the location privacy protection of LBS users, many location anonymization techniques have been proposed. Cloaking and K-anonymity are the most commonly used forms of location anonymization [10–22]. Figure 1 depicts an example of the distributed grid based continuous cloaking (DGCC) area creation when the required K-anonymity level is 4 (e.g.,
The cloaking method in [12] considers both K-anonymity and L-diversity. It creates a minimum CR by first finding L number of buildings. After satisfying the L-diversity requirement, it extends the CR to satisfy the K-anonymity requirement (e.g., the CR contains at least K number of users). The New Casper proposed by Mokbel et al. [11] is a research prototype of the framework for anonymous LBS. It satisfies the four requirements of location anonymity: accuracy, quality, efficiency, and flexibility. The cloaking algorithm in [13] employs dummy generation in creating a CR.
To solve the building double counting problem, it adds the building grouping item to the index structure of the existing privacy grid approach and minimizes the CR by finding K users (e.g., K-anonymity) in the grid cells adjacent to the buildings in the CR. However, these previous schemes ignore the client's movements.
Location anonymization techniques for LBS that consider the movement information of mobile users have been suggested [24, 25]. The technique in [24] addresses the anonymization of snapshot and continuous LBS queries. It creates a minimum circular CR based on mobile user's location trajectories. However, this requires tolerance of temporal errors, as the direction and speed of user movement are not taken into account. The technique in [25] considers the user's speed and direction of movement in addition to location. It requires information about the exact location of all user nodes and calculates the querier's movements based on his/her direction of movement and speed. There are some additional anonymization techniques that consider client movements using the Voronoi diagram, road networks, and historical location data [26–29]. However, none of these existing techniques support spatial queries with cloaked areas (e.g., CRs). Recently, a method for private kNN queries has been proposed. It creates a CR for the querier and performs query processing based on the type of objects (e.g., restaurants and cafes) in the CR [30]. This method does not consider K-anonymity while taking into account object types, so it cannot be directly compared with the proposed AMV.
3. Proposed AMV Model
The AMV proposed in this paper considers client movements to create a minimized K-anonymous CR and supports spatial queries with cloaked locations. The system model of the proposed AMV contains three components: the centralized LBS server, the location anonymizer, and the client. The location anonymizer is a trusted third party that is placed between the client and the LBS server [6]. To obtain LBS, the querier sends its location along with the spatial query to the location anonymizer. The location anonymizer that periodically receives location updates from mobile users blurs users’ exact locations into CRs and sends the query, along with the CR, to the LBS server. The anonymizer creates a session ID that is valid during the entire service period for the querier. The LBS server then processes the CR-based query from the anonymizer and returns a candidate list of answers to the anonymizer. Finally, the anonymizer computes the exact query answer from the candidate list and sends it to the querier.
The proposed AMV assumes that the
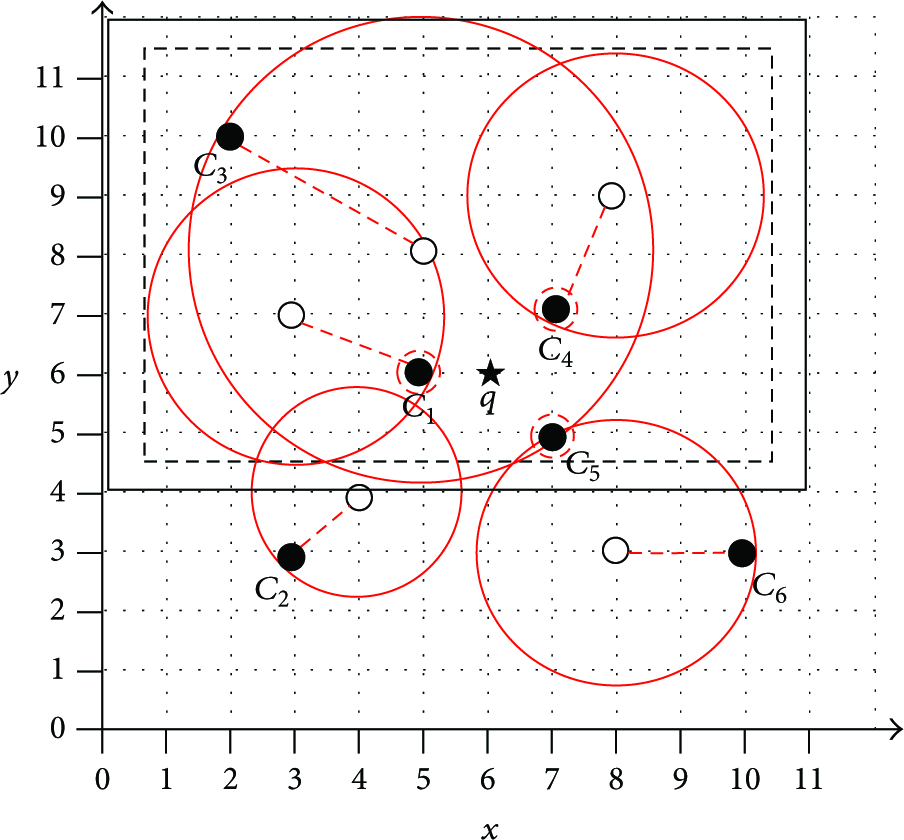
Figure 2 shows the CR produced by the previous MCR method that considers only the user's speed [24]. The dotted rectangle represents a minimum CR that satisfies the 4-anonymity requirement at
Figure 3 presents the CR created by the proposed AMV, which considers the speed and direction of movement using the motion vector. It is assumed that these clients are moving at the same speed as the clients in Figure 2. The 4-anonymous CR at

CRs satisfying 4-anonymity (the proposed AMV).
Compared to the existing technologies, the proposed AMV involves the extra cost of maintaining the speed and direction information of the moving users. However, the user can provide this motion information when submitting the location and K-anonymity parameter information to the LBS server. Thus, the overhead associated with this additional motion information is not significant. Assume that 1 byte of storage is required for the representation of client speed in the AMV and another 1 byte for the representation of client direction. As x- and y-axes exist in the coordinate information of object, it becomes 2 × coordinates (GPS coordinate information generally uses x-axis 4 bytes and y-axis 4 bytes; in case of detailed GPS measurement, the data size on x- and y-axes may increase). The size of object is typically assumed to be from 128 bytes to 1,024 bytes [31]. When the number of clients is 100, the size of data stored in the server is 1,000 bytes in the AMV, 900 bytes in the MCR, and 800 bytes in the DGCC. The DGCC yields the smallest data size, but it has a drawback that its data size increases by t times whenever an update is made. Note that the proposed work is not intended to reduce the data size maintained in the clients. This work aims to minimize the data to be delivered by the server by discovering
4. Finding
in NN Queries
This section illustrates how to create
In Figure 4, it is assumed that there are no objects inside the CR. The CR of the AMV described in Section 3 is used to find

Primary
Algorithm 1 describes the primary identification (filtering) of
01: check the CR; 02: 03: {take the grid cells around the CR one by one, e.g., the upper, lower, leftward, rightward, and diagonal grid cell of the CR is added by 1} 04: terminate the iteration when 05: 06: result = create a circle centering on the CR vertex farthest from 07: 08: result = result ∪ grid; 09:
The initial
Figure 5 depicts the secondary creation of

Secondary
The final
Algorithm 2 describes the secondary creation (refinement) of
01: check the vertices of the CR; 02: exclude mindist and maxdist; 03: create the circles of vertices B and C using the first respectively, with 04: Result = (the circle of B ∪ the circle of C); 05: Result = Result ∪ grid; 06: Result = Result ∪ result of Algorithm 1; 07:
In the event that objects exist inside the CR, the creation of

5. AMV Equations
This section defines the proposed AMV and the previous MCR using equations.
The computation of the CR that satisfies the K-anonymity requirement in the AMV is represented in
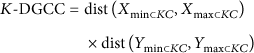
In comparison with the AMV, the circular CR of the MCR is transformed into a quadrate CR. The CR represented by a square is 1.17 times larger than the circular CR. If there are grid cells that intersect the CR, the CR is extended to enclose them. This decreases the error rate involved in CR-based queries. The equation below computes the CR of the MCR that satisfies the K-anonymity requirement:
Similar to K-AMV,
To represent the K-DGCC of the DGCC into an equation, the following definitions are made. When
The case of having objects inside the CR (
With the defined distances, the search area for the NN object that answers the CR-based query can be defined as follows:
The search area of mindist is included in that of maxdist, so its calculation can be omitted.
The search areas of
The final search area
In kNN queries, k nearest objects satisfying the query can be both inside and outside the CR. In this case, the final search area for both the inside objects and the outside objects is calculated individually using the equations presented in this section. The results are then combined, for example, inside
6. Experimental Evaluation
Through simulated experiments, the performances of the proposed AMV and the previous MCR were measured for comparison. These experiments were performed on a computer with a 2.9 GHz processor and 4 GB memory. C++ was used to conduct the experiments. It was assumed that the querier was stationary and that
Table 1 summarizes the parameter settings of the experimental environment.
Experimental environment settings.
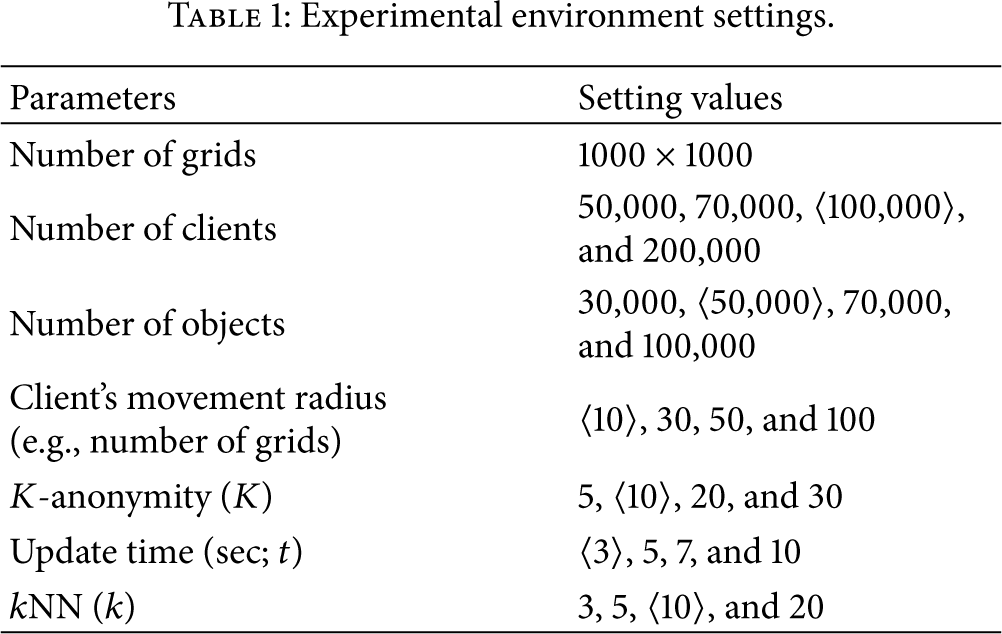
Figure 7 shows how the size of the CR varies according to the K-anonymity levels.

CR sizes with respect to K-anonymity levels.
In the experiments, the movement radius of the client was set to 10 grid cells and the update interval of the anonymizer was 3 seconds. CR of AMV generates 30.9% and 55.6% less CR for each of the MCR and the DGCC.
Figure 8 shows the size of CRs with respect to the movement radius of the client. In the experiments, the K-anonymity level was set to 10 (

The size of CRs with respect to the client's movement radius.
Figure 9 depicts the size of CRs with regard to the location anonymizer's update interval, denoted by t. The location of the moving client at t is predicted based on the speed and direction of the client's motion vectors, and the CR is created by considering the predicted client location. In the experiments, the K-anonymity level was 10, and the client's movement radius was 10 and 30 grid cells. On average, CR of AMV makes 42.7% and 65.2% less CR for each of the MCR and the DGCC.

CR sizes with respect to the anonymizer update intervals.
Figures 10 through 14 examine the search area

Figure 10 shows
The size of
Figure 11 presents

Figure 12 shows
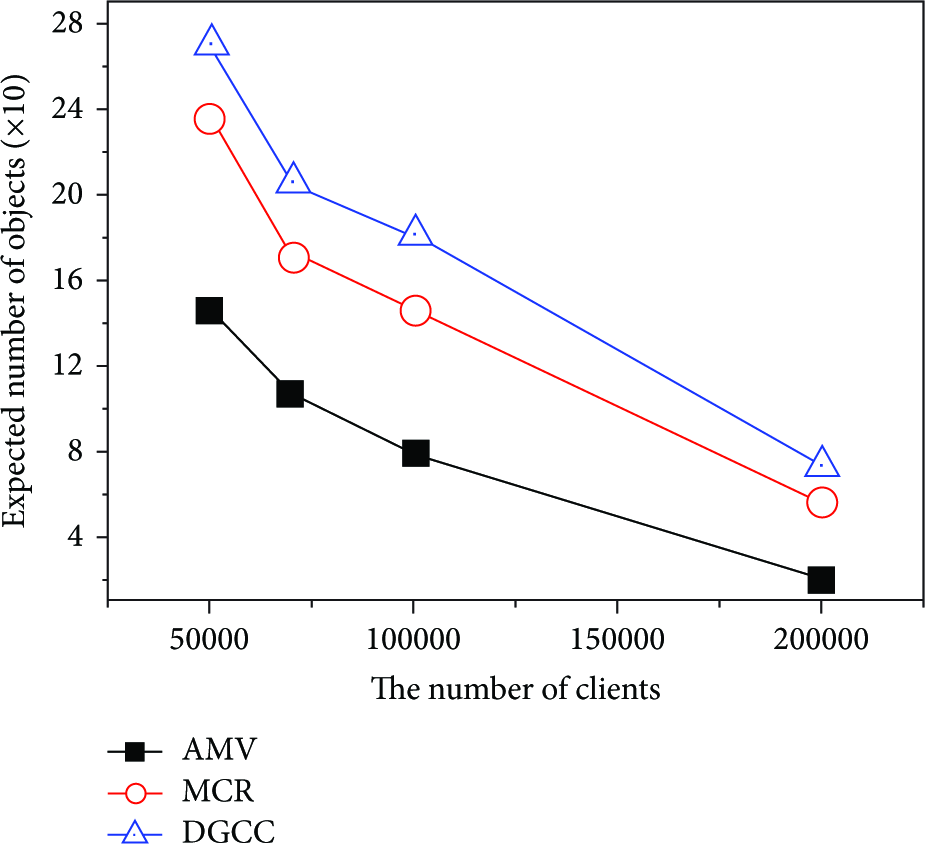


Figure 13 shows
Figure 14 presents
7. Conclusion
This paper presents a cloaking system model that enables mobile users to make spatial queries without revealing their exact location information. The proposed AMV generates a minimum K-anonymous CR by predicting the future location of the moving client based on the motion vector. This enables the AMV to generate a smaller CR than the previous cloaking method. In addition, the AMV creates a search area
In the future, the performance of the AMV can be further examined through experiments in which the querier is moving rather than remaining stationary.
Footnotes
Notations
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Authors’ Contribution
Kwangjin Park and Moonbae Song are equal contributors to this paper.
Acknowledgments
This research was supported by Basic Science Research Program through the National Research Foundation of Korea (NRF) funded by the Ministry of Science, ICT & Future Planning (2013R1A1A1004593 and 2014R1A1A2054315).