Abstract
Wireless technology will be widely used in libraries with the development of the mobile network in the near future. This paper focuses on MAC protocol for wireless network based on ultra-wideband band (UWB) to solve the problems of real-time and reliability in the wireless transmitting. According to the particular signal characteristics such as low energy consumption and excellent location, we propose a multichannel MAC protocol (UWBIMAC) based on status-adaptive to choose the channel mechanism. Simulation results show that the protocol had the ability of stronger antijamming, improved network throughput, and provided better average delay performance than IEEE802.15.4 MAC, IEEE802.11 MAC, and other UWBIMAC protocols. This method could be used in the process of wireless transmission service in the library or other similar scenarios. To a certain extent, it solves the problem of real-time and reliable performance in the process of wireless communication.
1. Introduction
The development of information technology, data storage technology, and the demand of providing diversified information services have pushed library industry to reform. Internet technology makes the traditional library services of the library change to the service mode of the digital library. The rapid development of wireless communication technology and application opens up the library from cable network services to the wireless mobile network service model. Forcing on wireless technology in the library, the most intuitive impression and concept are that users cannot be limited by time and place. With wireless terminal equipments, such as mobile phone, tablet, and e-Reader, users can query, browse, and get the service of information resources. At present, many users in China use mobile technology to expand the library services, for example, using short messages to remind the due service of documentation, renew service, new business introduction about the library.
Wireless applications involving mobile subsystems or just the desire to save cabling makes wireless technologies attractive. First of all, the cost and time needed for the installation and maintenance of the large number of cables that is normally required in such an environment can be substantially reduced, thus making buildings setup and reconfiguration become easy [1, 2]. In a library, some place such as classroom, meeting rooms, and reading room, it is difficult to use wired LAN. As mobile devices are becoming more and more, cable network has no way to provide so many ports to readers, but wireless way can transmit easily from one port extension to hundreds or thousands of application ports. The readers can be connected to the library website at any time and place to carry out the study. So how to apply wireless technology into the library has become the target of information construction in the library. The structure of a wireless network in the library can include wireless local area network (WLAN) and wireless ad hoc network. WLAN and wireless ad hoc network are different. Ad hoc network is a kind of self-organizing network on demand. It can be used for collecting and transmitting document quickly instead of the library staffs to a certain extent. Readers can find the location of a book and receive the document information by wireless devices in the library quickly. When the wireless nodes do not need the network connection, nodes can disconnect the network and release network resources. So the wireless ad hoc network is more flexible and lower cost than WLAN. In fact, wireless sensor network (WSN) is a kind of ad hoc networks, and it has been applied in various fields. So wireless ad hoc network could have a wide range of application prospects in the future, and it is a good supplement to the WLAN.
Wireless technology will realize the liberation of the users in time and space, and the users can access data and information anytime and anywhere from the library. It brings great convenience and effectiveness for people's work and study. In terms of current technology, the advantages and disadvantages coexist to a certain extent. Wireless technology has some problems as follows. (1) Wireless technology can support mobile users demand, but the reliability needs to be improved. (2) Library information resources are rich, but the services of wireless network communications are limited. Some works had been done to investigate its feasibility and to find sound technical approaches in 2002 [1, 2]. Wireless links are prone to possible transmission errors caused by deep fading (which occurs when the received signal strength drops below a critical threshold) or interference. One of the central problems in the design of wireless communications systems is that the reliability and real-time requirements found in these systems are more likely to be jeopardized over wireless channels than they would be over a wired channel. Accordingly, there is significant interest in mechanisms which makes transmission over wireless channels more reliable and robust. Comparing with the conventional wireless communication technology, UWB consists of short pulses of low-energy radiation [3, 4]. The shape of the pulse gives it the property of generating radio energy over a wide frequency range, but at very low energy. This allows UWB to overlap other radio bands such as WiFi and other services in the 2.4 GHz ISM band without interfering. Generally, other radio modulation schemes such as DSSS will see UWB as just impulse noise, so they are easily filtered out. Since UWB uses pulses, it is capable of being detected over a much longer range than other signal forms. Pulse signal can penetrate solid objects better than continuous wave signals [5]. For example, one approved use of UWB is for radar's ground penetrating and position. And low-energy radiation requires less transmit power and results in longer battery life for battery-powered devices. These characteristics make UWB become an exciting new technology with great potential for transmitting. So UWB is more suitable than other wireless technologies for ad hoc network in the library.
Since it is practically impossible to guarantee delivery of packets within prescribed deadlines over error-prone wireless links, one strategy of improving transmission reliability is to improve the lower layer protocols, namely, the physical layer (PHY) and link-layer protocol. This paper adopts another strategy to improve the transmission reliability and real-time. It is named medium access control (MAC) protocol.
The rest of this paper is organized as follows. Section 2 reviews the UWB transmission principles. Section 3 describes the related work and Section 4 introduces the MAC scheme based on UWB for wireless ad hoc network in the library. Section 5 introduces the communication process. Sections 6 and 7 discuss and analyze the performance of the proposed MAC scheme. And future work on UWB for the library is presented in Section 7.
2. Review of UWB Transmission Principles
UWB is a new field of communications. In the military field, radars use ultra-short pulses of energy and complex pulse sequences for location and communication. UWB signals are characterized by the ratio of their bandwidth to their center frequency. Normal narrowband signals have bandwidth-to-center-frequency ratios that are 0.01 or less. Wideband and spread spectrum signals have bandwidth-to-center-frequency ratios that are 0.01 to 0.25. However, UWB signals have bandwidth-to-center-frequency ratios that are 0.25 to 2.0. Since the bandwidth is so large, these signals lose their sinusoidal nature and take on a whole new set of properties [6]. A UWB signal is produced by generating an ultra-short pulse that is in many cases less than a nanosecond in duration. This makes the pulse duration at the same sequences as the radio frequency (RF) cycle. In addition to the short duration pulses, these UWB devices can be made with high pulse repetition frequency. The pulses can be repeated at the sequences of microseconds. With very fine variations of the spaces of these pulse sequences, sophisticated messages can be communicated with the device. With correlation technology, a significant quantity of information can be transmitted. Therefore, these devices can be joined together to realize communication and co-location among them. Multiple accessing is achieved by using time-hopping (TH) codes; for multiuser communication, the transmitted signal is

TH pulse-UWB transmitter signal.
Equation (1) shows that the time-hopping code provides an additional shift of
Wireless RF environment is usually unstable in the library. Serious interference and multipath phenomenon will seriously deteriorate the quality of communication in the wireless RF environment. And the real-time and reliability of communication usually have higher requirements, although UWB technology itself has inherent natural physical technical advantages. For instance, the good location ability of UWB ensures that wireless nodes can realize location between each other. The low energy of UWB ensures that wireless nodes can be long-term survival [7, 8]. But there are still difficulties to meet the real-time and reliability of communication. So the study of the upper protocol based on UWB technology is very necessary. The paper proposed the MAC layer protocol to solve the real-time and reliability of wireless ad hoc network.
3. Related Work
In some applications, wireless technologies are usually used for controlling or monitoring. In these applications, the network is composed of many sensors [9–12]. Of course, in library, we can use wireless sensors to monitor the environment. On the other hand, the library staffs and users can locate and find the books or documents by wireless ad hoc network. By wireless nodes, the wireless network transmits the information. People will receive the information that they demand in the library. The key problem is to disseminate information to the destination reliably and efficiently. How to solve the reliable communication should be solved in the UWB wireless ad hoc network. At present, network protocols that exploit the UWB technology are yet to mature. There was no prior work on the design based on UWB for library network. So the research that set up a reliable and efficient UWB protocol for ad hoc network is a valuable and challenge work. In recent years, the works [13, 14] were only suitable for high speed, short wireless personal area networks (WPANs). But wireless ad hoc network in the library is a kind of relative long distance communication network system. The existing MAC protocols for high-speed UWB wireless ad hoc application cannot apply to the library. The main reason is that the different application requirements make the UWB physical layer technology and MAC protocols different; for example, the multiband UWB signal transmission technology adopted centralized MAC protocol, centralized MAC protocol faced huge network costs, and once the control center fails, it would lead to the problem of network paralysis. Therefore, literature [15, 16] proposed MAC protocols based on IEEE802.15.4 standard. In Section 6, the paper will analyze the performance of the two protocols. The literature [17] optimized the length of the medium access control frame body to maximize the energy efficiency in IEEE 802.15.6 ultra-wideband (UWB) in wireless body area networks (WBANs), but the transmission distance was too short in WBANs to be suitable for wireless network in library. And it focused on the high QoS mode in physical layer, ignoring the real-time and reliability. Literature [1, 18, 19] needed to be supported by effective technology in the routing layer or physical layer to realize the appropriate pulse rate. That meant that UWB equipment needed to modify the existing technology of UWB physical layer [18, 19]. This paper presented a MAC protocol based on TH pulse UWB. It concentrated on improving real-time and reliability in the wireless network for applying library.
4. The Design of MAC Protocol Based on UWB
4.1. The Division and Using of Channel Design
In the wireless network based on TH pulse UWB, nodes get a number of different THC codes to realize multiple access. In UWBIMAC protocol, all nodes use the same THC as a link to set up the control channel and use different THC into different data channel to realize communication between nodes, as shown in Figure 2.
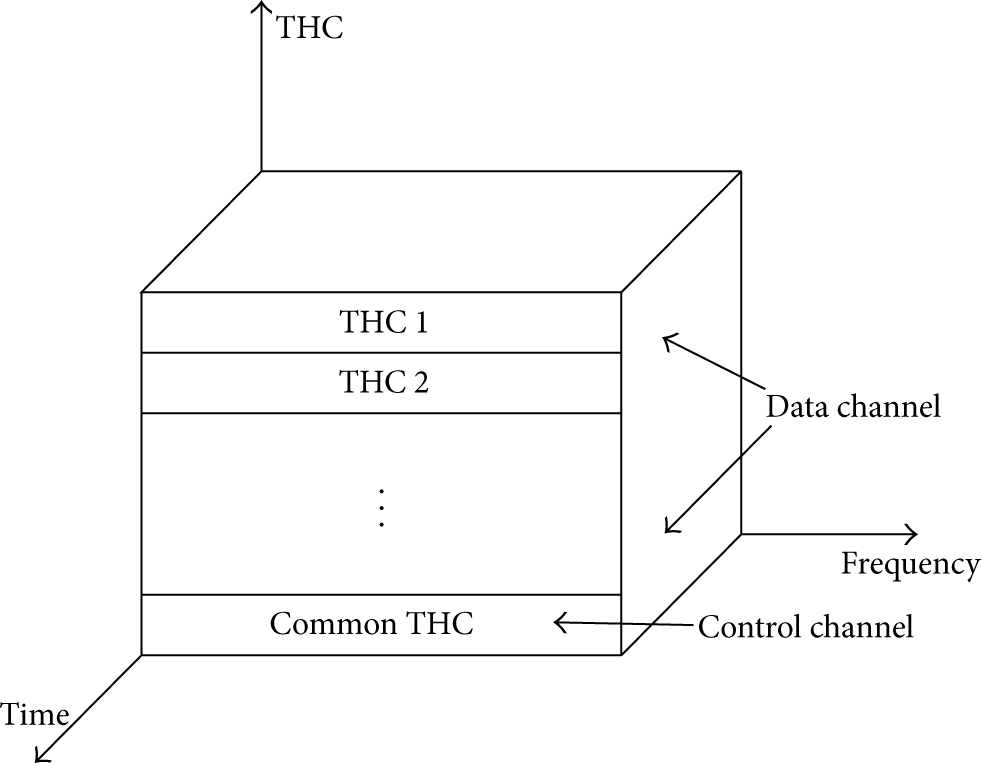
Data and control codes in the proposed protocol.
4.2. Conflict Avoidance and Back-Off Algorithm for Control Channel
In UWMIMAC protocol, only RTS information can transmit on the control channel. In order to solve the bottle neck and cost problems, communication requirements can be classified by the signal priority level; multiple communication requirements can be sent once the synchronization is over. It can reduce the control channel capacity and reduce the incidence of the bottleneck. According to the need of the wireless network transmission in the library, signals were divided into three categories: real-time signal, periodic signal, and nonreal-time signals. The control channel would meet the requirements of real-time signals as much as possible and ensured the real-time data transmission. On common control channel, only communication node sent request information RTS, according to the signal priority level; the priority of the RTS itself was divided into the corresponding priority. Each node itself had a back-off queue to cache the RTS that was not sent. Each node can establish a neighbor node location and status information lists as in Table 1.
Neighbor nodes list.

Conflict avoidance and back-off algorithm are as follows.
When a node sent RTS, it sent the same RTS to its neighbor nodes according to the information of the neighbor list at the same time. When the nodes received the RTS, they perform the corresponding action according to the following. The neighbor node cannot do anything if it had not RTS to send. The neighbor node itself had RTS to send, the low priority RTS entered back-off queue, and the high priority RTS was sent and performed (1). If the priority was the same, the RTS of the current node was sent and performed (1). After sending information, if a RTS conflict was detected, the high priority RTS adhered to send, and low priority RTS returned and inserted to cache queue's head, executed back-off algorithm.
The paper adopted the index of the binary back-off algorithm; it means that the number of conflicts and the number of waiting time slots were selected at random from 0 to
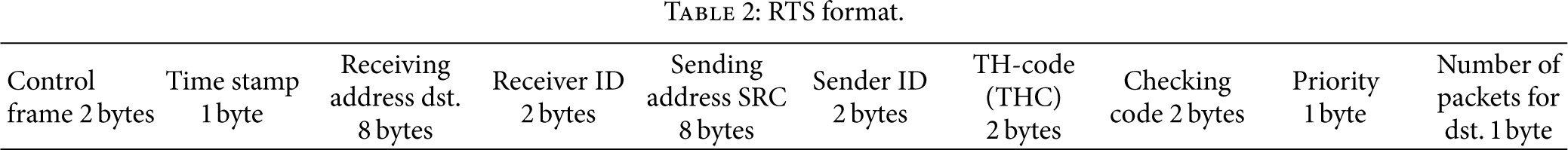
The RTS frame format was as shown in Table 2.
RTS format.
4.3. Selection and Use of the Data Channel
While the wireless network was running, each node periodically used different THC, except for public THC, which sent hello information to the free neighbor node in order to estimate real-time quality of using data channel classified by different THC. According to the current optional channel estimate, each node set up real-time status information of the channels, stored and ordered in the node channel queue. When the node sent data packets, it would choose the first element in the queue, and used THC was recorded on neighbor nodes list. Table 1 shows example of the neighbor nodes list.
5. Communication Process of UWBIMAC Protocol
In UWBIMAC protocol, the sending node SRC chose the first THC from current channel queue. Using common control channel, the THC with RTS was sent to the receiving node DST. DST received RTS, and it sent CTS by data channels specified in the RTS to further confirm the data channel unobstructed. If the RTS/CTS was not received correctly because of transmission collision or interference, the handshake was a failure and the transmission was into the corresponding failure state. If handshake was successful, the SRC received CTS within a specified time (
The CTS, DATA, and ACK/NACK frame formats are as shown in Tables 3, 4, and 5.
CTS format.

DATA format.

ACK/NACK format.

The process of transmitting is shown in Figure 3. The sending node periodically checks transmission queue status. The delivery process is as follows.
The sending node extracted receiver ID number to transmit queue, determining the number of the messages from the same receiver. The sending node checked whether the receiver was just free; if so, the sending node through the receiving node can continue to receive and to perform (4); otherwise sending node performed (3). The sending node performed channel selection mechanism, determined the right THC, and then sent the RTS on the common control channel. The sending node sent RTS and waited for CTS from the receiver R. Within the specified time, if the sending node did not receive the CTS, the sending node sent CTS again, and the number of times was limited to six times, more than six times, sending node performed (3). After the sending node received the CTS, it sent DATA according to THC code by the agreement and waited for confirmation ACK from the receiving node. Within the specified time, the sending node received the ACK, checked whether there were other DATAs to be sent in the queue, executed (4), continued to send DATA, and waited for ACK acknowledgment from the receiving node. If the sending node received the NACK, it would take rate adjustment mechanism, resent DATA, and performed (7). If the sending node did not receive any ACK/NACK, it had to select data channel and performed (3).

Transmitting process.
The process of receiving is shown in Figure 4. When public control channel RTS is in the idle state, the receiving node performed receiving process as following.
The receiving node tested RTS to identify DST in receiving address, if it did not agree with the address of the receiving node, the receiving node abandoned the RTS, and receiving process terminated. The receiving node was idle, and DST was the same as receiving node's address. The receiving node issued CTS by the designated THC and entered the active state. If the receiving node did not receive the DATA within a specified time, it returned to the idle state. When the receiving node received a packet DATA successfully, it returned a confirmation ACK, and then go into idle state, otherwise calculating BER value, if less than a specified threshold, it sent NACK.
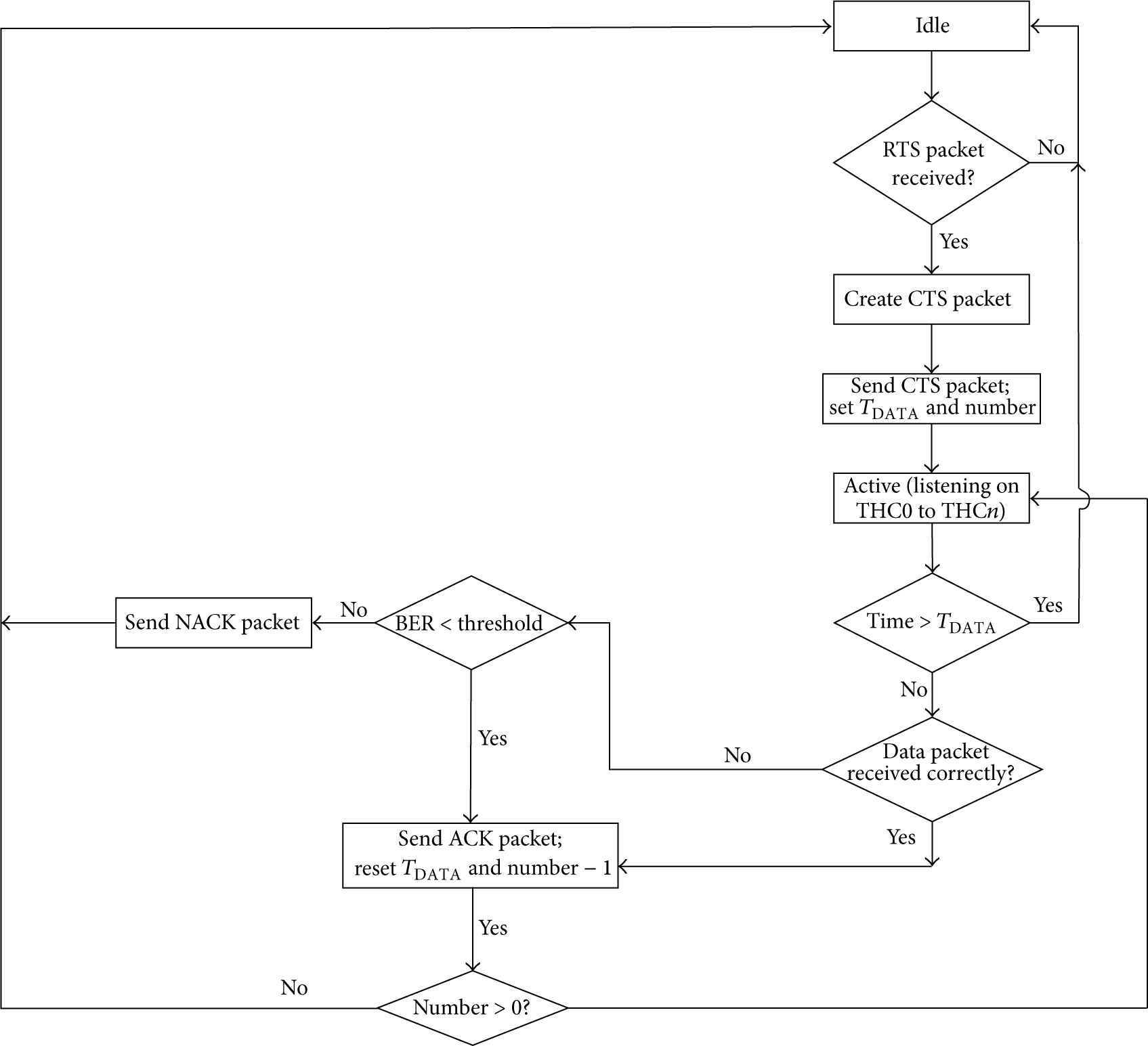
Receiving process.
6. Performance Analysis
To test the performance of the proposed UWBIMAC protocol, the paper chose network simulation tools NS2 to realize UWBIMAC protocol and its performance comparison with (UWB)2 [15], DCC-MAC [16], IEEE802.15.4 [18] MAC, and IEEE802.11 [19] MAC protocols. So far, (UWB)2 and DCC-MAC [16] protocols were the relatively complete MAC protocols based on UWB technology in the last ten years. IEEE802.15.4 and IEEE802.11.MAC protocols are the classical and traditional wireless network technology. They can be applied for WLAN and wireless ad hoc network. Network simulators as NS2 and OPNET can provide the simulation support of the above protocols. In addition, compared to other MAC protocols, these four protocols are more suited to wireless communication in the library. So simulation results can instruct whether UWBIMAC protocol is superior to other four protocols or not.
6.1. Simulation Parameters and Network Scenario Settings
UWBIMAC protocol was realized by NS2 as the simulation experiment platform. And the existing NS2 model was modified, the physical layer was based on a TH multiple access, and the calculation of BER was in the physical layer. Different channel was divided according to TH sequence, using RCPC channel code [20] to realize variable speed. The paper used the IEEE802.15.4a physical channel transmission model [7]. The simulation environment was 100 m by 80 m. The total transmission bandwidth was 2 MB/s, and coding rate was 8/11, 1/2, and 1/3 respectively. Considering the influence of the industrial field, the effective transmission radius was 30 m, and the size of the data packet was 32 bit/s. Routing protocol was DSR, and transmission protocol was UDP. Packets interval of each node obeyed Poisson distribution. Every simulation time was 300 s. The simulation scene of network was as shown in Figure 5. Sending node and the receiving node were static, and the node M was on behalf of the interference factors existing in the field. In order to simulate the industrial field environment, node M was moving, moving distance was from 1 M to 30 M, and rate was 1 M/s. In order to determine the validity of the protocol to interference, we changed each simulation movement rate and transmission power to increase the interference of the interfering node. It simulated mobile obstacles or sudden phenomenon such as power interference in the industrial field in order to verify the reliability and real-time performance of UWBIMAC protocol.

Local network simulation scene.
6.2. The Results of Simulation and Analysis
The throughput performance of five protocols was as shown in Figures 6 and 8. Figures 7 and 9 were the delay performance of MAC layer to real-time data using five protocols. The simulation results were shown in Table 6.
Simulation results.

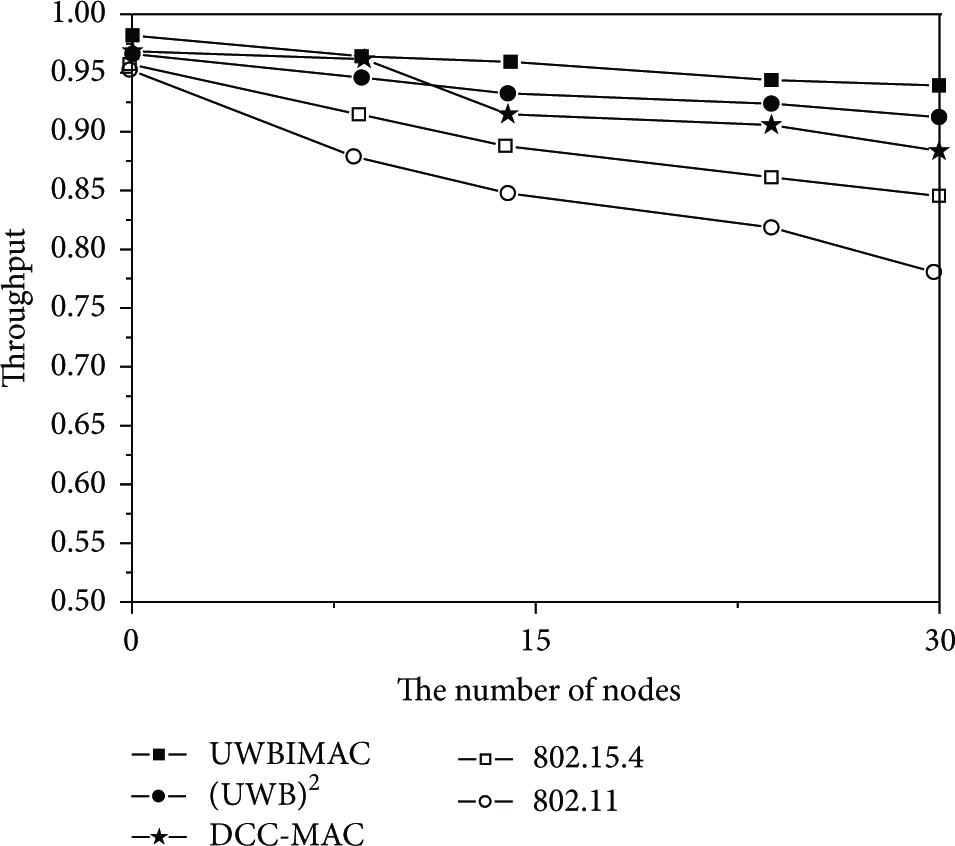
Throughput graph without interference.

MAC delay graph without interference.
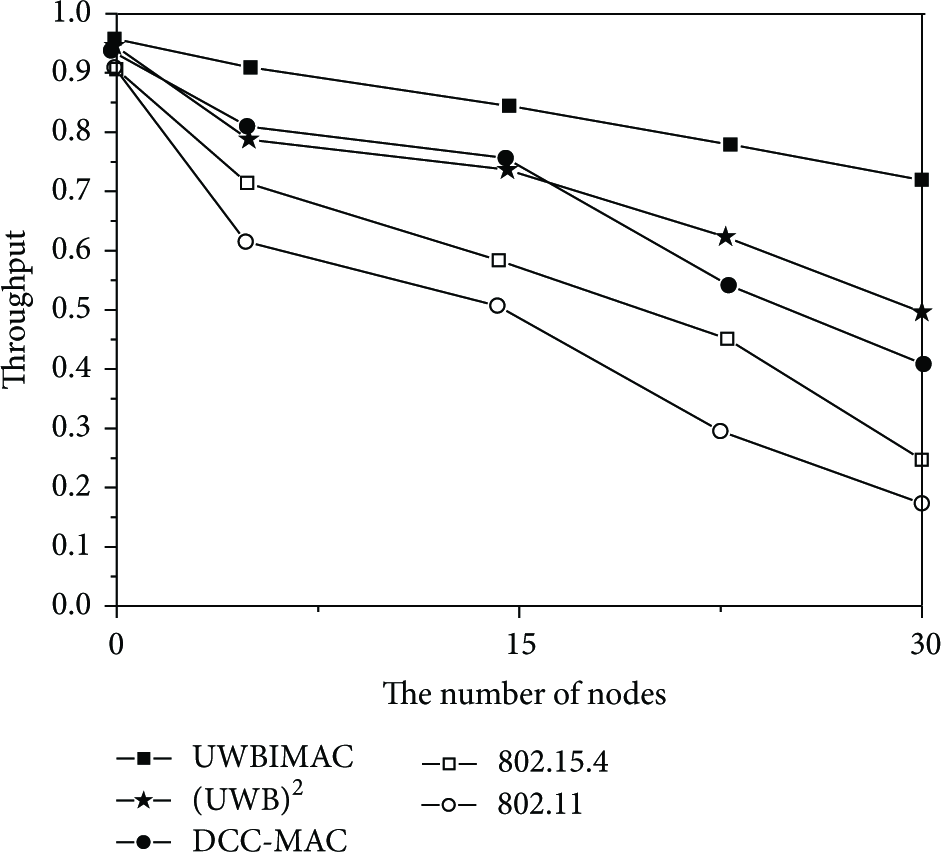
Throughput graph with interference.
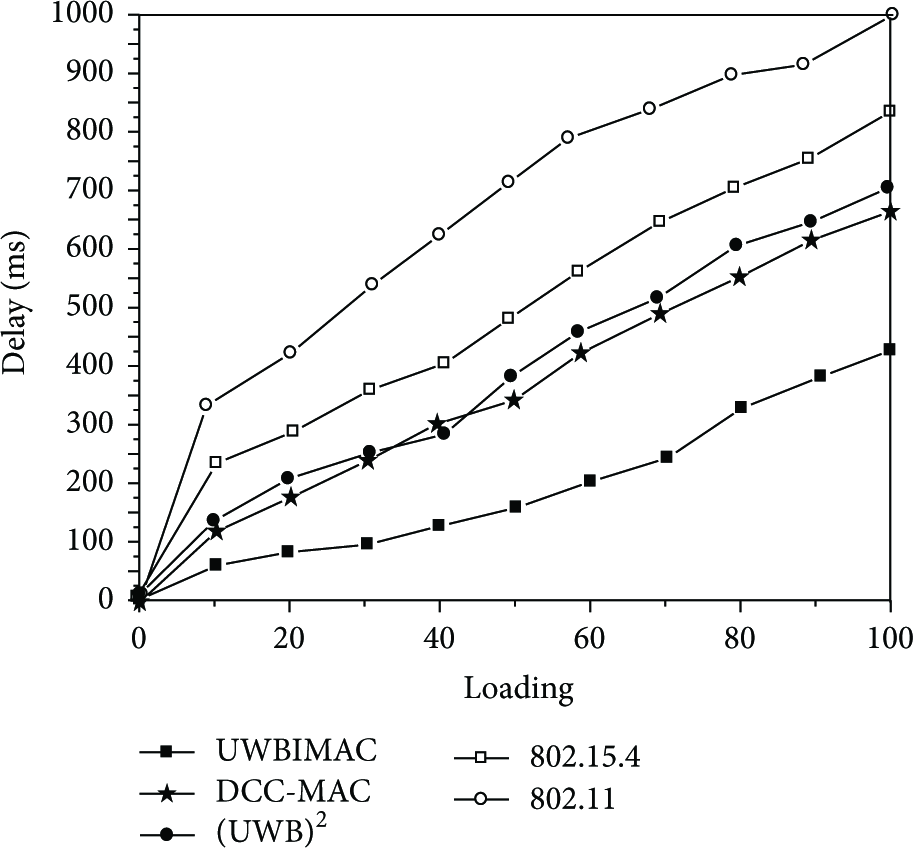
MAC delay graph with interference.
In Figures 6 and 7, under the condition of without outside interference, throughput and delay performance of multichannel UWBIMAC, (UWB)2, DCC-MAC, and IEEE802.15.4 protocols were superior to single channel 802.11 protocol, because more channel means lower competitive strength and the collision probability. The performance of (UWB)2 and DCC-MAC protocols were almost the same. Their performances were better than that of 802.15.4 protocol because they adopted the UWB technique, using the multichannel mechanism divided into the control channel and data channel. Compared with the frequency hopping multichannel 802.15.4 protocol, it had technical advantages of low conflict probability. At the same time the super frame mechanism in the 802.15.4 MAC protocol needs network synchronization, and the concurrent capability of data transmission of was relatively weak. The throughput and delay performance of (UWB)2 and DCC-MAC protocols were slightly lower than UWBIMAC. This was due to the existed problems of channel bottleneck. It limited the amount of channel used for transmission and caused that a large number of channels cannot be fully used. And these protocols were all lack of processing mechanism for real-time data; therefore under the same load, the delay of real-time data was above UWBIMAC protocol.
To compare and analyze transmission reliability and real-time performance under the interference condition, we increased the number of interference sources, and interference radius was 100 m. The nodes all worked under full loading. Figures 8 and 9 give throughput and delay performance contrasting curves of five protocols with interference condition. For UWBIMAC protocol, there was a slight decline in throughput. For the other 4 protocols, the throughputs are very obvious falling under the interference condition. When the nodes were up to 30, compared without interference, the throughput of UWBIMAC, (UWB)2, DCC-MAC, IEEE802.15.4, and 802.11 MAC protocols declined quickly. In Figure 9, there were great influences under the interference condition. When loading reached 100, the maximum delay of UWBIMAC protocol was about 400 ms, DCC-MAC protocol was about 650 ms, (UWB)2 protocol was about 700 ms, 802.15.4 MAC protocol was about 825 ms, and 802.11MAC protocol was about 1000 ms; it could be seen that minimal delay was UWBIMAC protocol. This showed that 802.15.4MAC, 802.11MAC, (UWB)2, and DCC-MAC protocols had no effective solution to the interference mechanism; the occurrence of interference can only adopt the method of multiple retransmission to solve interruption or error during data transmission. For single channel protocol 802.11, multiple retransmissions caused more congestion. Data channel conflict was more serious leading to throughput falling sharply compared to others’ protocols and delay increasing sharply compared to others’ protocols. For (UWB)2, DCC-MAC, and 802.15.4 MAC protocols, multichannel only partially solved problems of the single channel congestion and packet conflict. When the disturbance happened the retransmission methods still leaded to the bottleneck problem of the control channel. As there was no real-time data priority mechanism, so the real-time data transmission delay and loss phenomenon existed. When the network load was serious, it would cause a sharp dropping in throughput and delay increasing dramatically. Because the proposed protocol provided a channel selection, real-time data processing and the retransmission mechanism aimed at the interference phenomena.
Table 6 shows the simulation results of five MAC protocols. It showed that the proposed UWBIMAC protocol can reduce degradation of throughput and delay, especially under the condition of interference. Its performance was better than other four MAC protocols, and it was more suitable for real-time and reliable communication.
7. Conclusion
With the advance of wireless communication technology and intelligent mobile terminal equipment, users can conveniently access to the rich resources of the library. Users can rely on mobile terminals to enjoy library services. But wireless network can lead to instability because of wireless bandwidth, rate, and limited sending ability of the mobile terminal nodes. But we should also see that the service of the wireless digital library will be the important direction in the future, so the research and exploration are significant.
Aiming at the real-time and reliability of the wireless network in the library, the paper proposed wireless media access control protocol based on UWB technology. The simulation results show that the proposed protocol has a considerable advantage compared with the existing MAC protocols based on UWB and other existing wireless MAC protocols adopted other wireless communication technologies. We will research optimal back-off algorithm for control channel and reasonable BER threshold values and verify our simulation results in the actual UWB physical experiment platform. Our works would lay a good foundation for future applications. With the improvement of hardware equipment interoperability between standards, as well as the effective cooperation of library basic services, wireless technology will become one of the important information service platforms in the cloud and the mobile computing environment.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work is partially supported by National Social Science Fund Project (Grant no. 14BTQ038); International Science & Technology Cooperation Program of China (Grant no. 2014DFA11350); ISTIC Research Projects (Grant no. YY-201416).


