Abstract
Many cluster-based routing protocols had been proposed which had rarely considered the network security issues so far. The existing key management methods have imperfection when they combine with cluster-based routing protocols. Normally cluster-based key management method has better performance than the distributed key management method, but most of the layer-cluster key management methods do not consider the problem of key updating and being captured for cluster heads. Considering the nodes’ capture probability, particle swarm optimization algorithm was used to optimize the clustering of sensor networks. A dynamic key management method was proposed to achieve key updating regularly and provided a security strategy for sensor networks to solve the problem of being captured for cluster heads. The simulation illustrates that the proposed key management method can achieve better security performance.
1. Introduction
Sensor network security issues are becoming the focus of the industry recently [1, 2]. Because of limited storage space and computing power, lacking of a priori knowledge for later nodes deployed, and inability to guarantee the physical security in deployment region for sensor network, the traditional network security method is not suitable for sensor networks. Lightweight key management method, which aims to secure communication, becomes the most important and basic aspect of security research for wireless sensor networks [3–5].
According to the differences of topological structure, sensor networks can be divided into flat networks and layer-cluster networks. Layer-cluster wireless sensor networks have the advantage of high-energy efficiency. Recently, many scholars had proposed cluster-based routing protocols [6–8], which only considered the energy factor but paid no attention to security issues. Key management is an important way to protect the safety of clustering. Nodes are often deployed in the enemy area for monitoring, so they could be captured by the enemies. In particular in layer-cluster networks, cluster heads play an important role in the network. Once being captured, they will reveal more keys and information. It will threaten the safety of the whole network. This paper presents a kind of capture probability model of network nodes. The model considers the capture probability as network clustering, and the nodes which hold lower capture probability will be the cluster heads first. On the basis of this model, a dynamic key management method (DKMM) was proposed. The key management method can achieve dynamic key update and solve the problem of system security defense when the cluster heads are captured. The system simulation indicates that the proposed method based on clustering routing protocol has the features of lower storage consumption and strong ability of resistance to capture.
2. Related Work
There are many kinds of key management methods proposed [9–12]. In the field of distributed key management method, Eschenauer and Gligor (E-G) [13, 14] first presented a random key predistribution method. In this method, each node randomly selects m keys from the key pools before deployment. If the adjacent nodes at least have one same key, they can directly establish a session key. Chan et al. [15] also proposed a method based on the E-G method which is called q-composite key management method. In this scheme, the adjacent nodes can establish communication if they at least have q same keys. The connection rate of these two methods is lower, and the cost of keys storage is higher.
In the field of cluster-based key management methods, Zhu et al. [16] devised a method called LEAP. This method not only can support the processing inside the network, but also is a kind of key management method with fine ability of resistance to capture. In order to meet the different security requirements, LEAP supports the establishment of four types of keys. They are individual key, group key, clustered key, and pair key, respectively. It also provides the network node authentication based on one-way key chain. But its mechanisms of key update, revocation, nodes canceling, and nodes adding are not perfect, and clusters will dynamically be changed in practical applications. Jolly et al. [17] proposed a low-energy key management protocol that supports revocation for the attacked nodes. Since each node can only communicate with the cluster heads or base station, each sensor node only needs to store two symmetric keys in the key predistribution process. This method adopts the multilayer network architecture, which greatly reduces the energy consumption caused by the key management. However, this method has poorer network expansibility. The key update is not supported, so it increases the chance of being cracked by the enemy when using one kind of key in a long period of time. Du et al. [18] devised a key predistribution for heterogeneous sensor networks. This method takes the high-energy nodes as cluster heads, which can store a lot of keys and be equipped with tamper-proof hardware devices. The ordinary nodes will only be preloaded with a small number of keys. Compared with the existing random key predistribution methods, this method enhances the anticapture capabilities. But its storage overhead of keys is larger and the cluster heads are unable to be changed dynamically. Once being captured, the clusters will not work properly.
3. Network Model
The proposed DKMM method adopts the model of layer-cluster wireless sensor network, which is shown in Figure 1. We make some assumptions as follows.
The node has a unique ID and is randomly deployed in the monitoring area. After being deployed, all the nodes are stationary and energy-constrained. All nodes are with the same capacity, equal status. Once being captured, they would reveal the keys they had stored. Nodes can adjust the transmission power according to the distances. All nodes are aware of their position and perform the data collection tasks periodically. Data fusion technology can be used to reduce the amount of data transferred. The base station (BS) is trusted and has sufficient energy, and it can communicate with all the nodes in monitoring area. Once a node is captured, it will be detected immediately by BS.

Schematic diagram of sensor network model (BS is base station; CH is cluster head).
This paper also presents a model of capture probability of the network nodes shown as follows:
4. Clustering Based on PSO
Particle swarm optimization (PSO) is an algorithm based on iterative optimization [19]. PSO initializes particle swarm as a group of random solutions and then searches optimal solution in the solution space by following the current optimum particles. In the process of iteration, the particles are updated according to the two extreme values which are called the individual extreme value and the global extreme value. Thereinto, the individual extreme value is the optimal solution which is founded by each particle, and the global extreme value is the optimal solution which is founded by global particle swarm. Particle position and velocity can be updated by
The implication of parameters in PSO.

The clustering is based on centralized control strategy and realized by base station with unlimited energy. Polling mechanism is applied to protocol implementation, and each round includes two stages: the setting-up of clustering and steady state of clustering. After the nodes deployment, they will report the base station about the information of their position and energy. Because the base station knows the initial energy of all the nodes, it can estimate the energy consumption of the nodes by each round clustering information and gets node energy information after each round. The node's location is fixed. Therefore, nodes do not need to send the information of position and energy to the base station subsequently. According to application requirements and the circumstance of network operation, they will resend the information of position and energy after a long interval of cycle. The probability of nodes being captured will be considered in the process of clustering. The fitness function is set as follows: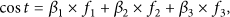

Figure 2 is the flowchart of PSO clustering, and the specific steps of PSO clustering are as follows.
Initialize S particles, and each particle contains K cluster heads randomly selected from the eligible candidates of cluster head. Node Find the individual and global best solution for each particle. Update the particle's velocity and position. Map the particle's location to cluster heads’ location. Repeat the above steps until achieving the maximum number of iterations.

Flowchart of PSO clustering.
It will get into the steady phase after building cluster, and then the cluster heads will complete the tasks as data collection and fusion. After a period of time, in order to ensure the safety of the system, it should update the clustering to repeat the process above.
The pseudocode of this PSO clustering is shown in Pseudocode 1.
Random initialization for velocity Map the particle's location to the nodes’ location according to the distance between the position of each cluster heads and the position of the nodes Calculate fitness
Update Map the particle location to the location of the eligible candidates of cluster head Calculate fitness of particles
Pseudocode 1
5. The Key Management Method for Sensor Networks Based on Dynamic Clustering
5.1. Key Establishment
Suppose N nodes are safe for a period of time after deployment, and they could not be captured by the enemy. Each node stores the initial key 
After receiving the information from each node, base station considers the probability of nodes being captured and makes the clustering by the method above. Then it will broadcast 
Each node, which is not the cluster head, decrypts the received information and then chooses the nearest cluster head to join in according to the location information. They also calculate the session key and a cluster key which are used for communicating with cluster head and base station, respectively. After establishing three kinds of session keys, the initial key 


After receiving the information, cluster head will calculate the session key for communicating with base station:
Then
After calculating according to formula (7)~(10), the base station will obtain the session keys used for communication with all the nodes and the cluster keys of all the clusters, and then it will tell the cluster heads about all the information of its corresponding nodes assigned to them by
5.2. Key Update
In the stable transmission phase, if the key was used for a long time, it will have the risk to be cracked by the enemies; so the key needs to be updated. Key update will be launched by the cluster head, and each cluster head needs to calculate the formula 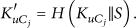
5.3. Key Establishment in Clustering by Polling
Suppose time T of establishing the cluster is less than time
Each noncluster head node decrypts the received information and then chooses the nearest cluster head to join in according to the location information. They also calculate the cluster key and the session key which are used for communicating with cluster head, while updating the session key used for communicating with the base station. After establishing the session key, 

The base station tells cluster head the information of its corresponding nodes assigned in its cluster by
5.4. Key Revocation
If the base station found a noncluster head node captured, it would tell cluster head to delete the keys related to the captured node by the key used to communicate with the cluster head. If the captured node was cluster head, the base station would find the node whose energy is greater than the average energy of the nodes in the cluster and its probability of being caught is the smallest, and let it be the new cluster head. As the cluster head does not store the cluster key in the key establishment process, the base station would transfer the information m about the captured cluster head and the information of the new cluster head, as well as the key update parameter 
After the nodes in cluster received the message, the session key for communicating with old cluster head will be deleted, and a new session key for communicating with the new cluster head will be created:
The base station passes the information about the nodes in cluster to the new cluster head by
6. Performance Evaluation
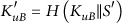
We would evaluate the performance of our proposed key management method from the aspects of connectivity, storage overhead, communication overhead, and security by system simulation. In the simulation experiment, 100 nodes are deployed in the area of 100 × 100 m2. We adopt the wireless communication model proposed in literature [10]. If we transmit k-bit message and the transfer distance is d, the energy consumption of transmitter can be expressed as 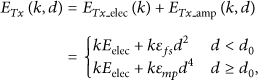
When receiving k-bit data, the energy can be consumed as 
6.1. Comparison of the Capture Probability of Cluster Heads
DKMM was proposed based on the type of layer-cluster network structure. Cluster heads are the key nodes in the network which contain a large number of keys. The keys will be revealed when the cluster heads are captured, and rebuilding the cluster needs a great deal of energy consumption. Therefore, nodes with lower capture probability should be selected as cluster heads in the clustering process. The clustering method with particle swarm algorithm considering the probability of nodes being captured (PSO-G) will be compared with the clustering method with particle swarm algorithm without considering the probability of nodes being captured (PSO-C). The simulation parameters are shown in Table 2, and the curves of capture probability model of the nodes are shown in Figure 3.
Simulation parameters definition.


The curves of capture probability model of the nodes.
In PSO-C method, nodes whose energy is greater than the average energy of the nodes can be a candidate of the cluster heads. PSO-G2 is a kind of clustering method based on PSO-C which considers the capture probability of the nodes. PSO-G1 is also a kind of clustering method based on PSO-C which not only considers the capture probability of the nodes, but also makes the nodes whose energies are more than half of the average energy become the candidates of cluster head. Normally the time duration from the starting to the time when the first dead node appears is defined as the survival time of the network. Figure 6 shows that the first dead node in PSO-G1 appears on the 203rd round, PSO-G2's first death node appears on the 216th round, and the PSO-C's first death node appears on the 218th round. The average capture probability of cluster heads in PSO-G1 and PSO-C is shown in Figure 4. In order to analyze better, capture probability value of a cluster head could be taken in every ten rounds, and it is shown in Figure 5.

The average capture probability of cluster heads in each round.
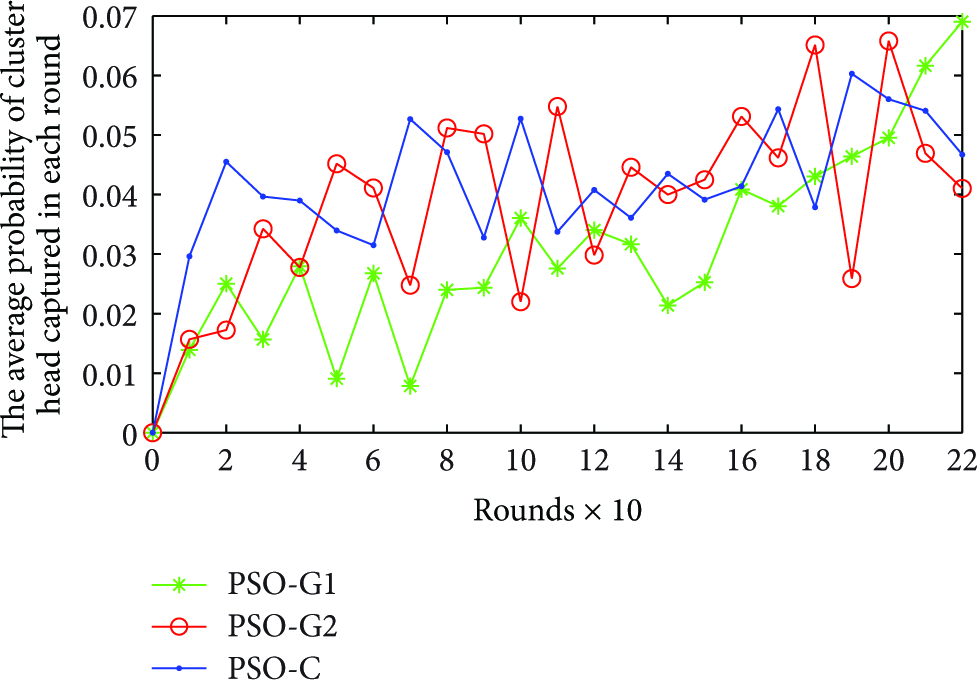
The average capture probability plot of cluster heads of PSO-G1 and PSO-G2 compared with PSO-C (get the average capture probability of cluster heads in every 10 rounds).

The curves of the network lifetime for three methods.
As shown in Figures 4 and 5, in front of the 203rd round, we can find that the average capture probability of cluster heads in PSO-G1 is lower than PSO-C's in the process of nearly 90% rounds, and the average capture probability of cluster heads in PSO-G2 is lower than PSO-C's in the process of more than 60% rounds. It indicates that the cluster heads will be safer if they are selected by considering the capture probability of the nodes. In PSO-G1 method, we can choose the nodes with lower capture probability as cluster heads, since it reduces the influence of energy for electing the cluster heads. There exist more candidate cluster heads for electing. However in PSO-G2 method, only the nodes whose energies are greater than the average energy can be the candidate cluster heads. This shrinks the range of selecting for cluster heads. Thus we can draw a conclusion that the security of cluster heads which are selected by PSO-G1 is better than the thing in PSO-G2. In Figure 6, the network lifetime and energy balance of PSO-G1 are all worse than PSO-G2 and PSO-C. Its first dead node appears only ahead of 15 rounds compared to the others. PSO-G1 has greatly improved the security of the network by sacrificing a little network survival time, so it can be acceptable from the view of the whole process.
6.2. Storage Overhead
The storage space of sensor network nodes is limited, so it is necessary to reduce consumption of node's key storing under the condition of safety. In DKMM, each node needs to store one cluster key and two session keys which are used for communicating with base station and cluster heads. At the same time, cluster heads need to store keys which are used for communicating with nodes in its cluster and base station. Assuming that there are N ordinary nodes and M number of cluster heads in the network, so it needs to store
In the E-G method, each node needs to store a large number of keys in advance. In order to guarantee the connectivity rate reaching 0.5, it is necessary to store 75 keys for each node when the size of the key pool reaches 10000. In q-composite method based on E-G, it will store more keys to keep the same connectivity rate compared with E-G. If each node selects m keys from the key pool randomly, the number of keys of storage in E-G will be equal to
In the PKAS [20] and MUQAMI [21] schemes, the storage space requirement will be equal to
Figure 7 shows the comparison of key storage consumption regarding DKMM with the methods of E-G, PKAS, and MUQAMI.

The comparison of key storage consumption regarding DKMM with E-G, PKAS, and MUQAMI.
6.3. Energy Consumption
In the strategy of DKMM, the nodes only need to receive the updated parameters of secret keys transmitted from base station to get their session secret keys by the one-way hash function. So its energy consumption is lower. Because the energy consumption of calculation is smaller compared with the energy consumption of communication, we only consider the total communication energy consumption of the nodes while setting up the keys. Based on this circumstance, the comparison of energy consumption for DKMM, E-G, and CECC [22] is shown in Figure 8. It is clearly observed that the communication energy consumption for setting up keys of DKMM is the lowest one.

Comparison of communication energy consumption for setting up keys regarding DKMM with E-G and CECC.
7. Security Analysis of the Scheme
The cluster head is the key node in the layer-cluster network structure, which contains a large number of keys. It will reveal a lot of information once being physically captured by the enemies. Rebuilding clusters will also consume a lot of energy. So in order to guarantee the security and effectiveness of the network, we should select the nodes with lower capture probability as the cluster heads when building clusters.
Clustering by PSO with consideration of the capture probability factors of the nodes can ensure the nodes with lower capture probability to become the cluster heads. As illustrated in Figures 4 and 5, we can find that the cluster heads of PSO-G1 and PSO-G2 have lower capture probabilities than PSO-C in the most part of the iteration process. After the first dead node appearing, the average capture probabilities of cluster heads of PSO-G1 and PSO-G2 start to be higher than PSO-C. The reason is that the nodes with lower capture probability will be the cluster heads with many times, and their energy consumption will be greater, so most of the dead nodes will be this kind of secure nodes. With energy reducing of these nodes, energy becomes the major factor of electing the head clusters. That is why the cluster heads’ average capture probabilities of PSO-G1 and PSO-G2 are higher than PSO-C after the first dead node appearing, and it goes up quickly. Fortunately, after the first dead node appearing, it is out of the network's normal life time; so, in the normal life cycle of the network, clustering with PSO-G1 and PSO-G2 is more secure than PSO-C.
As Figure 5 illustrates, the security of cluster heads elected with PSO-G1 is higher than PSO-G2 from an overall perspective. The energy threshold of PSO-G1 for selection of candidate cluster heads is lower than PSO-G2; it reduces the influence of energy for cluster heads’ election in PSO-G1, so it leads to emerging more candidate cluster heads in PSO-G1. This brings the chance to select more nodes with lower capture probability to become the cluster heads. But, in PSO-G2, only the nodes whose energies are greater than the average energy of the nodes could be the candidate cluster heads, this shrinks the scope of cluster heads’ selection. So the security of cluster heads elected by PSO-G2 is lower than PSO-G1. Although the network survival time and the balance of energy consumption of PSO-G1 are not as good as PSO-G2 and PSO-C and the round of its first dead node appears ahead of 13 rounds and 15 rounds, respectively, compared to PSO-G2 and PSO-C, the network survival time and the balance of energy consumption of PSO-G1 are still better than LEACH protocol. PSO-G1 greatly improves the security of the network by sacrificing a little balance of energy consumption of the network. This kind of sacrifice is acceptable and valuable indeed.
In the scheme of DKMM, the keys of each node communicating with base station or cluster heads are different from each other. When a node is captured, it will not reveal the communication keys between other nodes. Cluster heads, as the key nodes in the network, will be selected from the more secure nodes as clustering. When a cluster head is captured, the base station will select a new cluster head according to the residual energy and capture probability of the nodes within cluster, and it will inform the nodes within cluster by cluster keys. Therefore the antidestroying ability of DKMM is better. When the node is captured, it will not influence the secure communication between other nodes.
For the widely used dynamic key management scheme of EBS matrix method [23], when multiple nodes are captured within cluster at the same time, the captured nodes could obtain the whole EBS key set of the cluster by sharing their respective keys. This will make the whole cluster lose the security and seriously threaten the safety of whole network. But in the scheme of DKMM, even though multiple nodes are captured within a cluster at the same time, this will not reveal the keys between other nodes. So DKMM has higher security. For LEAP key management method, it also has fine antidestroying ability, but each node needs to store cluster key which is shared by the whole network. Once a node is captured, the update of keys will consume a lot of energies.
8. Conclusion
This paper puts forward a probability model of nodes being captured. We not only consider the energy in the case of dynamic clustering, but also take the capture probability of nodes into consideration. A kind key management method named DKMM was proposed, and this key management strategy makes more secure nodes most likely have the chance to become the cluster heads. Although considering the safety of the cluster heads while clustering, the cluster heads may still be possible to be captured. So DKMM method considers the possibility that the cluster heads may be captured. By the realization of the cluster head's reselection mechanisms and the dynamical updating mechanisms of the keys, we can minimize the risk of information leaking due to the cluster heads’ capture.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work was supported by the National Nature Science Foundation of China (no. 61273068), Nature Science Foundation of Shanghai (no. 12ZR1412600), and Scientific Research Innovation Project of Shanghai Education Committee (no. 13YZ084).


