Abstract
We study opportunistic decode-and-forward relaying transmission in cooperative cluster-based wireless sensor networks (WSNs) with secrecy constraints, where a passive eavesdropper may overhear the source message. To deal with this problem, we consider the novel opportunistic relay section cooperative transmission for the cluster configuration of WSNs. The system performance in terms of the secrecy outage probability and the probability of nonzero secrecy capacity are analyzed and the exact closed-form expressions are derived over Rayleigh fading channels. Furthermore, we derive the asymptotic secrecy outage probability which accurately reveals the secrecy diversity order. Finally, numerical results are presented to verify the theoretical analysis and depict that node cooperation has a great potential to enhance physical layer security against eavesdropping.
1. Introduction
In recent years, wireless sensor networks (WSNs) have gained worldwide attention for use in different applications, such as military target tracking and surveillance, natural disaster relief, biomedical health monitoring, and industrial automation. Because of the low computational capabilities of wireless motes, their limited battery lifetime, and the broadcast nature of wireless communication, WSNs present significant challenges in designing security schemes [1]. Especially the distribution of the key and the high computational complexity of the traditional cryptographic techniques are at the heart of any security design.
In the last decade, physical layer security (PLS) was drawing a lot of attentions as an alternative technique to achieve secure communication by exploiting the physical characteristics of wireless channels. This work was pioneered by Shannon in [2] and further extended by Wyner in [3]. To improve physical layer security of wireless transmissions, some recent works were proposed by exploiting cooperative diversity [4]. The achievable secrecy rates in cooperative relaying schemes using amplify-and-forward (AF) and decode-and-forward (DF) protocols have been investigated in [5–7], respectively. The secrecy outage performance for DF relay beamforming scheme is considered in [8]. Almost all of the above works are under the assumption that the eavesdropper's channel state information (CSI) is known at the transmitter. Clearly this assumption is sometimes impractical, such as the case of passive eavesdropping, where the instantaneous CSI of the eavesdropper's channel is not available at the transmitter and only an estimation of the average channel gains can be performed. The authors of [9] have proposed a joint cooperative beamforming and jamming scheme to enhance the security of an AF cooperative relay network without the CSI of eavesdropper. The proposed relay selection scheme in [10] selects a trusted relay to assist the secondary transmitter and maximize the achievable secrecy rate for cooperative cognitive networks. Considering no knowledge of the eavesdropper channels is available at the transmitter, the authors in [11] investigate the secrecy outage performance of conventional relay selection scheme. Specially, [11] only focuses on the high SNR regime where all the relay nodes successfully decode the source transmission. Different from [11], the other secrecy performance, that is, the intercept probability and secrecy diversity order, has been derived for several of AF and DF relay selection schemes without any knowledge of the eavesdropper channels in [12]. However, most of previous works focus on general cooperative communication scenario; thus, the security transmission strategy and analysis framework should be modified a lot in cooperative WSNs. On the other hand, cooperative transmission or virtual MIMO has been explored to increase the energy efficiency and improve the reliability of cluster-based WSNs [13, 14]. To the best of our knowledge, there are very few works making use of cooperative transmission to enhance the wireless security against eavesdropping attack in WSNs. In addition, the above observations raise two questions: (1) can cooperative transmission improve the secrecy performance for cluster-based WSNs? (2) How to design the optimal cooperative transmission scheme to enhance the wireless security for cluster-based WSNs?
To address these questions, we study physical layer security transmission in cooperative clustered WSNs in presence of a passive eavesdropper. In order to achieve cooperative diversity to enhance physical layer security, we design a novel opportunistic relay selection cooperative transmission scheme through exploiting the special cluster configuration of WSNs, which includes two time slots: the Intracluster Slot, used for data sharing within the cluster, and the Cooperation Slot, used for transmission from the best node chosen in cluster to the date gathering node faraway. Different from the conventional relay selection scheme, our proposed cooperative transmission scheme chooses the best node among the source and the capable decoding nodes considering the special structure of clustered WSNs. The exact closed-form expressions of the secrecy outage probability and the probability of nonzero secrecy capacity for our opportunistic relay selection cooperative transmission are derived over Rayleigh fading channels. Furthermore, we derive the asymptotic secrecy outage probability which accurately reveals the secrecy diversity order performance and shows the secrecy diversity order as
2. System and Channel Model
We consider a clustered WSN with sensors grouped in cooperative clusters (see Figure 1), similar to [12]. Throughout this paper, we consider that there are one source-destination pair (S and D), one eavesdropper E, and N relays, where all nodes are equipped with a single antenna. Such a scenario has applications in wireless sensor networks [13, 14]. Quasistatic fading has been assumed.

Cooperative transmission in clustered wireless sensor networks.
Clustering of sensor nodes is carried out following the opportunistic DF relaying transmission scheme against eavesdropping attacks. When a sensor node has confidential data to transmit, it first broadcasts these data within its cluster, and the other nodes in the cluster decode the received signals. Next, the source and the decodable nodes as relays will act together and perform opportunistic DF relaying scheme, in which the node with the best SNR to the destination among the source and the decodable relays is selected to retransmit/forward the signal encoded by the widely adopted wiretap code [3]. Noticing that, during the first slot, the source talks to the surrounding relays with low power, whereas the destination and eavesdropper are far away from the source and relays and cannot hear such a transmission, and the eavesdropper only can hear the signals in the second slot. We consider a passive eavesdropper, as such the CSI of the eavesdropper's channel is not known at the source and relays. Thus, from eavesdropper's point of view, the optimum node selection for main channel in the second slot is a random node selection for the eavesdropper channel, as the main channel and the eavesdropper channel are uncorrelated.
In the first slot, the source node broadcasts its confidential message with the power
When the capacity is larger than a targeted secrecy data rate
Without loss of generality, because the source and relays locate in the same cluster and are close to each other, we assume that all subchannels from the source to the relays and from the relays to the destination or the eavesdropper are symmetrical; that is,
In order to reduce complexity but still realize the potential benefits of multiple-relay cooperation for cooperative clustered WSNs, relay selection techniques designed for general cooperative communication scenario in [11] may have emerged as a promising solution. However, different from the conventional relay selection scheme in [11], our proposed cooperative transmission scheme has some modification aiming to the special structure of clustered WSNs. If the decoding set is empty, that is,
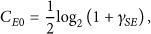
Thus, if the source retransmits the confidential message, the corresponding instantaneous channel capacity of the S-D link and S-E link is given, respectively, by
If the ith relay is selected and forwarded the confidential message, the corresponding instantaneous channel capacity of the
Hence, combining 4, 5, 6, and 7, the instantaneous secrecy rate is given by [13] as follows:
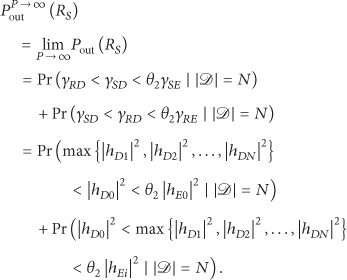
3. Exact Secrecy Performance Analysis
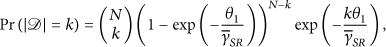
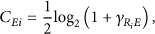
The secrecy outage probability is defined as the probability that the achievable secrecy rate is less than a given secrecy transmission rate
For
For
On the other hand, for
By combining 10, 11, and 12, the exact closed-form expressions of the secrecy outage probability are shown as
The secrecy outage probability expression in 13 is derived in closed-form and is useful to evaluate the impacts of the transmit power and the number of relays on the secrecy performance of cooperative clustered WSNs.
In addition, we note that 13 is useful to calculate other secrecy metrics, such as the probability of nonzero secrecy capacity discussed in [15]. As is known, positive secrecy is achievable when the mail link between legitimate users has better propagation conditions than the wiretap link from the legitimate users to eavesdropper. Thus, the probability of nonzero secrecy capacity for our opportunistic relaying transmission scheme is obtained as
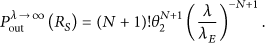
4. Asymptotic Behavior and Secrecy Diversity Gain
In this section, we turn our attention to the asymptotic analysis to characterize the behavior of secrecy outage probability when the average SNR of the main channel is sufficiently high. The asymptotic result will enable us to explicitly examine the impact of opportunistic relaying transmission on the secrecy performance in terms of the secrecy outage diversity order, which is the slope of the secrecy outage probability curve, describes how fast the secrecy outage probability decreases with the increase of the average SNR.
Without loss of generality, let
(
1) Case of
Considering that
Base on 16, it is worthy that increase of transmit power will not always lead to the improvement of secrecy performance, which is significantly different from the traditional wireless communication systems. Obviously, the SOP is independent of the transmit power in the high transmit power, and the secure outage probability is converge to constant values as the performance floors. Thus, the traditional diversity order [16], which characterizes the slope of bit error rate (BER) curve as SNR tends to infinity, is not applicable to measure the secrecy performance.
(
2) Case of
Using
From 18, we can observe that the SOP
5. Numerical Results
This section presents the numerical results to examine the impacts of the average SNRs and the number of relays on the secrecy performance. We see from the figures that the exact curves precisely agree with the simulations, which validate the accuracy of our analytical results. In all cases,
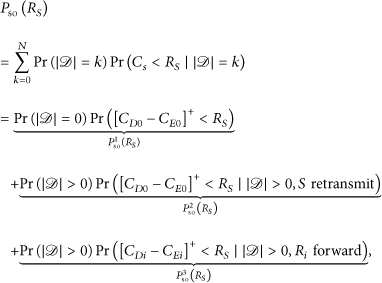
Figure 2 depicts the impact of the average SNR
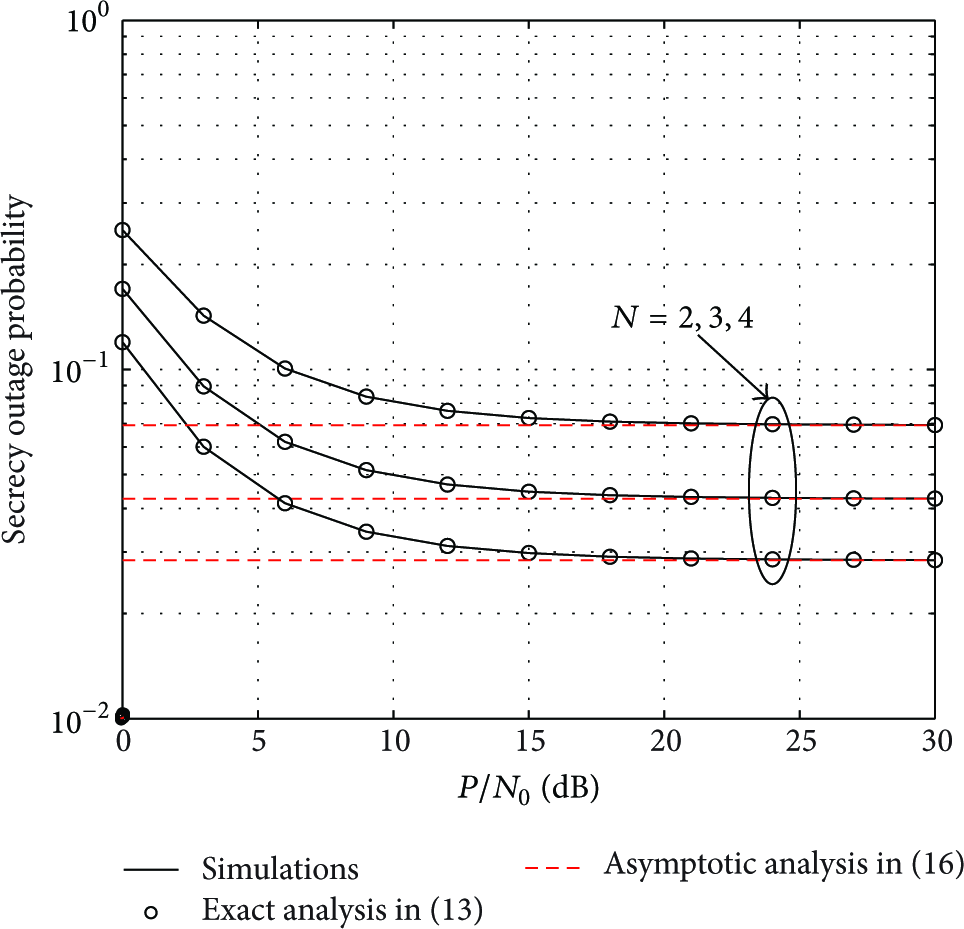
Secrecy outage probability versus
In Figure 3, the impact of

Secrecy outage probability versus λ.
6. Conclusions
In this paper, we investigate the physical layer security in cooperative clustered WSNs in presence of a passive eavesdropper. In order to exploit the cluster configuration of WSNs, we propose the novel opportunistic relay section cooperative transmission to enhance physical layer security. The exact closed-form expression of the secrecy outage probability for the opportunistic decode-and-forward relaying transmission scheme is derived over Rayleigh fading channels. In addition, the asymptotic behavior of the secrecy outage probability and the secrecy diversity order are discussed via two special cases. Both theoretical analysis and numerical results depict that node cooperation not only improves the transmission reliability and coverage performance of WSNs but also has great potential to enhance physical layer security against eavesdropping, and the achievable secrecy diversity order of our opportunistic relaying transmission scheme is
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This research was supported by the National Natural Science Foundation of China (no. 61371122 and no. 61471393) and the China Postdoctoral Science Foundation under a Special Finance Foundation (no. 2013T60912).