Abstract
For network users roaming in a wireless sensor network (WSN), they can broadcast queries to WSNs to obtain the latest sensed data from sensor nodes using their mobile devices. In such a scenario, each sensor node has to verify the validity of every query sent from users. In this paper, RSA-like public key cryptography is employed to design a mechanism for multiuser broadcast authentication in WSNs. Within the proposed scheme, the use of certificates becomes optional. When users broadcast queries to WSNs, each sensor node can verify every query immediately without buffering any one. As a result, the energy cost for verifying a query by a sensor node is very small. Furthermore, our scheme provides enough scalability and security. The quantitative analyses show that our scheme is efficient in terms of storage and computational overheads.
1. Introduction
Wireless sensor networks (WSNs) are widely used in various applications, such as building automation, mobile object tracking, and habitat monitoring [1, 2]. A WSN usually consists of one or more base stations and a large number of sensor nodes. Because the sensor nodes are resource-constrained and usually deployed in hostile environments, they are vulnerable to malicious attacks. Thus, broadcast authentication becomes a critical issue in WSNs, which can prevent adversaries from injecting bogus queries. Traditional schemes [3–8] applied the key pools, space pools of matrix or polynomials to establish the pairwise key between any two neighboring sensor nodes. Although these schemes can establish a secure communication channel, they cannot withstand injecting bogus queries.
Thus, three scenarios are considered in this paper. The first scenario is that users broadcast messages to WSNs using their own mobile device dynamically, and then each sensor node will verify these messages. The second scenario is that once malicious users are revoked by the base station, the action of rekeying will be triggered by the base station. The third scenario is that when new users join WSNs, the base station will take some appropriate actions for these users.
In this paper, an RSA-like scheme is employed to construct a multiuser broadcast authentication mechanism. Although it is usually thought that RSA is expensive for sensor nodes in terms of computational overhead, however, the authors in the work in [9] showed that the cost of the RSA signature verification is not really expensive. Because each sensor node only needs to verify the RSA signature, the computational cost for a sensor node to verify a message is acceptable. As reported in [10], public key cryptography is viable on an Atmel ATmega128 at 8 MHz for resource-constrained sensor nodes. The authors tested and implemented elliptic curve point multiplication and RSA operations on two 8-bit microcontrollers with assembly languages. Elliptic Curve Cryptography (ECC) is more computationally efficient than RSA, but RSA can still be implemented for sensor nodes, such as Crossbow MICA Motes. For example, in the implementation of [10], it requires 0.81 s for 160-bit ECC point multiplication and 0.43 s and 10.99 s for RSA-1024 public key operation and private key operation, respectively. Furthermore, the Chinese Remainder Theorem (CRT) can accelerate RSA private key operations, namely, decryption and signature generation.
Broadcast authentication enables each sensor node to verify the received messages which are originated with the authorized source and were not modified. In our scheme, when a user broadcasts a query message to WSNs, each sensor node only has to verify the signature attached in the message using the public key computed by the base station. At the beginning of network initialization, the base station generates RSA public key and private key for each sensor node and each user, respectively. Once a user is revoked, the base station has to regenerate a new RSA public key for each sensor node. At the same time, other users do not have to change their own private key. So sensor nodes do not have to store a revocation list in their own memory. The main contributions of this paper are described as follows:
We propose an RSA-like scheme to secure the multiuser broadcast. Our scheme provides enough security with 1024-bit RSA and great scalability. In our scheme, each sensor node does not buffer any message, and it can verify every message immediately. Thus, the impact of DoS attacks can be mitigated. Once illegal network users are revoked by the base station, all the current users do not have to obtain new authentication information from the base station. On the other hand, there is no need for each current user to reobtain his/her private key from the base station after he/she has participated in WSN. Each sensor node only has to store one network public key, which is 1024 bits. No matter how many network users are there in WSNs, each sensor node can verify these messages. Therefore, our scheme is more efficient in terms of storage overhead as compared with the previous schemes. A quantitative energy consumption analysis on computational cost for verifying a message shows that our scheme indeed outperforms the previous schemes.
The rest of this paper is organized as follows. In Section 2, the related work will be introduced. In Section 3, the network and adversary models used in this paper are presented. Subsequently, RSA cryptosystem and the concept of RSA master-key will be described in Section 3. In Section 4, the proposed multiuser broadcast authentication scheme is presented. Section 5 is the discussions of our proposed scheme. Section 6 is the performance evaluation in terms of communication, storage, and computational overheads. The conclusion is made in Section 6.
2. Related Work
In order to prevent adversaries from injecting bogus queries, the authors in the work in [11] first proposed a scheme, called μTESLA, to overcome this problem. They employed a one-way hash function to generate a key chain for the authentication of broadcast messages. However, a source requires maintaining a long chain of keys for the long-term uses. In addition, μTESLA suffers from serious DoS attacks. Each sensor node has to buffer all received messages within a time interval, and then it can verify these messages by using the delayed disclosure key broadcasted by the base station at the next time interval. The base station and sensor nodes are assumed to be loosely time synchronized.
Furthermore, the authors in the work in [12] proposed a novel protocol called BABRA to address the problem of broadcast authentication in WSNs. Unlike μTESLA, BABRA can support broadcast for infinite rounds. At the same time, it eliminates the requirement of key chain. Nevertheless, BABRA also suffers from serious DoS attacks, since each sensor node has to buffer all messages before the corresponding key is disclosed.
In [13], the authors proposed a broadcast source authentication mechanism based on multiple MACs (Message Authentication Codes). The scheme requires sensor nodes to have different overlapping set of keys. When the source wants to broadcast a query, it uses its keys to compute multiple MACs and appends them to the message. Then, the recipient can verify the message based on the MACs by using the common keys shared with the source. In comparison with the above schemes, each recipient could verify a message immediately. Therefore, the impact of DoS attacks can be mitigated. However, the key predistribution under a hierarchical structure results in scalability issues. The authors in the work in [14, 15] proposed broadcast authentication schemes using one-time signature. As compared with the above schemes, each sensor node can verify a query immediately without buffering others. However, the number of signatures is limited when a lot of queries are signed by the source.
The authors in the work in [16] first proposed a protocol for multiuser broadcast authentication, in which any unauthorized user cannot broadcast queries to a WSN arbitrarily. Each authorized user may be equipped with a powerful mobile device, and then he/she can broadcast queries to WSNs for the purpose of obtaining the latest sensed data from sensor nodes in WSNs. Whenever a WSN processes a query, sensor nodes are able to verify the query. However, the user's public key certificate incurs additional communication and computational overheads.
In [17–19], the main idea of these schemes is to preload each sensor node/network user with some secret information. After that, sensor nodes can compute session keys shared between them and users. Hence, the authenticity of users can be verified through these session keys. All the above schemes are based on challenge-response protocols. Although the above schemes have been proposed for user authentication, most of them do not provide adequate efficiency. By contrast, some schemes in [20–22] focus on the mechanism, in which each sensor node can verify every query directly without challenging any nonce. These schemes provide adequate efficiency for multiuser broadcast authentication. However, it is still difficult to deal with the resource-constrained problem and sensor nodes compromise attack. An efficient scheme is proposed to address the problems without incurring much overhead.
The authors in the work in [16] proposed the first solution to the problem called authenticated querying. They utilized Elliptic Curve Cryptography (ECC) to construct the user authentication scheme, which only considered the situation that a user's query involves a single sensor node. Besides, this scheme incurs additional communication overhead because the user's certificate needs to be transmitted. Furthermore, each sensor node has to verify the user's certificate and signature. Obviously, it also incurs additional computational overhead. A fully symmetric key based solution was proposed for authenticated querying [17]. The authors used a bivariate polynomial to establish shared keys between the user and the sensor nodes that should process the user's query. Then, these sensor nodes can verify the authenticity of the user by using the shared keys between them and the user. The scheme is effectively tolerant of the sensor node compromise attack, but it still incurs additional communication overhead because the collection of MACs needs to be transmitted. In particular, when there are a large number of sensor nodes that should process the user's query, the collection of MACs will be big.
The authors in the work in [19] proposed a distributed user access control scheme, which includes local authentication and remote authentication. Unfortunately, this scheme incurs significant communication overhead, especially when the user's access control list is heavy. The reason is that the access control list needs to be transmitted. In [18], the authors proposed a user authentication scheme with the self-certified key (SCK) cryptosystem. The main idea is to establish pairwise keys between the user and his/her local sensor nodes. Then, these sensor nodes can verify the authenticity of the user. Because each sensor node is preloaded with a public/private key pair, the scheme suffers from serious sensor node compromise attack. An adversary may utilize the keying material of a compromised sensor node to impersonate a legal user to destroy the WSNs.
In [22], the authors initially proposed two basic schemes called CAS and DAS. In CAS, each user is equipped with a public/private key pair and his/her public key certificate signed by the base station, and then he/she signs every broadcast message with his/her private key. Upon receiving the message, each sensor node can verify the public key certificate of the user by using the public key of the base station. Finally, each sensor node can verify the message the user broadcasts in the WSNs. However, the certificate has to be transmitted and verified by each sensor node. CAS introduces additional communication and computational overheads. In DAS, each sensor node has to store all the users' ID information and their corresponding public keys. However, the storage of DAS is neither efficient nor scalable. This scheme is not suitable for storage-constrained sensor nodes when there are a large number of users.
Subsequently, the authors proposed two advanced schemes called BAS and HAS. In BAS, each sensor node is required to store a Bloom filter and k hash functions. Upon receiving a message, each sensor node can check whether the user's ID and his/her corresponding public key are authentic by using the Bloom filter and k hash functions. However, the probability of a false positive (
The authors in the work in [21] proposed three broadcast authentication schemes. The first scheme is CAS as mentioned before, and the second scheme is based on Merkle hash tree. The base station first constructs a Merkel hash tree, in which each leaf node contains the hash value of a user's ID and his/her corresponding public key. Then, each sensor node has to store the value of the final root node of the hash tree. At the same time, each user has to obtain his/her auxiliary authentication information (AAI). When a user broadcasts a message to the WSNs, he/she signs the message and appends his/her AAI to the message. Upon receiving this message, each sensor node can verify the user's public key by using AAI. If the final hash value is equal to the value of the final root node, each sensor node can verify the user's public key. The Merkle hash tree based scheme does not require the users' public key certificate to be transmitted. In addition, this scheme can be improved by increasing the number of stored hash values in each sensor node. Thus, the size of AAI can be reduced. However, once a user is revoked by the base station, each current user has to obtain his/her updated AAI from the base station. It is impractical for the current users. The third scheme is an ID-based authentication scheme. The concept of ID-based cryptography originated from [23]. A user's ID is just like the user's public key. In this scheme, the user's public key is
An ID-based signature scheme called BNN-IBS [24] is based on Schnorr signature [25], and the authors in the work in [20] proposed a variant of BNN-IBS called vBNN-IBS with a smaller signature size. The proposed scheme called IMBAS [20] is also used to secure the multiuser broadcast. When a user wants to broadcast a message to WSNs, he/she signs the message using vBNN-IBS signature. The base station can also broadcast a message to WSNs with a smaller message size. Upon receiving a message broadcasted by the user (or the base station), each sensor node can verify it immediately. Furthermore, each sensor node also has to store the IDs of the revoked users as a revocation list infinitely when the number of revoked users increases unceasingly. As a result, it can be found that the public key cryptography is easier to be used for multiuser broadcast authentication than the symmetric key cryptography.
In [20–22], the authors used Elliptic Curve Cryptography (ECC) based schemes to secure multiuser broadcast authentication.
3. Preliminaries
First, the concepts of the proposed network model and adversary model are introduced. Then, the review of RSA public key cryptosystem and the concept of RSA master-key are presented in the section.
3.1. The Network Model
In this model, the sensor network consists of a base station and a large number of sensor nodes. The base station is assumed to be powerful, while sensor nodes are resource-constrained. Furthermore, there are a large number of network users. These users who roam in WSNs can use their mobile devices to broadcast queries to WSNs for the purpose of obtaining the latest sensed data. The mobile devices of the users are more powerful than resource-constrained sensor nodes in terms of computation, communication, storage, and energy abilities. The number of network users may be dynamic. In this paper, the WSNs time is assumed to be loosely synchronized.
3.2. The Adversary Model
We assume that the base station is always trustworthy, but sensor nodes may be compromised by an adversary. Therefore, there may be some malicious sensor nodes in the WSNs. The adversary is able to compromise or capture not only sensor nodes but also users' mobile devices, and then all the secret information (e.g., keying material or secret data) held by them is known by the adversary. In addition, the adversary may impersonate these captured users to broadcast bogus messages to WSNs. So these users of WSNs have to be revoked by the base station to prevent them from destroying WSNs. Furthermore, the adversary can flood bogus messages into WSNs to exhaust the precious energy of sensor nodes. Note that the adversary can also eavesdrop and resend the messages.
3.3. RSA Public Key Cryptosystem
We give an introduction to RSA public key cryptosystem. In RSA cryptosystem, each participant holds a public/private key pair, which is generated by a certificate authority (CA). The steps of generating the public/private key pair are described as follows:
(1) Two large primes p and q are randomly chosen, and then (2) To choose a parameter e, (1) have to be satisfied:
where (3) Finally,
Now, assume that A wants to send a message M to B. If A wants to prove the confidentiality of M, he/she can use B's public key
3.4. RSA Master-Key
The authors in the work in [26] proposed an RSA master-key scheme, which is built on RSA cryptosystem. Suppose that there are n entities CA randomly chooses large primes Let For Therefore, each
4. The Proposed Multiuser Broadcast Authentication Scheme
In this section, a scheme for multiuser broadcast authentication, which is based on RSA cryptosystem and the master-key scheme [26], is presented. The detailed steps of our scheme are described in the following sections.
4.1. Our Scheme
We assume that there are m network users in WSNs, and the base station is the highest authority. The task of the base station is to generate a private key for each user and assign a public key for each sensor node. We use the RSA-like scheme to secure the multiuser broadcast. When the event which a user joins or leaves happens, our scheme can cope with the situation. Furthermore, once a user is compromised, the base station will take an appropriate action to cope with such a situation. The steps of our scheme are described as follows.
4.1.1. The Setup Phase
First, the base station randomly chooses
4.1.2. The Key Generation Phase
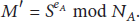
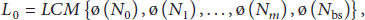
The base station computes the least common multiple
4.1.3. The Key Assignment Phase
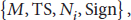
After finishing the above key generation, the base station can preload/broadcast each sensor node with
4.1.4. Multiuser Broadcast Authentication
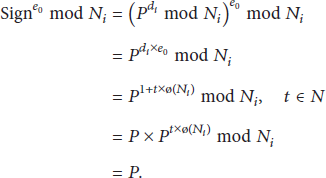
Assume that a user

The two-layer structure.
4.2. User Revocation
In our scheme, once a user is revoked, the base station has to regenerate a corresponding public key
4.2.1. The LCM Regeneration
The base station computes the least common multiple
4.2.2. The Public Key Regeneration
To update
4.2.3. The Public Key Broadcast
After regenerating
4.3. User Join
When a new user wants to join WSN, the steps are similar to the process of user revocation. Once a new user
5. Discussion
In this section, the scheme in terms of security, DoS attacks, and scalability is analyzed.
(1) The Problem of Factoring
(2) The Problem of Preventing the Unauthorized User. When an adversary impersonates a legal user
(3) Denial of Service (DoS) Attacks. According to [21, 27], μTESLA suffers from serious DoS attacks because each sensor node has to buffer all the messages received within one time interval. This problem can be mitigated by the immediate verification of messages. In our scheme, each sensor node can verify messages sent by legal or illegal users immediately, so our scheme can mitigate the impact of DoS attacks. If an adversary wants to broadcast forged messages to WSNs, this attack will be detected by the sensor nodes. And then they may notify the base station of such a situation.
(4) Scalability. When old sensor nodes exhaust their energy or the sensing region of a WSN has to be enlarged, new sensor nodes have to be deployed. Our scheme can deal with this problem by preloading these sensor nodes with the network public key
6. Performance Evaluations
In this section, the performance of our scheme in terms of communication, storage, and computational overheads is evaluated. Moreover, the scheme is compared with the previous schemes that were proposed for multiuser broadcast authentication.
6.1. Communication Overhead
In this section, our scheme and the previous schemes in terms of the communication overhead are evaluated. In [20–22], the authors used Elliptic Curve Cryptography (ECC) based schemes to secure multiuser broadcast authentication. To provide the same level of security strength as 1024-bit RSA, ECC requires p of 160 bits, if
Like the assumptions used in [21],
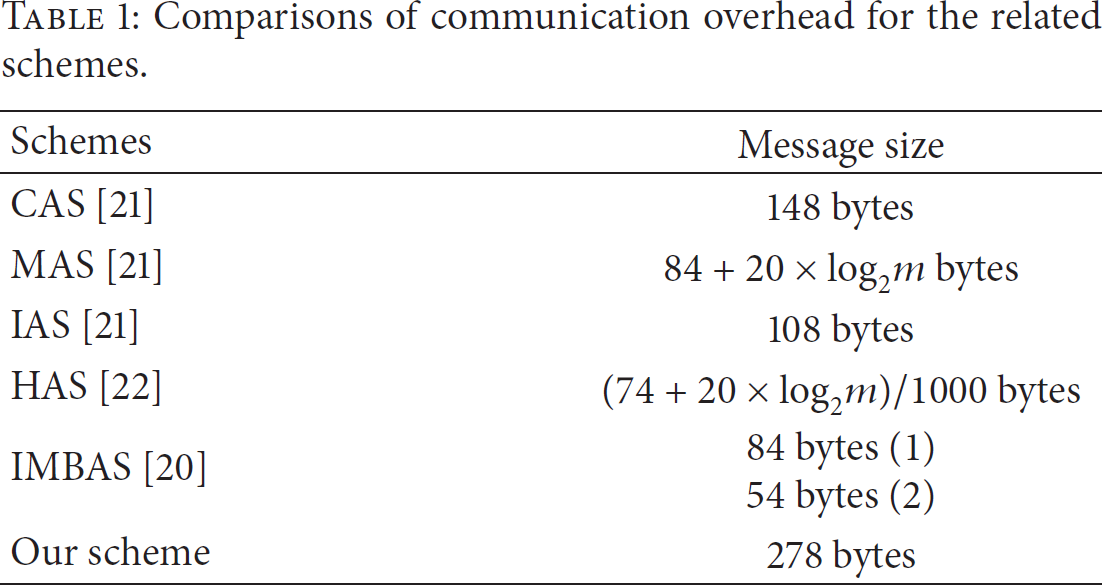
In this paper, 1024-bit RSA are applied to compare our scheme with the previous schemes. We recall that our broadcast message includes a user's ID
In the remaining part of this paper, we refer to the certificate-based, Merkle hash tree based, and ID-based authentication schemes [21] as CAS, MAS, and IAS, respectively. The parameter m denotes the total number of users.
In CAS, a broadcast message includes a message M, a timestamp
In HAS [22], the broadcast message includes a part message
In IMBAS [20], the message broadcasted by a user (situation (1)) includes a message M, a timestamp
Table 1 shows the comparisons of the different schemes in terms of message size. Furthermore, Figure 2 shows the evaluation results of the impact of the total number of network users on message size. When the number of network users varies from
Comparisons of communication overhead for the related schemes.

Message size versus the total number of network users.
In addition, we quantify the performance on message broadcast for the six schemes. We use the MICA2DOT mote which is a popular platform for WSNs. The MICA2DOT mote is equipped with the Atmel ATmega128L 8-bit microcontroller at 4 MHz and the Chipcon CC1000 low-power wireless transceiver [9]. As reported in [9], the energy consumption of MICA2DOT mote in active and power-down modes is 13.8 and 0.0075 mW, respectively. Furthermore, the MICA2DOT mote consumes 59.2 and 28.6 μJ to transmit and receive one byte, respectively.
In our scheme, the broadcasting message is
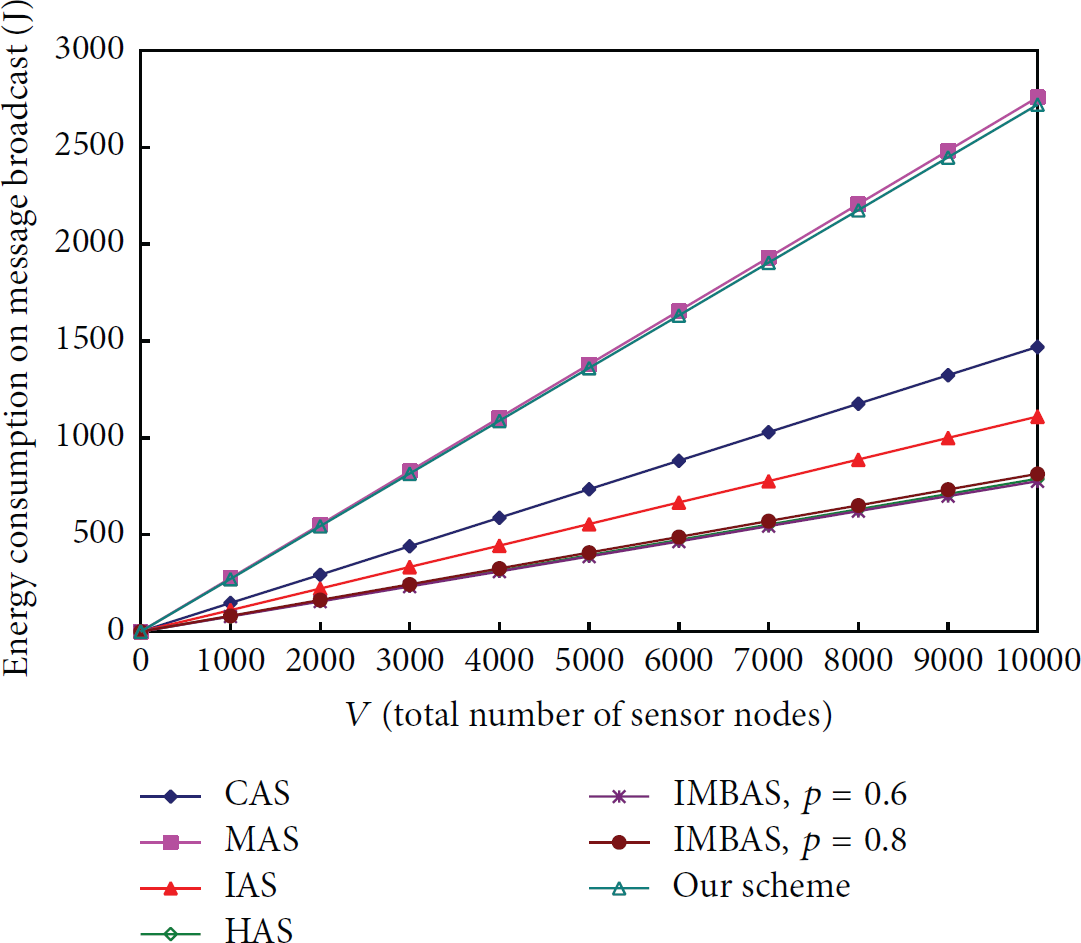
Energy consumption on message broadcast versus the total number of sensor nodes.

Energy consumption on message broadcast versus the number of neighbors for a sensor node.
6.2. Storage Overhead
In the comparison, the same settings are used as in Section 6.1. In CAS, each sensor node is required to store the ECC's parameters
In MAS, it requires each sensor node to keep the value
In IAS, each sensor node also has to be preloaded with the ECC's parameters
The parameters used by IMBAS [20] are similar to IAS's parameters not including
The comparisons of the different schemes are shown in Table 2. Clearly, it can be observed that most of the schemes outperform HAS in terms of storage overhead for each sensor node. In addition, from Figure 5, it can be observed that the storage size of our scheme is much less than HAS. Moreover, the storage size of HAS increases significantly when the number of network users varies from
Comparisons of storage overhead for the six schemes.


Storage size per sensor node versus the total number of network users.
6.3. Storage Overhead on Revocation List
An adversary may capture the devices of legal users, and then he/she can impersonate these legal users to broadcast bogus messages to WSNs for the purpose of exhausting the precious energy of sensor nodes. So the base station has to revoke these illegal users in WSNs. The previous schemes require each sensor node to store the IDs of revoked users infinitely when the number of revoked users increases unceasingly. For example, CAS, HAS, and IMBAS require each sensor node to store the revoked IDs. Therefore, the three schemes may incur a large amount of storage overhead.
In IAS, each sensor node stores the revoked IDs only within one time interval and removes them at the beginning of the next time interval because each user has to obtain a new private key from the base station at the beginning of each time interval. Instead, MAS and our scheme do not require each sensor node to store any revoked ID due to the update of
Figure 6 shows the comparisons of the storage size for the six schemes with respect to the number of revoked users. In addition, once an illegal user is revoked, MAS requires current users to obtain the updated AAIs regenerated by the base station. This may be impractical for the current users roaming in WSNs. In IAS, each current user also has to obtain a new private key from the base station at the beginning of each time interval, so it is still impractical for the current users. Table 3 illustrates whether or not current users have to obtain new authentication information from the base station.
A table illustrating whether or not current users have to obtain new authentication information from the base station for the six schemes.


Storage size per sensor node versus the number of revoked users.
6.4. Computational Overhead
In this section, the computational overhead of each sensor node will be evaluated by us. We focus on the computational overhead of verifying a message broadcasted by a user for each sensor node. Note that we still use the same assumptions as mentioned before for our evaluations. In order to compare our scheme with the other schemes in terms of computational overhead, we define seven notations as follows:
In CAS, each sensor node has to perform two ECDSA signature verification procedures and two hash function operations. In MAS, to verify the user's public key, it requires a chain of hash function operations, and we assume that there are λ hash function operations to be performed. In IAS, it requires one modular exponentiation operation in
According to [9], the energy cost to verify an ECDSA signature is 45.09 mJ in a MICA2DOT mote. Thus, we can estimate the time to perform an ECDSA signature verification is 45.09 mJ/13.8 mW = 3.267 s. We recall that 13.8 mW is the energy consumption of the MICA2DOT mote in active mode. Besides, assume that SHA-1 is used, and its energy consumption is 5.9 μJ/byte [9]. Therefore, the time to perform the SHA-1 hash function is 0.01 s when the input size is 24 bytes. Obviously, the time is very small, so it can be ignored.
For a MICA2 mote at 8 MHz, it takes 0.81 s to perform one point multiplication operation over an elliptic curve [10]. Thus, MICA2DOT mote roughly needs
According to [21], the MapToPoint hash function takes 3.0 ms, a modular exponentiation operation in
The cost of generating an RSA signature is higher than that of verifying an RSA signature, but it does not matter in our scheme. The reason is that signatures are generated by users who are equipped with mobile devices or the powerful base station. In our scheme, each sensor node is required to perform only one RSA signatures verification.
Table 4 shows the computational time of the six schemes for verifying a message. We can observe that the computational time of our scheme is significantly less than that of the remaining schemes. Furthermore, it can also be inferred that IAS introduces a much higher computational overhead as compared to the remaining schemes because it requires each sensor node to perform two pairing operations.
Comparisons of computational overhead for the six schemes.
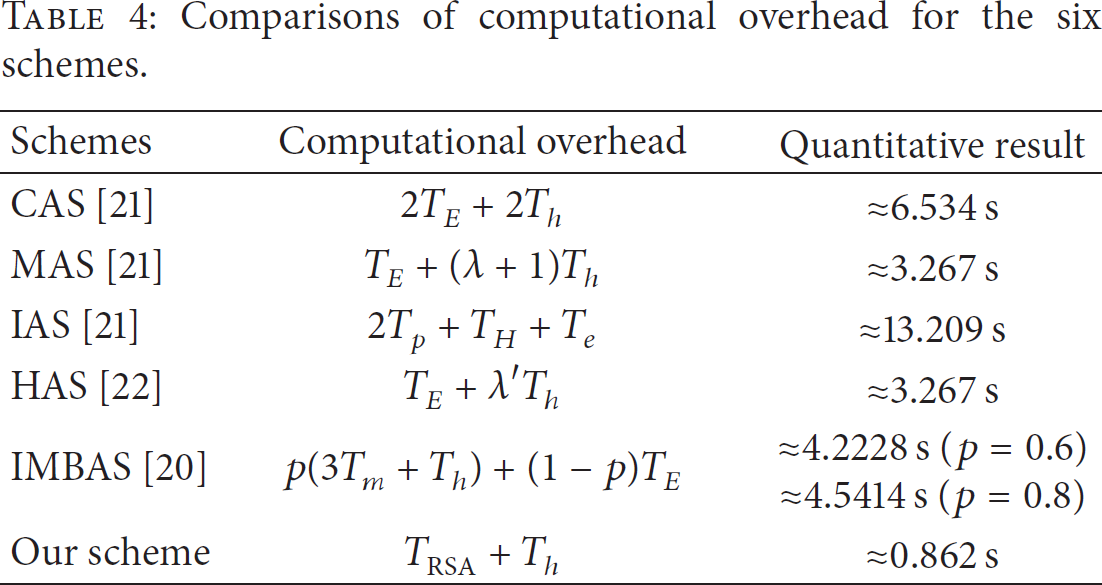
Figure 7 also shows the energy consumption of the schemes for verifying a message when the total number of sensor nodes varies from

Energy consumption for verifying a message versus the total number of sensor nodes.
7. Conclusions
In this paper, we propose an RSA-like multiuser broadcast authentication scheme in WSNs. Although it is assumed that RSA is unsuitable for resource-constrained sensor nodes, the energy cost to verify an RSA signature is still acceptable for the sensor nodes. The quantitative analysis on computational cost for verifying a message shows that our scheme is more efficient than the previous schemes. Moreover, the main cost of computation always falls in the base station which is trustworthy and powerful. In our scheme, the storage cost for each sensor node takes a network public key only. No matter how many users are compromised in WSNs, the storage cost for each sensor node is still invariable because it only needs to update the network public key. On the other hand, each sensor node is able to verify every message immediately, so our scheme can mitigate the impact of DoS attacks. As a result, although our scheme has bigger message size, it is still adoptable for the WSNs in terms of storage overhead, computational overhead, scalability, and security requirements.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.