Abstract
For distributed data storage in Unattended Wireless Sensor Networks (UWSNs), security issues have been focused on by extensive researches in recent years. In this paper, an enhanced, reliable, and secure data distribution scheme based on erasure codes for UWSNs is proposed, which adapt the MOVE-ONCE survival strategy. In the proposed scheme, two-hop neighbor set has been utilized as data shareholders of data distribution. Through the analysis, we can find that there is more number of candidate secure data holders in two-hop neighbor set than one-hop neighbor set. Thus our new scheme could further enhance both probabilistic Backward Secrecy (BSe) and the reliability on data retrieval. Theoretical analysis and dense simulations show advantages of our new scheme which is compared with several previous related schemes proposed for UWSNs.
1. Introduction
In the past decades, wireless sensor networks (WSNs) have attained tremendous attentions with development in microelectromechanical systems technology [1]. Unattended Wireless Sensor Networks (UWSNs) are the category of wireless sensor networks that operate without online data collecting entity. In UWSN, the mobile sink accesses network with irregular and even unpredictable frequency while data has to be secured by every node until the next visit of the mobile sink. This situation may happen for reasons as the sensing field is too far from the base station and sending data through intermediate nodes may result in weakening the security or increasing the energy consumption of the nodes close to the base station. UWSNs can be used typically for many military applications, where unattended underground, underwater, and airborne sensors are deployed in hostile environments to sense adversary activities [1–6]. A typical demonstration is LANdroids [7], where sensors are deployed in hostile environment, in order to collect some military information so as to upload it to affined vehicles upon their arrival.
Compared with original WSNs, UWSNs have more challenges on security. Since the mobile sink accesses network periodically for information collection, each sensor node must hold its data of measurements for a definite time. Intervals between successive sink accesses could be potential periods of attacks. The major attacks that we are concerned with are mobile adversary, which is denoted as ADV hereafter. ADV may roam in UWSN periodically by compromising and releasing sensors to establish knowledge on sensing data while absence of mobile sink happens. As sensing data is stored and accumulated in these sensor nodes, Forward Secrecy (FSe) is a critical requirement, which is to guarantee that there would be no revelation on precompromise data when sensors are compromised. Furthermore, ADV might release compromised sensors and then go to compromise other sensors in UWSN. Therefore, Backward Secrecy (BSe) is the second requirement, which is to ensure that there would be no revelation on postcompromise data. Furthermore, data reliability, that is, to retain accumulated sensing data survival when partial sensors could not work, is also very critical [8–10].
The main contribution of this paper is that we propose an enhanced secure data distribution scheme based on erasure codes, which adapt the MOVE-ONCE survival strategies. Our new scheme could further improve the probabilistic BSe and the reliability on data retrieval. Based on erasure codes scheme, well-designed values of m and n could be chosen to maximize both security and reliability more efficiently. We show that our scheme could offer better FSe, enhanced probabilistic BSe, and data reliability through theoretical analysis and dense simulations.
The organization of paper is as follows. Section 2 gives some related works. In Section 3, network assumptions, adversary model, design goal, and evaluation metrics are presented. Section 4 provides the detailed description on design strategies and the proposed schemes. Security and efficiency of our scheme are analyzed in Section 5. Then, we evaluate the performance by numeric simulations in Section 6. Finally, Section 7 is the conclusion.
2. Related Work
To deal with FSe and BSe issues in UWSNs, Ma and Tsudik [3] proposed DISH protocol using key evolution and sensor cooperation to provide FSe and BSe, respectively. The proposed protocol involves each sensor sharing an initial key with the sink. At any time, sensors are either healthy or sick. Healthy sensors are currently not compromised and their current keys are unknown to the adversary, while adversary knows the current keys of all sick sensors. FSe is obtained via key evolution. To gain BSe, each sensor requests random contributions from a set of randomly selected peers and computes its next key based on its prior key and all received randomness. With this cooperative approach, a healthy sensor always keeps healthy, as long as it is not compromised directly; however, a sick sensor could become healthy if it receives randomness from healthy peers. DISH has been evaluated analytically and via simulations; one notable observation is that the ratio of sick to healthy sensors tends to stabilize after a few rounds.
Di Pietro et al. [4] proposed a distributed self-healing scheme (POSH) which is based on proactive sensors cooperation. The core idea about POSH is that each sensor could supply the source of randomness for other sensors. Consequently, a sensor whose randomness is compromised could retrieve security and produce a new key unknown to ADV, if it acquires at least one “infusion” of randomness from a neighbor sensor whose randomness is secure and not currently compromised. Together with key evolution, POSH provides both FSe and BSe to deal with a powerful ADV.
Although these two schemes above are proposed to achieve FSe and probabilistic BSe in an UWSN where all sensors and all communications are reliable, they could not be resilient enough to sensor failure. To address this issue, Wang et al. [8] adopt secret sharing and Reed-Solomon (RS) Codes [11], in which some portions of whole data shares need to recover original sensing data, increasing data redundancy to offer resilience to sensor failure.
Since all these above schemes could not satisfy the overall secure and reliable requirements needed for UWSNs, Ren et al. [9, 10] proposed a data distributed scheme which is also based on RS Codes. Furthermore, Ren proposed an improved scheme considering that sensors might either be compromised or failing.
As we discuss below, although Ren's scheme could provide FSe, enhanced probabilistic BSe, and data reliability, it still has potential space to be improved; therefore, it could serve as a stepping stone for our work in this paper.
3. Problem Formulation
3.1. Network Assumptions
Assuming an UWSN which is composed of N sensors, the set of the sensors is denoted by
These sensors are strategically deployed, while mobile sink (MS) that accesses the UWSN to gather information stored in sensors periodically and mobile adversary (ADV) can compromise the sensors to learn all secrets on sensors. Once information is collected, sensors could be reset to its original status where no MS exists. Thus, ADV's attacks cannot be accumulative, so we focus on the discussion within one access interval, which could be denoted by T.
3.2. Adversary Model
The UWSNs impose some attacks on many aspects. Here, we just focus on an ADV that may cruise in the UWSN while the MS is absent. The ADV has the following abilities [3, 4, 10]:
The ADV could compromise k sensors at most, where The ADV could randomly choose some sensors to physically corrupt, such that these sensors may absolutely lose their functionality. The ADV could monitor all the communications between sensors. It could only eavesdrop between currently compromised sensors.
Without loss of generality, we adopt the following assumption [4]:
Time can be divided into several compromise rounds. At the end of every round, the ADV could choose a subset of at most k sensor nodes to compromise during the following round. At the start of every round, this subset from the last round would be released and the new subset would be compromised. There is the same duration between compromise and collection rounds. Moreover, they are all synchronized.
3.3. Design Goals and Evaluation Metrics
In this paper, ADV is interested in stealing data stored on sensors without being detected and can also monitor the communications of the compromised sensor [9]. Thus, the design goals of our proposed scheme are to ensure security and reliability of sensing data, dealing with the attacks by ADV.
As shown in Figure 1, we assume that ADV compromises a sensor

Scenario of attacking by ADV in UWSN.
We define the metrics to measure data confidentiality and data reliability.
Data Confidentiality. As in Figure 1, we further make some subdivision on data confidentiality: secrecy of sensing data generated before
Data Reliability. Distribution scheme should be enough resilient to failure of sensors so that sensing data could be retrieved even if some sensors have absolutely lost their functionalities.
4. Strategies and Improved Scheme
4.1. Constrained Optimization on Data Distribution
Since symmetric encryption for data distribution could not provide BSe, it only retains as long as sensors rely on themselves for data security. Ren et al. [9, 10] proposed the constrained optimization scheme for data distribution, where BSe could be guaranteed probabilistically if sensor cooperates with its neighbors, while data reliability is achieved similarly if sensor cooperates with its neighbors in order to increase data redundancy. We discuss this scheme as follows.
To provide FSe for sensor node
To deal with this issue, Ren et al. [9, 10] proposed an optimized scheme which is based on RS Codes. Assume each sensor has corresponding Probability Vector Maximum security without redundancy: under this situation, where Maximum security with redundancy: under this situation, where
We first set data redundancy as its upper bounder by
4.2. Improved with Survival Strategy
Based on the discussion in the above section, we now consider adapting the survival strategy to improve the data distribution scheme. From the network's aspect, there are three intuitive strategies [2]:
DO-NOTHING: the primal strategy is to do nothing; just leave sensing data resident on sensor which acquired it and simply wait for the MS. MOVE-ONCE: an alternative strategy is to move sensing data to another randomly selected sensor right after collection. These data then would be resident on their new data holders until MS access. KEEP-MOVING: the more complicated strategy is to move sensing data continuously; that is, at every round, every sensor moves its sensing data individually to another randomly picked sensor.
Since Ren's scheme [9, 10] can be considered as the data distribution which adapts the DO-NOTHING survival strategy, in this case neighbors of sensor with origin sensing data leave their data shares encoded by RS Codes resident on their own and wait for the MS; we would consider adapting yet another survival strategy to improve the security of data distribution scheme. As KEEP-MOVING is too heavy in the communication cost for sensor node, we choose MOVE-ONCE strategy, so that each neighbor sensor moves its data share to its neighbor sensor, which should be the two-hop neighbor of sensor with origin sensing data, right after first data distribution by RS Codes. In this case, the shareholders of data distribution are two-hop neighbor of sensor with origin sensing data, rather than sensors in neighbor set
4.3. Scheme Description
The improved data distribution with MOVE-ONCE strategy is described as follows.
Step 1 (network initialization).
Sensor nodes exchange their ID and prior security level ID; prior security level; immediate neighbor,
where immediate neighbor is the way that the sensor can send data to its two-hop neighbor.
Step 2 (security initialization).
The MS adapts a specifically secure hash function denoted by
Step 3 (data encryption).
And then this is encrypted by utilizing key
Then,
Step 4 (data shares generation).
Step 5 (data distribution with sensor selection).
Step 6 (data reconstruction).
MS gathers any m survival data shares from these sensors and recovers sensing data based on
5. Security Analysis
5.1. Forward Secrecy (FSe)
It is very hard that ADV could derive previous key from the current key it acquires as a characteristic of hash function. Hence, even if ADV compromised the sensors to get enough data portions, it only obtains the whole
5.2. Backward Secrecy (BSe)
The probabilistic BSe can be guaranteed which is similar to that in Ren's scheme [9, 10]. However, we will prove that our scheme outperforms it in BSe.
Lemma 1.
BSe of sensor the sensor the ADV has the ability to compromise k sensor in UWSN, where the ADV compromises at lowest m two-hop neighbor sensors of
If all three conditions are met, probability
Proof.
Since ADV could compromise the BSe if ADV could compromise
Since the major difference between our scheme and Ren's scheme is the candidate shareholder set of data distribution, two-hop neighbor set versus one-hop neighbor set, it is important to show which candidate set is better in this context.
Lemma 2.
Assuming sensors are distributed in deployment region uniformly, the expected number of two-hop neighbors is higher than that of one-hop neighbors with different node degree.
Proof.
We will prove Lemma 2 according to the mathematic model in [12]. Assume N sensors distributed in the deployment region uniformly, and then arbitrary sensor
Assume

Effective two-hop neighbor.
The expected number for one-hop and two-hop neighbors,

Excepted number of one-hop and two-hop neighbors.
Since there are more sensors in two-hop neighbor set than one-hop neighbor set, the sensors with different compromise probability are distributed uniformly, and we can deduce that two-hop neighbor set offers more possibilities to find sensors with high security level to become the data shareholders. Overall, two-hop neighbor set is better candidate shareholder than one-hop neighbor set for security of data distribution, and then our scheme outperforms Ren's scheme in BSe.
5.3. Data Reliability
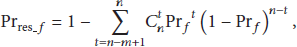
MS could recover original sensing data when the number of failure sensors n is lower than the threshold number n-m. Thus, probability of recovering data as function of sensor failures can be expressed as
5.4. Efficiency
We follow the same way as in [9, 10] to analyse the proposed scheme's performance in respect of the cost of computation and communication overhead, as well as storage overhead.
Computation Cost. By comparison of detailed scheme description, we can directly find that the total cost of computation at the data source sensor in the proposed scheme is the same as Ren's scheme.
Storage and Communication Overhead. The increased overhead on storage which is caused by our improvement is the size of neighborhood table: two-hop neighbor set is larger than two-hop neighbor set as in the analysis in Section 5.2. Otherwise, the total communication overhead of the proposed scheme is twice as much as Ren's scheme. Hence, we improve the security of data distribution at the cost of storage and communication overhead.
6. Performance Evaluation
We adopt our proposed scheme on Ren's simulator [13] for comparison, and then we show several numerical results through dense simulations. We set an UWSN, where 200 sensors are distributed randomly in a 500 m by 500 m region. Transmission range (TR) of every sensor is equal to 60 m. The final results by simulations are averaged among the 100 randomly deployed UWSNs. Sensors are divided into 4 groups with different compromised probability
As shown in Figures 4–6, we can observe that our proposed scheme could achieve best probabilistic BSe compared to Wang's scheme [8], Ren's scheme [9], and the naive scheme [9], whatever redundancy factor τ is. That observation nicely agrees with all discussions in Section 5.2 where two-hop neighbor set is the better candidate shareholder than one-hop neighbor set for security of data distribution, and then our scheme outperforms other schemes in BSe.

BSe for data distribution without redundancy.
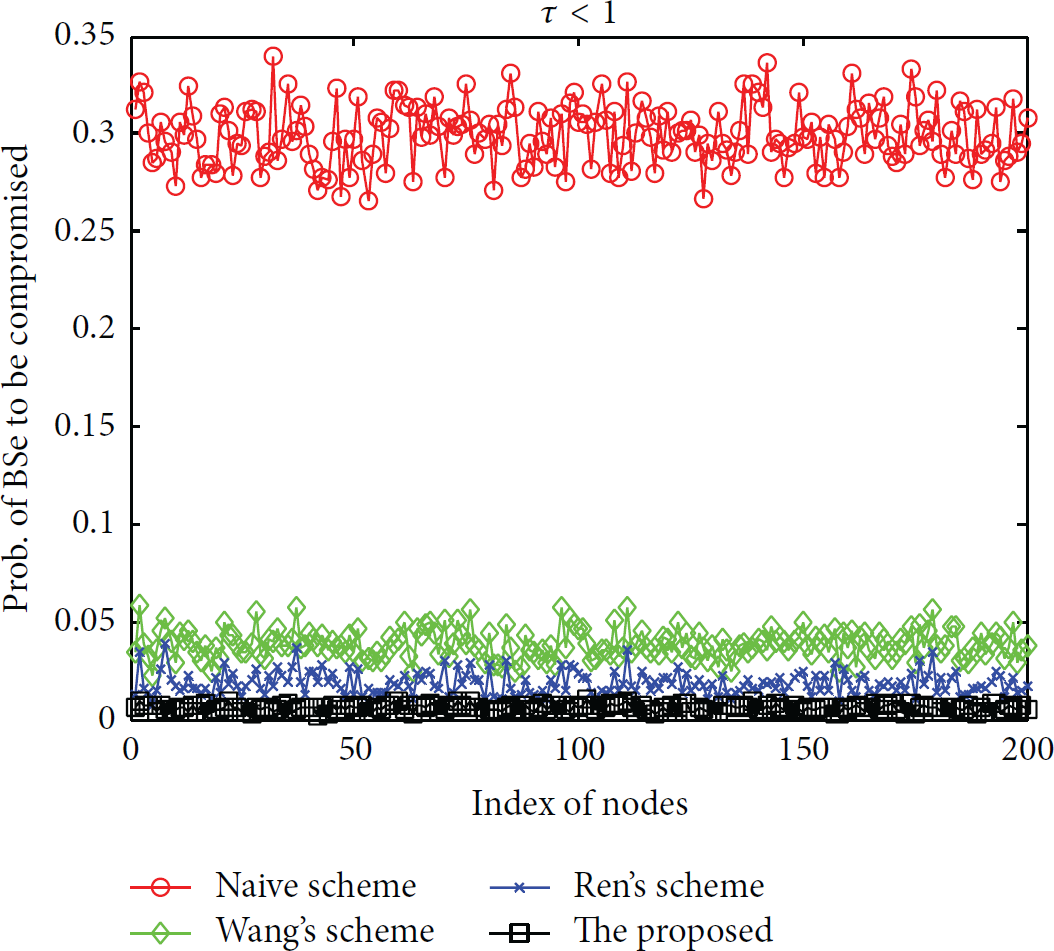
BSe for data distribution with redundancy.

BSe versus number of one-hop neighbors.
As shown in Figures 7–9, we can observe that our proposed scheme could achieve the best data reliability only when data distribution is carried out with redundancy. When

Data reliability without redundancy.

Data reliability with redundancy.

Data reliability versus number of one-hop neighbors.
Since all these sensors are distributed randomly in these simulations, the number of one-hop neighbor sensors might be different, which may influence both BSe and reliability. These effects on BSe and data reliability in UWSN are shown in Figures 6 and 9. We can observe that our proposed scheme holds the best performance on data reliability no matter how
7. Conclusions
We propose a novel data distribution scheme based on erasure codes which adapt the MOVE-ONCE survival strategies. Two-hop neighbor set has been utilized as data shareholders in the proposed data distribution scheme. Since two-hop neighbor set is the better candidate shareholder than one-hop neighbor set for security of data distribution, our proposed scheme could further improve both the probabilistic BSe and the reliability of data acquisition. Numeric simulations show that the proposed approach outperforms several previous approaches developed for UWSNs.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
The authors would like to thank Dr. Yi Ren in the University of Agder for his papers and simulator, which have motivated and helped this work. The authors had many discussions and improved the simulator. They would like to thank editors and reviewers for their helpful advice and comments. This work is supported by the National Natural Science Foundation of China under Grants nos. 61301092 and 61401360; Fundamental Research Funds for the Central Universities under Grant 3102014JCQ01055; Natural Science Basis Research Plan in Shaanxi Province of China under Grant 2014JQ2-6033; and China Postdoctoral Science Foundation under Grant 2012M512026.