Abstract
We propose and analyse a medium access control (MAC) protocol for low energy critical infrastructure monitoring (LECIM) networks. As the packet drop probability plays crucial role in LECIM applications, we propose framed slotted aloha based MAC for LECIM using linearly increased contention window size to reduce the packet drop probability. We present a mathematical model of our proposed MAC under both saturated and nonsaturated traffic scenarios. We use probabilistic approach to find the performance metrics such as collision probability, packet drop probability, throughput, and energy consumption. Also, we obtain the probability-generating function of the head-of-line (HoL) delay of packet. The analytical results match with simulations. Our results can be used in the design of a system by providing the optimum system parameters for endpoints satisfying the given quality of service requirements on packet drop probability, energy consumption, and delay.
1. Introduction
Critical infrastructure is a term used by governments to describe assets that are essential for the functioning of a society. Border surveillance, medical alerts for at-risk populations, first-responder tracking, soil monitoring, oil and gas pipeline monitoring, public transport tracking, cargo container monitoring, and railroad condition monitoring are some of the applications and facilities that are associated with LECIM networks. Here, we describe in detail two service applications—railway track condition monitoring and oil and gas pipeline monitoring.
The railway network is the most important system in the transportation infrastructure of a nation. It helps to sustain commerce in almost every sector of the national economy and is used for both pleasure and necessity by almost every citizen. Maintaining this system at a high performance level is vital for public safety, societal well-being, and economic productivity and growth. Railway tracks comprise significant and critical discrete links in the transportation system. Clearly, the job of monitoring the condition of rail infrastructure assets has become increasingly important over the last few years, for reasons of performance optimization to facilitate growth in traffic intensity, cost reduction in maintenance processes, railway patrolling staff role, cheaper measurement and data storage, and analysis capability. The preventive maintenance of railway tracks and structures has long centered in traditional methods for the early detection of potentially catastrophic faults. Such methods include visual inspections, which require a degree of experience to obtain results that are still subjective in interpretation. Further, such tests are invariably time-consuming and tedious to perform. They are qualitative in nature and can only assess outward appearance. Any internal damage may go unnoticed for a long period of time. With the relentless aging of the railway track infrastructure, an effective railway track monitoring system has become imperative.
Oil and gas installations are assets of high importance and value. To move oil and gas from producing sites to refineries and from there to the markets for distribution, immense networks of pipeline are used. These pipelines are installed through densely populated urban areas, in some cases, over the surface of the earth, whereas in some cases they are located underground. Pipeline faces threats of leaks, damage, and breaks, which can be caused by terror attacks or due to aging equipment, extreme weather, earthquake, and so on. These threats lead to huge revenue losses, bedlam on international oil markets, and environmental pollution problems [1].
An ever increasing number of works are dealing with the protection of the sensed data in critical infrastructure monitoring applications; but accessing the shared medium in such networks has received comparatively little attention. The survey in [2] covers the general ideas about using WSN (wireless sensor network) to ensure the protection of critical infrastructure. In [3], the authors provide an overview of the main challenges and open research issues on critical information infrastructure security. In [4], the authors identify the precise security requirements for distributing the symmetric keys along the one-dimensional WSN used for monitoring an extended piece of linear infrastructure such as a pipe. The authors in [4] also propose lightweight key distribution schemes which could benefit applications like perimeter surveillance and pipeline monitoring. In [5], the authors make two contributions. First, they propose a model to maximize the amount of monitoring-related data that can survive after a portion of the critical infrastructure suffers a disaster. Second, they address the distribution of sensors in a specific application like oil pipeline so that an optimal placement of sensors could be achieved, while satisfying deployment constraints. The IEEE TG4k was formed to facilitate low energy operations for multiyear battery life and a simple and low cost communication environment with reliable data transfer. For this purpose, several proposals and MAC protocols were presented in [1, 6–13]. In [6], authors presented a MAC protocol for downlink communication using wake-up radio. In [1], Ullah et al. proposed multihop MAC for LECIM networks using wake-up radio. In [8], we proposed a MAC protocol based on a framed slotted aloha for LECIM network. In [8], we presented basic collision resolution approach, in which endpoints choose a slot for transmission in a super frame of size M. As the packet drop probability plays an important role in many LECIM applications such as oil/gas pipeline monitoring, railroad condition monitoring, and bridge condition monitoring, we propose a framed slotted aloha based MAC for LECIM using linearly increased contention window size to reduce packet drop probability. We call this mechanism enhanced collision resolution approach. In this approach, the endpoints increase the contention window (CW) linearly after collision instead of retransmitting the packet in the just next super frame.
In this paper, we present the mathematical analysis of our proposed MAC under both saturation and nonsaturation traffic scenarios. For nonsaturation case, we only consider CASE II (packets arrive to and queue in the buffer). We use probabilistic approach to find the performance metrics such as collision probability, packet drop probability, HoL-delay, and energy consumption for both saturation and nonsaturation traffic scenarios. The analytical results are then verified for accuracy by detailed comparison to simulation. Our results can be used to find the optimal number of endpoints while satisfying the QoS (quality of service) on the packet drop probability, energy consumption, and HoL-delay.
The rest of the paper is structured as follows. In Section 2, we discuss our basic collision resolution approach. In Section 3, we discuss the enhanced collision resolution scheme. In Section 4, we describe analytical model under saturated load. Section 5 gives analytical model for nonsaturated traffic scenario. We present analytical and simulation results in Section 6 followed by the conclusions.
2. Basic Collision Resolution Scheme
In the basic approach after packet arrival, the endpoints wait for the beacon. After listening to the beacon, the endpoints then choose a slot randomly using uniform distribution on [1, M] and then transmit in the slot. After collision, the endpoints choose a slot in the same manner in the just next super frame of size M. The packet gets dropped when the maximum retransmission limit R is reached (see Figure 1).

Flowchart describing the basic collision resolution scheme.
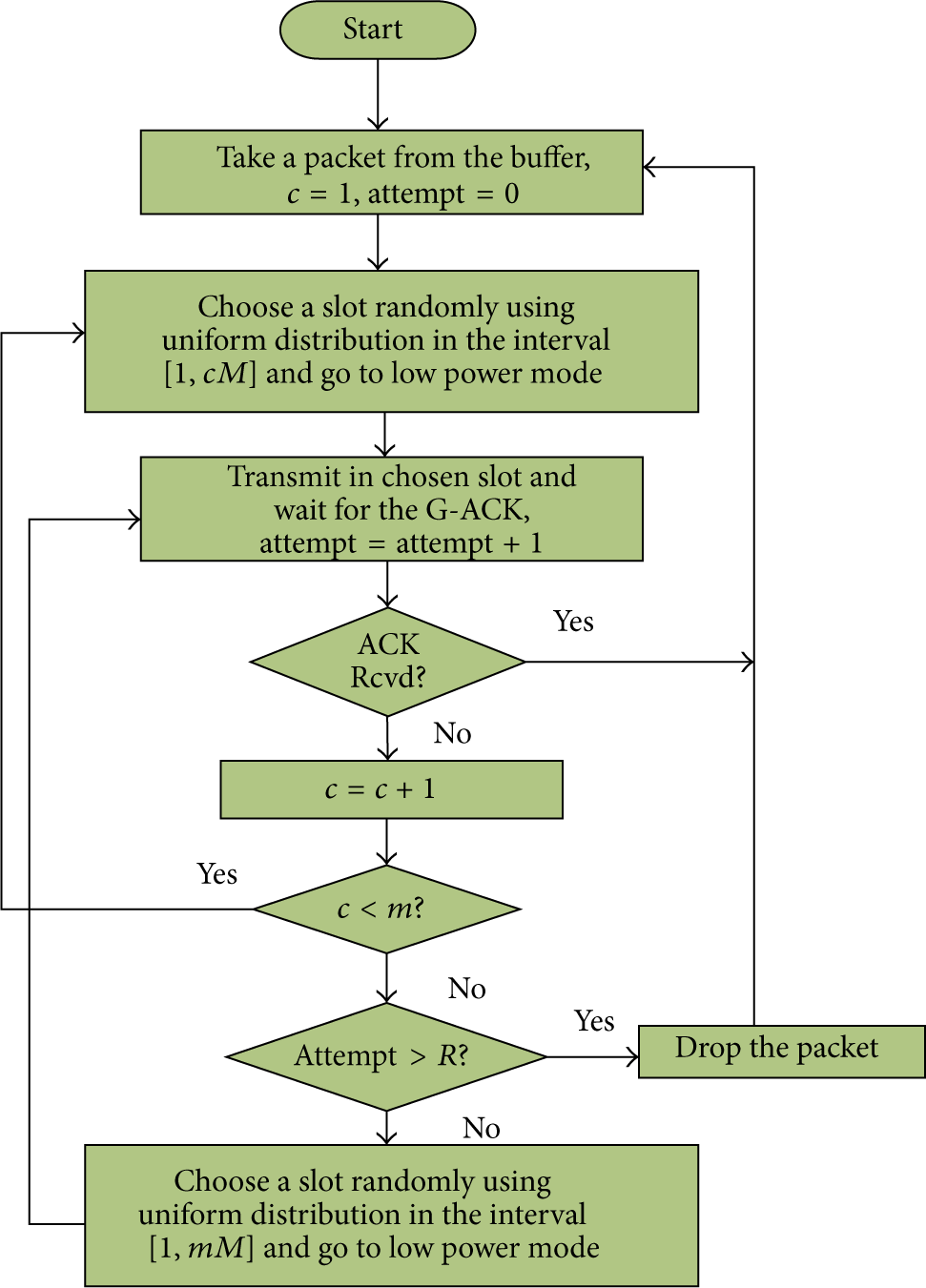
3. Enhanced Collision Resolution Approach
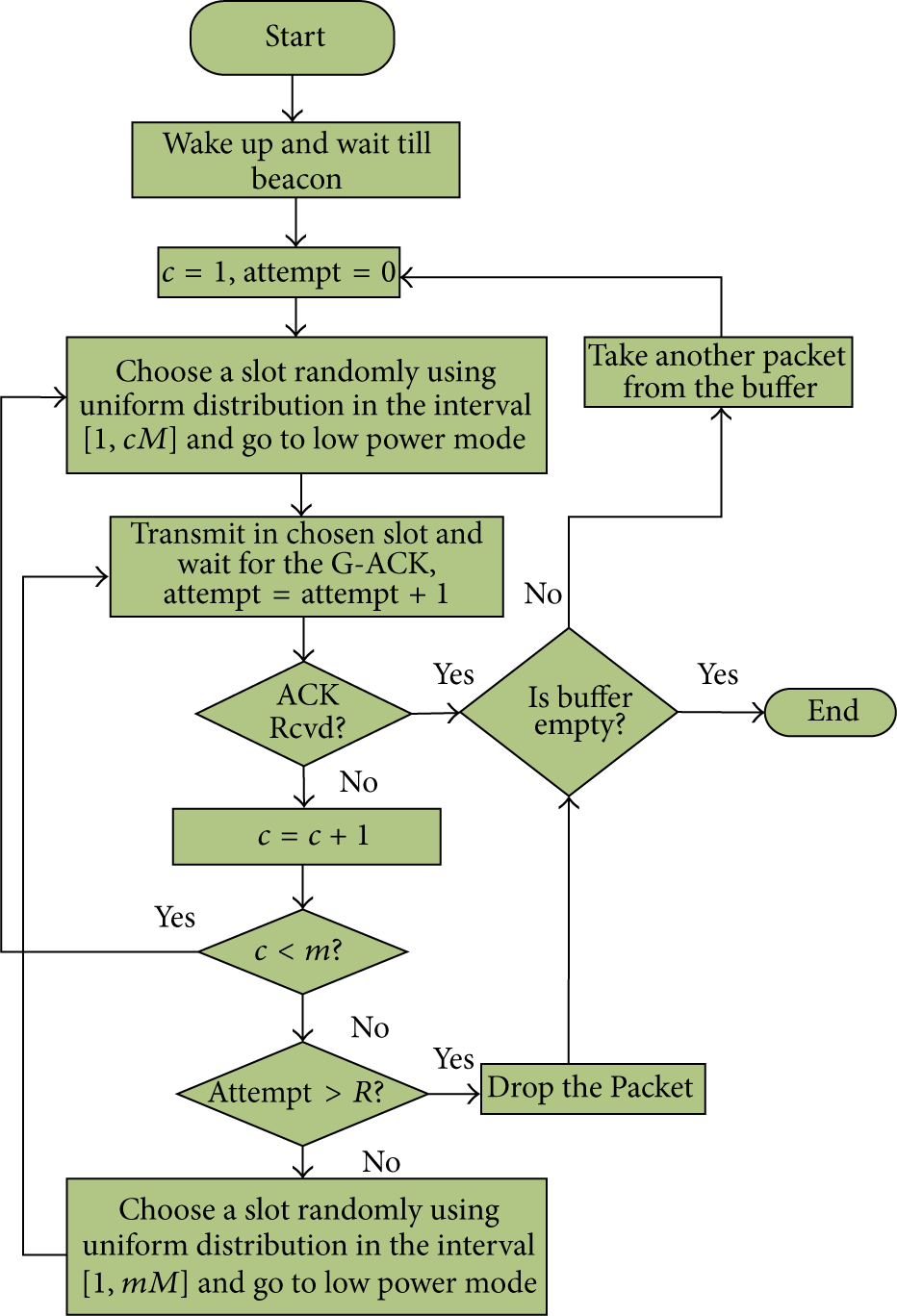
Unlike the basic approach, in the enhanced approach, the endpoints increase their contention window in linear order after collision. At the first transmission attempt, endpoints choose a random number in the interval
Flowchart depicting the transmission in saturated mode using enhanced collision resolution scheme.
4. Performance Analysis under Saturated Load
In saturation condition, endpoints’ queue never empties and, just after the completion of a transmission, endpoints take another packet from the buffer and start the transmission process. In the case of collision, the collided endpoints handle the collision as discussed above. The flowchart in Figure 2 describes the proposed collision resolution scheme under saturated traffic condition.
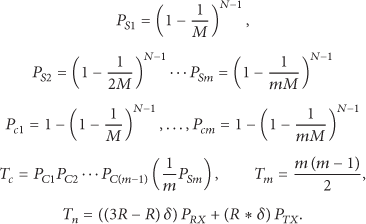
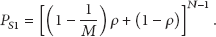
A transmission of the tagged endpoint is said to be successful if no other endpoint will select the slot chosen by the tagged endpoint. The probability of success
4.1. Packet Drop Probability
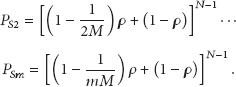
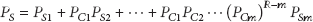
In our proposed approach, the tagged endpoint drops the packet and takes another packet from the buffer if the packet reaches specified retransmission limit. The packet drop probability
4.2. HoL-Delay
The HoL-delay is defined as the time interval from the time when the packet is at the head of the queue ready to be transmitted until an acknowledgement for the packet is received or the packet is dropped.
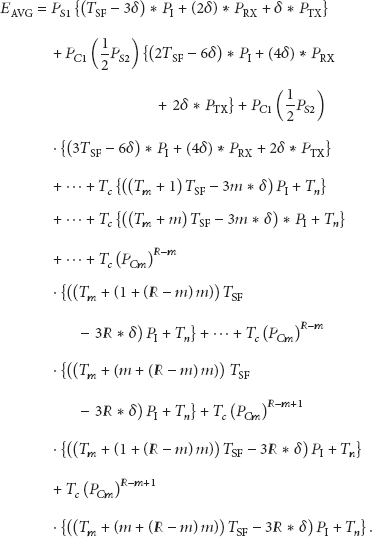
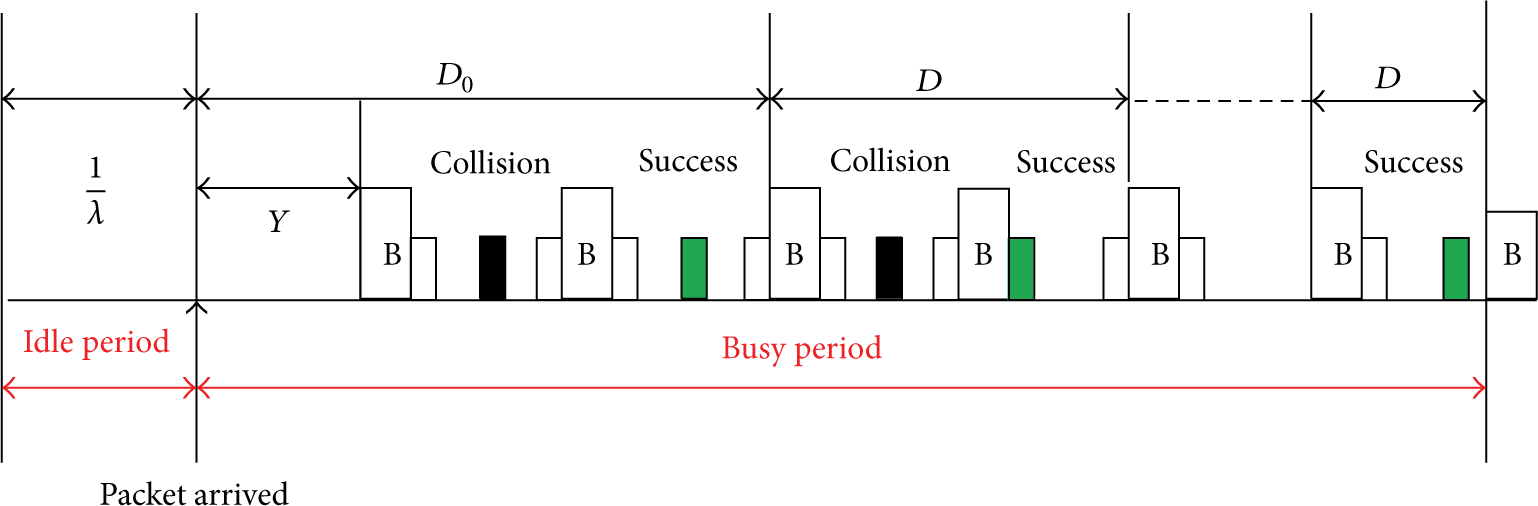
Using Figure 3, the average HoL-delay of packet,

Head-of-line delay of the tagged packet.
Let
4.3. Energy Consumption
Energy consumption is one of the most important performance metrics in LECIM. Using symbols
5. Performance Analysis under Nonsaturated Load
Nonsaturation mode means that endpoints sometimes have no packets to transmit. Nonsaturated mode can be classified into two cases. Case I refers to the situation where a new packet is not generated when the previous packet is in service. Case II is that packets arrive to (e.g., according to a Poisson process) and queue in a buffer at the endpoints even during the service of the preceding packet. We consider here Case II of nonsaturated mode, because in LECIM the chances of packets arrival during the processing of the existing packets are high. For analysis, we assume the tagged endpoint as
Waiting time using exception first service time.
In Figure 4, we see the packet that arrives to an empty queue has to wait till the beacon (this waiting time is denoted by Y) and after listening to the beacon the transmission process will start, while the subsequent packets (i.e., those that arrive during the service of the first packet) start their transmission process just after the transmission of the preceding packet. They need not to wait for Y.
Thus,
The expression for
The
It is known [14, Equation
Using the law of total probability, the probability of success
Flowchart depicting the transmission in nonsaturated case.
Similarly, we can derive the formulas for
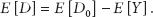
5.1. PGF of
and D
The tagged packet is transmitted successfully with probability
The PGF
As
The mean HoL-delay of packet
5.2. Energy Consumption
We use (20) to find the energy consumption of the tagged endpoint using our enhanced collision resolution scheme:
6. Results and Discussions
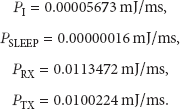
In this section, we present analytical results of both the saturated and nonsaturated traffic scenarios to evaluate the performance metrics. We set the length of a super frame to be 64, 128, and 256 slots long. The data rate is 40 Kbps. We assume a fixed size packet of length 80 bytes. The power consumption parameters are [15]
Figure 6 shows the packet drop probability in saturated case for different values of R and M. In the figure, we see rapid increase in the packet drop probability as the number of endpoints increases for small values of R and M (e.g.,

Packet drop probability.
In the case of large super frame size and R values, the packet drop probability is quite low (e.g., for
Figure 7 depicts the HoL-delay of packet. Unlike packet drop probability, the HoL-delay increases with the increase of R and M values. As the number of endpoints increases, collision among the packets also increases which causes the endpoints to increase the length of the contention window. The large contention window size causes more HoL-delay of packet and small packet drop probability. For example, we see in Figures 6 and 7, for small values of R and M, the delay is low but the packet drop probability is high, while for large values of the same parameters the delay is high and the packet drop probability is low.
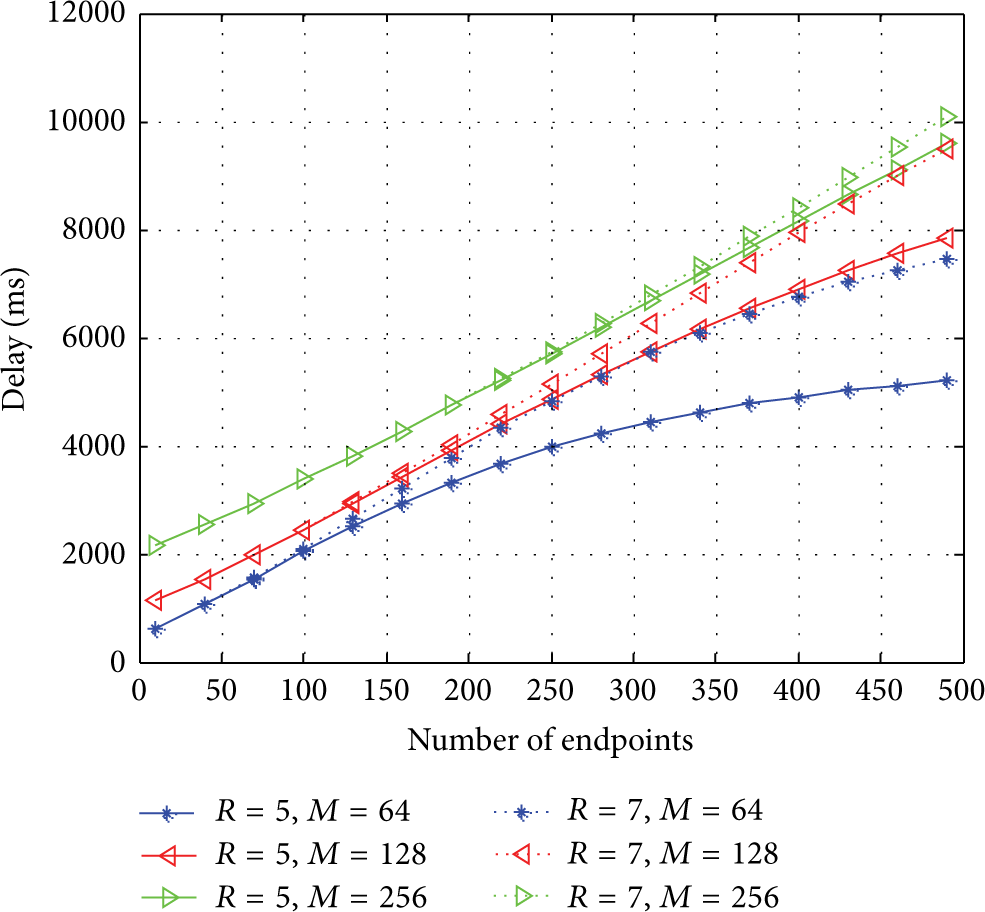
Head-of-line delay of packet.
Figure 8 depicts the average energy consumption (mJ). We see in the figure that, due to the high ratio of collisions in a super frame with small values of M than large values of M, more transmission attempts are needed, which results in more energy consumption. We see less amount of energy consumption for the longer super frame sizes (e.g.,

Average energy consumption.
Figures 9 and 10 depict the performance comparison in terms of packet drop probability and HoL-delay of the enhanced collision resolution scheme against the basic scheme under saturated traffic conditions. According to our intuition, we see the reduction in the packet drop probability in the enhanced approach as compared to the basic approach. As in the enhanced approach, the endpoints increase their contention window after collision; therefore, the delay increases and the packet drop probability decreases.

Packet drop probability comparison between the basic and enhanced approaches.

Delay comparison of the basic and enhanced approach.
Figure 11 shows the average energy consumption against the number of endpoints in the basic as well as in the enhanced methods for different values M and a fixed value of R which is equal to 7. In the figure, we see that, for the small number of endpoints, the energy consumption of both methods is almost same and when the number of endpoints increases, the enhanced method dominates the basic method in terms of energy efficiency. The decrease in energy consumption of the enhanced method is due to the reduction of packet collision probability.

Energy consumption comparison under saturated traffic conditions between the basic and enhanced approaches.
Figures 12 and 13 show the comparison of packet drop probability and HoL-delay of packet for different arrival rates under nonsaturated traffic condition. We see that, for small number of endpoints and low arrival rates, the packet drop probability and HoL-delay in both methods is very close to each other. For large number of endpoints, the enhanced approach performs well in terms of packet drop probability as compared to the basic approach. Although the delay in the enhanced approach is more than the basic approach, this small increase in delay has fewer effects on the overall performance of the protocol.

Packet drop probability under nonsaturated case. Dotted curves represent enhanced approach; solid curves represent basic approach.

HoL-delay under nonsaturated case. Dotted curves represent enhanced approach; solid curves represent basic approach.
Figure 14 displays the comparison of both methods in terms of average energy consumption for different values of λ. The gap between the energy consumption curves for the same arrival rates of both the methods increases slowly as the number of endpoints increases. In the case of low arrival rates, due to fewer collisions, the gap between the curves is very small (e.g., for

Comparison of energy consumption between the basic and enhanced collision resolution schemes. Dotted curves represent enhanced approach; solid curves represent basic approach.
7. Conclusion
In this paper, we presented our proposed enhanced collision resolution scheme for uplink communication in LECIM networks. We investigated packet drop probability, HoL-delay, and average energy consumption under both saturated (endpoints always have data to transmit to the coordinator) and nonsaturated (endpoints sometimes have no data to send) traffic conditions. We considered Case II (packets arrive to and queue in the buffer) of nonsaturation traffic scenario.
We compared our enhanced collision resolution approach with the basic approach and found that the new approach performs better than the basic approach in terms of packet drop probability and energy consumption. Optimal values of parameters can be chosen depending on the needs of each application. For example, given the number of endpoints equal to 400,
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
This work was supported by the National Research Foundation of Korea (NRF) grant funded by the Korea Government (MEST) (no. 2010-0018116).