Abstract
The proliferation of wireless communications systems poses new challenges in terms of coexistence between heterogeneous devices operating within the same frequency bands. In fact, in case of high-density concentration of wireless devices, like indoor environments, the network performance is typically limited by the mutual interference among the devices themselves, such as for wireless local area networks (WLANs). In this paper, we analyze a protocol strategy for managing multiple access in wireless networks. A network of sensors colocated with the WLAN terminals forms a control layer for managing the medium access and scheduling resources in order to limit collisions and optimize the WLAN data traffic; this control layer is based on a low-power wideband technology characterized by interference robustness, like CDMA (code division multiple access) or UWB (ultra-wideband) for sensors. In this work, we perform an analytical and simulative performance study of the saturated throughput, showing numerical results for the UWB-IR (Impulse Radio) sensors case and highlighting the advantage that can be provided particularly in very high capacity systems, which constitute the necessary evolution of current WLAN versions.
1. Introduction
Modern wireless systems are required to manage radio resources in an effective and flexible manner in order to maximize the network capacity. In this context, when several devices share the same medium, the mutual interference becomes the main limiting factor in terms of performance. The need for low reuse factors of the same frequency bands, for improving network capacity, requires an efficient management of the radio access resources (e.g., time, frequency, and space) in order to control or mitigate the interference impact on the network terminals.
For WLANs (wireless local area networks), the transmissions are typically organized on a packet basis, so that each node occupies the medium for a time interval that is much shorter than the transmission period. In this context, with reference to conventional multiple access schemes, both deterministic [1] and random [2], several methods for controlling or mitigating the mutual interference have been proposed in the recent years. In general, the most classical approaches are based upon the concepts of interference averaging, when interference is distributed statistically among the users, or interference avoidance, when some form of coordination in the network allows the minimization of the interference effects [3–7]. In this category we find the traditional techniques for assuring orthogonality or quasi-orthogonality among the channels, as frequency, time and code division techniques, and random access protocols. A classical example of a MAC (medium access control) protocol is carrier sense multiple access (CSMA), which is a contention-based access integrated by Collision Detection (CD) or collision avoidance (CA) mechanisms. In CSMA each node verifies the presence of other transmitting nodes on the same physical medium before a transmission attempt. Then, in case traffic is detected, the node waits until the medium is free. More recently, solutions related to the interference control concept have acquired interest: interference alignment [8] is one of the most relevant examples of a mechanism for controlling the interference components at a generic receiver.
In this paper, the idea is to work on the concept of interference avoidance in the context of MAC protocols for WLANs: the rationale behind this choice is that interference averaging is not efficient enough for the increasing rate demands and, at the same time, interference control mechanisms are really difficult to be implemented effectively and easily in the WLAN context, characterized by low-cost multiple, uncoordinated access points in license-free bandwidths. So here we investigate and analyze the design of a protocol whose first version was presented in [9] as an ultra-wideband (UWB) Control Layer Medium Access (CL-MA): a primary wireless network achieves efficient access coordination using a distinct control layer (CL), dedicated to the resolution of the terminals collisions. So the underlying idea is the combination of a low-rate, interference-resilient CL, for medium access control, with a high-rate, interference-limited communication layer, for data transmission. A crucial feature of the CL is its coexistence with WLAN and other communication channels, thanks to its wideband, low-power transmission, typical of sensor networks based on wideband technologies. The CL proposed in [9] was based on UWB-IR (Impulse Radio) and its application to the WLAN context was investigated by means of a study on the potential compatibility between the UWB-IR and WLAN transmission ranges, according to their typical path loss models. In this work, starting from that original idea, we develop the design framework for the CL-MA protocol, extending it to a general wideband system, including UWB-IR but also Code Division Multiple Access (CDMA). In addition, after updating several aspects of the CL-MA protocol for optimizing its performance and its backward compatibility (i.e., the coexistence with WLAN terminals, non-equipped with the CL), we present the analysis of the final throughput in the WLAN layer, allowing a direct comparison with other access techniques based on a signaling channel separated from the data one. Finally, also the channel model for the analysis has been improved by introducing a correlation factor between CL and WLAN path losses, inspired by the numerical results obtained with a ray-tracing technique; in fact, the main difficulty of the study in [9] was the comparison between realistic path losses experienced by signals having different bandwidths but propagating between the same transmitters and receivers.
The CL-MA protocol may be applied to any primary wireless network technology with short-medium transmission range, including those characterized by absence of global synchronization and centralized coordination. Hence CL-MA should be effective and easy to implement in low cost wireless networks employing heterogeneous standards, like those designed for WPAN (wireless personal area network), WLAN (wireless local area networks), and WSN (wireless sensor networks). The main advantages provided by a separated wideband CL with respect to standard MAC protocols or dedicated signaling channels belonging to the WLAN layer are (i) robustness against collisions (i.e., simultaneous, multiple detection and reception in case of conflicts on the channel), (ii) coordination of the network for achieving high network efficiency and capacity, and (iii) possibility of additional services to the primary network, such as accurate terminals localization, which is favoured by the wideband nature of the CL signals and is an important feature for context-aware indoor applications. An interesting result, shown in Section 6, is that the advantage of such an approach tends to be more evident at very high channel bit rates, which constitute the next future of WLANs (see, e.g., the new families IEEE 802.11ac/ad/ax). On the contrary, the main challenges and drawbacks related to the implementation of this solution are (i) increased energy consumption (i.e., the impact of the control layer on the power consumption), (ii) cost and complexity of additional hardware, and (iii) communication range of the sensors that implement the CL, generally different from the WLAN one. Nevertheless, we can also observe that modern devices tend to integrate multiple radio interfaces, making reasonable assumption of colocation between a WLAN and a wideband technology.
The main novel contributions of this work are as follows:
Throughput analysis of the CL-MA when applied to a standard WLAN traffic layer under conditions of saturated traffic (Section 5). Comparison, in terms of throughput performance, among the proposed access scheme, the standard WLAN MAC, and the main scheme based on a signaling channel (Section 6.2). Study of the role of the fundamental system parameters, like bandwidth, processing gain, and time slots in the design of the CL (Section 3.1). Study of coexistence between UWB and WLAN signal in an indoor scenario with a model justified by means of accurate ray-tracing simulations (Section 6.1).
Section 2 discusses the related work in the literature, remarking the differences with this study. Then, Section 3 describes the network scenario and the system model, while Section 4 describes the access scheme details. Section 5 is dedicated to the analysis of WLAN saturation throughput in the presence of a CL. Finally, Section 6 presents the numerical results and discusses performance of the control layer scheme based upon the UWB-IR technology.
2. Related Work
The CL-MA protocol offers the possibility to provide access and possibly network information to a master station (or access point) in the primary network in order to schedule transmissions on the network, thus maximizing throughput and optimizing the data traffic. Here the choice for this control layer, which coexists with and serves the WLAN traffic layer with specific sensing capabilities of the interference and access attempts, has fallen on wideband technologies characterized by a processing gain and hence an inherent robustness with respect to fading and interference. As relevant examples of such technologies, we consider the well-known CDMA and UWB-IR, in which trains of narrow pulses are position-modulated and transmitted with a low duty cycle. These technologies could operate on the same bandwidth of the WLAN or in other portions of the spectrum, including the 60 GHz bandwidth, which has been attracting growing interest in the recent years.
The CL-MA protocol is related mainly to the concepts of Cognitive Pilot Channel (CPC) and out-of-band signaling scheme. The CPC can provide auxiliary information to a network, which can be used for improving medium access coordination, interference avoidance, and coexistence [10–14]. However CL-MA differs from the CPC concept since the peculiar usage of this channel is not for information exchange to allow dynamic or opportunistic spectrum access techniques (as seen in the cognitive radio framework) but for the implementation and resolution of a robust random access contention scheme. On the other hand, an out-of-band signaling scheme is used for managing the channel access contention. In [15] the authors show that IEEE 802.11 MAC protocol based on the distributed coordination function (DCF) may increase performance considerably when an additional, separated channel (denoted as out-of-band signaling or OBS) is used just for the channel access. This additional signaling channel reuses the same IEEE 802.11 medium access control scheme just for reserving data slots in the data channel and hence it exploits a greater efficiency since it does not suffer from the data traffic loading. This solution will be considered as a benchmark for CL-MA in Section 6. In [16], a CDMA-based control channel for the RTS/CTS (request-to-send/clear-to-send) handshaking scheme is proposed; the additional use of directional antennas improves throughput and spatial reuse of the channels and it partially solves the hidden terminal problem. In particular, RTS/CTS packets are transmitted with an omnidirectional directivity pattern, for avoiding the deafness problem, while ack and data packets exploit a directional pattern. In [17], an OFDM physical layer is combined with an appropriate dynamic resource allocation strategy at the MAC layer. Transmission of control packets follows the classical CSMA scheme, so a new transmission opportunity appears only when the whole channel is idle. Then, all the stations contend different subchannels after the channel is idle for a certain period and transmit simultaneously the RTS. The access point selects the stations allowed to transmit and allocates time-frequency resources according to users traffic demands. In [18], the authors present a novel technique, which provides a decoupled low overhead control plane for an OFDM-based physical layer and retains the simplicity of distributed asynchronous operations. Stations are allowed to send short control messages concurrently with data transmissions on specific slots in the OFDM time-frequency grid while ensuring correct detection of data packets and a minimal impact on network efficiency. This approach provides efficient, QoS-aware, and fair medium access, while eliminating control overheads including data plane contention, RTS/CTS, and random back-offs. In [19], under M2M (machine to machine) and MTC (machine-type communication) scenarios, the degradation of throughput and delay performance caused by the handshaking mechanism and its related overhead is reduced by sending many RTS in parallel by different stations on different frequency subbands. Since the RTS messages do not collide with each other, the proposed strategy reaches better saturation throughput and delay especially in loaded networks.
With respect to these solutions related to the concept of out-of-band signaling, our approach differs in the adoption of a channel that performs both signaling and collisions resolution at the physical layer by exploiting the interference robustness of the wideband CL signals and allowing even multiple, simultaneous transmissions/receptions of the access requests. This realizes a potential performance improvement especially at very high channel data rates and, at the same time, a resolution of the hidden and exposed terminals problems [9].
More recently, also other approaches have been proposed for enhancing the MAC WLAN protocol. First, some of the most recent versions of 802.11 standards include updated mechanisms, as the Hybrid Coordination Function (HCF) envisaged in IEEE 802.11e. This version comprises improved versions of the well-known 802.11 DCF/PCF mechanisms: Enhanced Distributed Channel Access (EDCA) and HCF Controlled Channel Access (HCCA), which are contention-based and contention-free channel access methods, respectively (similar to DCF and PCF). Both improve the overall system performance in terms of throughput efficiency and total achievable data rate and particularly, for EDCA, incorporate additional features related to the concept of providing differentiated QoS based on data traffic types (“access categories”) and, on priority levels, assigned to users data frames. This turns out to be particularly useful for real time audio-video applications (or other high data rate services) and in networks with a large number of stations.
Modifications of the original DCF scheme can be found also in [20], where it is proposed as an Enhanced Collision Avoidance (ECA) mechanism which reduces the drawbacks of the binary exponential back-off strategy and in [21] where it is presented as a simple but effective sender-initiated reservation scheme, a modification of DCF in which a transmitter may reserve additional time for sending multiple frames and improving the network throughput (about 20%).
Another technology which is under consideration for improving MAC efficiency in the next WLAN generations is the Orthogonal Frequency Division Multiple Access (OFDMA). We refer to [22] for a recent review of OFDMA-based MAC protocols known in the literature; these protocols are compared according to a framework that includes specific design issues for next generation WLANs.
The multiple packet reception capability of CL-MA can be found also in other approaches based on multipacket reception (MPR) schemes. In [23], it is observed that WLAN throughput could be increased significantly by allowing multiple nodes to transmit even in the presence of ongoing transmissions in the wireless medium and, instead of discouraging overlapping transmissions as in the original 802.11 DCF, the proposed MAC layer is thought for facilitating their occurrence and taking advantage from MPR.
Collision awareness, which is another characteristic of CL-MA, is the basis of the algorithm proposed in [24]. This protocol, denoted as semi-DCF, exploits the collision detection capability of receivers for disseminating information on optimal back-offs to the contenders and it is characterized by an opportunistic migration from random to deterministic back-off according to the traffic conditions.
Finally, also cooperative approaches have been recently considered for solving the problems caused by collisions. For example, in [25] a novel MAC protocol, named network coding cooperative MAC, uses cooperation to relieve the hidden station issue problem: the opportunistic cooperative transmission, realized by means of random linear coding (RLC), turns out to be promising in terms of network throughput and delay performance.
3. Network Scenario and System Model
The reference scenario considers a primary wireless network comprising
3.1. Control Layer Multisignals Detection
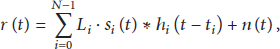
When N terminals are accessing simultaneously a time slot of the control layer In a binary CDMA-based CL, the signal In a binary UWB-IR based CL,
Performance of simultaneous detection of transmitted packets is a crucial step for the analysis of the CL-MA scheme. The received energy per bit The master station sends control signals to the N CL transmitting station in order to increase or decrease the transmitting power at the N stations and make received If the transmitted power is constant and fixed to a maximum allowed value (this could be the typical case of the UWB-IR based CL with an average power spectral density equal to
Now, in order to provide a general framework for the analysis, we rely on the following assumptions, applicable to the performance evaluation of wideband systems with asynchronous interference:
A rake receiver based on maximum ratio recombination is adopted for collecting the energy of more multipath components in the wideband signal. As this reduces the impact of random fluctuations due to multipath fading, we assume that the final random distribution of the available signal energy at the receiver is dominated by the log-normal density, effect of the channel shadowing (and mitigated by the power control, as stated in A3). The order of the rake receiver allows collecting all the available energy of the signal. Considering the most unfavorable UWB channel models, it turns out that a rake with 10–20 taps (mutually spaced by multiples of The log-normal densities of the signal components at the receiver derive from the channel shadowing contribution mitigated by the closed loop power control. This means that the power loop control is not able to equalize entirely the channel shadowing variations and the residual fluctuations can be still modeled by a log-normal density but with a reduced standard deviation The interference is modeled by an additional white noise with spectral density
Under these assumptions we can evaluate the impact of interference on the performance by means of the following steps. For the ith generic received signal at the master station and
Considering now the CL performance to be guaranteed, the minimum value of the signal-to-noise ratio, denoted as
Now (3) and (4) are combined for deriving the system design relation. According to the outage probability
3.2. WLAN Access Model
In the 802.11 protocol, the fundamental mechanism to access the medium is called distributed coordination function (DCF). This is a random access scheme, based on the carrier sense multiple access with collision avoidance (CSMA/CA) protocol. Retransmission of collided packets is managed according to binary exponential back-off rules. The standard also defines an optional point coordination function (PCF), which is a centralized MAC protocol able to support collision free and time bounded services. The stations access the medium according to a polling, centralized mechanism without collisions and organized in a sequence of time periods equal to

Medium access control in the time and frequency domains. Organization of the contention phase.
4. CL-MA Protocol
In this section, we present the mechanisms of the CL-MA protocol. As anticipated, time is divided into a sequence of time slots. The idea is that, during each time slot, the control layer resolves all the current access conflicts and it allows the transmission scheduling of the WLAN data layer, according to the PCF scheme (Figure 1). Therefore, an active device in the primary WLAN uses the CL as the control channel. The CL time slot It is Medium Access Contention Phase (MACP) where devices contact the master station (AP) and communicate their intention to transmit in the WLAN channel through a specific packet (TRP). It is Resource Allocation Phase (RAP) where the master station assigns radio resource to the recognized devices in the MACP. It is Medium Access Ack Phase (MAAP) where the master station transmits an ack packet (named TRPA) to the devices that are allowed to transmit in the primary network. Of course the TRPA may contain the necessary information about transmission time and frequency.
In terms of spectrum occupation, the control and data layers may operate on different or partially overlapping bands. The CL bandwidth is considerably larger than the WLAN one and WLAN band is often divided further into subbands for multiple access, while CL typically exploits a multiaccess code division technology. It should be noted also that the processing gain of the control layer is much larger than the WLAN one and this is a key aspect for the proposed protocol because of the need of robustness against collisions and mutual interference (Section 3.1). As already observed in [9], the CL-MA strategy of adopting two separate control and data layers with these characteristics provides a simple solution also to some common problems in the CSMA mechanisms that are among the most relevant limiting factors in terms of full capacity exploitation.
The backward compatibility, that is, the possibility of coexistence between terminals equipped with a control layer and standard WLAN terminals, is guaranteed by the fact that the master station manages both the control layer and the other terminals through the PCF scheme.
4.1. Control Layer Operations
The access phase is governed by the CL master station, colocated within the WLAN master station. The N terminals that join the contention phase (MACP) transmit the specific transmitting request packet, TRP, containing the fields necessary for the station identification. So, during the MACP, the master station has to decode all the incoming detectable TRP packets, sending a TRP ack (TRPA) to the devices that will be allowed to transmit. The intrinsic advantage of the procedure is that, in the control layer, the packets are usually distinguishable because of the spreading code redundancy differently from the traffic layer in which collisions generate interference and they are often destructive. In addition, the master stations, which receive the TRPs, are free to decide their strategies, according to the network load and/or channel conditions. It is important to note that the sensor network that implements the CL provides a low rate communication platform that should be more robust (to multipath fading and collisions) than the corresponding traffic layer. If necessary, the contention phase can be organized also on a demand basis instead of a periodic way. The main operations of a connecting terminal are as follows:
Access request by means of the broadcast of a TRP packet with its identification. Wait for access permission by listening to the channel during the MAAP. The terminal is allowed to transmit when it receives the TRPA from the master station.
On the other side, each active master station is supposed to perform the following operations:
Detect TRP packets during the MACP. Decide resource division during the RAP. Transmit TRPAs when incoming connections are allocated.
In the CL, it is also possible to request reports containing the transmitting devices and information on transmitting times, channels, or interference. The report generation should be an on-demand service that a new device requests in order to know active nodes, to estimate synchronization, and to obtain other information on the network. This request can be part of a cognitive approach or of a procedure that needs the estimation of the signal to interference ratios. In addition, during the report and access phases, some optional services as localization of the nodes and spectrum sensing could be included.
4.2. Minimum Required Control Layer Rate
The control layer is characterized by multiple low data rate signals, composed by short packets. The minimum length of the single packet can be estimated between
5. Analysis
The analysis of the system is based on the adaptation of the model in [15, 27] used for evaluating the saturation throughput of the distributed coordination function (DCF), that is, the medium access control (MAC) technique of IEEE 802.11. In particular, as reviewed in Section 2, [15] considers the analysis with an additional out-of-band signaling channel dedicated to DCF, just for the access contention. The performance estimation is achieved by describing the station behavior with an appropriate Markov model, characterized by the sequence of back-off times, activated at successive transmission attempt failures. In [15] the Markov model reproduces the signaling channel and the traffic channel is modeled by a single server queue (SSQ) formed by the stations allowed for transmission. The main assumptions shared with these analyses are (i) the ideal channel conditions (i.e., no hidden terminals and capture phenomena are taken into account), (ii) traffic saturation (i.e., the
The probability of collision is the decisive factor in the model since it accounts for the event of multiple transmissions in the same slot. Here, with respect to the standard conditions of the DCF mechanism, the model is modified according to the inclusion of the CL (Section 4). In the analytical study we assume that all the stations and clearly also the master AP have the CL activated since we are validating the potential advantage of the approach with respect to the standard DCF in the signaling channel; however, we remark that these stations may coexist with unequipped stations with backward compatibility. The main modifications introduced in our analysis are the following:
After each access contention in There is a success probability There is not a Markov model for the control layer (the equivalent of the out-of-band signaling channel) because our control layer is not governed by the DCF mechanism but it relies only on the detection capability of concurrent signals (Section 3.1).
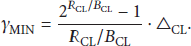
The probability
So the arrival rates of i stations to the SSQ, in the presence of N stations in the CL, can be estimated as
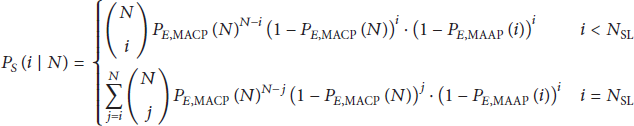
On the other hand, the service rate of the SSQ, which implements the traffic channel model, is given by
6. Numerical Results for the UWB CL-MA
In the numerical simulations, we have considered an UWB-IR scheme utilizing pulse position and amplitude modulation. Namely, we refer to signal (1) with chip time
In the sequel, Section 6.1 is devoted to the discussion of the propagation and shadowing model used for deriving the numerical results and to the predictable compatibility between the WLAN traffic layer and the necessary transmission rate achieved in the CL. Then, Section 6.2 presents the results obtained for the WLAN throughput under different system parameters and conditions.
6.1. UWB Channel Model and Compatibility between WLAN and UWB
In UWB-IR systems, the transmitted signal carrying the information bit usually spans a period of time occupying a number of consecutive time frames and we can refer to the organization of these pulse sequences as described in the IEEE 802.15.4a standard [28].
The channel model is a key issue in this work since the system under consideration involves the propagation of two signals, with different bandwidths, in the same environment. In addition the channel models for UWB transmission are accurate for short distances, usually within 20–30 m, but they do not provide parameters for longer ranges, typical of WLAN models instead [29]. In particular, the propagation loss is the critical part of the model and a limited number of articles are published in the literature regarding medium-long distances (>10–20 m) [30–32]. Differently from the approach chosen in [9] where we have analyzed the relation between UWB and WLAN coexisting channels extending the application range of existing models, in the present work we investigate the relation between these channels by employing ray-tracing (RT) simulations carried out at various frequencies over the signal bandwidth in an indoor square test environment with rich multipath: the area has a side equal to
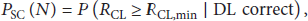
Now, from the ray-tracing data, we extend the UWB path loss model to longer distances in order to check and analyze the compatibility with WLAN. The maximum UWB achievable rate is computed in order to evaluate CL-MA performance for different distances and path loss model parameters and assure the WLAN requirements. First, with reference to Figure 2, we have computed the maximum UWB achievable rate

Achievable UWB rate versus distance considering maximum path loss from RT simulations, for varying N (a) and correlation factor between UWB and WLAN path losses as a function of distance (b).
Starting from this verified assumption of correlation among the path losses of the two wireless systems, we build up a simple path loss model for the UWB control layer
Now, considering the simplified model (9), we have evaluated the probability of success of UWB transmission on the control layer, for varying distances, correlation factor among UWB and WLAN path losses ρ, and UWB additional path loss


On the contrary, fixing three typical WLAN operative ranges and evaluating
6.2. WLAN Throughput
Here we have collected the numerical results regarding the throughput of the traffic layer, based on the WLAN IEEE 802.11 technology. We have used the same system parameters reported in [15] and we have included, as a reference system, the standard DCF based WLAN and the PCF with an out-of-band signaling scheme capable of data rates equal to As expected, when the UWB control layer works correctly with low failure probability (≤ When the channel conditions of the UWB control layer become worse than the WLAN one (Figures 7 and 8), the throughput performance is preserved (i) for short distances (i.e., below 20 m) regardless of the correlation factor ρ or (ii) also for medium-large distances when ρ is high (i.e., above Figure 9 shows the impact of the design parameter

Maximum throughput as a function of the channel bit rate

Maximum throughput as a function of the number of active users

Throughput as a function of the channel bit rate
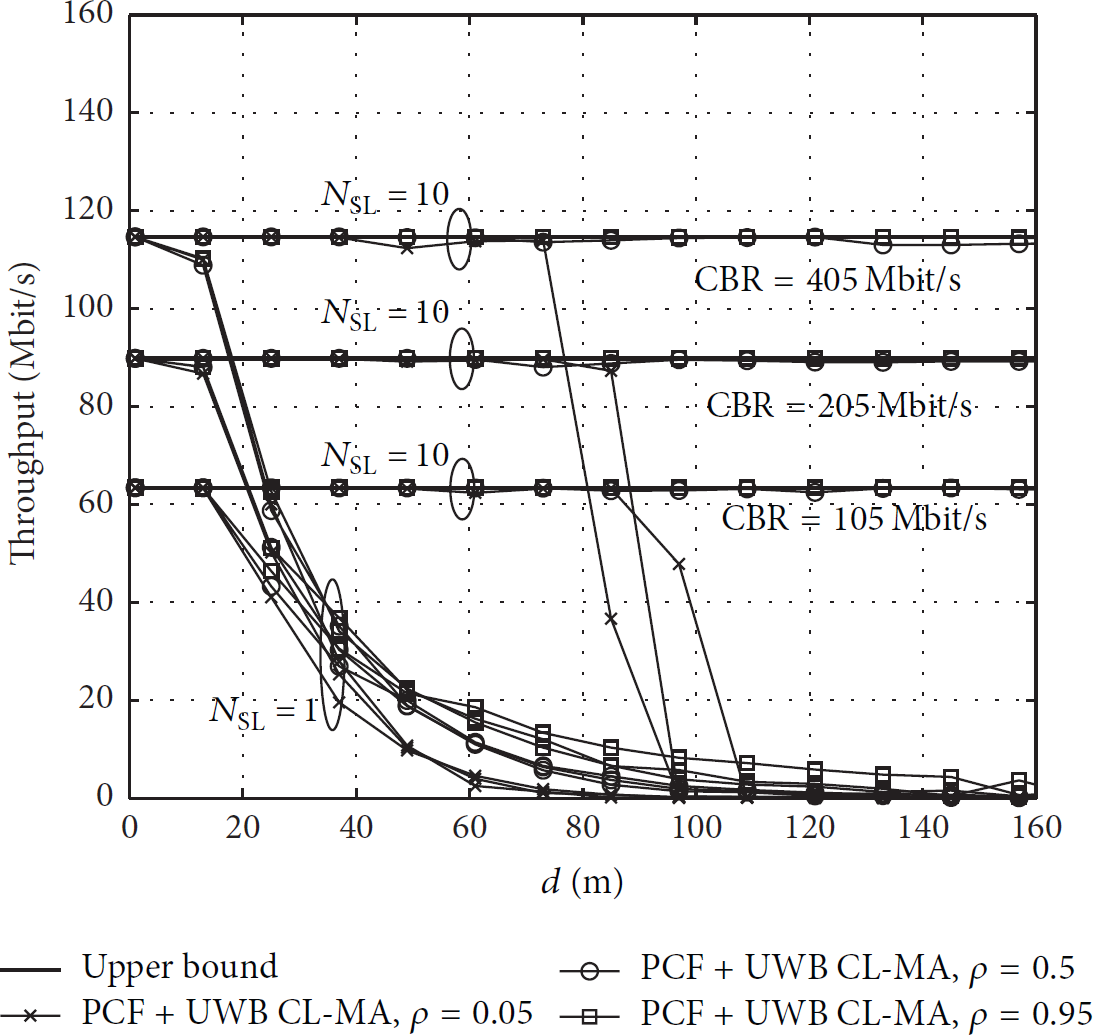
Throughput as a function of the distance for CL-MA with

Throughput of CL-MA as a function of increasing slot times
7. Conclusions
In this paper, we have analyzed a medium access control mechanism, denoted as CL-MA (Control Layer Medium Access), relying upon a low-power, wideband control layer and designed for enhancing coexistence in wireless local area network (WLAN) systems. The work focuses on the performance analysis of the WLAN throughput and on its comparison with the standard access mechanisms and solutions based on out-of-band signaling schemes. The numerical results, which exploit also propagation data obtained by ray-tracing simulations, show that an UWB-IR control layer is compatible with the WLAN network, at least for short-medium ranges or when the correlation between the WLAN and UWB channel propagation path losses is high. The relation between the control layer and the PCF (point coordination function) WLAN access scheme is designed in order to guarantee the backward compatibility with terminals not equipped with the CL mechanism. When the CL-MA works correctly, the access collisions are resolved and the output WLAN throughput achieves its upper limits even for very high channel bit rates and hence advanced physical layers, like those based on multiple antennas. The potential throughput gain with respect to the access protocol DCF is around 25–30% at current, typical channel bit rates (<100 Mbit/s) and it increases to 50–60% for channel bit rates above 300 Mbit/s.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.