Abstract
Disastrous events are one of the most challenging applications of multihop ad hoc networks due to possible damages of existing telecommunication infrastructure. The deployed cellular communication infrastructure might be partially or completely destroyed after a natural disaster. Multihop ad hoc communication is an interesting alternative to deal with the lack of communications in disaster scenarios. They have evolved since their origin, leading to different ad hoc paradigms such as MANETs, VANETs, DTNs, or WSNs. This paper presents a survey on multihop ad hoc network paradigms for disaster scenarios. It highlights their applicability to important tasks in disaster relief operations. More specifically, the paper reviews the main work found in the literature, which employed ad hoc networks in disaster scenarios. In addition, it discusses the open challenges and the future research directions for each different ad hoc paradigm.
1. Introduction
Ad hoc networks have been proposed as an appealing communication technology to deal with the unexpected conditions emerging during and/or after the occurrence of a disaster. Communication between victims and crew members involved in rescue operations is crucial in order to alleviate the disaster consequences and save lives. The first 72 hours after the occurrence of the disaster are the most important according to some studies [1, 2]. This period of time is called “the golden relief time.” After the golden relief time, the probability of finding survivors is very low. Consequently, coordination of first responders and/or victims is of paramount importance. Communications in general and among the first responders in particular play an important role in achieving an efficient coordination. Nowadays, people mostly communicate with each other by mobile phones and smartphones, making calls or sending text messages through Internet and social networks via applications such as WhatsApp, Facebook, Twitter, and others [3]. However, cellular-based communications may not be possible after a disaster due to the damages in the telecommunication infrastructure, leaving many people isolated and unprotected. In [4], the authors present Disaster Recovery Networks (DRN) and Search and Rescue Network (SRN) as the main networks needed for disaster relief. The objective of a DRN consists of providing emergency support to victims and crew members taking part in rescue operations. On the other hand, a SRN is a network formed to track individuals in an emergency operation. In [4], the authors state the main features required for DRN and SRN, such as quick response, life expectancy of the network, interoperability, tariff-free operation, network coverage, support for heterogeneous traffic types, network capacity, ease of use and cost of equipment, outdoor and indoor operation, high precision for localization, and search operation. Mobile ad hoc networks [4, 5] exhibit many of the above-mentioned features so they are suitable for both DRN and SRN and consequently for disaster response networks in general. Furthermore, in [6], the authors state the key obstacles in effective disaster response, such as communication and collaboration support, provision of real-time data to field personnel and to incident command post, unified approach to data handling, visual data capture, on-site building assessment, access to building design documents, personal mobility support, resource allocation issues, and multiple connectivity. Ad hoc networks can be a feasible solution for those complications related to real-time communication and collaboration between the personnel taking part in the rescue operations.
The basic idea of ad hoc networks is based on defining a multihop communication path between two or several nodes in the network. This initial idea has been constantly evolving, leading to the development of new ad hoc paradigms such as Vehicular Ad Network (VANETs), Delay Tolerant Networks, Wireless SensorNetworks (WSNs) [7], and others. This paper addresses the applicability of such multihop ad hoc networks in disaster response scenarios. The main contributions of this paper are listed as follows:
A detailed description of the existing multihop ad hoc network paradigms applicable to disaster response scenarios, including types of communications, wireless technologies, and research directions. A thorough review of the existing work for each ad hoc paradigm, highlighting the necessity of interoperability among different ad hoc paradigms. A review of the future open challenges for multihop ad hoc networks in disaster response scenarios.
This paper continues as follows. Section 2 presents the evolution of multihop ad hoc networks and the different ad hoc paradigms that can be used in disaster scenarios, describing the main features of each paradigm. Existing works for each ad hoc network in disaster scenarios are reviewed in Section 3. Section 4 discusses the open challenges and future research directions, and finally the main conclusions of this survey are presented in Section 5.
2. Evolution of Ad Hoc Network Paradigm and Its Application to Disaster Response Scenarios
In the classical viewpoint of ad hoc networks, nodes communicate with each other without requiring a central system or any type of infrastructure. Thus, nodes act as routers and hosts at the same time, being responsible for generating the content and disseminating it efficiently throughout nearby nodes in the network. Under this communication paradigm, mobility is actually a problem in classical MANETs (Mobile Ad hoc Networks), where routing protocols must deal with mobility of nodes and continuous topological changes in order to establish and maintain a communication path between a pair of source-destination nodes. The first idea of MANET was the replication of wired Internet communication like TCP/IP communications in mobile environments. However, in mobile scenarios, the replication of TCP/IP communications through a multihop path is not an easy task. The MANET paradigm has evolved since its born leading to new ad hoc paradigms based on the basic idea of communicating electronic devices through a multihop communication path and in a decentralized way.
2.1. The Evolution of Multihop Ad Hoc Networks
One of the first evolutions of traditional MANET is VANETs [7], which consider cars as the carriers of wireless transceiver, so cars can communicate with each other. The main idea behind VANETs is similar to that of MANETs but with a higher mobility of nodes and being limited to traffic lanes. There are also other clear differences in the wireless technologies used, MAC and application layers. Furthermore, Delay Tolerant Networks (DTNs) have arisen in the last decade as one of the most interesting evolutions of classical MANETs [52]. In DTNs, nodes do not require a high connectivity in order to communicate with each other. The transmitted information is not delay-sensitive so nodes follow the carry-store and forward paradigm in which nodes generate certain information and store it until they have a new opportunity to deliver it, that is, whenever they meet other nodes. For this feature, DTNs are also referred to as opportunistic networks, where each encounter between two nodes in the network is seen as a new opportunity to deliver information. In contrast to MANETs, mobility is seen as an advantage for disseminating information in DTNs since the higher the mobility, the higher the number of possible encounters with other nodes.
Other static ad hoc networks such as WSNs [53] or Wireless Mesh Networks (WMNs) [54] are also evolutions of classical MANETs applicable to disaster scenarios. With regard to mobility, WSNs are normally static networks where nodes sense environmental variables such as temperature and CO2 emissions. With respect to network hierarchy, in WSNs, there is normally a central node in charge of gathering sensed data from other nodes, processing the data and sending this information to a wider range of networks such as the Internet. WMNs are normally applied to extend Internet connectivity to areas where traditional connections via cable are difficult, if not impossible.
2.2. Multihop Ad Hoc Communications for Disaster Scenarios
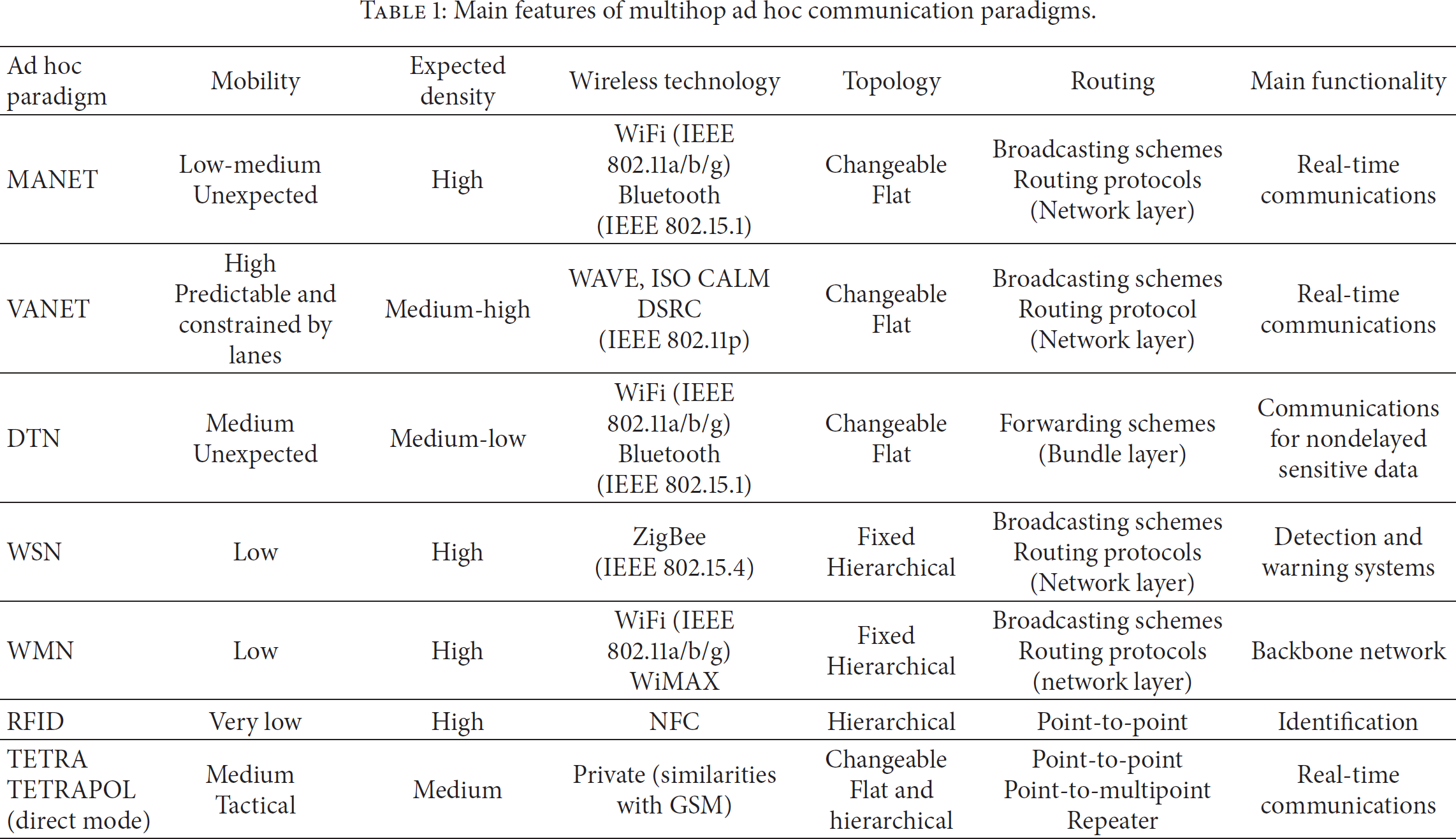
This subsection is aimed at presenting the main features of the different ad hoc communication paradigms such as MANETs, VANETs, DTNs, WSNs, WMNs, RFID, and TETRA and, most importantly, their applicability for disaster scenarios. Table 1 summarizes the main features of the ad hoc communication paradigms that will be described in this section. For more information about the different ad hoc networking paradigms and wireless technologies, the reader can refer to [52, 55–57].
Main features of multihop ad hoc communication paradigms.
2.2.1. MANETs
Two types of communications can be considered in classical MANETs, broadcast and multihop communications via routing protocols.
In broadcast communications, a node shares the same information simultaneously with its one hop neighbouring node. It may be suitable for transmitting warning messages and alarms, which are crucial forms of communications in disaster scenarios. Although this type of communication is the simplest way of transmitting data among nodes, for example, employing simple flooding, it may exhibit some problems in congested scenarios due to the broadcast storm problem [58]. A basic classification of broadcasting schemes in ad hoc networks categorizes the schemes into two groups, namely, the deterministic and the probabilistic schemes. In deterministic schemes, a subset of the nodes in the networks is selected as the potential forwarders to retransmit the broadcast packets [59]. In contrast to deterministic schemes, in probabilistic protocols, nodes retransmit the broadcast packets with a precalculated forwarding probability [60, 61].
When nodes rely on routing protocols for establishing a communication path to a destination node, nodes should maintain routing tables in order to select which is the best next hop to route the information. Regarding the types of routing protocols, two main categories are distinguished: proactive routing protocols and reactive routing protocols [62]. The main difference between both types is that, in proactive protocols, nodes exchange routing tables and topology information periodically. In contrast, in reactive protocols, routes are only created and maintained whenever they are needed and they are active. Research on routing protocols for ad hoc networks has been an active field for the last two decades [62, 63]. They can be applicable to important tasks in disaster scenarios. Let us imagine a situation where a rescue team needs to retransmit certain information to a central unit. A multihop route can be established from a crew member to the central unit. The routing protocol would be responsible for selecting the best nodes to retransmit the data packets from the crew member to the central unit.
Regarding the wireless technology used in MANETs, the IEEE 802.11a/b/g has been the technology usually employed. The Wireless Fidelity (WiFi) standard is based on IEEE 802.11 technology and it is used as the main technology to connect smartphones to the Internet access points in home connections. However, the applicability of IEEE 802.11 technology in MANETs requires the IEEE 802.11 wireless transceiver to be configured in Distributed Coordination Function (DCF) in order for nodes to function in ad hoc mode, which is different from the normal operation of IEEE 802.11 in smartphones. Bluetooth technology is also included in smartphones and, consequently, it is a potential candidate to be used in MANETs. However, Bluetooth requires the manual configuration of some parameters in order to establish communications. Another shortcoming is that the use of Bluetooth in smartphones implies a considerable increase of power consumption reducing the autonomy of the smartphones, which is a crucial parameter in disaster scenarios. Recently, WiFi Direct has appeared as appealing technology for ad hoc communications. However, it is not widely used in smartphones yet, but it must be considered in near future.
2.2.2. VANETs
Regarding the application of VANETs in disaster scenarios, it is obvious that communication among vehicles can also play an important role in reducing the consequences of disasters. Situations such as traffic accidents, reorganization of traffic by reducing congestion through proposing alternative routes, localization of victims, and communications between ambulances and victims or other rescue teams like firefighters or police officers are only few possible applications of the VANET paradigm in disaster scenarios. The basic types of communications in VANETs are the same above-mentioned in MANETs, so nodes (vehicles) can use both broadcast communications and multihop communications via routing protocols [64]. However, there are significant differences in the design of broadcasting and routing protocols for VANETs. Firstly, since mobility is higher than in MANETs, a fast medium access is needed in order to establish rapid communications among nodes. In this sense, the IEEE 802.11p MAC protocol is preferred rather than the traditional IEEE 802.11a/b/g. In IEEE 802.11p, several levels of prioritization are defined. Secondly, in VANETs scenarios, there are also static nodes of the network, namely, Road Side Units (RSUs), which are intended to offer services to vehicles. Consequently, in VANET scenarios, Vehicle To Infrastructure communications (V2I) and Vehicle To Vehicle communications (V2V) can be distinguished. However, in disaster scenarios, these road units are likely to be destroyed or malfunctioned so V2V communications should be considered as the main application of VANETs. Another important difference is related to power consumption. While in MANETs nodes use the wireless transceivers of smartphones designed for low consumption, in VANETs the wireless transceivers are self-charged by the cars' batteries. Consequently, energy is not a key routing parameter in VANETs. Both broadcasting schemes and routing protocols for VANETs have been active research fields in the last decade [65]. The readers can refer to [66] for more information on projects and standardization actions in the vehicular networking.
Regarding the wireless technology to be used in VANETs, they have been recently standardized into two technologies. The first one was mainly led by the Unites States of America (USA) and its Department of Transportation (USDOT); it was called Wireless Access for Vehicular Environments (WAVE) [7]. It is a protocol suite composed by the IEEE 802.11p and the IEEE 1609 protocols. The second one was mainly led by the European Union (EU); it was called Communications Access for Land Mobiles (ISO CALM). Both protocols present similarities. The ISO CALM protocol allows more transmission technologies (GSM, UMTS, CEN DSRC, etc.) having also included WAVE as one of them under the name CALM-M5. The main shortcoming is that WAVE and ISO CALM technologies are still under study and they are not used in commercial cars yet. In order to be used in disaster scenarios, public vehicles such as ambulances and police's vehicles must be equipped with WAVE or ISO CALM technologies.
2.2.3. DTNs
Like MANETs, opportunistic networks are also suitable for disaster scenarios, for example, in scenario where high density of nodes cannot be guaranteed or when they move with high mobility. These conditions may cause a malfunction of the normal mechanism of an ad hoc routing protocol (route discovery plus route establishment). In DTNs, we cannot make the distinction between broadcasting and routing protocol-based communications, because there is only one way of communication between nodes, which is used in every new encounter between two nodes [67]. In DTN communication, the information is sent in units called Bundles. When a node generates information, it is split in different bundles and then the node waits until encountering another node in order to deliver the information (bundle protocols). Consequently, while MANET routing protocols work on network layer, the bundle protocols for DTNs work on an upper layer, namely, bundle layer, which is between the transport layer and application layer. Note that the DTN paradigm refers to the idea of storing and carrying the information until a new encounter occurs so we can also consider DTNs in vehicular scenarios. In contrast to MANET scenarios, when a node cannot transmit a message to the destination it puts the message in a sending buffer, and, after waiting for certain time, the node will drop the stored message.
As a rule, DTN paradigm is suitable in cases of low density of nodes. For example, a police officer who is participating in a rescue operation and carrying certain information shares this information with all encountered victims. Furthermore, DTN are also suitable in high mobility networks, where traditional MANETs fail due to the continuous breakages of routes between the pair source-destination nodes.
Finally, the wireless technologies applicable for DTNs are the same for MANETs, so WiFi and Bluetooth are the main candidates.
2.2.4. WSNs
WSNs are suitable for early detection of possible disasters, for example, earthquake detection systems and flooding detection. In [58], the authors state the main issues to be solved when using WSN in disaster scenarios such as discovery and naming, robust routing, prioritization of critical data, security, and tracking device location. Furthermore, WSNs are envisioned to be an important component to achieve the Internet of Things paradigm [5, 68, 69]. Consequently, interoperability with WSNs is a key requirement for a disaster response communication system. WSNs are centralized networks where nodes are normally grouped in clusters [53]. In general, a node acts as the central node, head of cluster, or sink node and the other nodes are collecting certain data from the environment and sending it towards the central node. In this type of ad hoc network, it is possible to route the data from a sensor node to the central node through a multihop communication path. However, there are clear differences from the previous multihop mechanisms. Firstly, power consumption is the key parameter when designing routing protocols. Nodes in WSN are normally powered by batteries, whose replacements or changes may be difficult or even impossible. Secondly, wireless technology is focused on low power consumption rather than on bandwidth. The IEEE 802.15.4 standard has arisen as the standard de facto in WSNs, which allows nodes to communicate using a low rate but with long network's lifetime. Another important difference from previous ad hoc networks is related to mobility of nodes; in WSNs, mobility is very low since most nodes are static. As for the applicability in disaster scenarios, WSNs should play detection and warning roles. WSN is a suitable communication paradigm to be deployed in areas that are likely to suffer from natural disasters. Let us imagine a WSN deployed in an area in order to sense the earth vibrations for detecting possible earthquakes or a WSN deployed in a forest to monitor and detect fires.
2.2.5. WMNs
Regarding WMNs [54], the main communications are similar to that of MANET paradigm (broadcasting and routing protocols). However, the applications of traditional MANET and WMNs are different [54], making the goals of the routing protocols designed for WMNs also different. In WMNs, communications are mostly focused on extending Internet connectivity. We can imagine nodes in an urban area which have Internet connectivity thanks to a WMN deployed. The main application of WMNs in disaster scenarios is to form a backbone network able to provide Internet or extend connectivity in a wireless local network, for instance, to a rescue team operating in an evacuation mission.
Regarding the wireless technologies suitable for WMNs, we should consider WiFi and WiMAX as the main candidates.
2.2.6. RFID
RFID is also an ad hoc technology which allows two electronic devices to communicate without requiring a central system. RFID systems are normally employed in identification systems, for example, for tracking goods. In RFID systems, communications are point-to-point without any kind of routing. There are basically two types of devices: a tag and a reader. The reader obtains the information from the tag and it is responsible for initializing the communications. Another important distinction between the reader and the tag is that the tag does not need to be powered because it obtains the energy from the electromagnetic waves sent by the reader. The readers can refer to [70] for more information about RFID systems. As for the applicability in disaster scenarios, RFID systems are interesting for triage applications and building assessment [6]. In addition, it is worth highlighting that the RFID technology Near Field Communications (NFC) is already incorporated in some recent smartphones. This fact will facilitate the interoperability of RFID systems with other ad hoc paradigms.
2.2.7. TETRA and TETRAPOL Direct Mode
Terrestial Trunked Radio (TETRA) is the wireless private technology normally used by public services such as police, firefighters, ambulances, and security services. In its normal operation, TETRA is an infrastructure-based technology which has been developed since 1990s with the cooperation of the European Commission and the ETSI (European Telecommunications Standards Institute) members [71]. TETRA works at 380–383 MHz and 390–393 MHz bands in Europe and is suitable for transferring voice and data information. However, it does not support high data rates. In addition, as a private technology, TETRA specification defines all communication layers from the physical to the application layer.
Moreover, TETRA terminals can also communicate with each other in direct mode without needing infrastructure. Several types of communications (up to 5) are defined in TETRA direct mode. Basically, TETRA direct mode allows user to realize point-to-point communications, realize point-to-multipoint communications, communicate with gateways, and configure a TETRA terminal as repeater (reader can refer to [71] for more details about these types of communications).
Furthermore, TETRAPOL has been presented as the main competitor of TETRA in Europe [72]. It is an FDMA (Frequency Division Multiple Access) trunking system that was developed by EADS Telecom (formerly Matra Communications and later Matra Nortel Communications) for the French public safety forces [71].
Although TETRA and TETRAPOL technologies have been defined for emergency scenarios, providing desirable features such as security and resilience, they both lack an important aspect, which is the interoperability with other free bands wireless technologies such as WiFi and Bluetooth.
2.2.8. LTE-Advance in Device-to-Device Mode
The new generation of cellular communications such as Long Term Evolution advance (LTE-advance) also allows ad hoc communications between two terminals [73]. However, the terminals need the telecommunication infrastructure to start the communications. The infrastructure is responsible for detecting two candidates for ad hoc communications. It can be a problem in disaster scenarios since the deployed infrastructure can be destroyed due to the disaster damages. Consequently, this technology could not be always applicable. Another shortcoming is that the technology used for disaster response networks must be free of charge in order to be used for everyone affected in a disaster scenario.
The main features of the described ad hoc communication paradigms are included in Table 1.
It contains important aspects such as mobility, expected density, topology, routing protocols, wireless technology, and the main functionality of each paradigm in disaster response scenarios. Notice that the values of the mentioned fields in Table 1 represent the standard values for an optimal performance of each ad hoc paradigm. Regarding the field expected density, DTNs are suitable for sparse networks with low density levels, while MANETs require high density in order to establish real-time communication paths between two nodes in the network.
2.3. The Necessity of Interoperability among Ad Hoc Communication Paradigms for Disaster Scenarios
Communications in disaster scenarios may require interoperability among the mentioned ad hoc communication paradigms. Let us illustrate the necessity of such interoperability with the following example. Suppose that a crew member of a rescue operation needs to communicate with other crew members in a well-connected network like a MANET. For example, establishing a communication path with another crew member through a routing protocol or spreading out the same information to all crew members via a broadcasting protocol, for example, an emergency message indicating that he/she is in danger. This can be done using a specific technology like TETRA or TETRAPOL. However, later he/she would also require communicating with victims in a sparse situation like a DTN in order to transmit a possible evacuation route to the victims. This cannot be done using TETRA since the victims will not have a TETRA terminal. The same crew member would like to communicate with an ambulance in order to indicate the location of trapped victims, so the MANET terminal should be able to communicate with the wireless transceivers incorporated in the vehicles (VANET). Eventually the crew member can come across a WSN deployed in a building, which is partially destroyed but it has monitored certain data on the building before and during the disaster. This information can be very important to determine tactical movements in the subsequent rescue operations. Consequently, the MANET terminal should be able to communicate with WSN technologies. Although this is a simple example, the importance of the interoperability of different networks in order to achieve an integral and complete communication system for disaster response situations has been highlighted. The interoperability of different ad hoc paradigms has also envisioned a primordial objective for the proliferation of market applications of ad hoc networks in a multiparadigm era [52].
This interoperability must go further than connecting different ad hoc networks. The ad hoc networks must also communicate with other wireless technologies, such as satellite communications [50], and with the infrastructure in zones where it is still functioning [74].
In order to achieve a high interoperability, it is important that wireless devices are able to communicate with each other using the same wireless technology. For this reason, the use of smartphones seems to be the most reasonable alternative. Most smartphones found in the market are equipped with WiFi and Bluetooth transceivers, which provide the potential of developing relevant application for ad hoc network paradigms in disaster scenarios.
3. Review of Existing Work on Multihop Ad Hoc Networks for Disaster Scenarios
This section focuses on incorporating the main work on the application of the different ad hoc communication paradigms presented in the previous section to disaster scenarios. We have not included TETRA and LTE-advance technologies in this section since ad hoc mode is not their normal operation.
Although simulation is the main tool for evaluating the different approaches, some experimental work can also be found in the literature in the last few years. A common issue to be solved in communications for disaster scenarios is security. During a disaster, information plays an important role, but the exchange of data must be secure and reliable. Security issues in IT for disaster scenarios are addressed in [75, 76].
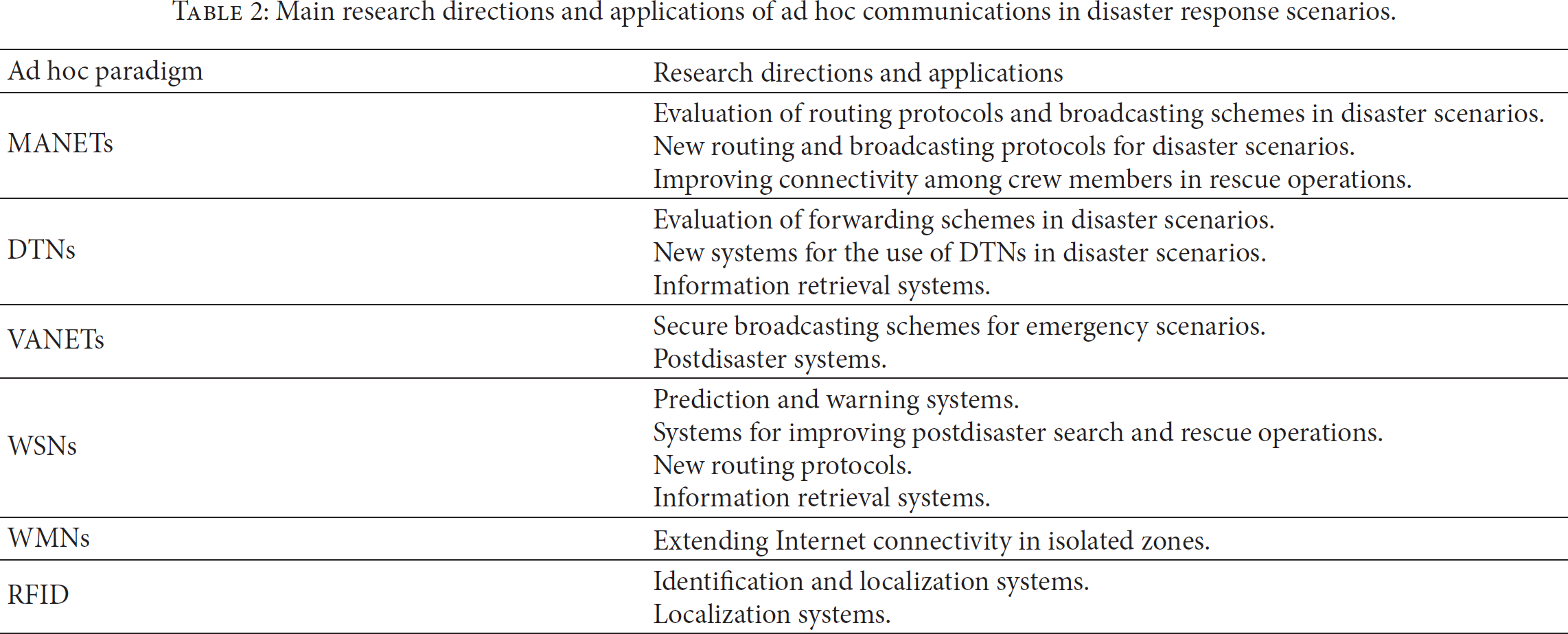
Table 2 summarizes the main research directions and problems for the different ad hoc paradigms in disaster scenarios.
Main research directions and applications of ad hoc communications in disaster response scenarios.
3.1. MANETs
The main works done on evaluating MANETs in disaster scenarios are based on the comparison of different MANET routing protocols in a disaster scenario. Table 3 summarizes the properties of the routing protocols designed for MANETs and evaluated in disaster scenarios. Regarding the type of routing protocols, we distinguish between reactive and proactive routing protocols and also between unicast and multicast protocols. Reactive routing protocols create route only on demand, that is, when a route between a source and a destination node is required. On the other hand, proactive routing protocols maintain routing tables for all possible destinations. In unicast routing protocols, the data packets are sent to a single destination, while in multicast routing protocols, the data is sent to several destinations simultaneously.
Summary of MANET routing protocols evaluated in disaster scenarios.
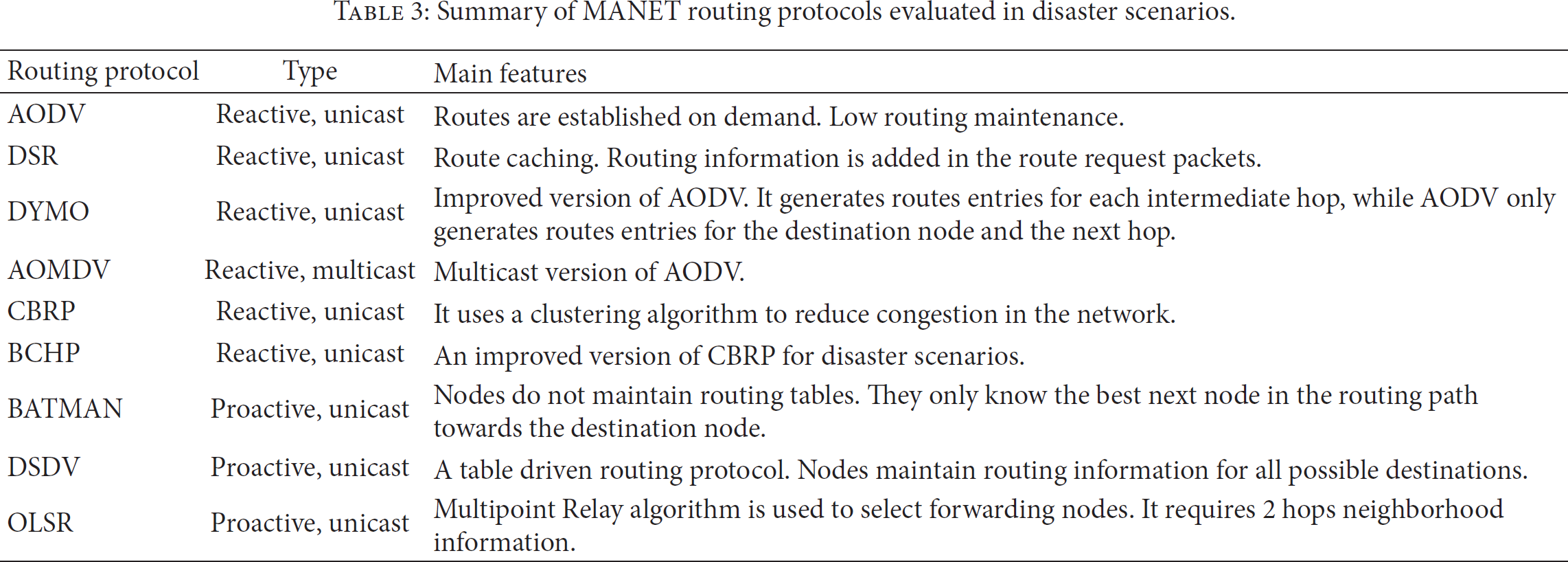
In [8, 9], several popular routing protocols for MANETs (AODV [77], AOMDV [78], and DSR [79]) are evaluated in disaster scenarios, considering different communication patterns. The obtained results in [8, 9] conclude that the reactive routing protocol AODV (Ad hoc On-demand Distance Vector) is the most suitable protocol for the scenarios considered. A similar evaluation is conducted in [10] in which also several routing protocols for MANETs (AODV [77], DYMO [80], BATMAN [81], and OLSR [82]) are evaluated under a real emergency scenario, modeling an explosion in a chemical facility. According to the results shown in [10], AODV again achieved the best results. In [11], the authors also evaluate by simulation several routing protocols for MANETs (AODV, DSDV, and CBRP). The main difference from the previous evaluation is that in [11] the Waypoint mobility model is used instead of disaster area mobility model [83]. In this case, the authors conclude that CBRP protocol outperforms its counterparts AODV and DSDV. In [12], the authors evaluate the following routing protocols AODV, CBRP, and the proposed Backup Cluster Head Protocol (BCHP), which is a cluster-based routing protocol specifically designed for disaster scenarios. They used a mobility scenario based on a map of the city of Loja (Spain). The results in [12] indicate that BCHP improves the availability and convergence of the network compared to AODV and CBRP protocols.
Regarding the evaluation of broadcasting schemes in disaster scenarios, in [13, 14], the authors used evolutionary approaches to optimize a broadcasting scheme based on dissimilarity coefficients for disaster scenarios. In [13], the authors used a single objective genetic algorithm, and in [14] they presented the broadcast problem as a multiobjective optimization problem. In [15], the performance of simple broadcasting protocol is enhanced by positioning auxiliary nodes using a genetic algorithm in low connected areas of the disaster response scenario.
3.2. DTNs
There is a continuous research on DTNs or opportunistic networks for disaster scenarios, as these networks are very suitable in case of a disaster as mentioned previously. The work done on DTNs is diverse, ranging from evaluating existing protocols to proposing new routing protocols and even new systems to improve the network performance in disaster areas. Table 4 summarizes the main properties of the forwarding protocols designed for DTNs and evaluated in disaster scenarios. We have classified the forwarding algorithms into two types, oblivious and delegation-based algorithms. In oblivious algorithms, nodes do not use any knowledge about the network. Consequently, nodes follow the same forwarding rules in any encounter. Alternatively, in delegation-based algorithms, nodes use a previously obtained knowledge of the network to delegate the responsibility of delivering the information to other nodes, which have a higher probability of encountering with the destination node.
Summary of DTN forwarding protocols evaluated in disaster scenarios.

In [16], the authors evaluate the performance of different opportunistic network's forwarding protocols (Epidemic [84], PRoPHET [85], MaxProp [86], and TTR [20]) in disaster scenarios. For comparison purposes, the disaster area mobility model proposed in [87] is used. Three main characteristics (number of nodes, number of messages created, and message size) are tested in the simulations. The results show that MaxProp protocol has the best delivery ratio, while the TTR protocol has the best overhead and cost results. It is concluded that there is no such thing as the absolute best protocol. It depends on the scenario and the metric to be optimized. Similar work is presented in [17], evaluating the performance of current DTN routing protocols in disaster scenarios. In [18], the performance of several forwarding protocols (Direct delivery, First contact, Epidemic, Spray and Wait, Binary Spray and Wait, and PRoPHET) is evaluated in terms of the fairness in delivering messages between nodes. According to the simulations, it is concluded that none of the tested protocols are able to satisfy the fairness criteria. Similarly, in [19], the authors evaluated the delivery probability and the overhead ratio of five DTN routing protocols (Epidemic, PRoPHET, Spray and Wait, MaxProp, and Spray and Focus) in a disaster area using a cluster mobility model. The results show that Spray and Wait protocol has the best performance in terms of overhead ratio. With regard to the delivery probability, there is no certain superior protocol in terms of performance, but it depends on different constrains such as the buffer size, transmission range, Bluetooth interface density, carrier node speed, and message size.
New forwarding schemes for DTNs in disaster scenarios have also been proposed. In [20], two energy efficient opportunistic routing protocols (PropTTR and PropNTTR) are proposed. In [21], the authors propose a DTN forwarding protocol that assigns priorities to the messages before handling each message according to that priority.
The works in [22–27] all propose new systems for better utilization of DTNs in disaster scenarios. A system to forward information about victims in disaster scenarios using electronic triage tag, Haggle, and mobile devices is presented in [22]. In [24], the authors present an evacuation guidance system that depends on the evacuees themselves to collect helpful data such as road blockage, safe paths, or even location 4 of rescue teams, and share this data among them using an opportunistic network. Both [25, 26] propose systems with Cognitive Wireless Network and an enhanced media coordinate system, respectively, to improve the performance of DTNs during disaster scenarios in rural areas, where there are lesser nodes and considerably large areas to be covered compared to urban areas. A content-based image prioritization technique that collects images from disaster areas, processes them, and prioritizes them depending on the critical information they carry and then sends them using a DTN according to their priorities is proposed in [27]. In [28], the authors present Twimight, an opportunistic-based Twitter application for disaster scenarios. Twimight can perform in both modes, normal mode as Twitter and disaster mode in which the messages are exchanged opportunistically in every encounter among two nodes.
3.3. VANETs
It is important to highlight that VANET technologies such as WAVE and ISO CALM are being developed considering emergency situations. Since a disaster scenario is an emergency scenario, most of VANET research focused on emergency situations can be also applied to disaster response scenarios. The main work done on vehicular ad hoc networks for disaster scenarios is focused on two guideless items. The first one is protocol improvement in the emergency messages dissemination among vehicles, proposing new broadcasting and routing protocols for emergency scenarios. The second one is the creation of an attached schema specifically designed for attending disaster situations in the actual VANET infrastructure.
Information exchange via broadcasting messages in VANETs for safety applications is summarized in [88]. Broadcast communications for emergency scenarios are studied in [29–32]. In [30], the authors present DEEP (Density-Aware Emergency message Extension Protocol) to solve the broadcast storm problem, achieving low dissemination delay and providing high reliability focused on a realistic multilane freeway scenario. In [31], vehicle-density-based forwarding scheme for broadcasting emergency messages (VDEB) is presented. They address the broadcast storm problem from two sender and receiver oriented schemas, getting lower delay and lower overhead for emergency message broadcasting. A novel dissemination protocol with directional and intersection broadcast modes is proposed in [32], where they use a binary-partition-based approach to divide the transmission area.
Furthermore, there are some works specifically focused on pre- and postdisaster situations. In [33], RescueME system is incorporated in the existing communication infrastructures to provide the method and entities to store users' location. It establishes different functions and roles of its entities before and after disasters; for example, users are just drivers who enjoy the services provided when there is no disaster around and become potential survivors when disasters occur. The authors highlight the importance of privacy and security in this kind of networks and propose a Public Key Infrastructure (PKI), which encrypts every stored data and method for the position update. The access to the information is only temporally allowed to the key authority during the disaster situation.
3.4. WSNs
The main work done on wireless sensor networks in disaster scenarios is concentrated on two aspects. The first one is disaster prediction and alert systems: how can WSNs be used to detect and warn about a possible disaster? The second one is assisting in the postdisaster search and rescue missions by deploying nodes in the disaster area as the WSN node mobility is low. The readers can refer to [89] for a review on different available technological solutions that use WSN either for disaster detection and alerting systems or search and rescue operations.
A disaster alert system that uses WSN and Analytic Network Process (ANP) to predict any possible landslide disasters is proposed in [90]. In [34], the authors propose a flash-flood alerting system based on a WSN in a rural area. In [35], machine learning techniques for distributed event detection using WSN are proposed and evaluated for early detection of residential fires. A design for the sensor input interface and equipment control output interface for an earthquake disaster wireless monitoring system is proposed in [35]. In [36], the authors propose an IEEE 802.15.4 based WSN for wildfire detection. Sensor nodes are grouped in clusters and equipped with temperature and humidity sensors in order to detect wildfire. The harvested information is sent to the control centre, an IEEE 802.11 based node which can connect to the Internet.
Regarding the work done for postdisaster scenarios, in [37], the authors propose a multiagent system based WSN approach for crisis management. A new type of WSN system named die-hard sensor network is proposed in [38]; the system is used immediately in a disaster area to assist in the search and rescue. In [39], a mechanism for processing spatial queries on WSN to detect dangers in disaster situations that increased the energy efficiency by 40% is presented. In [91], the authors propose a system that aids victims to send messages from their mobile devices using WSN in disaster areas. A WSN model with a new routing protocol is presented for a more energy efficient performance in a disaster scenario in [40]. In [41], a WSN protocol for disaster management (WSNPDM) is presented and evaluated. In [42], the authors propose some algorithms for retrieving and storing information on WSNs after disaster scenarios.
3.5. WMNs
The main application of WMNs for disaster response networks is being a backbone network to extend Internet connectivity or to extend local connectivity in a WLAN, so the WMNs can be seen as the mechanism to rapidly form an ad hoc infrastructure.
In [43], the authors present SKYMESH, a mesh network based on WiFi access points to provide rapid access to a WLAN network in a disaster area. For this purpose, they use helium-filled balloons floating in the air with WiFi transceivers as nodes to form the mesh network. A similar approach is presented in [44], where the authors propose a WMN for providing multimedia services in a disaster area.
3.6. MANETs
Although a large amount of literature can be found about broadcasting protocols in MANETs and good comparison among different schemes have been also proposed, an evaluation of different broadcasting protocols in disaster scenarios is still to be proposed. In the real experimentation work surveyed in this paper, OLSR routing protocol has been the one selected to be implemented. However, OLSR is a proactive routing protocol, which has problems of scalability in networks with a high number of nodes. Other reactive routing protocols like AODV can perform better in disaster scenarios according to the results obtained in [8, 9]. Modelling mobility of nodes in disaster scenarios is also a field, which deserves more research. The work done in [83, 87] allows the generation of synthetic mobility of rescue teams following tactical movements in disaster scenarios. However, further studies including the movements of victims are also needed.
3.7. RFID
In [45], the authors propose the use of RFID system for building assessment after a disaster occurrence so crew members arriving in a disaster zone can evaluate the building conditions before acting. In [46], a localization system based on RFID for indoors scenarios in emergency scenarios is presented. In the line of localization systems, in [92], the author proposes an RFID based victim localization system. In general, RFID based solutions for indoors localization is an active research topic due to the unavailability of GPS in those scenarios [93].
3.8. IoT
The IoT envisions a world full of connected electronic devices exchanging real-time information. Those devices can be separately forming other ad hoc networks such as MANETs, WSNs, and VANETs. In [47], the authors indicate disaster scenarios as one of the potential applications for the IoT paradigm in areas such as remote personnel monitoring (health, location), resource management and distribution, response planning, and sensors built into building. In [49], the authors use the IoT paradigm to predict possible man-made disasters like crimes. The proposed solution is based on a distributed system composed by cameras and other sensors connected as an IoT ecosystem. An information system based on IoT for snowmelt flood early-warning is presented in [94]. In [48], the authors propose the modelling of an IoT enabled smart environment and its smart objects' discovery and harvesting through a social networking analysis for disaster scenarios.
3.9. Integration of Different Ad Hoc Paradigms
Section 2.3 states the importance of combining different ad hoc paradigms in a complete solution for disaster response networks. However, there is no evidence of work which includes all the ad hoc paradigms reviewed in this paper. Yet there are some promising works on combining several ad hoc paradigms. The combination of MANETs and DTNs is particularly relevant in such situations. The main issue to address is when nodes should switch from MANET to DTN paradigm. It is obvious that the density of nodes must be the main clue for taking such decision. In high density scenarios, nodes should behave as in MANETs and in sparse situations nodes should switch to DTN behavior. In [95], the authors modify two well-known routing protocols for ad hoc networks such as BATMAN and OLSR in order to be able to switch between MANET and DTN modes. The main change done in the used routing protocols (BATMAN and OLSR) is that nodes store the data packets generated instead of dropping them when a route to the destination is not available. The authors do not change the rest of the functionality of the used routing protocols. The results showed in [95] indicate that the performance of BATMAN and OLSR is enhanced compared to the results obtained by the standard versions of BATMAN and OLSR.
In [23], the authors present DistressNet, a system that supports the search and rescue operation after a disaster. DistressNet is a complete complex system that adopts DTNs as well as WSNs and MANETs. DistressNet allows users to quickly and reliably store and retrieve data in a cloud-like manner. Emergency response personnel can use portable devices such as tablets or smartphones to monitor field data and collaborate with other teams. Thousands of sensors are deployed over the disaster area, continuously monitoring for potential survivors. WSN data is stored and replicated locally on battery powered devices and at the same time is backed up to a cloud service. The data generated in the disaster area is passed on over a delay tolerant network to the Command and Control center. Real emergency response teams contributed in the development of DistressNet by providing their system needs and requirements. DistressNet is an academic effort that has only been evaluated in a realistic situation on a small scale, as the evaluation of such systems on a large scale is time and resource consuming. Tests are made during real-life evaluation to optimize the system's performance in terms of what protocols to be used, the deployment, and setup of the nodes.
In [96], the authors present an opportunistic based network for urban search and rescue activities, which includes sensor networks in order to retrieve information from the disaster scenario. They define the following four elements in the opportunistic network: (1) regular sensors, composed of sensor measuring environmental variables like heat, light, and sound; (2) human-based sensor, that is, people carrying a smartphone; (3) witness units which are stationary information holders that perform the following tasks, receive, store, and deliver information; the main goal of these elements is to improve the connectivity of the opportunistic network; and finally (4) mule units, which are similar to the above-mentioned witness unit but with the objective of connecting different opportunistic networks like different search and rescue teams. The authors simulate the proposed opportunistic network using two different forwarding schemes such as the epidemic and the Spray and Wait algorithm. The results indicate that the epidemic algorithm performs faster than the Spray and Wait counterpart.
A real prototype of a communication system for ad hoc communications in disaster scenarios combining both MANET and DTN paradigms is presented in [97]. It is based on a smartphone application, which switches between both modes. The routing protocol used for MANET mode is OLSR and the routing in DTN is based on epidemic forwarding. In order to switch between MANET and DTN modes, nodes utilize information such as battery level, accelerometer, and surrounding smartphone information (density) in order to make the right decision. The authors define a density threshold based on the current number of neighbors below which nodes perform in DTN mode in order to save energy. Then, nodes check the acceleration information in order to determine their speeds. If nodes are moving with high speed, then nodes will switch to DTN mode. As it has already been stated, DTNs are more suitable for ad hoc networks with high mobility. Next, nodes check the remaining energy. Since MANET mode requires more exchange of topology information among nodes, it will only be activated when the remaining energy of a node is above a prefixed energy threshold. Furthermore, the prototype can also be connected to other networks, for example, a mesh network, by using gateways. The authors validate their prototype with two field experiments. The first experiment is focused on message relay in urban area, while the second is focused on the interconnection with Unmanned Aircraft Systems (UAS). It has been noted that in this sense ad hoc network for communication among unmanned vehicles is a promising vision.
In [50], the authors combine MANETs and WMNs with satellite communications. The crew members of a rescue team communicate with each other in a MANET. The coverage range provided by this method is enlarged using a WMN with WiMax technology. In addition, the different rescue teams operating in different zones can communicate via a satellite. Experimental results are presented in [50] validating the proposed communication architecture.
In [6], a system for building assessment is proposed. The system is composed of a RFID system, MANET [45], and WSNs. The RFID system is used to assess the building status. The crew members are equipped with a system which enables them to communicate with each other forming a MANET and also allows the crew member to read the RFID tags to know the status of the building after a disaster. Additionally, a “black box”, namely, building information hub is presented. This provides building information, such as temperature, humidity, personnel location, and stress in structural elements via the use of sensors. Real experimentation of the proposed system can be found in [6].
In [58], the authors present CodeBlue, a suite of protocols and services for many types of devices such as wireless sensors, location beacons, handheld computers, laptops, and others. The authors focus on the issue of interconnecting constrained devices in terms of power consumption and resources in disaster scenarios. Regarding WSNs, this approach is based on Mica2 mote, which is a popular wireless sensor node developed by UC Berkeley. Integration of medical sensors, routing and prioritization, and 3D location are among the services offered by CodeBlue for disaster response networks.
3.10. Mobility Models for Simulating Multihop Ad Hoc Networks in Disaster Response Scenarios
Since simulation is still the main mechanism to evaluate multihop ad hoc networks, mobility models that emulate crew members and victims during disaster scenarios are primordial in order to achieve reliable simulation results. We can classify the mobility models for disaster response scenarios into three categories, as shown in Figure 1. These are synthetic, map-based, and trace-based mobility models.

Classification of mobility models for disaster response scenarios.
Synthetic mobility models are normally generated by a mobility generator like BonnMotion [51]. They are easy to use and, moreover, different mobility conditions can be generated by using different seeds allowing repeatability of results. Most of the work done on evaluating MANET paradigm in disaster scenarios used the synthetic disaster area mobility model presented in [87] and used in [98] to model realistic disaster scenarios. The disaster area mobility model is based on a method called separation of the room [50, 74]. In the disaster area mobility model, a disaster scenario is divided into different context-based areas. These areas (see Figure 2) are incident site, casualty treatment area, transport zone, and technical operational command zone:
Incident site: it is the place where the disaster happened. Here injured people are normally found waiting to be transported to a casualty treatment area. With regard to the rescue team, fire-fighters or police officers could belong to the incident site. Casualty treatment area: it consists of two places, (a) patient waiting for treatment and (b) the casualty clearing station. In (a), people wait for a first inspection and classification; after that, they can be transported to a casualty clearing station (b) in which patients will be waiting to be transported to a hospital. Paramedics belong to this area. Transport zone: it is an area where transport units wait in stand-by areas to transport people to hospitals. The transport units can be either ambulances or rescue helicopters. Technical operational command: it is the zone where the rescue operations are commanded, usually located in the casualty treatment area.
Using this mobility model, MANET routing protocols, DTN forwarding schemes, and hybrid solutions have been evaluated. However, one of the main limitations of this mobility model is that it only considers the mobility of crew members, while the mobility of possible victims is not taken into consideration. A similar mobility model is proposed in [99], where the authors present CORPs, a synthetic mobility model for first responders. In this mobility model, attraction points called attention events are defined so first responders move to these points.

Disaster area mobility model.
Another possibility is to use scenarios based on real maps and integrate the mobility of nodes restricted to those maps in a network simulator. This is the case of map-based mobility models. For example, in [12], the authors use a map-based mobility model utilizing a map of the city of Loja in Spain. Mobility tools such as Car For Road (C4R) [100] and MOVE [101] are examples based on real maps that can generate mobility models for multihop ad hoc networks. In [102], the authors propose a map-based mobility model for DTN, where the mobility of both rescue workers and victims is considered. Regarding the victims, they move towards evacuation centers and the rescue workers move towards the victims in order to supply relief food. With map-based mobility model, we achieve more accuracy in the model of the disaster scenario. However, the mobility of nodes is still synthetically generated.
A step forward on modelling mobility in disaster scenario is to use trace-based mobility models. In this case, the mobility of nodes is based on real movements of people. These movements are obtained from wireless devices such as sensor motes and/or smartphones. In this line of work, the Community Resource for Archiving Wireless Data at Dartmouth (CRAWDAD) [103] is an open project aimed at archiving data collected from real-life experimentation so many traces are available. As for specific mobility models based on traces for disaster response scenarios, in [83], the authors model the mobility of ambulances based on real traces.
3.11. Summary of Existing Work on Disaster Scenarios
Table 5 summarizes the reviewed work on the application of multi-hop ad hoc networks in disaster scenarios. It contains the ad hoc paradigm for which each work is proposed, the research subject, and the main methodology used for the evaluation.
Summary of existing work on disaster scenarios.

4. Open Challenges
This section presents a detailed list of open challenges and future work on the application and evaluation of ad hoc network paradigms in disaster scenarios. We have followed the same criterion of the previous sections, so that different challenges and future work can be found for the different ad hoc network paradigms reviewed in this survey. A common future work in all ad hoc paradigms is the necessity of more real experimentation since most of the work done remains in the simulation phase. Another common challenge is to achieve secure mechanisms for exchanging information.
4.1. DTNs
Although new DTN forwarding protocols are constantly being proposed, a customized protocol or disaster scenarios considering properties such as fairness in delivering the message or energy efficiency have not been presented. Consequently, more research on forwarding schemes for disaster scenarios is required. Furthermore, most of the evaluations presented in literature are done in only one disaster scenario, while various scenarios such as an earthquake, a volcano, a tsunami, and a hurricane should be used to evaluate the performance of the proposed schemes. As the action of the nodes (people or cars) differs in each scenario, the performance of the scheme could also change according to the scenario. Therefore, modelling real disaster scenarios is still an issue requiring more research. In addition, many systems using DTNs in disaster areas have been proposed; most of these systems have only been evaluated using simulations, and the system's performance is not evaluated in real-life scenarios. By evaluating systems in real-life scenarios, the practical requirements of using these systems in disaster scenarios will be assessed. Although the difficulty in evaluating the systems in real disaster scenarios is clear, most of the functionalities of the systems can be proved in real-life scenarios emulating a postdisaster situation as it is done in [48]. Finally, many of the proposed schemes depend on manual user interaction, which can be inefficient. For future work, more automated independent systems can be researched.
4.2. VANETs
Broadcasting for emergency scenarios is an active research topic in VANETs. However, there is no comparison among all the proposed schemes in the literature. Furthermore, the efficient deployment of ad hoc RSU after a disaster is also seen as a challenge for VANETs.
4.3. WSNs
Regarding open challenges in WSNs, more automated WSN node deployment systems need to be researched as it is sometimes difficult to deploy the nodes manually in a disaster area either during or after the disaster. On the other hand, most of the evaluation of the proposed work is simulated using static nodes, which is not the case in some real scenarios; thus the performance of proposed work using mobile nodes still requires further research. Since the sensor market continues to evolve, new sophisticated solutions based on WSN will be possible in the near future. Mobile phone sensing and crowd sensing will be possible due to the incorporation of new sensor technologies in the new generation of smartphones.
4.4. Integration of Different Ad Hoc Paradigms
Although there are existing works that prove the feasibility of the combination of different ad hoc networks in a unique system, more work is needed to find an integral and complete solution. The interoperability between MANETs and DTNs has already been demonstrated successfully in several works [51, 95]. However, little effort has been applied to demonstrate the interoperability between other technologies such as WSNs and MANETs or DTNs. The main issue for this interoperability is due to the fact that these ad hoc paradigms normally use different wireless technologies. It could be solved by incorporating bridge platforms in WSNs, for instance, to communicate WSNs using ZigBee and MANET or DTN using WiFi and/or Bluetooth.
4.5. Mobility Models
In general, most studies are based on synthetic mobility models, which are the least accurate. Consequently, more studies based on real traces are necessary to validate ad hoc communication in real-life disaster scenarios. Regarding the design of mobility models for disaster response scenarios, the majority only considers the mobility of crew members ignoring the positions and mobility of possible victims. Furthermore, real-time decision making of tactical movements for crew members is based on the actual conditions of disaster scenarios with respect to victims' positions and their movements.
5. Conclusions
The applicability of ad hoc networks in disaster scenarios is still in an initial phase. Most works done on this idea are only based on simulations rather than real experimentation. After more than a decade of study, it is time to put in practice the main findings on ad hoc networks which reveal a suitable technology to cope with the hostile and decentralized conditions during and after a natural or man-made disaster. The work based on real experimentation presented in this survey reveals that the application of ad hoc networks in disaster scenarios is feasible and may help save many lives and reduce the number of casualties. In this paper, the main fields of application of the different ad hoc paradigms found in the literature are surveyed and the main contributions made by researchers in the last decade are also reviewed. However, it is clear that more research is needed; in particular, more work is required to achieve the desirable interoperability among the different ad hoc paradigms, which is a primordial requirement to obtain an integral and complete ad hoc system for disaster response. In this sense, the use of smartphones seems to be crucial in achieving this objective since it is a portable device that is used by civilians on daily basis. Private solutions would restrict the application field of disaster response networks to rescue teams carrying specialized electronic devices. Therefore, an open solution is required to combine the efforts and obtain collaboration among the crew members of rescue teams, civilians acting as volunteers, and the victims, that is, achieving collaboration among all the possible elements taking part in disaster scenarios.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgment
This work was supported in part by the University of Seville under the PhD grant PIF (Personal Investigador en Formación) of Daniel Gutiérrez Reina.
