Abstract
In last decade, there have been many research works about wireless sensor networks (WSNs) focused on improving the network performance as well as increasing the energy efficiency and communications effectiveness. Many of these new mechanisms have been implemented using the behaviors of certain animals, such as ants, bees, or schools of fish. These systems are called bioinspired systems and are used to improve aspects such as handling large-scale networks, provide dynamic nature, and avoid resource constraints, heterogeneity, unattended operation, or robustness, among many others. Therefore, this paper aims to study bioinspired mechanisms in the field of WSN, providing the concepts of these behavior patterns in which these new approaches are based. The paper will explain existing bioinspired systems in WSNs and analyze their impact on WSNs and their evolution. In addition, we will conduct a comprehensive review of recently proposed bioinspired systems, protocols, and mechanisms. Finally, this paper will try to analyze the applications of each bioinspired mechanism as a function of the imitated animal and the deployed application. Although this research area is considered an area with highly theoretical content, we intend to show the great impact that it is generating from the practical perspective.
1. Introduction
In recent years, researches on wired sensor networks have evolved to wireless infrastructures for implementing wireless sensor networks (WSNs) [1]. A WSN consists of interconnected nodes connected using the air medium to perform distributed sensing tasks. These networks are widely used in agriculture [2], health [3], natural disaster monitoring [4], security and surveillance [5], war ambient [6], and many other fields of interest. WSNs are considered the most appropriate choice in various disciplines for monitoring, sensing, and collaborative decision making. The integration of detection systems, signal processing, and data communication functions converts the WSN in a powerful platform to process the data collected from the environment. The algorithms and protocols for these networks must be able to permit the network operation during the initialization, normal process, and emergency situations. WSNs researchers pursue several requirements, among which we can highlight the following.
Ensure sufficient bandwidth to ensure proper performance.
Reliability in the network, ensuring a sufficient level of fault tolerance to recover when there is a node failure [7].
The energy becomes a crucial point because sensor devices are powered by batteries [8, 9].
The consumption of hardware resources is another of the associated problems especially when it comes to devices intended to be deployed in large spaces monitoring, control, and sensing of intelligent environments, and so forth [10].
The type of used routing protocol is an important aspect to bear in mind because in most cases, it is in charge of multihop wireless networks in which each node must perform the routing functions of those data from a node to another [11].
Efficient architectures and topologies to solve any WSNs requirements [12, 13].
Besides the safety aspects covered by WSNs requirements, it is important to include the availability, integrity, authentication, and confidentiality [14].
These problems and requirements have been widely addressed by the scientific community and there are solutions that have been successfully applied in several application areas. However, recent researches in the WSNs field tend to mimic some biological and animal behaviors which can be easily observed in nature. They are known as bioinspired systems.
Bioinspired systems can be built by hardware or software configurable systems and electronic systems that emulate the way of processing information and problem solving of biological systems. When we look at nature, many types of behavior are observed. Most species of animals show social behaviors. In some species, there is a dominant individual who leads all group members. This is the case of lions, monkeys, and deer. However, there are other types of animals that live in groups with no dominant leaders. In such animals, each individual has an organized behavior that allows them to move through their environment without leader such as birds, fish, bees, ants, or flocks of sheep. In this second type of behavior, animals have no knowledge of the group and the environment in which they move. Instead of this, they move through the environment by sharing information with the closest members. This simple interaction between individuals makes the group behavior more sophisticated [15]. Within imitated bioinspired behavior systems we can also find biological models such as the spread of epidemics or immune systems. The immune system of a human or animal is a complex natural defense mechanism. It has the ability to learn about foreign substances (pathogens) that enter in the body and respond to them by producing antibodies that attack the antigens associated with the disease [16, 17]. These biological behaviors are, in general, the result of millions of years of the nature evolution.
New systems and architectures are tending to include bioinspired systems. The main reasons, among others, are [18] as follows.
They are able to adapt to the medium changes.
The bioinspired systems exhibit high strength and resistance to failures caused by internal or external factors.
Allow implementing complex situations and behaviors in a limited set of basic rules.
These systems are able to learn and evolve as new conditions occur.
They are able to efficiently manage limited resources.
The set of nodes that implement these systems are able to self-organize in a fully distributed manner achieving an efficient collaboration.
These features give rise to different levels of implementation to the each proposed bioinspired approach, design, and algorithm in every network layer of the WSN, making them more robust, efficient, and resistant to any kind of failure.
We have found in other areas, like MANET, several surveys which include the main bioinspired mechanism [19, 20]. This survey is intended to review the state-of-the-art of the main animal behavior and bioinspired systems used in WSNs. The study will be performed from two points of view. The first one analyzes and explains the main animal and natural behaviors used in the field of WSNs. The second point of view will consider the applications in which these bioinspired mechanisms are employed. Finally, we will statistically analyze the use of each type of application as a function of each mechanism.
The rest of the paper is structured as follows. Section 2 presents and explains the main features of each mechanism as well as the aspects of the imitated natural behavior. Section 3 shows other proposals based on nonanimal behaviors. Using the data presented in Sections 2 and 3, Section 4 will perform an analytical discussion about the use of each mechanism. Finally, conclusion and future works will be shown in Section 5.
2. Animal Behavior Used in WSN
This section presents animal behaviors which are most used in WSNs. They are reviewed from both perspectives, the development of new systems and the improvement of existing systems.
2.1. Ant Colony Optimization (ACO) Algorithm
This section presents the operation of ACO and its principles in which bioinspired systems are based. After that, we will see some examples where ACO has been used with different purposes.
2.1.1. Imitated Natural Behavior Mechanism
In the natural world, initially ants wander randomly. When the food is found, they come back to their colony leaving a trail of pheromones. If other ants find the trail, probably, these ants do not continue walking randomly and follow the pheromone trail. If they eventually find food, ants return and reinforce the trail.
However, over time the pheromone trail starts to evaporate; thus its attraction is reduced. The more time an ant takes to go and come back through the trail, the more time the pheromones will be evaporated. A short path, by comparison, is transited more often, and thus the pheromone density becomes larger in short paths than in longer ones. Pheromone evaporation also has the advantage of avoiding convergence to local optima. If there was no evaporation at all, the paths chosen by the first ants would tend to be excessively attractive to the following ants. In that case, the search space of solutions would be limited.
Therefore, when an ant finds a good path between the colony and the food source, the other ants will most probably follow this path and the positive feedback eventually leads all the ants to a single path. The idea of the ant colony algorithm is to imitate this behavior with “simulated ants” walking through a graph representing the problem. Figure 1 shows the evolution of pheromones that an ant deposits in a way, and how the preferred routes are generated in ant colonies.
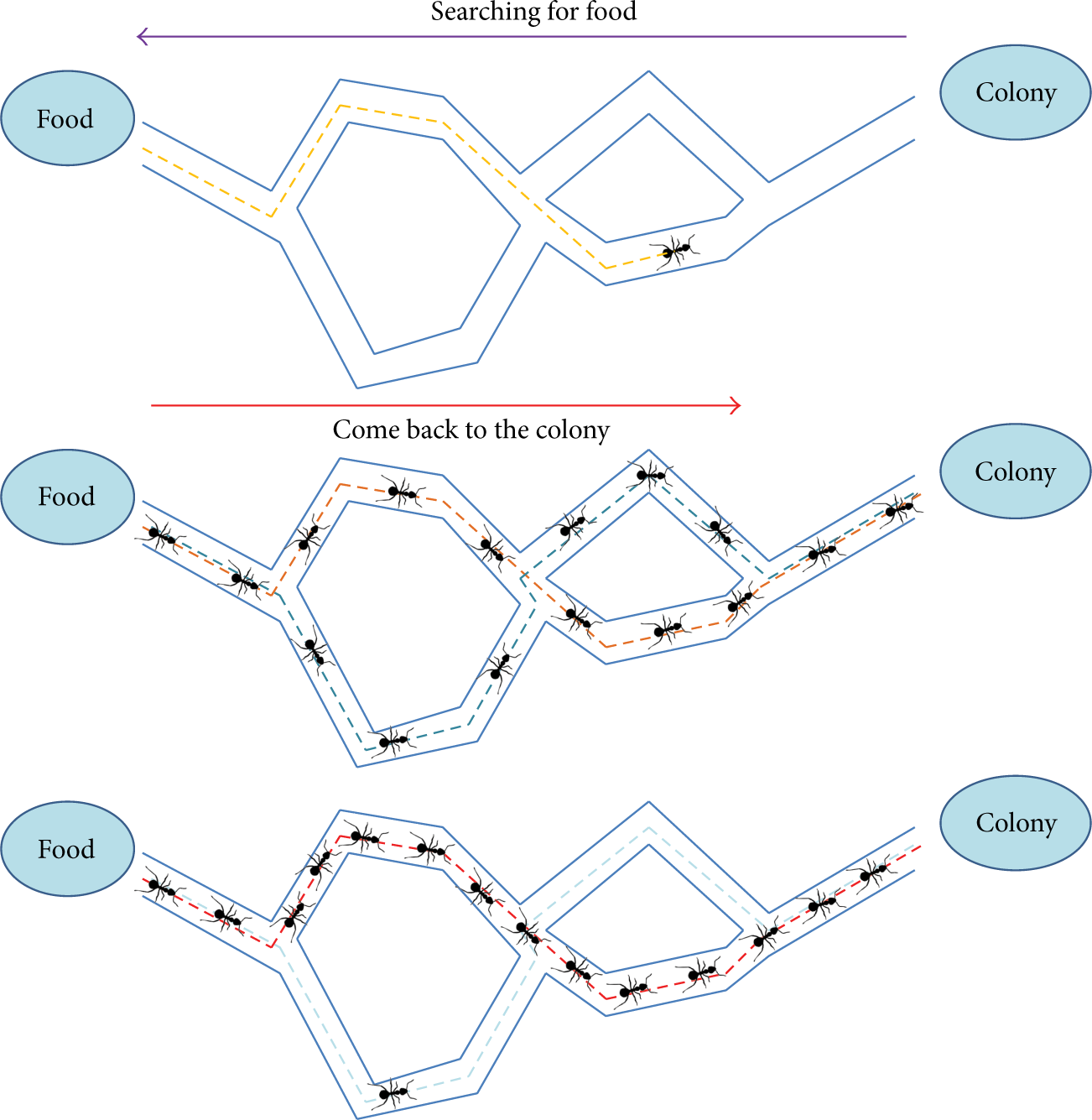
Evolution of pheromones that an ant deposits in a way and how the preferred routes are generated in ant colonies.
The original idea comes from observing the exploitation of food resources among ants, in which ants cognitive abilities are limited individually and together are able to find the shortest path between a food source and their nest or colony [21]. The process runs as follows.
An ant wanders randomly around the colony.
If it locates a food source, it returns to the colony more or less directly, leaving behind a trail of pheromones.
The closest ants will be attracted to these pheromones and new ants adhere to the track more or less directly.
Returning to the colony, ants have strengthened that route.
If there are two paths to reach the same food source, then, in the same given amount of time, the shortest route is traveled by more ants than the longest path.
The shortest path will have increased the amount of pheromones and therefore it will begin to be more attractive.
The longest route will disappear because pheromones are volatile.
Finally, all the ants have determined and chosen the shortest path.
Ants use the environment as a means of communication. They exchanged information indirectly by depositing pheromones on their path, detailing the status of their work. The information exchanged has a local environment. Only an ant located near to the deposited pheromones will know that they are there. This system is called Stigmergy and occurs in many societies of animals. This system is based on the positive feedback (deposition of pheromone attracts other ants and these strengthen such feedback) and negative feedback (route dissipation by evaporation). Theoretically, if the amount of pheromone was the same on all routes at all times, no route was chosen. However, due to feedback, a slight variation on a route will amplify the trail and then, the best path will be chosen.
2.1.2. Works Bon Ant Colony Algorithm
In [22], Camilo et al. presented two ant-based routing algorithms. The first one considerably reduces the size of routing tables, which implies a reduction of the required memory by the node. This proposal also considers the energy levels of the nodes where system gives preference to a longer path with high energy level than a shorter one with lower energy levels. Authors also present the Energy-Efficient Ant based Self-organized Routing (EEABR) which aims to create the best path based on the best pheromone distribution. In this proposal, nodes near the sink present the highest pheromone levels and remote nodes will be forced to find better paths. Their experiments show that EEABR leads to very good results in different WSN scenarios.
T-ANT [23] is a bioinspired approach for data gathering in WSN. This algorithm is based on ant swarm that controls the election of cluster head for obtaining a uniform distribution. Compared with tradition methods such as LEACH, T-ANT needs less memory resource because it can exploit the inherent data correlations in sensed data signals. The results demonstrated that T-ANT reaches significant energy savings for periodic monitoring applications.
An ant-aggregation method for WSN is proposed in [24, 25]. The main aim is to find a solution for the optimal aggregation problem. The method is based on multihop connections and in its operation builds trees with the aim of having the smallest accumulation of cost. In this proposal, the ants have to find the shortest path to the sink or to the nearest aggregation node. Authors compared the simulations of both, the opportunistic aggregation method and the incremental aggregation method. The results show that the energy efficiency in opportunistic aggregation method depends on the number of sources. Simulations show that optimal aggregation method is able to save more than 45% of energy waste in some cases.
The protocol Many-to-One Improved Ant Routing (MO-IAR) is proposed in [25, 26]. MO-IAR is specifically tailored for routing upstream many-to-one sensory data. This protocol operates on two different stages. Firstly, the system finds the shortest path between the nodes and the nest. When those paths are found, it searches the shortest route taking into account the network congestion for minimizing the packet loss. Authors compare their proposal with other related ACO algorithms. MO-IAR presents higher performance in terms of finding the shortest path in the shortest time. The congestion behavior of MO-IAR also presents satisfactory results in comparison with other tested protocols.
Almshreqi et al. [25] and Chen et al. [27] presented other ant system that overcame defects of the conventional routing protocols based on ACO. They adopt a “retry” rule to avoid the deadlock algorithm. The system also adds search ants that are able to reduce the number of “retry.” Finally, these proposals introduce a strategy for simulating the pheromone update aimed to accelerate the network convergence. Their simulation results show that this algorithm is able to reduce the total routing cost in WSNs. Their protocols are also more scalable, practicable and efficient than traditional ones.
Saleem et al. [28] and Okdem and Karaboga [29] proposed routing protocols based on ant colony optimization to obtain longer network lifetime, but ensuring, at the same time, that data transmission is efficiently achieved. These proposals discover the shortest paths using an evolutional optimization technique. It provides an effective multipath data transmission. In case that a node fails, the communication inside the WSN remains working. For the implementation, authors used reduced size hardware to solve the space constraints.
Almshreqi et al. [25] and Salehpour et al. [30] show a methodology for cluster-based large scale wireless sensor networks. This proposal works in two stages. Firstly, the system works in intra-cluster level where the sensor nodes transmit their information immediately to the cluster head. Secondly, using the ant-based system, the head clusters discover the route to the sink node. Authors performed a comparison between LEACH and ACO algorithms. Their results show that proposed algorithm present higher network lifetime than the other methodologies. Other simulations between LEACH and the proposal show that proposed algorithm keeps the same level of dissipated energy than LEACH, even changing the number of cluster heads.
SensorAnt [25] uses a new routing scheme to optimize the energy of the sensor nodes. In this scheme, each node compares its information with its neighbors at the beginning of process in order to find the best route to the skin. Authors compare their proposal with EEABR. Their algorithm presents better performance than EEABR in terms of total energy consumption and the energy efficiency. SensorAnt maintains the energy consumption even when WSNs increase the number of sensor nodes. Energy consumption in EEABR increases when the WSN becomes larger.
Wen et al. proposed a dynamic adaptive ant algorithm called E&D ANTS [31]. This algorithm is based on the Energy and Delay metrics for routing operations. Their main objective is to maximize the network lifetime though reducing the propagation delay. In order to achieve these goals, E&D ANTS uses a variation of reinforcement learning. The experimental results show that E&D ANTS presents better performance than AntNet and AndChain. E&D ANTS present communication efficiency up to seven times higher than the AntNet and improve the performance of Ant Chain by more than 150%.
BIOSARP [28] is an Ant Colony inspired Self-Optimized Routing Protocols. It is a specific mechanism that takes into account three variables: speed, link quality and remaining energy in the mechanism. Authors proposed the use of a cross layer design which offers a better delivery radio, maintaining the energy consumption. This issue is especially remarkable in the case of real time traffic. The used algorithm is able to avoid permanent loops. Simulations compared BIOSARP with a real time routing protocol in terms of load distribution. The results show that BIOSARP presents better performance.
Liao et al. used ACO algorithm to solve the deployment problems [32]. The proposed deployment scheme ensures the maximum coverage and reduces the energy consumption. This implies an improvement in the WSN lifetime. The algorithm was tested in five different scenarios with different initial node density and remaining energy. The results show that when node density and remaining energy in nodes increase near to the sink, the system registers higher network lifetime. Furthermore, the proposal presents better performance than the methods previously presented.
Pavai et al. [33] and Juan et al. [34] proposed the use of Minimum Ant-based Data Fusion Tree (MADFT) as a routing algorithm for gathering correlated data in WSN. This algorithm identifies each node as an ant. Firstly, one of these ants constructs a route. After this, the other ants search the nearest point of this previous discovered route. Using a probabilistic function composed of pheromones and costs, the system can estimate the minimum total cost of the path. MADFT optimizes the transmission and fusion costs. It also adopts an ant colony system to achieve the optimal solution.
Wang and Lin proposed a swarm intelligence optimization based routing algorithm for WSNs [35]. The main goal of this proposal is to accelerate the algorithm convergence rate. The main idea of algorithm is to take less hop numbers into consideration, choosing the nodes with less pheromone as the next hop to avoid prematurely exhaust the energy of some nodes because of having many concentrated routes through those nodes. This will help system to balance the global energy consumption in network. The experiments show that the algorithm proposed in this paper is better than the Directed Diffusion routing protocol in terms of global energy equilibrium.
Jiang et al. [36] proposed a communication protocol called Quantum-inspired Ant-Based Routing (QABR) algorithm for WSNs. QABR combines the operation of quantum-inspired evolutionary algorithms (QEA) and ACO. On the one hand, authors used the concept and principles of quantum computing, such as quantum bit and the superposition of states used in QEA. In QABR algorithm, Q-bit and quantum rotation gate adopted in QEA are introduced into ACO. Their simulations let them conclude that QABR performs better than other conventional routings, such as ACOA and AODV routing. The result is that they obtain a quick algorithm with low convergence time that presents good global search ability.
A new enhanced ant colony inspired self-organized routing mechanism for WSNs is presented in [37]. Saleem et al. focused their efforts on improving the delay, energy and speed in WSNs. The proposal is based on ACO method which is utilized for the optimum route discovery in the WSN. The adopted factors help the WSN in improving the overall data throughput, especially in case of real time traffic, while minimizing the energy consumption. This algorithm is also able to avoid permanent loops. The simulations show that it is an efficient protocol that tries to enhance the sensor network requirements, including energy consumption, success rate and time. Finally its algorithm is improved with reinforcement learning feature to get a superior optimal decision.
Okazaki and Frohlich proposed in [38] a routing protocol based on HOPNET called Ant-based Dynamic Zone Routing Protocol (AD-ZRP). The proposal is a multihop and self-configuring reactive routing approach for WSN. The main aim of this protocol is to reduce the number of control packets sent from the WSN. Simulation results show that AD-ZRP presents better performance than HOPNET. The new methodology has lower routing overhead (because it needs less ants in the network). When studying the performance of AD-ZRP, the authors observed that it presents higher data packet delivery ratio and lower broken routes ratio than HOPNET.
Finally, Hui et al. [39] presented a dynamic and adaptive routing protocol based on ACO. This routing protocol is used to minimize the energy waste thought optimizing the global balance energy in the nodes. For this purpose, the protocol takes into account parameters such as path delay, node energy and the frequency that a node acts as a router to achieve a dynamic and adaptive routing. The tests are performed to check three important aspects: neighbor discovery, routing and data transmission, and route maintenance. Simulations compare this proposal with two popular WSN routing protocols, SPEED protocol and EAR protocol, in order to demonstrate the increased WSN lifetime. The proposal shows better performance in terms of energy consumption levels versus node density and higher node operational time than SPEED and EAR.
2.2. Honey Bee Colony
The Honey Bee Colony behavior is explained in this subsection. This subsection also presents several examples and proposals where this mechanism is used to solve some issues in WSNs.
2.2.1. Imitated Natural Behavior Mechanism
Bees are social insects that live together in large and well-organized family groups. Their high evolution allows them to perform many complex tasks that cannot be performed by solitary insects. Tasks such as communication, construction of the hive, environmental control, defense or the division of tasks are just some of the behaviors that bees perform in social colonies.
A honey bee colony typically consists of three kinds of adult bees: workers, drones, and a queen. Each member has a task to perform, related to its adult age. Surviving and reproducing take the combined efforts of the entire colony. Individual bees cannot survive without the support of the colony. The structure of the colony is maintained by the presence of the queen and workers and depends on an effective communication system. The distribution of chemical pheromones among members and communicative “dances” are responsible for controlling the activities necessary for the colony survival. As the size of the colony increases, so does the efficiency of the colony.
In computer science and operations research, the artificial bee colony algorithm (ABC) is an optimization algorithm based on the intelligent foraging behavior of honey bee swarm, proposed by Karaboga in 2005 [40]. In the ABC model, the colony consists of three groups of bees: employed bees, onlookers and scouts. The algorithm assumes that there is only one employed bee for each food source, that is, the number of employed bees in the colony is equal to the number of food sources around the hive. Figure 2 shows an example of hive.
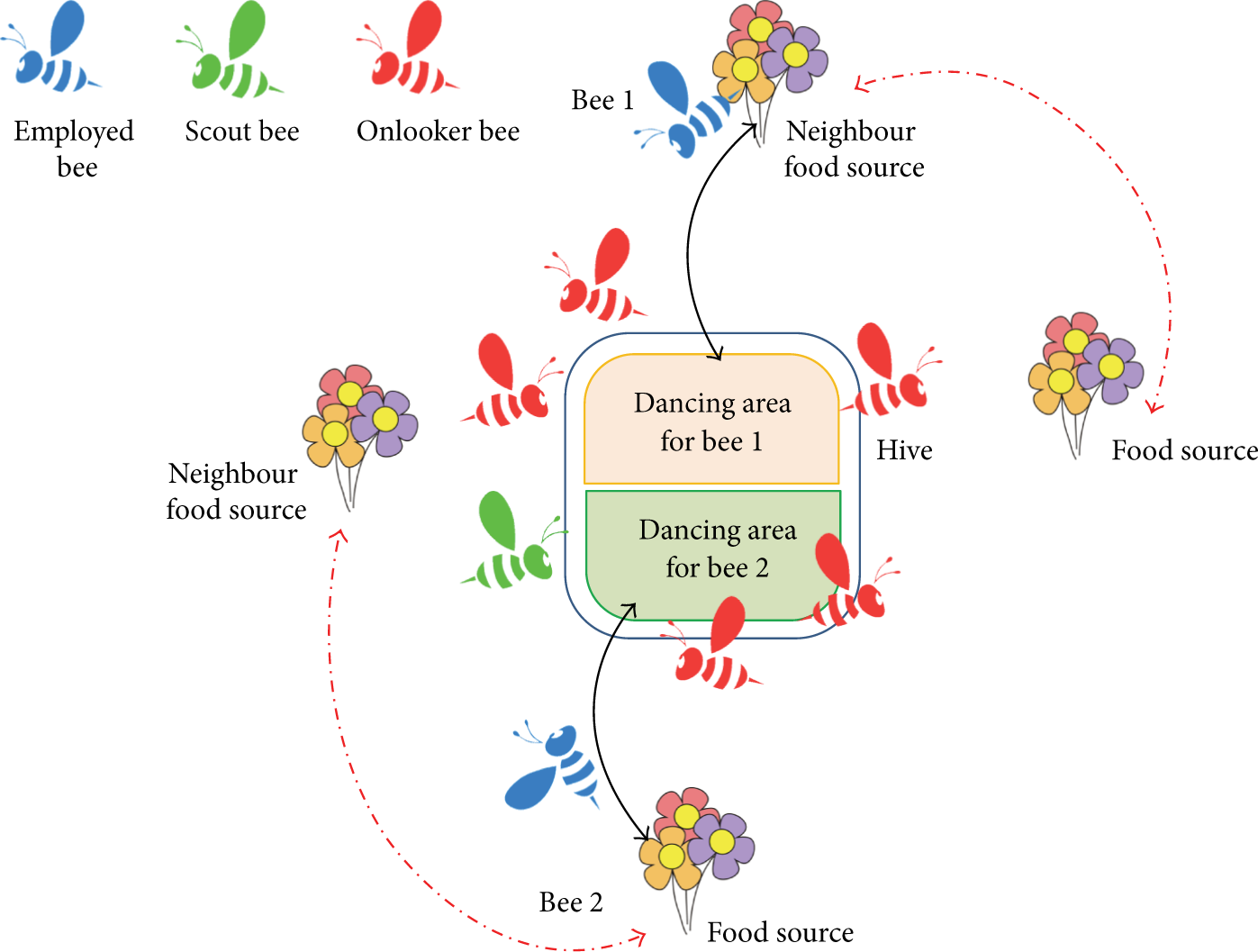
Hive and the kind of bees involved in the process.
In this case, employed bees go to a food source in their memory and determine a neighbor source. Then, the bee evaluates its amount nectar and comes back to the hive and dances around the hive's area. The employed bee whose food source has been abandoned becomes a scout and starts to search for finding a new food source. Abandoned food sources are determined and are replaced with the new food sources discovered by the scouts. Onlookers watch the dance of the employed bees and choose one of their sources depending on the dances, and then they go to that source. After choosing a neighbor around that, it evaluates its amount nectar. Finally, the best found food source is registered. This process is repeated until the requirements of nectar are met.
2.2.2. Works Based on Bee Honey Colony Algorithm
BeeSensor [39] is a bee-inspired power aware routing protocol for WSN. This protocol has better performance than the traditional ones, like the optimized version of Ad hoc On-demand Distance Vector (AODV). The percentage of delivery packets for BeeSensor is 25% higher than for AODV. In addition, the computational complexity and control overhead are higher in AODV than BeeSensor. Finaly the BeeSensor lifetime is better than the values offered by AODV.
The Pheromone-Signalling-Based Load Balancing Algorithm is presented in [40]. It is based on the process in which the bee queen brings pheromones to the other bees in the hire. When the bees do not feel the pheromone, they assume that the bee queen is death and create a new bee queen. In WSNs, there is a sensor node, or queen node (QN), responsible of managing the execution of all service requests it receives. The other nodes are work nodes (WN). All the nodes (QN and WN) can execute all different tasks, but WN only execute tasks if QN explicitly asks them. Once the QN transmits the “pheromones” to the nearest WN, a WN can transmit it to the other WNs that are far from the QN. The performance of this algorithm allows higher network lifetime (around 10%) than the average time. But, it also presents up to 85% of improvements in service availability in final stages of the system lifetime.
Ismail and Hassan [41] proposed a 6LoWPAN Local Repair Using Bio Inspired Artificial Bee Colony Routing Protocol. The system is aimed to improve the modified AODV for 6LoWPAN to minimize the energy waste and delay with minimum network overhead in a 6LoWPAN mesh network. This proposal is designed with the aim to minimize the new initiation of route request. With all these improvements the network lifetime increases.
BEES [42] is considered as a novel backbone construction protocol for WSN. This protocol is aimed to create bee tiles as identical regular hexagons around the sink node. Its main advantage is that BEES helps to mitigate many of the challenges inherent to WSN such as localization and clustering. It also can simplify many management tasks as data aggregation, leader election, task management, and routing.
BEE-C is a routing algorithm that can reduce the energy consumption in WSN. It was proposed by Da Silva Rego et al. in [43]. BEE-C uses a bionsipered method for clustering the network which is based on the bees’ reproduction behavior. It is used to group sensor nodes in order to optimize energy consumption. The experiment results show that the performance of BEE-C presents enhances in comparison to other traditional algorithms like LEACH and LEACH-C. The most important advantages are given in the network lifetime, the low number of sent packets to the base station and in the total network coverage, as a result of using the energy efficiently in the network.
2.3. Bird Flocks and Fish Swarms
This section presents a description of several Bird Flocks and Fish Swarms inspired mechanisms.
2.3.1. Imitated Natural Behavior Mechanism
Swarming behavior is a collective behavior shown by animals of similar size which move together, milling about the same point or moving in masse. Swarming is usually applied to insects, but this term can also be applied to any other animal that exhibits swarm behavior. The flocking term is often used for referring specifically to swarm behavior in birds, herding refers to swarm behavior in quadrupeds, shoaling or schooling refers to swarm behavior in fish. This subsection explains the generalized swarm behavior for fish swarm and bird flocks. The explanations will be particularized for bird flocks, although these words could be particularized for fish swarms [44, 45].
A flock is a group of birds that present a similar flight or while foraging behavior. The main benefit is the safety of the group that implies an increase of foraging efficiency. The flocks of animals can be formed for specific purposes and the benefit of aggregating is very important in aspects such as defense against predators in closed habitats where predation is often given by ambush. Flocking also has costs to socially subordinate birds which are often bullied by dominant birds. These birds may often be sacrificed in benefit of the rest of the flock.
The basic models of flocking behavior are explained by three simple rules that follow a distributed natural flock behavioral model:
Separation: a bird will turn when another bird gets too close.
Alignment: a bird tends to turn when it is moving in the same direction that nearby birds.
Cohesion: a bird will move towards other nearby birds (unless another bird is too close).
When two birds are too close, the “separation” rule overrides the other two, which are deactivated until the minimum separation is achieved. Each bird always moves forward at the same constant speed. Figure 3 shows these three behaviors.

Bird behavior: (a) separation; (b) cohesion; (c) alignment.
Each bird acts as an independent object that navigates according to its local perception of the environment, following the physics laws that rule its motion. The bird can perceive other birds at a given distance and at an angle with respect to the direction of its motion, that is, the bird cannot see beyond a certain boundary or beyond a specific angular range. Figure 4 shows this situation.

Geometric neighborhood.
2.3.2. Works Based on Bird Flock Algorithm
The flock-based congestion control (Flock-CC) is proposed in [46] and with some modifications in [47]. It can be considered as a robust and self-adaptable congestion control mechanism. This mechanism involves a minimal exchange of information and it can increase the WSN lifetime. It also maintains a high quality of service (QoS). The aim of this approach is to guide packets (birds) to create flock and pass (flying) together towards a global actuator, trying to evade the congested regions (obstacles). The performance results show that Flock-CC approach reaches low packet loss, high packet delivery ratio and thus reliability, fault tolerance and low latency. It also outperforms congestion-aware multi-path routing approaches in terms of packet delivery ratio. Antoniou et al. also indicate that Flock-CC has low energy consumption [48].
Ruihua et al. presented a double cluster-heads clustering algorithm based of the particle swarm optimization algorithm [49]. Authors define a new function that takes in account two factors in the cluster-head selection algorithm. The first factor is in regard to the minimum distance between the cluster head and the member node. The second one is the residual energy of the nodes. The system adopts the dual cluster head strategy for balancing the network load. The results indicate that this new algorithm makes the WSN achieve larger network lifetime in comparison with traditional protocols such as LEACH and the combination PSO-LEACH.
In [50], Ma et al. presented the Adaptive Assistant-Aided Clustering protocol for WSN using Niching Particle Swarm Optimization (AAAC-NPSO). Authors define a threshold function to decide the assistant-aided CH in a cluster. The function considers some parameters such as the residual energy, distance between the CH and the base station, and the number of nodes in the cluster. NPSO algorithm is able to reduce the energy consumption and prolong the network lifetime compared to LEACH and PSO-C.
Particle Swarm Optimization is also used to solve the problem of node location after the network deployment [51, 52]. Authors develop a set of simulations to estimate the goodness of this approach. Simulations evaluated some parameters such as the number of localized nodes, computation time, and localization accuracy. The simulation results of PSO, bacterial foraging algorithm, and a traditional method show that PSO is the method that determines the coordinator node in a shorter time.
2.3.3. Works Based on Fish Swarm Algorithm
In [53], authors proposed a hierarchical routing protocol based on Artificial Fish Swarm Optimization (AFSO). This model imitates some fish behaviors such as praying, swarming, following fishes, and so forth. Song et al. used AFSO in the cluster formation phase to solve the NP-hard problem of finding k optimal clusters according to a set of given rules. Traditional protocols, like LEACH, do not offer any guaranties of the position and number of cluster heads. AFSO showed better clusters formation because it dispersed the cluster head nodes throughout the network. Results show that AFSO protocol improves the energy efficiency and prolongs the WSN lifetime thanks to the distribution of the cluster heads.
Neshat et al. [45] and Gao et al. [54] presented a proposal called Improved Artificial Fish Swarm Algorithm (IAFSA). IAFSA included advantages like high convergence speed, flexibility, error tolerance, and high accuracy, while maintaining the behavior of AFSA. The experimental results show that IAFSA presents some advantages such as the fact that it has faster convergence time or higher global search accuracy in respect to the standard AFSA. These enhances make IAFSA advisable for applications in various fields like optimization, control, image processing, data mining, improving neural networks, data networks, scheduling, and signal processing.
Jiang et al. proposed the use of the crossover operation into the Artificial Fish-Swarm (AFA) optimization algorithm and a fusion of the Culture Algorithm (CA) and AFA to enhance the optimization efficiency and combat the blindness of the search of the AFA (CAFAC) [55]. A total of four versions of the CAFAC algorithm are explored. Numerical results show that this new algorithm can outperform the original AFA. The knowledge-based AFA performs much better than the original algorithm. Therefore, the knowledge in the cultural framework can be viewed as an effective and directive term in the evolution of the AFA.
Wang and Ma presented a hybrid artificial fish swarm algorithm, which is combined with CF approximation algorithm and Artificial Fish Swarm Algorithm to solve the packing problem [56]. Experiment results show that when it is compared with GA, the Hybrid Artificial Fish Swarm Algorithm has a good performance with broad and prosperous application, enhancing aspects such as computing speed and accuracy.
The algorithm presented by Fernandes et al. in [57] is a modified version of the artificial fish swarm algorithm for global optimization, denoted by Fish Swarm Intelligent (FSI) algorithm. The main modifications of this algorithm are the following ones: an extension to bound constrained problems meaning that any fish movement will be maintained inside the bounds along the iterative process; modified procedures to translate random, searching, and leaping fish behaviors; the introduction of a selective procedure and different termination conditions. The results show that FSI improves some WSN issues that other existing algorithms are not able to solve.
Yiyue et al. presented a deployment optimization scheme for WSNs which is composed of fixed sensor nodes and some mobile sensor nodes [58]. This proposal is also based on the Optimized Artificial Fish Swarm Algorithm (OAFSA). In this case, authors introduced a modification in OAFSA for including a dynamic threshold to improve the coverage problems of AFSA. Simulations compared OAFSA and traditional ASFA. The results show that the new approach presents better performance. In fact, OASFA is able to increase the network coverage. However, the convergence speed of AFSA is higher than the OAFSA so; there is no improvement in the convergence speed.
2.4. Bat Behavior
Most species of bats rely on echolocation to find their prey. For this reason, they have no problem to find a prey in dark environments. Calls from the bat can reach up to 130 decibels and it is considered as the highest of all flying animals in the world [59].
The echolocation process is very complex and it has been studied in detail by several researchers [60]. Bats are able to differentiate between incoming and outgoing signals and it is the way they can differentiate between sent and received communication. Bats use sonar echoes to detect and avoid obstacles. It is generally known that the sound pulses are transformed to the frequency that is reflected from an obstacle. Bats use delay time from transmission to the reflection for navigation. After hitting and reflecting on the object, bats transform their own pulse to use this information to measure how far away the prey is. Figure 5 shows a bat emitting and receiving a wave to detect an object and the perceived wave by the animal for each ear.

A bat emitting and receiving a wave to detect an object and the perceived wave that the animal has for each ear.
This behavior can be modeled using the following three general rules [61].
All bats use echolocation to sense the distance, and they also guess the difference between food/prey and background barriers in an inexplicable way.
Bats fly randomly and they fix a minimum frequency, varying wavelength, and loudness to search for a prey. They can automatically adjust the frequency of their emitted pulses depending on the proximity of their target.
Although the loudness can vary in many ways, we should assume that the loudness varies from a high to a minimum constant value.
This algorithm is mainly used for node localization in WSNs. There are very few works based on bat algorithm. Some of them are the next ones.
Goyal and Patterh addressed in [62] the problem of nodes localization in WSN. They proposed to use the Bat Algorithm (BA) to solve this problem. Authors performed a comparative simulation between BA and the Biogeography-Based Optimization (BBO) algorithm. Simulations were performed considering 40 target nodes. 20% of these anchor nodes were randomly deployed in a field of
Goyal and Patterh also studied how the mean location error was affected by parameters as field size, transmission range, anchor nodes, and sensor nodes [63]. After a set of simulations, the results show that the localization mean error decreases when the number of anchors and transmission range increase. This value also increases when the number of sensor nodes and field size gets higher.
2.5. Fireflies Behavior
There are about two thousand firefly species and most of them produce short and rhythmic flashes. The pattern of flashes is often unique for a particular species. The flashing light is produced by a process of bioluminescence. There are many theories regarding to the importance of flashing light in firefly's life cycle but many of them converge to mating phase [64], that is, to communicate, to attract a prey, and as protective warning mechanism [65].
The light intensity at a given distance from the light source follows the inverse square law. Air also acts as absorbent and light gets weaker when the distance increases [66]. Combining these two factors the visibility of fireflies is reduced to a limited distance. But, it is sufficient for fireflies to communicate between them at distances of few hundred meters at night.
The flashing light of fireflies can be modeled to formulate new optimization algorithms for WSNs. Firefly algorithm is based on the flashing characteristic of fireflies. It follows three idealized rules.
All fireflies are considered as unisex and a firefly will be attracted to other fireflies regardless of their sex.
Attractiveness is proportional to their brightness, thus for any two flashing fireflies, the less bright one will move towards the brighter one. The attractiveness is proportional to the brightness, that is, for a couple of individuals, the less bright firefly will move towards the brighter one. But if no one is brighter than other, they will fly randomly. In addition, the brightness of both will decrease as their distance increases.
The brightness of a firefly depends on the aim function [67].
The main application of this mechanism is to find the optimized solution for a given problem. Because of its operation principles, this animal behavior is not widely used. Now some examples are presented.
Liao et al. proposed a sensor deployment scheme based on glowworm swarm optimization (GSO) [68]. This proposal can increase the coverage of the sensor with limited movement after the initial position. Its advantage is that this system does not need a centralized control, so it is easy to scale it for large WSNs. The simulation results show that GSO algorithm (compared to nonbioinspired mechanism) has higher coverage rate with limited sensor movement.
Sun et al. proposed a clustering scheme based on firefly behavior [69]. The scheme is called Clustering Firefly Synchronization Algorithm (CFSA) and it is an improvement of the Reach back Firefly Algorithm (RFA). The proposed scheme works in different steps. Firstly, each cluster achieves its own intracluster synchronization. Secondly, all clusters achieve the intercluster synchronization. After some comparative simulations, they saw that CFSA outperforms the RFA.
2.6. Other Less Used Animal Behaviors
There are some other animals’ behaviors which are less used such as the ones presented in this subsection. However, they propose very interesting approaches.
2.6.1. Termites
Termites are beings of small size and small number of neurons. They are not able to perform complex tasks individually. However, termite colony is seen as an intelligent entity because of their great level of self-organization. This allows them to perform very complex tasks. Based on the termites’ behavior, Zungeru et al. [70] performed a comparative study between three routing algorithms SC, FF, AODV, and Termite-hill algorithm. The analogy in regards to termite behavior, each node serves as a router and as a source, and the hill is a specialized node called sink which can be one or more nodes as a function of the network size. In addition, each network node can also serve as a termite-hill. The basic operation principles are the following ones. Termite-hill discovers routes only when they are required. When a node has some events or data to be relayed to a sink node, and it does not have the valid routing table entry, it generates a forward soldier and broadcasts it to all its neighbors. Authors tested the performance of the algorithm on static and dynamic sink scenarios. The results show that Termite-hill algorithm is scalable and presents lower network energy consumption.
2.6.2. Elephants
Elephants are the biggest land mammals. They live in groups. These groups can raise more than 50 individuals, so they need a well-organized structure and good communication. Some of the quotidian actions developed by the group are teamwork, offspring care, group defense, and resource acquisition. All these decisions are made by the oldest female of the group [71].
Desai et al. presented a new approach to enhance the WSN lifetime [72]. This proposal is based on the Elephant Based Swarm Optimization model. Authors present a cross layer (routing, MAC, and radio layers) approach which is compared with LEACH protocol in terms of efficiency. Simulation results show that the proposed elephant swarm optimization technique presents better performance than LEACH. The proposed model improves the network lifetime, reduces the sensor node energy decay rate, and presents lower communication overheads and higher active node ratios.
Other proposals based on Elephant Swarm Optimization model is presented in [71, 73]. Their aim also is to increase the network lifetime. As in [72], these proposals use the elephant Swarm Optimization mode to create clusters. In both proposals, there is collaborative processing to enhance the data reliability during aggregation. Authors performed several simulations comparing their proposal with the ACO model. Their results show that the data reliability of the WSN increases when Elephant Swarm Optimization model is used.
2.6.3. Monkeys
Rhesus macaques live in large multimale and female group. Females in a group very rarely move away from their groups, but the males often wander away in search of mating opportunities after attaining their puberty. Females are arranged according to their matrilineal family relationship. If that monkey dies, automatically the rank is passed to the next monkey in the hierarchy. The less dominant monkeys’ are involved in intergroup communication for giving alert calls. Following this model, Kumar and Kusuma [74] proposed a hybrid methodology based on the monkeys’ behavior to improve the traditional LEACH protocol. Simulations were performed in terms of number of dead nodes and energy consumption. The results show that this proposal presents lower energy waste than LEACH regarding the set-up phase of LEACH. The new protocol presents good scalability and it can be easily adapted for its use in WSNs.
2.6.4. Hybrid Algorithms
Breza and McCann [75] proposed the combination of two different bioinspired algorithms. They tested two combinations: flocking-fireflies and firefly-gossip. The results show that in both cases the performance of the hybrid method is the same or even better than each method alone. In flocking-fireflies combination, the synchronization time was shorter than the firefly algorithm. This is because the flocking algorithm increases the number of neighbor population of any given agent. Authors concluded that there could be certain combinations of bioinspired algorithms that may have negative effects, generating lower performance.
The hybrid algorithm based on fish and particle swarm algorithm is presented in [76]. This combination is used to solve the coverage problem. The system tries to organize the sensor nodes in order to obtain the maximum coverage for improving the performance. The combination of AFSA and particle swarm optimization (PSO) allowed it to acquire the global search capacity (from AFSA) and the rapid search ability (from PSO). The simulation results show that this new algorithm can optimize the deployment of the sensors and improve the coverage.
A combination of PSO with Voronoi Diagram is presented by Aziz et al. in [77]. This method can be used to optimize the coverage problem in WSN. Authors implemented the algorithm using MATLAB with different specifications of the WSN. They studied the effects on the algorithm due to changes in the number of sensors and the size of the region. Their results show that the proposed algorithm presents better performance with high number of sensors and small region of interest. Results are also promising for low number of sensors and large region of interest.
Sun and Tian proposed in [78] a new hybrid method for route optimization in WSNs. This method is based on a combination of modified ACO algorithm with GA. Hybrid method is used to reduce the complexity and enhances greatly its efficiency. Moreover, authors added a multipath route for transmitting data. After simulations, the results display that the new method is effective and has a better performance than ACO and GA working separately.
Falcon et al. proposed a kind of cooperative networking system in which a small team of robotic agents are placed in a base station [79]. The mission of those robotic agents is to serve an already-deployed WSN. Robotic agents perform a periodic replacing of all the damaged sensors in the field to preserve the existing WSN coverage. Authors called this novel application as multiple-carrier coverage repair (MC2R). The replacement trajectories followed by the robotic fleet are originated by a hybrid algorithm in a short running time. That hybrid algorithm uses the swarm of artificial firefly algorithm and the exploratory principles featured by Harmony search. Results show that promising solutions can be obtained in a limited time span.
2.6.5. Predator-Prey Behavior
The Lodka-Volterra model is based on nonlinear equations that predict the behavior of a predator-prey system. The variation of population size as a function of the time can be modeled as a simple balance equation. This equation predicts the changes on the population size and it depends on the interaction with resources, competitors, mutualisms, and natural enemies. The Lodka-Volterra model is based on a deterministic competition model which involves two coexisting species. In this case, the fitness of one individual is negatively influenced by the presence of the individual specie. Those individuals can be of the same specie (intraspecific competition) or from different species (interspecific competition) [80]. According to [80, 81], a WSN can be compared to an ecosystem where the nodes are grouped in different clusters. Authors proposed to use this behavior to create a congestion control mechanism. Lodka-Volterra model is able to preserve the global properties of biological processes, that is, stability, self-adaptation, scalability and fairness. Lodka-Volterra model shows that it can overcome traditional protocols like Additive Increase Multiplicative Decrease.
2.6.6. Spiders
The social spider of Congo presents a very impacting behavior when hunting its prey. These spiders live in groups which can be greater than 5000 individuals in the same spiderweb. They start the predatory behavior “dancing” on the spiderweb altogether. After certain time, all of them stop moving and detect the vibrations in the spiderweb. If a vibration is detected, it means that there is a prey in the spiderweb and all spiders move together to hunt it. The preys do not usually have any opportunity to avoid the attack. In this behavior, there is no direct communication between individuals. The silk actuates as a vector of information. Vibration goes through the silk and transmits the information from the prey. From this information, the number of spiders required for that prey is determined [82].
This behavior was used by Benahmed et al. [82] to propose a mechanism which is able to detect and delete misbehaving sensor nodes in WSNs. Like spiders, monitor nodes at each time period enter on a very short listening time. If any other node transmits in this period, it is considered as an abnormal behavior and the identity of this node is archived. If this pattern is detected in this node more times, the communications with this node will be isolated form the rest of the WSN and it will not participate in more network activity. Their simulation results show that in this new methodology, monitor nodes can detect the presence of intruder nodes. This detection probability is higher in the simulations with higher monitor nodes density.
2.7. Summary
In this section we summarize the number of works found of each revised bio-inspired mechanism. They are shown in Table 1. The most used animal inspired mechanism is the ant colony. It was the first to appear and is more widespread than the others. In the lasts years new ones like monkey behavior or elephant behavior have started to be in use.
Resume of animal bioinspired mechanisms.

3. Other Biological Behaviors Used in WSN
3.1. Genetic Algorithm (GA)
In the 1970s, John Henry Holland proposed a new idea within artificial intelligence, genetic algorithms (GA). They are so named because they are inspired by biological evolution and molecular-genetic basis. A GA is a directed search method based on probability. Under a very weak condition (that the algorithm keeps elitism, that is, always save the best element of the population without making any changes) it can be shown that the algorithm converges in probability to the optimum. That is, by increasing the number of iterations, the probability of the optimum in the population tends to 1. In recent years, GAs are being used in many areas, including advanced security mechanisms [83]. GA is based on the process that drives biological evolution, the natural selection. It is based on a series of individual solutions of a population that is modified as a function of the time. At each step, one of the individuals is selected randomly from the current population. This individual becomes a parent that produces the children for the next population. After some steps, the population starts to evolve towards an optimal solution [84].
Hussain et al. proposed in [85, 86] the use of a genetic algorithm to create energy efficient clusters for data dissemination in WSNs. After simulations, authors concluded that GA has better performance than traditional clustering protocols as LEACH or hierarchical cluster-based routing (HCR). GA also uses a cross layer optimization, so the energy consumption during the reconfiguration is minimal. Furthermore, this algorithm works trying to adapt itself to the energy levels in nodes; other cluster-based protocols do not use this technique. The proposed algorithm is able to increase the network lifetime.
Ferentinos and Tsiligiridis presented an algorithm for multiobjective optimization such as optimal design, dynamic adaptation, and energy management [87]. This proposal is based on the evolutionary optimizations of GA. The algorithm has sophisticated characteristics that make it able to decide about the sensors’ activity/inactivity schedule as well as the rotation of the CH. It also manages different sensors roles according to their wireless signal. All these improvements contribute to increase the network lifetime in the WSN.
Other approaches based on GA are presented in [84]. In this case, Bhondekar et al. use a GA for node placement. Sensors are spread and the GA decides which sensors must be active or inactive and which one will be the CH. It also decides if the normal nodes (no CH) should have medium or low transmission range. Results show that GA-generated design presents better performance than random designs. The uniformity of sensing points of optimal designs was satisfactory, operational communication, and energy consumption were minimized while maintaining the connectivity constraints.
The energy-efficient Coverage Control Algorithm (ECCA) is presented by Jia et al. in [88]. This proposal is inspired in multiobjective genetic algorithms (MOGAs). The mechanism is used in the data gathering inside the WSN. Its goal is to activate the lowest possible number of nodes in a densely deployed environment. The protocol presents two restrictions. The first one is in regards to coverage rate of the WSN. The other restriction is the number of the chosen nodes from the whole network. ECCA offers several important advantages such as negligible computation time and one-time resetting of the working state of the sensor nodes. It can also use the desired sensor field coverage and model parameters as inputs, so it has great flexibility.
In [89] authors presented a solution, based on GA paradigm, for the problem of placing multiple sinks in a time-sensitive WSN. It is called Genetic Algorithm-based heuristic for sink placement (GASP). Authors developed a series of tests aimed to compare the solution based on GA with nonbioinspired methods. Their results show that the performance of GASP is better than pure random search. GASP has more favorable behavior in respect to the quality of the solutions found and the computational effort invested, especially in large-scale networks.
Another application based on GA is presented in [90]. In this case, the algorithm is used to solve the problem of knowing the location of the sensor nodes in WSN. This information is essential in many tasks such as routing, service delivery, or cooperative sensing. Traditional methods do not bring an accurate solution. The presented algorithms were used in a simulation on a WSN with fixed number of nodes whose distance measurements were corrupted by Gaussian noise. Their results show that the proposal was able to give an accurate location of the nodes.
3.2. Immune Systems
The immune system that protects the body form the attacks of pathogens is a complex system that self-adapts to different situations. Artificial immune systems are based on functions and algorithms that mimic the behavior and properties of immunologic cells. There are two main procedures, that is, pathogens detection and pathogens elimination. In order to detect pathogens, the system must be able to distinguish between self and nonself cells. In human body, this task is performed by lymphocyte cells. When a detector finds a nonself-cell with a different mechanism, depending on the harmfulness of this cell, it can be triggered to delete that cell [91].
In [92], authors proposed a biological inspired secure autonomous routing mechanism named BIOSARP. This routing mechanism is based on ACO and a self-security mechanism based on artificial immunity system (AIS). It is able to detect the nonself-antigens (most commonly known attacks). If the system finds an abnormality, it will immediately generate a decision agent. Once the intruder alarm is generated by the monitoring agents, the security management will implement the authentication process. The system provides the security with no additional cost (control, energy waste, and computational cost), so it has a higher performance.
A new bioinspired technique for autonomous plausibility checking and data processing for WSNs was proposed by Jabbari and Lang in [93]. This methodology consists of two stages. In the first one a Neuroimmune system is introduced and developed, which is used to predict the sensor records. The second algorithm is used to evaluate the sensor records to check the plausibility of the records in the WSN. The performance of the developed technique presents a more correct data approximation than the sliding back propagation technique.
Teng et al. presented in [91] an immune inspired system which is used to locally discover and recover from losses of query messages. Authors propose the use of a cluster of loss detectors for each sensor node which cooperate in a distributed and scalable way. Detectors cooperate to locally recover from query losses, similar to antibodies in an immune system. The results show that this proposal is energy-efficient and scalable to operate in a fully distributed manner.
3.3. Bacteria
Bacterial foraging algorithm is based on the behavior of Escherichia coli (E. coli). It is a bacterium that lives in some mammals’ intestine. E. coli uses a pattern of two different moving types: tumbling and swimming and uses them to search the rich-nutrient areas. When E. coli is in neutral medium, it alternates both types of moving. When E. coli is moving to the direction of a rich-nutrient area, it uses a swimming direction. However, when swimming movement raises a low-nutrient area, a tumble movement appears and the swimming direction changes. After this tumble and few swimming steps, called chemotactic round, the bacterium finally raises a rich-nutrient location. The bacterium that raises these areas can be split into two new bacteria and the others that do not reach that area die. The bacteria reproduction process is explained in [51].
In [51, 52], a bacterial foraging algorithm is used to solve the problem of node location after the deployment. Simulations were performed for estimating the accuracy of this methodology. Simulations evaluated the number of nodes localized, the computation time, and the localization accuracy. During the PSO simulations, the bacterial foraging algorithm and a traditional method were compared. Bacterial foraging algorithm was the method that locates the sensor nodes with more accuracy.
Dhiman presented a new routing protocol in [94]. It is a hybrid protocol, partially based on bacteria foraging optimization. The Bioinspired Hybrid Routing Protocol (BIHP) uses de BFO technique in the cluster head selection phase and the hybrid protocol for achieving the improvements. Simulations compared BIHP and LEACH. BIHP is able to improve the energy efficiency of the WSN up to 35% better than LEACH. BIHP also helps to balance the energy consumption and improves the stability period for the WSN.
On the other hand, Sribala and Virudhunagar presented a modification of BFA [95] called Modified Bacterial Foraging Algorithm (MBFA). BFA is used in routing tasks to enhance the nodes’ lifetime. Meanwhile MBFA can be used for large scale optimization problems. Authors performed comparative simulations with BFA, MBFA, and LEACH. The controlled parameters were data transmission, energy waste, and the number of alive nodes. The results show that MBFA presents better performance than LEACH and BFA. BFSA is able to increase more nodes’ lifetime than the other analyzed protocols.
3.4. Artificial Plant Optimization Algorithm (APOA)
In natural environments, plants survivals depend on their capacity to sense the environment and data storage. Plants use this information to decide their next movements, that is, the new areas that are going to be colonized. Plants are continuously sensing biotic environment, but they can also do it actively. Some of the sensed parameters are light and gravity [96].
In [96] authors propose a biologically inspired (Botany) mobile agent based self-healing wireless sensor network (BIMAS). It was inspired on the concept of adopting the mobility of a wireless sensor node as a potential solution for handling the energy utilization of the wireless sensor network. The use of those mobile agents for sending sensed data to the base station can help to maintain the energy levels at sensor nodes, especially in the nodes close to the base station. If those nodes lose their energy the network may fail but BIMAS can efficiently handle this problem.
Artificial plant optimization algorithm (APOA) is a new evolutionary computation inspired by plant growing process presented by Li et al. [97]. APOA is used to solve the coverage optimization problem. APOA defines three operators: a photosynthesis operator, a phototropism operator, and apical dominance operator. Phototropism operator has the most important role for the grow direction of the branch. The phototropism operator is developed to increase the search efficiency. After simulations, the results show that APOA presents better node distribution than other algorithms.
4. Analytical Study about the Use of Bioinspired Systems
After reviewing the main models of animal and natural behavior used in the development of new improved systems for WSNs, we can perform a statistical analysis. This study can be performed from different viewpoints. On the one hand, we can analyze the type of mechanism used, that is, animals or other natural behaviors and the type of behavior that they imitate. On the other hand, it is important to know the type of application in which these systems and proposals are intended. Of course, we cannot speak in absolute values on the use of each type of mechanism. However, we can see these data as relative values to show us the tendency of researchers within this field. This section discusses and compares these data.
The first classification shows the trend of using each type of system. A relevant fact is that most bioinspired systems proposals for WSNs are based on the animal behaviors (75.00%). This is because each animal (its analogy in WSN is the sensor node) is considered as an individual which is able to perform a very limited series of tasks. However, the set of all the animals can develop very complex actions (in our case it would be the entire network of nodes) for the benefit of the whole group. In the WSN world, this benefit is translated into an improvement on energy consumption and improvement on the routing information, and so forth. The second most used method (with a value of 16.18%) is the imitation of physiological functions. This group is based on the interaction of the basic elements of a living being with its environment systems. To perform such functions, it is necessary to know both the particles as a whole organism and the environment.
The behavior of plants is the third most common mechanism (with a value of 5.88%) and, finally, bacteria behavior is the fewest employed (nearly to 3%). Figure 6 shows the measurements obtained about the percentage of mechanisms used in bioinspired proposals for WSNs.

Percentage of mechanisms used in bioinspired proposals for WSNs.
Regarding animal behavior, bioinspired systems can imitate tens of animals. However, only some of them are the most used systems (see Figure 7). The most used mechanisms are those which are based on a colony, flock, or swarm of animals. Ant colony is the most widely imitated mechanism (more than 35%). After it, bird flock, fish swarm, bee honey colony, and hybrid animal behavior present similar percentages of use (around 9–12%). With a percentage of use lower than 5%, we can find some animal behavior which is in natural habitat, although they live in society, their behavior does not imply the collaboration of several individuals. Finally, we highlight the predator-prey behavior because it is not a behavior between animals of the same society.

Bioinspired mechanism based on animals’ behavior.
Within the bioinspired systems, we have also found proposals which are not based on animals. This group includes the imitation of immune systems (17.65%), bacteria behavior (23.53%), and genetic algorithms (47.06%). Plant based bioinspired systems are used in 11.76% of cases. Figure 8 shows the percentage of use of nonanimals bioinspired systems.

Bioinspired mechanism based on nonanimals behavior.
It is important to analyze the main utilities developed and proposed for improving the efficiency of several issues in regards to WSN which use these animal and natural behaviors. As Figure 9 shows, almost 50% of new proposals are related to routing protocols. We can see that researchers are also interested in improving energy consumption (around 16%) and node localization in WSN (almost 12%). Other important issues that bioinspired systems solve are congestion control, fault tolerance, and coverage optimization, among others. Finally, we can see that there are very few bioinspired systems useful for improving security, coverage, and data collection systems in WSN. Each one represents a percentage of 2.94%.

Main purposes of bi-inspired systems in WSN.
Finally, we are going to analyze the uses of each bioinspired mechanism and whether a behavior can be used in different applications. As Figure 10 shows, most behaviors are used to solve more than one problem. However, bat, termites, elephant, spider, and predatory-prey algorithms are used to solve only one problem. The bioinspired mechanism with more utilities is the genetic algorithm with 5 different applications (routing protocol, node location, enhance energy efficient, data collection systems, and security systems). Honey bee colony, bird flock, and fish swarm behaviors have 4 different uses. Ant colony, immune systems, and bacteria behavior have 3 different purposes. The rest of bioinspired mechanisms have two different applications. Approaches in routing protocols are present in almost all behaviors (except in bat, elephant, spider, and predatory-prey behaviours). On the other hand, uses like fault tolerance, coverage optimization, or security systems are implemented by less behaviors (only two each one).
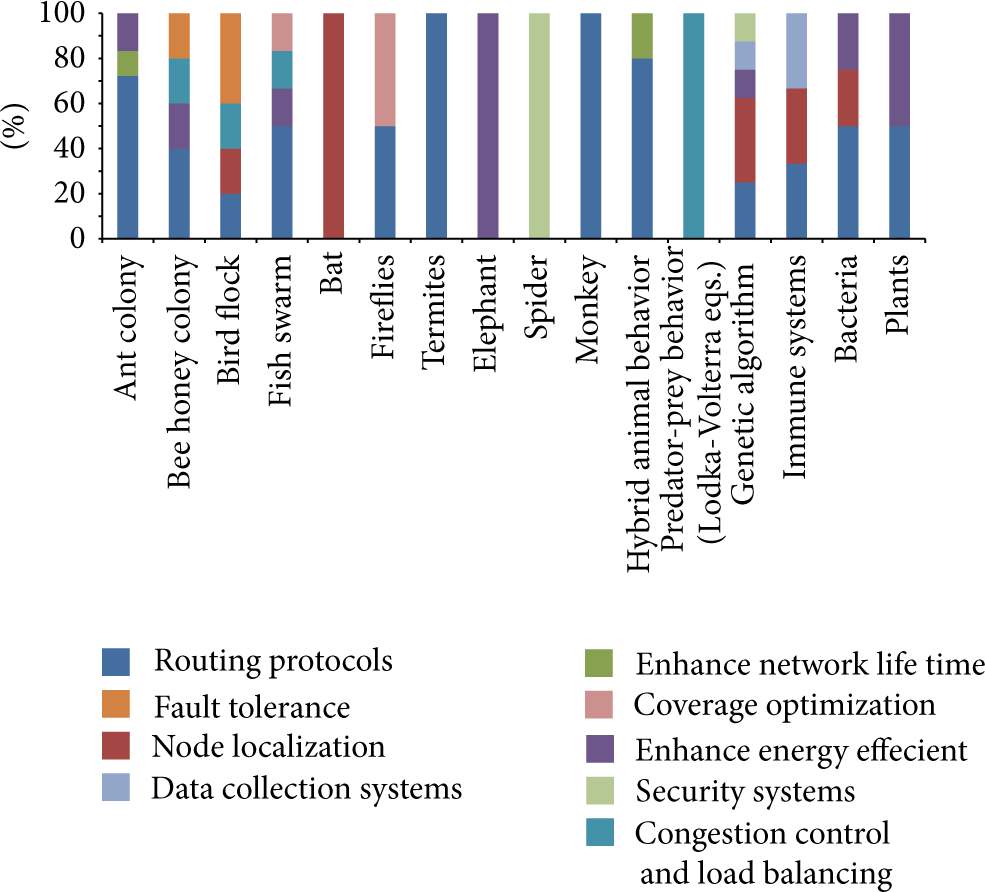
Different purposes for each bioinspired mechanism.
5. Conclusion and Future Works
Systems based on animals and natural behaviors are being used to improve and solve several issues in WSNs. Because of the interest of researchers in this topic, in this paper, we have analyzed the state of the art of bioinspired systems focused on WSNs’ issues. We have explained the most well-known animals behaviors used in bioinspired mechanisms, paying special attention to ant colony, bee honey colony, bird flocks, bats, and fireflies.
We have also analyzed several works based on nonanimal behaviors such as GA, immune systems, bacteria, or artificial plant optimization algorithm. As we can see, these behaviors are less used than animal behaviors. In fact, almost 75% of bioinspired proposed systems are based on animals’ behavior. Within nonanimals behavior, the most used is GA and the less used are the systems based on plants’ behavior.
Regarding imitated animals, the most used mechanism is the ant colony technique. Although, behaviors based on swarms or flocks are often used.
Finally, we have seen that almost 50% of proposals are focused on improving routing tasks aspects. The issue of enhancing the energy efficiency in WSN is a hot topic within bioinspired systems. A striking fact is that very few of these proposals are focused on enhancing the network security.
As we have seen, there exists a huge variety of bioinspired mechanisms. Due to the apparition of new systems in the last years, such as monkey or bat behavior, in last two years, we expect that this knowledge area will continue growing. We think that these systems will offer new contributions to the different areas where they can be applied, not only in WSN, but also in MANET, Ad-hoc network, Mathematics, Robotics, and other application fields.
As future works, we would like to analyze in depth some of these mechanisms to improve several of our proposals within WSN such as indoor location [98], environmental monitoring [2, 4, 99, 100], tracking animals [101], disabled and elderly people monitoring [102], underwater communications [103, 104], and some other systems.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
