Abstract
This paper studies the physical layer security issue for cognitive radio sensor networks (CRSNs) with primary outage constraint, for which a tractable framework is developed to analyze the secrecy performance for CRSNs related to the random channel characteristics, the spatial distributions of nodes, the nearest neighbour routing protocol, and the aggregate interference. Based on stochastic geometry technique, a novel random analysis method is proposed to derive the closed-form expression of secrecy transmission capacity and analyze the connection outage probability (COP) and secrecy outage probability (SOP) for both secondary (SR) and primary (PR) systems. Then, the concept of secrecy cognitive gain is produced to highlight the effect of SR systems with secrecy on the whole networks security. Comparing with a single PR system, the SR system is beneficial to enhance the secrecy level for overlaid CRSNs. In addition, the maximum achievable secrecy capacity is achieved through optimizing the density of SR systems satisfying outage constraints of PR and SR systems. Analytical results provide insights into regimes in which the SR system with secrecy is beneficial for the overlaid network secrecy.
1. Introduction
Wireless sensor networks (WSNs) are now widely used in many contexts of military and civilian applications [1], such as battlefield surveillance, environment monitoring, target detection, and tracking, especially in unattended and possibly hostile areas. All of these applications have resulted in a shortage of spectrum bands with respect to a tremendous demand for radio spectrums. Fortunately, the cognitive radio (CR) technology emerges, which is revealed to be a promising solution to this problem [2]. In cognitive radio networks (CRNs), secondary (SR) users could share the spectrum with primary (PR) users as long as the quality of service (QoS) of the PR network was not disturbed [3].
As a smart integration of WSNs and CRNs, cognitive radio sensor networks (CRSNs) have received a great deal of interest for the characteristic of large-scale and overlaid deployments [4]. In general, a wireless cognitive sensor network consists of sensor nodes equipped with cognitive radio. The transmission performance could be improved by sharing spectrum between primary sensor nodes and secondary sensor nodes, while ensuring that SR nodes can avoid interference with PR users. However, spectrum sharing leads to the security problem of data transmissions since broadcasting messages sent to intended receivers often face the risk of interception by some malicious eavesdroppers. Thus, the secrecy transmission in CRSNs becomes a critical issue.
Traditionally, the security of data transmission has been performed via cryptographic techniques [5] at the network layer. However, complicated encryption algorithms cannot be supported by wireless sensor nodes with limited computing power and storage space. As a powerful complement, the physical layer security has been proposed to achieve perfect secrecy without requiring key distribution and complex encryption/decryption algorithms. The fundamental principle of physical layer security is to exploit intrinsic properties of communication channels to restrict the amount of confidential messages that is possibly intercepted by unauthorized receivers.
In the past few years, physical layer security or information-theoretic security has become a very active area of research. In the seminal work on physical layer security [6], Wyner proposed the wiretap channel model for the point-to-point communication, where Alice transmitted confidential message to Bob and Eve tried to wiretap the message. Subsequently, various wiretap models have been proposed to evaluate the secrecy capacity for different applying scenarios. Csiszar and Korner and Liang et al. generalized it to broadcast channels and fading channels, respectively, in [7] and [8]. The secure MIMO channel was studied in [9, 10]. The secrecy capacity region of interference channel was presented in [11]. Motivated by emerging wireless applications, there is a growing interest in exploiting the benefits of relay channel to guarantee secure transmissions [12]. However, the majority of these works ignored the spatial distributions of network nodes but only focused on the configurations with a limited number of legitimate users and eavesdroppers.
With respect to the node spatial distribution, stochastic geometry techniques have been a powerful tool to analyze large-scale wireless networks [13]. Further, the Poisson point process (PPP) modeling [14, 15] has been shown to yield tractable results for secrecy performance of wireless networks. The secrecy graph was introduced to investigate the secure connectivity [16]. The work [17] established the secrecy outage probability with and without colluding eavesdroppers in cellular networks. Zhou et al. [18] proposed the concept of secrecy transmission capacity of a single wireless network, and they exploited secrecy guard zone to improve the network throughput. Zhang et al. [19] presented asymptotic analysis of secrecy capacity in large-scale networks and obtained order sense results for the secrecy capacity. Recently, Win et al. [20] show that cognitive interference was beneficial for the security of cognitive networks, while proposing corresponding interference engineering strategies. However, to the best of our knowledge, the exact expression of secrecy capacity has not been obtained for overlaid networks like CRSNs.
The primary goal of this work is to derive the exactly closed-form expression of the secrecy transmission capacity in CRSNs. Related works are [18, 21–25]. Shu et al. [21] characterized the secrecy capacity of PR networks considering a cognitive radio network but only focused on the effect of small-scale fading on the secrecy performance ignoring that of large-scale fading. In [22], the capacity and delay scaling laws were investigated for cognitive radio networks, which only gave an asymptotic prediction on the capacity without an exact expression. Elkashlan et al. [23] studied multiple antennas securing the transmission of the secondary network and presented new closed-form expressions for asymptotic secrecy outage probability. Chae et al. [24] investigated the optimal utilization of artificial noise for secrecy communication with a secrecy protected zone and derived the secrecy transmission rate without CSI of eavesdroppers. Liu et al. proposed four relay and jammer selection policies and derived new closed-form expressions for secrecy outage probability of cognitive DF relay networks [25]. Although Zhou et al. [18] introduced secrecy transmission capacity which quantified the achievable rate of successful transmission of secret message per unit area, this result was only limited in a single network and the distance between transmitter and receiver was simply defined as a fixed value.
The main contributions of this paper can be summarized as follows. This paper develops a framework for the analysis and design of CRSNs with secrecy in respect of the random channel characteristics, the nearest neighbour routing protocol, the spatial distributions of PR, SR and eavesdropping nodes, and the aggregate interference from intersystem and intrasystem. A novel method is proposed to derive closed-form expressions of secrecy transmission capacity of CRSNs under constraints of the connection outage provability (COP) and the secrecy outage probability (SOP), and the maximum achievable secrecy transmission capacity is obtained by optimizing transmission density. The result reveals an insight into the tradeoff between the security of SR system and reliability of PR system. The concept of secrecy cognitive gain is first introduced to evaluate the advantageous effect of SR system with secrecy on the secrecy capacity of the whole CRSNs. Compared with a single PR system, the SR system is beneficial to enhance the secrecy level for overlaid CRSNs. In summary, we quantify secrecy cognitive gain and characterize relationship between the secrecy performance and various system parameters.
The rest of this paper is organized as follows. System model and problem formulation are described in Section 2. Outage performance of CRSNs is analyzed in Section 3. The secrecy transmission capacity and secrecy cognitive gain are derived in Section 4. Some numerical results are presented in Section 5. Finally, conclusions are given in Section 6. The notations used in this paper are summarized as follows.
Notations and Description (“of System
k” Is Abbreviated,
P: transmission power,
2. System Model and Problem Formulation
Cognitive radio sensor networks in the presence of eavesdroppers, composed of a number of sensor nodes with cognitive radio function, are divided into PR systems, SR systems, and eavesdropping systems. Network model is depicted in Figure 1 with descriptions as follows. A PR system consists of legitimate sensor nodes with priority of spectrum access for secure communication. A SR system consists of legitimate sensor nodes which are allowed to utilize spectrum resources for secure communication guaranteeing the QoS requirement of PR system. An eavesdropping system consists of malicious nodes which attempt to bug the confidential data sent to intended receivers in the PR and SR system.
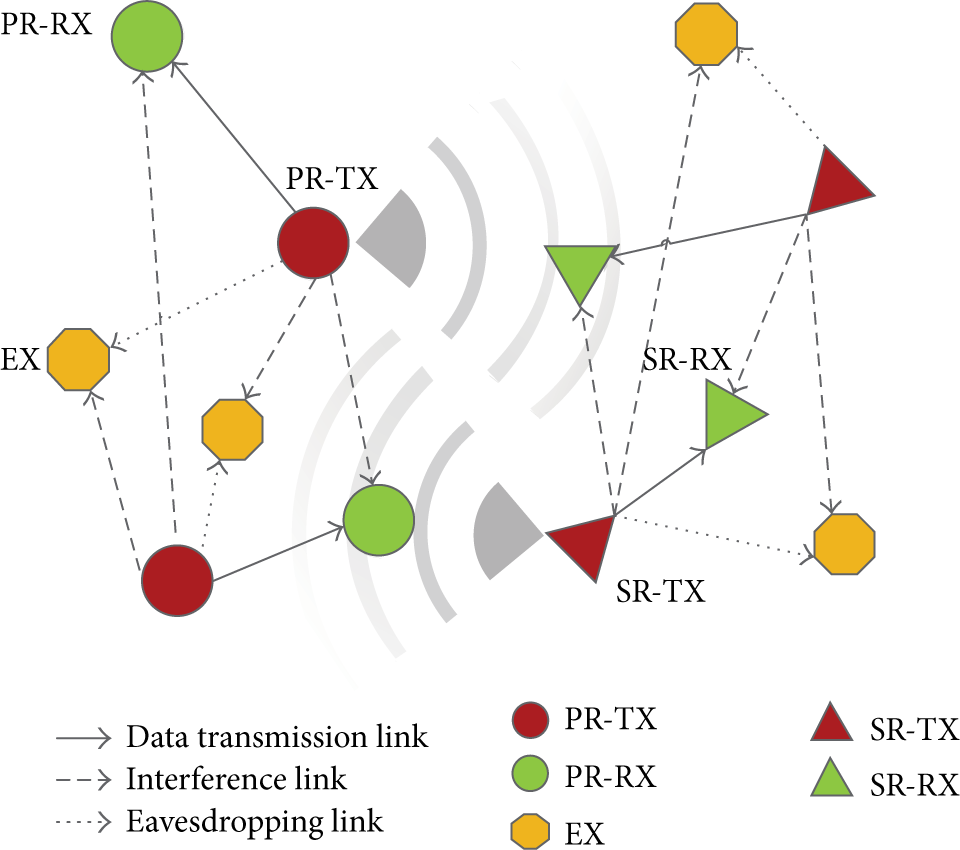
Network model with primary transmitters (PR-TX), primary receivers (PR-RX), secondary transmitters (SR-TX), secondary receiver (SR-RX), and eavesdroppers (EX). Solid, broken, and dashed lines are data transmission links, interference links, and eavesdropping links, respectively. Gray shadows represent mutual interference between PR networks and SR networks.
In CRSNs, a legitimate transmitter (Alice) wants to send a confidential message to a legitimate receiver (Bob), and multiple passive eavesdroppers (Eves) overhear the secret message. Because Alice does not know the channel state information (CSI) before transmission, she sets a constant secrecy transmission rate
Spectrum sharing networks are denoted as sets
It is assumed that Eves are not colluded with each other and follow another independent PPP distribution
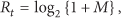
It is noted that the nearest neighbour routing protocol is considered in SR systems, each SR transmitter selects the nearest node as its intended receiver, and then the communication distance Connection outage Secrecy outage
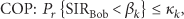
Accounting for the QoS requirement of legitimate link, the data transmission is interrupted when the instantaneous SIR is below the SIR threshold value
Furthermore, it is assumed that
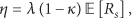
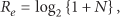
As an overlaid wireless network, the CRSN is considerably complicated due to variety of interference. Exploiting the transmission framework [26], a random analysis method is proposed to analyze the secrecy transmission capacity of CRSNs. In this section, the secrecy transmission capacity is defined as the achievable secrecy rate of successful transmission of secret messages under outage constraints, which is expressed as
3. Outage Performance Analysis
It is essential to evaluate COP and SOP of CRSNs to perform the security capacity analysis. Therefore, connection outage probabilities of the PR and SR system are derived in this section, and then secrecy outage probabilities are achieved for CRSNs. Details of outage performance analysis are given in the following lemmas.
3.1. Connection Outage Probability
Lemma 1.
The COPs of the PR and CR system are given by
Proof.
According to Slivnyak's theory [27], the SIR (2) at the typical receiver of system k can be rewritten as follows:
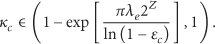
From a cognitive point of review, since the PR system has higher priority to access the spectrum, the SR system will control its density to guarantee the QoS of the primary system. In other words, the density of SR systems
Note that the outage probability
3.2. Secrecy Outage Probability
Lemma 2.
The SOP of legitimate nodes in CRSNs is given by
Proof.
All eavesdropping nodes in the CRSN are randomly and independently distributed, and the SOP can be evaluated by inspecting a typical wiretap link. Using the similar analysis adopted in Lemma 1, the eavesdropping probability of arbitrary wiretap link is found as
Integrating (5) with (16), it is easy to obtain that the SR density
4. Secrecy Transmission Capacity and Secrecy Cognitive Gain
In this section, the secrecy transmission rate is first analyzed for both PR and SR systems in the presence of eavesdroppers, and then the closed-form secrecy transmission capacity of CRSNs is derived. It has been focused on the evaluation of secrecy transmission capacity of SR systems, in which the nearest neighbour routing protocol is adopted. For the convenient analysis of secrecy cognitive gain, secrecy transmission capacity of PR systems at a given transmission distance is also evaluated. Finally, the secrecy cognitive gain is proposed to evaluate the beneficial effect of SR system with secrecy on the CRSN.
Theorem 3.
The secrecy transmission rate of network k in CRSNs is given by
Proof.
Exploiting (4) and (6), it can be observed that the transmission rate
4.1. Secrecy Transmission Capacity of PR Systems
In this section, the secrecy transmission capacity is derived for PR systems. Subsequently, one existing condition is presented to ensure a positive secrecy transmission capacity. As this paper mainly focuses on the impact of the SR system with secrecy on the security performance of whole CRSNs, to simplify analysis, the distance for PR transmission link is set as a fixed value; that is,
Theorem 4.
The secrecy transmission capacity of the PR system in CRSNs is given by
Proof.
Taking the distance between the primary transmitter and intended receiver as
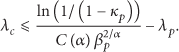
In PR systems, the successful transmission of confidential data for an intended receiver is limited by two constraints, PR-COP and PR-SOP. The limitations on density of PR systems can be deduced from outage constraints of (4) and (5), respectively. Combining (4) with (10), the density of PR systems
Corollary 5.
The condition of positive secrecy transmission capacity for PR systems is given by
Proof.
It is easy to obtain the condition under which positive secrecy transmission capacity exists by solving
4.2. Secrecy Transmission Capacity of SR Systems
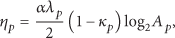
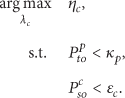
The secrecy transmission capacity of SR systems is derived on the base of the result of the secrecy rate, and the effect of the PR-COP and the SR-SOP on the secrecy transmission capacity is illustrated in this section. Note that the nearest neighbour routing protocol is considered in SR networks. Furthermore, the SR density
Theorem 6.
The secrecy transmission capacity for the SR system in CRSNs is given by
Proof.
Plugging (3) and (20) into (9), the achievable secrecy rate of SR system in CRSNs is derived as
It is shown that the secrecy transmission capacity is primarily determined by the SR transmission density
Corollary 7.
The condition of positive secrecy transmission capacity of SR systems is given by
Proof.
This result is obtained by solving
The above condition gives a tradeoff between the QoS and the security level for a given
From (28), the secrecy transmission capacity of the SR system mainly depends on the SR density. Now, the problem of finding the optimal secondary density
Corollary 8.
The optimal value of
Proof.
The objective function
Remark 9.
Using the optimal spatial density of SR systems, the maximum achievable secrecy transmission capacity of the SR systems is defined as
Corollary 10.
The achievable density of
Proof.
From (30) and (34), we can easily see that
Remark 11.
Now, we provide a new perspective on the constraint of security level based on the density of eavesdroppers. Obviously, the secrecy transmission will be disrupted if
4.3. Secrecy Cognitive Gain
In this section, the concept of secrecy cognitive gain is proposed to quantify the improvement of security level generated from SR systems. And it is defined as the secrecy capacity ratio between the sum of capacities for CRSNs with secrecy and the secrecy capacity of a single PR system, which is given by
Based on the analysis of secrecy transmission capacity in above sections, the sum of capacities for CRSNs is denoted as the sum of secrecy capacity between PR systems and SR systems, which is given as
Theorem 12.
The secrecy cognitive gain of CRSNs is given by
Proof.
Taking into account a single PR system in the absence of the SR system, the secrecy capacity
Substituting (23) and (28) into (38), we achieve the following expressions:
From Theorem 12, it can be reflected that the presence of SR system is beneficial for the improvement of secrecy capacity of CRSNs compared with the secrecy capacity of a single PR system.
In practice network design, these system parameters including the COP, the SOP, and spatial transmission density could be under the control of the system designer. The derived closed-form expressions of secrecy transmission capacity and secrecy cognitive gain are helpful for design and optimization for CRSNs respecting security.
5. Numerical Results and Analysis
In this section, numerical results are presented to characterize the secrecy transmission performance, such as the secrecy transmission capacity, the secrecy outage probability, and the secrecy cognitive gain. The path loss exponent α is set as 4 and the transmission power is set as 1.
Figure 2 quantifies the secrecy transmission capacity of SR systems versus the SR density

Secrecy transmission capacity
Figure 3 presents the secrecy transmission capacity of SR systems versus the SR-COP

Secrecy transmission capacity
Figure 4 compares secrecy connection probability (SNP) versus the achievable eavesdropping density

Secrecy connection probability
Figure 5 characterizes secrecy cognitive gain θ versus the PR density
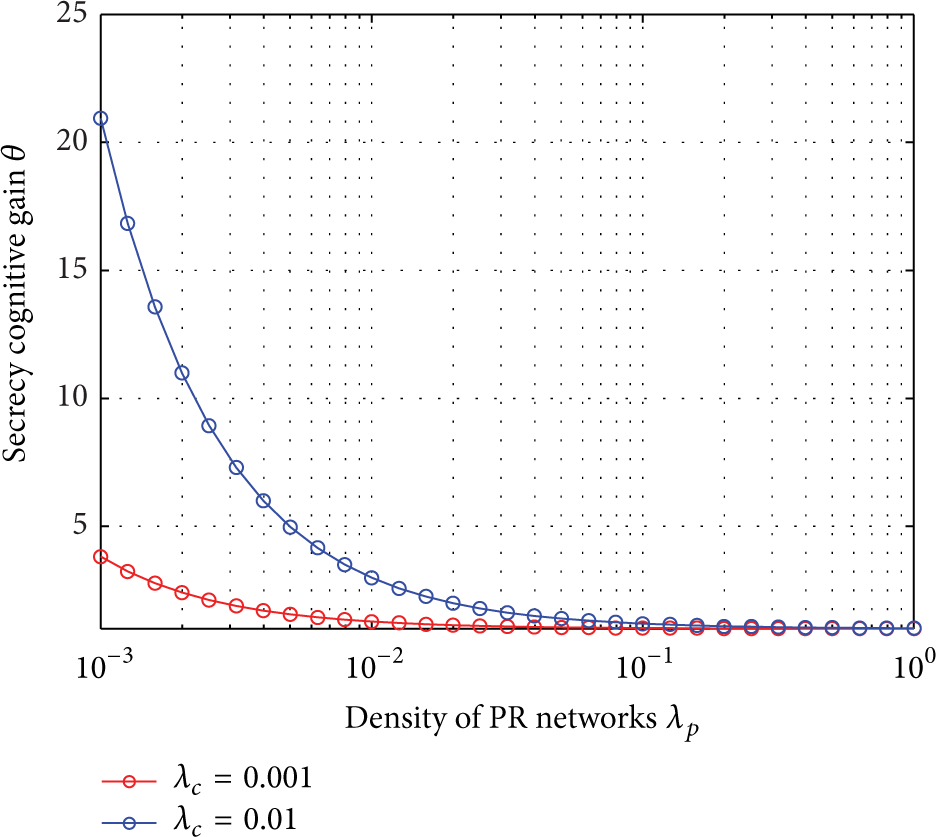
Secrecy cognitive gain θ versus density of PR networks
6. Conclusions
This paper investigates the physical layer security problem in cognitive radio scenario with wireless sensors. A novel random analysis method is presented to derive secrecy performance metrics, such as the connection outage provability (COP), the secrecy outage probability (SOP), the secrecy transmission capacity, and the secrecy cognitive gain. Specifically, the optimal density of SR systems, maximizing the secrecy transmission capacity via stochastic geometry analysis, is achieved whilst guaranteeing constraints of the PR-COP and SR-SOP. In addition, the nearest neighbour routing protocol is considered in SR systems. Comparing with a single PR system, the SR system with secrecy is beneficial to enhance the secrecy level of whole CRSNs. Numerical results show that there exists a tradeoff between the reliability of PR systems and the security of SR systems. Future work could extend to a more general scenario where receivers are equipped with multiple antennas and eavesdroppers are colluding, which is expected to provide more accurate performance assessment for physical layer security.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work is supported by National Natural Science Foundation of China (61171099), National High Technology Research and Development Program of China (863 Program) (2015AA011303), and Huawei Technologies Co. Ltd. Project (YB2013120018).