Abstract
With the rapid growth of the distributed sensor networks, the distributed sensor network data security problems begin to attract the attention of people. The previous research of distributed sensor network security has focused on secure information in communication; however the research of secure data storage has been overlooked. As we know, cloud data storage and retrieval have become popular for efficient data management in distributed sensor networks; thus they can enjoy the on-demand high-quality cloud storage service. Meanwhile, it also introduces new security challenges. To tackle with these security challenges, many classic auditing schemes of cloud storage have been proposed. However, these schemes all need very expensive pairing computation, which is not suitable for sensor networks. In this paper, we propose an efficient pairing-free auditing scheme for data storage of distributed sensor networks. We exploit homomorphic message authentication codes (MACs) to reduce the space used to store the verification information. We also employ the random masking technique to make sure the TPA cannot recover the primitive data blocks of the sensor networks data manager. Experimental results show that our auditing scheme is more light-weight than previous auditing schemes and more practical in applied distributed sensor networks environments.
1. Introduction
Nowadays, distributed sensor networks have been rapidly applied in many practical environments in our social life [1, 2]. With distributed sensor networks being applied widely, the sensor network data managers often need to collect massive data and choose to be stored in the cloud server, while the security and privacy of sensor networks storage data become increasingly important [3, 4]. As we know, cloud computing is an alternative to conventional computing model since it can provide a flexible, resilient, and cost-effective infrastructure [5]. So it is suitable option to store the massive sensor network data on cloud server [6]. While cloud storage is an important service of cloud computing, which allows cloud users to move data from their local computing systems to the cloud, by data outsourcing, the cloud users can be relieved from the burden of local data storage and maintenance. Thus the cloud servers can concentrate on their core business issues and operate other business applications through the Internet, rather than incurring substantial hardware, software, and personnel costs involved in deploying and maintaining applications in-house.
Although the cloud storage service makes these advantages more appealing than ever before, it also introduces new security challenges towards user's outsourced data [7–9]. Firstly, the cloud users would worry their data could be misused or accessed by unauthorized users. Many researches have been done on this security issue of data hosting [10–12]. Secondly, the cloud users would worry their data could be lost in the cloud. This is because data loss could happen in any infrastructure, no matter what high degree of reliable measures the cloud service providers would take [13, 14]. Sometimes, the cloud service providers may be dishonest and they may discard the data which have not been accessed or rarely accessed to save the storage space or keep fewer replicas than promised. Moreover, the cloud service providers may choose to hide data loss and claim that the data are still correctly stored in the cloud. Consequently, the cloud users need to be convinced that their data are correctly stored in the cloud.
As the cloud users no longer physically possess the storage of their data, traditional cryptographic primitives for the purpose of data security protection can not be directly adopted. Thus how to efficiently verify the integrity of outsourced cloud data without the local copy of data files becomes a big challenge for data storage security in cloud computing. Checking on retrieval is a common method for checking the data integrity, which means cloud users check the data integrity when accessing their data. This method has been used in peer-to-peer storage systems [15], network file systems [16, 17], web-service object stores [18], and database systems [19]. However, checking on retrieval is not sufficient to check the integrity for all the data stored in the cloud. There is usually a large amount of data stored in the cloud; the ability to audit the correctness of the data in a cloud environment can be formidable and expensive for the cloud users [20, 21]. Therefore, in order to save the communication resources as well as the online burden potentially brought by the periodic storage correctness verification, cloud users can delegate a third party (TPA) to perform security auditing tasks as it is not economically feasible for them to handle it by themselves. Meanwhile, the cloud users also hope to keep their data private from the TPA and the cloud server.
1.1. Related Work
Until now, a number of auditing schemes have been proposed in the context of ensuring remotely stored data integrity without the knowledge of the entire data with different requirements [20, 22–24]. However, these schemes need the expensive pairing computation; it is a burden for the sensor network. And most of these schemes [20, 22, 24] do not consider the privacy protection of user's data. Indeed, the user's data may be revealed to some curious adversaries. This shortcoming will greatly affect the security of these schemes in cloud computing. In the view of protecting the data privacy, the users can rely on the TPA for the storage security of their data, and they also do not want this auditing process to introduce new vulnerabilities of unauthorized information leakage toward their data security [25]. The unauthorized data leakage still remains possible due to the potential exposure of decryption keys. In 2013, Wang et al.'s [26] has presented a privacy-preserving public auditing scheme for cloud storage; it resorts to the homomorphic authenticator technique and random masking technique to achieve privacy-preserving public auditing and utilizes the technique of bilinear aggregate signature to realize batch auditing. However it also acquires very expensive pairing computation, which is time-consuming. Therefore, how to design an efficient privacy-preserving auditing scheme for cloud storage in distributed sensor networks, especially without needing the expensive pairing computation, is the important work we are going to do in this paper.
1.2. Our Contribution
Motivated by the above, in this paper, we propose an efficient pairing-free privacy-preserving auditing scheme for cloud storage in distributed sensor networks. In particular, we utilize the modified Schnorr signature to construct homomorphic authenticator so that the TPA can verify the integrity of the data without retrieving the entire data. Additionally, we exploit homomorphic MACs [27] to reduce the space used to store the verification information. As a necessary tradeoff, we allow the TPA to share a private key pair with the DSN data manager, which we refer to as authorized auditing. Due to the function of the random masking, even if the authorized TPA possesses the private key pair, the TPA cannot recover the primitive data blocks of the DSN data manager. As the individual auditing of these growing auditing tasks can be tedious, we extend our basic scheme to support batch auditing for multiuser, which can thus enable the TPA to efficiently perform multiple auditing tasks in a batch manner simultaneously. Furthermore, compared with the previous classic auditing scheme [26], our experimental results show that our auditing scheme is more light-weight, and this is mainly because our auditing scheme does not need the expensive pairing operations, which can satisfy the requirement of the sensor network.
1.3. Organization
The rest of this paper is organized as follows. We introduce the preliminaries of our work in Section 2. We give the formal pairing-free privacy-preserving auditing scheme for cloud storage with distributed sensor networks in Section 3. We give the analysis of the proposed auditing scheme in Section 4. We make a performance comparison in Section 5. We make a conclusion in Section 6.
2. Preliminaries
2.1. The Cloud Data Storage Model in Sensor Network
We exemplify the security needs in data storage with a distributed sensor networks application scenario. Here, for simplicity, after collecting the data by the sink node, we assume that we assume that a DSN (distributed sensor network) data storage manager processes and transfers sensor networks data to the cloud sever. Since DSN data storage manager does not own additional computing resources, it only takes advantage of the limited computing capacity of the sink node to finish the secure DSN data storage. For the part of DSN, it can be considered as a data storage manager, while, for the part of the CSP (cloud service provider), it can be considered as a special cloud user. In our distributed sensor networks application scenario, we suppose Pob is a DSN data owner; his business is that to collect sensor network data which are processed to supply various service to clients. Since he does not have enough money to buy devices and hire professionals, he wishes to turn to CSP and outsource his data to CSP. However, he will worry about the following questions: (1) he cannot physically control the data, and CSP may repudiate that the data are lost, which makes him verify the integrity of data at any time; (2) CSP is honest and curious, Pob wants to guarantee his data confidentiality, and he must assure his storage mode has the function of privacy-preserving; (3) Pob's main work is responsible for sensor network, and he needs an efficient audit scheme to complete this task.
As illustrated in Figure 1, sensor nodes collect data from the target setting and send them to sink node; Pob is a distributed sensor networks data owner; he can assign a DSN data storage manager to sign and encrypt data, then outsource data and tags to CSP, and delete local data simultaneously. If the DSN data storage manager wants to verify data integrity stored in the cloud server, he makes a request for TPA; TPA verifies tags after it receives the requests. If it is true, it generates a challenge message. After receiving the challenge message request, CSP supplies the response proof to TPA; TPA verifies the response proof message and returns the verified result to the DSN data storage manager. Finally, the DSN data storage manager submits the auditing result to Pob.

DSN data storage in the CSP.
The sensor network (DSN) data manager can rely on the cloud server for cloud data storage and maintenance. They may also dynamically interact with the cloud server to access and update their stored data for various application purposes. The DSN data manager may resort to the TPA for ensuring the storage security of their outsourced data, while hoping to keep their data private from the TPA. We consider that a semitrusted cloud server exists. Namely, in most of time it behaves properly and does not deviate from the prescribed protocol execution. However, during providing the cloud data storage based services, for the benefits the cloud server might neglect to keep or deliberately delete rarely accessed data files which belong to the DSN data manager. Moreover, the cloud server may decide to hide the data corruptions caused by server hacks or failures to maintain reputation. We assume that the TPA, who is in the business of auditing, is reliable and independent and thus has no incentive to collude with either the cloud server or the DSN data manager during the auditing process. The TPA should be able to efficiently audit the cloud data storage without local copy of data and without bringing in additional online burden to the DSN data manager. However, any possible leakage of DSN manager's outsourced data towards the TPA through the auditing protocol should be prohibited.
2.2. Design Goals
To enable privacy-preserving auditing for cloud data storage under the aforementioned model, our auditing scheme should achieve the following security and performance guarantee:
public auditability: to allow the TPA to verify the correctness of the cloud data on demand without retrieving a copy of the whole data or introducing additional online burden to the DSN data manager, storage correctness: to ensure that there is not a cheating cloud server that can pass the auditing from the TPA without indeed storing DSN data manager data intact, privacy-preserving: to ensure that there exists no way for the TPA to derive DSN data managers’ data content from the information collected during the auditing process, batch auditing: to enable the TPA with secure and efficient auditing capability to cope with multiple auditing delegations from possibly large number of different DSN data managers simultaneously, lightweight: to allow the TPA to perform auditing with minimum communication and computation overhead.
2.3. Cryptographic Definition
Definition 1.
Discrete Logarithm problem states that, given a multiplicative cyclic group of order of p and
The Discrete Logarithm assumption holds in G if no polynomial time algorithm has a nonnegligible probability in solving the Discrete Logarithm problem, which means it is computationally infeasible to solve the Discrete Logarithm problem in G.
Now we introduce homomorphic MAC, described in [27].
Definition 2 (Homomorphic MAC).
Given a data block
We know that, given
3. Pairing-Free Privacy-Preserving Auditing Scheme for Cloud Storage in Distributed Sensor Networks
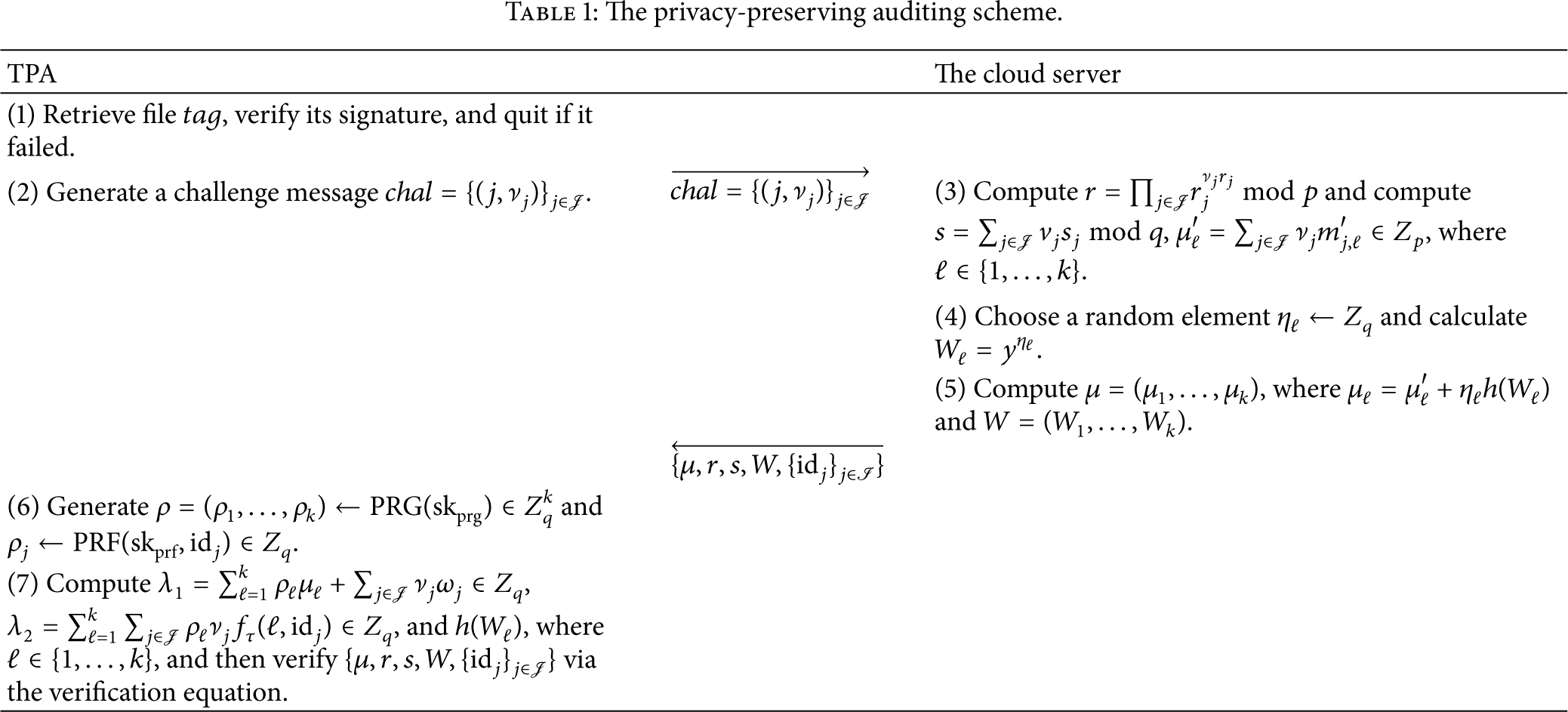
In this section, we propose our privacy-preserving authorized auditing scheme for cloud storage in distributed sensor networks, and our scheme does not need pairing computation and thus can reduce much computation cost. The privacy-preserving auditing scheme is illustrated in Table 1. Here, we need to define a semitrusted TPA, who is only responsible for auditing the integrity of data blocks honestly; however, it is curious and may try to reveal the DSN managers’ primitive data blocks based on verification information. Our scheme consists of the following four algorithms. They are Setup, SigGen, ProofGen, and ProofVerify, respectively.
The privacy-preserving auditing scheme.
Setup. The initial system chooses two large prime numbers p and q, satisfying that q is a prime factor of
SigGen. Given a data block choose output
Denote the set of signatures by
ProofGen. In this phase, for each data block
Now it comes to the important part of the auditing process. To audit the integrity of data file, a DSN data manager first sends an auditing request to the TPA. After receiving an auditing request, the TPA generates an auditing challenge message as follows.
Randomly choose a c-element subset For each Output an auditing challenge message
After receiving an auditing challenge message Compute Compute Compute
To blind
ProofVerify. Given an auditing response proof Generate Compute Verify the response proof by checking whether the verification equation
If the verification equation
4. Analysis of the Proposed Auditing Scheme
In this section, we begin to analyze the proposed auditing scheme, including its correctness, unforgeability, and privacy-preserving. Considering the scalability of the auditing scheme, we also extend it to support batch auditing.
4.1. Correctness
According to the ProofVerify phase of the auditing scheme, the correctness of the verification equation is elaborated as follows:
Thus the verification equation
4.2. Unforgeability
Theorem 3.
With the from DSN data manager's data file
In the proposed auditing scheme, we make use of homomorphic MACs to compress each data block to efficiently decrease the amount of storage space needed to store verification information. According to the discussions and proofs in [27], we know that the probability for an adversary to break one homomorphic MAC on a data block is
Besides generating a forgery of a homomorphic MAC, if the malicious cloud server can win Game 1, it can generate an invalid auditing response proof for the challenged data blocks and enable this invalid auditing response proof to successfully pass the verification. Now we describe Game 1 as follows.
Game 1. After receiving an auditing message from the DSN data manager, the TPA sends an auditing challenge message
Now we begin to show that if the malicious cloud can win the above Game 1, we can find a solution to the Discrete Logarithm problem. We first assume that the malicious cloud wins Game 1. Then, according to the verification equation, we have 
Because G is a multiplicative cyclic group of order q, for two random elements 
Obviously, we can find a solution to the Discrete Logarithm problem. Particularly, given α,
Moreover, if the malicious cloud server tries to forge the aggregate signature, that means the cloud server generates an invalid response proof as
Therefore, it is computationally infeasible for the malicious cloud to generate an invalid auditing proof, which can pass the verification equation.
4.3. Privacy-Preserving
Theorem 4.
Given an auditing response proof message
Proof.
If the combined message
4.4. Support for Batch Auditing
With the usage of privacy-preserving auditing scheme in the cloud storage, the TPA may receive amount of multiple auditing requests from different DSN data managers in a short time. Unfortunately, allowing the TPA to execute the separate auditing task can be tedious and very inefficient. Therefore, we further extend our scheme to support batch auditing. Batch auditing not only allows the TPA to execute the multiple auditing tasks simultaneously, but also dramatically decreases the computation cost on the TPA side. This is because aggregating L verification equations into one helps save a considerable amount of auditing time. The details are described as follows.
Setup Phase. The DSN data managers just perform setup independently. Suppose there are L DSN data managers in the auditing system, and each DSN data manager θ has a data file
Then each DSN data manager θ computes Choose output
Denote the set of signatures by
Audit Phase. The TPA first retrieves and verifies the data block
To verify the response, the TPA first does as follows.
Generate Compute
Then the TPA checks if the following verification equation holds: 
Thus the verification equation
5. Performance Comparison
In this section, we begin to compare the performance of our privacy-preserving auditing scheme for cloud storage with the auditing scheme in [26]. We first focus on discussing the computation cost and the communication cost. Then we evaluate the performance comparison between the two schemes in experiments to show our auditing scheme advantages.
5.1. Computation Cost
We first give the computation cost of our pairing-free auditing scheme for cloud storage with the auditing scheme in [26]. The main cryptographic operations used in our scheme include multiplications, additions, and hash operations. For simplicity, we omit the computation cost of the pseudorandom number generator
During the auditing process, the TPA first generates some random values to construct the auditing message, which only introduces a small cost in computation. Then, after receiving the auditing message, the cloud server needs to compute a proof
To check the correctness of the proof, the TPA verifies it based on verification equation and the computation cost of verifying the auditing proof is
5.2. Communication Cost
The communication cost of our scheme is mainly introduced by two factors: the auditing message and the auditing proof. For the auditing message
5.3. Experimental Results
We now compare the cloud server computation cost and the TPA auditing computational cost of our auditing scheme with the work of [26] in experiments. Since the random mask needs one exponentiation operation, one multiplication operation, one hash and one addition operation, so the sum of the extra cost that resulted from the random mask only needs a constant,
As also discussed in [26], the extra cost resulting from the random masking is only a constant:
Our experiments are implemented on a Windows 7 system with an Intel Core 2 i5 CPU running at 2.53 GHz, 2 GB DDR 3 of RAM (1.74 GB available). All algorithms are implemented by C language, and our code uses the MIRACL library version 5.6.1. The elliptic curve we use is a MNT curve, the base field size is 159 bits, and the embedding degree is 6. The security level is chosen to be 80 bit, and
As described in Figures 2 and 3, the experimental results show that, compared with the auditing scheme in [26], the computation cost of the cloud server and the TPA auditing time of our auditing scheme are much more light-weight than [26]. More specifically, with the increasing of the number of challenge data blocks, our auditing scheme is more advantageous than [26] in computation cost. This is mainly because the auditing scheme in [26] needs very expensive pairing computation which is much more time-consuming.

Comparison on the computation cost of cloud server.

Comparison on the auditing time between our scheme and the scheme in [26].
6. Conclusions
Data outsourcing, one of the fundamental components of cloud computing, centralizes DSN data manager's data to the cloud server and enables the DSN data managers to enjoy high quality service. However, the DSN data managers do not have physical possession on their own data; hence it is indispensable to create schemes on how to protect the security of the data, unlike the previous auditing schemes [26] which need expensive pairing operations. In this paper, we propose a pairing-free privacy-preserving auditing scheme for data storage security in distributed sensor networks. We employ the homomorphic linear authenticator and random masking to guarantee that the TPA would not only eliminate the burden of the DSN data managers from the tedious and possible expensive auditing task, but also alleviate the DSN data managers’ fear of their outsourced data leakage. We also utilize homomorphic MACs to effectively reduce the amount of storage space needed to store verification information. Moreover, we further extend our auditing scheme to support batch auditing for multiple DSN data managers, where the TPA can perform multiple auditing tasks simultaneously. Extensive security and performance compared analysis shows that the proposed auditing scheme is more light-weight and more practical in distributed sensor networks environments.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work is supported by the National Natural Science Foundation of China (no. 61370203) and the Science and Technology on Communication Security Laboratory Foundation (Grant no. 9140C110301110C1103).
