Abstract
Noise is a powerful resource for the implementation of cryptographic primitives, especially in wireless networks. In general, a key agreement protocol is tailored to the channels and relies on the assumption that knowledge on the eavesdropper's channel is available. This is not practical. In this paper, we focus on the problem of developing key agreement schemes for secure communication across wireless channels and propose a key evolution scheme to alleviate the assumption. Keys evolve continuously based on the transmitted messages over the noisy wireless channel. Even if the eavesdropper's channel is superior to the legitimate receiver, the legitimate parties can establish secret keys. To further confuse the eavesdropper, we present a strategy for legitimate parties to send artificial noise if the eavesdropper cannot distinguish the sources of messages. Finally, we propose a k-resistant encryption scheme that can use different keys to encrypt and decrypt messages if there are no more than k bits which differ between the encryption and decryption keys.
1. Introduction
Traditionally, security in wireless channels is regarded as an independent feature addressed above the physical layer, and all widely used cryptographic protocols are designed and implemented assuming the physical layer has already been established. An alternative notion of communication security, information theoretic security, was introduced by Wyner [1] and later by Csiszar and Korner [2]. The basic principle of information theoretic security calls for the combination of cryptographic scheme with channel coding techniques that exploit the randomness of communication channels to guarantee that the messages sent cannot be decoded by a third party maliciously eavesdropping on the wireless channel. In a wiretap channel, the honest parties Alice and Bob are separated by a channel called the main channel; any eavesdropper Eve observes information transmitted by Alice through another channel called the wiretapper's channel. Suppose Alice and Bob try to communicate a k-bit message M across the main channel; Alice encodes M into an n-bit codeword X. The legitimate receiver Bob and an eavesdropper Eve receive X through two different channels and their observations are denoted as Y and Z, respectively. Alice's encoding should achieve two objectives: (1) security: Z should provide no information about M; (2) reliability: Y can be decoded into M with negligibly small probability of error. Wyner showed that both objectives can be attained if the channels satisfy some conditions. The advent of wireless communication, which is particularly susceptible to eavesdropping, has motivated a renewed interest for information theoretic security, which has recently emerged as a very active research area, such as in [3–13].
The key distribution problem in wiretap channels has been studied in [14, 15]. The objective of key distribution is for Alice and Bob to agree on a common k-bit key about which Eve's entropy is maximal. Most key agreement protocols require some level of interactive communications between Alice and Bob to arrive at a common yet secret key [14], where the exchange of information is by way of a parallel, error-free public channel between Alice and Bob used during the key agreement phase [16].
In general, the lower bound of the eavesdropper's equivocation about the key generated by a key agreement protocol is valid only if the protocol is tailored to the channels, which requires knowledge of the channel statistics. The assumption that the main channel is known is usually reasonable; however, it is hardly realistic to assume that the eavesdropper's channel statistics are known exactly. In this paper, we propose a key evolution scheme which can alleviate the stringent requirement. The basic idea of key evolution is that keys evolve continuously based on the transmitted messages over the noisy wireless channel. If Eve cannot avoid at least a small bit error probability, her equivocation about the current key will be accumulated, and eventually she has no information about the new key. On the other hand, as the keys are continuously refreshed, the on-going cryptanalytic attacks can be thwarted. It also forces Eve to keep monitoring communications all the time after compromising a key; otherwise, she will lose control of it. We begin by discussing a special wiretap channel with a noiseless main channel and a binary symmetric channel (BSC) as the wiretapper's channel and then extend it to a more generalized wiretap channel that have BSCs as both the main and wiretapper's channel. We show that Alice and Bob can transform a wiretap channel that is advantageous to Eve into a channel in which Eve suffers more errors than Alice and Bob.
Cooperative jamming techniques, by which one or more legitimate transmitters send jamming signals to increase the confusion of Eve, can be used to increase the secrecy capacity in multiuser channels [17, 18]. If Bob can impersonate Alice to send forged messages, Alice and Bob can exploit the reciprocity of the channel to their advantage to further confuse the eavesdropper. Finally, we propose a k-resistant encryption scheme (k-RES) that can use different keys to encrypt and decrypt messages. Consider that Alice and Bob use a symmetric encryption algorithm to exchange confidential messages, but some errors occur to Bob's secret key during storage or transmission. In general, Bob cannot recover the message encrypted by Alice and they need to negotiate a new shared key. The objective of k-RES is to utilize the slightly different keys to encrypt a relatively small size message. If a pair of keys only has at most k-bit different, the receiver can recover the message; otherwise, he obtains no information about the message. In this setting, a k-RES can be viewed as a conceptual wiretap channel that has a main channel and a worse wiretap channel.
Key evolution can be used in sensor networks. The large number of sensors makes it hard to change code or data stored in every sensor; it is much easier to mass-produce sensors that are identical even on fireware and data level and are deployed in batches. To secure the communication between sensors, they can use key evolution scheme to obtain a relatively secret key and refresh it as quickly as possible.
2. Preliminaries
Throughout the sequel, a random variable X induces a probability distribution
In general wiretap channel, the main channel and the wiretap channel are discrete memoryless channels (DMCs). The main channel is denoted as
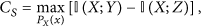
The notion of secrecy introduced by Wyner [1] has an operational meaning of being the maximum possible rate of information transmission between Alice and Bob that still enables Eve to be kept totally ignorant. The secrecy capacity
If
3. Key Evolution
3.1. Noiseless Main Channel and Binary Symmetric Wiretapper's Channel WTC
We begin with a simpler wiretap channel with a binary symmetric channel as the wiretapper's channel and a noiseless main channel, that is, WTC
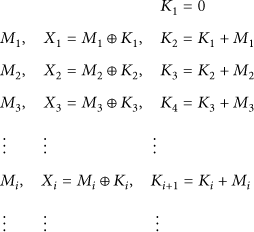
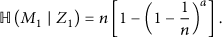
The heart of key evolution is a rekeying protocol that continuously refreshes the secret key based on transactional data. Let a message set
Remarks 1.
(1) In the key evolution protocol, Alice and Bob compute a new key
(2) As will be discussed later, under certain condition,
(3)
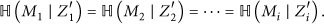
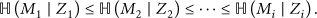
The objective of key evolution is for Alice and Bob to distill a secret key about which Eve has negligible information. Note that, if
Suppose Alice generates random bit strings
Let
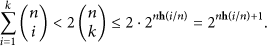
For
Therefore, the uncertainty of
In the same way, we can estimate
Let
If
Let
Because
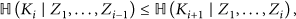
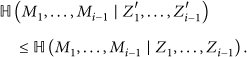
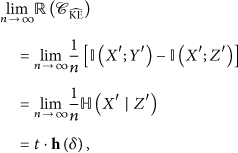
Next we want to analyze the secrecy performance of key evolution in terms of advantage distillation rate. Since hash function G can be chosen arbitrarily, it is difficult to model and analyze
In
Note that the wiretap channel in
However, in
Because
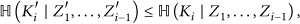
Notice that
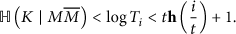
For the secret key is a function of
The protocol
In
Remark 2.
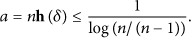
3.2. Noisy Main Channel and Wiretapper's Channel WTC
In this subsection, we consider a realistic wireless communication system where both the wiretapper's channel and the main channel are BSCs. More specifically, the wiretapper's channel is a BSC with crossover probability δ, and the main channel is another BSC with crossover probability ϵ.
As discussed in Section 3.1, if the main channel is noiseless, Bob can receive messages sent by Alice without any bit error and refresh their secret key in the same way as Alice does. If the main channel is noisy, Alice and Bob can use an appropriate error-detecting code C and a repeating transmission strategy to alleviate the transmission error. Consider now Alice sending
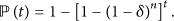
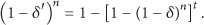
Assume the length of a message is n bits. The probability that a message is received correctly by Bob is
Eve, on the other hand, eavesdrops messages sent by Alice via the wiretapper's channel with bit error probability δ. The probability that a message is correctly eavesdropped by Eve is
The main channel from Alice to Bob may be viewed as a noiseless channel after the message is transmitted t times, since after t times of retransmission on average Bob will get the message correctly; the wiretapper's channel thus corresponds to a BSC with bit error probability
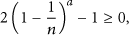
Obviously,
Examples 3.
Assume
However, for each message m, Eve can get
Therefore, if Eve has eavesdropped N different traces of message m and satisfies the condition
4. Artificial Noise to Confuse Adversaries
Cooperative jamming, or artificial noise [17, 18], by which one or more legitimate transmitters send jamming signals to increase the confusion of the adversaries, can be used effectively to increase the secrecy capacity in multiuser channels.
Along this line, if Bob can impersonate Alice to send forged messages and Eve cannot distinguish the sources of messages, Bob can cause further confusion of Eve. Eve receives a mixture of messages from Alice and forged messages from Bob. From her perspective, every message is equally likely and she cannot do better than randomly guessing the sources of each message.
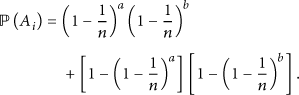
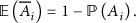
For simplicity, let
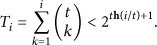
For
For some cases, Eve may not choose all subset of messages received to construct secret keys. Without loss of optimality she can choose all subset of messages whose cardinality is less than
For simplicity, let
By applying result (35), we have
In general, Bob's optimal strategy to generate noise is to inject j forged messages
5. k-Resistant Encryption
Symmetric encryption algorithm uses a secret key shared between the legitimate parties to encrypt and decrypt messages. If some bit errors occur to the secret key held by one of parties, we have to discard it and negotiate a new secret key. Unlike a symmetric encryption scheme, in which the legitimate parties are in possession of a shared secret key, a k-resistant encryption scheme (k-RES) uses different keys to encrypt and decrypt messages provided there are at most k discrepancies of n-bit between two keys.
5.1. Problem Description
Let
Formally, a k-resistant encryption scheme (k-RES) is defined as follows.
Definition 4 (k-resistant encryption scheme).
An encryption scheme is called k-resistant if the following conditions are satisfied.
Decodable Condition. Alice encrypts a plaintext message if Security Condition. Eve can only obtain a negligible amount of information about M if her key
The decodable condition guarantees that anyone with a key K satisfying
Intuitively, a k-RES can be viewed as a wiretap channel in which Alice sends secret information to Bob virtually in the main channel, and the adversary Eve receives Alice's output through an independent wiretapper channel.
To send a message X to Bob, Alice sends
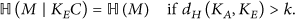
It was further shown in [21] that if
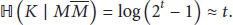
Suppose Alice and Bob try to securely communicate a m-bit message M across the main channel; Alice encodes
Notice that
The secrecy capacity of k-RES depends on parameters a and k. The less the value
5.2. Construction Methods
A trivial k-RES can be constructed by a classic error-correcting code. We can choose (n, m) error-correcting code, which maps a message
Eve, on the other hand, cannot get the message correctly, since what she can obtain is
Next we estimate the amount of information that this solution of k-RES can handle. In general, a linear (
Hence, if
This solution can be used to construct k-RES when few errors are more likely to occur. The error-correcting code may also give some side information to Eve. From a practical perspective, the design of a k-RES turns out to be a problem of the construction of codes for a wiretap channel, so we can use the method that was introduced by Wyner and Ozarow [1, 22] to construct k-RES.
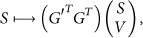
Consider a stochastic coding method consisting of a linear code and its cosets. To transmit m-bit message, we first select a (
A decoder maps a word X to a message as
Though the above correspondence is deterministic, the encoding procedure has a random component in the selection of the transmitted word. The message S can be determined without error across the main channel, and every S is equally likely across the wiretapper's channel. For an eavesdropper who can observe a set of μ bits, if all submatrices of G with μ columns have rank μ, the above coset coding guarantees perfect secrecy against the eavesdropper [22]. Guided by this result, we could choose C as a capacity-achieving code to design a k-RES.
Remarks 5.
A binary wiretap channel model in which the wiretapper is known to access no more than μ of n transmitted bits is called a wiretap channel of type II. The equivalent wiretap channel of k-RES differs from wiretap channel of type II in that the eavesdropper cannot in principle choose which μ bits are observed. In a k-RES, for
According to [22], let
Theoretically, if we use coset coding to construct a k-RES, we only need to select a generator matrix G whose submatrix
Note that Eve's observation contains a number of bits in fixed positions; her ability is restricted compared with the eavesdropper in a wiretap channel of type II. Intuitively, a code designed for this wiretap channel may achieve rates arbitrarily approximate to the secrecy capacity, but how to design such code is still unknown.
In [23, 24], Dodis et al. considered a notion of fuzzy extractor. Their construction can be rephrased to give a construction of k-RES. fuzzy extractors allow one to extract some randomness R from ω and then successfully reproduce R from any string
Construction ofk-RES from Fuzzy Extractors. On input of a message The generation procedure Gen on input To decrypt The security property of fuzzy extractor guarantees that, for any distribution
6. Conclusions
Key evolution seems realistic because current wireless communication is prevailing and the channel is noisy. Even if Eve uses a much better receiving antenna she cannot avoid at least a small bit error probability. The noise allows for the construction of information theoretically secure cryptographic protocols.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
The authors would like to thank the reviewers for their valuable comments and discussions. This work is partly supported by the Key Program of NSFC-Guangdong Union Foundation (U1135002) and National Natural Science Foundations of China (61100235, 61173135, 61100230, 61100233, 61202389, and 61202390).