Abstract
Constructive interference (CI) is a synchronous transmission technique for multiple senders transmitting the same packet simultaneously in wireless sensor networks (WSNs). CI enables fast and reliable network flooding in order to reduce the scheduling overhead of MAC protocols, to achieve accurate time synchronization, to improve link quality of lossy links, and to realize efficient data collection. By achieving microsecond level time synchronization, Glossy realizes millisecond level CI-based flooding and 99% reliability. However, Glossy produces substantial unnecessary data forwarding, which significantly reduces the network lifetime. This is a very critical problem, especially in energy-limited large-scale wireless sensor networks for agriculture and forestry (WSN-AF) system. In this paper, we present an energy adaptive CI-based flooding protocol (EACIF) by exploiting CI in WSN-AF. EACIF proposes a distributed active nodes selection algorithm (ANSA) to reduce redundant transmissions, thereby significantly reducing energy consumption and flooding latency. We estimate the performance of EACIF both with real data traces and with uniformly distributed topology. Simulation results show that EACIF achieves almost the same packet reception ratio (PRR) as Glossy (e.g., 99%), while reducing 63.96% energy consumption. EACIF also reduces 25% flooding latency. When the packet interval is 30 seconds, EACIF achieves 0.11% duty cycle.
1. Introduction
With the emergence of the Internet of Things (IoT) [1, 2], wireless sensor networks for agriculture and forestry (WSN-AF) are becoming a research hotspot. WSN-AF systems can provide real-time field data, including environment temperature, relative humidity (RH), O2 concentration, CO2 concentration [3], and ethylene (C2H4) concentration. The implementation of WSN-AF system demands forwarding data [4], synchronizing sensor nodes [5], creating data collection tree [6], locating the monitored objects [7], reprogramming the revised code [8], and so forth. All these common applications in WSNs depend on the service of network flooding which propagates a packet through the whole network.
Power consumption, latency, and reliability are three critical factors of flooding in wireless sensor networks (WSNs). Recently, constructive interference- (CI-) based flooding is emerging as a latency optimal and high reliability flooding technique. As a representative CI-based flooding protocol, Glossy [9] realizes 99th percentile packet reception ratio (PRR). Real testbed (MoteLab, Twist, and Local) experiments show that Glossy achieves millisecond level flooding latency which is almost 100 times faster than traditional flooding solutions [10, 11]. Then a question arises: is Glossy energy-efficient? Unfortunately, Glossy makes all nodes involved in the data forwarding, which directly triggers enormous number of superfluous data transmissions, eventually leading to unnecessary energy consumption and network life reduction. This is a very critical problem, especially in energy-limited large-scale WSNs. One effective solution is to reduce redundant transmissions while maintaining the advantages of CI-based flooding.
A concurrent transmission scenario of CI-based flooding can be illustrated in Figure 1. In this example,

Compared with Glossy, EACIF can reduce redundant transmissions.
Inspired by this insight, we propose an energy adaptive CI-based flooding protocol (EACIF) for WSN-AF. EACIF improves energy adaptive CI-based flooding through energy scheduling and topology control. Compared with the state-of-art CI-based flooding protocols, EACIF achieves lower energy consumption, lower latency, and the same coverage and reliability. The major contributions of this work are summarized as follows. We are the first to propose a lightweight distributed energy adaptive CI-based flooding protocol (EACIF) for WSNs. EACIF adapts to the network changes in residual energy and selects the optimized forwarding set via the communication between neighbors. EACIF constructs a sparse topology for CI-based flooding via an approximate minimum connected dominating set (MCDS) algorithm, which can be completed approximately in EACIF proposes a k-covered mode switching algorithm (KMSA) for k-covered UDG and theoretically derives the energy saving formula for CI-based flooding. We simulate EACIF based on uniformly distributed topology and real topology. Simulation results show that EACIF can achieve the same reliability as Glossy, while reducing 63.96% energy consumption on the real trace.
The rest of the paper is organized as follows. We review the related work in Section 2. In Section 3, we analyze the process of CI-based flooding and present active nodes selection algorithm (ANSA) and k-covered mode switching algorithm (KMSA). We evaluate the performance of EACIF in Section 4 and conclude the paper in Section 5.
2. Related Work
Constructive interference (CI) is a physical layer phenomenon and was first experimentally discovered by Dutta et al. [12]. Subsequently, CI is used in backcast [13] to avoid broadcast storm problem. CI can be achieved by submicrosecond time synchronization of all coordinated senders. A typical scenario of CI is shown in Figure 2;

The basic principle to generate CI.
CI requires that multiple senders simultaneously transmit the same packet. This behavior is consistent with the characteristics of network flooding. Besides CI-based flooding, opportunistic flooding [17] also achieves fast network flooding by constructing a tree-based topology. Previous technologies such as CF [11] and RBP [10] schedule the data forwarding through link quality assessment. Moreover, when multiple sensor nodes simultaneously send an identical packet to the same destination, existing flooding solutions (RBP [10], FLASH [18], and CF [11]) need to dispatch the transmission order. Otherwise, it will cause mutual interference. The dispatch overhead should never be neglected in the large size of WSN-AF system. Fortunately, CI-based flooding can eliminate redundant dispatch overhead while increasing the flooding speed.
Glossy [9] achieves the synchronization condition (
Recently, Wang et al. [23] prove that Glossy has a scalability problem. The PRR of Glossy is inversely proportional to the hops of independent paths. The reason is that independent paths increase cumulative synchronization errors. For example, the GreenOrbs project [3] is designed to deploy 1000 nodes in Tianmu Mountain, Jiaxing, China, for forest carbon sink. In order to achieve accurate data acquisition, GreenOrbs deploys 8~20 neighbors (according to the diversity of node's communication range) for every sensor node. The drawback of scalability problem is more serious in such a high dense WSN-AF system. Wang et al. also propose SCIF protocol which leverages grid topology to reduce the number of independent paths. However, the grid topology increases the path length of CI-based flooding and therefore increases the network delay. CX [24] uses the changes of relay count to conduct link selection, to some extent, reducing the number of nodes involved in transmission. Due to the randomness of relay count, CX costs considerable computational overhead and energy consumption. Compared with the above CI-based flooding protocols, EACIF is an energy adaptive CI-based flooding mechanism. EACIF achieves high reliability, high speed, and low-power network flooding via distributed management of node residual energy.
3. EACIF Implementation
Enlightened by SCIF [23], we find that a sparse topology can help to achieve energy adaptive CI-based flooding. However, there are still some challenges. The first challenge is to guarantee full network coverage while achieving fast network flooding and high packet reception ratio (PRR). The second challenge is to achieve a lightweight distributed energy scheduling algorithm for redundancy cover sets. In this section, we introduce the implementation of EACIF. We analyse the state migration of CI-based flooding in Section 3.1. Then, we introduce the topology control algorithm in Section 3.2, followed by the design of k-covered mode switching algorithm in Section 3.3. Moreover, we theoretically analyze the energy consumption of EACIF in Section 3.4.
3.1. The Analysis of CI-Based Flooding
CI-based flooding is a network flooding technique based on the hierarchical model. In the first round, the initiator broadcasts a packet to its one-hop neighbors. Then, the one-hop neighbors will forward the received packets to the initiator and the two-hop neighbors in the second round. Every other round, nodes on each layer forward the flooding packet once. Each node stops forwarding packet if its transmission count reaches the transmission threshold.
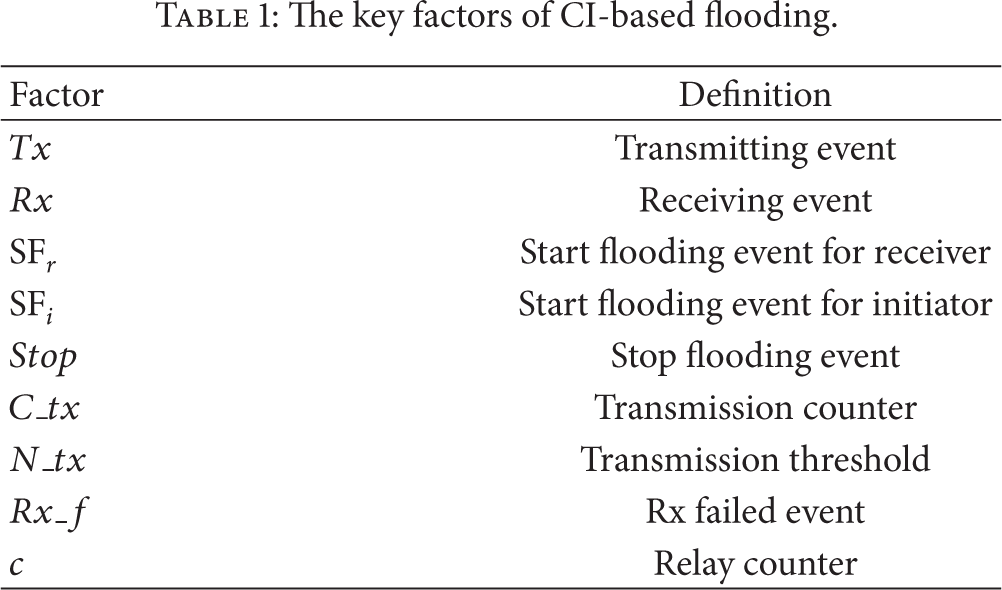
Key factors of CI-based flooding are listed in Table 1.
The key factors of CI-based flooding.
As Figure 3 shows, CI-based flooding has four correlative states including Radio off state, Standby state, Send state, and Receive state. When
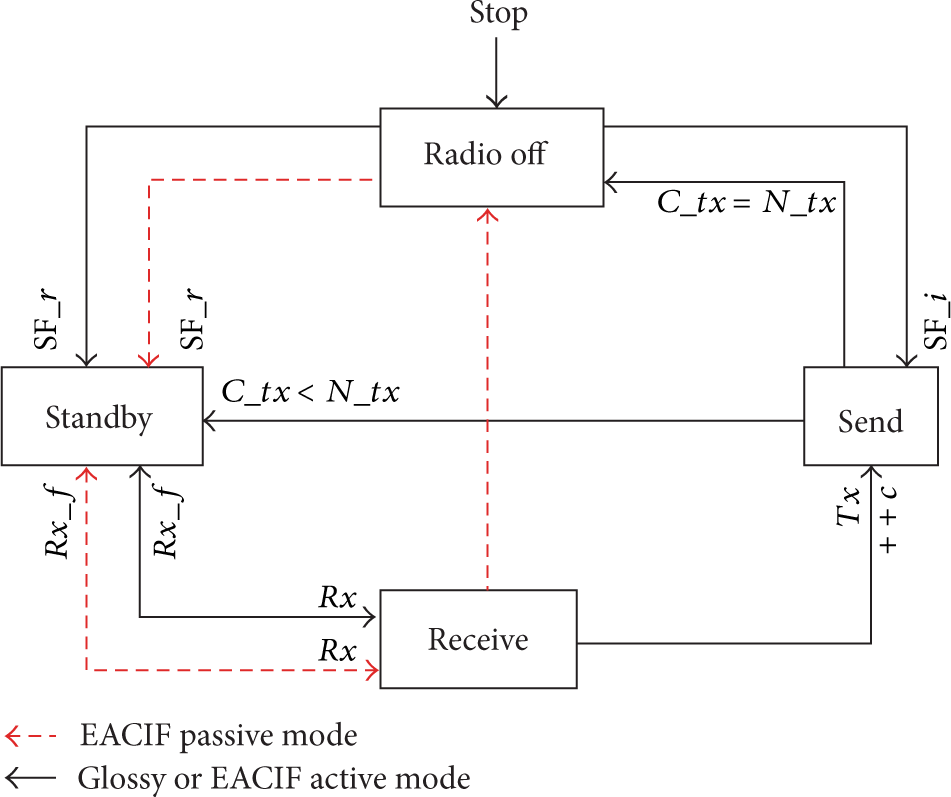
Node's state transition graph for CI-based flooding. Black solid lines represent the node working in active mode and red dashed lines represent the node working in passive mode.
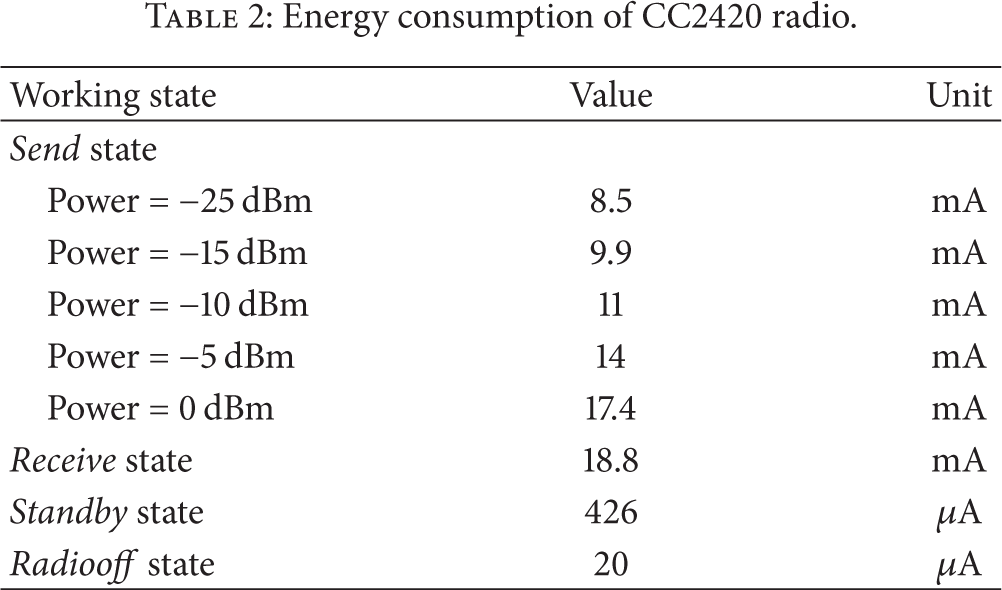
Table 2 shows the energy consumption of a typical IEEE 802.15.4 compliant radio CC2420 [25]. The power consumption of Send state and Receive state is at milliampere level, while Radio off state and Standby state only consume microampere-level power. Obviously, CI-based flooding should convert the nodes to Send state and Receive state as seldom as possible. As a topology independent CI-based flooding protocol, Glossy employs all nodes in WSNs looping in Standby → Receive → Send until flooding ended. Each cycle has two “milliampere-level” states and one “microampere-level” state. As Figure 3 shows, each node in EACIF has two interconvertible modes: the active mode and the passive mode. In active mode, the node has the same state conversion schedule with Glossy, while the node in passive mode need not forward the received packet. If it has received the packet successfully, the node will turn to Radio off state to save energy. If the reception has failed, the node will turn to Standby state for the next
Energy consumption of CC2420 radio.
The scenario shown in Figure 4 illustrates the flooding process of EACIF when

Flooding process with EACIF (
3.2. Topology Control Algorithm
To save energy, one of the main challenges is to find the fewest nodes in active mode to cover the whole WSN. Then, we need to design an energy-driven policy for mode scheduling. In order to complete these challenges, EACIF proposes a distributed algorithm to select the active nodes in a given topology and develops a mode scheduling policy based on residual energy.
3.2.1. Geometric Definitions
We assume a WSN consisting of n sensor nodes deployed in a two-dimensional plane. The node set is defined as V. A set of edges E can be defined by the Euclidean distance of any two nodes. In this way, we can define a simple undirected graph
Definition 1.
In a simple undirected graph
Definition 2.
In
Definition 3.
In
Definition 4.
A
We call the nodes in D “active dominators” (
3.2.2. Active Nodes Selection Algorithm
Enlightened by Section 3.1, we consider to construct an approximate MCDS as a sparse backbone. In a previous work, Wan et al. [26] have proposed an effective MCDS generation algorithm for wireless ad hoc networks. However, Wan's approach does not optimize the residual energy. In this paper, we propose a distributed active nodes selection algorithm (ANSA) which generates an approximate MCDS according to node's residual energy.
Definitions 2 and 3 indicate that “active nodes” include the
AD Election Subalgorithm.
( residual energy of v; ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( ( (
AG Election Subalgorithm. As Algorithm 2 shows, all
( ( announcement and ( ( ( ( ( ( ( ( (11) (12) (13) //u, w are (14) (15) (16) ( (18) (19) ( ( ( ( ( ( ( ( ( (
Time Complexity. As a distributed algorithm, the time complexity of a
3.3. k-Covered Mode Switching Algorithm
According to Definition 4, a k-covered
( ( ( ( ( ( ( ( ( (11) (12) (13) (14) (15) (16) (17) (18) (19) (
3.4. Power Consumption Model
In this section, we first establish the model of power consumption for CI-based flooding and then analyse the energy saving by EACIF in k-covered UDG.
Referring to Section 3.1, we define the main specifications of CI-based flooding. The unit time power consumption of Standby state, Send state, and Receive state can be, respectively, described as
Glossy completes flooding after all nodes run 
The energy consumption of active nodes is the same as Glossy, while the passive nodes only need to run 


4. Performance
In this section, we evaluate EACIF in both real trace and uniformly distributed topology. Section 4.1 evaluates ANSA algorithm of Section 3.2. Section 4.2 measures the packet reception rate (PRR) of EACIF. Sections 4.3 and 4.4, respectively, evaluate the latency and energy consumption.
4.1. Topology Control Evaluation
We first evaluate the topology control algorithm of Section 3.2 by MATLAB 7.11 platform. We use a real trace of previous work [28] which has 1052 nodes deployed in a ten-kilometer area. As Figure 5(a) shows, all nodes labeled as

Active nodes selection in real traces. In (b),
4.2. The PRR Evaluation
Figure 6 shows the evaluation of PRR. We define CI-based flooding parameters as follows: the length of packet payload is 32 bytes, the variance of clock frequency drift

The PRR evaluation.
As Figure 6(a) shows, the PRR of EACIF and Glossy are more than 97.1% (
4.3. Flooding Latency Evaluation
For each node, the flooding latency is defined as the duration from

Flooding latency evaluation.
Figure 7(b) plots the flooding latency of a uniformly distributed network with 2000 nodes. Using EACIF, 125-node latency is less than 1 ms. In uniformly distributed topology, Glossy spends 27% time more than EACIF. Although Glossy is a fast CI-based flooding protocol, our evaluation results show that EACIF can flood much more quickly. This is because EACIF reduces retransmissions by constructing a sparse network topology. The simulation results indicate that EACIF can effectively resolve the scalability problem in large-scaled WSNs.
4.4. Energy Consumption Evaluation
We use the average radio on time to evaluate the energy consumption of EACIF. Figure 8(a) shows the average radio on time of real trace. When the transmission distance is increased from 40 m to 100 m, the average radio on time of Glossy changes from 22.4 ms to 19.7 ms, while the average radio on time in EACIF changes from 15.1 ms to 7.1 ms. When the transmission distance is 100 m, EACIF can save 63.96% more energy consumption than Glossy. Figure 8(a) indicates that EACIF's effect of energy saving is proportional to network density. Simulation results verify the indication of (4).

Average radio on time evaluation.
In Figure 8(b), the node number increases from 500 to 2000. The average radio on time of Glossy has 31.2% increasement. It means that Glossy suffers scalability problem. However, the average radio on time of EACIF has a slight decrease. When the node number is 2000, the average radio on time of EACIF is 11.2 ms. We assume that a WSN-AF system sends a packet every 30 seconds. The duty cycle of EACIF is 0.11%.
5. Conclusions and Future Work
In this paper, we introduce EACIF, the first work to improve energy adaptivity of CI-based flooding. We first implement ASNA to construct a sparse backbone on a given topology. Then, we propose KMSA algorithm to control the flooding process. We experimentally validate the performance of EACIF on real trace and the uniformly distributed topology. Simulation results indicate that EACIF can efficiently reduce redundancy retransmissions and significantly reduce energy consumption. Our future work includes the performance measurements of EACIF in real-world large-scale WSN-AF and the exploitation of EACIF in wireless time synchronization and remote reprogramming.
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This work is partially supported by the National Natural Science Foundation of China (NSFC) under Grants nos. 61272426, 61373079, 61325013, 61033015, 61272430, 61173173, 61472227, 61272244, 61373175, 61175053, 61272369, and 11271007, the National Science Foundation of Shandong Province under Grants nos. ZR2011FL008 and ZR2011FL004, Specialized Research Fund for the Doctoral Program of Higher Education under Grants nos. 20130201120016 and 20123718110010, and the Fundamental Research Funds for the Central Universities of China under Project no. 2012jdgz02 (Xi'an Jiaotong University).
