Abstract
Verifiable top-k query processing in tiered sensor networks, which refers to verifying the authenticity and the completeness of top-k query results received by the network owner in tiered sensor networks, has received attention in very recent years. However, the existing solutions of this problem are only fit for static sensor network. In this paper, we try to solve the problem in a tiered mobile sensor network model, where not only static sensor nodes but also mobile sensor nodes existed. Based on the tiered mobile sensor network model, we propose a novel verifiable scheme named VTMSN for fine-grained top-k queries. The main idea of VTMSN is as follows: it maps each of the positions where sensor nodes are in a static state to a virtual node and then establishes relationships among data items of each virtual node with their score orders, which are encrypted along with the scores of the data items and the time epochs using the distinct symmetric keys kept by each sensor node and the network owner. Both theory analysis and simulation results show the efficiency and the security of VTMSN.
1. Introduction
More and more attention has been paid to two-tiered sensor networks in recent years [1–3]. A two-tiered sensor network, which is shown in Figure 1, consists of a lot of resource constrained sensor nodes at the lower level and some master nodes with relatively abundant resource at the upper level. The main tasks of the sensor nodes are to monitor the surroundings and generate sensing data, while the main tasks of the master nodes are to collect the sensing data from the sensor nodes and answer queries from the network owner. This two-tiered architecture is known to improve the scalability and capacity of the sensor networks. Besides, it is also able to reduce system complexity and prolong the network lifetime [3].

A traditional tiered sensor network model.
In this paper, we present a new sensor network model named TMSN (tired mobile sensor network) based on the two-tiered network architecture, which is shown in Figure 2. The difference between TMSN and the traditional two-tiered sensor network model is that mobile sensor nodes existed at the lower level of TMSN while all sensor nodes are static in the latter case. There are many advantages when mobile sensor nodes are introduced into the two-tiered network architecture. As an example, moving some of the mobile sensor nodes to heavy traffic regions can help balance the energy consumption of the sensor nodes at the lower level of TMSN. Another example is target coverage [4]. Some of targets in a tiered sensor network may lose coverage because of the early death of some sensor nodes or bad initial deployment of the sensor nodes. If some mobile sensor nodes exist, they can move to the position where dead nodes are located or to some other places by well designing [5].

A tired mobile sensor network (TMSN) model.
Top-k query is an important kind of queries in sensor networks. To obtain the top k data items from all the data items generated by the sensor nodes in the interested region, the network owner first sends a top-k query to each of the master nodes whose cells are intersected with the interested region. Each of the master nodes processes the top-k query locally and finds out the top-k query result in the intersected region in its own cell. Then the master nodes send their own query results to the network owner. Finally, the network owner finds out the final top-k query result according to the data received from the master nodes.
Nowadays, the security of top-k queries in tired sensor networks is under threat. If the master nodes are compromised, they may tamper the query results and return incomplete and/or false top-k query results to the network owner. Moreover, although introducing mobile sensor nodes into tiered sensor network architecture can bring many advantages, it also brings some challenges. One of the challenges is that the data items generated by the same sensor node may be generated at different locations, and the compromised master node may take place the data items generated in the query region with the data items generated by the same sensor node in other places. This is hard to be detected using the existing security verification method in tired sensor networks.
To verify the authentication and the completeness of the top-k query results received by the network owner in TMSN, we propose a novel verification scheme, which is called VTMSN. We assume that each sensor node in TMSN has two states: a mobile state and a static state, and they only generate sensing data when they are in a static state. The main technique of VTMSN is that it maps each of the positions where mobile sensor nodes are in a static state to a virtual static node. Thus, a mobile sensor node becomes one or many static sensor node/nodes for a given time interval. Then, with some modifications, schemes used in static tired sensor networks to verify the authentication and the completeness of the top-k query results received by the network owner can be used in TMSN.
In summary, the main contributions of this paper are listed as follows:
We present a new sensor network model named TMSN based on the two-tiered network architecture, where mobile sensor nodes are introduced into the lower tier of the architecture. We investigate the problem of verifiable fine-grained top-k queries in TMSN for the first time and propose an effective verification scheme called VTMSN to verify the authentication and the completeness of the top-k query results. Theory analysis and extensive experiment have been conducted to show the efficiency and feasibility of our scheme VTMSN.
The rest of this paper is organized as follows. Section 2 presents the related work; Section 3 presents the network and attack models; Section 4 presents the notations, some definitions, and the problem statement; in Section 5, we provide the novel verification scheme VTMSN as well as the analysis of its detection probability and energy efficiency; the simulation results and their analysis are given in Section 6; Section 7 makes a conclusion.
2. Related Work
Many schemes and protocols are developed to secure query processing in two-tiered sensor networks. Some of them are proposed for range queries [6]. Range queries ask for data within one or multiple attributes falling into specified ranges, and they are different from top-k queries, which aim at finding k data items with peak values among all the data items generated in the query region. Some other papers focus on the problem of securing top-k queries [3, 7–10]. Zhang et al. [3] proposed three schemes, which are the closest work to ours, to solve the problem of verifiable fine-grained top-k queries in two-tiered sensor networks. All of them are only fit for static tiered sensor networks, because it is assumed that the network owner knows the mapping between sensor node IDs and their respective geographic locations. This assumption can not hold in TMSN because of the mobile sensor nodes.
There are also some works for mobile sensor networks or for mobile target detection in sensor networks [11]. Good schemes [4, 12, 13] are proposed to solve many kinds of coverage problems in mobile sensor networks; [14–17] are dedicated in localization in mobile sensor networks; routing protocols are studied in mobile sensor networks in [18–20]; an efficient framework for in-network data replication and acquisition in mobile sensor networks are proposed in [21]. In [22], mobility management of mobile sensors was discussed for the purposes of forming a better wireless sensor network. In [23], low cost data gathering using mobile hybrid sensor networks is achieved. In [24], a group-based discovery mechanism was proposed to reduce the discovery delay in low-duty-cycle mobile sensor networks. To the best of our knowledge, no work has been done considering mobile sensor nodes in tiered sensor networks at present.
3. Network and Attack Models
3.1. TMSN Model
Similar to the traditional tiered sensor networks, TMSN also contains two levels. At the lower level, there are a lot of resource-constrained sensor nodes, which are deployed into many cells. At the upper level, there are some master nodes with relatively abundant resource, each of which is responsible for one cell of sensor nodes at the lower level. We assume that time is divided into epochs, which is the same with [3]. At the end of each epoch, each sensor node sends all of its data generated during the epoch to its corresponding master node. After collecting the data from sensor nodes, master nodes can answer top-k queries from the external network owner. The network owner can communicate with some of the master nodes via an on-demand wireless (e.g., satellite) link, which is relatively low-rate. We assume that each sensor node communicates with its neighboring sensor nodes with short-range radios while master nodes can communicate with their neighboring master nodes through relatively high-rate, long-range radios.
The significant difference between TMSN and the traditional tiered sensor networks is that mobile sensor nodes existed in TMSN while all sensor nodes are static in the latter case. The manner of mobility for a sensor node can be divided into two kinds: controllable mobility and uncontrollable mobility. In this paper, we assume the mobility behaviors of sensor nodes are controllable. Specifically, we assume that each sensor node only moves in its own cell. The sensor nodes do not always move because their energy is limited. They will stop moving and monitor the surroundings to meet the demand of applications. When a sensor node stops at some place, the first thing it does is to estimate its position. We assume that some localization techniques in mobile sensor networks such as [14–17] are adopted to help the sensor nodes estimate their current locations. Thus, each sensor node in TMSN has two states: a mobile state and a static state. We assume that all sensor nodes generate sensing data only when they are in a static state, and we consider it a reasonable assumption because data items often need to be bound up with the locations where they are generated. Besides, we assume that all mobile sensor nodes will stop moving at the end of each epoch and assist other sensor nodes to route their data to the corresponding master nodes in the cell.
3.2. Adversary Model
Our attack model is similar as [3]. Specifically, we assume that both master nodes and sensor nodes can be compromised, and the sensor nodes that are not compromised are the majority. Adversaries may insert forged data to query results and/or return incomplete query results to the network owner through the compromised master nodes. We do not require the confidentiality of the top-k query results as in [3], but we do require the authenticity and completeness of top-k results. Because each master node in TMSN is in charge of one cell and each sensor node corresponds to one master node, an attacker who wants to break the authenticity and/or completeness of top-k query results in one cell can not get help from the compromised nodes in other cells. Thus we only focus on a cell C consisting of N sensor nodes, which are denoted by
4. Definitions, Notations, and Problem Statement
In this section, we present some definitions and important notations used throughout the paper as well as the problem investigated in this paper.
4.1. Definitions and Notations
We first list some definitions used in this paper as follows.
Definition 1 (virtual node).
A virtual node is a position where a real sensor node is in a static state, and it only exists in the epoch/epochs when the sensor node is in a static state at the position.
Definition 2 (mother node and child node).
A mother node is a real sensor node, and the child nodes of the mother node are virtual nodes generated by the same mother node.
Definition 3 (queried sensor node).
If at least one child node of a sensor node is in the query region of a top-k query during the interested time epoch, the sensor node is called queried sensor node for the query.
Definition 4 (qualified and unqualified data item).
If a data item is among the top k data items generated in the query region of a top-k query during the interested time epoch, the data item is qualified for the query. Otherwise it is unqualified for the query.
Definition 5 (qualified and unqualified virtual node).
If at least one qualified data item is generated on a virtual node for a top-k query, the virtual node is called a qualified virtual node for the query. Otherwise it is called an unqualified virtual node for the query.
Now we present the notations used in this paper. Assume that, during epoch t, each node
We use
4.2. Problem Statement
In this subsection, we present the problem and some metrics that we use to evaluate the performance of the verification scheme proposed in this paper.
Given a query
One of the performance metrics used in this paper is
(i)
(ii)
(iii)
5. Verifiable Top-k Queries in TMSN
In this section, we first propose a novel scheme named VTMSN for verifiable top-k queries in TMSN. For clarity, we ignore compromised sensor nodes temporarily in Section 5.1. Then
5.1. VTMSN: A Novel Verification Scheme in TMSN
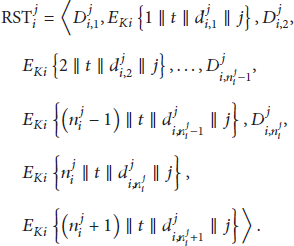
VTMSN enables completeness verification by establishing relationships between every two ordered neighboring data items of each virtual node with their orders, which are encrypted along with the time epoch numbers and the virtual node IDs by the symmetric keys shared by sensor nodes and the network owner
5.1.1. Data Preparation
At the end of each epoch, each sensor node if if
where term
5.1.2. Data Submission
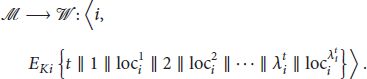
After preparing the information for each virtual node
When the message is received by
5.1.3. Query Processing
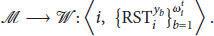
When a top-k query primitive If If If If If If where If
After
If
In fact, the amount of information in
5.1.4. Verification
When receiving a top-k query result
Completeness verification of
Input: top-k query Output: completeness (1) completeness = true (2) (3) Decrypt each term (4) (5) (6) (7) if (8) }else{ (9) (10) } (11) } (12) } (13) }else if no data item is in (14) (( (15) {completeness = false} (16) } (17) (not all the values of j in the encrypted terms in number in the encrypted terms in (18) (19)
In Algorithm 1, lines (1)–(16) can verify the completeness of
5.2. Performance Analysis of VTMSN
Theorem 6.
As long as none of the queried sensor nodes is compromised, a compromised master node can not insert forged data into query results without being detected by VTMSN.
Proof.
This theorem is actually proved in the verification stage in Section 4.1.
Theorem 7.
As long as none of the queried sensor nodes is compromised, a compromised master node can not replace data items generated during the interested time epoch with data items generated in some other time epochs without being detected by VTMSN.
Proof.
Each encrypted term in top-k query results contains an epoch number t in VTMSN. Thus, it is easy to detect such behaviors by checking the time epoch numbers in the encrypted terms.
Theorem 8.
As long as none of the queried sensor nodes is compromised, a compromised master node can not replace qualified data items with unqualified data items generated during the same epoch without being detected by VTMSN.
Proof.
It is clear that the corresponding verification information should also be replaced if some data items are replaced. Then, the following two propositions prove that Theorem 8 holds.
The compromised master node can not replace qualified data items with unqualified data items of the same virtual node without being detected by VTMSN. This is because the orders in the encrypted terms following the data items will not be consecutive if such behavior is made. The compromised master node can not replace qualified data items with unqualified data items of some other virtual nodes without being detected by VTMSN. The verification information of a virtual node in the query region can not be totally replaced with those of another virtual node because each virtual node in the query region is asked to include its verification information in the query result. Besides, if some qualified data items of a virtual node are replaced with unqualified data items of some other virtual nodes, either the encrypted terms for the same virtual node in the query result can not be decrypted by the same key or the values of j got from each encrypted term following each data item of the same virtual node in the query result are not the same. According to Algorithm 1, both cases can be detected by VTMSN.
Theorem 9.
As long as none of the queried sensor nodes is compromised, VTMSN can detect any incomplete top-k query result with probability
Proof.
There are totally two methods for
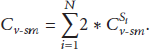
Next, we will analyze the in-cell communication cost
Parameters and their meanings.

For a child node, which does not have data item in time epoch t, of sensor node 
Let 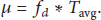
Then, for a child node that has data items in time epoch t of sensor node 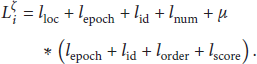
For each sensor node 
Let 
Then we have
In this paper, we assume that the energy consumption incurred by sending and receiving one bit of data is the same as in [3]. So in formula (17), the total energy consumption is doubled.
Suppose that a query 
Let The first case is that The second case is that
where 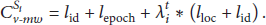
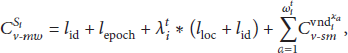
If 
If sensor node 
Then we have

Similarly, we assume that the energy consumption incurred by sending and receiving one bit of data is the same across the on-demand wireless link. Thus,
5.3. Impact of Compromising Some Sensor Nodes
In above sections, we never consider the case that some sensor nodes are compromised. Thus we now further analyze the impact of compromised sensor nodes. If some sensor nodes are compromised, the following two kinds of attack may be launched.
(1) The compromised sensor nodes may collaborate with 
However, some countermeasures can be adopted to solve this problem. One countermeasure is to shrink the query region, so that
(2) If
6. Performance Evaluation
In this section, we evaluate the efficiency of VTMSN and illustrate the impact of some factors on the metrics presented in Section 4. We use OMNET++ as our simulator. In our simulation model, we assume the size of a cell in TMSN is 400 m × 400 m. In each cell, 500 sensor nodes are deployed randomly. They switch their states between mobile state and static state periodically. Some other default parameters are listed in Table 2, where R is the communication radius of each sensor node,
Default evaluation parameters.

6.1. The Results of
and the Corresponding
To evaluate the performance of
6.1.1. Impact of Parameters
,
, and
Figure 3 shows that

Impact of parameters

Impact of parameters
From Figure 3, we can also find that the longer the total time for sensor nodes to be in a static state in one epoch is, the larger
Now we explain why
6.1.2. Impact of Parameter
From Figure 5, we can see that the larger

Impact of parameter

Impact of parameter
6.2. The Results of
and the Corresponding
In this subsection, we evaluate the performance of our verification scheme VTMSN on
6.2.1. Impact of Parameters
and k
Figure 7 shows the impact of the query region

Impact of parameters
Figure 8 shows the impact of
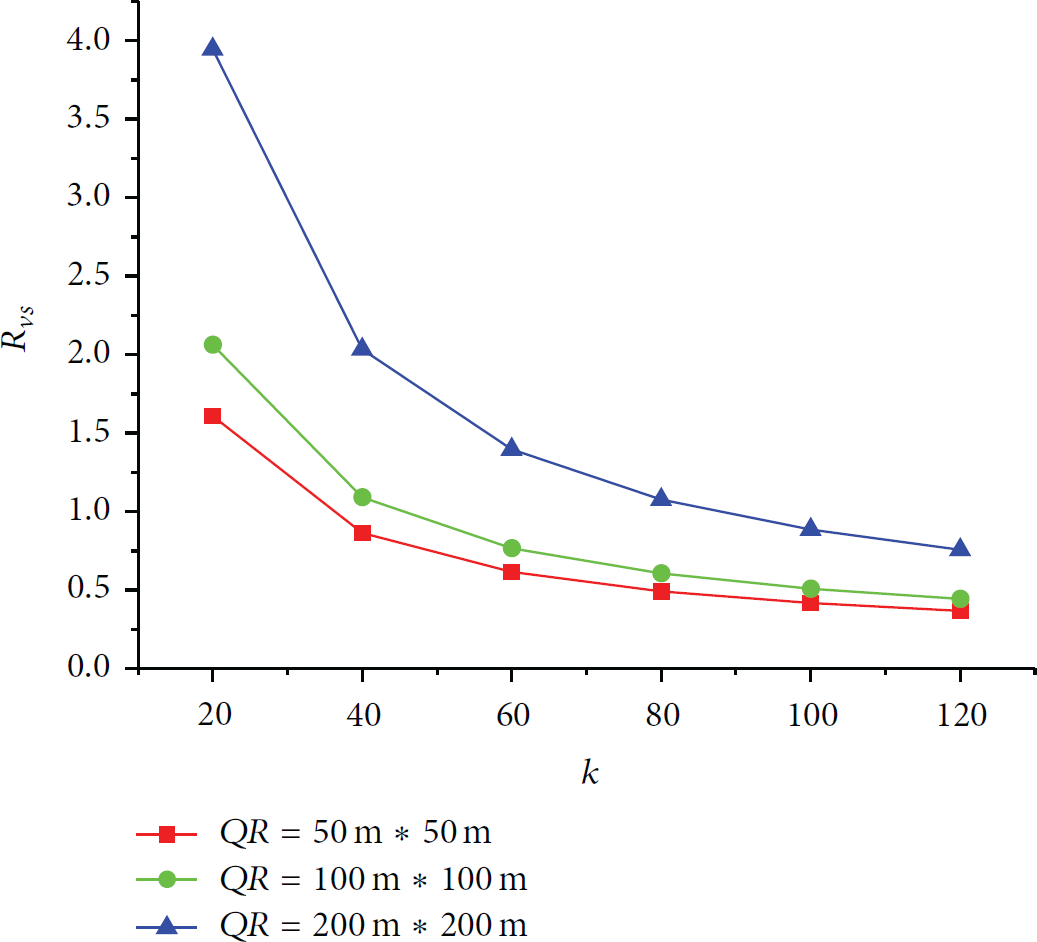
Impact of parameters
6.2.2. Impact of Parameters
,
, and v
Figures 9 and 10 show the impact of moving period

Impact of parameters

Impact of parameters
In theory, with the same other parameters, the more the times for sensor nodes to switch their states in one epoch are, the larger
6.2.3. Impact of Parameter
Figures 11 and 12 show the impact of query frequency

Impact of parameter

Impact of parameter
7. Conclusion
In this paper, we present a tiered mobile sensor network model named TMSN for the first time and propose an effective verification scheme called VTMSN to verify the authentication and the completeness of the top-k query results received by the network owner in TMSN. The proposed scheme achieves the goal of making the network owner verify the authenticity and completeness of top-k query results in TMSN with high probability and good efficiency via the mechanisms of virtual node mapping and data binding. Theory analysis shows that VTMSN can detect any forged and/or incomplete top-k query result with probability that
Footnotes
Conflict of Interests
The authors declare that there is no conflict of interests regarding the publication of this paper.
Acknowledgments
This research is supported by the National Natural Science Foundation of China under Grant no. 61562005, the Natural Science Foundation of Guangxi Province under Grant no. 2015GXNSFAA139286, 2015 Scientific and Technological Research Projects of Universities in Guangxi Province under Grant no. KY2015YB486, and the Project of Outstanding Young Teachers' Training in Higher Education Institutions of Guangxi Province.